Silent Whisper espionnage WhatsApp Signal est présenté comme une méthode gratuite permettant d’espionner des communications chiffrées. Cette chronique de sécurité numérique déconstruit cette affirmation à partir de limites cryptographiques irréversibles, identifie les zones de non-action, et fixe un point d’arrêt souverain fondé sur la responsabilité technique et juridique.
Résumé express — Silent Whisper et le mythe de l’espionnage WhatsApp et Signal
Le récit
Silent Whisper circule comme un outil gratuit d’espionnage WhatsApp et Signal, prétendument capable d’accéder à des messages chiffrés sans accès au téléphone ciblé, sans interaction utilisateur et sans trace visible.
La limite irréversible
Le chiffrement de bout en bout repose sur une décision d’architecture : les clés de déchiffrement sont générées et conservées localement sur le terminal. Cette limite est cryptographique et matérielle, non logicielle et non contournable à distance.
Zone de non-action
Ne pas agir est ici la seule action souveraine. Télécharger, tester ou exécuter un tel outil suffit à transférer le risque vers l’utilisateur, par malware, phishing ou vol d’identifiants.
Responsabilité éditoriale
Cette analyse est publiée sous la responsabilité de Freemindtronic. Elle n’encourage aucune expérimentation, aucune “preuve par test”, et n’externalise aucune décision critique vers des outils ou automatismes.
Si un outil promet d’espionner WhatsApp ou Signal sans accès physique au terminal, toute action supplémentaire augmente irréversiblement le dommage potentiel.
Paramètres de lecture
Résumé express : ≈ 1 min
Résumé avancé : ≈ 4 min
Chronique complète : ≈ 40 min
Date de publication : 2026-01-05
Dernière mise à jour : 2026-01-05
Niveau de complexité : Doctrinal & cybersécurité
Densité technique : ≈ 72 %
Langues disponibles : FR · EN · ES · CAT · AR
Focalisation thématique : Sécurité numérique, cryptographie, mythes de surveillance, souveraineté cognitive
Format éditorial : Chronique — série Freemindtronic Digital Security
Niveau d’impact stratégique : 8,1 / 10 — épistémologique et opérationnel
Résumé avancé — Espionnage WhatsApp Signal, limites techniques et inversion de la menace
Silent Whisper appartient à une catégorie récurrente de récits promettant l’accès universel à des communications chiffrées. Or, le chiffrement de bout en bout élimine précisément cette possibilité. Le réseau, les serveurs et les intermédiaires ne disposent jamais des clés nécessaires à la lecture.
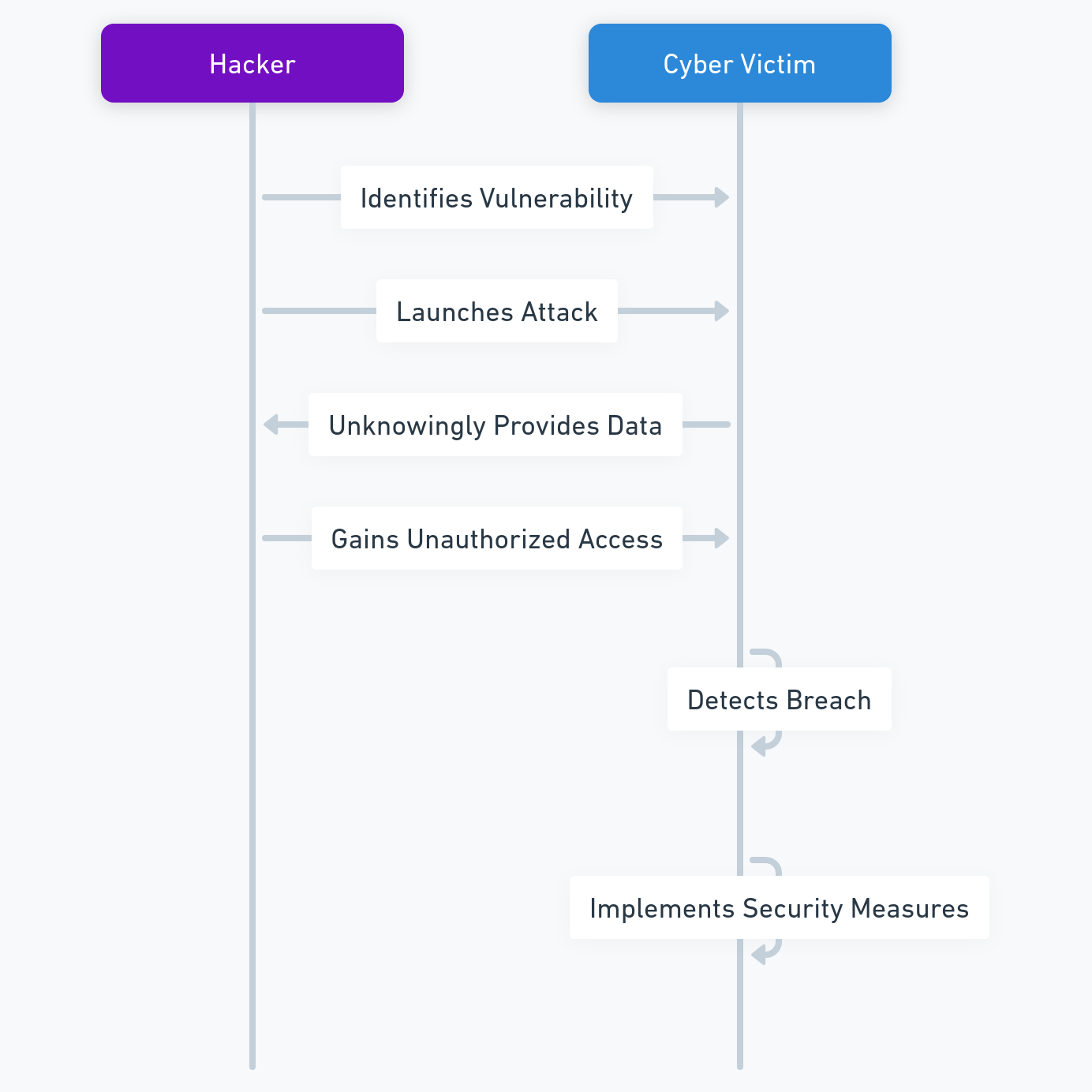
Toute tentative crédible passe donc par le terminal : compromission du système, ingénierie sociale, vol d’identifiants ou installation de code malveillant. Cette réalité inverse la menace : l’attaquant potentiel devient la cible.
