P2P WebRTC secure messaging is the technical and sovereign backbone of CryptPeer’s direct, end-to-end encrypted communication. This synergy now reshapes the very architecture of digital exchanges. At the crossroads of network engineering, protocol security and applied cryptography, this chronicle explores how CryptPeer relies on the peer-to-peer model to enforce fully local control of the flow, with no third-party intermediate server and no structural dependency on cloud platforms, relying at most on an optional self-hosted local relay node that only forwards encrypted traffic. P2P and WebRTC technologies are not just about performance or confidentiality. They embody a fundamental break with centralised systems by enabling a technical dialogue where each user becomes the sole holder of the secret, the channel and their own exposure. In this sense, direct communication is not a simple architectural option but a doctrinal stance: proving sovereignty by design
Quick summary — What to remember
Fast read ≈ 2 min — WebRTC and the peer-to-peer model form the backbone of P2P WebRTC secure messaging : direct, encrypted communication independent of any third-party cloud server. CryptPeer relies on this architecture to establish a sovereign channel between browsers, where each user keeps local control of the flow, the keys and their own exposure.
Principle: the direct-to-direct connection replaces the traditional centralised scheme. The flow no longer passes through a third-party platform: it is negotiated, encrypted and maintained between the peers, with at most a user-controlled local relay node forwarding only ciphertext. This approach reduces the attack surface, limits involuntary data collection and neutralises structural dependence on cloud infrastructures.
Foundation: WebRTC builds real-time communication on a triptych — SDP negotiation, NAT traversal via ICE/STUN/TURN and DTLS-SRTP encryption. The DataChannel completes the design with a robust P2P channel for messages, metadata and binary transfers.
Observation: in 85 to 90% of cases, the direct connection is established without any relay at all, ensuring minimal latency and full control. In the remaining cases, an optional self-hosted, portable relay node can forward only end-to-end encrypted traffic. The signalling server is used only before the connection and keeps no state. Once the link is established, the communication path remains fully under user control.
Stake: this architecture is not just a technical choice. It shifts the centre of gravity of trust — from the cloud back to the user — and reminds us that sovereignty is exercised through local control: end-to-end cryptography, no cleartext storage on servers, network autonomy.
⮞ In short: CryptPeer shows that P2P WebRTC secure messaging is not a fallback option but a new standard for direct, encrypted and independent communication, where trust is proven by design rather than delegated.
Reading parameters
Quick summary: ≈ 2 min
Extended summary: ≈ 7 min
Full chronicle: ≈ 32 min
Publication date: 2025-11-14
Last updated: 2025-11-14
Complexity level: Sovereign & Technical
Technical density: ≈ 78 %
Languages available: FR · EN · ES · CAT · AR
Thematic focus: P2P, WebRTC, encryption, direct communication
Editorial type: Chronicle — Freemindtronic Cyberculture Series
Impact level: 8.4 / 10 — technical and sovereign

Table of contents
- Quick summary — Key takeaways
- Extended summary — P2P, WebRTC and technical sovereignty
- P2P architecture, WebRTC protocol and communication sovereignty
- P2P model — Operation, strengths and limits
- WebRTC — Negotiation, encryption and direct flows
- ICE, STUN, TURN — NAT traversal and resilience
- DataChannel — Sovereign off-media exchanges
- CryptPeer application — Proven direct communication
- Security — DTLS, SRTP and local trust model
- Performance — Latency, optimisation and stability
- Contemporary challenges — P2P vs network policies
- Technical sovereignty — Local proof and non-retention
- Perspectives — Towards a decentralised Internet
- P2P & WebRTC FAQ
- What we didn’t cover
- Sovereign use cases — Freemindtronic
Extended summary — P2P, WebRTC and sovereign architectures for direct communication
According to the IETF (RFC 8825, 8826), WebRTC defines a set of mechanisms that allow two devices to negotiate, encrypt and maintain a direct connection. This architecture goes far beyond pure network optimisation: it enforces a paradigm in which each user holds operational control over the channel, without delegating it to a third-party server. Communication sovereignty here depends on the ability to establish, maintain and secure an end-to-end connection without structural dependency.
Technical definition — IETF WebRTC Framework (RFC 8825)
“WebRTC is a set of protocols enabling interactive multimedia sessions between browsers or applications using a secure peer-to-peer communication model.”
It involves:
- SDP negotiation: describing audio/video capabilities, codecs and cryptographic parameters;
- Secure transports: DTLS for key exchange, SRTP for protecting media flows;
- Connectivity resolution: ICE, STUN and TURN to find a direct path across NATs;
- P2P data channels: DataChannel for fast, sovereign off-media exchanges.
In a systemic reading, Rescorla (author of the WebRTC security model) reminds us that meaningful confidentiality in communications first depends on the ability to avoid intermediaries. Encryption is only relevant if the channel remains sovereign — that is, established and controlled by the peers themselves.
For Hardy and W3C’s work, the rise of centralised architectures makes it essential to prioritise protocols that enable direct interactions. Technical autonomy becomes a prerequisite for protecting identities and metadata.
Contemporary normative frameworks — Towards proven and sovereign communication
Modern cybersecurity standards converge on the same conclusion:
- NIST SP 800-207 (Zero Trust) — mandates continuous verification and rejects any implicit trust in servers;
- ENISA 2024 — Secure communications — values local trust architectures where the technical proof is held by the user;
- IETF ICE Working Group — confirms that communication resilience depends on the ability to establish direct paths;
- Regulation (EU) 2023/1543 e-Evidence — underlines that non-retention of flows and metadata provides compliance by absence.
These frameworks reinforce the Freemindtronic doctrine: trust must be proven by design, not delegated.
