Understanding why encrypt SMS is crucial in today’s cybersecurity landscape by Jacques Gascuel – This post in the Digital Security section highlights a cybersecurity wake-up call, addressing the growing cyber threats to government agencies and presenting solutions for secure communication. Updates will be provided as new information becomes available. Feel free to share your comments or suggestions.
Understanding why encrypt SMS is crucial in today’s cybersecurity landscape by Jacques Gascuel – This post in the Digital Security section highlights a cybersecurity wake-up call, addressing the growing cyber threats to government agencies and presenting solutions for secure communication. Updates will be provided as new information becomes available. Feel free to share your comments or suggestions.
Summary: Why Encrypt SMS Is Essential for Cybersecurity
The recent cyberattacks orchestrated by Salt Typhoon emphasize the vulnerabilities in telecom infrastructure, exposing sensitive government communications. This article explores these risks, highlights advanced threats targeting global telecom networks, and presents DataShielder NFC HSM Defense as a sovereign solution for regalian institutions.
Explore More Digital Security Insights
→ Discover related articles on cybersecurity threats, advanced solutions, and strategies to protect sensitive communications and critical systems.
Why Encrypt SMS? Understanding the Critical Flaws in MMS, and RCS Protocols
In 2024, telecom network vulnerabilities have become a major threat to both governmental and commercial communications. These weaknesses in protocols such as SS7 and Diameter highlight the urgency of addressing telecom vulnerabilities this year with robust encryption measures.
While SMS, MMS, and RCS remain widely used, their reliance on outdated and vulnerable protocols makes them prime targets for exploitation. The FBI and CISA identified the following key risks:
- Interception of Messages: Unencrypted SMS and MMS are transmitted in plaintext, making interception relatively easy for cybercriminals.
- SIM Swapping Attacks: Threat actors take control of victims’ phone numbers, granting them access to sensitive accounts secured by SMS-based two-factor authentication (2FA).
- Telecom Infrastructure Exploits: Weaknesses in protocols such as SS7, Diameter, and RCS allow adversaries to compromise entire networks, intercepting metadata, call records, and live communication streams.
IMSI Catchers: A Hidden Threat
IMSI catchers, also known as Stingrays, exploit weaknesses in telecom infrastructure to intercept unencrypted SMS and voice communications. Both Salt Typhoon and Flax Typhoon have used such methods to target sensitive government and corporate data. These attacks underscore why SMS encryption is no longer optional but a critical measure for safeguarding sensitive information.
Related Threats Protocols
Protocols like SS7, originally designed in the 1970s for 2G and 3G networks, were never built with modern security standards in mind. Vulnerabilities in SS7 and related protocols, including Diameter (4G/5G) and SIP (VoIP), further exacerbate the risks of telecom-based attacks.
📑 Explore SS7 vulnerabilities in detail:
- CISA 2025 Guidance: Why Encrypt SMS for Mobile Communication Security
- Why Encrypt SMS: A Crucial Step for Mobile Communication Security
- Summary: Why Encrypt SMS Is Essential for Cybersecurity
- Why Encrypt SMS? Understanding the Critical Flaws in MMS and RCS Protocols
- IMSI Catchers: A Hidden Threat
- Related Threats Protocols
- Salt Typhoon: The Scope of Cyberespionage
- Salt Typhoon: A Case Study in Telecom Exploitation
- Global Implications
- International Cooperation to Combat Telecom Threats
- Regulatory Responses to Salt Typhoon: FCC’s Call to Action
- Practical Steps to Secure Communication: Why Encrypt SMS Matters
- Why Secure Messaging Platforms Are Critical for Government Enterprises Under CISA Guidance
- Expanding Beyond SMS: Aligning with CISA for Universal Communication Encryption
- Why Choose DataShielder?
- Proactive Cybersecurity for Regalian Institutions
- A Sovereign Solution: DataShielder NFC HSM Defense
- Expanding Encryption: Universal Communication Protection
- How CISA Cybersecurity Guidance Supports Secure Messaging Platforms
- Best Tools for SMS Encryption in Government
- Related Threats Protocols
- Proactive Cybersecurity for Regalian Institutions
- Explore Official Reports and Recommendations
- DataShielder NFC HSM and HSM PGP: A Comprehensive Product Line for Strategic and Corporate Needs
- Dual Civilian and Military Applications
- Comparison Table: DataShielder NFC HSM Product Line
- CISA Cybersecurity Guidance for Mobile Communication Security
CISA 2025 Guidance: Importance of SMS Encryption
On December 3, 2024, the FBI and CISA, joined by global cybersecurity agencies, issued a stark warning about the vulnerabilities of unencrypted SMS, MMS, and RCS communications. Highlighting exploits by state-sponsored groups like Salt Typhoon, a Chinese cyberespionage campaign, the alert underscores the urgent need for end-to-end encryption to strengthen mobile communication security and protect sensitive government and institutional data. This alert emphasizes why encrypting SMS is no longer just a precaution but an essential strategy for safeguarding communications in a rapidly evolving cybersecurity landscape.
In this context, solutions such as DataShielder NFC HSM Defense are designed to offer sovereign-grade protection against the growing threats targeting mobile networks. With encryption methods tailored to protect both governmental and institutional communications, adopting these technologies is a crucial step in maintaining the confidentiality and integrity of sensitive data.
Updated CISA 2025 Guidance & Implications
The Cybersecurity and Infrastructure Security Agency (CISA) has updated its recommendations on mobile communication security in the November 2025 edition of the “Mobile Communications Best Practice Guidance.” Some key updates include:
- Strengthening the importance of E2EE (End-to-End Encryption) for all forms of messaging, including SMS, MMS, and RCS.
- Advising against the use of SMS for OTPs and 2FA due to ongoing exploitation risks.
- Advanced security practices for iOS and Android, such as enabling encrypted DNS, Lockdown Mode, and reviewing mobile app permissions.