Points structurants
- La limite est cryptographique et intentionnelle, non logicielle.
- Un logiciel distant ne peut outrepasser une clé locale.
- Le risque principal est l’auto-compromission.
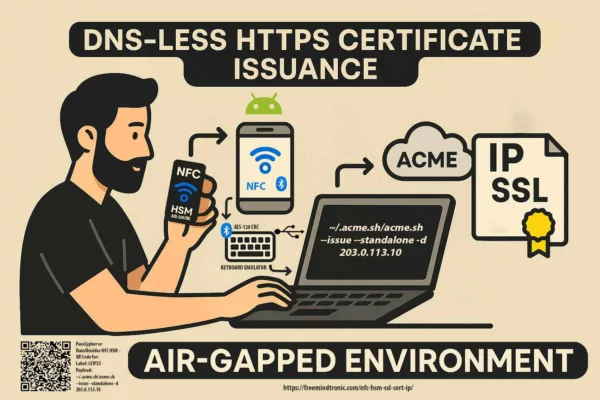
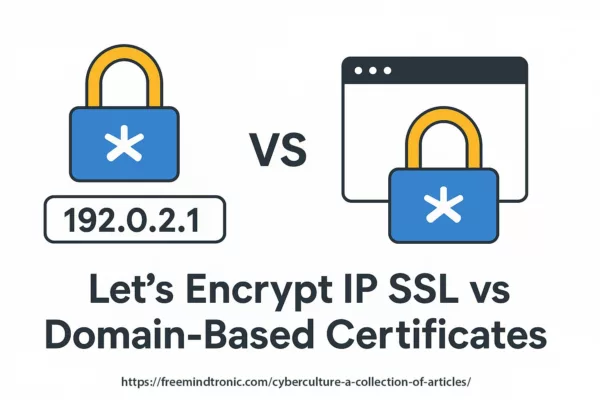
Les chroniques affichées ci-dessus ↑ appartiennent à la même série éditoriale Digital Security. Elles prolongent l’analyse des limites techniques de la sécurité numérique et des récits de surveillance en confrontant le promesses virales aux réalités cryptographiques, aux contraintes des terminaux et aux conditions d’arrêt souveraines. Cette sélection complète la présente chronique dédiée à Silent Whisper espionnage WhatsApp Signal — un cas typique de mythe opérationnel qui transforme la curiosité en vecteur de compromission.
- 🔝 Retour en haut
- Résumé express
- Résumé avancé
- Chronique — Silent Whisper et l’espionnage WhatsApp Signal décryptés
- Zones de non-action face aux récits d’espionnage WhatsApp et Signal
- Origine du mythe Silent Whisper
- Historique technique et documentation scientifique
- Posture souveraine face aux mythes de surveillance
- Découverte du mécanisme réel et confusion terminologique
- Chronologie des faits et dérive du récit public
- Métadonnées, messageries chiffrées et Silent Whisper
- Dérive médiatique autour de l’espionnage WhatsApp et Signal
- Réactions des éditeurs et correctifs partiels
- Limites irréversibles de l’espionnage WhatsApp et Signal
- Distinction logiciel / décision matérielle
- Perspective non automatisable
- Espionnage WhatsApp Signal : usages abusifs et cybervictimes réelles
- Métadonnées et Silent Whisper : vecteurs cyber indirects
- Métadonnées des messageries chiffrées face à l’architecture EviLink
- Limites structurelles des métadonnées des messageries
- Architecture EviLink et rupture de corrélation
- Pourquoi Silent Whisper est inopérant avec EviLink
- Posture doctrinale sur les métadonnées
- Responsabilité humaine face à la surveillance WhatsApp et Signal
- Impact réel — Technique, cognitif et juridique
- Perspective stratégique du Silent Whisper Espionnage
Chronique — Silent Whisper et l’espionnage WhatsApp Signal décryptés
Cette chronique examine le récit « Silent Whisper » non comme un outil, mais comme un objet informationnel révélateur d’un malentendu persistant autour du chiffrement de bout en bout. L’objectif n’est pas de réfuter une rumeur par dénigrement, mais de replacer les faits techniques, scientifiques et humains dans leur cadre réel.
En analysant successivement l’origine académique du mécanisme, sa transformation médiatique, ses usages abusifs et ses impacts cognitifs, cette chronique établit un point d’arrêt clair : aucune interception silencieuse à distance des messages WhatsApp ou Signal n’est techniquement possible sans compromission du terminal.
Ce décryptage repose sur des limites irréversibles, des zones de non-action assumées et une responsabilité éditoriale explicite. Il s’adresse à ceux qui cherchent à comprendre, non à exploiter.
Zones de non-action face aux récits d’espionnage WhatsApp et Signal
Lorsqu’un outil promet une capacité d’espionnage “silencieuse” et “à distance”, toute action technique supplémentaire est déconseillée. L’inaction protège l’intégrité des preuves, la sécurité du terminal et la responsabilité juridique.
