EviSSH: solution for secure management of SSH keys storable in HSM
EviSSH SSH Key Management simultaneously improves the simplicity, creation, management and security of secure network communications storable in an HSM such as NFC HSM or EviKey NFC HSM whose implementation you can read (How to secure your SSH key with NFC HSM USB Drive EviKey). This innovative platform transforms the way we manage SSH keys. It ensures secure and efficient management, essential in today’s cybersecurity landscape.
EviSSH stands out by simplifying complex processes. It offers an intuitive interface, making SSH key management accessible to all. With EviSSH, secure system administration becomes straightforward and reliable.
This tool integrates cutting-edge technology for robust security. It seamlessly encrypts data, fortifying network interactions. EviSSH provides peace of mind, securing sensitive digital assets effectively.
In sum, the technology EviSSH represents a leap in digital security. It meets the growing demands for safe, user-friendly SSH key management solutions.
EviSSH SSH Key Management: Mastering SSH Fundamentals
Secure Shell (SSH) is a cryptographic network protocol that provides a secure way to access a computer over an unsecured network. SSH is widely used for remote login, file transfer, and tunneling other protocols.
SSH uses public-key cryptography to authenticate users and encrypt data. A public key is shared with the remote computer, while the private key remains confidential. When a user connects to a remote computer using SSH, the remote computer uses the public key to authenticate the user and encrypt the data sent between the two computers.
SSH is a secure alternative to insecure protocols like Telnet and FTP, which do not use encryption. SSH is also more efficient than Telnet and FTP, as it does not require the user to enter a username and password each time they connect to a remote computer.
In today’s digital world, SSH is essential for secure network administration. SSH is used to manage servers, transfer files, and access remote systems. SSH helps to protect sensitive data from unauthorized access.
Defining EviSSH in SSH Key Management
EviSSH is an innovative method for simplifying SSH key generation and management through a browser extension.
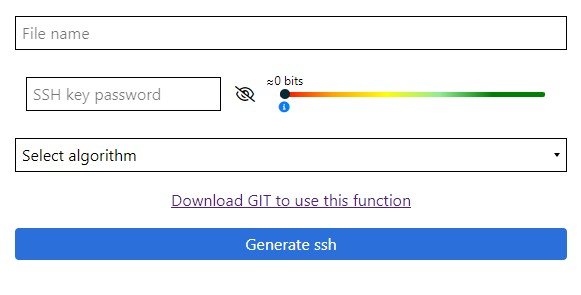
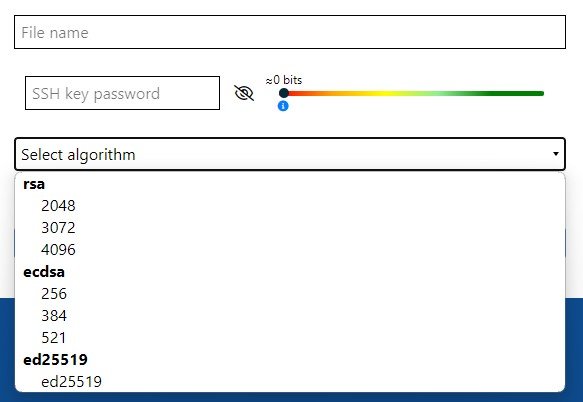
Image 1: The EviSSH User Interface for Key Generation
This image shows the EviSSH user interface where the user begins the SSH key creation process by inputting a file name and choosing a password, with a visual strength indicator assisting in creating a strong password.
Operational Mechanics of EviSSH
EviEngine stands out as a versatile and forward-thinking technology, offering several pivotal functions:
- Web Service Automation: This technology expertly automates actions in web services, eliminating the need for servers or databases. Your data remains accessible and secure, stored wherever you choose on your computer.
- License Management: With EviEngine, managing software licenses becomes effortless. It streamlines the usage of browser extensions across various devices, provided you hold the necessary license key.
- Extension Activation: EviEngine activates specific functions in extensions using license keys from the web extension publisher. This approach allows access to varied features based on the license key in possession.
- System-Browser Communication: Bridging the gap between computer systems and web browsers, EviEngine facilitates smooth communication. It sends commands to browsers, enabling them to execute actions within web services efficiently.
Each function of EviEngine contributes to a seamless, efficient digital experience, marking it as an essential tool in modern technological ecosystems.
Functions of EviSSH
EviSSH’s primary functions include SSH key generation, management, and storage, with support for various encryption algorithms.
Compatibility and Requirements
- Browser Extension Compatibility: Chrome, Firefox, Edge.
- Supported Algorithms: RSA, ECDSA, ed25519.
- OS Compatibility: Windows, macOS, Linux* (*EviEngine may not function with Linux when managing licenses via hardware due to system access restrictions.)