These updated recommendations further emphasize the need for end-to-end encryption (E2EE) and sovereign-grade solutions like DataShielder NFC HSM, which provide robust protection against these emerging threats.
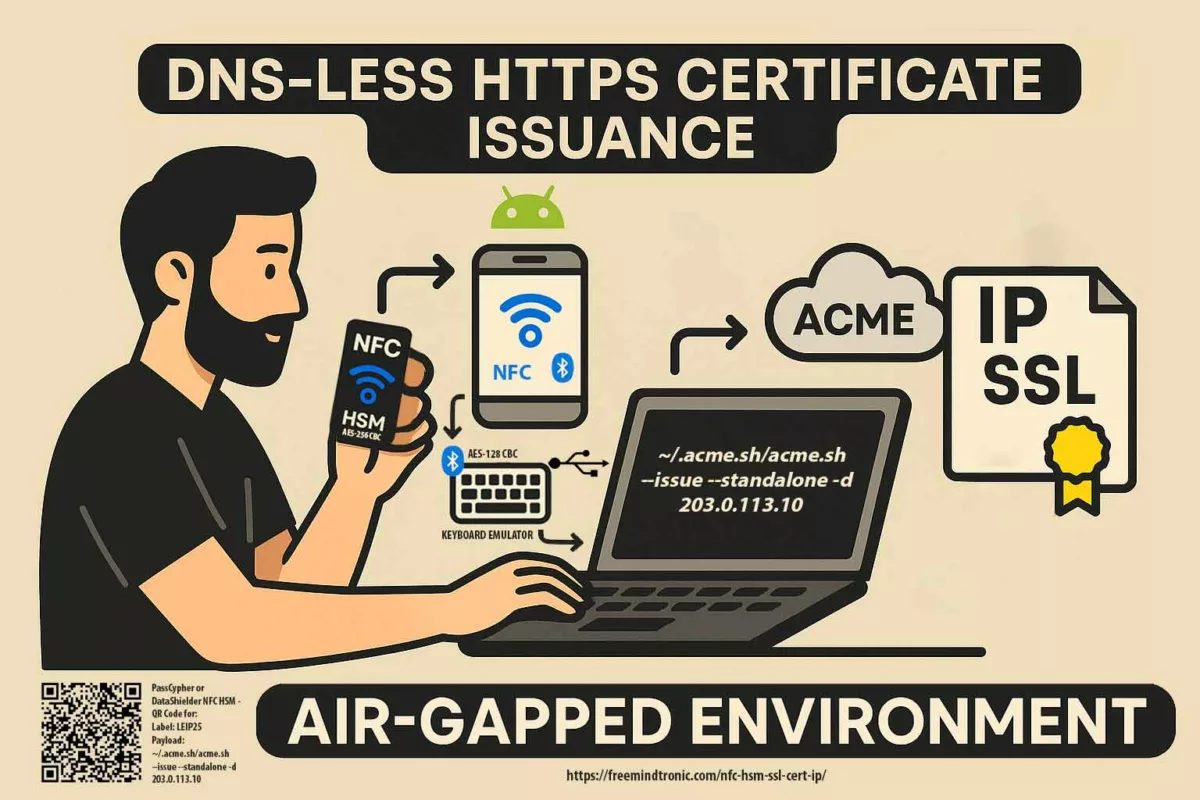
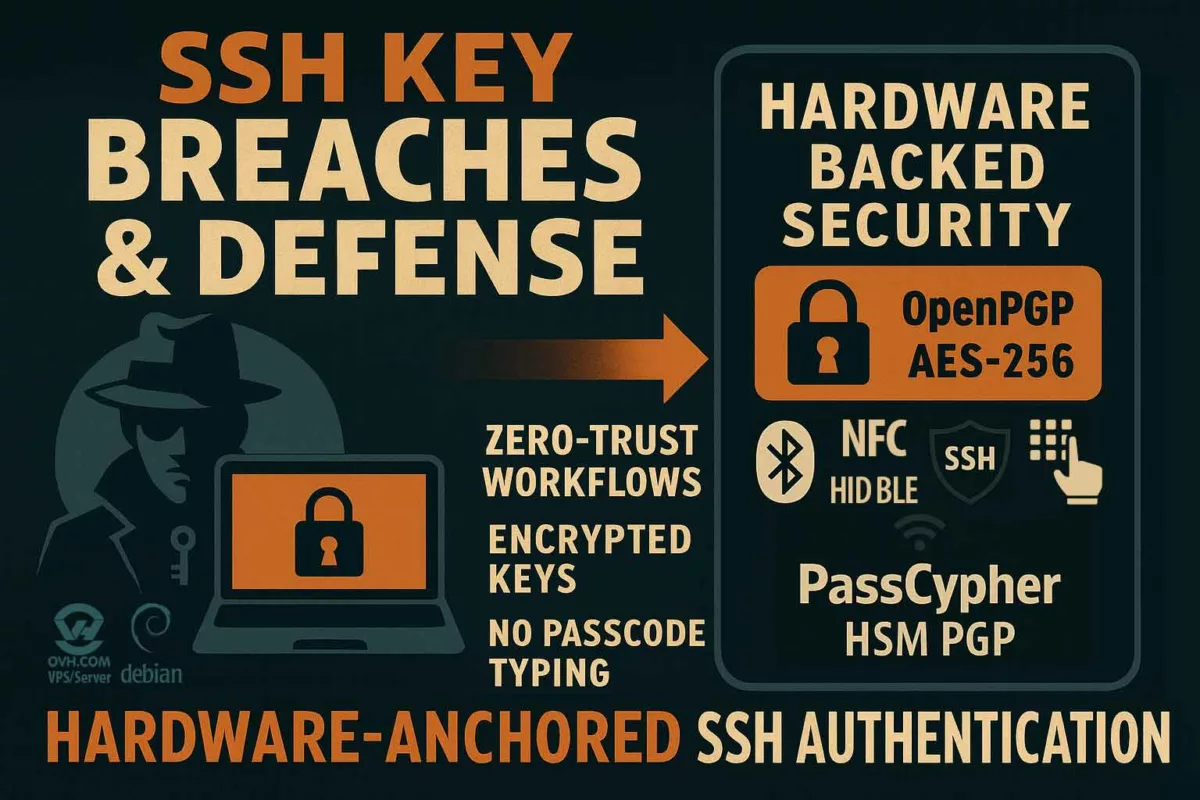
2026 Authentication Evolution: MFA Without SMS and Hardware Solutions
In line with this evolution, authorities now recommend phishing-resistant MFA solutions, excluding SMS and OTP via SMS as authentication mechanisms. This shift aligns with a broader trend towards more secure methods, such as FIDO2 and hardware keys, which offer enhanced resistance to phishing attacks and other cyber threats. Solutions like PassCypher HSM PGP and PassCypher NFC HSM stand out in this domain by offering robust, password-free authentication, completely offline and serverless. These tools are the ideal alternative to traditional MFA solutions based on SMS or OTP codes, which have been increasingly recognized as vulnerable.
