Phishing Cyber Victims by Jacques Gascuel This article will be updated with any new information on the topic, and readers are encouraged to leave comments or contact the author with any suggestions or additions.
Phishing: how cyber-victims are caught between scam and blackmail
Have you ever received an email or a message that looked like an official communication from a trusted organization, such as your bank, your phone operator or your social network? Did it ask you to confirm your personal or financial information, to pay a fine or to update your software? If so, you may have been targeted by a phishing attack.
2025 2026 Digital Security
May 26, 2026
2026 Cyber Doctrine Digital Security
February 24, 2026
2026 Digital Security
February 21, 2026
2026 Digital Security
February 18, 2026
2026 Digital Security
January 23, 2026
2026 Digital Security
January 17, 2026
2026 Digital Security
January 8, 2026
2026 Digital Security
January 7, 2026
Discover our other articles on digital security
Phishing is a fraudulent technique that aims to deceive internet users and to steal their information, money or identity. Phishing is a major threat for the security of individuals and organizations, as it can lead to financial losses, identity theft, extortion or malware infections. In this article, I will explain to you what phishing is, how to protect yourself from it, what to do if you fall victim to it and what are the current trends of this phenomenon.
What is phishing?
Phishing is a form of social engineering that exploits the human factor rather than the technical factor. In other words, phishing relies on manipulating people’s emotions, such as fear, curiosity or greed, rather than hacking their devices or systems.
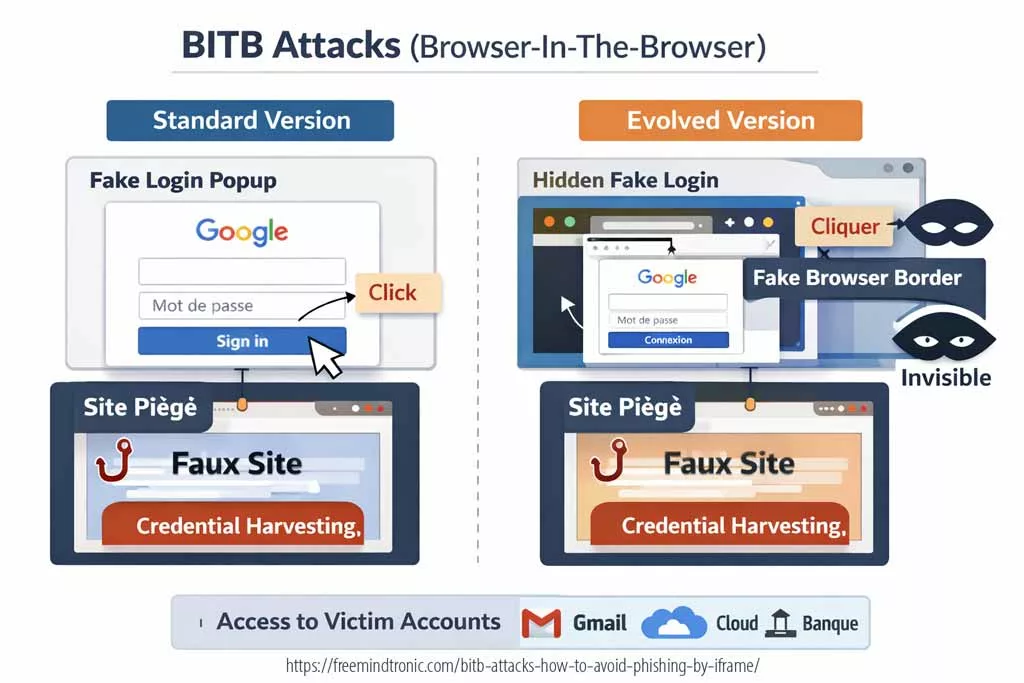
Phishing usually involves sending emails or messages that mimic the appearance and content of official communications from legitimate organizations. These messages often contain a link or an attachment that directs the recipients to a fake website or a malicious file. The goal of phishing is to trick the recipients into revealing their personal, financial or confidential information, such as their passwords, their bank account numbers or their credit card details. Alternatively, phishing can also persuade the recipients to make fraudulent payments or to download malware on their devices.
Phishing can target anyone who uses the internet, whether they are individuals or organizations. However, some groups are more vulnerable than others, such as seniors, students or employees. According to a report by Verizon (https://enterprise.verizon.com/resources/reports/dbir/), phishing was involved in 36% of data breaches in 2020.
How to protect yourself from phishing?
To protect yourself from phishing, you need to be able to recognize the signs that can indicate that a message is fraudulent. Here are some examples of signs to watch out for:
- Spelling or grammar mistakes in the message.
- Suspicious addresses or links that do not match the supposed organization behind the message.
- Urgent or unusual requests, such as confirming your bank details, paying a fine or updating your software.
- Attachments or links that invite you to download or open a file.
If you receive a suspicious message, do not click on the links, do not open the attachments and do not reply to the message. Instead, check the source of the message by looking at the sender’s address, hovering over the links with your mouse to see their real destination or contacting directly the organization supposed to be behind the message by another means (phone, official website, etc.).
You can also use some tools and practices to enhance your security online, such as:
- Installing an antivirus software and keeping it updated.
- Using strong and unique passwords for each site and service you use.
- Enabling two-factor authentication whenever possible.
- Avoiding public Wi-Fi networks or using a VPN (Virtual Private Network) when accessing sensitive sites.
- Educating yourself and others about cyber threats and how to prevent them.
What to do if you are a victim of phishing?
If you have clicked on a link, opened an attachment or disclosed personal or financial information following a fraudulent message, you may be a victim of phishing. In this case, it is important to act quickly to limit the consequences. Here are some tips to follow:
- Change your passwords on all sites and services you use, especially those related to your bank accounts, your social networks or your email accounts.
- Contact your bank or your phone operator to report the incident and block your cards or lines if necessary.
- File a complaint with the competent authorities, such as the police, the FTC (Federal Trade Commission) or the IC3 (Internet Crime Complaint Center).
- Report the fraudulent message to the concerned organizations, such as https://www.antiphishing.org/ or https://www.us-cert.gov/report-phishing. These sites also offer you information and services to help you cope with the consequences of phishing.
What is the new bill on justice and why is it raising concerns about privacy?
The bill on justice is a legislative project. It aims to modernize and simplify justice in France. It covers civil, criminal, administrative and digital justice. It also strengthens the investigation and prosecution of serious offenses, such as terrorism and organized crime.
One measure authorizes remote activation of phones by the police for some investigations. Article 3 “An unfailing commitment to better prevent radicalization and fight against terrorism” of the bill includes this measure. It modifies article 706-102-1 of the code of criminal procedure. This article defines how to activate remotely any electronic device that can emit, transmit, receive or store data.