Integration Requirements for Windows
- Git for Windows: A prerequisite for SSH key management features.
- EviEngine: Required for full EviSSH functionality, offering advanced web service automation.
Future Developments
EviSSH is continually evolving, with a strong focus on enhancing cross-platform compatibility. A significant future development will address the current limitations on Linux systems. Efforts are underway to achieve total compatibility with Linux, ensuring that EviSSH will provide the same seamless user experience on Linux as it does on other operating systems. This includes finding solutions to bypass the native system access restrictions imposed by Linux without compromising security or user experience.
Another point of future development is to add a secure practices automation system by providing options to automate SSH key rotation and renewal, aligning with security best practices and reducing administrative burden on users.
Step-by-Step Guide to EviSSH SSH Key Management
Here’s how to use EviSSH, as visually depicted in the interface images:
- File Name: Enter a name for the SSH key for identification.
- SSH Key Password: Create a password, guided by a visual strength indicator.
- Select Algorithm: Choose from a range of encryption algorithms, as shown in the dropdown menu in the image.
Image 2: EviSSH Interface Highlighting the Algorithm Selection and Key Generation
This image captures the dropdown menu for selecting the encryption algorithm and the ‘Generate ssh’ button, which the user will click to create their SSH key. It also indicates the need to download Git for certain functionalities.
EviSSH is more than just an SSH key management tool; it’s a cybersecurity solution that incorporates deep protective measures for robust and secure key management.
Advanced Security with EviSSH SSH Key Management
EviSSH’s design is security-centric, ensuring that every aspect of SSH key management is fortified against potential vulnerabilities. The platform employs a multifaceted security approach to safeguard digital assets:
- Advanced Encryption Algorithms: EviSSH is equipped with the latest and most secure encryption algorithms, including RSA 4096, ECDSA, and ed25519. These algorithms are recognized for their ability to create cryptographic keys that withstand the test of current computational capabilities, deterring even the most sophisticated decryption attempts.
- Robust Password Protection: The system enforces a strict password policy, reinforced by real-time visual feedback on password strength based on Shannon’s math. This mechanism encourages users to create strong, complex passwords, which are then hashed and salted, providing an additional layer of security.
- Secure Key Storage Options: Recognizing the importance of not only generating but also securely storing SSH keys, EviSSH offers integration with hardware security modules like EviKey NFC HSM. This collaboration enables keys to be stored in a physically secure environment, requiring multi-factor authentication to access, thus significantly reducing the risk of theft or unauthorized use.
EviSSH’s Role in Enhancing Cyber Safety
Beyond basic protection, EviSSH introduces several layers of cyber safety measures that stand out in the SSH key management landscape:
- Key Management Isolation: By isolating the key management process within the browser extension, EviSSH ensures that sensitive operations are compartmentalized, reducing the attack surface for potential exploits.
- User-Centric Security Practices: EviSSH advocates for and educates on best practices in key management, promoting user behaviors that contribute to a more secure digital ecosystem.
Enhanced Value Through Security Integration
EviSSH’s value proposition extends to its commitment to integrating security into every feature:
- Ease of Use with Security: The intuitive interface of EviSSH does not compromise on security. Instead, it bridges the gap between user-friendliness and sophisticated security measures, allowing users to manage SSH keys with confidence.
- Customizable Security Settings: Advanced users have the option to customize their security settings within EviSSH, tailoring the security level to their specific needs and preferences.
Through its comprehensive cyber safety and security framework, EviSSH not only simplifies the SSH key generation and management process but also elevates it to meet the high-security demands of the modern digital landscape.
Sequence Diagram: From Data Input to Key Storage
To visualize the process from the user’s data input to the secure storage of the SSH key, let’s look at the sequence diagram that details the interactions between different components.
Sequence Diagram: The EviSSH Process Flow
The sequence diagram should be placed here to provide a visual explanation of the steps listed below:
- Step 1 – User Data Input: The user provides the necessary data for the SSH key within the EviSSH extension.
- Step 2 – Key Generation Request: EviSSH communicates with EviEngine to initiate key generation.
- Step 3 – EviEngine Processing: EviEngine interacts with Git for Windows, which is responsible for creating the key.
- Step 4 – Key Generation: Git for Windows generates the SSH key.
- Step 5 – EviEngine to EviSSH: The key is passed back through EviEngine to the EviSSH extension.
- Step 6 – Key Display: EviSSH displays the newly created SSH key to the user.
- Step 7 – Secure Key Storage: Finally, the user has the option to securely store the SSH key on EviKey NFC HSM.
This diagram helps to encapsulate the technical flow and the integration points, making the understanding of EviSSH’s functionality clearer for the user.