Why Encrypt SMS: A Crucial Step in Mobile Communication Security
As noted by the FBI and CISA in their 2024 warning, unencrypted SMS, MMS, and RCS communications pose a significant risk, highlighting the necessity of encryption in securing mobile communications. The need to protect sensitive government and institutional communications from cyberespionage, especially by state-sponsored groups like Salt Typhoon, has made encryption an essential strategy rather than an option.
Understanding how telecom protocols, such as SS7 and Diameter, can be exploited by cybercriminals and state-sponsored actors is crucial for mitigating these risks. With sovereign-grade encryption solutions like DataShielder, organizations can protect sensitive communications and critical infrastructure globally, ensuring their integrity and confidentiality.
Unencrypted SMS, MMS, and RCS leave crucial gaps in mobile communication security. These gaps can be exploited to intercept and steal sensitive data. By adopting encryption methods, organizations can mitigate such risks, safeguarding against cybercriminals and other malicious actors. This makes encrypting SMS a critical element of any security strategy, ensuring data confidentiality and protecting sensitive information from interception.
📍 Learn from official sources:
Read the full article to understand the risks and the solutions that can help secure your communications. Share your thoughts and take action to protect your systems.
Updated CISA 2025 Guidance & Implications
La Cybersecurity and Infrastructure Security Agency (CISA) a mis à jour ses recommandations sur la sécurité des communications mobiles dans la version de novembre 2025 du “Mobile Communications Best Practice Guidance”. Parmi les évolutions importantes :
- Renforcement de l’importance de l’E2EE (chiffrement de bout en bout) pour toutes les formes de messagerie, incluant SMS, MMS, et RCS.
- Déconseil de l’utilisation de SMS pour les OTP et 2FA en raison des risques d’exploitation persistants.
- Pratiques de sécurité avancées pour iOS et Android, telles que l’activation du DNS chiffré, Lockdown Mode, et la révision des permissions pour les applications mobiles.
Ces nouvelles recommandations renforcent l’argument en faveur du chiffrement de bout en bout (E2EE) et des solutions souveraines comme DataShielder NFC HSM, qui offrent une protection robuste contre ces menaces.
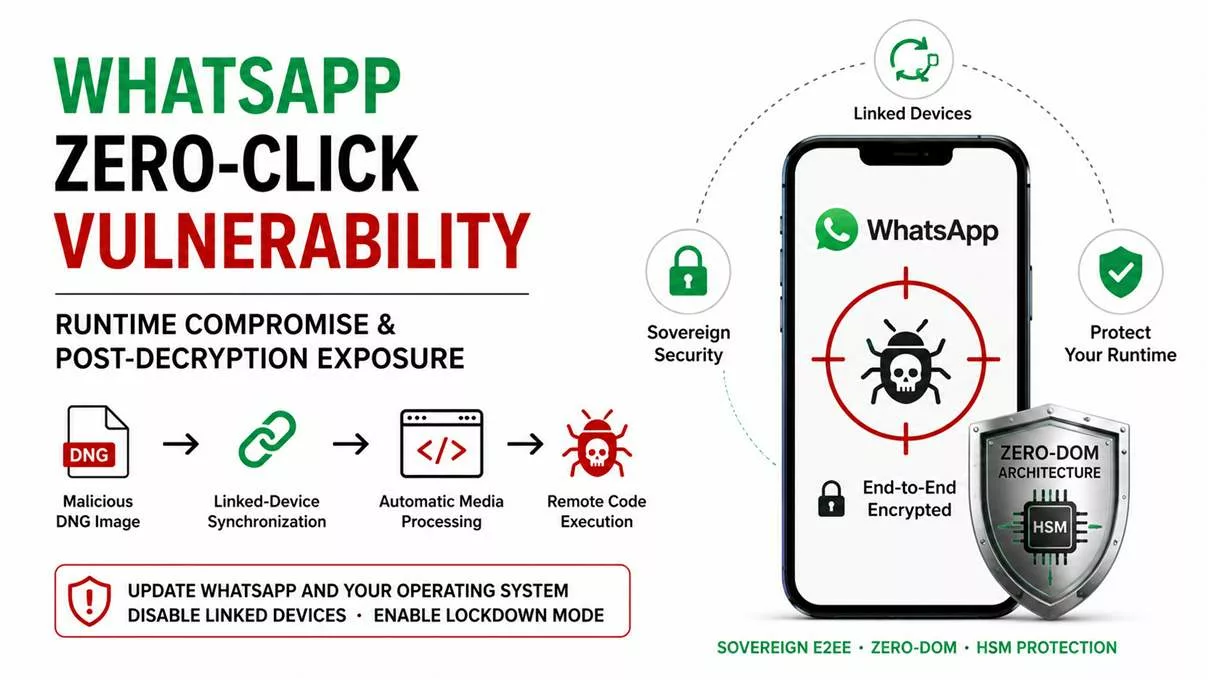
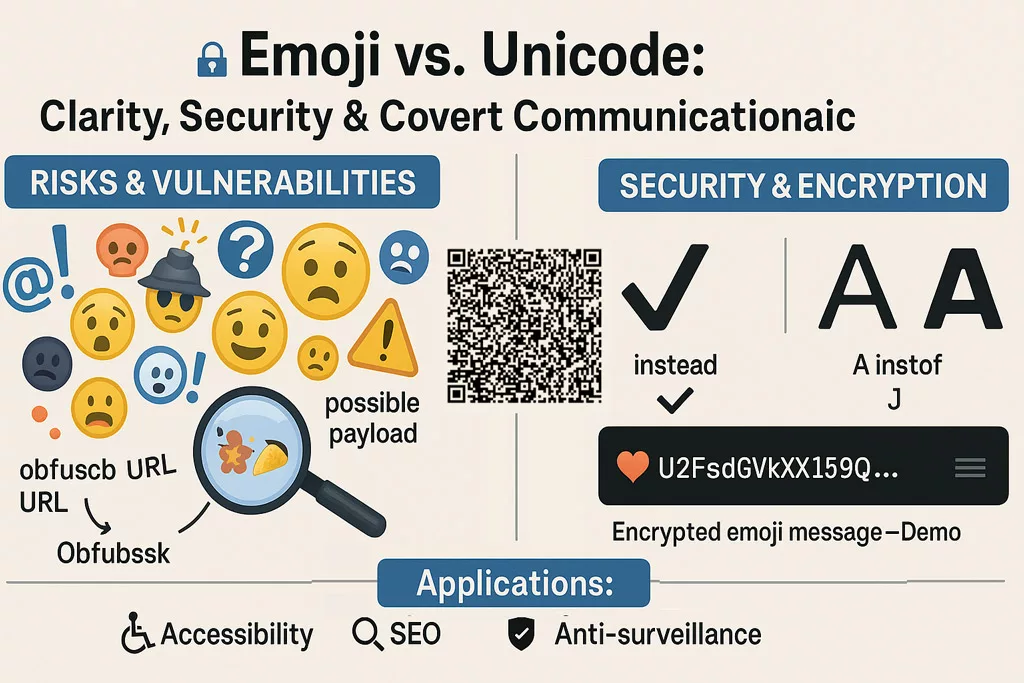
Spyware Risks on E2EE Platforms
Emerging threats now include the use of commercial spyware targeting encrypted messaging apps like Signal and WhatsApp. Cybercriminals exploit QR codes, linked devices, and other vectors to bypass encryption protections, highlighting the need for an additional layer of hardware-based security.
Solutions like PassCypher NFC HSM and DataShielder NFC HSM provide enhanced protection against these attacks by incorporating physical security mechanisms to ensure the integrity of exchanged data. These hardware-based solutions offer critical safeguards, making them indispensable in the battle against evolving cybersecurity threats.