Avant d’analyser les mécanismes techniques et les dérives médiatiques associées à Silent Whisper, il est nécessaire de comprendre comment ce récit est apparu, par qui il a été formulé, et à quel moment une recherche scientifique limitée a été transformée en promesse d’espionnage généralisé. Cette mise en perspective permet de distinguer l’origine factuelle du phénomène de son amplification narrative.
Origine du mythe Silent Whisper
Historique technique et documentation scientifique
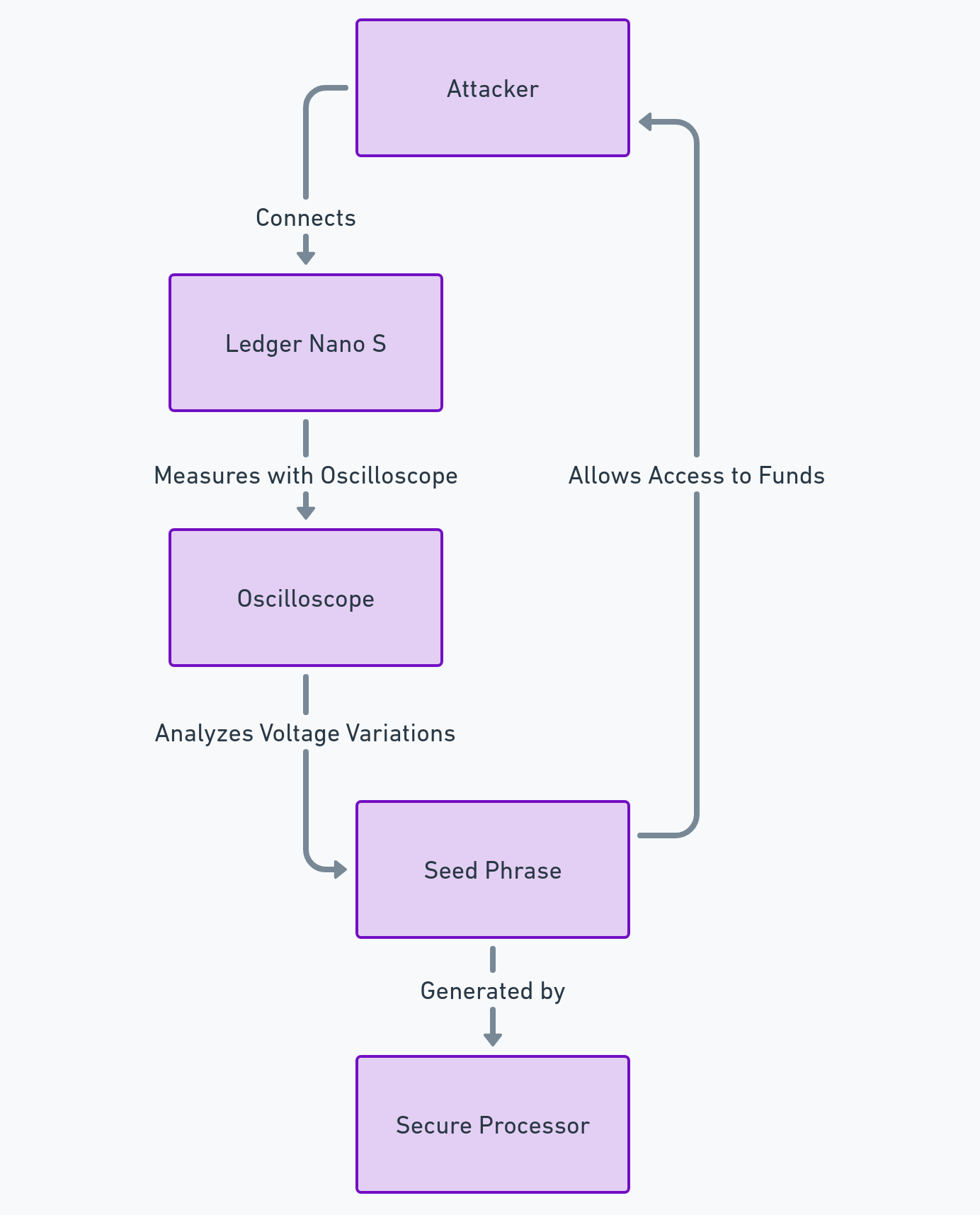
Des chercheurs en sécurité informatique de l’Université de Vienne et de SBA Research ont documenté une technique applicable à WhatsApp et Signal montrant comment des accusés de réception silencieux peuvent être utilisés pour surveiller l’état d’un terminal (écran, activité réseau, nombre de dispositifs) sans alerte visible de la cible. Cette recherche, distinguée au RAID 2025, constitue la base scientifique souvent mal interprétée du terme “Silent Whisper”.
Ces travaux sont formalisés dans une publication académique évaluée par les pairs, intitulée “Careless Whisper: Exploiting Stealthy End-to-End Leakage in Mobile Instant Messengers”, disponible sur la plateforme scientifique arXiv : https://arxiv.org/abs/2411.11194
.
Cette étude constitue la référence primaire souvent invoquée — et fréquemment mal interprétée — à l’origine du récit médiatique autour de « Silent Whisper ».
Les travaux académiques à l’origine de cette analyse ont été présentés dans des cadres scientifiques reconnus, notamment lors de conférences spécialisées en sécurité des systèmes et réseaux, et sont accessibles via des archives de prépublication académique.
