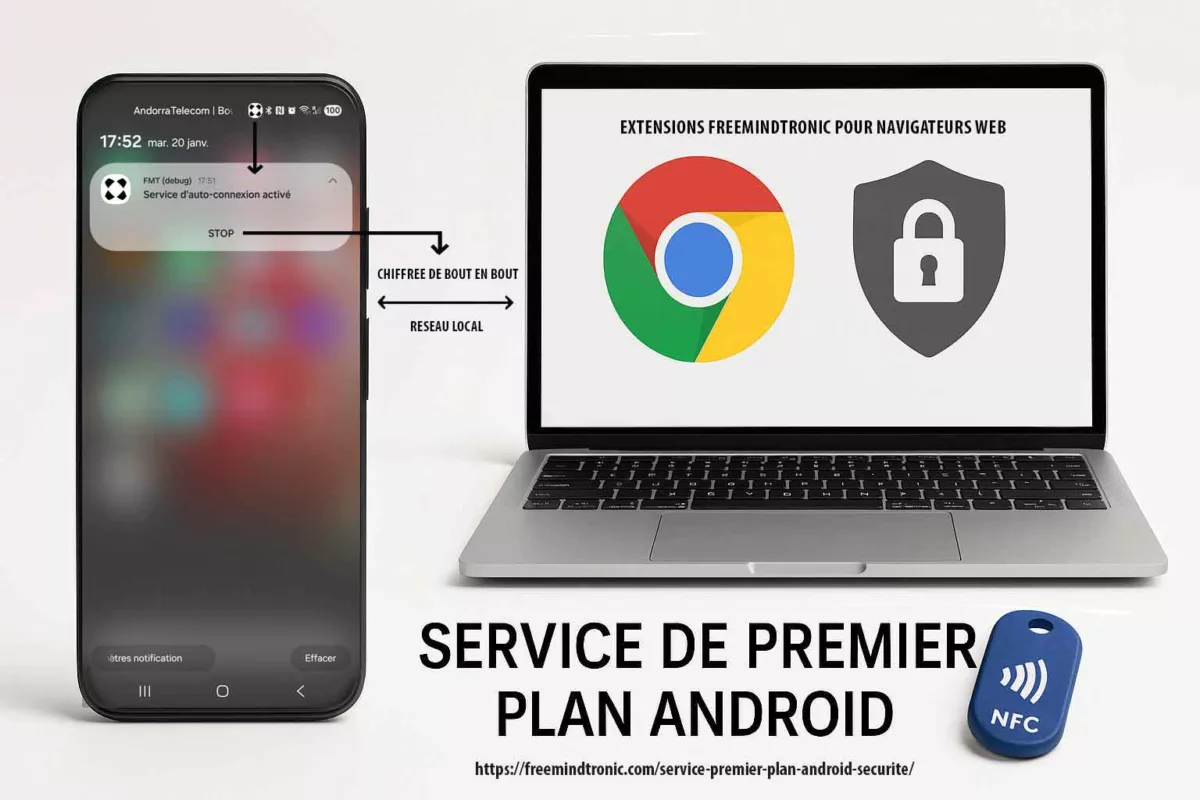
Android foreground service: Google Play compliance, user control, and NFC HSM PC Connection via a Chromium-based extension. This dossier shows how a Foreground Service (FGS) requirement becomes a verifiable trust marker. The session is strictly local-only (no proxy, no VPN, no routing). It relies on local pairing via EviDNS Zeroconf. It also exposes a persistent notification with a STOP action. Finally, it enforces granular data controls and a 2-minute audit path.
Executive summary
Context
Android continues to restrict background execution. At the same time, it tightens the governance of foreground services. The goal is clear: reduce invisible work, limit abuse, and preserve battery and reliability.
With Android 16 (API level 36), enforcement becomes more direct. As a result, compliance becomes observable during real-world review and testing.
However, a well-designed foreground service is not a penalty. Instead, it becomes a trust marker. It is built on transparency, user control, and a minimal operational scope.
Purpose
This dossier provides a verifiable justification for using an Android foreground service. It is a required dependency for a core feature: PC Connection.
In other words, it documents why the service exists. It also shows how Google Play requirements can support transparency and security maturity.
Scope
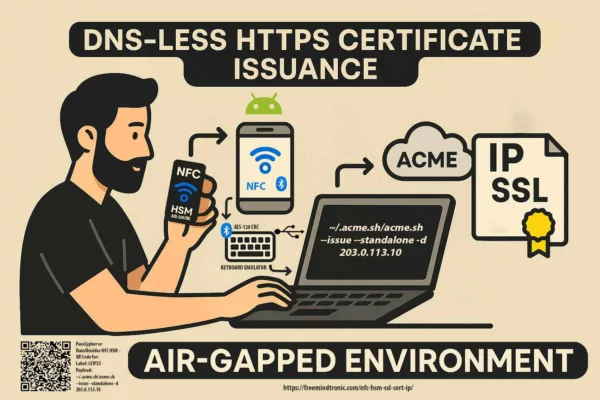
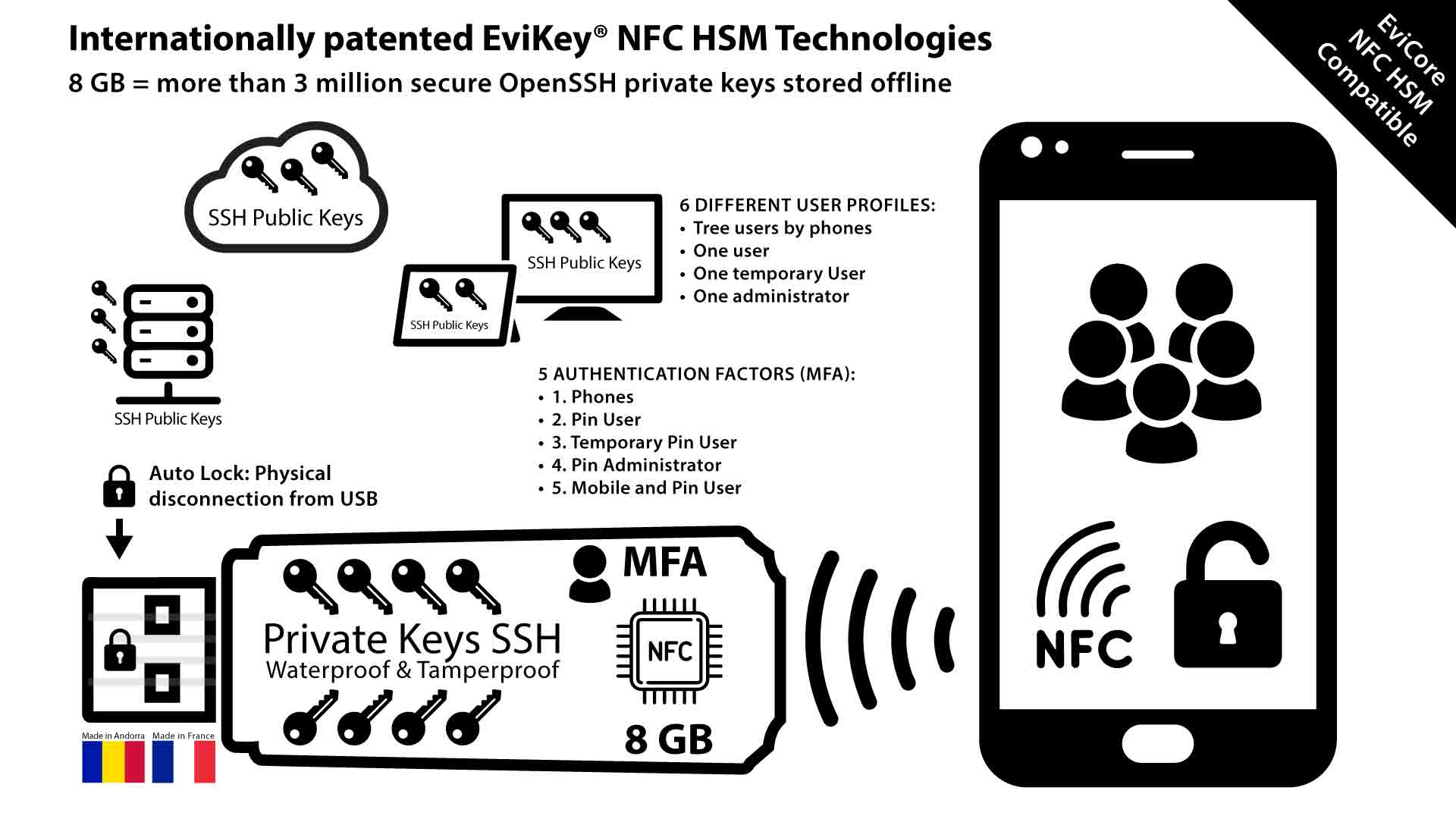
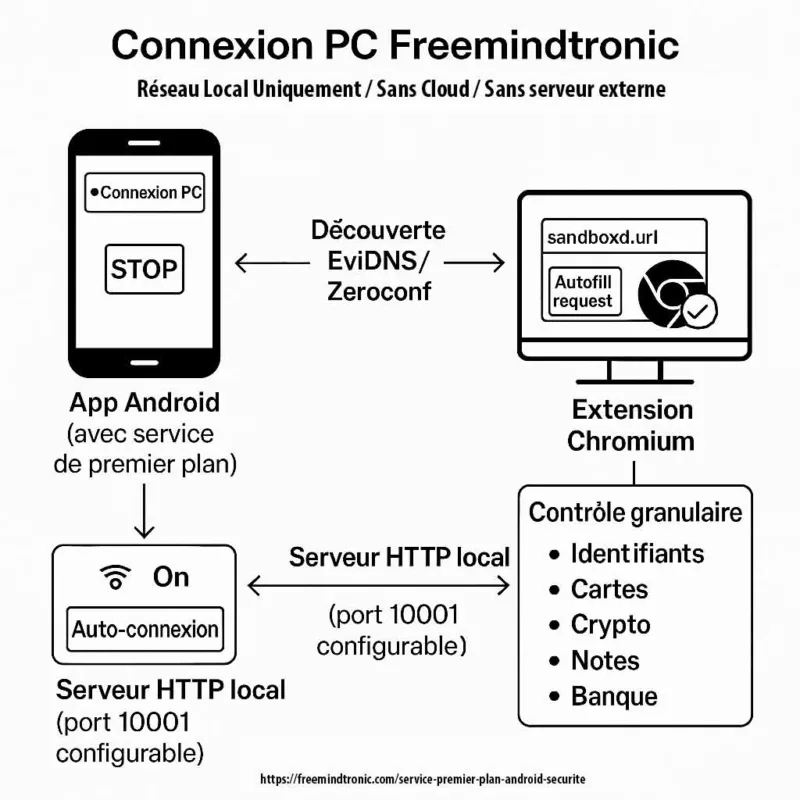
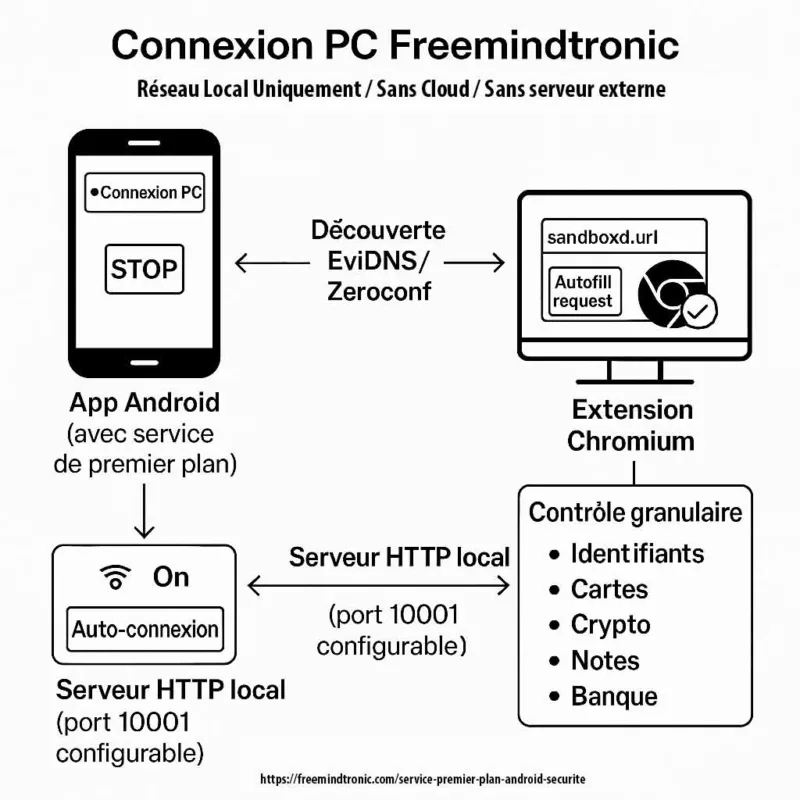
Feature in scope: PC Connection (phone ↔ desktop). It enables the use of NFC HSM devices from a computer. It does so through a Freemindtronic Chromium-based browser extension. No workstation software is required.
Importantly, the session is strictly local-only. There is no proxy, no VPN, and no routing. The local port is configurable (default: 10001).
Design doctrine
The service is not used to “stay active”. Instead, it makes a sensitive session visible and stoppable. It also keeps the session user-controllable.
Specifically, it uses a persistent notification and an explicit STOP action. Moreover, auto-login remains reversible. Finally, the user can restrict which data categories the extension is allowed to request.
Strategic differentiator
Android and Google Play keep hardening enforcement. Consequently, opaque implementations become structurally fragile.
By contrast, a demonstrable design reduces ambiguity. It combines user control, local-only scope, and operational transparency. Therefore, it becomes a competitive advantage.
This dossier explains the dependency. It also explains how users keep control. Finally, it shows how compliance can be turned into a durable differentiator.
Key takeaway
The Android foreground service is used only for the PC Connection session. The session stays visible and stoppable (persistent notification + STOP). This enables the use of an NFC HSM from a desktop via a Chromium-based extension.
In addition, the user can disable auto-login. The user can also restrict each authorized data category. The user can verify the strictly local-only scope (no proxy/VPN/routing). Finally, the user can audit compliance in 2 minutes.
📱 Freemindtronic (EviPro) on Google Play: open listing
Technical note
Summary reading time: ~2 minutes
Full reading time: ~20–25 minutes
Verification time (quick audit): ~2 minutes
Publication date: 2026-01-16
Last updated: 2026-01-20
Level: Android / Security / Audit
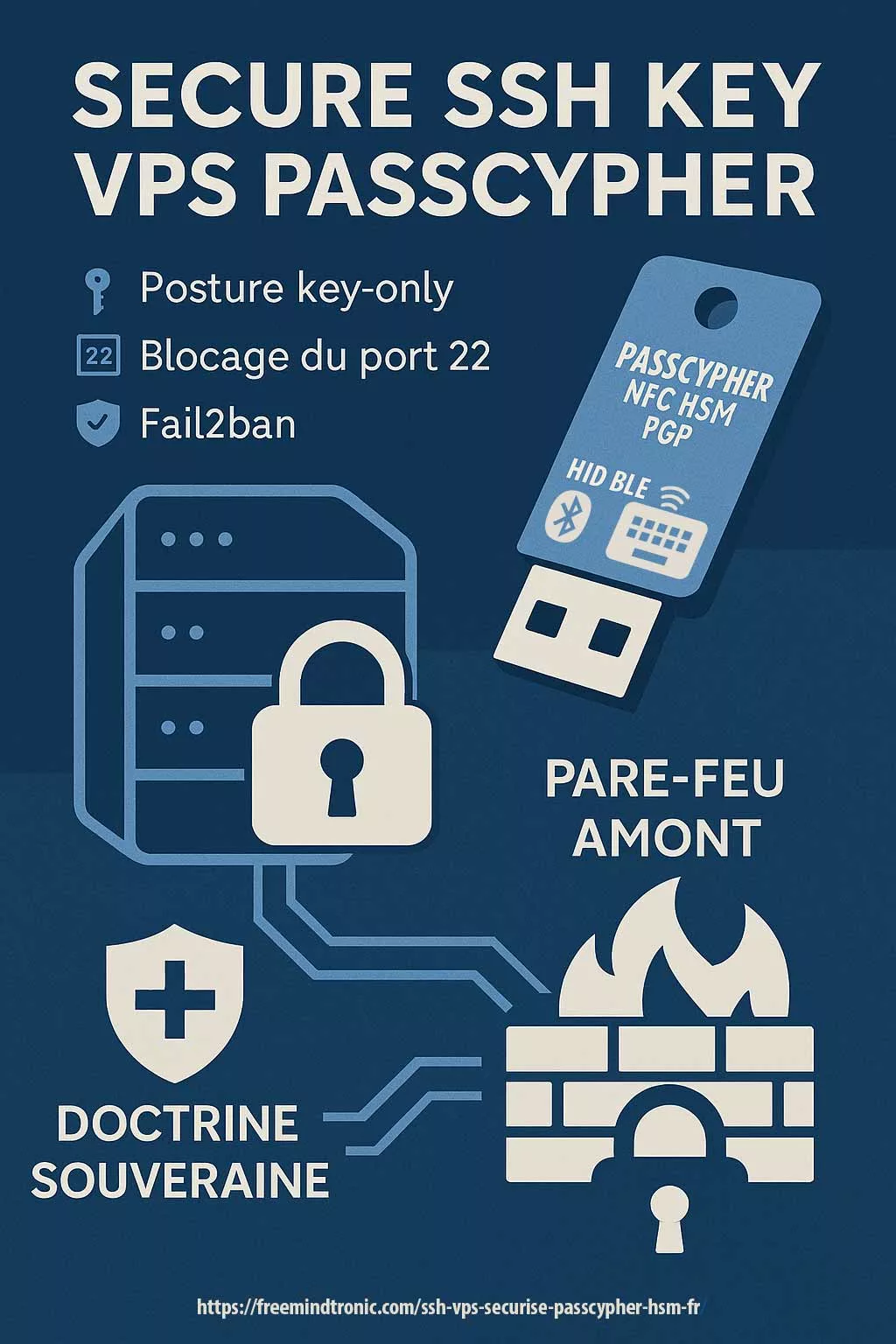
Posture: Local-only, user-in-control, least privilege
Category: Tech Fixes & Security Solutions
Available languages: FR · EN · CAT · ES
Impact level: 8.4 / 10 — store compliance, software transparency & local session security
This dossier is part of Tech Fixes & Security Solutions. It extends prior work on sovereign architectures and user control. It also addresses a recurring risk: treating “background persistence” as acceptable by default.
Here, the issue is broader than Android. It is the ability to prove (audit) behavior. It is also the ability to document (compliance) it. Finally, it is the ability to bound it (least privilege).
The dossier focuses on PC Connection (Chromium extension), local pairing via EviDNS Zeroconf, and per-data-category controls. Therefore, it shows how a Google Play requirement can become a concrete trust marker.
This work continues publications in: Tech Fixes & Security Solutions and, for sovereign and trusted architecture topics: Digital Security.
It follows the Freemindtronic Andorra AI transparency statement — FM-AI-2025-11-SMD5.
In mobile security and Android, this note belongs to the Tech Fixes & Security Solutions category. Moreover, it supports Freemindtronic’s sovereign operational toolkit (HSM, user control, local-only architectures, audit).
- Executive summary
- Android foreground service: why it has become a security marker
- Threat model: mobile ↔ desktop session, risks, and bounded scope
- Android foreground service: Google Play requirements (official sources)
- Android background execution vs foreground service
- Field feedback: approval, then rejection, of the Foreground Service
Connected Device declaration
- An ambiguous rejection signal, documented by the community
- Why this type of rejection is difficult to diagnose
- Resolution strategy: making the justification unambiguous
- Android 14+ — foreground service (FGS): declared type and verifiable justification
- Product impact and mitigation (Android 15/16, NFC, BAL, OEM specifics)
- Compatibility burden and update cycle impact
- Core feature: PC Connection for NFC HSM (Chromium extension)
- EviDNS Zeroconf: local, serverless pairing for desktop extensions
- Android foreground service: user controls (notification, STOP, settings)
- Least privilege: granular permissions
- Key proof: full and granular user control
(data, alerts, port, shutdown)
- Enabled by default, but never enforced
- Least privilege enforced at the data level
- Alert control: notifications, vibration, ringtone
- Local network scope: no proxy, no VPN, no routing
- What the PC Connection does not do
- Turning compliance into a competitive advantage
- Verifiable transparency: downloads, signatures, version history
- Implementation checklist for auditors
- Evidence pack (Google Play review / internal audit)
- Evidence ↔ Google Play requirements mapping (reviewer view)
- Quick audit: verify a foreground service and local-only scope (2 minutes)
- Sovereign use case: transparency and operational continuity
- Glossary
- FAQ — Android foreground service
- Related links
Android foreground service: why it has become a security marker
A foreground service is designed for operations that must remain active, visible to the user, and stoppable at any time.
In practice, it is often misused by applications that try to remain active silently, automate actions without explicit user intent, or extend background activity beyond what is strictly required.
For a security product, the correct posture is not to “work around the rule”, but to align with it.
The user must always know when a sensitive session is active, what it is doing, and how to stop it immediately.