CISA Cybersecurity Guidance: Why Encrypt SMS for Mobile Communication Security?
On December 3, 2024, the FBI and CISA, joined by global cybersecurity agencies, issued a stark warning about the vulnerabilities of unencrypted SMS, MMS, and RCS communications. Highlighting exploits by state-sponsored groups like Salt Typhoon, a Chinese cyberespionage campaign, the alert underscores the urgent need for end-to-end encryption to strengthen mobile communication security and protect sensitive government and institutional data. Understanding why encrypt SMS is essential helps organizations mitigate risks and enhance communication security. Learn how solutions like DataShielder NFC HSM Defense offer sovereign-grade security against these growing threats.
Why Encrypt SMS: A Crucial Step for Mobile Communication Security
On December 3, 2024, the FBI and CISA, joined by global cybersecurity agencies, issued a stark warning about the vulnerabilities of unencrypted SMS, MMS, and RCS communications. This highlights why encrypt SMS is no longer optional but a necessity for securing mobile communications. Highlighting cyberespionage by state-sponsored groups like Salt Typhoon, the alert underscores the necessity for encryption to protect sensitive government and institutional communications.
Discover how vulnerabilities in telecom protocols, from SS7 to Diameter, are exploited, and explore sovereign-grade encryption with DataShielder, solution designed to secure sensitive communications and critical infrastructure globally.
Unencrypted SMS, MMS, and RCS leave critical gaps in mobile communication security. This demonstrates why encrypt SMS is crucial for protecting sensitive data from interception and exploitation. Cybercriminals and state-sponsored actors can exploit these vulnerabilities to intercept sensitive information. By adopting encrypted communication methods, organizations can mitigate these risks, ensuring data integrity and confidentiality.
📍 Learn from official sources:
Read the full article to understand the risks and solutions. Share your thoughts and secure your communications.
Summary: Why Encrypt SMS Is Essential for Cybersecurity
The recent cyberattacks orchestrated by Salt Typhoon emphasize the vulnerabilities in telecom infrastructure, exposing sensitive government communications. This article explores these risks, highlights advanced threats targeting global telecom networks, and presents DataShielder NFC HSM Defense as a sovereign solution for regalian institutions.
Explore More Digital Security Insights
→ Discover related articles on cybersecurity threats, advanced solutions, and strategies to protect sensitive communications and critical systems.
Salt Typhoon: The Scope of Cyberespionage
Salt Typhoon’s impact on global telecom networks highlights the importance of securing sensitive data with sovereign-grade encryption solutions. The Salt Typhoon campaign demonstrates the global impact of cyberattacks on telecom networks. By targeting operators in the U.S., Europe, and other strategic regions, Salt Typhoon underscores the critical need for sovereign security solutions to protect sensitive communications worldwide.