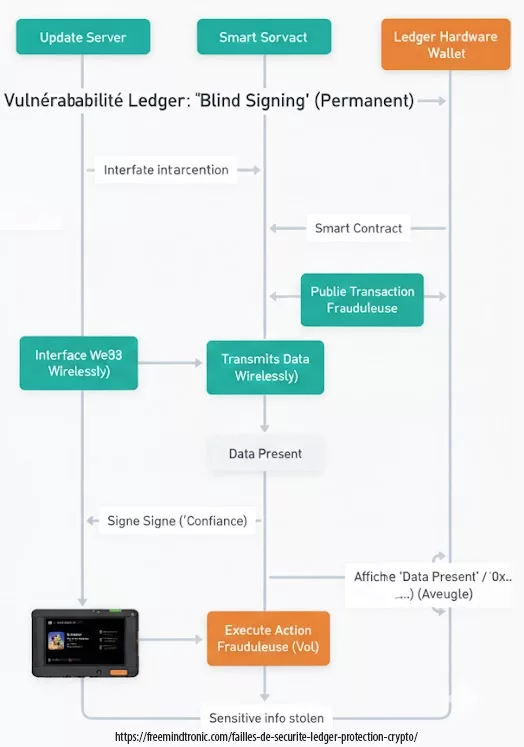
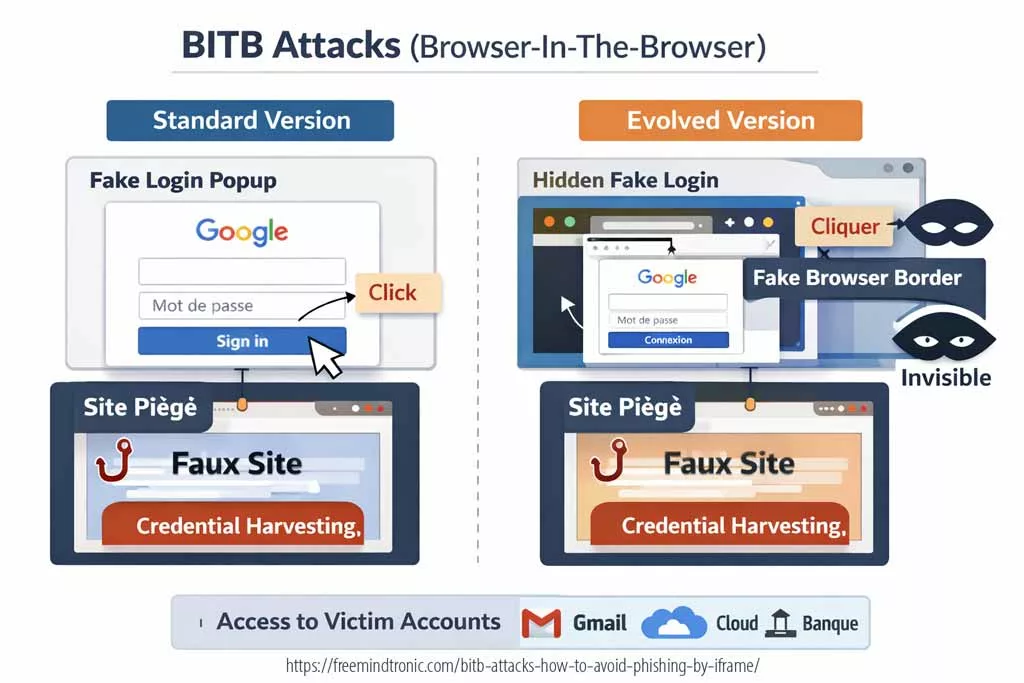
Cette approche n’est pas une compromission du chiffrement des messages, mais une exploitation d’un canal auxiliaire de timing, qui révèle des métadonnées comportementales exploitables depuis un simple numéro de téléphone.
Posture souveraine face aux mythes de surveillance
Face à des récits comme Silent Whisper, la réponse pertinente n’est ni un outil supplémentaire ni une manipulation technique. Elle relève d’une posture souveraine, c’est-à-dire d’une manière d’interpréter, de refuser et de poser des limites avant toute action.
Cette posture repose sur trois piliers indissociables. D’abord, la vigilance sur les métadonnées : comprendre que l’absence d’accès au contenu ne signifie pas absence totale d’observation. Ensuite, la compréhension des limites : reconnaître qu’une frontière cryptographique existe, qu’elle est intentionnelle, et qu’elle ne doit ni être niée ni “testée”. Enfin, le refus explicite des promesses magiques : toute affirmation de surveillance totale, gratuite et indétectable constitue un signal d’alerte, non une opportunité.
Adopter cette posture revient à déplacer le centre de gravité de la sécurité : du fantasme de contrôle vers l’acceptation lucide des limites techniques et humaines.
Découverte du mécanisme réel et confusion terminologique
Contrairement au récit populaire, Silent Whisper n’est pas né d’une application clandestine découverte par hasard. Le mécanisme réel a été compris et documenté par des chercheurs en sécurité informatique, notamment au sein de l’Université de Vienne et de SBA Research.
Ces travaux académiques ont mis en évidence une exploitation possible des accusés de réception silencieux comme canal auxiliaire de timing. Il s’agit d’une inférence d’états et de comportements, et non d’une lecture des messages chiffrés. Le terme « Silent Whisper » relève donc d’une désignation médiatique, pas d’une catégorie scientifique.
La confusion naît de l’écart entre la précision du langage académique et la simplification médiatique. Là où la recherche parle de métadonnées et de canaux auxiliaires, le récit public parle d’espionnage, alimentant un malentendu durable.
Le terme « Silent Whisper » ne figure pas dans la publication scientifique originale (arXiv:2411.11194) et relève d’une construction médiatique ultérieure.
Chronologie des faits et dérive du récit public
La compréhension de Silent Whisper nécessite une chronologie explicite. Elle débute par une recherche académique démontrant une fuite latérale limitée. Elle se poursuit par la publication d’un prototype de preuve de concept, destiné à illustrer cette possibilité dans un cadre contrôlé.
Vient ensuite la reprise médiatique, souvent décontextualisée, qui transforme une capacité d’inférence en promesse d’espionnage global. Enfin, la confusion publique s’installe : l’outil devient une “application”, la recherche devient une “faille critique”, et la nuance disparaît.