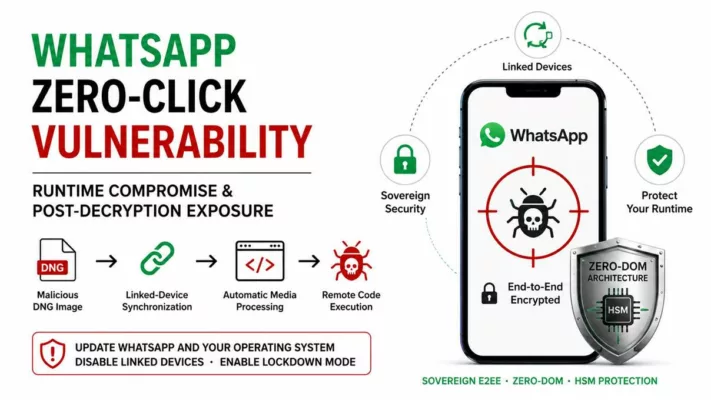
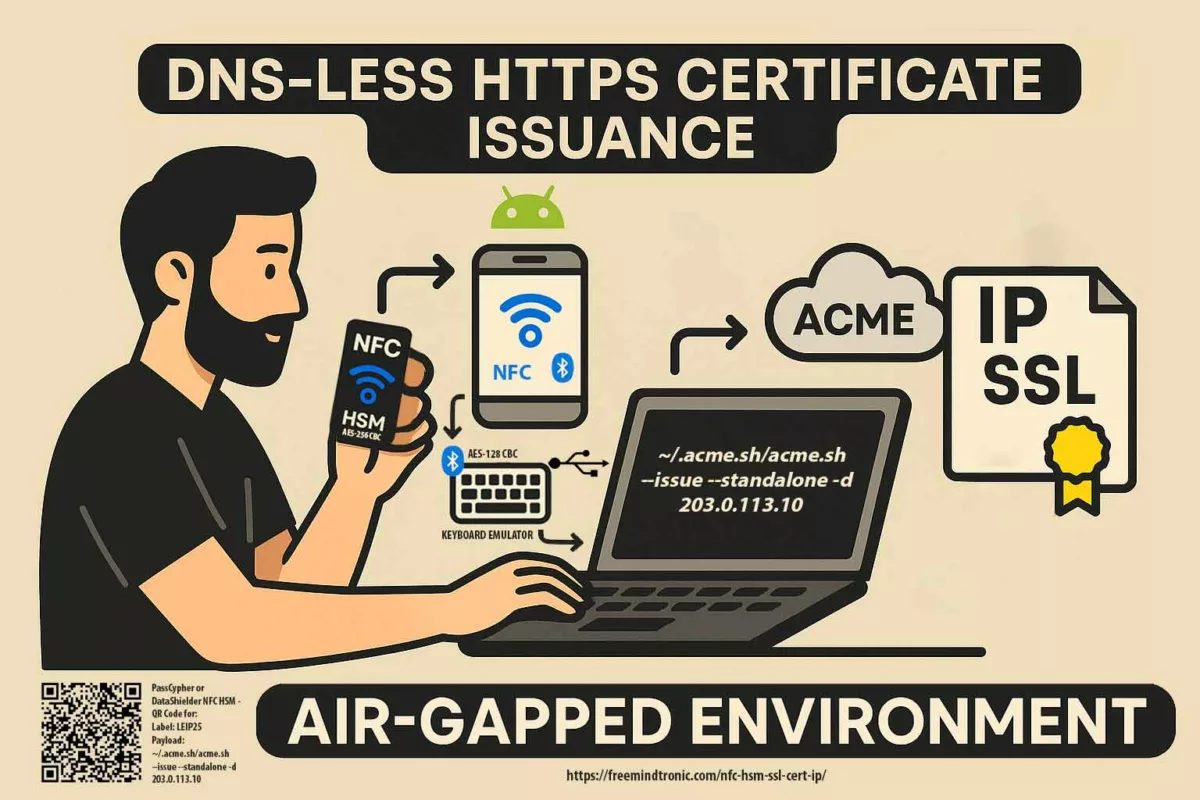
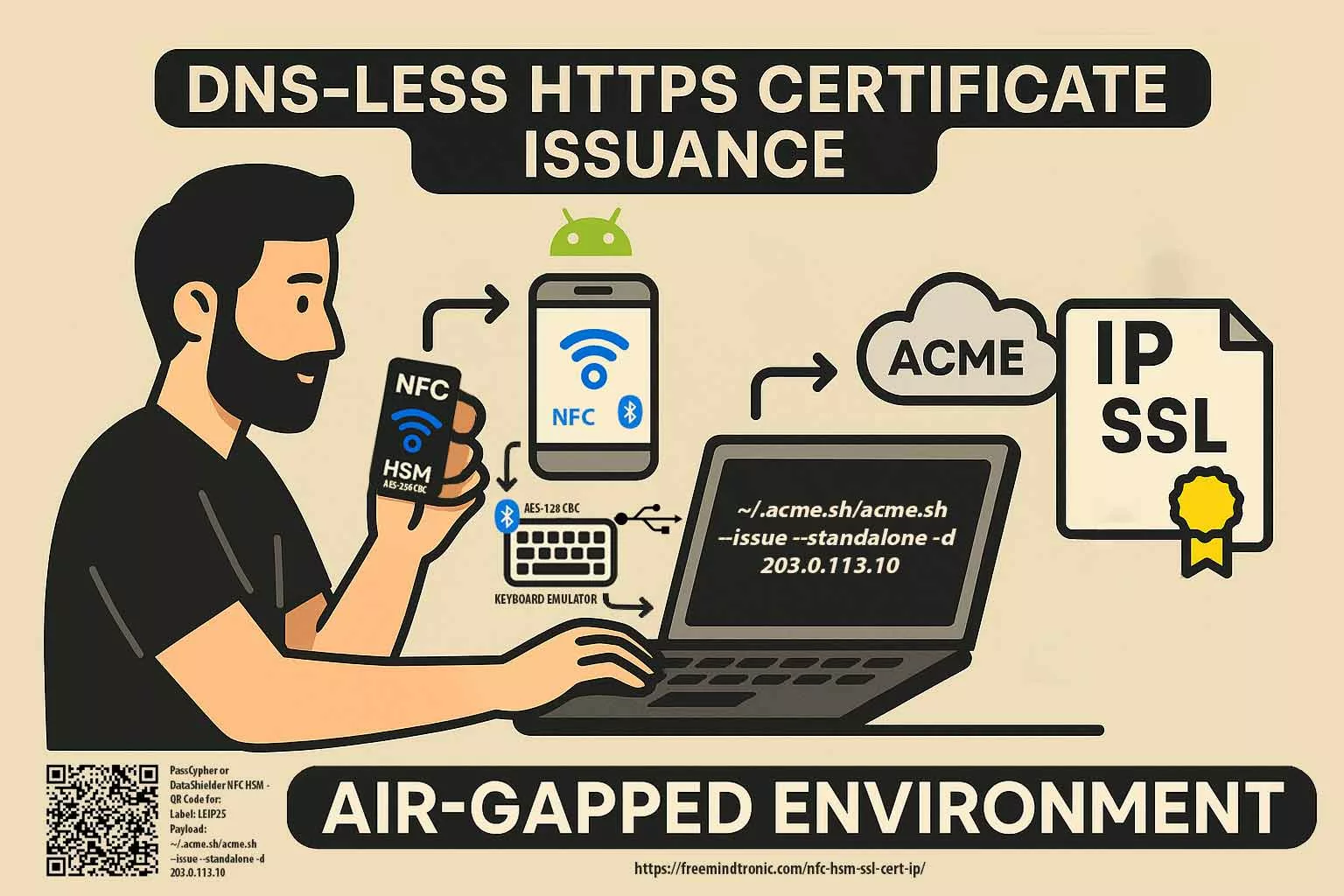
This requirement becomes critical when the phone acts as a gateway between hardware modules (NFC HSM) and a desktop browser environment.
Android: background execution vs foreground service
Across recent Android versions, background execution has been progressively restricted.
The objective is clear: limit invisible activity, reduce abuse, and preserve battery life and system reliability.
In this context, any feature that must remain active without being in the foreground must be justified and made perceptible.
This is precisely the role of a foreground service.
It makes sensitive activity visible (notification), stoppable (STOP), and explicitly bounded in time.
This approach follows a foreground service Android security architecture, aligned with Android foreground service compliance and Google Play requirements.
Here, visibility, immediate shutdown, and a strictly local-only scope are central criteria.
Key point: the correct question is not “how to stay active in the background”, but “how to make a persistent dependency auditable and controllable”. When designed correctly, a foreground service becomes a transparency marker, not a workaround.
Official Android Developers source — required foreground service types (Android 14+, including connectedDevice for interactions with peripherals such as NFC and Bluetooth):
https://developer.android.com/about/versions/14/changes/fgs-types-required
Threat model: why the PC Connection must remain visible and bounded
Realistic assumption: a phone used as a gateway (mobile ↔ desktop) represents an attack surface.
In this context, the foreground service acts as a mechanism of control and proof (notification + STOP), not as a way to persist silently.
| Risk | Example | Freemindtronic measure |
|---|---|---|
| Invisible persistence | Service running without user awareness | Foreground service with persistent notification and immediate STOP |
| Over-permission | Open session equals excessive access | Granular control by data category (least privilege) |
| Network expansion | Disguised proxy/VPN, implicit routing | Local-only: no proxy, no VPN, no routing |
| Operational failure | OS stops the service, breaking the workflow | Session explicitly dependent on the FGS, therefore predictable and verifiable |
Protection against capture and interception attacks:
the Freemindtronic application enforces system-level screenshot locking across all sensitive screens.
This mechanism prevents screenshots, screen recording, and equivalent capture APIs, including attempts by resident malware.
All screenshots and visual evidence provided for review purposes were produced using a debug build in which this protection is intentionally disabled.
In addition, PC Connection relies on a contactless, no-keyboard-input model, both on the phone and on the computer.
As a result, keylogger-based attacks are structurally ineffective, which significantly reduces the attack surface on the workstation side.
Android foreground service: Google Play requirements (official sources)
Google Play strictly governs foreground services. They must be justified by a core, user-beneficial feature. In addition, they must remain perceptible at all times through an explicit notification. Finally, they must be stoppable on demand. Since Android 14, declaring an explicit foreground service type is mandatory.
Official Android & Google Play references:
- Android 14 — Required foreground service types : https://developer.android.com/about/versions/14/changes/fgs-types-required
- Android SDK Platforms (includes Android 16 / API 36) : https://developer.android.com/tools/releases/platforms
- Android Manifest — Permission
FOREGROUND_SERVICE: https://developer.android.com/reference/android/Manifest.permission#FOREGROUND_SERVICE - Google Play Policy — Foreground service requirements : https://support.google.com/googleplay/android-developer/answer/13392821
- Android Developers — Declare a Foreground Service (API 34+) : https://developer.android.com/develop/background-work/services/fgs/declare
In this dossier, these requirements are applied to a real, verifiable case (PC Connection + NFC HSM). As a result, the user-in-control model (notification, STOP, opt-out, granular controls) turns a compliance constraint into evidence of security maturity.
Field feedback: approval, then rejection, of the Foreground Service Connected Device declaration
Real publication context: the FOREGROUND_SERVICE_CONNECTED_DEVICE declaration was accepted during an initial submission. It included a demo video and a justification that covered Android 14 and Android 15 requirements. However, during a late-December update, the same declaration was rejected. The reviewer requested “additional details” without providing actionable guidance on what was missing.
This situation is not isolated. Moreover, multiple developers report similar cases. In those reports, a previously accepted foreground service declaration is later rejected during an update. The rejection message can be ambiguous. Specifically, it may suggest the issue is either the justification text or the video, without stating which part is insufficient.
An ambiguous rejection signal, documented by the community
- Reddit – r/androiddev: developers describe repeated foreground-service-related rejections, with clarification requests that do not identify what to fix (text or video). Link: https://www.reddit.com/r/androiddev/comments/1fsuii4/has_anyone_had_repeat_issues_with_app_submission/
- Zoom developer forum: Play Store update rejection tied to foreground service permissions, with a demo video deemed insufficiently explicit and limited operational guidance. Link: https://devforum.zoom.us/t/app-update-rejected-due-to-foreground-service-permissions/103026
- Google Play Console support thread: developers report rejections for “insufficient information” about foreground service usage, without clarity on the missing criterion. Link: https://support.google.com/googleplay/android-developer/thread/299748806
Why this type of rejection is difficult to diagnose
- Lack of granularity: the rejection message does not state whether the issue is the Play Console justification, the video, or their consistency.
- Implicit reviewer expectation changes: what is “sufficient” at time T can be evaluated differently during a later update.
- Implicit criteria: Play often expects an even more explicit demonstration of the trio user-initiated → perceptible → stoppable, as well as immediate functional dependency.
Resolution strategy: making the justification unambiguous
When a rejection is generic, the only robust approach is to remove all room for interpretation.
- Play Console text: phrase the justification as a verifiable test: “if the user presses STOP, the session ends immediately and the extension loses NFC HSM access within the same second.”
- Video: show, without cuts, the full sequence: user action → visible notification → STOP → immediate session loss on the extension side.
- Semantic alignment: explicitly reuse Google Play terms: core feature, user benefit, perceptible, stoppable, cannot be deferred.
- Remove misunderstandings: explicitly restate “not a VPN, not a proxy, no routing, strictly local scope.”
This field feedback explains why this dossier includes an implementation checklist, an evidence ↔ Google Play requirements mapping, and a reproducible evidence pack. In short, when a rejection is generic, the only effective response is a demonstration that no longer depends on interpretation.
Android 14+ — foreground service (FGS): declared type and verifiable justification
Declared type and immediate functional dependency
- Declared type:
FOREGROUND_SERVICE_CONNECTED_DEVICE - Dependent core feature: PC Connection (phone ↔ Chromium extension)
- Justification: the phone acts as an active gateway to an NFC HSM device used from a computer, initiated explicitly by the user.
If the foreground service is stopped (via the STOP action in the notification or by disabling auto-login), the PC Connection session is immediately terminated, and the browser extension loses NFC HSM access. Therefore, the task cannot be deferred by the system without breaking the expected feature. Android reference — Foreground Service types: https://developer.android.com/develop/background-work/services/fgs/service-types
Android 15: continuity of the doctrine
It further tightens discipline around foreground services (startup, usage, behavioral expectations) and the consistency between user action, runtime duration, and purpose. Consequently, the trajectory confirms the “visible, stoppable, bounded” principle. It also favors demonstrable implementations (explicit notification + STOP + immediate functional dependency). Reference: https://developer.android.com/about/versions/15/changes/foreground-services
Android 16 (API level 36): quotas, diagnostics, operational limits
Foreground services — changes (includes Android 16 / API level 36): https://developer.android.com/develop/background-work/services/fgs/changes
Android 16 cap: Android 16 introduces a stricter framework of quotas, execution limits, and diagnostics. As a result, it favors short, local-only, explicitly user-controlled workflows over implicit or prolonged sessions. Diagnostic reference: https://developer.android.com/develop/background-work/services/fgs/troubleshooting
Android continues to improve diagnostics and reduce allowed scenarios. Therefore, a local-only workflow that is visible and stoppable remains the most robust strategy across successive hardening waves.
Operational detail — Freemindtronic Android NFC app
Operational detail: the foreground service is strictly event-driven. Launching the app is not enough to activate it. Instead, it starts only when an NFC tag is presented. Then, it remains inactive in the absence of NFC events, with no local server and no always-on service.
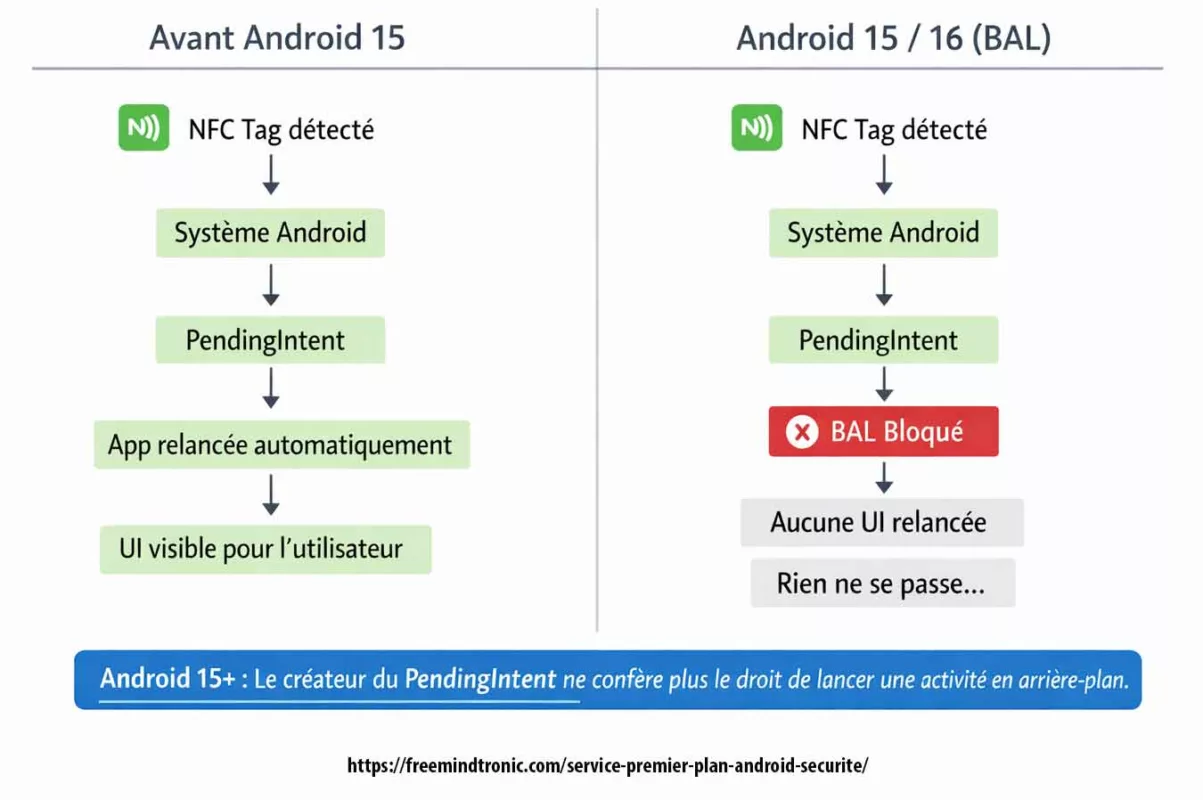
Product impact and mitigation (Android 15/16, NFC, BAL, OEM specifics)
Symptom
- Symptom: the NFC tag is correctly detected by the system, yet the attempt to relaunch or bring the UI to the foreground via
PendingIntentis blocked by BAL (Background Activity Launch). Consequently, the user perceives no reaction, or degraded behavior, even though the NFC event is received.
Cause
- Cause: Android 15, and even more Android 16, formally harden the rules for starting activities from the background. In particular,
PendingIntentobjects created by the app no longer implicitly carry the right to start or resume an activity in the foreground. This change directly impacts legacy NFC flows that relied on UI relaunch viaPendingIntent, including when the target activity is alreadyRESUMED. Official Android reference: https://developer.android.com/guide/components/activities/background-starts
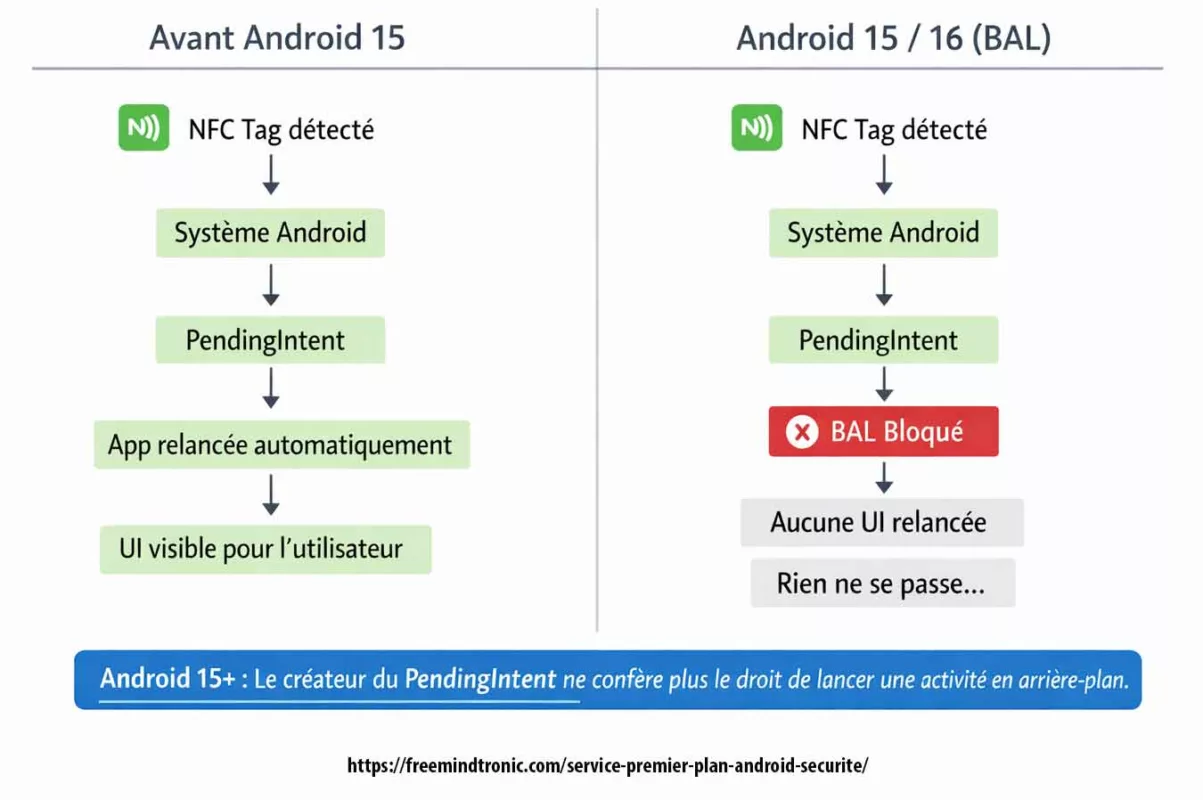
This behavior is observable even on Google Pixel (AOSP). Therefore, it confirms a structural platform change rather than an OEM-specific behavior.