State-Sponsored Cyber Attacks
Salt Typhoon, a Chinese state-affiliated group, exemplifies the modern-day cyberespionage threat. This group bypasses traditional endpoint security measures by directly targeting telecom infrastructure. Their tactics include:
- Exploiting Zero-Day Vulnerabilities: Leveraging unpatched software flaws in telecom systems to gain unauthorized access.
- Misconfiguration Exploits: Exploiting poorly configured core network components, enabling large-scale data extraction.
- Intercepting Call Detail Records (CDRs): Accessing metadata, live call data, and surveillance logs.
Salt Typhoon’s activities have compromised sensitive data involving high-ranking officials, security agencies, and critical businesses. The breach extends beyond the U.S., affecting telecom operators in France (SFR), Spain (Telefónica), and other global entities.
Global Implications
The breach highlights the structural vulnerabilities of international telecom networks. The PRC uses these intrusions to:
- Gather Strategic Intelligence: Inform military and economic policies.
- Undermine U.S. and Allied Credibility: Compromise allied infrastructure, including NATO and Five Eyes.
- Proliferate Cyber Tactics: Inspire other state-sponsored actors to replicate similar attacks.
These vulnerabilities underline the urgent need for coordinated international efforts to mitigate risks and safeguard sensitive communications.
International Cooperation to Combat Telecom Threats
The response to Salt Typhoon underscores the importance of global cooperation. Agencies from the Five Eyes alliance (USA, UK, Canada, Australia, and New Zealand) and European counterparts are actively working together to mitigate risks, share intelligence, and strengthen cybersecurity defenses globally.
Regulatory Responses to Salt Typhoon: FCC’s Call to Action
The Federal Communications Commission (FCC) has taken decisive steps to strengthen the resilience of telecommunications infrastructure following the Salt Typhoon cyberattack. This attack, confirmed on December 4, 2024, compromised sensitive systems in at least eight U.S. telecom companies and exposed vulnerabilities in critical infrastructure.
Key FCC Measures:
- Cybersecurity Obligations:
- Telecommunications carriers must comply with Section 105 of the Communications Assistance for Law Enforcement Act (CALEA) to secure their networks.
- Legal obligations extend beyond equipment to include network management practices.
- Compliance Framework:
- Annual certification for cybersecurity risk management plans.
- Expanded obligations for all communications providers to implement robust security measures.
- National Security Focus:
- Recognizing the critical role of telecom networks in defense, public safety, and economic systems, the FCC’s actions aim to build resilience against future cyberattacks.
📍 Read the FCC Fact Sheet for more details:
Salt Typhoon: A Case Study in Telecom Exploitation
The Salt Typhoon attack is a stark reminder of how state-sponsored actors bypass traditional security measures to target telecom infrastructure directly. Operating under the guise of Earth Estries—a Chinese cyberespionage group—their tactics reveal a sophisticated approach to large-scale data theft and network manipulation.
Salt Typhoon Tactics and Techniques:
- Zero-Day Exploits:
- Unpatched vulnerabilities in core telecom systems.
- Misconfigurations:
- Exploiting poorly configured network components to gain unauthorized access.
- Interception of Call Detail Records (CDRs):
- Accessing metadata, live communications, and surveillance logs without targeting individual devices.
Global Implications of Salt Typhoon Attacks:
Salt Typhoon has impacted major telecom operators globally, including:
- U.S. carriers (AT&T, Verizon, T-Mobile).
- European providers like SFR (France) and Telefónica (Spain).
Telecom protocols like SS7 and Diameter, though foundational to mobile communication, are plagued by vulnerabilities that open the door to cyber espionage. We will discuss by following how these weaknesses are exploited and why it is essential to address them.
Protocol Vulnerabilities: A Gateway for Cyber Espionage
While Salt Typhoon focuses on telecom infrastructure, vulnerabilities in SS7, Diameter, and related protocols serve as entry points for cyber adversaries.
Understanding the risks associated with outdated and vulnerable telecom protocols like SS7, Diameter, and RCS is essential for safeguarding mobile communication infrastructure.
Key Protocol Risks
- SS7 (Signaling System 7):
- Designed for 2G/3G networks, SS7 was never intended for secure communication, making it vulnerable to message interception and location tracking.
- Diameter Protocol:
- Used in 4G/5G networks, Diameter faces similar risks, including denial-of-service attacks and message tampering.
- RCS (Rich Communication Services):
- A modern SMS replacement, RCS still lacks robust encryption, leaving it open to interception and spoofing.
📑 Learn more about SS7 vulnerabilities:
IMSI catchers, or Stingrays, pose a critical threat by intercepting mobile communications through deception. Learn how these devices are leveraged by cyber adversaries to compromise sensitive data.
IMSI Catchers: A Gateway for Mobile Communication Interception
IMSI catchers, also known as Stingrays, are devices used to intercept mobile communications by mimicking legitimate cell towers. These tools are commonly employed by state-sponsored actors, such as Salt Typhoon and Flax Typhoon, to capture sensitive data, including SMS, calls, and metadata.
To learn more about IMSI catchers and their impact on mobile communication security, consult this detailed explanation provided by the Electronic Frontier Foundation (EFF).
