2023, 2026, Digital Security, Phishing
BITB Attacks: How to Avoid Phishing by iFrame
Browser-in-the-Browser (BITB) attacks: interface forgery through redirection iframes and the structural limits of browser trust. First published on May 10, 2023 and updated on February 27, 2026, this Chronicle documents an architectural shift in phishing methodology: credential compromise without breaking encryption, by relocating the attack surface from transport security to interface authority.
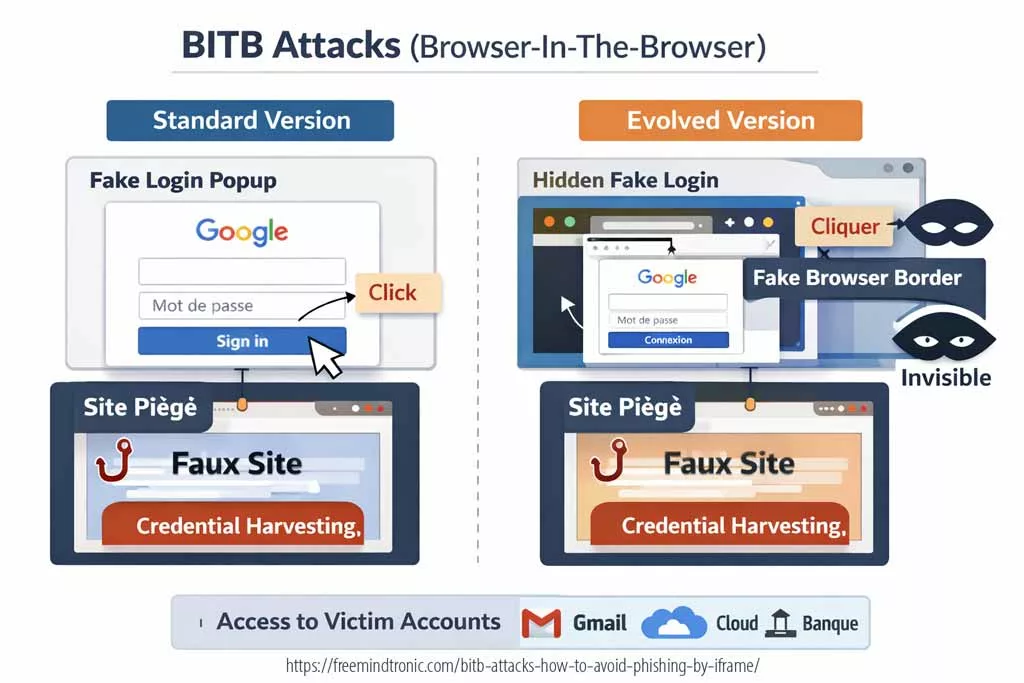
Originally demonstrated as visibly forged popup authentication windows rendered inside the browser viewport, BITB techniques have evolved toward more discreet DOM-integrated authentication simulations. The visual form may differ. The structural mechanism does not. In both cases, authentication is rendered inside a page-controlled context through redirection iframes and DOM authority abuse.
This Chronicle does not treat BITB as “advanced phishing.” It treats it as a browser authority boundary problem.
Browser-in-the-Browser (BITB) attacks do not break TLS. They exploit interface authority by rendering forged authentication flows inside page-controlled DOM contexts through redirection iframes. Visible popups and stealth layout-integrated variants share the same structural vector. Mitigation requires origin validation and reduction of DOM authority — not visual detection alone.
Executive summary
Context
Single Sign-On (SSO) adoption normalized the presence of third-party authentication windows inside web sessions. Users were trained to interpret visual familiarity as authenticity. However, modern web standards allow any page to render an interface visually indistinguishable from an external authority. Encryption protects payload confidentiality. It does not authenticate the legitimacy of what the user sees.
Purpose
This Chronicle provides a structural and doctrinal analysis of Browser-in-the-Browser attacks across both visible and stealth variants. It clarifies the boundary exploited, distinguishes perception from authority, and frames mitigation at the architectural level.
Scope
- Visible popup-based BITB demonstrations (2022–2023)
- Stealth DOM-integrated authentication forgeries (2024–2026 evolution)
- Redirection iframe exploitation
- Password manager autofill implications
- Credential harvesting without TLS compromise
Out of scope: cryptographic TLS break, browser zero-day exploitation, vendor-specific code weaponization.