This measure raises privacy concerns because it lets the police access personal or professional data in phones without the owners’ or possessors’ consent or knowledge. It also lets the police locate, record or capture sounds and images from phones without notification or justification. This measure may violate fundamental rights and freedoms, such as privacy, confidentiality, dignity, presumption of innocence and right to a fair trial.
What is remote activation of phones and how does it work?
Remote activation of phones by the police is an intelligence technique that allows law enforcement agencies to access data or record sounds and images from phones without the consent or knowledge of the phone users. This technique can be used for criminal investigations or national security purposes.
To remotely activate phones, law enforcement agencies need three factors: compatibility, connectivity, and security of the phones. They need to be compatible with the software or hardware that enables remote activation. They need to be connected to a network or a device that allows remote access. They need to have security flaws or vulnerabilities that can be exploited or bypassed.
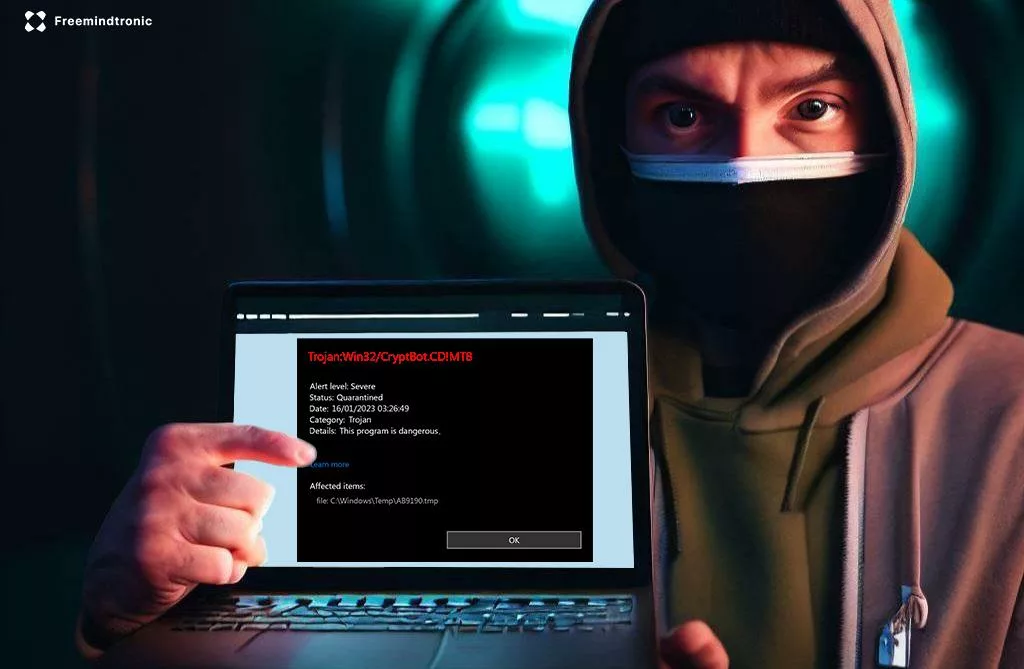
Law enforcement agencies can remotely activate phones by three methods: exploiting vulnerabilities, installing malware, or using spyware on phones. Exploiting vulnerabilities means taking advantage of security flaws or weaknesses in the phone’s operating system, applications, or protocols. Installing malware means putting malicious software on the phone that can perform unauthorized actions or functions. Using spyware means employing software or hardware that can monitor or control the phone’s activity or data.
By remotely activating phones, law enforcement agencies can access data such as contacts, messages, photos, videos, location, browsing history, or passwords. They can also record sounds and images such as conversations, ambient noises, or camera shots. They can do this in real time or later by retrieving the data from the phone’s memory or storage.
What is the French bill on remote activation of phones by the police and what are its implications?
The French bill on remote activation of phones by the police is a legislative text that was promulgated on 25 May 2021. It is part of the justice orientation and programming bill for 2023-2027, which aims to modernize the justice system and reinforce its efficiency and independence.
The bill introduces a new article in the code of criminal procedure, which allows the judge of liberties and detention (at the request of the prosecutor) or the examining magistrate to order the remote activation of an electronic device without the knowledge or consent of its owner or possessor for the sole purpose of locating it in real time. This measure can be applied for crimes or misdemeanors punishable by at least five years’ imprisonment, a fairly broad criterion.
The bill also allows the judge of liberties and detention (at the request of the prosecutor) or the examining magistrate to order the remote activation of an electronic device without the knowledge or consent of its owner or possessor for the purpose of recording sounds and images from it. This measure can be applied only for crimes relating to organized crime and terrorism.
These measures cannot concern parliamentarians, journalists, lawyers, magistrates and doctors, nor the defendants when they are in the judge’s office or with their lawyer.
The bill also specifies that the remote activation of an electronic device must be done in a way that does not alter its functioning or data, and that the data collected must be destroyed within six months after their use.
The bill aims to provide law enforcement agencies with more tools and information to prevent, investigate and prosecute crimes, especially in cases where phones are encrypted, hidden or destroyed. It also aims to harmonize the French legislation with other countries that have used or considered this technique, such as the United States, Germany, Italy, Israel, Canada, China, France, and the United Kingdom.
However, the bill also raises ethical and social challenges, as it involves a trade-off between security and privacy, as well as between effectiveness and legitimacy. It may undermine the right to respect for private life and the right to a fair trial, which are guaranteed by the European Convention on Human Rights and the French Constitution. It may also expose law enforcement agencies to legal or technical challenges or dangers, such as encryption technologies that can prevent or hinder remote activation. It may also create distrust or resistance among phone users or providers, who may use encryption technologies or legal remedies to protect their data or communications.
The bill has been criticized by several actors, such as lawyers, human rights defenders, digital rights activists, journalists and academics. They have denounced its lack of proportionality, necessity and oversight. They have also questioned its effectiveness and legitimacy. They have called for its withdrawal or amendment.
The bill is still subject to constitutional review by the Constitutional Council before its final promulgation.
How did the Senate vote on the bill and where to find the official sources?
The Senate adopted this measure on October 20, 2021, with some amendments. The Senate voted in favor of this measure by 214 votes against 121. The Senate also added some safeguards to this measure, such as limiting its duration to four months renewable once and requiring prior authorization from an independent judge.
The National Assembly still has to examine the bill before adopting it definitively. The National Assembly may approve, reject or modify this measure. The final text may differ from the one that the Senate voted.
The examination of the bill by the National Assembly will start on December 6, 2021. You can follow the progress of the bill on the website of the National Assembly. You can also find the official text of the bill and the report of the Senate on their respective websites. You can also consult the website of the Ministry of Justice for more information on the bill and its objectives.
What are the benefits and risks of remote activation of phones?
This technique can affect citizens’ and suspects’ behavior in different ways.
On one hand, it can deter people from serious offenses. It exposes them to a higher risk of detection and identification. It reduces their incentives for criminal activities.