Practical Steps to Secure Communication: Why Encrypt SMS Matters
One of the first steps to achieve this is to understand why encrypt SMS is a priority in cybersecurity strategies. Here’s how organizations and individuals can enhance their security posture, particularly around telecom network vulnerabilities in 2024 and the risks associated with unencrypted messaging:
- Adopt Encrypted Messaging Platforms
Leverage secure apps like Signal or Telegram, which provide end-to-end encryption to ensure the confidentiality of your communications. - Implement Secure Hardware Solutions
Utilize hardware-based tools such as the DataShielder NFC HSM Defense for sovereign-grade encryption. These solutions are specifically designed to protect against threats like Salt Typhoon and ensure data integrity. - Conduct Regular Audits
Evaluate and update telecom protocols such as SS7 and Diameter to address potential vulnerabilities. Auditing ensures that your systems stay ahead of evolving cyber risks. - Leverage International Guidelines
Follow frameworks and recommendations from global cybersecurity organizations, including CISA and FCC, to strengthen your defenses. These guidelines provide actionable steps to safeguard your communication infrastructure. - Use Multi-Factor Authentication (MFA)
Combine encrypted platforms with MFA to add an extra layer of security, mitigating the risks of SIM-swapping attacks and unauthorized access. - Train Employees on Cybersecurity Awareness
Educate staff on recognizing phishing attempts and other cyber threats. Awareness is a crucial defense against insider and external threats. - Perform Penetration Testing
Conduct regular penetration tests to uncover weaknesses in your telecom infrastructure. This proactive approach ensures that vulnerabilities are identified and resolved before they are exploited.
The answer is clear: unencrypted SMS, MMS, and RCS leave organizations exposed to interception and exploitation. Tools like DataShielder NFC HSM Defense and secure practices such as those outlined above provide critical safeguards against global telecom threats and state-sponsored cyberattacks.
Why Encrypt SMS Best Tools for SMS Encryption in Government
Securing SMS communications for government institutions and enterprises is no longer optional—it is essential to safeguard sensitive exchanges. Why encrypt SMS? Unencrypted messages remain vulnerable to interception and cyberattacks, making encryption a critical component of modern cybersecurity strategies. Among the top solutions available is the DataShielder NFC HSM Defense, tailored to meet the highest standards for sovereign entities and highly sensitive government communications:
- Hybrid Encryption (AES-256 CBC): Ensures all data is encrypted locally before transmission.
- Cross-Platform Compatibility: Works seamlessly with Android NFC devices, ensuring secure communication across various platforms.
- Offline Functionality: Eliminates the risk of internet-based vulnerabilities, providing unmatched security.
Why Encrypt SMS to Prevent Data Breaches?
Why encrypt SMS? Enterprises classified as ultra-sensitive or of national interest must protect their communications to prevent data breaches and safeguard operational security. Freemindtronic offers the DataShielder NFC HSM Master, a double-use version specifically designed to meet these rigorous demands:
- DataShielder NFC HSM Master: Balances enterprise flexibility with sovereign-grade encryption, making it ideal for strategic organizations working closely with government entities. This solution ensures data confidentiality, integrity, and accessibility.
Encryption Solutions for All Enterprises
For other businesses seeking advanced yet versatile encryption solutions, the DataShielder NFC HSM Lite and its complementary modules offer powerful data protection in a double-use capacity. These versions ensure comprehensive security without compromising accessibility:
- DataShielder NFC HSM Lite: Designed for enterprises needing reliable encryption for communication and data protection.
- DataShielder NFC HSM Auth: Provides authentication alongside encryption for streamlined security management.
- DataShielder NFC HSM M-Auth: Facilitates multi-authentication scenarios, ensuring secure access across distributed teams.
For businesses that require desktop-based encryption compatible with NFC HSM modules, Freemindtronic also offers the DataShielder PGP HSM Data Encryption. This solution extends protection to computers, ensuring comprehensive data security.
Regalian Security Through Sovereign Solutions
To address these vulnerabilities, DataShielder NFC HSM Defense offers a sovereign-grade encryption tool for regalian institutions, government agencies, and enterprises.
How DataShielder NFC HSM Defense Protects Communications:
Hybrid Encryption (AES-256 CBC):
- Encrypts data locally before transmission, ensuring total protection.
Cross-Platform Compatibility:
- Works with all Android NFC devices (version 6+), including:
- Fairphone (Netherlands).
- Shiftphone (Germany).
- Sonim Technologies (USA).
- Crosscall (France).
- Bullitt Group (UK).
Future-Ready Encryption:
- Secures current and emerging communication platforms, including SMS, MMS, RCS, and satellite messaging.
Sovereign Manufacturing
Built in France (Syselec) and Andorra (Freemindtronic SL), DataShielder is developed using STMicroelectronics components to meet the highest security standards.
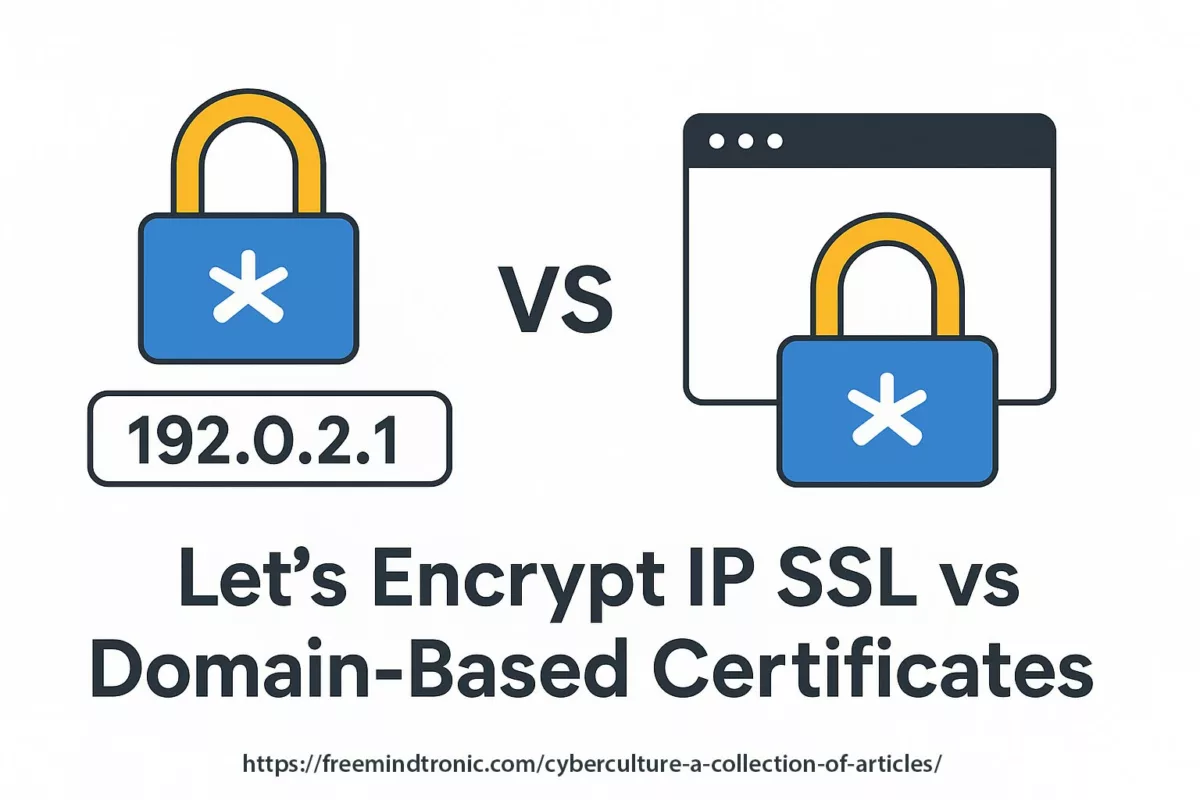
Expanding Beyond SMS: Aligning with CISA for Universal Communication Encryption
The sovereign-grade encryption with DataShielder secures more than just SMS. It acts as a comprehensive encryption tool for:
- MMS, RCS, and Email: Encrypts messages and attachments.