Technical evidence — BAL block (Android 15 / 16)
On Android 15, and even more on Android 16 (API level 36), blocking background activity launches (Background Activity Launch) is a structural platform mechanism. Moreover, it is directly observable in system logs.
Typical Logcat excerpt (anonymized) during an NFC event that attempts to relaunch the UI via PendingIntent:
Background activity launch blocked: pkg=com.freemindtronic.EviPro reason=background_activity_launch_not_allowed intent=Intent { act=android.nfc.action.TAG_DISCOVERED ... } callerApp=ProcessRecord{...}
This message confirms that:
- the NFC event is received by the system,
- the UI relaunch attempt is explicitly blocked by Android,
- the denial is independent from the app and results from BAL hardening at the platform level.
Therefore, this evidence clearly separates: structural Android change ≠ application bug.
- Additional NFC risk (platform): alongside BAL restrictions, NFC stack instabilities and behavior changes are observed on Android 15 and Android 16. They include NFC service crashes (
DeadObjectException), intermittent tag read failures, and version-dependent differences. These items are documented in Google Issue Tracker, including Android 16: https://issuetracker.google.com/issues/456078994
Additional NFC risk (OEM)
- Additional NFC risk (OEM): the issue is amplified on some devices due to manufacturer overlays and aggressive power optimizations. Public feedback and tickets report degraded or inconsistent NFC behavior on:
- Samsung Galaxy (One UI 7/8 – Android 15/16): aggressive activity suspension, intermittent NFC disablement after updates, and behavioral differences between screen-on and screen-off states.
- Xiaomi / Redmi / Poco (MIUI / HyperOS – Android 15/16): strong background restrictions, interactions between NFC, Bluetooth, and power saving, causing NFC scan failures or missing UI resumes.
- OnePlus / Oppo (OxygenOS / ColorOS – Android 15/16): restrictive background task handling and NFC service variability across builds.
- Fairphone 5 (Android 15): regressions reported after updates, with incomplete or delayed recognition of certain NFC tags.
- Google Pixel (Android 15/16 AOSP): AOSP reference showing BAL is structural even without an OEM overlay, confirming it is not only a manufacturer issue.
Robust mitigation
- Robust mitigation: remove any dependency on implicit UI relaunch via
PendingIntent. Instead, NFC processing must run inside the existing activity instance when it is already active (appropriatelaunchMode, handle events throughonNewIntent()). Alternatively, continue the flow through an explicit user-initiated action (notification action), in line with the Android “user-initiated” model recommended for Android 15+.
Key takeaway: starting with Android 15, NFC detection can work correctly without relaunching the UI. BAL blocks any implicit relaunch via PendingIntent. Therefore, a compliant implementation must process the event in the existing instance or require an explicit user action.
Known limits / behaviors not guaranteed by Android
- Android does not guarantee automatic UI relaunch after a system event (NFC, intent, PendingIntent), especially starting with Android 15 (BAL).
- NFC stack behavior can vary by Android version, system state (screen off, Doze, OEM restrictions), and manufacturer implementations.
- Session continuity depends on the user-initiated model and on maintaining Android foreground service Google Play compliance (visible notification, STOP, bounded duration).
These limits are structural to the Android platform. Therefore, they are neither an application bug nor a functional deviation.
Evidence and audit
- Evidence and audit: Android system logs explicitly reveal BAL blocks (“Background activity launch blocked” or equivalent messages) during NFC events. These logs are objective technical evidence. As a result, they should be archived in the internal compliance evidence pack and produced during Google Play review or security audits when needed.
This demonstrable functional dependency is a key element of Android foreground service Google Play compliance, as expected by reviewers since Android 14+.
Compatibility burden and update cycle impact
This section explains why these changes are not a minor code tweak, but a structural transformation of legacy Android workflows.
Since Android 6, the platform has stacked successive restrictions. Consequently, a “simple targetSdk upgrade” can become a structural refactor. The stack includes: background execution hardening, BAL restrictions on activity starts, stricter FGS governance with justification requirements, and NFC variability across versions and OEM implementations.
Starting with Android 15, apps that create PendingIntent objects no longer implicitly inherit BAL privileges. Therefore, explicit opt-in becomes required, which breaks many legacy workflows (notification → UI resume, “system event → bring activity to front”, NFC scenarios, etc.).
At the same time, Android 15/16 introduce documented behavior changes (targetSdk and compat framework changes). In addition, public tickets also show platform-level NFC instabilities. As a result, multi-device testing becomes more complex, degraded modes multiply, and release cycles slow down mechanically.
Official references (Android/Google):
• BAL restrictions (Android 15+), opt-in required for PendingIntent: https://developer.android.com/guide/components/activities/background-starts
• Android 15 — behavior changes (targeting API 35): https://developer.android.com/about/versions/15/behavior-changes-15
• Android 15 — compat framework changes (BAL privileges rescind by creator): https://developer.android.com/about/versions/15/reference/compat-framework-changes
• Android 16 — behavior changes (Android 16 / API level 36): https://developer.android.com/about/versions/16/behavior-changes-16
• Set up the Android 16 SDK (API 36): https://developer.android.com/about/versions/16/setup-sdk
• Google Play target API level requirement (enforced migration cadence): https://developer.android.com/google/play/requirements/target-sdk
• Android Developers Blog (Android 15 AOSP) — PendingIntent creators block BAL by default: https://android-developers.googleblog.com/2024/09/android-15-is-released-to-aosp.html
Developer feedback & public tickets (similar issues):
• StackOverflow (Android 15 BAL hardening, activity blocked via PendingIntent): https://stackoverflow.com/questions/77679032/with-android-15-bal-hardening-this-activity-start-may-be-blocked-if-the-pi-creat
• GitHub (Flutter community — request for BAL opt-in support, activity no longer starts): https://github.com/fluttercommunity/plus_plugins/issues/3688
• Reddit (React Native — activity launch blocked on Android 15): https://www.reddit.com/r/reactnative/comments/1k1zpk0/android_15_background_activity_launch_issue/
• Google Issue Tracker (NFC broken Android 15 Beta 2): https://issuetracker.google.com/issues/340933949
• Google Issue Tracker (NFC service dead / attempted recover): https://issuetracker.google.com/issues/341807213
• Google Issue Tracker (NFC crash DeadObjectException Android 16): https://issuetracker.google.com/issues/456078994
Core feature: PC Connection for NFC HSM (Chromium extension)
This section ties the foreground service to a core workflow. It also clarifies what breaks when the service stops.
Local phone ↔ desktop session: purpose and bounded scope
In practice, the Android app opens a local phone ↔ desktop session. Through this session, the Chromium-based extension sends explicitly authorized requests to the phone. Consequently, operations stay limited to NFC HSM actions defined by the user.
Local encrypted channel: segmented-key protocol and per-session unique key
Next, the session uses a local encrypted channel. It applies a segmented-key protocol and generates a unique key per session. As a result, the design avoids secret reuse and improves resilience against local interception.
Local HTTP endpoint: configurable port and anti-ambiguity (10001)
To support desktop calls, the service exposes a local HTTP endpoint on a configurable port (default: 10001). Therefore, the endpoint serves one purpose only: PC Connection. It does not act as a proxy, a tunnel, or a generic network relay.
Moreover, the endpoint remains session-bounded (unique per-session key, limited duration, immediate STOP). Accordingly, it provides no routing capability (no proxy, no tunnel, no routing).
User-initiated trigger: visible, stoppable, bounded
Importantly, the app does not run an “always-on” background daemon. Instead, the user triggers a perceptible session that stays time-bounded and stoppable at any moment.
Reviewer point: the user starts the PC Connection session explicitly. Without an explicit user action (PC Connection activation / expected usage), the app does not keep a foreground service running.
Finally, the workflow enables NFC HSM usage from a desktop browser without cloud dependency and without external infrastructure.
Local discovery: EviDNS Zeroconf (serverless)
On the desktop side, PC Connection relies on EviDNS Zeroconf. As a result, Freemindtronic extensions discover the phone automatically on the local network. They also retrieve its IP address and pairing port. Meanwhile, the process stays fully local: it requires no dedicated DNS/DHCP server and exposes nothing beyond the local perimeter.
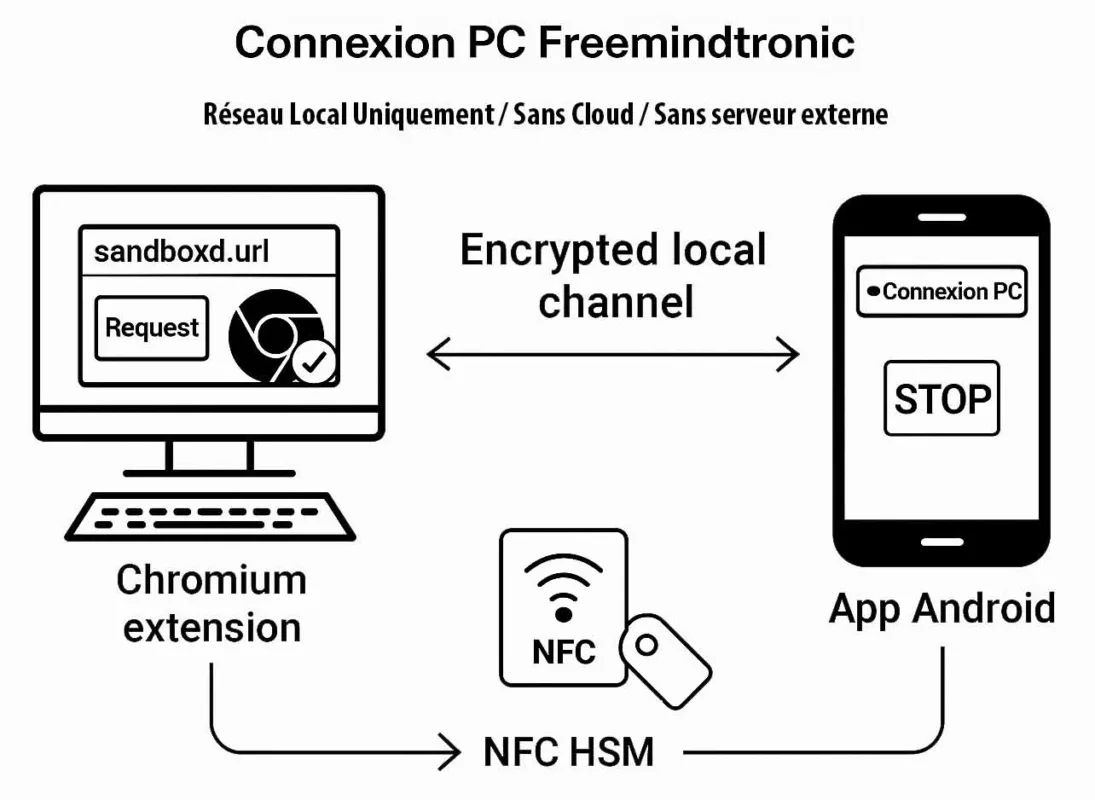
Freemindtronic secure scenario — A request initiated from the Chromium extension triggers the NFC HSM interaction on the Android phone. The secret is read locally and transmitted via a local encrypted channel based on a segmented-key protocol with a unique key per session. No external server is involved at any point.
Demonstrable functional dependency
PC Connection relies on a continuous session that remains visible and user-controlled on the Android phone. If the user presses STOP (or disables the feature), the session ends immediately. Consequently, the browser extension loses access and the desktop cannot use the NFC HSM until the user starts a new session.
EviDNS Zeroconf: serverless local pairing for desktop extensions
EviDNS Zeroconf (serverless) simplifies and secures local setup. Specifically, it supports service discovery and pairing between a desktop computer and an NFC terminal (phone) on the same network.
In practical terms, EviDNS lets desktop extensions locate the phone and retrieve the parameters required for PC Connection (IP + port). Therefore, it improves multi-OS robustness. Additionally, it removes any dependency on external infrastructure.
- Serverless: the local pairing does not rely on a dedicated DNS/DHCP server.
- Automatic discovery: the extension identifies the NFC terminal on the local network and collects IP/port for the session.
- Sovereign alignment: pairing stays within the user’s local perimeter, so the workflow does not need cloud to “keep” the connection.
- Reference: https://freemindtronic.com/technology/evidns-zeroconf-serverless-technology/
- “How it works” details: https://freemindtronic.com/technology/evidns-serverless-technology-how-it-works-find-connect-nfc-devices/
- Technical guides: https://freemindtronic.com/support/faq-technical-guides/
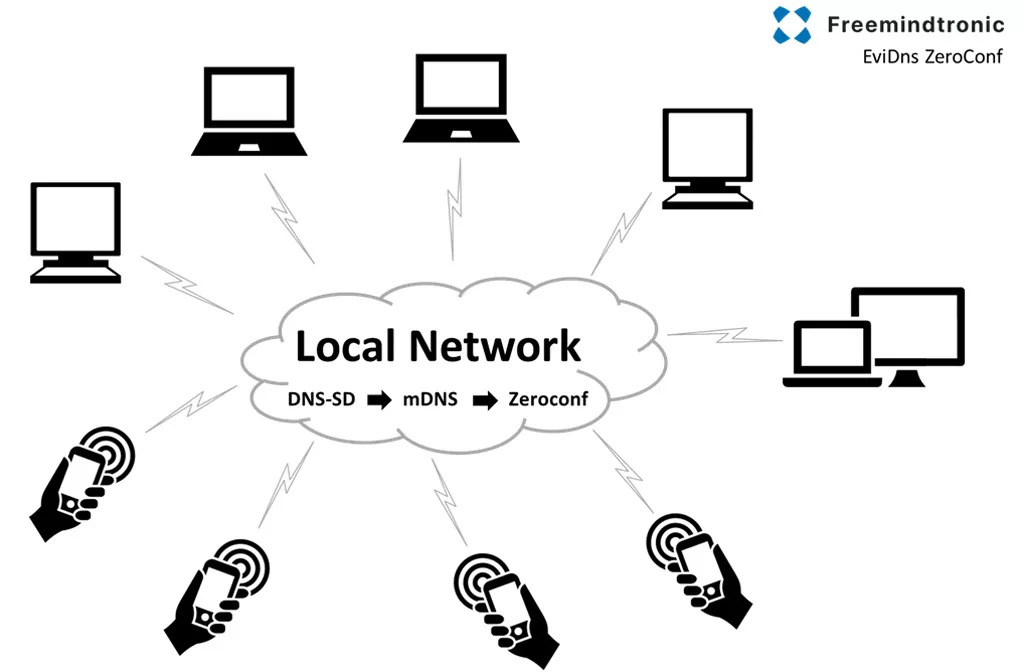
Key point
On the desktop side, Freemindtronic extensions use EviDNS Zeroconf to discover the phone on the local network and retrieve its IP address and pairing port — without a dedicated DNS/DHCP server.
Android foreground service: user controls (notification, STOP, settings)
A foreground service remains defensible only when user control is explicit, continuous, and verifiable.
This applies not only to the end user, but also to auditors and Google Play reviewers.
In practice, auto-connection may be enabled by default to preserve a smooth experience.
However, the user always retains full control.
At any time, the session can be stopped immediately through the STOP action in the notification.
In addition, the user can disable auto-login using a dedicated switch (Wi-Fi icon) in the “Freemindtronic Extension” settings.
PC Connection relies on four concrete controls that an auditor can validate within seconds:
| Control | Where it appears | What it demonstrates |
|---|---|---|
| Persistent notification | Android notification center | Session visibility; no hidden activity |
| STOP action | Button in the notification | Immediate user-driven termination (stoppable) |
| Configurable auto-connection | Extension settings (Auto-login + Wi-Fi icon) | “Enabled by default” does not mean “enforced” |
| Configurable local port | Application settings (default 10001) | Operational transparency and predictable scope |
Important note: when the user presses STOP, both the foreground service notification and the associated session terminate immediately.
By design, the system retains no residual UI state.
As a result, capturing an “after STOP” screen is impossible.
This immediate disappearance is precisely the proof that the service is stoppable and non-persistent.
Edge case (Android 13+): if the user denies the POST_NOTIFICATIONS permission, the session can no longer remain fully perceptible.
Therefore, to stay aligned with Google Play requirements, the flow must either guide the user to re-enable notifications or prevent activation of a non-visible PC Connection session.
Key proof: full and granular user control (data, alerts, port, shutdown)
One decisive point stands out: the user does not endure the foreground service.
Instead, the user controls it entirely.
This control remains observable through a persistent notification, an immediate STOP action, explicit deactivation options, and fine-grained authorization by data category.
Enabled by default, but never enforced
At installation, the auto-connection service may be enabled by default to ensure immediate availability of PC Connection.
However, this usability choice remains strictly bounded.
At any moment, the user can stop the session or disable automatic startup with a single action.
As a result, the principle remains clear: “enabled by default ≠ permanent ≠ uncontrollable.”
| Observable proof | Where | What it demonstrates |
|---|---|---|
| Persistent notification “Auto-connection service active” | Phone (Android status bar) | Session visibility and transparency |
| STOP button (shutdown action) | Android notification | Immediate user-driven termination (stoppable) |
| “Auto-login” switch (Wi-Fi icon) | User settings > “Freemindtronic Extension” | Simple and explicit deactivation |
| Configurable HTTP port (default 10001) | Service settings | Explicit local scope and clear diagnostics |
| Custom device name | Pairing settings | Local traceability and controlled association |
Least privilege enforced at the data level
One of the rare differentiators lies in the ability to restrict PC Connection to what is strictly required.
Each request category between the browser extension and the phone remains individually controlled.
Consequently, a persistent session becomes a user-bounded session rather than an open channel.
| Setting | Data type / usage | Control |
|---|---|---|
| isLogIn | Credential requests | ON / OFF |
| isLogWeb | Web extension requests | ON / OFF |
| isLogInAdd | Adding new accounts | ON / OFF |
| isLogCard | Credit card data | ON / OFF |
| isLogWebCard | Cards via web extension | ON / OFF |
| isLogCryptoMain | Cryptocurrency requests | ON / OFF |
| isLogCrypto | Detailed crypto data | ON / OFF |
| isLogIOTA | IOTA information | ON / OFF |
| isLogBank | Bank account data | ON / OFF |
| isLogBip39 | BIP39 seed phrases | ON / OFF |
| isLogPhone | Phone numbers | ON / OFF |
| isLogNote | Secure notes | ON / OFF |
| isLogCipher | Encryption keys (AES) | ON / OFF |
| isLogCloud | Cloud data (if applicable) | ON / OFF |
| isLogPing | Connection ping | ON / OFF |
Alert control: notifications, vibration, ringtone
In addition, the user can configure how the session signals activity.
This flexibility improves perceptibility while avoiding intrusive behavior.
| Setting | Function |
|---|---|
| isLogPingNotification | Notification on ping |
| isLogVibrate | Vibration on requests |
| isLogRing | Audible alert on requests |
Why this matters: a compliant foreground service is not merely “visible”.
It must also remain stoppable, disableable, and ideally rights-bounded.
Here, the user controls both the session itself and every exposed data class.
Key takeaway: the foreground service grants no extended access by default.
Instead, it materializes a visible and stoppable session boundary, within which each data category remains explicitly controlled by the user. This approach combines visibility, user control, and a measurable reduction of the attack surface, notably through the absence of keyboard input and enforced screenshot blocking.
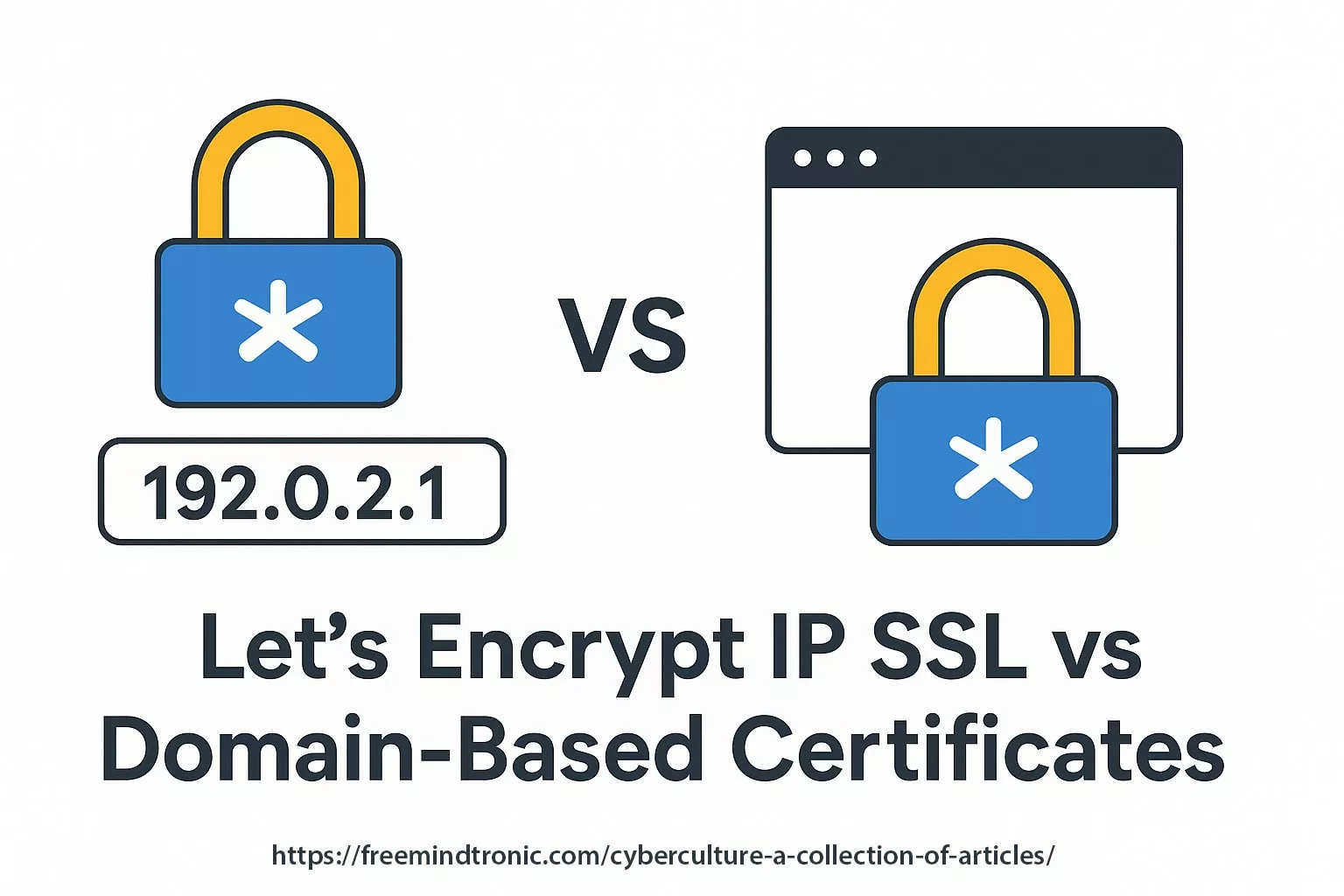
Local network scope: no proxy, no VPN, no routing
A “local session” is not a marketing claim.