On the other hand, it can also make people more cautious or paranoid. It increases their uncertainty and fear. It leads them to avoid electronic devices, encrypt their communications, or use countermeasures such as jamming devices.
This technique can also impact public safety and security positively and negatively.
On one hand, it can improve the efficiency and effectiveness of law enforcement agencies. It provides them with more information and evidence. It helps them prevent, investigate and prosecute crimes.
On the other hand, it can also pose risks for human rights and civil liberties. It allows intrusive and covert surveillance. It violates privacy, confidentiality and dignity. It can also be subject to abuse, misuse or error by law enforcement agents or hackers.
Finally, it can create a feeling of insecurity and mistrust towards institutions, which can access personal or professional data in phones. It can also harm respect for presumption of innocence by placing permanent suspicion on people targeted by this technique. It can also infringe on protection of journalistic sources or right to information by discouraging whistleblowers or witnesses from speaking freely. It can finally encourage people concerned to adopt avoidance or circumvention strategies, such as changing phones regularly, using encrypted applications or switching to airplane mode.
These strategies can reduce the actual effectiveness of this technique for preventing terrorism and organized crime.
What are the arguments in favor of remote activation of phones?
Some people support this technique because they think it has several advantages for law enforcement and public security.
How can remote activation of phones violate privacy and data protection?
One of the main arguments against this technique is that it can violate privacy and data protection for individuals and groups. Privacy and data protection are fundamental rights recognized by international standards and laws. They ensure human dignity and autonomy.
Remote activation of phones violates privacy and data protection by letting law enforcement agencies access personal or professional data without the owners’ or possessors’ consent or knowledge. It also lets law enforcement agencies access sensitive or confidential data without notification or justification. It also lets law enforcement agencies access excessive or irrelevant data without limitation or proportionality.
For example, remote activation of phones could let the police access medical records, financial transactions, political opinions, religious beliefs, sexual preferences, or other intimate information on a device or a communication. It could also let the police access information that is not related to the investigation or that is out of scope on a device or a communication. It could also let the police access information that is not necessary or appropriate for the investigation or that is disproportionate to the seriousness of the offense on a device or a communication.
How can remote activation of phones improve access to justice and evidence?
Another argument in favor of this technique is that it can improve access to justice and evidence for law enforcement agencies and victims of crimes. Justice and evidence ensure the rule of law and the protection of rights.
Remote activation of phones improves access to justice and evidence by letting law enforcement agencies obtain information that is otherwise inaccessible or difficult to obtain. It also lets law enforcement agencies obtain information that is more reliable and accurate than other sources. It also lets law enforcement agencies obtain information that is timelier and more relevant than other sources.
For example, remote activation of phones could help the police access data that is encrypted or password-protected on a device or a communication. It could also help the police access data that is authentic and verifiable on a device or a communication. It could also help the police access data that is up-to-date and pertinent on a device or a communication.
What are the arguments against remote activation of phones?
Some people oppose this technique because they think it has several disadvantages for human rights and civil liberties.
How can remote activation of phones violate privacy and data protection?
One of the main arguments against this technique is that it can violate privacy and data protection for individuals and groups. Privacy and data protection are fundamental rights recognized by international standards and laws. They ensure human dignity and autonomy.
Remote activation of phones violates privacy and data protection by letting law enforcement agencies access personal or professional data without the owners’ or possessors’ consent or knowledge. It also lets law enforcement agencies access sensitive or confidential data without notification or justification. It also lets law enforcement agencies access excessive or irrelevant data without limitation or proportionality.
For example, remote activation of phones could let the police access medical records, financial transactions, political opinions, religious beliefs, sexual preferences, or other intimate information on a device or a communication. It could also let the police access information that is not related to the investigation or that is out of scope on a device or a communication. It could also let the police access information that is not necessary or appropriate for the investigation or that is disproportionate to the seriousness of the offense on a device or a communication.
How can remote activation of phones undermine the presumption of innocence and the right to a fair trial?
Another argument against this technique is that it can undermine the presumption of innocence and the right to a fair trial for individuals and groups. The presumption of innocence and the right to a fair trial are fundamental rights recognized by international standards and laws. They ensure justice and accountability.
Remote activation of phones undermines the presumption of innocence and the right to a fair trial by letting law enforcement agencies access data that they can use against individuals or groups without any legal basis or due process. It also lets law enforcement agencies access data that they can manipulate or falsify by law enforcement agents or hackers. It also lets law enforcement agencies access data that individuals or groups can challenge or contest.
For example, remote activation of phones could let the police access data that they can incriminate individuals or groups without any warrant or authorization from a judge. It could also let the police access data that they can alter or corrupt by law enforcement agents or hackers. It could also let the police access data that individuals or groups can dispute or refute.
How can remote activation of phones create a risk of abuse and misuse by the authorities?
Another argument against this technique is that it can create a risk of abuse and misuse by the authorities for individuals and groups. Abuse and misuse are illegal or unethical actions that violate rights and obligations. They damage trust and legitimacy.
Remote activation of phones creates a risk of abuse and misuse by the authorities by letting law enforcement agencies access data that they can use for purposes other than those authorized or intended. It also lets law enforcement agencies access data that they can share or disclose to third parties without any oversight or control. It also lets law enforcement agencies access data that they can retain or store for longer than necessary or permitted.
For example, remote activation of phones could let the police access data that they can use for political, personal, commercial, or other interests on a device or a communication. It could also let the police access data that they can transfer or leak to other agencies, organizations, media, or individuals on a device or a communication. It could also let the police access data that they can keep or archive for indefinite periods on a device or a communication.
What are the alternatives and safeguards for remote activation of phones?
Some people suggest that there are alternatives and safeguards for remote activation of phones that can balance security and privacy.
What are the existing legal tools to access phone data with judicial authorization?
One of the alternatives for remote activation of phones is to use existing legal tools to access phone data with judicial authorization. Judicial authorization is a legal requirement that ensures respect for rights and obligations. An independent and impartial judge grants it after evaluating the necessity and proportionality of the request.
Existing legal tools to access phone data with judicial authorization include search warrants, wiretaps, geolocation orders, data requisitions, and international cooperation agreements. These tools let law enforcement agencies obtain information from phones in a lawful and transparent manner. They also provide legal protection and recourse for individuals and groups.
For example, search warrants let law enforcement agencies physically seize phones and extract data from them with judicial authorization. Wiretaps let law enforcement agencies intercept calls and messages from phones with judicial authorization. Geolocation orders let law enforcement agencies track the location of phones with judicial authorization. Data requisitions let law enforcement agencies request data from phone operators or service providers with judicial authorization. International cooperation agreements let law enforcement agencies exchange data with foreign authorities with judicial authorization.
What are the principles and conditions for remote activation of phones according to the bill?