The contemporary challenge is therefore to distinguish between “encrypted communication” (dependent on a server relaying the flow) and “sovereign communication” (no third parties, no emission of metadata beyond the peers).
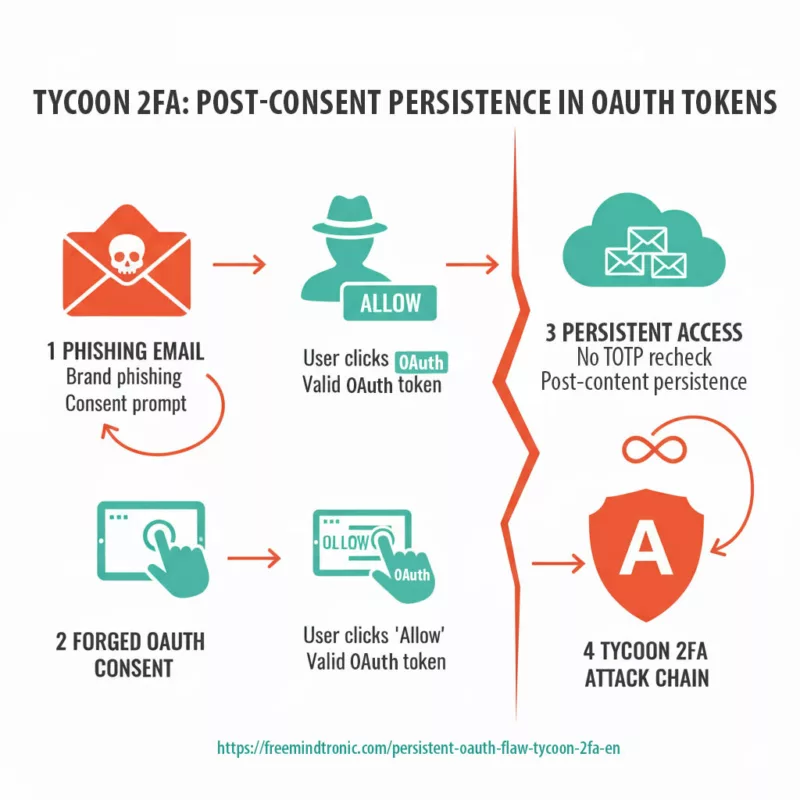
Threat landscape — The battle has moved into messaging apps
As bulk interception becomes less profitable (widespread encryption, TLS, DoH), the battlefield has shifted to the very core of messaging applications. This is now where intentions, social graphs and operational decisions converge, so that a single implant can in theory unlock “an entire life”. The same 0-click exploit chains and spyware families now target Signal, WhatsApp, Telegram and their clones, whether they are operated by state services or commercial spyware vendors. The line between state operations and private offerings is increasingly blurred: in practice, everyone hits the same building blocks (image/audio parsing, 0-click surfaces, official or fake clients), which industrialises the compromise of encrypted messengers.
Mapping table — P2P & WebRTC frameworks
| Technical framework | Key concept | Mode of application | Type of dependency | Source |
|---|---|---|---|---|
| IETF WebRTC 8825–8826 | Secure direct communication | Local negotiation · DTLS/SRTP | Network (NAT) | IETF |
| ICE/STUN/TURN | NAT discovery and traversal | Address resolution · direct paths | Network operators | RFC 8445 |
| W3C WebRTC API | User-side autonomy | Local control · DataChannel | Client applications | W3C |
| NIST SP 800-207 | Interactive Zero Trust | Local proof · continuous validation | Third-party servers | NIST |
1️⃣ Transport (finding a direct path),
2️⃣ Encryption (local DTLS/SRTP),
3️⃣ Autonomy (DataChannel, no third-party server in the loop).
This convergence enables truly sovereign communication, where each peer holds the full proof of confidentiality.
Thus, communication becomes an extension of technical autonomy: to control your channel is to self-govern in the digital space.
The chronicles displayed above ↑ belong to the same Cyberculture editorial section. They extend the analysis of sovereign architectures, local cryptography and distributed models, shedding light on the tension between network dependency and technical autonomy. This selection complements the present chronicle dedicated to P2P WebRTC direct communication, a cornerstone of the Freemindtronic doctrine.
Chronicle — P2P architecture, WebRTC protocol and communication sovereignty
P2P WebRTC secure messaging represents one of the most notable shifts in network architecture since the rise of the modern Internet. Unlike centralised infrastructures, where a server governs access, metadata and persistence, the peer-to-peer model distributes these functions across the users themselves. When this logic meets WebRTC, the result is a sovereign, end-to-end encrypted and near-instant channel whose technical control belongs solely to the two participants — the essence of secure P2P WebRTC communication.
In this chronicle, we analyse how WebRTC enables truly direct, serverless communication by combining SDP (signalling and negotiation), ICE/STUN/TURN (connectivity), DTLS/SRTP (end-to-end encryption) and the DataChannel (data transport). We also examine the central role of CryptPeer, which turns these principles into a sovereign, cloud-free secure messaging application with no server-side cleartext retention, no external third-party relay and no exploitable data collection.
P2P model — Operation, strengths and limits
The peer-to-peer model describes an architecture where each entity acts at the same time as sender, receiver and operational node. By removing centralised functions, P2P shifts trust to the edges of the network — the peers. This decentralised design naturally improves resilience, but it also requires tighter control over connectivity, authentication and traffic management mechanisms.
Key insights — The P2P model is built on three structural characteristics:
- Autonomy: no central entity monitors, filters or validates exchanges.
- Resilience: even with fragmented networks, peers can communicate as long as a path exists.
- Structural confidentiality: the absence of intermediaries automatically reduces the attack surface and exposure.