Rather, it represents a measurable and verifiable architectural commitment.
The illustration below highlights a critical transparency point:
the communication port used between the Android phone and the Freemindtronic browser extension is explicitly configurable by the user (default: 10001).
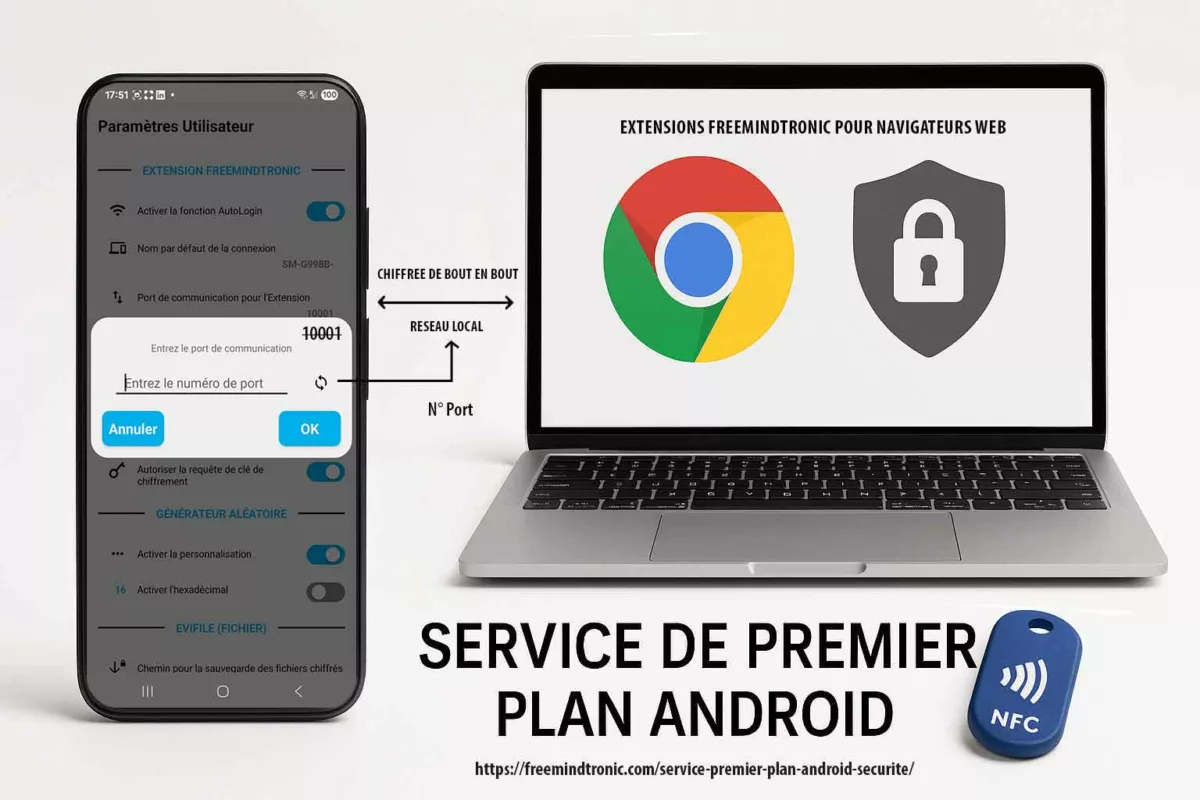
This deliberate choice allows users, auditors, and Google Play reviewers to verify immediately that PC Connection operates within a bounded and unambiguous local network scope.
Accordingly, the foreground service does not conceal any tunneling behavior, generic relay, or implicit traffic redirection.
PC Connection deliberately reduces its operational perimeter:
- No proxy: the application does not function as a generic HTTP or SOCKS proxy and does not relay third-party traffic.
- No VPN: it creates no network tunnel, does not intercept browsing activity, and does not implement
VpnService. - No routing: the feature does not redirect remote traffic or act as a network gateway.
- Explicit, configurable port: the exchange port (default 10001) remains visible, modifiable, and limited to PC Connection.
- No cloud dependency: no external server is required to maintain the session.
This explicit network bounding aligns with the Freemindtronic sovereign model:
no account, no user identification, and no central database.
All exchanges remain confined to the user’s local network, while secrets stay under user control and protected by NFC HSM devices.
Key point: port configurability is not an implementation detail.
Instead, it proves that PC Connection operates neither as a proxy nor as a VPN, but as a visible, auditable, local session enabled by a strictly bounded Android foreground service.
What the PC Connection does not do
- It does not collect user data for analytics or profiling purposes.
- It does not transfer secrets to any remote server; the session is designed to remain local-only.
- It does not operate as a proxy or a VPN and performs no generic traffic interception.
- It does not run silently in the background; the notification and STOP action make the state observable at all times.
Turning compliance into a competitive advantage
Beyond baseline requirements, PC Connection applies least privilege at the data level through per-category granular permissions.
Few competing solutions implement this level of control.
Meanwhile, store policies now require security applications to document and demonstrate their behavior.
This obligation is not a formality; instead, it acts as a maturity filter.
Over time, solutions that cannot explain a persistent activity in a verifiable way expose themselves to:
- publication rejections and prolonged review cycles,
- operating system–level restrictions,
- loss of trust caused by opaque behavior,
- increased regulatory pressure on sensitive use cases.
By contrast, the Freemindtronic implementation makes the foreground service measurable.
The session remains visible, stoppable immediately, configurable through auto-login settings, and strictly bounded to a local scope.
As a result, this operational clarity aligns with high-assurance environments.
It also becomes a differentiator when other solutions rely on ambiguous background behavior.
| Approach | Visible (notification) | Immediate stop | Per-data-type granularity | Local scope | Cloud dependency |
|---|---|---|---|---|---|
| Freemindtronic (PC Connection) | Yes | Yes (STOP + auto-login disable) | Yes (per category) | Yes (local-only) | No |
| Generic “background” approach | Often no | Often no | Rarely | Variable | Often yes |
| “Cloud-first” approach | Variable | Variable | Variable | No (network-dependent) | Yes |
Verifiable transparency: downloads, signatures, version history
A trust marker does not rely on statements alone.
Instead, it must allow independent verification.
For this reason, Freemindtronic publishes resources that support auditability and long-term software traceability.
| Resource | What it provides | Link |
|---|---|---|
| Official downloads | Direct access to software, version information, and checksums (MD5/SHA256 depending on pages), enabling reproducible verification | https://freemindtronic.com/support/download/ |
| Version history | Traceability of changes over time (internal audit, compliance, change justification) | https://freemindtronic.com/version-history-of-software-freemindtronic-andorra/ |
| Technical guides (FAQ) | Procedures, IP/port references, and architectural explanations for support and audit | https://freemindtronic.com/support/faq-technical-guides/ |
This documented transparency reinforces the credibility of a “local-only” architecture.
It also strengthens the ability to meet compliance requirements without relying on an opaque cloud layer.
Implementation checklist for auditors
The following points can be verified quickly by a reviewer, an auditor, or a security team.
This checklist also serves as a practical guide for any solution that must justify a foreground service in a sensitive context.
- Visible: a persistent notification clearly indicates an active session.
- Stoppable: a STOP action is directly accessible from the notification.
- Configurable: auto-connection can be disabled in user settings (extension: Auto-login).
- Minimal duration: the service runs only during the PC Connection session.
- Bounded scope: communication remains local; no proxy, VPN, or routing behavior.
- Least privilege: granular permissions are enforced per data category.
- Operational transparency: the port is configurable and behavior remains deterministic.
Evidence pack (Google Play review / internal audit)
To reduce back-and-forth, provide the following minimum evidence set during review:
- Capture 1: persistent notification showing “Auto-connection service active”.
- Capture 2: the STOP action visible inside the notification.
- Capture 3: “Freemindtronic Extension” settings page with the Auto-login switch and the Wi-Fi icon.
- Capture 4: port screen (default 10001) plus the phone name (pairing).
- Capture 5: an example of granular controls (at least 5 categories ON/OFF).
This evidence pack is designed for a Google Play reviewer evaluating a foreground service.
It provides observable, reproducible artifacts aligned with official requirements.
What Google Play can verify without reading the code
- A persistent notification is present during a PC Connection session
- The service stops immediately through STOP (no residual state)
- The browser extension loses the session instantly
- No
VpnServicedeclaration is involved - The local port is explicit (10001 by default, configurable)
These checks are sufficient to establish FGS compliance without source inspection.
What the reviewer will NOT see
- No source code to analyze in order to understand behavior.
- No remote server, no cloud, and no third-party API involved.
- No network tunnel, no VPN, and no implicit proxy behavior.
- No invisible persistent activity after STOP.
- No screenshots can be captured on sensitive screens in production builds (system-level screenshot locking).
- No keyboard input is required during PC Connection usage (on both phone and computer), making keylogger attacks ineffective.
Video plan (60–90 s): enable PC Connection → show the notification → press STOP → relaunch → disable Auto-login → confirm it does not restart → show port 10001 → prove the extension loses the session when STOP is pressed.
Android foreground service: evidence ↔ Google Play requirements mapping (reviewer view)
| Google Play requirement | Evidence provided | What the reviewer checks |
|---|---|---|
| Core feature with user benefit | PC Connection demo (extension ↔ phone) | The service is required for the primary workflow |
| Perceptible at all times | Persistent notification | No “hidden” execution |
| Stoppable on demand | STOP action inside the notification | Immediate stop with minimal friction |
| Cannot be deferred without breaking UX | Immediate session loss on the extension side when STOP is pressed | Demonstrable functional dependency |
| Minimal / bounded duration | Service runs only during the PC Connection session | No persistence beyond the need |
- Google Play policy (FGS requirements): https://support.google.com/googleplay/android-developer/answer/13392821
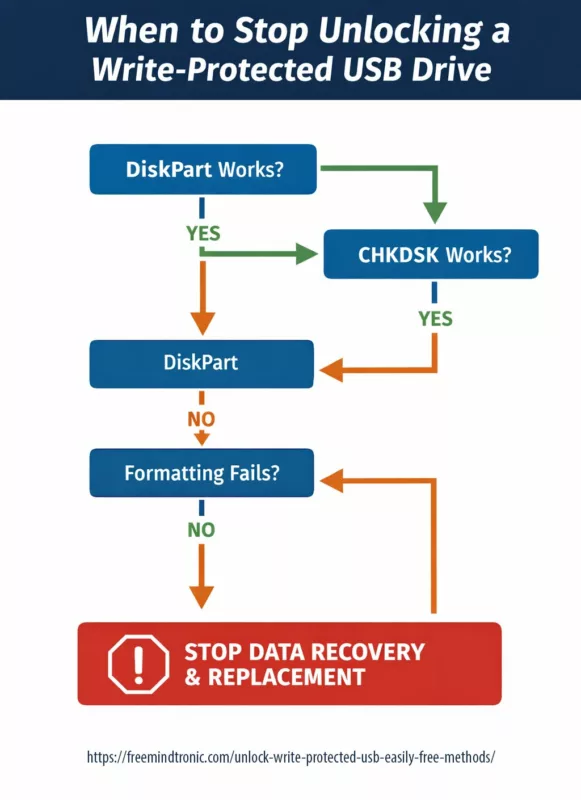
Quick audit: verify an Android foreground service and the local-only scope (2 minutes)
This procedure allows an auditor or a reviewer to verify, within minutes, three core properties: visibility, immediate stoppability, and a strict local-only scope.
- Verify perceptibility: enable PC Connection, then open the Android notification shade and confirm the presence of a persistent notification.
- Verify stoppability: press STOP in the notification and confirm that the session terminates immediately.
- Verify deactivation: in the “Freemindtronic Extension” settings, disable auto-login (switch + Wi-Fi icon), then confirm that no automatic restart occurs.
- Verify functional dependency: observe that the browser extension loses the session as soon as the service stops.
- Verify local scope: confirm that the port (default 10001) is a local parameter and that no cloud service is required for the session to operate.
Tip: on the extension side, automatic phone discovery (IP + port) can rely on EviDNS Zeroconf (serverless). This approach simplifies local pairing without requiring any dedicated infrastructure.
References: https://freemindtronic.com/technology/evidns-zeroconf-serverless-technology/ and https://freemindtronic.com/support/faq-technical-guides/
Sovereign use case: transparency and operational continuity
In sovereign or high-constraint environments, the worst scenario is not only an incident.
More critically, it is an operational dead end caused by an opaque tool.
A feature that silently depends on background execution may be restricted by the OS and fail precisely when it matters most.
By designing PC Connection around a foreground service that is visible, stoppable, configurable, and strictly local, the user can prove—at runtime—what is executing and why.
As a result, this transparency increases resilience against policy hardening.
It also reduces the risk of last-minute incompatibilities during sensitive deployments.
Finally, when comparable scenarios involve attempted exfiltration, a hardware-rooted sovereign approach limits the impact.
If secrets remain confined to NFC HSM devices and operations stay explicitly mediated by the user, any data recovered out of context remains unusable in clear form.
Note: PC Connection does not rely on the Play Integrity API or on SafetyNet to operate.
Compliance rests on observable mechanisms (notification, STOP, local scope), not on remote or opaque attestations.
Glossary
Foreground service type (FGS type)
Foreground service type API 34+
As a result, the system—and Google Play—can understand why the app runs a visible task.
Since Android 14, developers must declare an appropriate type for each foreground service and, when required, also declare the associated FGS permission.
This requirement turns a technical constraint into a compliance proof and a trust marker for audit.
Keywords: Android 14 foreground service type, API 34 FGS types required, Play Console FGS declaration.
Foreground Service declaration in Play Console
FGS declaration + reviewer video
First, the developer describes the feature that uses the foreground service.
Next, the developer explains the impact if the system defers or interrupts the task.
Finally, a video link demonstrates how the user triggers the feature, making the justification verifiable.
Keywords: Google Play foreground service requirements, foreground service video demonstration, reviewer evidence pack.
Foreground Service permission
FOREGROUND_SERVICE_* permissions
In practice, the app does more than display a notification; it aligns its manifest with the real purpose of the service.
Moreover, this granularity helps auditors verify that the app does not over-declare capabilities.
Keywords: FOREGROUND_SERVICE permission Android, manifest permission API 34, least privilege Android service.
Foreground service notification
Persistent notification and immediate control
It materializes the ongoing execution and exposes an immediate control (STOP), proving that the task remains stoppable.
This visible signal directly satisfies the Google Play rule: no hidden activity.
Keywords: foreground service notification, visible foreground service, stop foreground service.
POST_NOTIFICATIONS
Android 13+ notification permission
If the user denies notifications, the app must remain consistent with the “perceptible” requirement.
Accordingly, the flow should either guide the user or prevent activation of a non-visible session.
This behavior strengthens the store-readiness of an FGS workflow.
Keywords: Android 13 notification permission, foreground service notification blocked, perceptible to user.
shortService / systemExempted
FGS exceptions (special cases)
However, these cases do not apply to typical persistent session usage.
Therefore, a security app benefits from stating that it remains within the standard model:
core feature, notification, STOP, and minimal duration.
Keywords: short foreground service, systemExempted foreground service, foreground service policy.
Reference: https://support.google.com/googleplay/android-developer/answer/13392821
Demonstrable functional dependency
Immediate test (STOP proof)
FAQ — Android foreground service
Why must an FGS be declared in Play Console, and not only in the manifest?
Google Play reviewer requirements: description, impact, video
It also evaluates the user-facing justification.
For each declared foreground service type, the developer must describe the feature, explain what happens if the task is deferred or interrupted, and provide a video showing the user action that triggers PC Connection.
As a result, this process reduces reviewer back-and-forth and makes the FGS auditable.
Reference: https://support.google.com/googleplay/android-developer/answer/13392821
Why choose CONNECTED_DEVICE instead of REMOTE_MESSAGING for PC Connection?
Type justification: NFC HSM and local gateway
Instead, it maintains a local session that serves a hardware-based use case: accessing an NFC HSM from a desktop via a Chromium extension.
In this model, the phone acts as an active gateway to a device and to a bounded local flow.
Moreover, STOP immediately terminates the session, which proves functional dependency without implicit persistence.
Keywords: CONNECTED_DEVICE NFC, foreground service connected device use case, local-only phone-to-browser bridge.
Reference: https://support.google.com/googleplay/android-developer/answer/13392821
Does the foreground service turn the app into a proxy, VPN, or network relay?
No: strict local-only scope and user control
PC Connection implements neither a proxy, nor a VPN, nor any form of routing.
Instead, it maintains a strictly local-only session and exposes it visibly through a notification.
The user can stop the session instantly via STOP, at which point the extension immediately loses access to the NFC HSM.
Keywords: no VpnService, no Android proxy, local-only foreground service security.
What changes with Android 15 for foreground services in security workflows?
Duration, user action consistency, immediate STOP
Consequently, it favors implementations that start on a user action, remain visible, and stop immediately on demand.
Therefore, a short, local-only, stoppable session becomes more robust than implicit persistence.
Reference: https://developer.android.com/about/versions/15/changes/foreground-services
If Android blocks or stops the service, how can it be diagnosed without background workarounds?
FGS troubleshooting: understand refusals and fix them cleanly
Next, use the official Foreground Services diagnostics to identify “not allowed” errors and operational limits.
By doing so, you correct the root cause instead of bypassing the framework.
Reference: https://developer.android.com/develop/background-work/services/fgs/troubleshooting
What should the Play Console video show to validate a foreground service?
User trigger, notification, STOP, immediate impact
Then display the persistent notification to prove perceptibility.
Next, press STOP to demonstrate immediate termination.
Finally, show the functional impact: the extension loses the session as soon as the service stops, proving the task cannot be deferred without breaking the expected experience.
Reference: https://support.google.com/googleplay/android-developer/answer/13392821
If the user blocks notifications, does PC Connection remain compliant?
Perceptible also means controllable
Google Play expects execution to remain perceptible.
Therefore, if notifications are blocked (Android 13+), the app must stay consistent: either guide the user to re-enable notifications or adapt the flow to avoid a non-visible active session.
This approach preserves the “visible, stoppable, bounded” logic and reduces reviewer confusion.
Keywords: foreground service notification blocked, Android 13 POST_NOTIFICATIONS, perceptible to user.
Reference: https://support.google.com/googleplay/android-developer/answer/13392821
Why does Google insist on “user-initiated” for a foreground service?
The session starts because the user wants it
Instead, it must serve a core feature that the user triggers and understands.
Accordingly, the app ties the start to an explicit action (PC Connection), exposes the state through a notification, and provides immediate termination via STOP.
This design demonstrates continuous user intent and avoids any interpretation of “disguised persistence”.
Reference: https://support.google.com/googleplay/android-developer/answer/13392821
If Android refuses to start the service (“Start not allowed”), what should be done?
Diagnose first, then fix type, permission, and scenario
Then consult the official Foreground Services diagnostics, which document common “not allowed” causes and expected fixes.
By addressing the cause instead of bypassing background limits, Play compliance remains intact.
Reference: https://developer.android.com/develop/background-work/services/fgs/troubleshooting
What is an Android foreground service?
Official definition and security role
It always displays a persistent notification indicating ongoing activity.
This model prevents sensitive background execution and now serves as a transparency and security marker.
Official reference: https://developer.android.com/develop/background-work/services/foreground-services
How do you start a foreground service on Android?
User-initiated start and immediate notification
The user triggers a core feature (for example, PC Connection), after which the app starts the service and displays the persistent notification immediately.
Since Android 14, the app must also declare a consistent service type and, when required, the associated permission.
Official reference: https://developer.android.com/develop/background-work/services/fgs/declare
Why must a foreground service display a notification?
Perceptibility, user control, and auditability
It is the core user-control mechanism.
It makes the task perceptible, enables an immediate stop (for example, STOP), and prevents any hidden activity.
For Google Play and Android, a sensitive task without a notification equals non-compliance.
Reference: https://support.google.com/googleplay/android-developer/answer/13392821
How can foreground service notifications be removed?