Cette dérive narrative constitue en elle-même un risque informationnel, distinct de la réalité technique initiale.
Métadonnées, messageries chiffrées et Silent Whisper : ce qui est observé, ce qui ne l’est pas
Une confusion centrale alimente le mythe Silent Whisper : l’assimilation entre espionnage de métadonnées et accès au contenu des messages. Or ces deux notions relèvent de registres techniques radicalement différents.
Les messageries comme WhatsApp ou Signal protègent le contenu des messages par chiffrement de bout en bout. En revanche, certaines métadonnées fonctionnelles demeurent observables par conception : états de livraison, délais de réponse, activité réseau ou corrélations temporelles. Ces signaux ne permettent jamais de lire un message, mais peuvent révéler des comportements.
Silent Whisper s’inscrit exclusivement dans ce second registre. Il exploite des canaux auxiliaires de timing pour inférer l’état d’un terminal (actif, inactif, mobilité probable), sans jamais toucher aux clés cryptographiques ni au contenu chiffré. Il ne s’agit donc pas d’une interception, mais d’une observation indirecte.
Cette distinction est fondamentale. Confondre métadonnées et contenu revient à attribuer au chiffrement des promesses qu’il n’a jamais formulées, puis à le déclarer « cassé » lorsqu’il ne protège pas ce qu’il n’a pas vocation à protéger. Silent Whisper n’expose pas une faiblesse cryptographique, mais une limite structurelle connue des systèmes de communication.
Le danger ne réside pas dans l’existence de ces métadonnées, mais dans leur sur-interprétation. Présentées comme une capacité d’espionnage total, elles nourrissent un climat de défiance injustifié envers des protections pourtant effectives, et déplacent l’attention loin des véritables vecteurs de compromission.
Exploitation des contacts : le levier relationnel quand le contenu est chiffré
Lorsque le contenu des messages est protégé par un chiffrement de bout en bout, l’attention de l’observateur se déplace vers une autre surface : les relations. L’exploitation des contacts ne consiste pas à lire des messages, mais à inférer des informations à partir du graphe relationnel : qui communique avec qui, à quelle fréquence, selon quels rythmes et avec quelles synchronisations.
Dans les messageries centralisées, les identités persistantes, les carnets d’adresses corrélables et les mécanismes de présence créent un environnement où ces relations deviennent observables indirectement. Associées à des signaux temporels — comme ceux exploités dans le cadre académique à l’origine du mythe Silent Whisper — ces données permettent de réduire l’incertitude comportementale sans jamais accéder au contenu chiffré.
Cette exploitation relationnelle peut servir à des usages variés : cartographie sociale, repérage de relations fortes ou faibles, observation de dynamiques de groupe, ou préparation d’actions ultérieures telles que l’ingénierie sociale, le stalking numérique ou la surveillance ciblée. Le risque ne provient pas de la donnée isolée, mais de sa corrélation avec d’autres signaux observables.
Il est donc essentiel de distinguer clairement l’espionnage de messages — techniquement impossible sans compromission du terminal — de l’observation indirecte des relations, qui repose sur des choix architecturaux et non sur une rupture du chiffrement.
Spy ou Track ? Pourquoi cette confusion alimente le mythe Silent Whisper
De nombreux articles et contenus en ligne décrivent Silent Whisper comme une technique de “spying” (espionnage) ou de “tracking” appliquée à WhatsApp, Signal ou à d’autres messageries chiffrées. Cette terminologie est largement responsable de la confusion actuelle.
En cybersécurité, ces termes ne sont pas équivalents :
- Spy (espionner) implique un accès non autorisé à un contenu protégé
: messages, fichiers, communications ou clés de chiffrement. - Track (suivre) désigne l’observation d’événements, de signaux ou de comportements
sans accès au contenu lui-même.
Silent Whisper ne relève en aucun cas de l’espionnage. Il ne permet ni la lecture des messages, ni l’interception des conversations, ni la compromission du chiffrement de bout en bout.
Il s’inscrit exclusivement dans une logique de tracking indirect de métadonnées, reposant sur l’inférence comportementale à partir de signaux observables (timing, accusés de réception silencieux, états d’activité).
Employer le terme spy pour décrire Silent Whisper est donc techniquement incorrect. Cette approximation transforme une capacité d’observation limitée en une menace fantasmée, et entretient l’idée erronée que le chiffrement serait contourné.
Silent Whisper ne permet pas d’espionner des messages chiffrés. Il permet tout au plus de suivre des signaux d’activité dans des architectures où ces métadonnées restent observables.
Cette distinction est cruciale. Confondre tracking de métadonnées et espionnage de contenu affaiblit la compréhension des protections réelles, et détourne l’attention des véritables vecteurs de compromission : le terminal, l’ingénierie sociale et l’action humaine.
Dérive médiatique autour de l’espionnage WhatsApp et Signal
La persistance du mythe Silent Whisper ne repose pas uniquement sur des abus techniques. Elle s’explique aussi par la responsabilité informationnelle des médias et des plateformes de diffusion. Des titres sensationnalistes évoquant un « espionnage total » ou une « surveillance invisible » entretiennent une confusion durable entre profilage comportemental et lecture de contenu chiffré.
Les plateformes sociales jouent un rôle amplificateur : la viralité favorise les récits simples, anxiogènes et polarisants, au détriment des explications nuancées. Cette dynamique transforme une recherche académique limitée en une menace perçue comme omnipotente.
Cette confusion peut être involontaire — simplification excessive — ou volontaire — recherche d’audience. Dans les deux cas, elle produit un effet délétère : elle affaiblit la confiance dans les protections réelles et favorise une résignation numérique fondée sur une peur mal comprise.