Distributed architecture: local control of the flow
In a P2P architecture, each peer holds the full session context. This means that flow description, negotiation, encryption and data transfer are not offloaded to a central server but handled locally on the endpoints. This technical autonomy rewires the trust model: the user no longer depends on a third party to exchange messages, media or files over a secure P2P WebRTC channel.
Structural limits of the P2P model
Because peers usually sit behind NAT routers or restrictive firewalls, address discovery and path establishment require more complex strategies than in a centralised model. This is exactly what WebRTC automates, while preserving operational sovereignty for end-to-end encrypted, peer-to-peer communication.
WebRTC — The core of direct communication
WebRTC is a structured set of protocols, specified by the IETF and the W3C, that enables two devices to communicate directly without relying on a central relay server operated by a third party. Unlike traditional technologies (SIP-based VoIP, WebSocket, RTP tunnels), WebRTC encapsulates the entire process — negotiation, encryption, network discovery and media/data transport — into a coherent, modern architecture designed for secure, sovereign real-time communication.
Key insights — WebRTC rests on four pillars:
- SDP: describes and negotiates peer capabilities.
- ICE/STUN/TURN: finds the best network path for direct connectivity.
- DTLS/SRTP: locally established end-to-end encryption for media flows.
- DataChannel: a sovereign P2P data transport layer for messages and files.
SDP — The common language of peers
The Session Description Protocol describes the full capabilities of each peer: codecs, keys, ports and network options. This description is never stored by the signalling server, which merely passes it along. As a result, only the user devices hold the real state of the session, which is essential for a serverless, zero-knowledge secure messaging model.
DTLS and SRTP — Locally negotiated encryption
Unlike classic messaging platforms, where the server often orchestrates key management, WebRTC negotiates keys locally between peers using DTLS. The SRTP encryption, derived from DTLS, then protects the media flows. The outcome is that even a TURN relay server cannot decrypt the packets it forwards within a P2P WebRTC secure messaging session.
ICE, STUN, TURN — NAT traversal and resilience
ICE (Interactive Connectivity Establishment) coordinates network path discovery. STUN helps determine a peer’s public address. TURN serves as a last resort when no direct path can be established. Together, these building blocks make it possible to set up direct communications in roughly 85% of real-world network configurations, even with carrier-grade NAT or strict firewalls.
DataChannel — Sovereign off-media exchanges
The WebRTC DataChannel makes it possible to send text, binary data, files and metadata directly from one browser to another. It runs over SCTP encapsulated in DTLS, providing high reliability and sovereign confidentiality. No third-party application server has visibility on these data streams; at most, a user-controlled relay node forwards opaque ciphertext, which is crucial for private file-sharing, secure P2P chat and metadata-minimising collaboration.
CryptPeer — Sovereign implementation of the P2P WebRTC model
CryptPeer implements the “direct-to-direct” paradigm in a strict way. No plaintext content or key material is ever stored on any server; only end-to-end encrypted technical data may transiently exist on a user-controlled relay node. The application uses a server only for the initial signalling phase and, when needed, a locally self-hosted relay for connectivity, after which the WebRTC session remains fully peer-to-peer and end-to-end encrypted. Because CryptPeer runs entirely in a standard web browser, with no app or plugin to install, this sovereign model remains compatible with locked-down workstations, hardened terminals and BYOD environments.
This approach is fully aligned with the Freemindtronic doctrine: sovereignty is demonstrated through local control of cryptography, the channel and exposure — a P2P WebRTC secure messaging model where users keep ownership of their secrets, their traffic and their communication surface.
Beyond classic secure messengers — segmented digital HSM and per-message keys
Unlike traditional end-to-end encrypted messaging apps that rely on the operating system of the phone or PC to protect keys, CryptPeer is anchored in a segmented-key digital HSM. In the version distributed by FullSecure, this sovereign security layer is implemented with Freemindtronic’s EviLink HSM PGP technology. Cryptographic secrets are therefore managed outside the endpoint OS, in a dedicated HSM-inspired layer under organisational control. This design significantly reduces the impact of device compromise, forensic analysis or OS-level exploits.
For each message exchanged between peers, CryptPeer derives a specific ephemeral key from this segmented-key model. Every message is cryptographically compartmentalised: compromising one message does not grant access to any other, and removing a contact can trigger local destruction of the associated reply keys on the sender’s side. The result is a fine-grained, message-level blast radius that goes far beyond traditional “one key per conversation” designs.
100% browser-based, zero-install secure collaboration
This zero-install browser-based approach is crucial for locked-down environments, hardened workstations, shared terminals and BYOD scenarios where deploying native clients is either impossible or undesirable.
Despite this purely browser-based model, users benefit from a full sovereign collaboration environment: end-to-end encrypted text messaging, audio and video calls, mission-centric teams and groups, and large encrypted file transfer. On untrusted or shared machines, users can choose to keep only locally encrypted copies of files and decrypt them temporarily to a trusted external medium when needed. The relay server still only ever sees ciphertext and never handles cleartext payloads.
Identity model and need-to-know compartmentalisation
Unlike phone-number- or e-mail-based messengers, CryptPeer anchors identity in cryptographic keys, optionally represented by avatars rather than public identifiers. Real-world affiliation (service, unit, mission, organisation) is handled through administration and categories instead of global user accounts.
Every new contact must be assigned to one or more categories, which define their contact bubble (unit, service, mission, partner, theatre, etc.). There is no global directory exposing the whole organisation. This category-based model enforces a strict need-to-know perimeter and limits lateral movement, social engineering and internal espionage opportunities.