Stop the service instead of hiding its state
The only correct way to remove the notification is to stop the service.
If notifications are blocked at the system level (Android 13+), the app must avoid maintaining a non-perceptible session or guide the user to restore visibility.
Official reference: https://developer.android.com/develop/background-work/services/foreground-services
Related links
- Tech Fixes & Security Solutions category:
https://freemindtronic.com/tech-fixes-security-solutions/ - Technical News category:
https://freemindtronic.com/news/technical-news/ - Digital Security category:
https://freemindtronic.com/news/digital-security/ - EviDNS Zeroconf technology (serverless):
https://freemindtronic.com/technology/evidns-zeroconf-serverless-technology/ - EviDNS: how it works (IP/port discovery):
https://freemindtronic.com/technology/evidns-serverless-technology-how-it-works-find-connect-nfc-devices/ - Technical FAQ guides (EviDNS / IP + port):
https://freemindtronic.com/support/faq-technical-guides/ - Official downloads (MD5/SHA256 hashes):
https://freemindtronic.com/support/download/ - Version history (traceability):
https://freemindtronic.com/version-history-of-software-freemindtronic-andorra/ - Freemindtronic technologies overview:
https://freemindtronic.com/technology/ - Freemindtronic overview:
https://freemindtronic.com/freemindtronic/ - Application — Freemindtronic (EviPro) on Google Play:
https://play.google.com/store/apps/details?id=com.freemindtronic.EviPro
Service premier plan Android : conformité Google Play, contrôle utilisateur et Connexion PC NFC HSM via extension Chromium. Ce dossier montre comment une exigence Foreground Service (FGS) devient un marqueur de confiance : session local-only (sans proxy, sans VPN, sans routage), appairage local EviDNS Zeroconf, notification persistante avec bouton STOP, contrôle granulaire des données et audit rapide vérifiable.
Résumé exécutif
Contexte
Android durcit l’exécution en arrière-plan (background execution) et renforce l’encadrement des services de premier plan (Foreground Services) afin de limiter l’activité invisible, réduire les abus et améliorer fiabilité et autonomie. Sur Android 16 (API level 36), cette exigence devient vérifiable et incontournable. Loin d’être une contrainte pénalisante, un service de premier plan correctement conçu devient un marqueur de confiance : transparence, contrôle utilisateur et périmètre opérationnel minimal.
Objectif
Documenter, de manière vérifiable, l’usage d’un service de premier plan Android comme brique indispensable à une fonctionnalité cœur : Connexion PC. L’objectif est de montrer comment une exigence Google Play devient un marqueur de transparence, de contrôle utilisateur et de maturité sécurité.
Portée
Fonction analysée : Connexion PC (téléphone ↔ ordinateur) pour utiliser des dispositifs NFC HSM via une extension navigateur Freemindtronic basée sur Chromium, sans installer de logiciel sur le poste. Session local-only (pas de proxy, pas de VPN, pas de routage), port configurable (défaut 10001).
Doctrine
Le service n’est pas utilisé pour “rester actif”, mais pour rendre une session sensible visible, stoppable et désactivable : notification persistante, bouton STOP, auto-login réversible, et contrôle granulaire des catégories de données autorisées.
Différenciateur stratégique
Dans un contexte de durcissement Android/Google Play, les solutions opaques deviennent fragiles. Une implémentation démontrable (contrôle utilisateur + périmètre local + transparence) devient un avantage concurrentiel. Ce dossier explique pourquoi ce service existe, comment l’utilisateur le maîtrise, et en quoi cette approche transforme une exigence de conformité en atout stratégique.
À retenir
Le service de premier plan Android est utilisé uniquement pour maintenir une session Connexion PC visible et stoppable (notification persistante + STOP) permettant l’usage d’un NFC HSM sur ordinateur via extension Chromium. L’utilisateur peut désactiver l’auto-login, limiter chaque catégorie de données autorisée, vérifier la portée local-only (pas de proxy/VPN/routage), et auditer la conformité en 2 minutes.
📱 Application Freemindtronic (EviPro) sur Google Play clic ici
Note technique
Temps de lecture (résumé) : ~2 minutes
Temps de lecture (intégral) : ~20–25 minutes
Temps de vérification (audit rapide) : ~2 minutes
Date de publication : 2026-01-16
Dernière mise à jour : 2026-01-20
Niveau : Android / Sécurité / Audit
Posture : Local-only, user-in-control, least privilege
Rubrique : Tech Fixes & Security Solutions
Langues disponibles : FR · EN · CAT · ES
Niveau d’enjeu : 8.4 / 10 — conformité store, transparence logicielle & sécurité des sessions locales
En sécurité mobile et Android ↑ cette note appartient à la rubrique Tech Fixes & Security Solutions et s’inscrit dans l’outillage opérationnel souverain de Freemindtronic (HSM, contrôle utilisateur, architectures local-only, audit).
- Résumé exécutif
- Service premier plan Android : pourquoi il est devenu un marqueur de sécurité
- Threat Model : session mobile ↔ desktop, risques et bornage
- Service premier plan Android : exigences Google Play (sources officielles)
- Android : arrière-plan vs Service premier plan Android (Foreground Service)
- Retour d’expérience : validation puis rejet sur la déclaration Foreground Service Connected Device
- Un signal de rejet ambigu, documenté par la communauté
- Pourquoi ce type de rejet est difficile à diagnostiquer
- Stratégie de résolution : rendre la justification non équivoque
- Android 14+ — Service premier plan Android (FGS) : type déclaré et justification vérifiable
- Impact produit et mitigation (Android 15/16, NFC, BAL et spécificités OEM)
- Charge de compatibilité et impacts sur le cycle de mise à jour
- Fonction cœur : Connexion PC pour NFC HSM (extension Chromium)
- EviDNS Zeroconf : appairage local serverless pour extensions desktop
- Service premier plan Android : contrôles utilisateur (notification, STOP, réglages)
- Moindre privilège : autorisations granulaires
- Preuve clé : contrôle utilisateur total et granulaire (données, alertes, port, arrêt)
- Actif par défaut, mais jamais imposé
- Moindre privilège appliqué au niveau des données
- Contrôle des alertes : notifications, vibration, sonnerie
- Portée locale : ni proxy, ni VPN, ni routage
- Ce que la Connexion PC ne fait pas
- Transformer la conformité en avantage concurrentiel
- Transparence vérifiable : téléchargements, signatures, historique des versions
- Checklist d’implémentation pour auditeurs
- Kit de preuves (review Google Play / audit interne)
- Mapping preuves ↔ exigences Google Play (reviewer)
- Audit rapide : vérifier un Service premier plan Android et la portée local-only (2 minutes)
- Cas d’usage souverain : transparence et continuité opérationnelle
- Glossaire
- FAQ : Service premier plan Android (Foreground Service)
- À relier avec…
Service premier plan Android : pourquoi il est devenu un marqueur de sécurité
Un service de premier plan est destiné aux opérations qui doivent rester actives, visibles pour l’utilisateur, et arrêtables à tout moment.
Dans la pratique, il est souvent détourné par des applications qui tentent de rester actives silencieusement, d’automatiser des actions sans intention explicite, ou de maintenir une activité en arrière-plan au-delà du strict nécessaire.
Pour un produit de sécurité, la bonne posture n’est pas de « contourner la règle », mais de s’y aligner : l’utilisateur doit toujours savoir quand une session sensible est active, ce qu’elle fait, et comment l’arrêter instantanément.
Ce point devient critique lorsque le téléphone sert de passerelle entre des modules matériels (NFC HSM) et un environnement navigateur sur ordinateur.
Android : arrière-plan vs Service premier plan Android (Foreground Service)
Android durcit depuis plusieurs versions l’exécution en arrière-plan (background execution) pour limiter l’activité invisible, réduire les abus, et préserver batterie et fiabilité. Dans ce contexte, une fonctionnalité qui doit rester active sans être au premier plan doit être justifiée et rendue perceptible. C’est précisément le rôle d’un service de premier plan : rendre l’activité sensible visible (notification), stoppable (STOP), et bornée dans le temps.
Cette approche s’inscrit dans une “foreground service Android security architecture”, alignée sur les exigences de service de premier plan Android conformité Google Play, où visibilité, arrêt immédiat et périmètre local-only constituent des critères centraux.
Point clé : le bon raisonnement n’est pas « comment rester actif en arrière-plan », mais « comment rendre une dépendance persistante auditable et contrôlable ». Un Foreground Service bien conçu devient ainsi un marqueur de transparence, pas un contournement.
Source officielle Android Developers — types de services de premier plan requis (Android 14+, y compris connectedDevice pour interactions avec des périphériques comme NFC et Bluetooth) :https://developer.android.com/about/versions/14/changes/fgs-types-required
- Permission manifeste : https://developer.android.com/reference/android/Manifest.permission#FOREGROUND_SERVICE
Threat Model : pourquoi la Connexion PC doit rester visible et bornée
Hypothèse réaliste : un téléphone utilisé comme passerelle (mobile ↔ desktop) est une surface d’attaque. Le service de premier plan est ici un mécanisme de contrôle et de preuve (notification + STOP), pas un moyen de persister silencieusement.
| Risque | Exemple | Mesure Freemindtronic |
|---|---|---|
| Persistance invisible | Service actif sans que l’utilisateur le sache | Foreground Service + notification persistante + arrêt immédiat |
| Sur-autorisation | Session ouverte = accès trop large | Contrôle granulaire par type de données (moindre privilège) |
| Élargissement réseau | Proxy/VPN déguisé, routage implicite | Local-only : pas de proxy, pas de VPN, pas de routage |
| Défaillance opérationnelle | OS stoppe le service → rupture de workflow | Session explicitement dépendante du FGS, donc prévisible et vérifiable |
Protection contre les attaques par capture et interception : l’application Freemindtronic applique un verrouillage système des captures d’écran sur l’ensemble des écrans sensibles.
Ce mécanisme empêche toute capture via screenshot, screen recording ou API équivalente, y compris par des malwares résidents.
Les démonstrations et captures fournies à des fins de revue ont été réalisées à partir d’une version de debug dans laquelle cette protection est volontairement désactivée.
De plus, la Connexion PC repose sur un modèle sans contact et sans saisie clavier, ni sur le téléphone ni sur l’ordinateur.
En conséquence, les attaques par keylogger sont structurellement inopérantes, ce qui réduit significativement la surface d’attaque côté poste de travail.
Service premier plan Android : exigences Google Play (sources officielles)
Google Play encadre strictement l’usage des services de premier plan : ils doivent être justifiés par une fonctionnalité cœur bénéfique pour l’utilisateur, être perceptibles à tout moment (notification explicite), et rester arrêtables à la demande. Depuis Android 14, la déclaration d’un type de service de premier plan est obligatoire.
Références officielles Android & Google Play :
- Android 14 — Types de services de premier plan requis : https://developer.android.com/about/versions/14/changes/fgs-types-required
- Android SDK Platforms (inclut Android 16 / API 36) : https://developer.android.com/tools/releases/platforms
- Android Manifest — Permission
FOREGROUND_SERVICE: https://developer.android.com/reference/android/Manifest.permission#FOREGROUND_SERVICE - Google Play Policy — Foreground service requirements : https://support.google.com/googleplay/android-developer/answer/13392821
- Android Developers — Déclarer un Foreground Service (API 34+) : https://developer.android.com/develop/background-work/services/fgs/declare
Dans ce dossier, ces exigences sont appliquées à un cas réel et vérifiable (Connexion PC + NFC HSM), en démontrant comment le contrôle utilisateur (notification, STOP, désactivation, granularité) transforme une contrainte de conformité en preuve de maturité sécurité.
Retour d’expérience : validation puis rejet sur la déclaration Foreground Service Connected Device
Contexte réel de publication : la déclaration du type FOREGROUND_SERVICE_CONNECTED_DEVICE a été acceptée lors d’une première soumission, avec vidéo démonstrative et description justificative couvrant les exigences Android 14 et Android 15. Toutefois, lors d’une mise à jour fin décembre, la même déclaration a été rejetée avec une demande générique de « précisions supplémentaires », sans indication exploitable sur les nouveaux détails attendus.
Ce type de situation n’est pas isolé. Plusieurs développeurs rapportent des cas similaires où une déclaration Foreground Service initialement acceptée est ensuite rejetée lors d’une mise à jour, avec un message ambigu indiquant que le problème peut se situer soit dans la description justificative, soit dans la vidéo, sans préciser lequel des deux est jugé insuffisant.
Un signal de rejet ambigu, documenté par la communauté
- Reddit – r/androiddev : des développeurs décrivent des rejets répétés liés aux Foreground Services, avec des demandes de clarification sans indication précise sur la partie à corriger (texte ou vidéo). Lien : https://www.reddit.com/r/androiddev/comments/1fsuii4/has_anyone_had_repeat_issues_with_app_submission/
- Forum développeurs Zoom : rejet d’une mise à jour Play Store lié à des permissions Foreground Service, avec exigence de vidéo démonstrative jugée insuffamment explicite, sans guidance opérationnelle claire. Lien : https://devforum.zoom.us/t/app-update-rejected-due-to-foreground-service-permissions/103026
- Support Google Play Console : retours de développeurs signalant des rejets pour « information insuffisante » concernant l’usage d’un Foreground Service, sans précision sur le critère exact manquant. Lien : https://support.google.com/googleplay/android-developer/thread/299748806
Pourquoi ce type de rejet est difficile à diagnostiquer
- Absence de granularité : le message de rejet ne précise pas si la non-conformité concerne la description Play Console, la vidéo ou leur cohérence.
- Évolution implicite des attentes reviewer : une justification jugée suffisante à un instant T peut être réévaluée différemment lors d’une mise à jour.
- Critères implicites : Play attend souvent une démonstration encore plus explicite du triptyque user-initiated → perceptible → stoppable, ainsi que de la dépendance fonctionnelle immédiate.
Stratégie de résolution : rendre la justification non équivoque
Face à un rejet générique, la seule approche robuste consiste à supprimer toute ambiguïté d’interprétation.
- Texte Play Console : formuler la justification comme un test vérifiable : « si l’utilisateur appuie sur STOP, la session est interrompue immédiatement et l’extension perd l’accès au NFC HSM ».
- Vidéo : montrer sans coupe l’enchaînement action utilisateur → notification visible → STOP → perte immédiate de session côté extension.
- Alignement sémantique : reprendre explicitement les termes utilisés par Google Play : core feature, user benefit, perceptible, stoppable, cannot be deferred.
- Élimination des malentendus : rappeler explicitement « pas un VPN, pas un proxy, pas de routage, périmètre strictement local ».
Ce retour d’expérience explique pourquoi ce dossier inclut une checklist d’implémentation, un mapping preuves ↔ exigences Google Play et un kit de preuves reproductible : lorsqu’un rejet est formulé de manière générique, la seule réponse efficace reste une démonstration qui ne laisse plus de place à l’interprétation.
Android 14+ — Service premier plan Android (FGS) : type déclaré et justification vérifiable
Exigence Android 14 : justification explicite et vérifiable
Type déclaré et dépendance fonctionnelle immédiate
- Type déclaré :
FOREGROUND_SERVICE_CONNECTED_DEVICE - Fonctionnalité cœur dépendante : Connexion PC (téléphone ↔ extension Chromium)
- Justification : le téléphone agit comme passerelle active vers un dispositif NFC HSM utilisé depuis un ordinateur, sur initiative explicite de l’utilisateur.
Si le service de premier plan est arrêté (bouton STOP dans la notification ou désactivation de l’auto-login), la session Connexion PC est immédiatement interrompue et l’extension navigateur perd l’accès au NFC HSM. La tâche ne peut pas être différée par le système sans empêcher la fonctionnalité attendue.
Référence Android — Types de Foreground Services : https://developer.android.com/develop/background-work/services/fgs/service-types
Continuité de la doctrine sur Android 15
Continuité Android 15 : Android 15 renforce encore la discipline autour des services de premier plan (démarrage, usage, attentes de comportement) et la cohérence entre action utilisateur, durée d’exécution et finalité. Cette trajectoire confirme le principe « visible, stoppable, borné » et favorise les implémentations démontrables (notification explicite + STOP + dépendance fonctionnelle immédiate).
Référence : https://developer.android.com/about/versions/15/changes/foreground-services
Évolutions Android 16 (API level 36) : quotas, diagnostics et limites opérationnelles
Foreground services — changes (inclut Android 16 / API level 36) : https://developer.android.com/develop/background-work/services/fgs/changes
Cap Android 16 : Android 16 introduit un cadre renforcé de quotas, de limites d’exécution et de diagnostics, ce qui favorise les workflows courts, local-only et explicitement contrôlés plutôt que des sessions implicites ou prolongées. Référence (diagnostic) : https://developer.android.com/develop/background-work/services/fgs/troubleshooting
Android continue d’outiller le diagnostic et de resserrer les scénarios autorisés ; par conséquent, un workflow local-only, visible et stoppable reste la stratégie la plus robuste face aux durcissements successifs.
Précision de fonctionnement — application Android NFC Freemindtronic
Précision de fonctionnement : le service de premier plan est strictement événementiel. Le lancement de l’application ne suffit pas à l’activer : il démarre uniquement lorsqu’un tag NFC est présenté, puis reste inactif en l’absence d’événement NFC, sans serveur local ni service persistant.
Impact produit et mitigation (Android 15/16, NFC, BAL et spécificités OEM)
Symptôme
- Symptôme : le tag NFC est correctement détecté par le système, mais la tentative de relance ou de remise au premier plan de l’interface via
PendingIntentest bloquée par le mécanisme BAL (Background Activity Launch). L’utilisateur perçoit une absence de réaction, ou un comportement dégradé, alors que l’événement NFC est bien reçu.
Cause
- Cause : Android 15 et plus encore Android 16 durcissent officiellement les règles de lancement d’activités depuis l’arrière-plan. Les
PendingIntentcréés par l’application ne bénéficient plus implicitement du droit de lancer ou de ramener une activité au premier plan. Ce durcissement impacte directement les parcours NFC historiques reposant sur la relance d’UI viaPendingIntent, y compris lorsque l’activité cible est déjà en étatRESUMED. Référence officielle Android : https://developer.android.com/guide/components/activities/background-starts
Ce comportement est observable y compris sur Google Pixel (AOSP), confirmant qu’il s’agit d’un changement structurel de la plateforme et non d’une spécificité OEM.
Preuve technique — blocage BAL (Android 15 / 16)
Sur Android 15 et plus encore Android 16 (API level 36), le blocage du lancement d’activité depuis l’arrière-plan (Background Activity Launch) est un mécanisme structurel de la plateforme, observable directement dans les journaux système.
Extrait Logcat typique (anonymisé) lors d’un événement NFC tentant de relancer l’UI via PendingIntent :
Background activity launch blocked:
pkg=com.freemindtronic.EviPro
reason=background_activity_launch_not_allowed
intent=Intent { act=android.nfc.action.TAG_DISCOVERED ... }
callerApp=ProcessRecord{...}
Ce message confirme que :
- l’événement NFC est bien reçu par le système,
- la tentative de relance d’interface est explicitement bloquée par Android,
- le refus est indépendant de l’application et résulte du durcissement BAL de la plateforme.
Cette preuve permet de distinguer clairement : changement structurel Android ≠ bug applicatif.
- Facteur aggravant NFC (plateforme) : en parallèle des restrictions BAL, des instabilités et changements de comportement de la pile NFC sont observés sur Android 15 et Android 16, incluant des crashs du service NFC (
DeadObjectException), des échecs intermittents de lecture de tags et des différences de comportement entre versions. Ces points sont documentés dans l’Issue Tracker Google, notamment sur Android 16 : https://issuetracker.google.com/issues/456078994
Facteur aggravant NFC (OEM)
- Facteur aggravant NFC (OEM) : la problématique est accentuée sur certains appareils en raison des surcouches constructeur et des politiques d’optimisation agressives. Des retours publics et tickets font état de comportements NFC dégradés ou incohérents sur :
- Samsung Galaxy (One UI 7/8 – Android 15/16) : suspension agressive des activités, désactivation intermittente du NFC après mise à jour, et différences de comportement entre états écran allumé/éteint.
- Xiaomi / Redmi / Poco (MIUI / HyperOS – Android 15/16) : restrictions fortes en arrière-plan, interactions entre NFC, Bluetooth et économie d’énergie, entraînant des échecs de scans NFC ou des non-relances d’UI.
- OnePlus / Oppo (OxygenOS / ColorOS – Android 15/16) : gestion restrictive des tâches en arrière-plan et comportements variables du service NFC selon les builds.
- Fairphone 5 (Android 15) : régressions signalées après mise à jour, avec reconnaissance incomplète ou retardée de certains tags NFC.
- Google Pixel (Android 15/16 AOSP) : référence AOSP montrant que le blocage BAL est structurel même sans surcouche OEM, confirmant que le problème n’est pas uniquement constructeur.
Mitigation robuste
- Mitigation robuste : abandonner toute dépendance à une relance implicite d’UI via
PendingIntent. Le traitement NFC doit être effectué dans l’instance existante de l’activité lorsque celle-ci est déjà active (launchModeadapté, traitement viaonNewIntent()), ou bien être poursuivi via une action explicitement initiée par l’utilisateur (notification avec action), conformément au modèle Android “user-initiated” recommandé pour Android 15+.
À retenir : à partir d’Android 15, la détection NFC peut fonctionner correctement sans que l’interface utilisateur ne soit relancée. Le blocage Background Activity Launch (BAL) empêche toute relance implicite via PendingIntent. Une implémentation conforme doit donc traiter l’événement dans l’instance existante ou exiger une action explicite de l’utilisateur.