Design doctrine
Authentication integrity is not a transport property. It is a boundary property. When authentication UI is rendered inside a page-controlled DOM, authority collapses into that page. Visual cues become unverifiable.
Strategic differentiator
BITB is frequently categorized as phishing sophistication. This Chronicle frames it differently: a browser authority misplacement. Whether the interface is visibly simulated or seamlessly integrated into layout, the dependency remains identical — DOM authority combined with redirection control.
Key takeaway
HTTPS secures transport. It does not secure interface authority. Whether authentication appears as a visible popup or an integrated form, if it is rendered inside a page-controlled DOM through redirection iframe logic, its legitimacy cannot be cryptographically guaranteed. Mitigation must therefore address structural authority — not visual perception.
Technical note
Express: ≈ 3–4 minutes
Advanced: ≈ 5–6 minutes
Chronicle: ≈ 30–40 minutes
First publication: May 10, 2023
Major update: February 27, 2026
Level: Web Security / Authentication Integrity / UI Authority
Posture: Architectural boundary analysis
Category: Digital Security
Available languages: EN · FR · CAT · ES
Impact level: 8.9 / 10 — credential integrity compromise vector
Key insights
- Encryption does not authenticate interface authority.
- BITB evolved perceptually, not structurally.
- Redirection iframes remain the invariant attack vector.
- Password managers can amplify risk if origin validation is weak.
- Sovereign authentication boundaries neutralize DOM authority exposure.
- Executive summary
- Advanced summary
- Chronicle core
- Evolution 2023–2026
- Structural mechanism
- Visible vs stealth BITB
- Stealth BITB vs AiTM phishing
- BITB vs Reverse Proxy phishing
- Recent examples
- Visual demonstrations
- Statistics
- How to fight BITB
- EviBITB — Prevent & Protect
- How EviBITB protects
- Browsing experience impact
- How to use EviBITB
- Stop point
- Signals watch
- Sovereign use case
- Beyond DOM authority — PassCypher architecture
- How to get started
- Glossary
- FAQ
- What we didn’t cover
- Strategic outlook
Advanced summary
The initial public demonstrations of BITB rendered a visually convincing browser window inside the viewport, complete with simulated address bar and lock indicators.
Subsequent evolutions reduced overt visual signals. Authentication fields may now be blended into page layout, activated conditionally, or presented without clear modal boundaries.
However, both variants share identical structural dependencies:
- Page-controlled DOM authority
- Redirection iframe or embedded origin simulation
- User trust transferred from visual familiarity
The evolution is perceptual. The authority boundary remains unchanged.
Chronicle core — browser authority displacement
Evolution 2023–2026
The 2022–2023 BITB demonstrations showed clearly visible simulated authentication popups.
By 2024–2026, phishing infrastructures increasingly integrated authentication forgery into layout itself, reducing perceptual anomalies. The absence of a visible modal does not remove the underlying mechanism. It merely reduces detection probability by human observation.
The attack surface remains:
- Redirection iframe injection
- DOM-controlled rendering
- Credential submission inside page authority
External confirmation — embedded authentication risk
Modern security guidance from major platform vendors confirms the structural risk of embedded or page-controlled authentication flows.
- Google Identity Security Guidance explicitly warns against performing OAuth flows inside embedded webviews or page-controlled contexts, emphasizing origin validation and external authority enforcement.
- OWASP Clickjacking documentation describes UI redress attacks where invisible or overlaid frames manipulate user interaction without breaking transport security.
- Microsoft Security research documents phishing campaigns that harvest credentials and OAuth tokens without TLS compromise, relying on interface deception and redirection control.
• Google Identity — OAuth security considerations: developers.google.com
• OWASP Clickjacking: owasp.org
Structural mechanism
BITB does not require transport compromise. It requires authority confusion.
The browser enforces TLS at the connection layer. It does not enforce authenticity of interface elements rendered inside a page context.
When authentication is performed inside a page-controlled environment, the page effectively becomes the authority — even if it visually simulates an external provider.
Risks and consequences
For users:
- SSO identity compromise cascading across services
- Credential replay and session hijacking
- Financial and reputational damage
For organizations:
- Trust boundary erosion
- Regulatory exposure
- Operational compromise
- Brand degradation
Threat model — who can exploit BITB and why it scales
BITB should be modeled as a trust-boundary displacement rather than a content interception attack. The attacker does not need to decrypt traffic. The attacker needs the victim to authenticate into a page-controlled interface that is rendered to appear like an external authority.