Security — DTLS, SRTP and the local trust model
The security of WebRTC communications relies on a methodical composition of protocols designed to establish local trust. Encryption is not an add-on feature; it is the very backbone of the transport layer. This structural approach distinguishes P2P WebRTC secure messaging from traditional chat platforms, where the service often acts as a cryptographic intermediary, sometimes generating or storing keys. Here, keys never leave the peers.
From “jackpot” attacks to impact-limited design
In most centralised messengers, years of history, social graphs and encrypted secrets live in the same silo. When an implant succeeds, it enjoys a “jackpot effect”: a single compromise can drain a huge archive of past conversations. The design doctrine behind CryptPeer starts from the opposite angle: accept that an implant may exist, but reduce what it gains when it does. Segmented keys managed outside the OS, ephemeral derivations in RAM, compartmentalised communication bubbles and the ability to keep messages masked by default all restrict what an attacker can see to a narrow, local, time-bound perimeter. The goal is not to make attacks impossible, but to drive down their operational value and destroy their scalability by design.
Key insights — WebRTC security relies on three inseparable mechanisms:
- DTLS: local key negotiation directly between peers;
- SRTP: application-layer encryption of audio/video streams;
- Identity Assertion: optional external validation to authenticate peers.
These three mechanisms make interception technically pointless, even via a TURN relay server.
Segmented-key HSM and pre-quantum resilience
Beyond protocol security, CryptPeer’s segmented-key digital HSM imposes a very different attack model from classical secure messengers. An adversary cannot simply point a (future) quantum computer at a static encryption key: to even define a meaningful search space, they would first need to compromise every key segment, understand the internal derivation logic and capture the precise moment when the derived key exists in volatile memory.
In practice, this means that an attacker must achieve a deep, multi-layer compromise of terminals and the HSM before any large-scale cryptanalytic effort becomes relevant. Only after bypassing segmented-key management, local governance and ephemeral in-RAM derivation would they face the underlying hardness of AES-256. CryptPeer therefore shifts the problem from “breaking a long-lived key in the abstract” to “controlling multiple, compartmentalised secrets and a sovereign HSM in real time” — a far more demanding scenario for any adversary, classical or quantum.
DTLS — Cryptographic negotiation without a third party
WebRTC uses DTLS to negotiate cryptographic keys directly between peers. Unlike centralised protocols, no server takes part in the negotiation. DTLS establishes a secure channel across the network, ensuring that only authenticated peers can derive the SRTP keys required to encrypt the flows.
SRTP — Application-level encryption of media streams
Once keys are exchanged via DTLS, WebRTC applies SRTP to encrypt every audio and video packet. This protection works independently of the network topology, guaranteeing confidentiality even when a TURN server is used as a relay. Transport conditions never downgrade the security of the flow.
Local proof and sovereign communication
Because no server holds the keys, the confidentiality of the flow depends exclusively on the peers’ ability to secure their local environments. This model inverts the traditional trust economy: security no longer relies on a central entity, but on local, verifiable proof.
Performance — Latency, optimisation and stability
P2P WebRTC is characterised by very low latency, because no third-party cloud platform relays the packets and, in most cases, traffic flows directly between peers. This native optimisation is essential for video conferencing, interactive streaming, screen-sharing and any real-time communication scenario that is sensitive to jitter and delay.
Key insights — WebRTC performance is based on:
- Congestion control: GCC/TFRC-style algorithms that dynamically adapt bitrate;
- Codec agility: automatic selection between VP8, VP9, H.264 depending on capabilities;
- Adaptive transport: keeping the flow alive even under temporary degradation.
Minimal latency and direct path
Thanks to its direct transport mechanisms, WebRTC eliminates server-side processing and reduces latency to the bare minimum. This enables more natural, fluent and reliable secure calls, even under heterogeneous network conditions.
Resilience to packet loss
WebRTC implements error-correction mechanisms and selective retransmission. The flow stays coherent even in the presence of occasional packet loss — a critical feature for unstable environments such as mobile networks or congested Wi-Fi.
Contemporary challenges — P2P vs network policies
The multiplication of NAT devices, carrier restrictions and enterprise security policies reduces the probability of establishing direct connections. Although WebRTC is designed to bypass most of these obstacles, certain extreme environments still require TURN relays.
Technical sovereignty — Local proof and non-retention
The sovereignty of a communication in CryptPeer rests on two verifiable principles: local proof and no cleartext server-side retention. In CryptPeer’s implementation, a segmented-key digital HSM manages secrets outside the endpoint operating system, and each message uses a dedicated ephemeral key. Compromising one device or one message does not unlock the rest of the history or the organisation’s directory.
On the transport side, any optional relay node is self-hosted and only ever sees ciphertext. On the storage side, servers never retain readable content, metadata or usable keys. Users can decide, per file and per terminal, whether to keep only locally encrypted copies or also a temporary decrypted version — a critical feature on shared or untrusted machines. Any residual traces remain encrypted and under user or organisational control.
In practice, CryptPeer — distributed by FullSecure and based on Freemindtronic’s EviLink HSM PGP technology — pushes this logic further. Secrets are handled outside the phone OS, keys are derived in RAM only and can be combined with masked-display modes where messages remain encrypted by default and are decrypted on demand. This combination sharply reduces the amount of exploitable material available to an implant at any given time.
This approach is fully consistent with the Freemindtronic doctrine: a sovereign architecture is measured by its ability to operate without harming user autonomy and without delegating cryptographic governance — a truly peer-to-peer secure messaging stack that can run locally, offline and entirely under national or organisational control.
Perspectives — Towards a decentralised Internet
As cloud architectures continue to centralise services, the P2P WebRTC model restores balance by returning control of the communication flow to users. Current trends — edge computing, digital sovereignty, Zero Trust architectures and contested environments — all converge towards this paradigm: direct, end-to-end encrypted communication as the default, not the exception.