Limites connues / comportements non garantis par Android
- Android ne garantit pas la relance automatique d’une activité UI après un événement système (NFC, intent, PendingIntent), en particulier à partir d’Android 15 (BAL).
- Le comportement exact de la pile NFC peut varier selon la version Android, l’état du système (écran éteint, Doze, restrictions OEM) et les implémentations constructeur.
- La continuité d’une session dépend du respect du modèle user-initiated et du maintien du service de premier plan Android conformité Google Play (notification visible, STOP, durée bornée).
Ces limites sont structurelles à la plateforme Android et ne constituent ni un bug applicatif ni une déviation fonctionnelle.
Preuve et audit
- Preuve et audit : les journaux système Android permettent d’identifier explicitement les blocages BAL (“Background activity launch blocked” ou messages équivalents) lors d’événements NFC. Ces logs constituent des preuves techniques objectives à archiver dans le kit de conformité interne et à produire en cas de revue Google Play ou d’audit sécurité.
Cette dépendance fonctionnelle démontrable constitue un point clé de service de premier plan Android conformité Google Play, tel qu’attendu par les reviewers depuis Android 14+.
Charge de compatibilité et impacts sur le cycle de mise à jour
Cette section explique pourquoi ces changements ne relèvent pas d’un simple ajustement de code, mais d’une transformation structurelle des workflows Android historiques.
Depuis Android 6, la plateforme a empilé des restrictions successives qui transforment une “simple montée de targetSdk” en refactoring structurel : durcissement de l’exécution en arrière-plan et du lancement d’activités depuis l’arrière-plan (BAL), encadrement des services de premier plan (FGS) et exigences de justification associées, ainsi que variabilité du comportement NFC et de la pile système selon les versions et les implémentations OEM. À partir d’Android 15, une application qui crée des PendingIntent ne bénéficie plus implicitement des privilèges BAL : l’opt-in explicite devient requis, ce qui casse de nombreux workflows historiques (notification → relance UI, flux “événement système → ramener l’activité”, scénarios NFC, etc.).
Dans le même temps, Android 15/16 impose des changements de comportement documentés (targetSdk, compat framework changes), et des tickets publics montrent aussi des instabilités NFC à la plateforme, ce qui augmente la complexité des tests multi-appareils, multiplie les modes dégradés, et ralentit mécaniquement les cycles de publication.
Références officielles (Android/Google) :
• Restrictions BAL (Android 15+), opt-in requis pour PendingIntent : https://developer.android.com/guide/components/activities/background-starts
• Android 15 — behavior changes (targeting API 35) : https://developer.android.com/about/versions/15/behavior-changes-15
• Android 15 — compat framework changes (BAL privileges rescind by creator) : https://developer.android.com/about/versions/15/reference/compat-framework-changes
• Android 16 — behavior changes (Android 16 / API level 36) : https://developer.android.com/about/versions/16/behavior-changes-16
• Set up the Android 16 SDK (API 36) : https://developer.android.com/about/versions/16/setup-sdk
• Exigence Google Play target API level (cadence de migration imposée) : https://developer.android.com/google/play/requirements/target-sdk
• Android Developers Blog (Android 15 AOSP) — PendingIntent creators block BAL by default : https://android-developers.googleblog.com/2024/09/android-15-is-released-to-aosp.html
Retours développeurs & tickets publics (problèmes similaires) :
• StackOverflow (BAL hardening Android 15, activité bloquée via PendingIntent) : https://stackoverflow.com/questions/77679032/with-android-15-bal-hardening-this-activity-start-may-be-blocked-if-the-pi-creat
• GitHub (Flutter community — demande support opt-in BAL Android 15+, activité ne se lance plus) : https://github.com/fluttercommunity/plus_plugins/issues/3688
• Reddit (React Native — activity launch bloqué sur Android 15) : https://www.reddit.com/r/reactnative/comments/1k1zpk0/android_15_background_activity_launch_issue/
• Google Issue Tracker (NFC cassé Android 15 Beta 2) : https://issuetracker.google.com/issues/340933949
• Google Issue Tracker (NFC service dead / tentative recover) : https://issuetracker.google.com/issues/341807213
• Google Issue Tracker (Crash NFC DeadObjectException Android 16) : https://issuetracker.google.com/issues/456078994
Fonction cœur : Connexion PC pour NFC HSM (extension Chromium)
Cette section décrit concrètement la fonctionnalité cœur qui justifie l’usage d’un service de premier plan, et pourquoi son interruption entraîne immédiatement une perte de capacité opérationnelle.
Session locale téléphone ↔ ordinateur : finalité et bornage
Concrètement, l’application Android maintient une session locale téléphone ↔ ordinateur afin que l’extension Chromium puisse émettre des requêtes explicitement autorisées vers le téléphone, dans le cadre strict des opérations NFC HSM définies par l’utilisateur.
Canal chiffré local : protocole à clé segmentée et clé unique par session
Ensuite, la session s’appuie sur un canal chiffré local reposant sur un protocole à clé segmentée, avec une clé unique par session, afin d’éviter toute réutilisation de secret et de renforcer la résilience aux interceptions réseau locales.
Point de terminaison HTTP local : port configurable et anti-ambiguïté (10001)
Pour ce faire, le service expose un point de terminaison HTTP local, associé à un port configurable (par défaut 10001). Ce point de terminaison reste exclusivement dédié à la Connexion PC : il ne s’agit ni d’un proxy, ni d’un tunnel réseau, ni d’un service généraliste.
Ce point de terminaison est strictement borné à la session (clé unique par session, durée limitée, arrêt immédiat via STOP) et n’a aucune vocation de relais réseau (ni proxy, ni tunnel, ni routage).
Déclenchement user-initiated : visible, stoppable, borné
Il est important de souligner que ce mécanisme n’est pas un démon « always-on » en arrière-plan. Au contraire, il s’agit d’une session explicitement perceptible, déclenchée par l’utilisateur, bornée dans le temps, et arrêtable à tout moment.
Point reviewer : le démarrage de la session Connexion PC est strictement user-initiated : sans action explicite de l’utilisateur (activation Connexion PC / usage attendu), aucun service de premier plan n’est maintenu.
Sa seule finalité consiste à permettre l’usage d’un NFC HSM sur ordinateur via navigateur, sans dépendance cloud et sans infrastructure externe.
Découverte locale : EviDNS Zeroconf (serverless)
Côté ordinateur, cette Connexion PC s’appuie sur la technologie EviDNS Zeroconf, ce qui permet aux extensions Freemindtronic de découvrir automatiquement le téléphone sur le réseau local, d’identifier son adresse IP et son port d’appairage, puis d’établir la session, le tout sans serveur DNS/DHCP dédié et sans exposition hors du périmètre local.
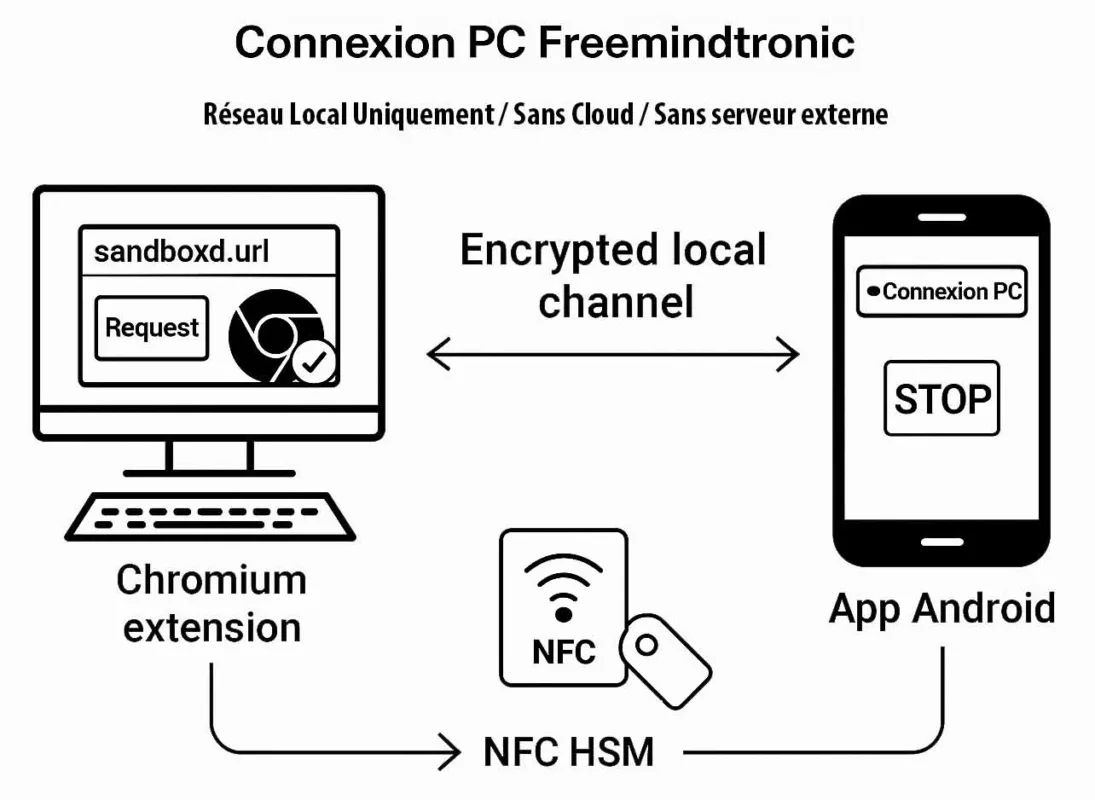
Scénario sécurisé Freemindtronic — Une requête initiée depuis l’extension Chromium déclenche l’interaction NFC HSM côté téléphone Android. Le secret est lu localement et transmis via un canal chiffré local basé sur un protocole à clé segmentée avec clé unique par session. Aucun serveur externe n’intervient à aucun moment.
Dépendance fonctionnelle démontrable
La fonctionnalité Connexion PC chiffré de bout en bout repose sur une session continue, visible et maîtrisée sur le téléphone Android. Dès que le service de premier plan est interrompu (STOP ou désactivation), l’extension navigateur perd immédiatement la session, rendant l’usage des NFC HSM sur ordinateur indisponible.
EviDNS Zeroconf : appairage local serverless pour extensions desktop
La technologie EviDNS Zeroconf (serverless) est conçue pour simplifier et sécuriser la configuration réseau en environnement local : elle facilite la découverte de services et l’association entre un ordinateur et un terminal NFC (téléphone) sur le même réseau.
Concrètement, EviDNS permet aux extensions desktop de trouver le téléphone et d’identifier les paramètres nécessaires à la Connexion PC (IP + port). Cette approche améliore la robustesse multi-OS et évite de dépendre d’une infrastructure externe.
- Serverless : aucune dépendance à un serveur DNS/DHCP dédié pour l’appairage local.
- Découverte automatique : identification du terminal NFC sur le réseau local et récupération IP/port pour la session.
- Alignement souverain : l’appairage reste dans le périmètre local de l’utilisateur, sans obligation de cloud pour “tenir” la connexion.
- Référence : https://freemindtronic.com/technology/evidns-zeroconf-serverless-technology/
- Détails “How it works” : https://freemindtronic.com/technology/evidns-serverless-technology-how-it-works-find-connect-nfc-devices/
- Guides techniques : https://freemindtronic.com/support/faq-technical-guides/
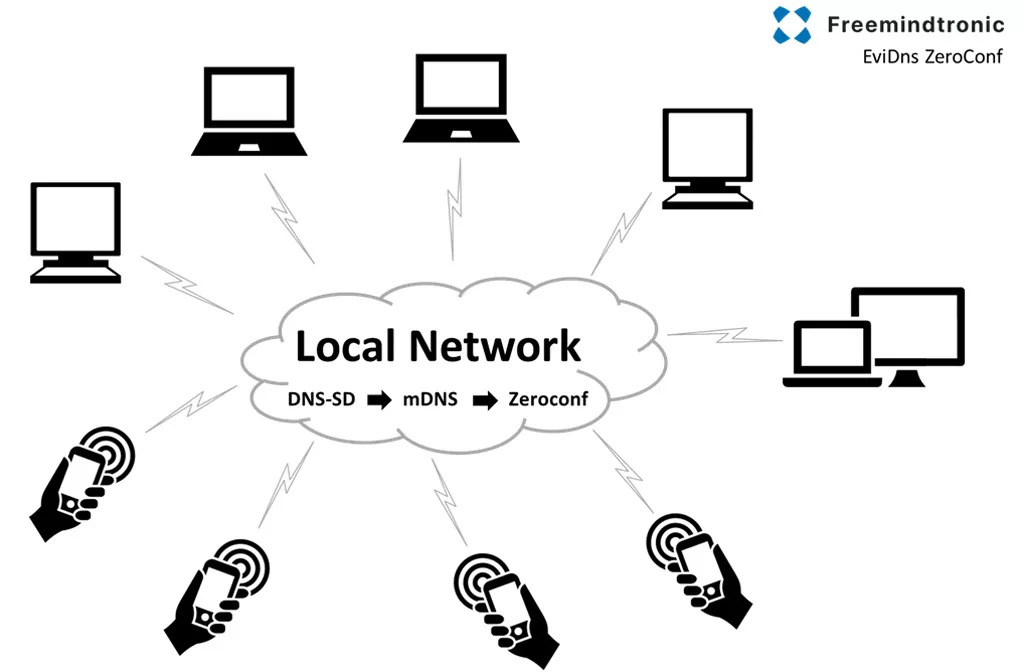
Point clé
Côté ordinateur, les extensions Freemindtronic s’appuient sur la technologie EviDNS Zeroconf pour découvrir automatiquement le téléphone sur le réseau local et obtenir son adresse IP et son port d’appairage — sans serveur DNS/DHCP dédié.
Service premier plan Android : contrôles utilisateur (notification, STOP, réglages)
Un service de premier plan est défendable lorsque le contrôle utilisateur est explicite, constant et vérifiable, aussi bien pour l’utilisateur final que pour un auditeur ou un reviewer.
L’auto-connexion peut être activée par défaut afin d’offrir une expérience fluide. Toutefois, elle reste totalement réversible : arrêt immédiat via le bouton STOP dans la notification, et désactivation de l’auto-login (switch avec pictogramme Wi-Fi) dans les paramètres « Extension Freemindtronic ».
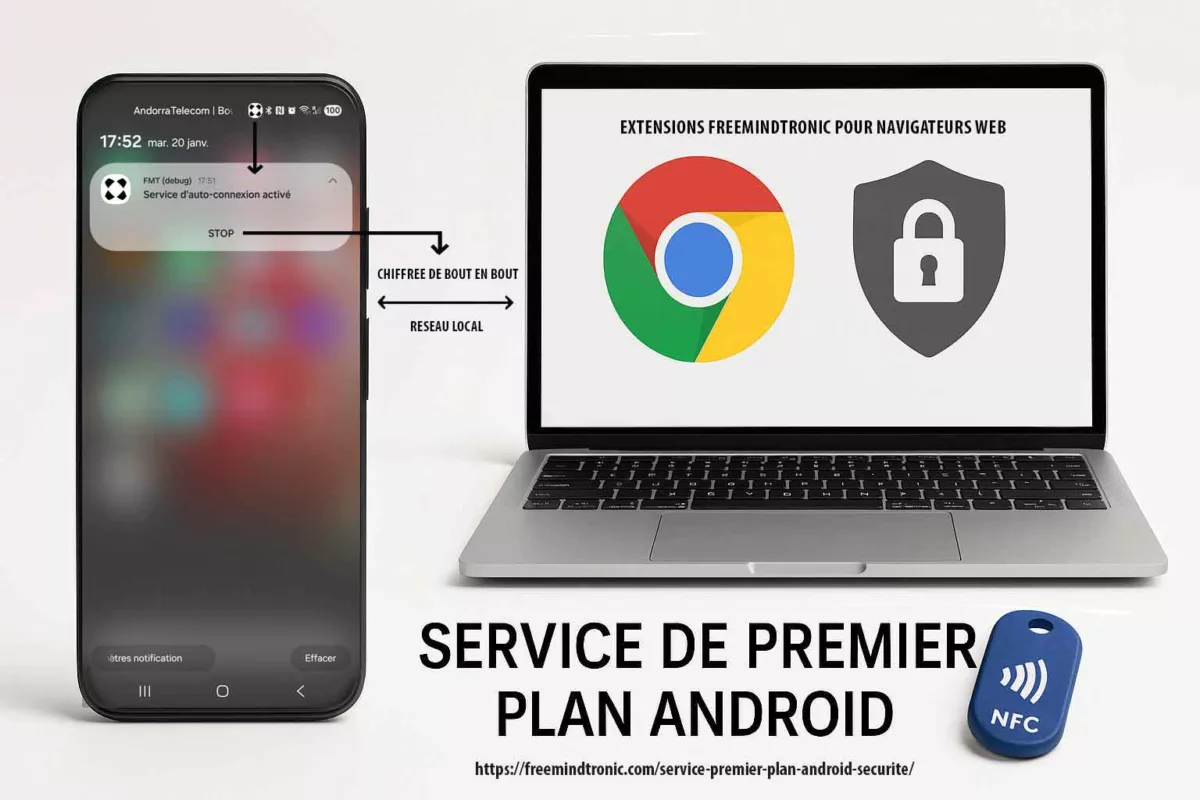
La Connexion PC s’appuie sur quatre contrôles concrets qu’un auditeur peut valider en quelques secondes :
| Contrôle | Où il apparaît | Ce que cela démontre |
|---|---|---|
| Notification persistante | Centre de notifications Android | Session visible ; aucune activité cachée |
| Action STOP | Bouton dans la notification | Arrêt immédiat à la demande (stoppable) |
| Auto-connexion configurable | Paramètres de l’extension (Auto-login + pictogramme Wi-Fi) | « Actif par défaut » ≠ « imposé » ; désactivation simple |
| Port local configurable | Paramètres de l’application (défaut 10001) | Transparence opérationnelle ; périmètre prévisible |
Note importante : lorsque l’utilisateur appuie sur STOP, la notification de service de premier plan et la session associée sont interrompues immédiatement. Par conception, aucun état résiduel n’est maintenu à l’écran, ce qui rend impossible la capture d’un « écran après STOP ». Cette disparition immédiate constitue précisément la preuve du caractère stoppable et non persistant du service.
Cas limite (Android 13+) : si l’utilisateur refuse l’autorisation POST_NOTIFICATIONS, la session ne peut plus être pleinement “perceptible”. Par cohérence avec les exigences Google Play, le parcours doit soit guider l’utilisateur pour réactiver les notifications, soit empêcher l’activation d’une session Connexion PC non visible.
Moindre privilège : autorisations granulaires
Beaucoup d’applications considèrent une session persistante comme une capacité sans limites. Freemindtronic adopte l’approche inverse.

La Connexion PC intègre une autorisation granulaire par catégories de requêtes, permettant à l’utilisateur de décider explicitement ce que l’extension a le droit de demander pendant une session active.
| Paramètre (exemple) | Objet | Rationale sécurité |
|---|---|---|
| isLogIn (identifiants) | Autoriser les requêtes d’identifiants | Réduit l’exposition si non nécessaire au workflow |
| isLogWeb (web) | Autoriser les requêtes web | Sépare navigation et gestion de secrets |
| isLogCard (cartes) | Autoriser les requêtes cartes | Garde sous contrôle une catégorie à forte valeur |
| isLogCryptoMain / isLogCrypto (crypto) | Autoriser les requêtes cryptomonnaies | Réduit la surface de risque pour les actifs |
| isLogBip39 (seed) | Autoriser les requêtes BIP39 / seed | Garde un verrou explicite sur la classe la plus sensible |
| isLogCipher (clés) | Autoriser les requêtes de clés de chiffrement | Segmente la manipulation des clés |
| isLogPing (connexion) | Autoriser les pings | Contrôle et diagnostic transparents |
Autrement dit : le service de premier plan ne signifie pas « accès étendu ». Il fournit une frontière de session, et l’utilisateur contrôle ce qui peut se produire à l’intérieur de cette frontière.
Preuve clé : contrôle utilisateur total et granulaire (données, alertes, port, arrêt)
Un point décisif l’utilisateur ne subit pas le service de premier plan. Il le contrôle entièrement : notification persistante, arrêt instantané, désactivation dans les paramètres, et autorisation granulaire par type de données.
Actif par défaut, mais jamais imposé
Le service d’auto-connexion peut être actif par défaut à l’installation afin d’assurer une disponibilité immédiate de la Connexion PC. Ce choix d’ergonomie est encadré par des mécanismes d’arrêt et de désactivation accessibles en un geste, ce qui répond au principe : “actif par défaut ≠ permanent ≠ incontrôlable”.
| Preuve observable | Où | Ce que cela démontre |
|---|---|---|
| Notification persistante “Service d’auto-connexion active” | Téléphone (barre d’état Android) | Session perceptible ; transparence |
| Bouton STOP (action d’arrêt) | Notification Android | Arrêt immédiat par l’utilisateur (stoppable) |
| Switch “Auto-login” (picto Wi-Fi) | Paramètres utilisateur > “Extension Freemindtronic” | Désactivation simple du démarrage automatique |
| Port HTTP configurable (défaut 10001) | Paramètres de service | Périmètre local explicite ; diagnostic clair |
| Nom du téléphone personnalisable | Paramètres d’appairage | Traçabilité locale et maîtrise de l’association |
Moindre privilège appliqué au niveau des données
L’un des points les plus rares sur le marché est la capacité à limiter la Connexion PC au strict nécessaire en contrôlant
individuellement chaque type de requête autorisée entre l’extension navigateur et le téléphone.