From an operational standpoint, the threat model includes:
- Commodity phishing operators using turnkey kits and template flows (SSO imitation, iFrame injection, credential forwarding).
- Targeted operators embedding BITB into realistic pretexts (invoice workflows, IT notices, crypto dashboards, SaaS access portals).
- Hybrid campaigns combining mail delivery + web payload + conditional rendering to bypass sandboxes and automated crawlers.
The scaling factor is not sophistication. It is repeatability: once an interface can be forged at the DOM layer, it can be replicated across brands, languages, and contexts.
Visible vs stealth BITB — same mechanism, different perceptual footprint
The BITB family can be separated into two operational presentations:
- Visible BITB: a forged “window” rendered inside the viewport, typically with a simulated URL bar and provider branding.
- Stealth BITB: authentication forgery blended into layout (no distinct modal boundary), reducing human-detectable anomalies.
| Variant | What the user perceives | What stays invariant | Primary detection failure |
|---|---|---|---|
| Visible BITB | Popup-like window within the page | DOM-controlled rendering + redirection iframe logic | User trusts familiar popup visuals |
| Stealth BITB | Login fields appear “normal” inside page flow | DOM-controlled rendering + redirection iframe logic | No obvious modal boundary to trigger suspicion |
Stealth BITB vs AiTM phishing — structural distinction
BITB and Adversary-in-the-Middle (AiTM) phishing are frequently conflated. They are not identical threat classes. The distinction is structural.
- BITB (visible or stealth) forges authentication inside a page-controlled DOM context.
- AiTM phishing intercepts authentication through a reverse proxy positioned between victim and legitimate provider.
| Dimension | Stealth BITB | AiTM phishing |
|---|---|---|
| Primary vector | DOM authority + redirection iframe | Reverse proxy relay |
| TLS break required | No | No |
| Credential exposure | Submitted directly to attacker page | Relayed through attacker-controlled proxy |
| Session token theft | Possible if captured during flow | Primary objective (cookie/session capture) |
| User perception | Forged interface inside page | Real interface proxied transparently |
Stealth BITB displaces authority at the interface layer.
AiTM displaces authority at the network relay layer.
Both exploit user trust.
They differ in architectural insertion point.
BITB vs Reverse Proxy phishing (Evilginx class)
Reverse proxy phishing frameworks such as Evilginx-class toolkits implement AiTM logic at scale. They proxy legitimate authentication providers and capture session cookies after successful login.
BITB differs fundamentally.
- BITB simulates the authentication provider inside attacker DOM.
- Reverse proxy phishing forwards authentication to the legitimate provider and captures resulting session artifacts.
Key structural difference:
- BITB: authority illusion.
- Reverse proxy phishing: authority relay.
In BITB, the victim authenticates into a forged context.
In reverse proxy phishing, the victim authenticates into a real context that is transparently proxied.
Both bypass visual inspection heuristics.
Mitigation differs:
- BITB mitigation → origin validation + DOM authority reduction.
- Reverse proxy mitigation → relocation of authentication secrets outside browser-controlled contexts and enforcement of hardware-backed origin validation workflows.
Understanding this distinction prevents conceptual conflation and improves defensive architecture selection.
Recent examples of BITB attacks
BITB attacks are not new, but they have become more systematic with SSO adoption. The following cases illustrate early public reporting patterns (2020) that remain structurally relevant today.
- February 2020 (Steam / CS:GO lure): a campaign used fake game-related sites and a forged login window asking users to authenticate with Steam. Credentials were captured and accounts abused for item theft.
- March 2020 (Office 365): emails led to a counterfeit Office 365 page that displayed a forged login window; credentials were harvested and used to access cloud resources.
- September 2020 (Okta): phishing messages lured victims to a fake Okta page that rendered a forged authentication prompt, enabling compromise of downstream connected applications.
These examples show two stable properties:
- BITB can target any SSO provider, because the victim trusts the UI pattern.
- The redirect-to-legitimate behavior is part of the deception pipeline.
Visual demonstrations — why visible BITB still matters
The following demonstrations show the classic BITB model where a forged login window is visibly rendered within the browser viewport. This remains widely deployed because it leverages strong user trust reflexes and predictable SSO workflows.
Demonstration — identifying BITB reflexes (Mailinblack)
Stop Browser Fingerprinting & BITB Attack Protection — Freemindtronic — published February 4, 2025.