Navigating EviSSH SSH Key Management: User Essentials
EviSSH is an interface for generating and managing SSH keys from your web browser, simplifying the process by utilizing a user-friendly extension.
EviSSH enhances security through a visual password strength indicator, support for various encryption algorithms, and the option to store SSH keys on EviKey NFC HSM for secure hardware storage.
EviSSH is compatible with Windows and macOS. For Linux users, full compatibility is subject to the specific version of EviEngine used, especially when it involves hardware-based license management.
Yes, Git for Windows is required to manage SSH key functionalities, and EviEngine is necessary for the extension to operate seamlessly in your browser.
Securely Store Your SSH Keys with EviKey NFC HSM USB Drive
Prerequisites:
- EviKey NFC HSM USB Drive
- Computer with Git installed
Steps:
1. Connect the EviKey NFC HSM USB Drive
- Plug your EviKey NFC HSM USB drive into your computer.
2. Locate the SSH Key on the USB Drive
- Identify the drive letter assigned to your USB drive (for example, I:).
3. Create an SSH Directory
- Navigate to the root of your USB drive and create a .ssh directory.
4. Edit the .gitconfig File
-
Open the .gitconfig file with a text editor in administrator mode.
-
Add the following section at the end of the file:
[ssh]
IdentityFile = I:.sshevissh
- Save and close the .gitconfig file.
5. Verify the Configuration
- Open a command line and execute the following command:
git config --get ssh.IdentityFile
- The command should return the path to your SSH key directory on the USB drive, e.g., I:.sshevissh.
6. Troubleshooting
- If the command does not return the correct path, check the .gitconfig file for any errors. Ensure the line
[ssh] IdentityFile = I:.sshevisshis correct.
Additional Tips for Modifying the SSH Key Path:
-
Ensure the path to your SSH key is correct. You can verify the path by navigating to your USB drive in File Explorer.
-
Remember to escape backslashes in Windows file paths by using double backslashes ().
-
Always back up your .gitconfig file before making modifications.
For more information on this topic, please refer to our guide:
How to secure your SSH key with NFC HSM USB Drive EviKey
Link to article: https://freemindtronic.com/nfc-hsm-usb-drive-secure-ssh-key-evikey/
-
Secure Shell (SSH) is a cryptographic network protocol that provides a secure way to access a computer over an unsecured network. SSH is widely used for remote login, file transfer, and tunneling other protocols.
-
SSH uses public-key cryptography to authenticate users and encrypt data. A public key is shared with the remote computer, while the private key remains confidential. When a user connects to a remote computer using SSH, the remote computer uses the public key to authenticate the user and encrypt the data sent between the two computers.
-
SSH is a secure alternative to insecure protocols like Telnet and FTP, which do not use encryption. SSH is also more efficient than Telnet and FTP, as it does not require the user to enter a username and password each time they connect to a remote computer.
In today’s digital world, SSH is essential for secure network administration. SSH is used to manage servers, transfer files, and access remote systems. SSH helps to protect sensitive data from unauthorized access.
Creating a Custom Script or Alias for SSH Key Generation
While Git doesn’t provide a built-in method to change the default location for generating new SSH keys, you can create a custom script or alias to direct ssh-keygen to save new keys to your EviKey NFC HSM USB drive.
Creating a Custom Alias in Bash:
- Modify Bash Profile:
- Open your
.bashrcor.bash_profilefile in a text editor. - Add the following alias to the file:
-
bash
alias ssh-keygen-usb='ssh-keygen -t rsa -b 4096 -f /path/to/your/usb/drive/new_key'
- Replace
/path/to/your/usb/drive/new_keywith the actual path to your EviKey NFC HSM USB drive where you want to store the new key. - Save and close the file.
Using the Alias:
- Whenever you want to generate a new SSH key on your EviKey NFC HSM USB, use the command
ssh-keygen-usbin your terminal. - This will invoke
ssh-keygenwith the specified path, storing the new key directly on your USB drive.
Future Developments in EviSSH
EviSSH Integration:
- Future versions of EviSSH are planned to include a script that will automatically direct the path of new SSH keys to your EviKey NFC HSM USB drive.
- This feature will simplify the process, making it more user-friendly and efficient.
Note:
- The custom script or alias solution requires some knowledge of shell scripting and may not work in all operating systems or environments.
- Always ensure that your private keys are stored securely and that you follow best practices for SSH key management.
By implementing these steps, you can configure Git to use your EviKey NFC HSM USB drive as the default storage location for new SSH keys, enhancing the security and management of your SSH keys.
This tutorial provides a detailed guide on configuring Git to store SSH keys on a secure USB drive and includes a workaround for custom SSH key generation. It’s tailored for users who are comfortable with basic scripting and command-line operations.