One of the safeguards for remote activation of phones is to follow the principles and conditions for remote activation of phones according to the bill. The bill on justice sets some rules and limits for this technique to prevent abuse and misuse.
The principles and conditions for remote activation of phones according to the bill include:
- The technique can only be used for terrorism and organized crime investigations.
- An independent judge who authorizes it must supervise the technique. The technique can only last for four months renewable once.
- The technique must respect necessity, proportionality, subsidiarity, and legality.
- Parliament and independent authorities must oversee and control the technique.
- Experts and stakeholders must evaluate and review the technique.
These principles and conditions aim to ensure a reasonable and accountable use of this technique. They also aim to protect the rights and interests of individuals and groups.
What are the possible ways to limit or challenge remote activation of phones?
Another safeguard for remote activation of phones is to use possible ways to limit or challenge remote activation of phones by individuals or groups. These ways can help protect rights and interests, as well as ensure accountability and transparency.
Some of the possible ways to limit or challenge remote activation of phones are:
-
Using encryption technologies:
Encryption technologies can make data on phones unreadable or inaccessible to law enforcement agencies, even if they remotely activate them. Encryption technologies can also protect communications from law enforcement agencies’ interception or recording. For example, using end-to-end encryption apps, such as Signal or WhatsApp, can prevent law enforcement agencies from accessing messages or calls on phones.
-
Using security features:
Security features can prevent law enforcement agencies from installing or activating software or applications on phones that enable remote activation. Security features can also detect or remove software or applications that enable remote activation. For example, using antivirus software, firewalls, passwords, biometrics, or VPNs can prevent law enforcement agencies from accessing phones.
-
Using legal remedies:
Legal remedies can let individuals or groups contest or oppose remote activation of phones by law enforcement agencies. Legal remedies can also let individuals or groups seek compensation or redress for damages caused by remote activation of phones. For example, using judicial review, administrative appeals, complaints, lawsuits, or human rights mechanisms can challenge law enforcement agencies’ actions or decisions regarding remote activation of phones.
How does this technique compare with other countries?
Law enforcement agencies in other countries, such as the United States, Germany, Italy, Israel, Canada, China, France, and the United Kingdom, have used or considered remote activation of phones by the police. This technique is not new or unique. However, the legal framework, the technical methods, and the ethical and social implications of this technique vary from country to country..
How does remote activation of phones by the police work in different countries?
Remote activation of phones by the police is an intelligence technique that varies from country to country. It depends on the legal framework, the technical methods and the ethical issues of each country. Here are some examples of how it works in different countries.
- In the United States, this technique is known as “roving bugs” or “mobile device tracking”. The Foreign Intelligence Surveillance Act (FISA) authorizes it for national security purposes and Title III of the Omnibus Crime Control and Safe Streets Act for criminal investigations. It requires a court order based on probable cause and limited in scope and duration. It can locate or record sounds and images from phones. It can be done by installing malware or exploiting vulnerabilities on phones.
- In Germany, this technique is known as “Quellen-TKÜ” or “source telecommunications surveillance”. The Code of Criminal Procedure and the Telecommunications Act regulate it for criminal investigations and the Federal Intelligence Service Act for national security purposes. It requires a court order based on reasonable suspicion and proportionality. It can intercept communications from phones. To do so, it installs software or uses spyware on phones.
- In Italy, this technique is known as “Trojan horse” or “spyware”. The Code of Criminal Procedure and the Data Protection Code regulate it for criminal investigations. It requires a court order based on serious indications of guilt and necessity. It can access data or record sounds and images from phones. To do so, it installs software or uses spyware on phones.
- In Israel, this technique is known as “IMSI catchers” or “stingrays”. The Wiretapping Law and the Privacy Protection Law regulate it for criminal investigations and the Security Service Law for national security purposes. It requires a court order based on reasonable grounds and proportionality. It can locate or intercept communications from phones. To do so, it uses devices that mimic cell towers and trick phones into connecting to them.
- In Canada, this technique is known as “cell site simulators” or “IMSI catchers”. The Criminal Code and the Charter of Rights and Freedoms regulate it for criminal investigations. It requires a court order based on reasonable grounds and proportionality. It can locate or intercept communications from phones. To do so, it uses devices that mimic cell towers and trick phones into connecting to them.
- In China, this technique is known as “network interception” or “remote control”. The Criminal Procedure Law and the Cybersecurity Law regulate it for criminal investigations and national security purposes. It does not require a court order but only an approval from a higher authority. It can access data or record sounds and images from phones. To do so, it installs software or uses spyware on phones.
- In France, real-time geolocation is regulated by the Criminal Procedure Code and the Intelligence Law for criminal and national security investigations. Article 706-102-1 of the Criminal Procedure Code allows police officers and agents to use a technical device to access, record, store and transmit computer data without the consent of the persons concerned. This requires a court order based on serious reasons and proportionality. Article 230-32 of the Criminal Procedure Code states that “Any technical means for real-time location, throughout the national territory, of a person, without his consent, a vehicle or any other object, without the consent of its owner or possessor, may be used if this operation is required by necessity: “. This also requires a court order based on serious reasons and proportionality.
- In the United Kingdom, this technique is known as “equipment interference” or “hacking”. The Investigatory Powers Act regulates it for criminal investigations and national security purposes. It requires a warrant based on necessity and proportionality. It can access data or record sounds and images from phones. To do so, it installs software or uses spyware on phones.
How does remote activation of phones by the police raise ethical and social challenges?
Remote activation of phones by the police raises ethical and social challenges in different contexts and situations because it involves a trade-off between security and privacy, as well as between effectiveness and legitimacy.
Security versus privacy
On one hand, remote activation of phones by the police can enhance security by providing law enforcement agencies with more information and evidence to prevent, investigate, and prosecute crimes. It can also deter criminals from using phones to plan or commit crimes.
On the other hand, remote activation of phones by the police can undermine privacy by letting law enforcement agencies access personal or professional data without consent or knowledge. It can also violate human rights and civil liberties by letting law enforcement agencies monitor or record sounds and images without notification or justification.
Effectiveness versus legitimacy
On one hand, remote activation of phones by the police can be effective by increasing the chances of finding relevant information or evidence on phones that may be encrypted, hidden, or destroyed. It can also be efficient by reducing the costs and risks of physical surveillance or interception.
On the other hand, remote activation of phones by the police can be illegitimate by violating the legal framework, the technical methods, or the oversight and control mechanisms that regulate this technique in each country. It can also be counterproductive by creating distrust or resistance among phone users or providers, who may use encryption technologies or legal remedies to protect their data or communications.
The ethical and social challenges of remote activation of phones by the police depend on the legal framework, the technical methods, and the oversight and control mechanisms that regulate this technique in each country. They also depend on the cultural and political values, the public opinion, and the media coverage that shape the perception and acceptance of this technique in each country.
