Articles
Our articles
Welcome to the publication of our articles
Quantum-Resistant Passwordless Manager — PassCypher finalist, Intersec Awards 2026 (FIDO-free, RAM-only)
Quantum-Resistant Passwordless Manager 2026 (QRPM) — Best Cybersecurity Solution Finalist by PassCypher sets a new [...]
4 Comments
Nov
French IT Liability Case: A Landmark in IT Accountability
The Context of the French IT Liability Case The Rennes French Court of Appeal examined [...]
Jan
ANSSI Cryptography Authorization: Complete Declaration Guide
Complete Guide: Declaration and Application for Authorization for Cryptographic Means In France, the import, export, [...]
Oct
New Microsoft Uninstallable Recall: Enhanced Security at Its Core
Microsoft’s Revamped Recall System Microsoft recently overhauled its Recall feature, which had faced criticism for security [...]
Oct
EAN Code Andorra: Why It Shares Spain’s 84 Code
All About EAN Codes and Their Importance EAN Code Andorra illustrates how the EAN (European [...]
Sep
Russian Espionage Hacking Tools Revealed
Russian Espionage Hacking Tools: Discovery and Initial Findings Russian espionage hacking tools were uncovered by [...]
Aug
End-to-End Messaging Encryption Regulation – A European Issue
Regulation of Secure Communication in the EU The European Union is considering measures to regulate [...]
Jun
NFC vCard Cardokey: Revolutionizing Digital Networking
NFC vCard: Revolutionize Your Professional Networking As the creator of Cardokey, I am thrilled to [...]
Mar
EU Sanctions Cryptocurrency Regulation: A Comprehensive Overview
EU Sanctions Cryptocurrency Regulation: A Comprehensive Overview The EU is stepping up its regulatory game [...]
Mar
Encrypted messaging: ECHR says no to states that want to spy on them
Encrypted messaging: ECHR says no to states that want to spy on them The historic [...]
Feb
How the attack against Microsoft Exchange on December 13, 2023 exposed thousands of email accounts
How the attack against Microsoft Exchange on December 13, 2023 exposed thousands of email accounts [...]
1 Comment
Feb
How to protect yourself from stalkerware on any phone
What is Stalkerware and Why is it Dangerous? Stalkerware, including known programs like FlexiSpy, mSpy, [...]
Jan
Human Limitations in Strong Passwords Creation
Human Limitations in Strong Passwords: Cybersecurity’s Weak Link Passwords are essential for protecting our data [...]
1 Comment
Jan
Terrapin attack: How to Protect Yourself from this New Threat to SSH Security
Protect Yourself from the Terrapin Attack: Shield Your SSH Security with Proven Strategies SSH is [...]
Jan
Google OAuth2 security flaw: How to Protect Yourself from Hackers
Google OAuth2 security flaw: Strategies Against Persistent Cookie Threats in Online Services Google OAuth2 security [...]
Jan
Telegram and the Information War in Ukraine
How Telegram Influences the Conflict between Russia and Ukraine Telegram and the information war in [...]
Jan
Kismet iPhone: How to protect your device from the most sophisticated spying attack?
Kismet iPhone: How to protect your device from the most sophisticated spying attack using Pegasus [...]
Jan
The American Intelligence: How It Works
The American Intelligence: How It Works, Its Limits and Consequences The American intelligence is one [...]
Dec
Ledger Security Breaches from 2017 to 2026: How to Protect Yourself from Hackers
Ledger Security Breaches have become a major indicator of vulnerabilities in the global crypto ecosystem. [...]
5 Comments
Dec
TETRA Security Vulnerabilities: How to Protect Critical Infrastructures
TETRA Security Vulnerabilities: How to Protect Critical Infrastructures from Cyberattacks TETRA (Terrestrial Trunked Radio) is [...]