Cela transforme une session persistante en session bornée par l’utilisateur.
| Paramètre | Type de données / usage | Contrôle |
|---|---|---|
| isLogIn | Requêtes d’identifiants | ON / OFF |
| isLogWeb | Requêtes via extension web | ON / OFF |
| isLogInAdd | Ajout de nouveaux comptes | ON / OFF |
| isLogCard | Requêtes cartes de crédit | ON / OFF |
| isLogWebCard | Cartes via extension web | ON / OFF |
| isLogCryptoMain | Requêtes cryptomonnaies | ON / OFF |
| isLogCrypto | Données crypto détaillées | ON / OFF |
| isLogIOTA | Informations IOTA | ON / OFF |
| isLogBank | Requêtes comptes bancaires | ON / OFF |
| isLogBip39 | Seed phrases BIP39 | ON / OFF |
| isLogPhone | Numéros de téléphone | ON / OFF |
| isLogNote | Notes sécurisées | ON / OFF |
| isLogCipher | Clés de chiffrement (AES) | ON / OFF |
| isLogCloud | Données cloud (si applicable) | ON / OFF |
| isLogPing | Ping de connexion | ON / OFF |
Contrôle des alertes : notifications, vibration, sonnerie
L’utilisateur peut également configurer la manière dont la session est signalée, ce qui renforce la perceptibilité sans imposer une expérience intrusive.
| Paramètre | Fonction |
|---|---|
| isLogPingNotification | Notification lors d’un ping |
| isLogVibrate | Vibration lors des requêtes |
| isLogRing | Sonnerie lors des requêtes |
Pourquoi c’est structurant : un service de premier plan conforme n’est pas seulement “visible”.
Il doit être arrêtable, désactivable, et idéalement borné en droits.
Ici, l’utilisateur garde la main sur la session et sur chaque classe de données exposée à l’extension.
À retenir : le service de premier plan ne confère aucun accès étendu par défaut. Il matérialise une frontière de session visible et stoppable, à l’intérieur de laquelle chaque catégorie de données reste explicitement contrôlée par l’utilisateur. Cette approche combine visibilité, contrôle utilisateur et réduction mesurable de la surface d’attaque, notamment via l’absence de saisie clavier et le verrouillage des captures d’écran.
Portée locale : ni proxy, ni VPN, ni routage
« Session locale » n’est pas un argument marketing. C’est un engagement d’architecture mesurable et vérifiable.
L’illustration ci-dessous montre un point clé de cette transparence : le port de communication utilisé pour l’échange entre le téléphone Android et l’extension navigateur Freemindtronic est explicitement configurable par l’utilisateur (10001 par défaut).
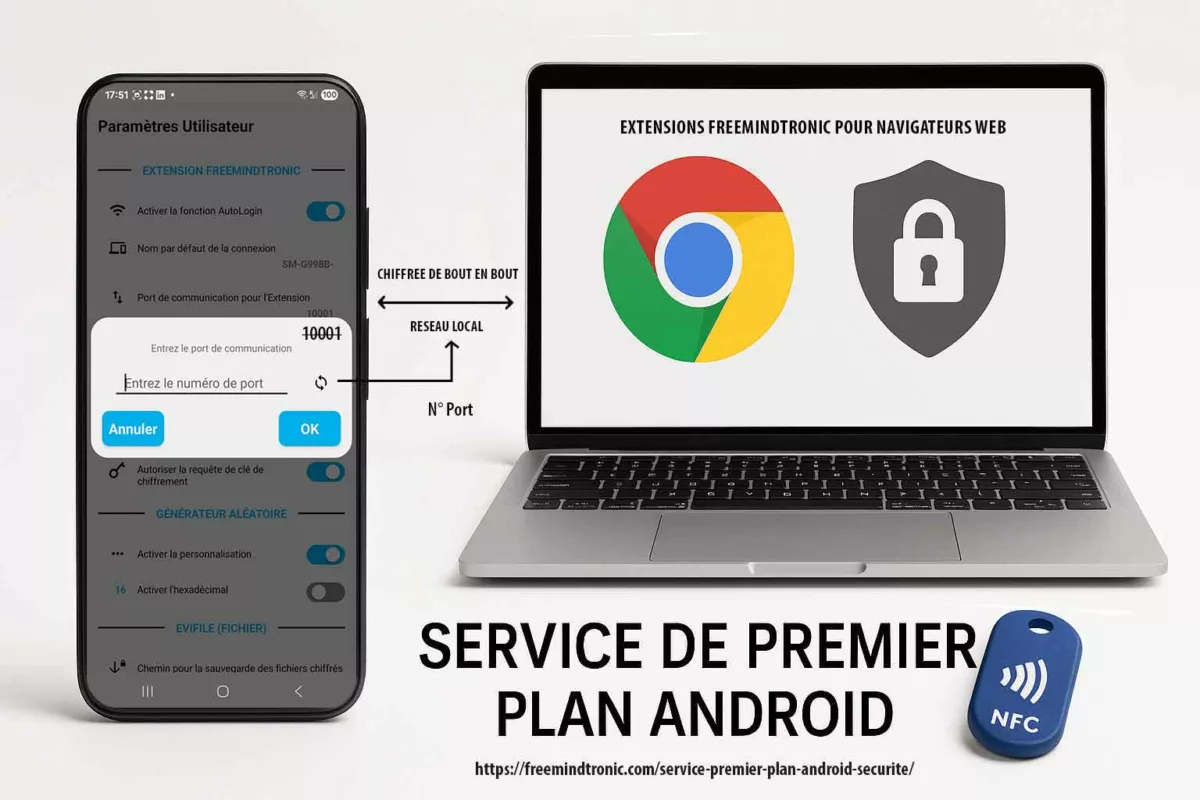
Ce choix volontaire permet à l’utilisateur, à un auditeur ou à un reviewer Google Play de vérifier immédiatement que la Connexion PC repose sur un périmètre réseau borné, local et non ambigu. Il démontre que le service de premier plan ne masque aucun comportement de tunnel, de relais générique ou de redirection réseau implicite.
La Connexion PC est conçue pour réduire strictement le périmètre opérationnel :
- Pas de proxy : l’application n’est pas un proxy HTTP/SOCKS généraliste et ne relaie pas des flux tiers.
- Pas de VPN : elle ne crée aucun tunnel réseau, n’intercepte pas la navigation et n’implémente pas de
VpnService. - Pas de routage : la fonctionnalité ne redirige pas de trafic distant et ne sert pas de passerelle réseau.
- Port explicite et configurable : le port d’échange (10001 par défaut) est visible, modifiable et limité à la Connexion PC.
- Pas de dépendance cloud : aucun serveur externe n’est requis pour maintenir la session.
Ce bornage réseau explicite s’inscrit dans le modèle souverain Freemindtronic : pas de compte, pas d’identification, pas de base centrale. Les échanges restent confinés au réseau local de l’utilisateur, et les secrets demeurent sous contrôle utilisateur, protégés par les dispositifs NFC HSM.
À retenir : la possibilité de modifier le port n’est pas un détail d’implémentation. C’est une preuve que la Connexion PC ne fonctionne ni comme un proxy, ni comme un VPN, mais comme une session locale, visible et auditabile, rendue possible par un service de premier plan Android strictement borné.
Ce que la Connexion PC ne fait pas
- Ne collecte pas de données utilisateur pour analyse ou profilage.
- Ne transfère pas les secrets vers un serveur distant : la session est conçue pour rester local-only.
- Ne fonctionne pas comme un proxy/VPN : aucune interception générale de trafic.
- Ne reste pas actif “en cachette” : la notification et STOP rendent l’état observable.
Transformer la conformité en avantage concurrentiel
Au-delà du minimum attendu, la Connexion PC applique le moindre privilège au niveau des données via des permissions granulaires par catégorie — une exigence rarement implémentée dans les solutions concurrentes. Les règles des stores obligent désormais les applications de sécurité à documenter et à démontrer leur fonctionnement. Ce n’est pas qu’une formalité : c’est un filtre de maturité.
À terme, les solutions incapables d’expliquer une activité persistante de manière vérifiable s’exposent à :
- des refus de publication et des cycles de revue prolongés,
- des restrictions au niveau du système d’exploitation,
- une érosion de la confiance liée à l’opacité,
- un renforcement de la pression réglementaire sur les usages sensibles.
L’implémentation Freemindtronic rend le service de premier plan mesurable : session visible, arrêt immédiat, auto-login configurable, périmètre local strict.
Cette clarté opérationnelle correspond aux attentes des environnements à forte assurance, et devient un différenciateur quand d’autres solutions reposent sur des comportements flous en arrière-plan.
| Approche | Visible (notification) | Arrêt immédiat | Granularité par type de données | Portée locale | Dépendance cloud |
|---|---|---|---|---|---|
| Freemindtronic (Connexion PC) | Oui | Oui (STOP + désactivation auto-login) | Oui (par catégorie) | Oui (local-only) | Non |
| Approche “background” (générique) | Souvent non | Souvent non | Rarement | Variable | Souvent oui |
| Approche “cloud-first” | Variable | Variable | Variable | Non (dépend réseau) | Oui |
Transparence vérifiable : téléchargements, signatures, historique des versions
Un marqueur de confiance ne se limite pas à “dire” : il doit permettre de vérifier. Freemindtronic publie des ressources qui facilitent l’audit et la traçabilité logicielle dans le temps.
| Ressource | Ce que cela apporte | Lien |
|---|---|---|
| Téléchargements officiels | Accès direct aux logiciels, informations de version, empreintes (MD5/SHA256 selon les pages) : transparence et vérification reproductible | https://freemindtronic.com/support/download/ |
| Historique des versions | Traçabilité des évolutions dans le temps (audit interne, conformité, justification des changements) | https://freemindtronic.com/version-history-of-software-freemindtronic-andorra/ |
| Guides techniques (FAQ) | Procédures, repères IP/port, explications d’architecture (support et audit) | https://freemindtronic.com/support/faq-technical-guides/ |
Cette transparence documentée renforce la crédibilité d’une architecture “local-only” et la capacité à répondre aux exigences de conformité sans dépendre d’un cloud opaque.
Checklist d’implémentation pour auditeurs
Les points suivants sont vérifiables rapidement par un reviewer, un auditeur ou une équipe sécurité.
Cette checklist sert aussi de guide pratique à toute solution qui doit justifier un service de premier plan dans un contexte sensible.
- Visible : notification persistante indiquant la session active.
- Arrêtable : action STOP accessible directement depuis la notification.
- Configurable : auto-connexion désactivable dans les paramètres utilisateur (extension : Auto-login).
- Durée minimale : service actif uniquement durant la session Connexion PC.
- Périmètre borné : communication locale ; aucun comportement proxy/VPN/routage.
- Moindre privilège : autorisations granulaires par catégories.
- Transparence opérationnelle : port configurable ; comportement déterministe.
Kit de preuves (review Google Play / audit interne)
Pour éviter les allers-retours, voici les preuves minimales à fournir dans une revue :
- Capture 1 : notification persistante “Service d’auto-connexion active”.
- Capture 2 : bouton STOP visible dans la notification.
- Capture 3 : paramètre “Extension Freemindtronic” avec switch Auto-login + pictogramme Wi-Fi.
- Capture 4 : écran du port (défaut 10001) + nom du téléphone (appairage).
- Capture 5 : exemple de contrôle granulaire (au moins 5 catégories ON/OFF).
Ce kit de preuves est conçu pour répondre explicitement aux attentes d’un Google Play reviewer foreground service, en fournissant des éléments observables, reproductibles et directement alignés sur les exigences officielles.
Ce que Google Play peut vérifier sans analyser le code
- Présence d’une notification persistante lors de l’usage Connexion PC
- Arrêt immédiat du service via STOP (sans état résiduel)
- Perte instantanée de session côté extension navigateur
- Absence de déclaration
VpnService - Port local explicite (10001 par défaut, configurable)
Ces éléments suffisent à établir la conformité FGS sans inspection du code source.
Ce que l’auditeur ne verra PAS
- Pas de code source à analyser pour comprendre le comportement.
- Pas de serveur distant, pas de cloud, pas d’API tierce impliquée.
- Pas de tunnel réseau, pas de VPN, pas de proxy implicite.
- Pas d’activité persistante invisible après STOP.
- Aucune capture d’écran possible sur les écrans sensibles en version de production (verrouillage système des screenshots).
- Aucune saisie clavier lors de l’utilisation de la Connexion PC (téléphone et ordinateur), rendant les keyloggers inopérants.
Plan vidéo (60–90 s) : activer Connexion PC → montrer notification → STOP → relancer → désactiver Auto-login → constater absence de redémarrage → montrer port 10001 → démontrer perte de session côté extension quand STOP.
Service premier plan Android : mapping preuves ↔ exigences Google Play (reviewer)
| Exigence Google Play | Preuve fournie | Ce que le reviewer vérifie |
|---|---|---|
| Fonctionnalité cœur bénéfique | Démonstration “Connexion PC” (extension ↔ téléphone) | Le service est indispensable au workflow principal |
| Perceptible à tout moment | Notification persistante | Aucune exécution “cachée” |
| Arrêtable à la demande | Bouton STOP dans la notification | Arrêt immédiat sans friction |
| Ne peut pas être différé sans casse UX | Perte immédiate de session côté extension quand STOP | Dépendance fonctionnelle démontrable |
| Durée minimale / bornée | Service actif uniquement durant la session Connexion PC | Pas de persistance hors besoin |
- Politique Google Play (FGS requirements) : https://support.google.com/googleplay/android-developer/answer/13392821
Audit rapide : vérifier un Service premier plan Android et la portée local-only (2 minutes)
Cette procédure permet à un auditeur (ou à un reviewer) de vérifier rapidement : visibilité, arrêt immédiat, et caractère local-only.
- Vérifier la perceptibilité : activer la Connexion PC, puis ouvrir le centre de notifications Android et confirmer la présence de la notification persistante.
- Vérifier l’arrêt : cliquer sur STOP dans la notification ; confirmer que la session s’arrête immédiatement.
- Vérifier la désactivation : dans les paramètres “Extension Freemindtronic”, désactiver l’auto-login (switch + pictogramme Wi-Fi), puis confirmer l’absence de relance automatique.
- Vérifier la dépendance fonctionnelle : constater que l’extension navigateur perd la session quand le service s’arrête.
- Vérifier la portée locale : confirmer que le port (défaut 10001) est un paramètre local et que la session n’implique pas de service cloud pour fonctionner.
Astuce : côté extension, la découverte automatique du téléphone (IP + port) peut s’appuyer sur EviDNS Zeroconf (serverless), ce qui facilite l’appairage local sans infrastructure dédiée.
Références : https://freemindtronic.com/technology/evidns-zeroconf-serverless-technology/ et https://freemindtronic.com/support/faq-technical-guides/
Cas d’usage souverain : transparence et continuité opérationnelle
Dans les environnements souverains ou à forte contrainte, le pire scénario n’est pas seulement l’incident : c’est l’impasse opérationnelle provoquée par un outil opaque.
Une fonctionnalité qui dépend silencieusement de l’arrière-plan peut être restreinte par l’OS, puis échouer au moment critique.
En concevant la Connexion PC autour d’un service de premier plan visible, stoppable, configurable et strictement local, l’utilisateur peut prouver — en temps réel — ce qui s’exécute et pourquoi.
Cette transparence rend le système plus résilient face au durcissement des politiques, et réduit le risque d’incompatibilité de dernière minute lors d’un déploiement sensible.
Enfin, lorsqu’un scénario comparable implique des tentatives d’exfiltration, une approche souveraine fondée sur le matériel borne les impacts : si les secrets restent confinés aux dispositifs NFC HSM et que les opérations demeurent explicitement médiées par l’utilisateur, les données récupérées hors contexte restent inexploitables en clair.
Note : la Connexion PC ne dépend ni de Play Integrity API, ni de SafetyNet pour fonctionner. La conformité repose sur des mécanismes observables (notification, STOP, périmètre local), et non sur une attestation distante ou opaque.
Glossaire
Type de service de premier plan (FGS type)
Foreground service type API 34+
Déclaration Foreground Service dans Play Console
FGS declaration + vidéo reviewer
Permission Foreground Service
FOREGROUND_SERVICE_* permissions
Notification de service de premier plan
Notification persistante + contrôle immédiat
POST_NOTIFICATIONS
Permission notifications Android 13+
shortService / systemExempted
Exceptions FGS (cas particuliers)
Dépendance fonctionnelle démontrable
Test immédiat (preuve STOP)
FAQ : Service premier plan Android (Foreground Service)
Pourquoi faut-il déclarer le FGS dans Play Console, et pas seulement dans le manifeste ?
Exigences reviewer Google Play : description, impacts, vidéo
Pourquoi choisir CONNECTED_DEVICE, et pas REMOTE_MESSAGING, pour la Connexion PC ?
Justification de type : NFC HSM + passerelle locale
Le service de premier plan transforme-t-il l’application en proxy, en VPN ou en relais réseau ?
Non : périmètre local-only, et contrôle utilisateur
Que change Android 15 pour les Foreground Services dans un workflow sécurité ?
Durée, cohérence action utilisateur, STOP immédiat
Si Android refuse ou coupe le service, comment diagnostiquer sans “bricoler” l’arrière-plan ?
Troubleshooting FGS : comprendre les refus et corriger proprement
Que doit montrer la vidéo Play Console pour valider un Foreground Service ?
Déclenchement utilisateur, notification, STOP, impact immédiat
Si l’utilisateur bloque les notifications, la session Connexion PC reste-t-elle conforme ?
Perceptible signifie aussi “pilotable”
Pourquoi Google insiste sur “user-initiated” pour un Foreground Service ?
La session démarre parce que l’utilisateur la veut
Si Android refuse le démarrage du service (Start not allowed), que faire sans contourner l’arrière-plan ?
Diagnostiquer proprement, puis corriger type, permission, scénario
Qu’est-ce qu’un service de premier plan sur Android ?
Définition officielle et rôle de sécurité
Un service de premier plan Android (Foreground Service) est un composant conçu pour exécuter une tâche que l’utilisateur doit voir, comprendre et pouvoir arrêter. Il s’accompagne obligatoirement d’une notification persistante indiquant l’activité en cours. Ce modèle vise à empêcher toute exécution sensible cachée en arrière-plan et constitue aujourd’hui un marqueur de transparence et de sécurité.
Référence officielle : https://developer.android.com/develop/background-work/services/foreground-services
Comment démarrer un service de premier plan sur Android ?
Démarrage user-initiated et notification immédiate
Un service de premier plan doit être démarré dans un scénario strictement user-initiated. L’utilisateur déclenche une fonctionnalité cœur (par exemple la Connexion PC), puis l’application démarre le service et affiche immédiatement la notification persistante. Depuis Android 14+, l’application doit également déclarer un type de service cohérent et, lorsque requis, la permission associée.
Référence officielle : https://developer.android.com/develop/background-work/services/fgs/declare
Pourquoi un service de premier plan doit-il afficher une notification ?
Perceptibilité, contrôle utilisateur et auditabilité
La notification n’est pas un détail d’interface : elle est le mécanisme central de contrôle utilisateur. Elle rend la tâche perceptible, permet un arrêt immédiat (ex. bouton STOP) et empêche toute activité invisible. Pour Google Play et Android, une tâche sensible sans notification est assimilée à une exécution cachée, donc non conforme.
Référence officielle : https://support.google.com/googleplay/android-developer/answer/13392821
Comment supprimer les notifications de service de premier plan sur Android ?
Arrêter le service plutôt que masquer l’état
Il n’est pas conforme de masquer durablement la notification d’un service de premier plan tant que celui-ci est actif. La seule manière correcte de faire disparaître la notification est d’arrêter le service. Si l’utilisateur bloque les notifications au niveau système (Android 13+), l’application doit éviter de maintenir une session non perceptible ou guider l’utilisateur pour rétablir l’affichage.
Référence officielle : https://developer.android.com/develop/background-work/services/foreground-services
À relier avec…
- Catégorie Tech Fixes & Security Solutions :
https://freemindtronic.com/tech-fixes-security-solutions/ - Catégorie Technical News :
https://freemindtronic.com/news/technical-news/ - Catégorie Digital Security :
https://freemindtronic.com/news/digital-security/ - Technologie EviDNS Zeroconf (serverless) :
https://freemindtronic.com/technology/evidns-zeroconf-serverless-technology/ - EviDNS : How it works (découverte IP/port) :
https://freemindtronic.com/technology/evidns-serverless-technology-how-it-works-find-connect-nfc-devices/ - FAQ guides techniques (EviDNS / IP + port) :
https://freemindtronic.com/support/faq-technical-guides/ - Téléchargements officiels (hash MD5/SHA256) :
https://freemindtronic.com/support/download/ - Historique des versions (traçabilité) :
https://freemindtronic.com/version-history-of-software-freemindtronic-andorra/ - Technologies Freemindtronic (vue d’ensemble) :
https://freemindtronic.com/technology/ - Freemindtronic (présentation) :
https://freemindtronic.com/freemindtronic/ - Transparence & traçabilité — https://freemindtronic.com/support/download/
- Historique des versions : https://freemindtronic.com/version-history-of-software-freemindtronic-andorra/
- Application concernée — Freemindtronic (EviPro) sur Google Play : https://play.google.com/store/apps/details?id=com.freemindtronic.EviPro
SSH Key PassCypher HSM PGP fournit une chaîne souveraine : génération locale de clés SSH au format natif OpenSSH, directement chiffrées par passphrase lors de leur création, injectée via PassCypher NFC HSM ou saisie clavier. La protection repose sur le chiffrement interne d’OpenSSH (AES-256-CBC. Cette méthode zéro-clé-en-clair permet des passphrases longues (≥256 bits) injectées via BLE-HID pour éliminer les risques de keyloggers lors d’accès à VPS Debian, macOS ou Windows.