Prototype d’outil et observations de terrain
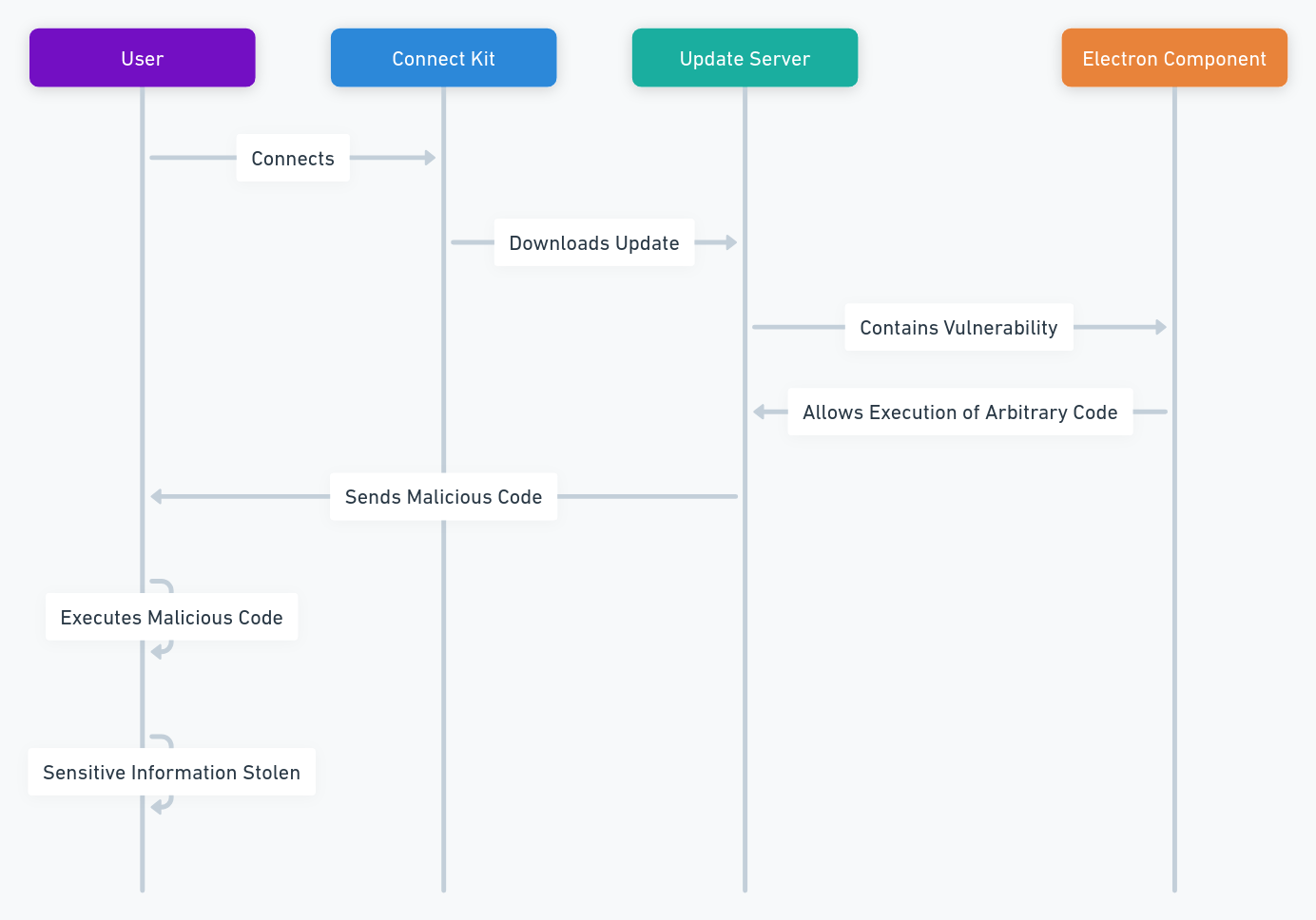
Un outil de preuve de concept publié publiquement sur GitHub démontre comment des probes silencieux peuvent tracer en temps réel l’activité d’un utilisateur à partir de son numéro de téléphone. Ce code ne génère aucune notification côté victime, mais peut infliger une consommation de batterie anormale et une pression sur les données mobiles, ce qui rend l’exploitation détectable par des mesures système spécialisées.
L’absence de correctif au niveau des accusés de réception persistants laisse cette vectorisation ouverte, malgré les efforts de limitation côté Signal et certaines protections avancées que les utilisateurs peuvent activer pour réduire l’exposition.
Réactions des éditeurs et correctifs partiels
Meta a récemment corrigé une vulnérabilité distincte liée à l’énumération globale de comptes via Contact Discovery, mais n’a pas encore réglé la question des accusés silencieux exploitables comme canal auxiliaire. Signal, de son côté, a renforcé des limitations de taux qui réduisent l’impact pratique sans résoudre la cause profonde.
Les éditeurs rappellent que le contenu des messages reste protégé par le chiffrement de bout en bout, ce qui souligne la distinction fondamentale entre métadonnées exploitables et violation du chiffrement lui-même.
Les positions officielles des éditeurs sont accessibles publiquement. WhatsApp détaille son modèle de sécurité et confirme que le chiffrement de bout en bout empêche tout accès au contenu des messages par des tiers : https://www.whatsapp.com/security.
Signal publie également une documentation complète sur son protocole de chiffrement et son modèle de menace, précisant que seules des métadonnées limitées peuvent transiter, sans accès au contenu : https://signal.org/docs/.
À ce jour, les correctifs déployés par les éditeurs portent principalement sur la limitation des abus à grande échelle (énumération, taux de requêtes, détection d’automatisation), mais ne suppriment pas entièrement la possibilité d’inférences comportementales ponctuelles. Cette limite est structurelle et relève de compromis protocolaires, non d’une vulnérabilité cryptographique.
Limites irréversibles de l’espionnage WhatsApp et Signal
Une clé cryptographique générée ou exposée sur une infrastructure non souveraine ne peut jamais retrouver un niveau de confiance initial. Aucun correctif logiciel ne peut inverser cet état.