Nov
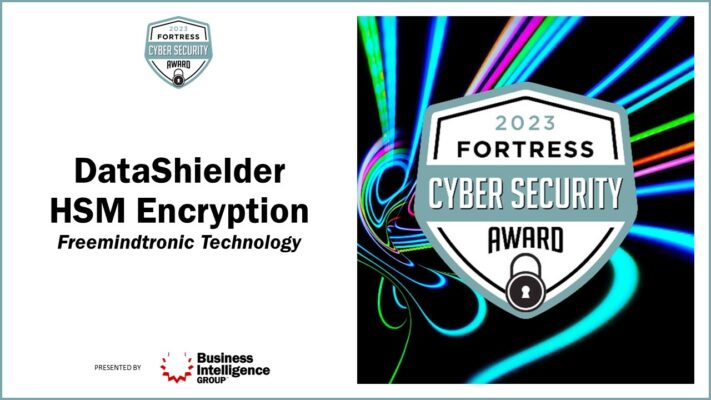
DataShielder Defense NFC HSM: Protect Your Sovereign Communications
DataShielder Defense NFC HSM: How to Protect Your Sovereign Communications with a Revolutionary Solution The [...]
11 Comments
Nov
FormBook Malware: How to Protect Your Gmail and Other Data
How to Protect Your Gmail Account from FormBook Malware Introduction Imagine that you receive an [...]
Nov
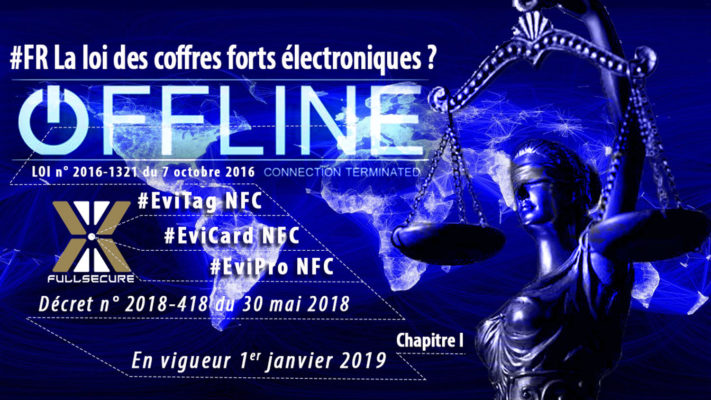
Dual-Use Encryption Products: a regulated trade for security and human rights
The international regulations on dual-use encryption products The main international regulations that apply to dual-use [...]
2 Comments
Nov
Quantum computing RSA encryption: a threat and a solution
Quantum computing RSA encryption: a challenge and a solution Quantum computing RSA encryption is a [...]
Nov
NFC Business Cards with Cardokey free for life: How to Connect without Revealing
NFC Business Cards: Create your NFC vCard with Cardokey, the Eco-Friendly and Secure NFC App [...]
Nov
Pegasus: The cost of spying with one of the most powerful spyware in the world
Pegasus: The Cost of Spying with the Most Powerful Spyware in the World Pegasus is [...]
Oct
Chinese hackers Cisco routers: how to protect yourself?
How Chinese hackers infiltrate corporate networks via Cisco routers A Chinese-backed hacker group, known as [...]
Oct
RSA Encryption: How the Marvin Attack Exposes a 25-Year-Old Flaw
How the RSA Encryption – Marvin Attack Reveals a 25-Year-Old Flaw and How to Protect [...]
Oct
Communication Vulnerabilities 2023: Avoiding Cyber Threats
Communication Vulnerabilities in 2023: Unveiling the Hidden Dangers and Strategies to Evade Cyber Threats 2023 [...]
Sep
ZenRAT: The malware that hides in Bitwarden and escapes antivirus software
How this malware hides in Bitwarden and escapes antivirus software to steal your information ZenRAT [...]
Sep
Freemindtronic’s Legacy: Rediscovering Excellence
Resurrecting Excellence: Freemindtronic’s Legacy in Nanotechnology and the ‘Fullprotect’ Revolution In 2013, Freemindtronic, a visionary [...]
Sep
Enhancing Crypto Wallet Security: How EviSeed and EviVault Could Have Prevented the $41M Crypto Heist
EviSeed and EviVault NFC HSM Technologies could have prevented the $41 million crypto theft by [...]
Sep
Why choose a Cold Wallet NFC HSM to secure your cryptocurrencies?
How to secure your cryptocurrencies with a cold wallet NFC HSM is the topic of [...]
Sep
How to choose the best multi-factor authentication method for your online security
Everything you need to know about multi-factor authentication and its variants Have you ever wondered [...]
Sep
How to Recover and Protect Your SMS on Android
Recover and Protect Your SMS on Android: A Complete Guide First of all, SMS are [...]