CryptPeer illustrates this transition in very concrete terms. The same stack can:
- run on a Raspberry Pi 5 or micro-node to create a local, air-gapped communication bubble without SIM cards or Internet,
- scale up to ministerial datacentres or critical infrastructure operators using the same segmented-key HSM model,
- serve multiple bubbles — crisis cells, theatres of operations, OIV partners — via an integrated multi-server manager, without mixing directories or categories.
Regalian & tactical bubble mode — outside classic interception chains
Operate CryptPeer in a self-contained tactical Wi-Fi bubble
In “bubble mode”, you operate CryptPeer over a private Wi-Fi link with smartphones left in airplane mode, without SIM cards and without any 2G/3G/4G/5G attachment or professional radio systems such as TETRA / PMR (~380–430 MHz) and certain LTE carriers (for example 800 MHz LTE band 20). The communication bubble stays physically limited to the propagation range of the Wi-Fi signal and never touches public mobile or PMR infrastructures.
Bypass classic telecom interception chains
In this configuration, CryptPeer structurally bypasses many of the usual telecom interception chains — operator core networks, lawful interception interfaces, LTE monitoring, TETRA / PMR capture and IMSI-catchers. An adversary must instead move physically close, equip themselves to sniff Wi-Fi bands (2.4 / 5 / 6 GHz) and, even then, they only ever see end-to-end encrypted ciphertext.
Accept that RF detection remains possible, but without metadata
Of course, a state-level electronic warfare unit that deliberately approaches the area can still detect RF activity in Wi-Fi bands and roughly localise the emission zone using standard direction-finding techniques. However, it never gains access to mobile-network metadata or to cleartext content, because no telecom operator participates in the communication loop and CryptPeer keeps all traffic peer-to-peer encrypted from end to end.
Reduce the local attack surface with a segmented-key digital HSM
On top of that, CryptPeer’s cryptography runs at the terminal level in volatile memory (RAM), with no server-side cleartext and no mandatory local cleartext storage on the device. Even on a smartphone limited to the local Wi-Fi network and completely offline, this architecture drastically reduces the attack surface: there is no telecom infrastructure to compromise, no persistent cleartext to recover, and only transient, RAM-based cryptographic material governed by the segmented-key HSM model.
Further reading — interception on public networks
For reference — examples of interception and lawful interception chains on public networks:
- ETSI – Lawful Interception standards for telecom networks
- Bundesnetzagentur – Technical guideline on lawful interception (TR TKÜV)
- ENISA – 5G security and the balance between lawful interception and end-to-end confidentiality
- CableLabs – Understanding IMSI-catchers and mobile network interception
- Public research on TETRA / PMR vulnerabilities and interception risks
At the same time, the current convergence between state operations and commercial spyware — from 0-click image and audio exploits in mainstream messengers to “middle-market” surveillance kits — reinforces this architectural choice. The question is no longer only “can I stop the implant?”, but “how much can it still steal if it succeeds?”. As long as years of history, social graphs and keys live in a single silo, a compromise remains a jackpot.
P2P WebRTC secure messaging is therefore more than a protocol choice; it defines a model of governance. Instead of relying on public cloud platforms and global directories, organisations choose to operate self-contained sovereign bubbles, where they control identities, keys, flows and exposure locally. By doing so, they pave the way for future trust-by-design communication systems that remain portable, compartmentalised and resilient, even when infrastructure and terminals no longer offer full trust.
Technical FAQ — P2P, WebRTC and CryptPeer
Key point — WebRTC always encrypts P2P traffic by design
Yes, modern WebRTC implementations always encrypt traffic by default. In every current browser, WebRTC secures audio and video streams with SRTP and protects data channels with DTLS/SCTP. As a result, no WebRTC packet travels in cleartext over the network, even for basic video calls or simple data transfers.
Because of this, P2P WebRTC secure messaging already starts from an encrypted transport layer. CryptPeer then goes further: it adds a segmented-key digital HSM and per-message ephemeral keys on top of WebRTC. In practice, WebRTC provides the secure tunnel, and CryptPeer builds a sovereign, end-to-end encrypted messaging layer inside that tunnel. This combination lets you benefit from both: standards-based, widely audited encryption at the transport level and a high-assurance, HSM-governed E2EE model for long-term confidentiality.
Interception question — What a relay really sees on the wire
No. A TURN relay never sees the readable content of a P2P WebRTC secure messaging flow. Instead, it simply forwards encrypted packets, without any access to the keys that protect them. Even in long-lasting sessions, the relay only handles ciphertext and never receives enough information to decrypt media or messages.
CryptPeer uses this property in a sovereign way. When a relay becomes necessary, it runs as an optional, self-hosted node under the organisation’s control, inside a local or national infrastructure. Consequently, telecom operators, cloud providers and external attackers do not gain a new vantage point on your flows. They only see opaque, end-to-end encrypted traffic, and the relay itself operates as a neutral pass-through component with no decryption power and no usable metadata retention.
Sovereignty question — Who really controls the channel and the keys?
CryptPeer delivers sovereign communication because it lets the organisation fully control infrastructures, keys and exposure. You run the servers yourself — from a Raspberry Pi 5 micro-node up to a ministerial datacentre — and you never give encryption power to a third-party cloud provider. The servers handle only signalling and, if needed, a self-hosted relay; they never see cleartext content or master keys.
At the same time, CryptPeer relies on a segmented-key digital HSM and per-message ephemeral keys to implement end-to-end encryption that does not depend on the phone or PC operating system. Combined with P2P WebRTC secure messaging and the ability to operate in completely local “bubble mode”, this model lets regalian services and operators of critical infrastructure keep cryptographic governance, traffic and identity perimeter entirely under their own control.