Distinction logiciel / décision matérielle
Le logiciel orchestre des opérations, mais il ne peut pas annuler une décision matérielle : clé locale, enclave sécurisée, isolation cryptographique. La réalité matérielle prévaut toujours sur l’intention logicielle.
Perspective non automatisable
La sécurité numérique ne se réduit pas à une checklist. Elle exige de reconnaître des seuils où l’action aggrave la situation. Cette capacité de renoncement informé constitue un acte de souveraineté opérationnelle.
Espionnage WhatsApp Signal : usages abusifs et cybervictimes réelles
Les techniques d’inférence comportementale associées au mythe Silent Whisper ne visent pas un public abstrait. Elles s’inscrivent dans des contextes asymétriques bien réels. Une personne cherche à surveiller une autre sans consentement, sans accès au contenu et souvent sans en comprendre les implications juridiques.
Les cas les plus fréquemment documentés relèvent du stalking numérique, notamment dans des situations de séparation, de conflit conjugal ou de contrôle coercitif. L’objectif n’est pas de lire des messages. Il s’agit d’inférer des habitudes : périodes d’activité, horaires, déplacements probables ou moments de vulnérabilité.
D’autres usages concernent la surveillance militante ou journalistique. L’enjeu porte sur l’identification de routines, de fenêtres d’exposition ou de corrélations temporelles. Enfin, le profilage discret peut viser des individus sans qu’ils en aient conscience, uniquement par observation indirecte de signaux faibles.
Dans tous ces cas, le danger principal ne réside pas dans une rupture du chiffrement. Il se trouve dans l’exploitation d’asymétries relationnelles et informationnelles. Ces pratiques sont aujourd’hui reconnues par de nombreuses autorités de protection des données comme des formes de surveillance abusive, même en l’absence d’accès au contenu des communications.
La confusion entretenue entre « espionnage de messages » et « inférence d’activité » aggrave ces situations. Elle masque les risques réels, banalise l’intention de surveillance et retarde la reconnaissance des victimes.
Métadonnées et Silent Whisper : vecteurs cyber indirects de surveillance
Contrairement aux récits sensationnalistes, les métadonnées issues des messageries chiffrées — y compris celles exploitées par les mécanismes associés à Silent Whisper — ne constituent pas un outil d’espionnage autonome. Elles forment cependant un levier cyber indirect, susceptible d’être intégré dans des chaînes d’attaque ou de surveillance plus larges, licites ou illicites.
Ces métadonnées peuvent inclure des signaux temporels, des états d’activité, des variations de latence ou des corrélations d’usage. Isolées, elles restent inoffensives. Agrégées, interprétées et corrélées à d’autres sources, elles peuvent devenir exploitables sur le plan opérationnel.
Usages cyber illicites possibles (sans accès au contenu)
Dans des contextes malveillants, ces signaux peuvent servir à préparer ou renforcer des attaques indirectes, sans jamais compromettre le chiffrement des messages. Les scénarios documentés relèvent notamment :
- de la synchronisation d’attaques d’ingénierie sociale (phishing contextuel, manipulation ciblée)
- du repérage de fenêtres de vulnérabilité temporelle (fatigue, isolement, routine)
- du profilage comportemental non consenti à des fins de contrôle ou de pression
- de la facilitation de campagnes de stalking numérique
Dans tous ces cas, la métadonnée ne provoque pas l’attaque : elle réduit l’incertitude de l’attaquant. La compromission effective reste conditionnée à une action humaine ou logicielle supplémentaire.
Usages cyber licites et cadres encadrés
À l’inverse, des usages licites existent dans des cadres strictement délimités : cybersécurité défensive, recherche académique, analyse de trafic, détection d’abus ou investigations sous mandat. Ces pratiques reposent sur des principes de proportionnalité, de traçabilité et de responsabilité juridique.
La distinction fondamentale ne repose donc pas sur la donnée elle-même, mais sur l’intention, le contexte et le cadre légal de son exploitation.
Point de clarification essentiel
Les métadonnées — y compris celles révélées par les canaux auxiliaires étudiés dans le cadre académique — ne permettent jamais d’accéder au contenu chiffré. Elles n’autorisent ni la lecture des messages, ni l’interception des conversations, ni la rupture du chiffrement de bout en bout.
Le risque réel n’est pas cryptographique, mais systémique : il naît de la combinaison de signaux faibles, d’interprétations humaines et d’actions ciblées.
Cette distinction constitue un point d’arrêt conceptuel : confondre métadonnées exploitables et espionnage de contenu revient à déplacer la menace du terrain réel vers un mythe paralysant.
Responsabilité humaine face à la surveillance WhatsApp et Signal
La question centrale soulevée par Silent Whisper n’est pas uniquement technique. Elle engage directement la responsabilité humaine, tant du côté de celui qui cherche à surveiller que de celui qui relaie ou exploite ces récits. Aucun mécanisme automatisé ne peut se substituer à une décision consciente face aux limites connues.
Chercher à exploiter des techniques d’inférence comportementale, même sans accès au contenu des messages, revient à franchir une frontière éthique et juridique claire. L’absence de déchiffrement ne neutralise ni l’atteinte à la vie privée, ni la responsabilité individuelle associée à l’intention de surveillance.
À l’inverse, relayer ou consommer des promesses de surveillance totale sans esprit critique participe à une délégation de responsabilité. La sécurité numérique devient alors un fantasme d’outil plutôt qu’un exercice de discernement, ce qui accroît la vulnérabilité collective.
Assumer une posture souveraine implique donc d’accepter que certaines capacités ne doivent pas être recherchées, même si elles semblent techniquement accessibles ou présentées comme anodines.