- Instant Messaging: Secures full platforms like Signal, Telegram, WhatsApp, LinkedIn…
- File Transfers: Encrypts sensitive documents prior to sharing.
- Satellite Messaging: Extends protection to off-grid communication.
By encrypting data at the source, DataShielder ensures that even intercepted messages are unreadable to adversaries.
Why Choose DataShielder?
By incorporating solutions like DataShielder NFC HSM Defense, government entities, strategic enterprises, and businesses of all sizes can mitigate risks associated with unencrypted communications. Whether addressing Why encrypt SMS? or securing data across platforms, DataShielder offers scalable and tailored solutions to meet diverse security needs.
- Complete Offline Operation: Functions without internet, eliminating server-based vulnerabilities.
- Segmented Key Authentication: Patented technology ensures unmatched encryption trust.
- Proven Sovereignty: Designed and manufactured in Europe using defense-grade components.
Proactive Cybersecurity for Regalian Institutions
The Salt Typhoon cyberattack and its associated vulnerabilities underscore the urgent need for robust, proactive measures to safeguard critical communications in the regalian sector. In December 2024, the Cybersecurity and Infrastructure Security Agency (CISA) published its Mobile Communications Best Practices Guidance to address these pressing challenges. These recommendations align seamlessly with the core principles of secure communication solutions like DataShielder NFC HSM Defense, designed to meet the highest standards for protecting sensitive government and enterprise communications.
Key Highlights from CISA’s Guidance
- Adopt End-to-End Encryption: Transition to secure messaging platforms like Signal to ensure all communications remain private and protected.
- Phishing-Resistant Authentication: Replace SMS-based MFA with FIDO security keys for maximum resilience against cyberattacks.
- Platform-Specific Recommendations:
- iPhone: Enable Lockdown Mode and utilize encrypted DNS services like Cloudflare’s 1.1.1.1 Resolver.
- Android: Prioritize devices with secure hardware features and enable Private DNS for enhanced protection.
By adopting solutions that align with the CISA Cybersecurity Guidance, such as DataShielder NFC HSM Defense, organizations can enhance their mobile communication security while mitigating the growing threats identified by global cybersecurity agencies, including the FBI and CISA.
These best practices not only emphasize the importance of secure communications but also highlight the critical need for solutions that integrate these principles effectively, such as DataShielder NFC HSM Defense.
Why Secure Messaging Platforms Are Critical for Government Enterprises Under CISA Guidance
- End-to-End Encryption: The CISA guidance emphasizes the need for encrypted messaging platforms to secure sensitive communications—an area where DataShielder NFC HSM Defense excels with its AES-256 encryption.
- Phishing-Resistant Authentication: Transitioning away from SMS-based MFA aligns with the Zero Trust framework of DataShielder, which ensures offline security and eliminates internet-based vulnerabilities.
- Platform Compatibility: DataShielder’s seamless integration with Android NFC devices addresses the secure hardware requirements outlined in the CISA guidance, ensuring protection across modern communication platforms.
Building on the importance of secure messaging platforms, the recent CISA Cybersecurity Guidance highlights actionable recommendations to strengthen mobile communication security. Here’s how DataShielder NFC HSM Defense aligns with these guidelines:
How CISA Cybersecurity Guidance Supports Secure Messaging Platforms
The newly released CISA Cybersecurity Guidance for Mobile Communication Security emphasizes the importance of robust measures such as end-to-end encryption, phishing-resistant MFA, and platform-specific security features to combat evolving cyber threats. These recommendations align seamlessly with DataShielder NFC HSM Defense, which provides sovereign-grade security tailored to meet these exact needs. Here’s how:
| CISA Recommendation | How DataShielder NFC HSM Defense Aligns |
|---|---|
| End-to-End Encryption | Implements AES-256 CBC encryption to secure sensitive communications locally before transmission. |
| Phishing-Resistant MFA | Integrates Zero Trust architecture, replacing vulnerable SMS-based MFA with secure offline authentication. |
| Offline Functionality | Operates entirely offline, eliminating internet-based vulnerabilities. |
| Platform-Specific Compatibility | Fully compatible with Android NFC devices and supports encrypted DNS, meeting CISA’s security criteria. |
| Sovereign Manufacturing | Designed and manufactured in Europe with STMicroelectronics components for ultimate trust and reliability. |
By choosing DataShielder NFC HSM Defense, organizations gain a cutting-edge solution aligned with the best practices outlined by CISA.