Store Your SSH Keys on EviKey NFC HSM USB Drive for Enhanced Security
Prerequisites:
- Default Storage Location: By default, SSH key pairs generated by EviSSH are stored in the default path created by Git, which typically resides in the user’s account on the operating system. For instance, on Windows, this would be C:Users[name].ssh.
Storing Keys on EviKey NFC HSM USB Drive:
- Copying or Moving Keys: Carefully select the SSH key pairs you intend to store on the EviKey NFC HSM USB drive, and transfer them to the previously created .ssh directory on your removable drive.
- Setting Git to Recognize Removable Drive: If you want Git to utilize your removable drive as the default storage location for SSH keys, follow the instructions outlined in the tutorial: “Configuring Git for Default SSH Key Storage on EviKey NFC HSM USB.” This tutorial guides you through the process of modifying Git’s configuration to recognize and utilize the SSH keys stored on your EviKey NFC HSM USB drive.
Note:
-
Securing Private Keys: When transferring SSH keys to the EviKey NFC HSM or any external device, ensure that you only move the private key that you intend to use from that specific device. Prioritize the security of your private keys during and after the transfer.
-
Updating Systems: After relocating your SSH keys to the EviKey NFC HSM USB drive, remember to update any systems or configurations that rely on these keys to point to the new location.
By following these simple steps, you can effectively manage your SSH keys with EviSSH and EviKey NFC HSM, enhancing your cybersecurity practices and maximizing the benefits of these cutting-edge technologies.
This addition to the FAQ provides clear instructions for users on how to manage SSH keys with EviSSH and EviKey NFC HSM, ensuring that they can efficiently leverage these technologies for enhanced cybersecurity practices.
Enterprise-Level Deployment
Simplified and Secure Access in Large Organizations
EviSSH enables IT departments to manage SSH keys across various servers, thereby streamlining access management and enhancing security against unauthorized access.
Secure Development Environments
Integrating EviSSH with EviKey NFC HSM for Developers
Developers working in secure environments can use EviSSH in conjunction with EviKey NFC HSM. Consequently, this ensures that SSH keys are securely protected by hardware, providing an additional defense layer.
Remote Server Administration
Reliable and Secure Method for System Administrators
For system administrators managing servers remotely, EviSSH offers a secure and dependable solution for generating and handling SSH keys. This is crucial for maintaining secure remote connections.
EviSSH in Action: Practical Scenarios
Case Study: EviSSH with PassCypher HSM PGP
In environments where hardware security modules are crucial, EviSSH’s compatibility with PassCypher HSM PGP illustrates its ability to secure SSH keys effectively. Moreover, it demonstrates flexibility in providing security for SSH keys.
Case Study: EviSSH with EviKey HSM PGP
EviSSH’s seamless integration with EviKey HSM PGP allows users to physically secure their SSH keys. Furthermore, it offers state-of-the-art hardware protection.
FIDO-like Scenario for Corporate Server Access
Implementing Secure, Efficient Server Access
In a corporate context, EviSSH is employed to provide a secure and efficient server access method similar to FIDO. This process involves SSH key generation, secure key storage on EviKey NFC HSM, and a streamlined server authentication process, thus enhancing security and user experience.
Windows Server Authentication with EviSSH
Enhancing Security with SSH Key-Based Access
For bolstering Windows server security, EviSSH is used to set up SSH key-based authentication. This includes SSH key generation with EviSSH, public key deployment to the server, secure key storage on EviKey NFC HSM, and implementing SSH key-based authentication for secure access.
Secure Remote Command Execution on Windows
Automated Tasks with SSH Key Security
EviSSH enables secure, automated task execution on remote Windows machines. The process includes SSH key generation, public key deployment, creation of remote execution scripts, and task scheduling for secure and efficient remote system management.
EviSSH: Our Commitment to Evolving SSH Key Security
At Freemindtronic, we’ve developed EviSSH as a key technological component, constantly evolving to enhance SSH key security. Our focus is on optimizing both the security of SSH keys and improving user experience, making it more accessible, especially for those not well-versed in technology.
EviSSH simplifies the complexities involved in SSH key management. By integrating advanced technologies like EviKey NFC HSM, we provide a solution that balances enhanced security with ease of use. This synergy reflects our ongoing commitment to adaptive and innovative cybersecurity solutions.
Looking ahead, EviSSH is poised to adapt and evolve in response to the ever-changing challenges of cybersecurity. Our development roadmap promises to introduce enhanced features, further bolstering digital communication security. EviSSH, therefore, is not just a solution for current needs but a foundational element for future advancements in digital security.
In summary, at Freemindtronic, we see EviSSH as a significant leap forward in securing digital communications. As an evolving technological component, it plays a crucial role in simplifying SSH key management, making secure technology accessible to a broader audience.