Métadonnées des messageries chiffrées de bout en bout face à l’architecture EviLink
Les messageries chiffrées de bout en bout comme WhatsApp ou Signal protègent efficacement le contenu des messages, mais continuent de produire des métadonnées structurelles : horaires de connexion, états de présence, accusés de réception, volumes de trafic ou corrélations temporelles. Ces éléments, bien que distincts du contenu chiffré, constituent la matière première des techniques d’inférence comportementale telles que celles exploitées dans le récit Silent Whisper.
La question centrale n’est donc pas l’existence des métadonnées — inévitable dans tout système communicant — mais leur capacité à être observées, corrélées et exploitées à distance.
Pourquoi les messageries centralisées exposent des métadonnées exploitables
Dans les architectures centralisées, les métadonnées sont :
- produites en continu par la plateforme,
- corrélables entre utilisateurs,
- associées à des identités persistantes,
- observables sans accès physique au terminal.
C’est cette combinaison — et non une faille cryptographique — qui rend possibles des scénarios d’inférence à distance. Le chiffrement protège le message, mais l’architecture rend visibles les comportements.
EviLink : rupture architecturale avec la corrélation des métadonnées
La technologie EviLink, embarquée notamment dans CryptPeer et dans les dispositifs matériels EM609, repose sur une logique fondamentalement différente. Elle ne cherche pas à « masquer » des métadonnées, mais à empêcher leur transformation en signaux exploitables.
Selon la configuration choisie, notamment en mode air gap ou réseau strictement local :
- aucune plateforme centrale n’agrège les comportements,
- aucun accusé de réception applicatif n’est observable à distance,
- aucun mécanisme de présence n’est exposé,
- aucun identifiant global ne permet une corrélation inter-pairs.
Dans ce cadre, les métadonnées réseau externes disparaissent, non par dissimulation, mais par absence structurelle d’observateur distant.
Pourquoi Silent Whisper est inopérant dans une architecture EviLink
Silent Whisper suppose l’existence :
- d’un canal auxiliaire observable à distance,
- d’un mécanisme de retour silencieux exploitable,
- d’une identité persistante joignable via une plateforme.
Ces prérequis ne sont pas réunis dans une architecture fondée sur EviLink fonctionnant hors plateforme corrélatrice. Il ne s’agit pas d’un « durcissement » contre l’attaque, mais d’une incompatibilité structurelle entre le modèle d’inférence et le modèle d’architecture.
Posture doctrinale sur les métadonnées
Elle devient un risque uniquement lorsqu’un humain décide d’en faire une arme.
La souveraineté numérique ne consiste donc pas à nier l’existence des métadonnées, mais à concevoir des systèmes où leur exploitation abusive devient structurellement impossible ou localement circonscrite. Cette distinction marque la frontière entre un chiffrement centré sur le message et une architecture centrée sur la souveraineté de l’environnement.
Impact réel de Silent Whisper Espionnage — Technique, cognitif et juridique
Techniquement, l’exploitation repose sur des fuites latérales au niveau protocolaire, mesurant les temps de réponse RTT des accusés de réception pour inférer si un appareil est en ligne, inactif ou en mouvement.
Les tests documentés ont montré que des probes intensifs entraînent une consommation de batterie significative, ce qui suggère que l’impact n’est pas totalement “invisible” au système.
Sur le plan technique, ces récits n’ont jamais démontré la moindre rupture cryptographique. En revanche, leur efficacité est maximale sur le plan cognitif : ils déplacent la perception du risque du système vers l’utilisateur.
La propagation de récits erronés confondant « inférence d’activité » et « espionnage de contenu » met en danger la confiance dans les protections cryptographiques réelles des messageries modernes. Ce phénomène cognitif est un risque autonome, distinct des capacités techniques réelles.
Sur le plan opérationnel, l’impact est double. D’une part, des utilisateurs installent des exécutables malveillants ou communiquent leurs identifiants en croyant « tester » un outil. D’autre part, des organisations surestiment des menaces inexistantes, ce qui conduit à des décisions de sécurité mal orientées, voire contre-productives.
Sur le plan juridique, la simple tentative d’exploitation de tels outils expose à des infractions graves : accès frauduleux à un système de traitement automatisé, atteinte à la vie privée, interception illégale de correspondances. Ces risques sont immédiats et irréversibles, indépendamment de tout résultat technique.
Enfin, sur le plan industriel et sociétal, ces mythes affaiblissent la confiance dans les outils de protection eux-mêmes. En insinuant que « tout est espionnable », ils produisent un effet paradoxal : dissuader l’usage de protections efficaces au profit d’une résignation numérique.
Impacts structurants
✗ Aucun impact cryptographique démontré
🧠 Impact cognitif élevé : désactivation des points d’arrêt
⚠ Risque juridique immédiat pour l’utilisateur
⚠ Affaiblissement de la confiance dans les protections réelles
🔋 Consommation de batterie significative lors de probes intensifs
⛔ Confusion entre inférence d’activité et espionnage de contenu
Perspective stratégique du Silent Whisper Espionnage
Silent Whisper n’est qu’un nom parmi d’autres. Tant que le chiffrement restera mal compris, ces récits réapparaîtront. L’enjeu stratégique de la sécurité numérique consiste donc à reconnaître les limites irréversibles, à formaliser des points d’arrêt clairs, et à assumer que certaines actions techniques ne doivent pas être entreprises. La souveraineté commence précisément là.
Dans ce contexte, la véritable ligne de défense n’est pas une mise à jour logicielle supplémentaire, mais la capacité collective à reconnaître qu’une limite cryptographique existe — et qu’elle ne doit ni être niée, ni « testée ».
Toute tentative de simplification excessive de ces phénomènes, en les réduisant à une « arnaque » ou à une « faille critique », produit plus de risques qu’elle n’en résout, en masquant les limites réelles et les responsabilités humaines.