What are some statistics on BITB attacks?
BITB is a specific phishing technique, but its prevalence can be inferred through broader phishing metrics and SSO-targeting trends. The following reference points reflect the historical period emphasized in the original Chronicle baseline:
- Phishing volumes increased sharply in 2020, with millions of detected phishing sites reported across quarters.
- SSO-centric phishing increased because “Sign in with Google/Microsoft/Apple” normalizes third-party authentication prompts.
- Early public BITB reporting demonstrated the technique in the wild well before it became widely discussed.
Operationally, the more relevant “statistic” is structural:
- As SSO penetration increases, the number of contexts where users expect popups increases.
- As that expectation increases, UI forgery becomes more reliable than domain spoofing alone.
How to effectively fight against BITB attacks?
BITB is difficult to detect because it attacks perception and routine. However, it is not undefeatable. Defensive posture must be built around authority verification rather than visual comfort.
- Do not trust UI URL strings displayed inside a forged window. Treat them as untrusted page content.
- Prefer manual navigation to known provider domains (typed URL or bookmarks) before authenticating.
- Harden the browser: reduce untrusted extensions, restrict script execution where possible, and prefer isolation profiles for high-value accounts.
- Constrain password manager behavior: require user confirmation, disable autofill on risky contexts, bind credentials to verified origins.
- Use MFA with correct expectations: MFA reduces replay value but does not stop credential harvesting if the victim submits secrets into a forged interface.
| Defense lever | What it mitigates | What it does not solve |
|---|---|---|
| Manual origin navigation | Reduces exposure to forged prompts | Does not help if the user is already inside a malicious session |
| Password-manager constraints | Prevents silent autofill into attacker forms | Does not stop manual credential typing |
| MFA (properly configured) | Reduces direct replay value of passwords | Does not prevent credential capture or token relay in some workflows |
| Isolation profiles | Limits cross-context contamination | Does not prove interface authenticity |
How to prevent and protect yourself from BITB attacks using EviBITB technology?
EviBITB is designed to mitigate the redirection iframe vector commonly exploited in BITB-style interface forgeries. The objective is structural: reduce DOM authority over authentication by removing redirection surfaces and enforcing origin compliance before any credential transfer.
Reference technology page:
EviBITB — embedded technology to stop BITB phishing attacks.
EviBITB is integrated within Freemindtronic extensions compatible with NFC HSM-based workflows. In this model, encrypted authentication materials (identifiers, passwords, OTP seeds) are stored in a hardware-backed boundary, and released only after origin validation.
Benefits include:
- Reduced exposure to forged authentication interfaces that rely on redirection iframes.
- Reduced keylogging value because fewer secrets are typed into untrusted contexts.
- Operational consistency across web contexts through validated origin workflows.
- Privacy reinforcement by limiting third-party iframe-driven tracking surfaces.
How can EviBITB protect you from BITB attacks?
EviBITB enhances security by implementing a verification workflow prior to autofill or auto-login actions. The principle is straightforward: no origin integrity, no credential release.
Operationally, EviBITB can:
- Analyze page structures to identify redirection iframe patterns commonly used in credential harvesting flows.
- Surface warnings when a redirection origin is not compliant with expected authority.
- Prevent credential transfer into contexts that fail origin validation.
This posture remains relevant even as BITB becomes less visually obvious, because the objective is to break the structural dependency of the attack.
How EviBITB technology can improve your browsing experience?
EviBITB is not only a security control. By neutralizing redirection iframes, it may also improve performance and privacy characteristics:
- Faster load paths by removing third-party iframe requests.
- Reduced bandwidth consumed by embedded cross-origin content.
- Lower exposure to ad and popup delivery via iframe sources.
- Reduced cross-site tracking via iframe cookie surfaces.
- Improved page readability and reduced layout distraction.
How to use EviBITB to protect yourself from BITB attacks?
When EviBITB detects a suspicious redirection iframe, it presents an operational decision surface. The objective is to avoid automatic trust transfer.
Typical actions include:
- Close Warning: closes the warning window without acting on the iframe.
- Never Show Warnings On This Site: adds the site to a trusted list (use only if authority is confirmed).
- Destroy: removes the suspected iframe from the page source context.
- Clean Storage: clears storage artifacts associated with the iframe context.
- Read More: redirects to the EviBITB documentation context.