Tactical scenario — P2P bubbles without any Internet backbone
Yes, P2P WebRTC works very well on a local network without any Internet connection. WebRTC can rely on ICE and mDNS to discover peers purely inside a private Wi-Fi or wired LAN. In that case, the entire P2P WebRTC secure messaging flow stays inside the local network perimeter and never touches the public Internet.
CryptPeer uses this capability to create tactical communication bubbles. Smartphones and laptops can stay in airplane mode, without SIM cards and without 2G/3G/4G/5G attachment. They still exchange messages and make calls in real time through a local micro-node, for example a Raspberry Pi 5 in Wi-Fi access point mode. This approach proves particularly useful on sensitive theatres of operations, in crisis rooms or in air-gapped environments where you deliberately cut any dependency on public cloud and telecom operators.
Incident response — Limiting the blast radius of a compromise
If an attacker compromises a terminal or a user account, CryptPeer’s design actively limits the damage. First, the segmented-key digital HSM and per-message ephemeral keys prevent a single compromise from unlocking an entire archive of conversations. Each message has its own derived key, so an attacker does not gain automatic access to the full history.
Second, CryptPeer organises users into categories and bubbles that strictly follow “need-to-know” principles. A compromised identity never sees the whole organisation, only its assigned perimeter: specific units, missions, services or theatres. As a result, the blast radius stays limited both cryptographically and organisationally. This model matches the threat scenarios of defence, intelligence and critical infrastructure operators, where you expect incidents to occur and you design the system to contain them by default.
Clarification — Secure transport alone does not guarantee true E2EE
No, WebRTC is not the same as full end-to-end encryption. WebRTC secures transport: it encrypts media and data flows on the wire using DTLS, SRTP and SCTP. This design protects against many network-level attacks, such as passive eavesdropping or simple man-in-the-middle attempts on intermediate routers.
However, true end-to-end encryption depends on how the application generates, stores and exchanges cryptographic keys. If a server creates or retains the keys, the system does not offer genuine E2EE, even if it uses WebRTC. CryptPeer therefore uses WebRTC as a secure transport foundation and adds a segmented-key digital HSM with per-message ephemeral keys. Servers never receive master keys in cleartext and cannot reconstruct them. In this way, CryptPeer turns secure WebRTC transport into a fully sovereign, end-to-end encrypted messaging and collaboration layer.
Privacy concern — Understanding what the other side can really see
In a direct P2P WebRTC session, each peer usually sees the network addresses that the connection uses, which can include public or private IPs depending on the topology. This behaviour is normal for any real-time IP communication: the two endpoints must know how to reach each other at the network level.
CryptPeer mitigates this in several practical ways. First, you can run CryptPeer entirely inside a local, air-gapped Wi-Fi bubble where peers only see local IP addresses that have no meaning on the public Internet. Second, all messages and calls use P2P WebRTC secure messaging with strong end-to-end encryption and no cleartext metadata retention on servers. Consequently, even when peers see IP information, they still never gain access to readable content, cryptographic keys or organisation-wide directories. For many institutional scenarios, this balance offers both operational efficiency and robust privacy.
Comparison — Beyond mainstream end-to-end encrypted messengers
CryptPeer differs from classic secure messaging apps on several strategic points. First, it runs 100% in the browser with zero installation, which means you can use it on locked-down workstations, shared terminals and crisis rooms where native apps are forbidden. You simply open a browser and join the P2P WebRTC secure messaging bubble.
Second, CryptPeer anchors security in a segmented-key digital HSM and per-message ephemeral keys instead of relying on the phone or PC operating system to protect secrets. Third, it works as a sovereign, self-contained communication bubble without Internet or public cloud, using only local or national infrastructure under organisational control. Finally, it structures identities through categories and bubbles aligned with “need-to-know” doctrines, not global user directories. In short, CryptPeer targets regalian services, defence ecosystems and operators of critical infrastructures rather than mass-market chat.
Governance vs surveillance — Admins manage the system, not the content
No. Administrators in CryptPeer do not read or decrypt user conversations. They manage infrastructure, categories, bubbles, server updates and resource monitoring, but they never receive end-to-end encryption keys. The relay server only forwards ciphertext and does not store cleartext messages or usable secrets.
At the same time, governance stays strong. Admins can enforce access policies, configure bubbles for different missions or theatres, and apply retention rules for technical data without turning CryptPeer into a mass-surveillance tool. This separation between administrative power and decryption capability aligns with “need-to-know” doctrines and with the expectations of defence, intelligence and critical infrastructure organisations that require robust governance without compromising confidentiality.
Legal angle — Compliance without introducing encryption backdoors
CryptPeer addresses lawful access and regulatory constraints through architecture and governance, not through cryptographic backdoors. The platform does not store cleartext messages or master keys on the server side, so it cannot retroactively decrypt an entire history of communications on demand. Instead, each organisation remains responsible for its own legal processes at the endpoint and for the way it manages devices and identities.
At the infrastructure level, CryptPeer can still provide audit information about resources, availability, connection events and server health — all under the organisation’s control. This approach supports compliance with internal policies and sectoral regulations while preserving the integrity of P2P WebRTC secure messaging and end-to-end encryption. In other words, CryptPeer separates lawful governance from encryption weakening, which is essential for high-assurance and regalian use cases.
Quantum angle — How P2P WebRTC secure messaging prepares for post-quantum threats
CryptPeer takes quantum threats into account at the architectural level. Today, it relies on well-established symmetric cryptography such as AES-256-GCM, which remains considered robust even in a post-quantum context when you use it with a 256-bit key. A large-scale quantum computer could accelerate brute-force attacks with Grover’s algorithm, but AES-256 still offers an enormous security margin for long-term, end-to-end encrypted communication.