Some of the ethical and social challenges of remote activation of phones by the police are how to :
- balance security and privacy in the use of this technique?
- ensure compliance with fundamental rights and freedoms in the use of this technique?
- prevent abuse, misuse, or error in the use of this technique?
- provide legal protection and recourse for individuals or groups affected by this technique?
- ensure accountability and transparency in the use of this technique?
- evaluate the effectiveness and legitimacy of this technique?
- foster trust and cooperation between law enforcement agencies and phone users in the use of this technique?
What is the impact of encryption technologies on this technique?
Encryption technologies are methods or systems that make data unreadable or inaccessible to unauthorized parties. Encryption technologies can have a significant impact on remote activation of phones by the police, as they can make this technique more difficult, risky, or controversial.
How can encryption technologies make remote activation of phones by the police more difficult or impossible?
Encryption technologies can make remote activation of phones by the police more difficult or impossible by preventing law enforcement agencies from accessing data or communications on phones, even if they remotely activate them. Encryption technologies can also protect phones from malware or spyware that enable remote activation.
For example, end-to-end encryption, which some apps such as Signal or WhatsApp use, can prevent law enforcement agencies from intercepting or reading messages or calls on phones, as only the sender and the receiver have the keys to decrypt them. Device encryption, which some operating systems such as iOS or Android use, can prevent law enforcement agencies from extracting or viewing data on phones, as they require a password or a biometric authentication to unlock them.
How can encryption technologies make remote activation of phones by the police more risky or harmful?
Encryption technologies can make remote activation of phones by the police more risky or harmful by exposing law enforcement agencies to legal or technical challenges or dangers. Encryption technologies can also harm phone users by compromising their security or privacy.
For example, breaking encryption, which law enforcement agencies sometimes do to access data or communications on phones, can expose them to legal challenges, as it may violate laws or regulations that protect encryption or privacy. It can also expose them to technical dangers, as it may weaken the security of phones or networks and create vulnerabilities for hackers or criminals. Hacking encryption, which law enforcement agencies sometimes do to install malware or spyware on phones, can harm phone users by compromising their security or privacy, as it may allow unauthorized access to their data or functions.
How can encryption technologies make remote activation of phones by the police more controversial or unacceptable?
Encryption technologies can make remote activation of phones by the police more controversial or unacceptable by raising ethical and social issues or debates. Encryption technologies can also create conflicts or tensions between law enforcement agencies and phone users or providers.
For example, undermining encryption, which law enforcement agencies sometimes request to facilitate remote activation of phones, can raise ethical and social issues or debates, as it may affect human rights and civil liberties, such as privacy, confidentiality, dignity, presumption of innocence, and right to a fair trial. It can also create conflicts or tensions between law enforcement agencies and phone users or providers. They may have different interests or values regarding encryption and security.
How does EviCore NFC HSM technology developed by Freemindtronic offer a high level of protection for phone users?
Remote activation of phones by the police can be facilitated by exploiting security flaws, installing malware, or requesting backdoors in encryption technologies. However, some encryption technologies may be resistant to these measures and offer a higher level of protection for phone users. One of them is the EviCore NFC HSM technology developed by Freemindtronic.
This technology lets users create their own encryption keys in a random way and store them in a physical device that communicates with the phone via NFC (Near Field Communication). The device also lets users define their own trust criteria that must be met to use the keys or their segments. The encryption is done in Quantum-Safe AES-256 mode from either a device compatible with the EviCore NFC HSM technology or from an encrypted enclave in the phone created in the Key chain (Apple) or the Key store (Android) via the EviCore HSM OpenPGP technology. The encryption keys are segmented and superior to 256 bits. Moreover, they are physically externalized from computer systems. Everything is designed by Freemindtronic to effectively fight against espionage and corruption of telephone, computer, communication and information systems. Finally, without a server, without a database, even in air gap and airplane mode works EviCore NFC HSM or EviCore HSM OpenPGP technology. Everything is designed to work in volatile memory to leave no trace in telephone and computer systems.
This technology offers a high level of security and privacy for phone users who want to protect their data from unauthorized access, including by the police. It also offers a high level of performance and usability for phone users who want to encrypt or over-encrypt all types of messaging in the world, including SMS and MMS. It also works with other applications that use encryption, such as email, cloud storage or blockchain.
Furthermore, this technology is designed to be totally anonymous, autonomous, unconnected, without a database, without collecting any information of any kind on the identity of the user, nor on the hardware, nor on the terminals used. The technology is designed to be totally isolated and totally independent of the security of the terminal used whether it is connected or not. Freemindtronic does not keep the unique pairing keys for each NFC HSM device. And even if it did, the user at installation will automatically generate segmented complementary keys for encryption with administrator and user passwords. Each NFC device has a unique 128-bit signature dedicated to fighting against counterfeiting of NFC devices. It is also used as a key segment. The secret stored in eprom memories or in enclaves of the phone and/or computer can be individually secured by other segmented keys characterized by additional trust criteria such as a geozone, a random hexadecimal code via an existing or generated QR code or Bar Code via EviCore HSM. It is therefore physically impossible for Freemindtronic but under judicial assignment to decrypt data encrypted via EviCore HSM technologies even with a quantum computer.
In conclusion, remote activation of phones by the police is an intelligence technique. It aims to fight terrorism and crime by accessing data or sounds and images from phones without consent or knowledge. Law enforcement agencies in various countries have used or considered this technique. For example, France, the United States, Germany, Italy, Israel, Canada, China, and the United Kingdom. However, this technique raises technical, legal, ethical, and social challenges. They need to be addressed.
On the technical side, remote activation of phones by the police depends on three factors: compatibility, connectivity, and security of the phones. It can be done by three methods: exploiting vulnerabilities, installing malware, or using spyware on phones.For example, EviCore NFC HSM technology developed by Freemindtronic protects data and communications on phones from remote activation by the police. Encryption technologies can make this technique more difficult or impossible by preventing law enforcement agencies from accessing data or communications on phones, even if they remotely activate them.
On the legal side, remote activation of phones by the police requires a legal framework that regulates its use and scope. Laws or regulations can authorize it and specify the conditions and criteria for its application. Legal remedies can also challenge it and contest or oppose its validity or legality.
On the ethical side, remote activation of phones by the police involves a trade-off between security and privacy, as well as between effectiveness and legitimacy. It can enhance security by providing more information and evidence to law enforcement agencies to prevent, investigate, and prosecute crimes. It can also undermine privacy by letting law enforcement agencies access personal or professional data without notification or justification.
On the social side, remote activation of phones by the police raises issues or debates that affect human rights and civil liberties. For example, privacy, confidentiality, dignity, presumption of innocence, and right to a fair trial. It can also create conflicts or tensions between law enforcement agencies and phone users or providers, as they may have different interests or values regarding encryption and security.