When not to act — the non-negotiable boundary
There are situations where “mitigation” becomes security theater. In those cases, the correct response is to change posture rather than proceed.
- If a login prompt appears inside a page and authority cannot be independently verified, do not authenticate.
- If a browser environment is contaminated (unknown extensions, persistent redirects, policy changes), treat it as compromised until proven otherwise.
- If a high-value workflow depends on UI trust alone, replace it with a sovereign boundary approach (hardware-backed secrets + verified origins).
If interface authenticity cannot be asserted, the correct response is not “be careful.” It is “change the boundary.”
Signals watch — indicators that BITB exposure is increasing
Weak signals
- More workflows shifting from passwords to SSO-only authentication.
- More “embedded login experiences” inside SaaS and web apps.
- Increased reliance on browser extensions for security decisions.
Medium signals
- More phishing kits blending UI into page layout (reduced modal cues).
- Higher frequency of conditional rendering (anti-bot gating, geo-fencing, timing triggers).
- More credential capture that ends with legitimate redirection.
Strong signals
- Credential compromise events where victims insist they “checked the URL” and it looked correct.
- Incidents where password managers autofilled into the wrong context.
- SSO account takeover cascading into multiple connected services.
Freemindtronic sovereign use case — reducing browser authority
Freemindtronic’s R&D posture treats credential integrity as a boundary property. The objective is to limit what the browser can decide and to relocate secrets to a hardened boundary.
Use-case principles (technology-agnostic):
- Keep authentication materials outside page-controlled contexts.
- Release secrets only after origin validation (sandboxed compliance).
- Prefer hardware-backed storage and controlled disclosure workflows.
Within the Freemindtronic ecosystem, EviBITB contributes by reducing the iframe redirection surface frequently exploited by BITB campaigns, while PassCypher-class workflows support a credentialless or reduced-typing posture.
Beyond DOM authority — PassCypher HSM PGP architectural boundary
PassCypher HSM PGP does not rely on browser-rendered interface trust, embedded web flows, or UI integrity heuristics.
Its security model is based on:
- Hardware-backed storage of authentication materials
- Cryptographic validation of origin before disclosure
- No automatic secret release inside page-controlled DOM contexts
- NFC HSM–mediated authorization outside browser authority
This distinction is critical.
BITB exploits DOM authority.
Reverse proxy phishing exploits session relay.
PassCypher relocates the trust boundary outside both.
Authentication secrets are not resident in the browser DOM, not dependent on embedded flows, and not transferable without hardware validation.
How to get started with EviBITB?
Deploying EviBITB follows a structured workflow aligned with origin validation and hardware-backed authentication principles.
- Download the browser extension corresponding to your environment.
- Install and configure origin validation parameters.
- Pair with an NFC-compatible Android device and/or NFC HSM if using hardware-backed authentication.
- Validate first-login origin capture to establish compliance baseline.
Official distribution channels:
- Chromium-based browsers: Chrome Web Store
- Microsoft Edge: Edge Add-ons
- Firefox (direct XPI package): Firefox extension package
Technology reference: EviBITB — embedded technology overview
Glossary — BITB and interface authority
Browser-in-the-Browser (BITB)
Definition
Redirection iFrame
Definition
Interface authority
Concept
FAQ — Browser-in-the-Browser attacks
Is BITB a TLS vulnerability?
Answer
Does checking the URL always prevent BITB?
Answer
Does MFA eliminate BITB risk?
Answer
Is BITB limited to popups?
Answer
Why can password managers increase exposure?
Answer
What We Didn’t Cover
- Zero-day browser rendering vulnerabilities
- Token relay attacks and advanced session hijacking patterns
- Mobile-specific BITB adaptations
- Reverse proxy phishing frameworks
- Vendor-specific implementation internals
Strategic Outlook — redefining authentication boundaries
BITB illustrates a structural inflection point in web security.
Historically, encryption equaled confidentiality. Modern web architectures show that confidentiality must now include interface integrity.
Modern web architectures show that confidentiality must now include interface integrity.
As authentication becomes increasingly embedded, modular, and visually normalized, the boundary between authority and presentation becomes fragile.
The strategic response is not incremental user training. It is architectural repositioning:
- Reduce DOM authority over credential workflows.
- Bind secrets to verified origins.
- Relocate authentication trust to sovereign hardware-backed boundaries.
When interface authenticity cannot be asserted independently of page rendering, security posture must evolve accordingly.