On top of that, CryptPeer does not stop at a single 256-bit key. The platform uses a segmented-key digital HSM: it generates several independent 256-bit segments and derives a master key only in volatile memory (RAM). From this master key, CryptPeer then derives per-message ephemeral keys for P2P WebRTC secure messaging. An attacker would therefore need to recover every segment, reconstruct the concatenation method and still brute-force extremely large key spaces — a scenario that goes far beyond classical attack models.
At the same time, CryptPeer deliberately uses standard, publicly reviewed algorithms rather than proprietary ciphers. This choice makes future transitions to post-quantum public-key schemes (for example for key exchange or signatures when WebRTC and DTLS evolve) much easier. In practice, the combination of AES-256-GCM, segmented-key HSM and per-message ephemeral keys already offers a very high level of resilience today, while keeping a clear migration path towards upcoming post-quantum standards.
What We Didn’t Cover
- Hybrid distributed architectures — how they coexist with WebRTC in mixed systems (edge computing, mesh networking).
- Advanced local compromise-detection models — essential to strengthen operational sovereignty on the user side.
- Latency-mitigation strategies in extreme environments — in particular on asymmetric or unstable mobile networks.
- Geopolitical impacts of decentralised communications — especially in relation to extraterritorial regulations.
- Dynamic pseudonymisation mechanisms — useful to decouple identity and channel in direct communication.
These topics build on the foundations laid here. They shed light on dimensions that directly influence the resilience, confidentiality and portability of sovereign P2P WebRTC architectures. They will be covered in other technical chronicles in the Freemindtronic Cyberculture series.
Sovereign use cases — Freemindtronic
The P2P WebRTC model deployed by CryptPeer is part of a broader ecosystem of sovereign devices designed by Freemindtronic. Each technology follows a common principle: local proof of trust.
Regalian & critical infrastructure focus — Beyond classic secure messengers
- Zero-install, 100% browser-based: compatible with locked-down workstations, hardened terminals and crisis centres where deploying apps is not acceptable.