Therefore, remote activation of phones by the police is a complex and controversial technique that requires a careful and balanced approach that respects the rights and interests of all parties involved. The French bill on remote activation of phones by the police and the EviCore NFC HSM Open PGP technology developed by Freemindtronic illustrate the complex and evolving relationship between intelligence and encryption in the digital age. They raise questions about finding a balance. It is between security and privacy, between public interest and individual rights, between innovation and regulation.
: According to Okta, privacy is the right to control how your information is viewed and used, while security is protection from threats or dangers (https://www.okta.com/identity-101/privacy-vs-security/).
: According to Carnegie Endowment for International Peace, finding a balance between security and privacy requires addressing technical, legal, and social questions (https://carnegieendowment.org/2019/09/10/moving-encryption-policy-conversation-forward-pub-79573).
: According to Springboard, finding a balance between innovation and regulation requires cooperation among stakeholders and respect for human rights (https://www.springboard.com/blog/cybersecurity/privacy-vs-security-how-to-balance-both/).
Phishing: Cyber victims caught between the hammer and the anvil
Responsibility for Phishing, SMiShing, typosquatting, ransomhack, spear phishing, sim swapping, vishing, email and web Spoofing cybervictims is engaged.
There can no longer be any doubt, the responsibility of the Internet user is legally engaged with almost no recourse for the victims to obtain any refund!
Note that we most often find the English term “phishing” which translates “phishing” into French, as well as for the typosquatting that comes from the English “typosquatting” or spear phishing targeted phishing via social engineering techniques or Spoofing technique of spotting.
Following the 2015/2366 directive of the European Parliament and the Council of 25 November 2015, Order No. 2017-1252 of 9 August 2017 makes amendments to Articles L133-16 and L.133-19 of the Monetary and Financial Code for victims of bank card phishing.
Article L133-16 of the Monetary and Financial Code (below) states: “As soon as he receives a payment instrument, the user of payment services takes all reasonable measures to preserve the security of his custom security devices. It uses the payment instrument in accordance with the conditions governing its issuance and use. »
https://www.legifrance.gouv.fr/affichCodeArticle.do?cidTexte=LEGITEXT000006072026&idArticle=LEGIARTI000020860774&dateTexte=&categorieLien=cid
Article L.133-19 of the Monetary and Financial Code (below) states in paragraph IV: “The payer bears all losses caused by unauthorized payment transactions if these losses result from fraudulent conduct on his part or if he did not intentionally or grossly negligently satisfy the obligations referred to in Articles L.133-16 and L.133-17 of the Monetary and Financial Code.”
https://www.legifrance.gouv.fr/affichCodeArticle.do?idArticle=LEGIARTI000020861589&cidTexte=LEGITEXT000006072026
The judgment of the Court of Cassation of 25 October 2017 and that of 28 March 2018 form a case law on the liability of the Internet user victim of phishing by telephone via identity theft and/or via a fake website and/or a fake email.
The judgment of October 25, 2017, (cases of 25.10.17, No. 16-11 644)
https://www.legifrance.gouv.fr/affichJuriJudi.do?idTexte=JURITEXT000035925298&fastReqId=1348908414&fastPos=5&oldAction=rechJuriJudi
Monde.fr press article: http://sosconso.blog.lemonde.fr/2017/10/26/elle-avoue-a-sa-banque-avoir-ete-victime-de-phishing
The judgment of March 28, 2018, (cases. of 28.3.18, No. 16-20 018)
https://www.legifrance.gouv.fr/affichJuriJudi.do?oldAction=rechJuriJudi&idTexte=JURITEXT000036780076&fastReqId=1780826332&fastPos=1
The cassation courts reinforce the obligation of caution of Internet users in the face of phishing attacks that can be telephone, via SMS or e-mail, relating to the use of its bank cards or confidential codes.
- The March 28, 2018 ruling deepens the liability framework for the Internet user by stating that the failure, by gross negligence, to take any reasonable measures to preserve the safety of its personalised security devices.
- The user of a payment service who discloses the personal data of this security device in response to an email that contains clues allowing a normally attentive user to doubt its provenance is held solely responsible
- The bank is not required to inform its customers of the risks of phishing.
How do cybercriminals circumvent 3D Secure code authentication?
Step 1: The cybercriminal must obtain from his next victim the identifiers and passwords of his phone operator.
What for? To enable the cybercriminal to set up telephone referrals of messages received in particular from his bank. It’s easier than stealing the phone. Hence the importance of regularly changing your passwords from your operator’s account. This point becomes more and more crucial since the smartphone is a mobile payment and/or access control terminal.
Step2: The cybercriminal must now obtain all the information from the bank card. Several possibilities; or phishing by email, SMS, blackmail, phone by impersonation by an agent of the operator. The victim overconfidence gives him his information. She is not aware that the 3D Secure will also be sent to cybercriminals.
The cybercriminal only has to make the payment that he can validate himself instead of the victim.
The victim informed at the same time as the cybercriminal that there is a request to validate a purchase via his bank card thinks, since she has not validated the payment, that she is safe. She can object to her credit card. Only it’s already too late. The payment is irrevocable and the bank’s liability is cleared. This is the judgment of October 25, 2017.
In another case, the theft of the smartphone with the bank card may have the same result. In the same way when you pay physically with your bank card where you can see in clear the CCV or CVC composed of 3 to 4 digits used for payments on the internet.
It is advisable to use Freemindtronic Andorra EviAlpha technologies for personal use and EviToken or EviCypher for professional use that allow, after you have physically removed the CCV or CVC code, to make payments on the internet safely. In case of bank card theft, the cybercriminal does not physically have access to the CCV or CVC, the protection with Fullsecure solutions is immediate. This solution is not dependent on the time factor associated with reporting loss or theft for use on the internet. In addition, this solution is capable of managing multiple bank cards and is compatible with any type of bank card internationally, at no additional cost or financial commitment.
There are CCVs or CVCs that change dynamically several times a day. A new security that has an additional annual cost. Used for physical payments, the CCV or CVC is visible. The cybercriminal has only a very short interval of time to rob his victims before the automatic change of the CCV or CVC. In case of theft of this type of bank card, the time depends on the time and date of the declaration of the theft as for other bank cards.
Sim swapping: What does the Monetary and Financial Code say about Secure?sim swapping 3D codes
According to Article L133-23 of the Monetary and Financial Code, it is up to the bank to provide proof of the registration of this type of authentication which makes it possible to presume that the payment has been validated by the rightful holder. Failing that, according to Article L133-18, the transaction is deemed “unauthorized”, the bank is obliged to repay.