Explore Official Reports and Recommendations
CISA Guidance: Practical Solutions for Today’s Threats
📤 Download the full CISA Mobile Communications Best Practices Guidance (PDF)
Explore how these recommendations align with sovereign-grade security solutions like DataShielder NFC HSM Defense, providing unmatched protection for critical communications.
- CISA Mobile Communications Best Practices Guidance
- FBI-CISA Joint Statement on PRC Cyberespionage
- CISA Enhanced Visibility and Hardening Guidance
- FCC Fact Sheet on Salt Typhoon
- Salt Typhoon Cyber Threats
- 5Ghoul: 5G Vulnerabilities
DataShielder NFC HSM and HSM PGP: A Comprehensive Product Line for Strategic and Corporate Needs
In an era where robust security is paramount, the DataShielder NFC HSM and HSM PGP product line offers versatile solutions tailored for a range of applications—from civilian to military, and enterprise to sovereign institutions. Explore how these innovative tools provide unmatched protection for sensitive data and communications.
Product Highlights
- DataShielder NFC HSM Master
A flagship product designed for the most demanding security requirements. Perfect for:- Sovereign institutions: Encrypting highly sensitive data.
- Strategic enterprises: Securing internal communications.
📍 Key Features:
- Hybrid encryption with AES-256 CBC.
- Advanced key management with Android NFC compatibility.
- Fully offline functionality to eliminate internet vulnerabilities.
➡️ Learn more
- DataShielder NFC HSM Lite
A lightweight yet powerful solution for businesses requiring accessible yet robust security.
📍 Ideal for:- SMEs and startups seeking cost-effective security.
- Sectors requiring localized control over sensitive data.
➡️ Discover the details
- DataShielder NFC HSM Auth and M-Auth
- NFC HSM Auth: Tailored for secure authentication and basic encryption.
- NFC HSM M-Auth: Advanced multi-authentication, ideal for:
- Decentralized teams.
- Segmented access with fine-tuned permission management.
- Dynamic AES-256 CBC key replacement via RSA 4096 encrypted key sharing.
➡️ Explore NFC HSM Auth
➡️ Explore NFC HSM M-Auth
- DataShielder NFC HSM Defense
📍 Exclusive Features:- Externalized contact management via NFC HSM: Make calls or send SMS, MMS, and RCS messages directly from the NFC HSM.
- Automatic deletion of call history and messages from the phone after use.
📍 Target Audience:
- Defense, government institutions, and industries requiring unmatched security for communications and data.
➡️ Learn more
- DataShielder Starter Kit
An all-in-one solution to introduce enterprises to the DataShielder ecosystem.
📍 Includes:- NFC HSM Lite for a seamless start.
- Comprehensive user guide and support.
➡️ View the Starter Kit
- DataShielder HSM PGP Data Encryption
Designed for dual civilian and military use, offering robust encryption for:- Multinational enterprises: Protecting sensitive data during cross-border exchanges.
- Military applications: Securing strategic communications.
➡️ Discover HSM PGP
Dual Civilian and Military Applications
DataShielder products are engineered to address diverse security needs:
- Civilian Use: Protecting digital assets, intellectual property, and sensitive communications for businesses.
- Military Use: Sovereign-grade security aligned with national and international defense standards.
Comparison Table: DataShielder NFC HSM Product Line
| Product | Usage | Key Features | Link |
|---|---|---|---|
| NFC HSM Master | Sovereign and strategic | AES-256 CBC, offline, advanced trust criteria, fleet management, NFC | Learn more |
| NFC HSM Lite | SMEs and startups | AES-256 CBC encryption, streamlined interface, essential security features | Learn more |
| NFC HSM Auth | Authentication and encryption | Identity protection + SMS, MMS, RCS encryption | Learn more |
| NFC HSM M-Auth | Multi-authentication scenarios | Dynamic AES-256 CBC key replacement via RSA 4096 encrypted key sharing | Learn more |
| NFC HSM Defense | Sovereign, defense, military | Externalized contact management, secure calls and SMS/MMS/RCS, automatic call/message log deletion | Learn more |
| Starter Kit | Cost-effective enterprise security | NFC HSM Lite + second module for key personnel | Learn more |
| HSM PGP Data Encryption | Dual-use civil/military | PGP encryption, offline operation, tailored for strategic communications | Learn more |
CISA Cybersecurity Guidance for Mobile Communication Security
The vulnerabilities in telecom networks and the global impact of cyberattacks like Salt Typhoon highlight the importance of adopting secure, sovereign-grade solutions. DataShielder NFC HSM Defense provides a trusted, scalable option for regalian institutions and strategic enterprises, offering unmatched protection in alignment with global best practices.
📍Don’t wait for vulnerabilities to be exploited. Secure your organization’s mobile communication today with DataShielder, the sovereign-grade encryption solution trusted for its alignment with CISA cybersecurity recommendations. Contact us for a personalized quote.
Secure your organization’s mobile communication today with DataShielder, the sovereign-grade encryption solution trusted for its alignment with CISA cybersecurity recommendations.
Best Practices Techniques (2025)
En complément du chiffrement de bout en bout, CISA recommande plusieurs pratiques avancées pour sécuriser les appareils mobiles :
- DNS Chiffré: Utilisation du DNS chiffré pour éviter les attaques de type Man-in-the-Middle.
- Lockdown Mode: Activation de ce mode pour restreindre l’accès aux applications et services critiques.
- Revue des Permissions: Revoir et limiter les permissions des applications pour minimiser les risques.
Ces pratiques doivent être accompagnées de solutions de chiffrement robustes comme DataShielder NFC HSM pour garantir une protection maximale.