- Local, self-contained bubbles: operation over private Wi-Fi or wired networks without SIM cards or Internet access, from a Raspberry Pi 5 micro-node to ministerial datacentres.
- Segmented-key digital HSM: per-message ephemeral keys and hardware-inspired key management, designed for high-assurance and defence-grade threat models.
- Identity without phone numbers or e-mail: cryptographic identities, categories and bubbles aligned with “need-to-know” doctrines instead of global user directories.
- No backdoors, no exploitable server-side data: servers never hold cleartext content or usable keys, and optional relay nodes only forward ciphertext under organisational control.
This principle guarantees that the user remains the exclusive holder of their keys, their secrets and their exposure surface.
DataShielder HSM PGP — Local protection and hardware encryption
- Offline key storage, inaccessible to remote servers.
- PGP encryption performed entirely inside the physical HSM.
- No digital footprint left outside the user’s perimeter.
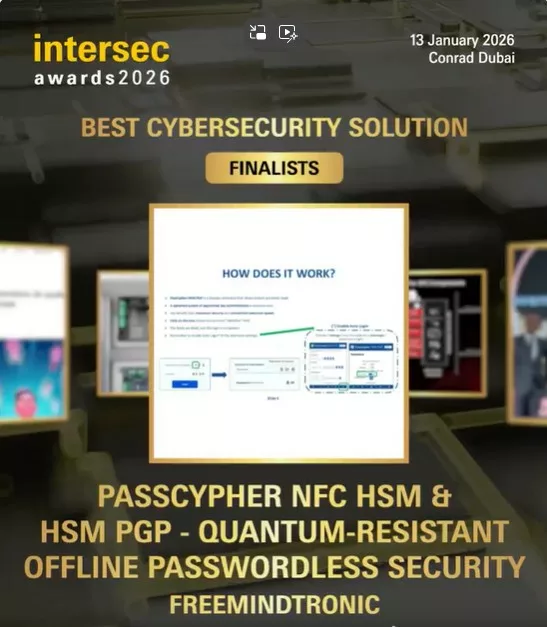
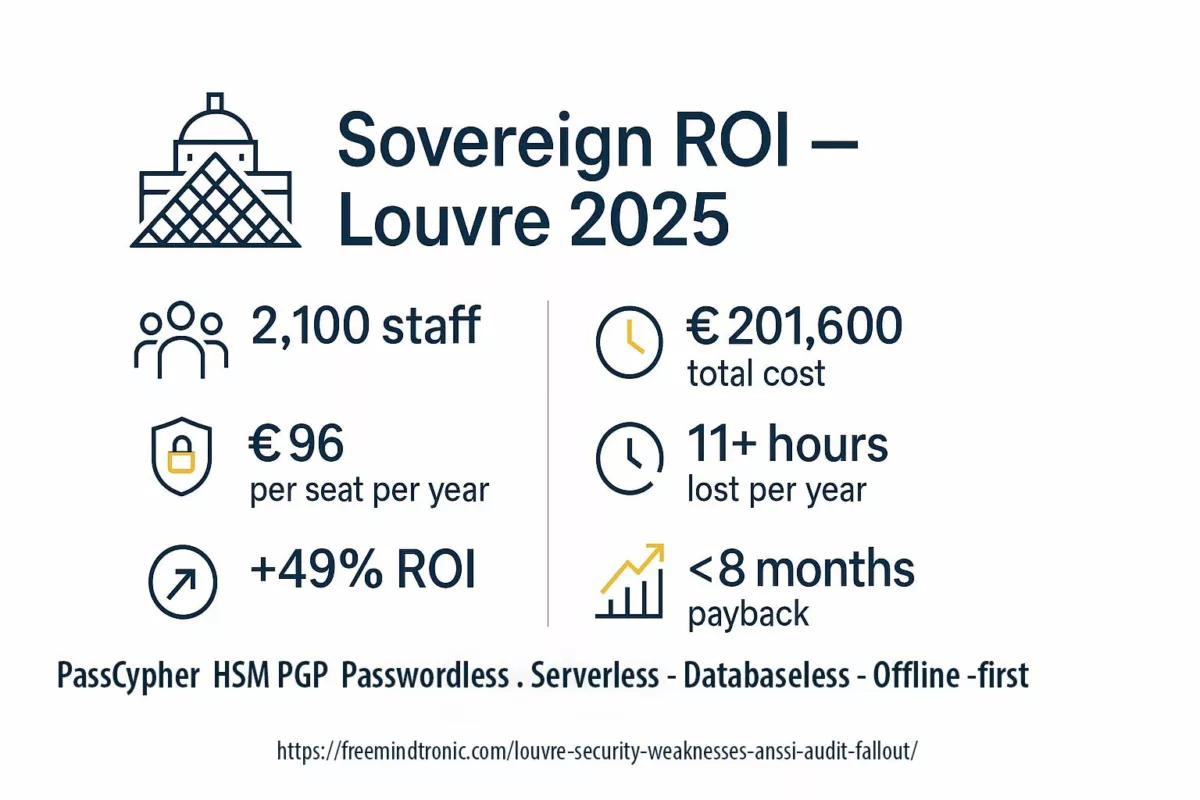
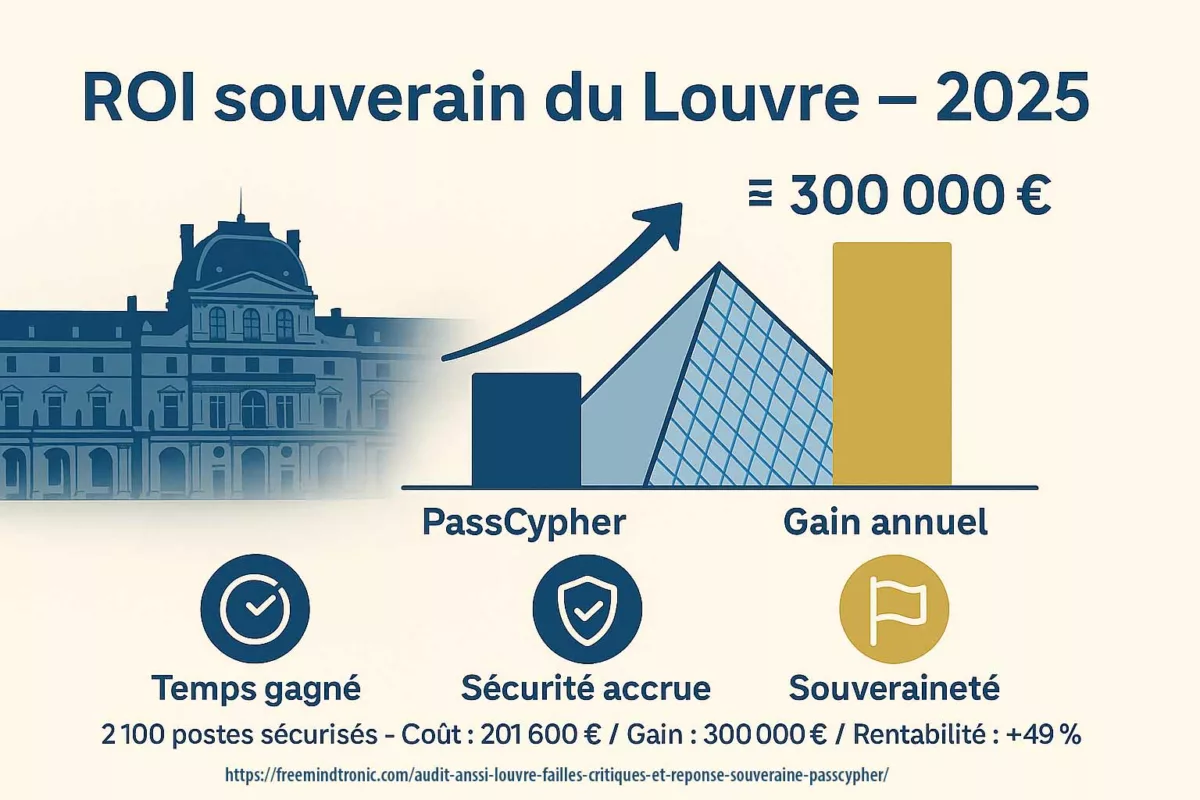
PassCypher NFC HSM — Sovereign identities and secrets
- Local management of identities, keys, secrets and OTPs.
- Cryptographic derivation with no cloud and no third-party infrastructure.
- Full operational autonomy, even offline.
CryptPeer — Direct P2P WebRTC communication
- Direct audio/video streams between peers, with no third-party relay; only an optional self-hosted local relay when direct paths are impossible.
- DTLS–SRTP encryption negotiated locally.
- Sovereign WebRTC DataChannel for messages and file transfer.
- In the version distributed by FullSecure, CryptPeer relies on Freemindtronic’s EviLink HSM PGP technology to provide the segmented-key digital HSM layer that governs keys and secrets.
- No readable metadata retained after the session ends; any technical traces remain encrypted and under user control.
By combining these devices, Freemindtronic builds a doctrine that unifies cryptographic, identity and communication sovereignty: own your keys, own your data, own your channel — the core promise of a P2P WebRTC secure messaging ecosystem.