Aug
Coinbase blockchain hack: How It Happened and How to Avoid It
How to Prevent Coinbase Blockchain Hack with EviVault NFC HSM Technology What happened to Coinbase [...]
Aug
Protect yourself from Pegasus spyware with EviCypher NFC HSM
How to protect yourself from Pegasus spyware with EviCypher NFC HSM Pegasus Spyware: what it [...]
Aug
Unitary patent system: why some EU countries are not on board
Why some EU countries are not on board What is the unitary patent? The unitary [...]
Aug
Protect US emails from Chinese hackers with EviCypher NFC HSM?
How EviCypher NFC HSM technology can protect emails from Chinese hackers The Chinese hack on [...]
Jul
Ommic case: How a French company allegedly handed over military secrets to China and Russia
Ommic case: The story of a French semiconductor company accused of spying for China and [...]
Jul
EviVault NFC HSM vs Flipper Zero: The duel of an NFC HSM and a Pentester
EviVault NFC HSM vs Flipper Zero: The duel of an NFC HSM and a Pentester [...]
Jul
Digital signature: How Freemindtronic secures its software
What is digital signature? Digital signature is a process that allows to authenticate the origin [...]
Jul
PassCypher NFC HSM: Secure and Convenient Password Management
PassCypher NFC HSM and PassCypher Pro NFC HSM: Secure and Convenient Password Management Introduction PassCypher [...]
7 Comments
Jun
NRE Cost Optimization for Electronics: A Comprehensive Guide
Efficient NRE Cost Optimization for Electronics NRE Cost Optimization, in the field of electronic product [...]
Jun
Securing IEO STO ICO IDO and INO: The Challenges and Solutions
Securing IEO STO ICO IDO and INO: How to Protect Your Crypto Investments Cryptocurrencies are [...]
Jun
Remote activation of phones by the police: an analysis of its technical, legal and social aspects
What is the new bill on justice and why is it raising concerns about privacy? [...]
Jun
Protect Meta Account Identity Theft with EviPass and EviOTP
Protecting Your Meta Account from Identity Theft Meta is a family of products that includes [...]
May
How BIP39 helps you create and restore your Bitcoin wallets
How BIP39 helps you create and restore your Bitcoin wallets Do you struggle to manage [...]
May
Segmented key authentication: an innovation by Jacques Gascuel to secure sensitive data
Segmented key authentication: an innovation by Jacques Gascuel to secure sensitive data What is segmented [...]
1 Comment
Recovery Phrase Backup: How to Secure It
This article will be updated with any new information on the topic, and readers are [...]
5 Comments
May
BITB Attacks: How to Avoid Phishing by iFrame
Browser-in-the-Browser (BITB) attacks: interface forgery through redirection iframes and the structural limits of browser trust. [...]
May
Snake Malware: The Russian Spy Tool
Snake: The Russian malware that steals sensitive information for 20 years Snake is a malware [...]
May
ViperSoftX How to avoid the malware that steals your passwords
ViperSoftX: The Malware that Steals Your Cryptocurrencies and Passwords ViperSoftX is a malware that steals [...]
1 Comment
May
What is Juice Jacking and How to Avoid It?
Juice Jacking: How to Avoid This Cyberattack Do you often use public USB chargers to [...]
May
Strong Passwords in the Quantum Computing Era
How to create strong passwords in the era of quantum computing? Quantum computing is a [...]
2 Comments
May
Protect Your Data from AMOS Malware
AMOS Malware Protection with Keepser Cold Wallet The Threat of AMOS Malware on macOS AMOS [...]
1 Comment
May
Cryptbot malware steals data cryptocurrencies
Understanding Cryptbot Malware: A Comprehensive Guide to the Threats and Risks Cryptbot malware is a [...]
1 Comment
May
The first wood transistor for green electronics
What is a wood transistor? A transistor is a device that can amplify or switch [...]
Apr
Kevin Mitnick’s Password Hacking with Hashtopolis
Password hacking tool: how it works and how to protect yourself Password hacking is a [...]
Apr
KingsPawn A Spyware Targeting Civil Society
QuaDream: KingsPawn spyware vendor shutting down in may 2023 QuaDream was a company that [...]
Apr
Our articles
Welcome to the publication of our articles Our articles deal with the subject of data [...]
May
Phishing Cyber victims caught between the hammer and the anvil
Phishing is a fraudulent technique that aims to deceive internet users and to steal their [...]
May