The 3D Secure code was developed by Visa and MasterCard to combat the risks of Internet fraud. This code is therefore sent by visa or Master Card’s digital services and is not known to the user until it is received. In fact, it cannot communicate it to a cybercriminal unless the latter has stolen the smartphone, managed to make a copy of the SIM and the most common access to the customer’s accounts of the telephone operator to make a call return to obtain the 3D Secure Code.
What is vishing?
Vishing is a form of phishing that uses the phone as a means of deceiving victims. The term comes from the combination of “voice” and “phishing”. Vishing involves calling victims and pretending to be a trusted person or organization, such as a bank, a public service or a phone operator, and asking them for personal, financial or confidential information. For example, a scammer may claim that the victim’s bank card has been compromised and ask them to confirm their card number and PIN. Vishing can also be used to persuade victims to make fraudulent payments or to download malicious software on their phone.
Vishing is a growing threat, as it exploits the trust that people have in the phone and their lack of vigilance against unsolicited calls. Moreover, scammers use sophisticated techniques to make their calls more credible, such as spoofing, which consists of falsifying the phone number displayed on the recipient’s screen. To protect themselves from vishing, it is important to never disclose personal or financial information over the phone, to verify the identity of the caller by calling back the official number of the organization they claim to represent, and to report any suspicious call to the relevant authorities.
How phishing detection ?
The Internet user must become an expert in phishing detection and typosquatting in the face of the ingenuity of cybercriminals.
According to the case law, the Internet user must carry out a “watchful examination of the correspondent’s changing internet addresses or certain clues, such as misspellings… which should provide clues “of a sufficient nature to appeal to the Internetuser.”
However, the criteria adopted by the case law since 2015 are already obsolete because of the quality of counterfeiting of websites in perpetual increase, but not only.
Indeed, the only test to detect a“changing address”has become complex for #cybervictimes. These ingenious cyber criminals find many solutions to deceive their vigilance, especially by the use of special characters in the domain name.
Jurisprudential obsolescence in the face of the evolution of phishing by Unicode
Cyber criminals use special characters similar to the Latin alphabet, theunicode E100. They have more than 26 characters at their disposal (Ḁ ḁ Ḃ ḃ Ḅ Ḇ ḇ Ḉ ḉ Ḋ ḋ ‘Ḏ ḏ Ḑ ḑ Ḓ ḓ Ḕ’, ‘Ḏ ḏ Ḑ ḑ Ḓ ḓ Ḕ’, ‘Ṟ’, ṟ, ‘, ‘ Ṯ’, ṯ, Ṱ, ṱ’. All they have to do is buy a domain name similar to the original, and replace one of the characters with a unicode character, as similar as possible, with for example a dot below the character.
For example, we will use the websites of telephone operators and banks, just by replacing the letter “r” with“O”it can give this “f-ee.fr”orby replacing “b” with “ḅ” “ḅouyguestelecom.fr” or “ḅanquepopulaire.fr”.
A perverse new game that would be imposed by the jurisprudence that involves the Cyber-Victim to detect the hidden difference in the URL (address).
Are cyber criminals responding to my request? Indeed I had suggested to them in order to help the #cybervictimes to change their modus operandi to help them in the face of jurisprudence. “Please don’t make any more spelling mistakes, and if it’s not grammatically correct, make sure that the simple review of the changing address is not obvious on the exam alone.”
With the fake URL and once the counterfeit site is identical to the original, the trap is activated to capture future #cybervictimes.
Smishing (SMS Phishing)
A cybercriminal sends you an SMS (i.e. a text message) asking you to click on a link. If you click on the link in the message, you will be redirected to a fake website asking you to provide your information in a phishing form.
The cybercriminal attempts to obtain your sensitive information through a text message (i.e. SMS). They will ask you to provide personal information such as a social security number, credit card or health insurance information. He claims that you must give this information or something bad will happen to you (e.g. your electricity is cut off, your credit card is blocked or your online account is terminated). To learn more about Smishing, click HERE.
Typosquatting another form of phishing
Almost identical to phishing, fake site, fake URL, with the big difference that the cybercriminal bets on the typos of #cybervictimes when the user informs the internet address. Examples include “fri.fr” without (ee) or “bouyguetelecom.fr” without (s) or “banque-populaire.fr” with the addition of a hyphen or “free.com” by changing the extension (.fr).
A new playground for cyber criminals, a fake address bar on Android phones that use the Chrome browser.
Google Chrome on Android smartphone only shows the title of the site visited rather than displaying the full address bar with the URL. A new feature for user comfort to make more room for content to be played. This allows the cybercriminal to pass a phishing page as a legitimate web page.
Spoofing over domain name extension makes many cyber victims, especially for domains in .com. The cybercriminal buys a .co domain name with a name identical to that of a known site, an example “www.amazon.co”. The cyber victim receives an email that appears to be from the original site. She is invited to log in via a link to the “www.amazon.co” mirror site. She’s not going to be careful that she’s not on the original site with a .co extension instead of .com. It is therefore with confidence that the cyber victim will enter personal information, especially his login ID and password.
How will the case law evolve to determine the threshold that will qualify the Cyber victim as “negligent”?
Natural protection against phishing and typosquatting
There is a barrier to phishing when the domain name extension is proprietary. This is the case, for example, of the extension of the BNP Paribas bank with its own extension “.bnpparibas” of the website “www.mabanque.bnpparibas”. In this case, it is a cost of around $185,000 and a binding procedure to obtain fromICANN its custom domain name extension that establishes a natural barrier against this type of attack. However, users of these sites still need to be informed of this distinction. Otherwise, the case law is unequivocal and will be imposed on cyber-victims. Indeed, it is difficult to explain that they did not see the different extension.
Learn more about custom extension
https://www.prodomaines.com/extension-personnalisee
Is the overall level of computing so linear among Internet users that they are all able to carry out such a review?
I doubt it very much.
In the same way, to think that only insiders are safe from phishing seems to me a very risky shortcut.
It is becoming more and more difficult for the Internet user to differentiate between the true and the false.
Shouldn’t case law or a revision of the law take into account the quality of the forger as for the currency, to exonerate the responsibility of the victim?
Instant transfer payment, a new eldorado of cybercriminals?!
What will cybercriminals imagine to create new victims following the new implementation initiated by the ECB with the instant transfer payment system, in less than 10 seconds, irrevocably, achievable with a simple telephone number?
How does it work? (Source the tribune)
It is a transfer in euros that is initiated from the website of his bank or his mobile banking application by choosing the instant mode. Simply enter the IBAN or, less tedious, its mobile phone number (converted to IBAN by the bank), or even scan a QR code to send the money. The account is credited in less than 10 seconds and payment confirmation is sent by SMS within 20 seconds. The transfer is irrevocable. The service is usable 24 hours a day, 365 days a year. A ceiling of 15,000 euros has been decided at European level (the Netherlands has abolished it).
I predict an increase in cybercrime on this new SEPA Express system, if the security system is not equal to or greater than that of bank cards!
Innovation goes further and further to allow the machine to gradually substitute for human physical consent since currents of thought believe that man is more failing than the machine.
To this day, we cannot assign a machine to court. In fact, no one is safe from being between the hammer and the anvil.
‘Ransomhack’: blackmail to non-compliance RGPD
Cyber criminals also use phishing to steal private data, known asransomhack. Taken hostage, this data is being blackmailed by using the new European regulations (RGPD) to put pressure on victims. The goal is to get the ransom faster. It is enough to threaten the victim to make public the data if the ransom is not paid, weighing the risk of strong criminal and civil penalties incurred in the event of non-reporting to the CNIL of the theft of data.
Once again the technique of hammer and anvil becomes a formidable weapon in the face of the fear of double punishment, victim and criminally and civilly litigant.
The phishing technique is no longer the preserve of cyber criminals: it may be more or less legal!
It is difficult to establish statistics, as victims do not file complaints. It is very likely that many of you will recognize yourself in this situation.
What for?
Despite the new provisions imposed by the RGDP, online sites selling goods and/or services have found a way to obtain their customers’ bank card information. However, there is no reason for the client to provide this type of information.
Only here, it takes on a legal appearance, to get this valuable information from bank cards. In principle, legally you have the right to request their removal.
Now that we’re done with the theory, let’s move on to practice
As we have seen before, giving the information of bank cards is under the full responsibility of the Internet user.
Similarly, it is common knowledge that cyber criminals regularly steal private data, including bank cards from the databases of merchant sites.
According to the principle of prudence established by the Court of Cassation, could it not be taken up against the victim? Could the Court not consider that there is no need to inform the Internet user that there is a risk that his credit card information will be derogating? That he is in fact the only one responsible for the information he transmits!
Why do online sales sites need this credit card information? What do they really do with it?
I believe that in terms of the RGPD, you would be entitled to ask the question.
There are many good reasons that will be invoked, but these are not for the customer but for the service provider, especially when the service provider has a recurring payment system in place.
This credit card information becomes valuable for the quality of the outstanding accountable or EENE. If you want to know more(https://comptabilite.ooreka.fr/astuce/voir/609429/effet-escompte-non-echu).
What to remember: The expected effect is passed on to another creditor or bank. The higher the quality of the debt, the less expensive the cost of the discount. Even if rates are low, it is a gain.
Another interest is the forgetting and withdrawal of small sums that often go under the radar of customers. Agreements are established that provide for automatic renewal and anniversary dates with a minimum period of time to report the contract.
New: drown the fish under the guise of updates to the terms and conditions of sale! The service contract for which you consented is unilaterally amended. The trick is the criterion of trust. You are made to accept new conditions that cancel the previous ones.
Let us go even further in the violation of the rules of law.
If you cannot be accepted for a new document, a principle of law that does not exist in contractual matters is used. Just as a contract cannot be changed unilaterally, either by adhesion or synallagmatically, without the consent of the co-contractor.
Silence is not worth acceptance!
However, many service companies send you emails informing you that if you do not respond within a certain period of time, the contract will be considered accepted. If you refuse, you lose the service for which the provider had committed. However, the commitment may also include back-doors such as the subject of an update of general terms of sale.
The hammer and anvil method is activated!
This is a form of blackmail that is illegal, done digitally but does not rank in cyber crimes.
What for?
A beginning of response trail, because they act overdrawn and they are legally registered in corporate registers but not cyber criminals in principle.
The deterrent force of a recourse by the Internet user!
They also have a master asset, the cost of a civil or criminal action procedure in relation to the small amounts involved. The cost of obtaining a court order, such as legal fees, legal fees, time spent and the uncertainty of obtaining redress, is enough to make any desire for prosecution give up.
Even if the civil and/or criminal dol can be qualified, no one will ever know that you are also the victim of phishing by deception of the co-contractor to obtain the information of bank cards or private data.
However, when you show the teeth against cybercriminals, they trade without resisting too much. It will also depend on who you are in the fuse position. Ane against measure of the Internet user. This will also depend on the caller in the fuse position.
The balance of power through blackmail can be balanced. The risk of bad publicity on social networks, the CNIL Pro or Private,can have morecostly consequences than the sums incurred. In the same way if the Internet user has insurance that pays for legal and procedural costs. In this hypothesis the blackmail is reversed by the Internet user. The latter is no longer between the hammer and the anvil.
In the end, the amicable arrangement is better than a long trial. As a result, the risk of bad publicity on social networkscan have more costly consequences than the sums incurred. In this case, this form of threat may allow the Internet user to no longer be between the hammer and the anvil.
What are the current trends of phishing?
Phishing is a constantly evolving phenomenon, which adapts to new technologies and new behaviors of internet users. According to the statistics provided by https://www.phishing.org/phishing-statistics/ or https://www.kaspersky.com/resource-center/threats/phishing-statistics-report, phishing increased significantly in 2020 and 2021, especially because of the Covid-19 pandemic that favored remote work and online shopping. Phishing accounts for about 80% of cyberattacks and affects both individuals and businesses.
Moreover, phishing diversifies and takes new forms, such as vishing, smishing or spear phishing. Vishing is a form of phishing that uses phone calls to trick victims. Smishing is a form of phishing that uses SMS or instant messages. Spear phishing is a form of phishing that targets specific individuals or organizations using personalized information. These new forms of phishing are harder to detect and prevent, as they exploit the trust and emotion of victims.
To conclude, phishing is a major risk for the security of internet users and organizations, which requires vigilance and prevention. By following the tips that I gave you in this article, you can protect yourself from phishing and reduce the chances of being a victim.
You want to know more about the deception of the co-contractor from a legal point of view.
https://www.superprof.fr/ressources/droit/droit-general/droit-des-obligations/faute-et-nullite-du-contrat.html
Having the freedom not to give credit card information outside of a single transaction and under the exclusive control and consent of the payer, should not be a right to defend. Freemindtronic technologies such as EviToken or EviCypher with web browser extensions protect bank card information and counter phishing attacks. It is above all a tool to exercise this right to no longer give his credit card information on the internet to be saved.
To learn more about our credit card protection solutions, you can read the following articles on Linkedin:
Why are Freemindtronic’s #NFC Offline electronic safes already in compliance with the decree that will come into effect on 01/01/19?
https://www.linkedin.com/pulse/pourquoi-les-coffres-forts-%C3%A9lectroniques-nfc-offline-de-gascuel/
A new cloud-free individual security service with anti-phishing to protect all types of bank cards from start to finish
https://www.linkedin.com/pulse/un-nouveau-service-de-s%C3%A9curit%C3%A9-individual-without-cloud-with-gascuel/
https://www.linkedin.com/pulse/victimes-dhame%C3%A7onnage-impunity%C3%A9-of-cybercriminals-jacques-gascuel/