Résumé express — Une authentification SSH souveraine pour tous les OS
⮞ En bref
Lecture rapide (≈ 5 minutes) : générez votre paire SSH dans PassCypher HSM PGP, exportez la seule clé publique vers le serveur, et conservez la clé privée au format OpenSSH natif (id_rsa, id_ecdsa, id_ed25519), directement chiffrée par passphrase lors de sa création (aucun conteneur OpenPGP). Le déchiffrement est éphémère, déclenché par une passphrase fournie manuellement ou injectée par PassCypher NFC HSM (émulateur BLE-HID).
Cette méthode garantit une authentification SSH totalement souveraine et une sécurité sans exposition de la clé privée, même sur disque ou en transfert.
⚙ Concept clé
Comment sécuriser une clé SSH ?
Freemindtronic répond à cette question par une approche souveraine : génération locale dans le HSM, encapsulation OpenPGP (AES-256 + KDF durci) et passphrase injectée via PassCypher NFC HSM ou saisie clavier. Cette architecture zéro-clé-en-clair permet des passphrases longues (≥ 256 bits) injectées via BLE-HID, éliminant les risques de keyloggers lors des accès à des VPS Debian, macOS ou Windows.
Interopérabilité
Compatible : Debian / Ubuntu / Fedora / FreeBSD / macOS / Windows (WSL, PuTTY) / Android (Termux, clients SSH) / iOS (Blink, etc.).
Format OpenSSH natif = portabilité maximale.
Paramètres de lecture
Temps de lecture résumé express : ≈ 5 minutes
Temps de lecture résumé avancé : ≈ 7 minutes
Temps de lecture chronique complète : ≈ 39 minutes
Dernière mise à jour : 2025-10-02
Niveau de complexité : Avancé / Expert
Densité technique : ≈ 73 %
Langues disponibles : CAT · EN · ES · FR
Spécificité linguistique : Lexique souverain — densité technique élevée
Ordre de lecture : Résumé → Architecture → Sécurité → Flux → Rotation → EviSSH → Ressources
Accessibilité : Optimisé pour lecteurs d’écran — ancres sémantiques incluses
Type éditorial : Chronique stratégique — Sécurité numérique ·Actualités techniques
À propos de l’auteur : Jacques Gascuel, inventeur et fondateur de Freemindtronic Andorra, spécialiste des technologies HSM NFC, de la cryptographie embarquée et des architectures zero trust. Ses travaux visent la souveraineté numérique et la préparation aux ruptures post-quantiques.
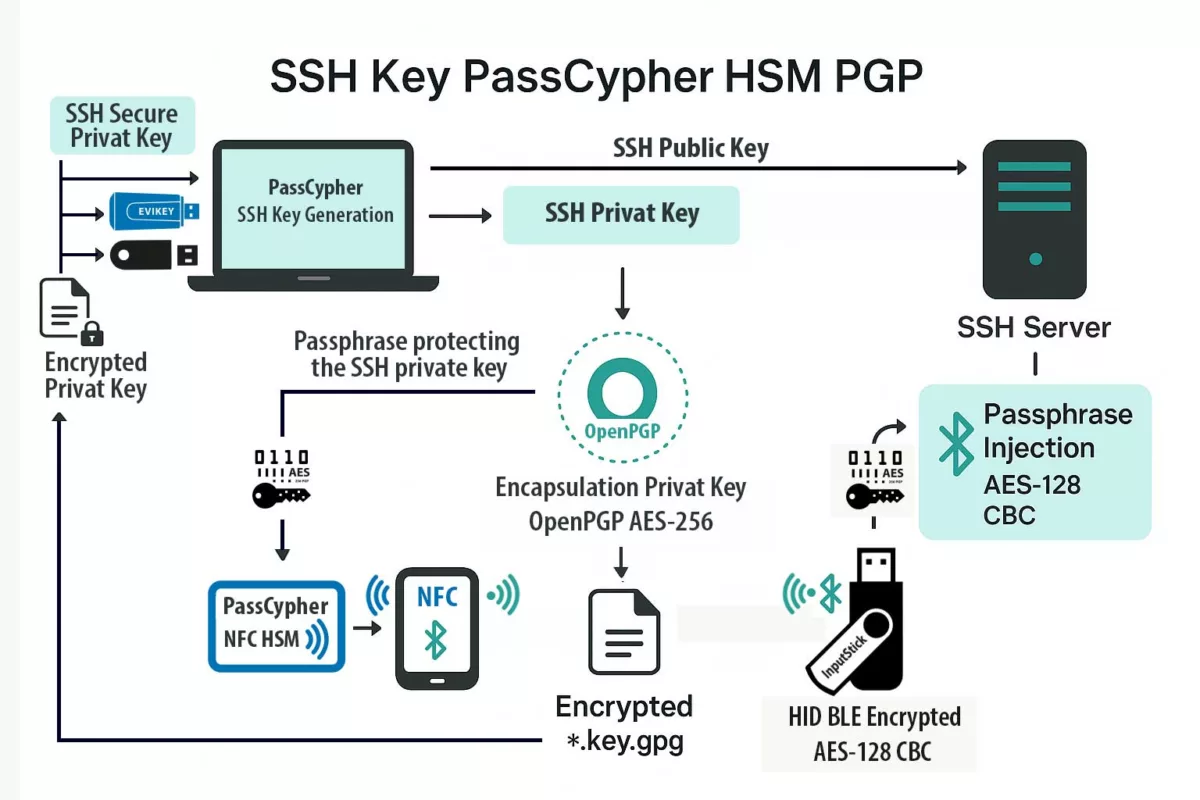
Résumé avancé — Architecture et flux SSH sécurisé via SSH Key PassCypher HSM PGP
⮞ En détail
Flux opérationnel : Génération (PassCypher HSM PGP — recommandation ed25519) → Chiffrement natif OpenSSH (AES-256-CTR + bcrypt KDF) → Export de la clé publique (.pub OpenSSH) → Stockage de la clé privée chiffrée au format OpenSSH (`id_*`) — duplications sûres possibles → Usage (décryptage éphémère local déclenché par passphrase fournie par le HSM ou saisie) → Connexion SSH (ssh -i ~/.ssh/id_* -p [port]).
Au-delà des plateformes classiques de gestion des clés SSH
Alors que la plupart des solutions de gestion des clés SSH reposent sur des infrastructures logicielles centralisées, des coffres-forts cloud ou des architectures dites zero-knowledge, PassCypher HSM PGP introduit une approche souveraine et matérielle. Toutes les opérations cryptographiques — de la génération à la rotation et à la gestion du cycle de vie des clés — sont réalisées localement dans le module HSM, sans intermédiaire logiciel ni dépendance réseau.
Cette conception combine les avantages des architectures zero-knowledge avec ceux de l’isolement matériel. Chaque clé SSH est générée au sein du HSM, encapsulée dans un conteneur OpenPGP AES-256 et conservée dans un état zéro clé en clair. Contrairement aux solutions logicielles qui synchronisent les secrets via un serveur ou un cloud, PassCypher garantit qu’aucune clé privée ni passphrase ne quitte jamais le périmètre matériel de confiance.
Cette gestion matérielle souveraine des clés SSH offre les mêmes capacités d’automatisation que les gestionnaires de secrets traditionnels — notamment la rotation des clés, le partage sécurisé au sein d’une équipe, la traçabilité complète et l’audit en temps réel — tout en assurant une indépendance totale vis-à-vis des services cloud. Le résultat est une solution zero cloud, zero clear key et post-quantum ready adaptée aux environnements souverains et critiques.
Pourquoi sécuriser SSH avec un HSM
Les clés SSH non chiffrées sont exposées au vol, aux copies et aux sauvegardes non souhaitées. PassCypher change le paradigme : la clé privée est encapsulée dans un conteneur chiffré et ne peut être utilisée qu’après un déchiffrement contrôlé. L’injection matérielle de la passphrase (NFC / BLE-HID) supprime le besoin de taper la passphrase sur un clavier exposé aux keyloggers.
Architecture HSM PGP — éléments techniques
- Format natif OpenSSH : AES-256-CBC selon implémentation, avec dérivation bcrypt intégrée ;
- Aucune encapsulation OpenPGP : la clé privée reste autonome et directement utilisable sur tout système compatible OpenSSH ;
- Passphrase : génération aléatoire dans le HSM (recommandation ≥ 256 bits pour posture « PQ-aware ») ;
- Injection : NFC pour déclenchement + émulateur BLE-HID pour saisie automatique et protection anti-keylogger ;
- Duplication sûre : fichiers
*.key.gpgcopiables (EviKey NFC HSM, clé USB, SD, NAS, QR imprimé) —
sécurisés tant que la passphrase/KDF restent protégés.
Utiliser SSH Key PassCypher HSM PGP sur un VPS Debian et au-delà
⮞ TL;DR
Cette section détaille la mise en œuvre concrète : génération d’une paire SSH via PassCypher HSM PGP, export dans un dossier comprenant la clé privée sécurisée (*.key.gpg) avec un mot de passe et sa clé publique. Lors de l’utilisation de la clé privée depuis un support de stockage même non sécurisé, le déchiffrement est réalisé de manière éphémère en mémoire volatile (RAM). La passphrase/mot de passe de la clé privée est obligatoire.
Elle peut être saisie au clavier ou, avantageusement, injectée depuis PassCypher NFC HSM via son émulateur de clavier Bluetooth sécurisé (BLE-HID) chiffré en AES-128 CBC. Cette méthode fluide, sans saisie manuelle, permet une authentification SSH totalement souveraine
sur VPS Debian (OVH) et autres environnements Linux, macOS ou Windows. Elle inclut également les bonnes pratiques de durcissement serveur (sshd_config, iptables, Fail2ban) et d’audit (journaux, rotation des clés, traçabilité horodatée).
L’utilisation d’un émulateur de clavier BLE-HID pour l’injection de passphrases complexes (> 256 bits) remplace avantageusement les solutions par QR code ou agents logiciels. Elle garantit à la fois la mobilité, la compatibilité multi-OS et une résistance native aux enregistreurs de frappe et aux attaques par injection réseau.
In sovereign cybersecurity ↑ Chronique appartenant aux rubriques Digital Security et Tech Fixes & Security Solutions. Voir les dossiers connexes : EviSSH — gestion SSH HSM, EviKey NFC HSM, SSH VPS Sécurisé — PassCypher HSM, PassCypher HSM PGP — note technique.
Chronique – EviSSH — Moteur embarqué dans PassCypher HSM PGP
EviSSH est la technologie embarquée dans PassCypher HSM PGP dédiée à la génération, la gestion et le stockage souverain des clés SSH.
Elle s’appuie sur le moteur EviEngine pour exécuter localement les opérations cryptographiques nécessaires à la création d’une paire de clés SSH et à son encapsulation chiffrée.
Aucune donnée, clé ni métadonnée n’est transmise à un serveur ou service cloud : toutes les opérations sont réalisées localement, côté client.
Rôle et fonctionnement
- Interface intégrée — EviSSH est accessible directement depuis l’extension web PassCypher HSM PGP.
- Génération locale — Les paires de clés SSH sont générées à l’aide de Git for Windows (ou de l’équivalent natif sous Linux/macOS) via l’orchestration d’EviEngine.
- Chiffrement — La clé privée est générée et chiffrée directement par OpenSSH via passphrase (AES-256 + bcrypt KDF) la clé reste dans son format OpenSSH natif.
- Stockage souverain — L’utilisateur choisit librement l’emplacement d’enregistrement : local (dossier .ssh), EviKey NFC HSM, NAS ou support externe.
- Interopérabilité — Les clés publiques sont exportées au format OpenSSH standard, pleinement compatibles avec Debian, Ubuntu, macOS, Windows, Android et iOS.
EviEngine — cœur d’orchestration
EviEngine assure la communication entre le navigateur, le système et les composants matériels HSM.
Il orchestre la génération de clés via Git, gère les licences d’extension PassCypher et assure l’exécution locale sans serveur.
Chaque action est réalisée directement sur la machine de l’utilisateur, garantissant la souveraineté totale du processus.
Intégration HSM
- PassCypher NFC HSM — Injection matérielle de la passphrase via canal BLE-HID chiffré (AES-128 CBC).
- EviKey NFC HSM — Stockage matériel sécurisé des fichiers de clés encapsulées (
*.key.gpg), protégés par la passphrase définie dans PassCypher.
Note : EviSSH n’est pas un outil séparé ; c’est une brique native de PassCypher HSM PGP reposant sur EviEngine. Son rôle est d’unifier la génération, la gestion et la souveraineté du cycle de vie des clés SSH dans un environnement 100 % local et auditable.
Génération d’une clé SSH souveraine avec PassCypher HSM PGP
La génération d’une clé SSH est effectuée par le module EviSSH intégré à PassCypher HSM PGP, via le moteur EviEngine. Cette opération repose sur Git pour la création native de la paire de clés SSH, immédiatement encapsulée et chiffrée par PassCypher HSM PGP. Aucune donnée n’est transmise à un service tiers : tout le processus est exécuté localement.
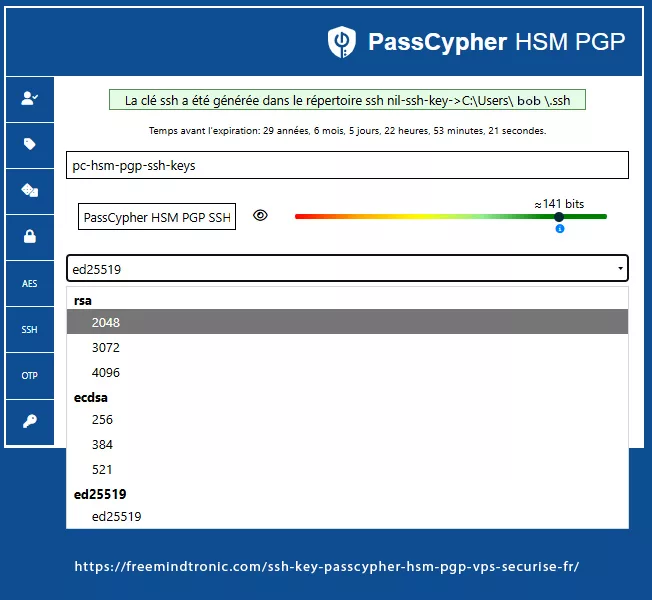
Sélection d’algorithme — Choix cryptographique dans l’extension PassCypher
L’utilisateur sélectionne l’algorithme et la taille de clé directement depuis l’interface de l’extension web PassCypher HSM PGP. Les options disponibles sont regroupées par famille :
- RSA : 2048 bits · 3072 bits · 4096 bits
- ECDSA : 256 bits (p-256) · 384 bits (p-384) · 521 bits (p-521)
- EdDSA : ed25519 — recommandé pour sa robustesse, sa compacité et sa compatibilité native avec OpenSSH
Étapes de génération — Processus transparent via l’extension web
- Ouvrir le module SSH dans PassCypher HSM PGP.
- Choisir un nom de clé (label) unique, par ex.
pc-hsm-pgp-ssh-key. - Sélectionner l’algorithme souhaité (
ed25519oursa-4096selon le cas). - Définir la passphrase : saisie manuellement par l’utilisateur ou injectée via PassCypher NFC HSM avec son émulateur BLE-HID sécurisé AES-128 CBC). Cette passphrase est celle utilisée pour chiffrer la clé privée encapsulée par PassCypher HSM PGP.
- Valider : EviSSH génère la paire SSH via Git, puis PassCypher HSM PGP chiffre la clé privée. Les fichiers sont automatiquement enregistrés dans le dossier défini par l’utilisateur (par défaut :
~/.ssh/ou sur un support matériel tel qu’un EviKey NFC HSM).
Résultat — Artefacts exportés
id_ed25519.pub— la clé publique, à copier sur le serveur distant.- id_ed25519 — la clé privée SSH au format OpenSSH natif, chiffrée par passphrase (AES-256-CBC + bcrypt KDF).
La passphrase, de préférence ≥256 bits d’entropie, peut être saisie depuis la mémoire humaine ou injectée automatiquement depuis le HSM via BLE-HID — évitant toute saisie sur un clavier exposé aux keyloggers.
Générateur de passphrase mémorisable — option « deux-mots + symbole »
✓ Objectif : Proposer une passphrase aléatoire mais facile à retenir : génération de 2 à 4 mots choisis au hasard dans une liste large + injection de caractères spéciaux séparateurs. Utile pour les usages mobiles ou opérateurs où la mémorisation est requise sans sacrifier l’usage d’un KDF durci et de l’injection HSM (BLE-HID / NFC).
Le générateur intégré permet :
- de tirer n mots aléatoires depuis une wordlist embarquée (taille configurable) ;
- d’insérer automatiquement 1–3 caractères spéciaux entre les mots ou en suffixe/prefixe ;
- d’afficher une estimation d’entropie (indicative) ;
- d’enregistrer la passphrase dans le HSM (optionnel) ou de l’injecter via BLE-HID au moment du chiffrement du conteneur
*.key.gpg.
⚠ Alerte entropie — 2 mots seuls offrent une entropie limitée sauf si la wordlist est très large (≥ 2²⁰ entrées). Pour une résistance robuste :
- préférer 3–4 mots issus d’une large wordlist (ex. > 10k entrées) ;
- ajouter au moins 2 caractères spéciaux aléatoires et un séparateur non alphabétique ;
- utiliser Argon2id (m élevé) dans PassCypher pour durcir la dérivation avant AES-256 ;
- pour posture « PQ-aware » : privilégier une passphrase d’entropie effective ≥ 256 bits ou confier la génération aléatoire au HSM.
Exemple pratique
Générer une passphrase mémorisable à 3 mots + 2 caractères spéciaux :
# Exemple conceptuel (interface PassCypher) 1) Choisir wordlist : « common-wordlist-16k » 2) Nombre de mots : 3 3) Séparateur : '-' ; caractères spéciaux aléatoires : '#!' → Exemple généré : atlas-siren#! Utilisation : injecter via PassCypher NFC HSM (BLE-HID) au moment du chiffrement du conteneur :
gpg --symmetric --cipher-algo AES256 --output id_ed25519.key.gpg --compress-level 0 id_ed25519 # la passphrase est fournie par PassCypher BLE-HID au prompt pinentry Recommandations opérationnelles
- Si la clef protège un accès critique (production, bastion) : préférer la génération HSM ou augmenter le nombre de mots ;
- Activer Argon2id (m >= 512MB, t >= 3, p >= 4) côté PassCypher lors du chiffrement ;
- Ne jamais conserver la passphrase en clair ni la noter sans protection matérielle ;
- Vérifier l’estimation d’entropie affichée dans l’UI et ajuster (mots supplémentaires / spéciaux) si nécessaire.
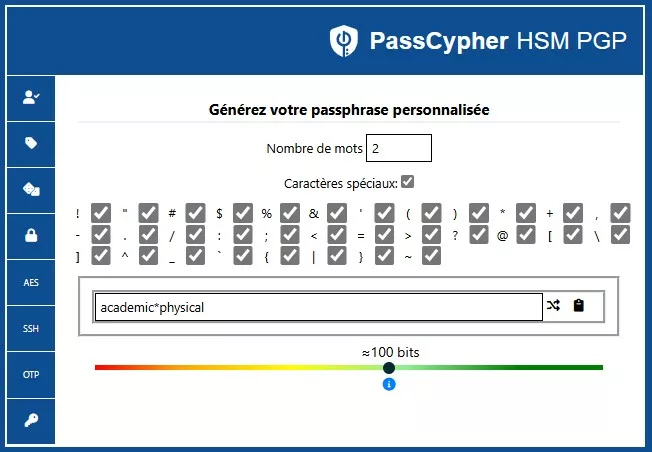
Générateur ASCII-95 — mot de passe / passphrase haute-entropie
L’interface illustrée ci-dessous permet de générer des mots de passe ou passphrases à très haute entropie, en s’appuyant sur l’ensemble complet des 95 caractères ASCII imprimables.Contrairement à un générateur « mots » mémorisables, ce mode vise la sécurité maximale : longueur libre, activation/désactivation fine des classes (majuscules, minuscules, chiffres, symboles) et estimation d’entropie en temps réel — souvent ≥ 256 bits selon la longueur choisie. Ce flux est destiné aux scénarios où la passphrase sera stockée de façon chiffrée (QR chiffré, HSM) et injectée via l’écosystème PassCypher (BLE-HID / NFC) sans affichage en clair à l’écran.
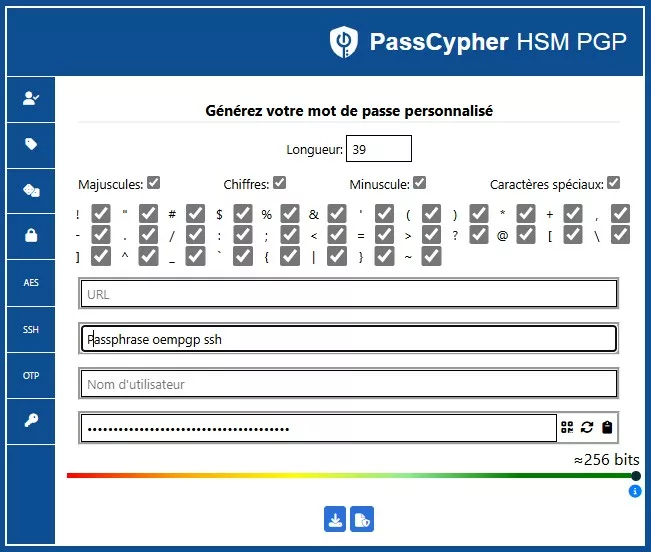
Export QR Code — transfert direct vers un HSM NFC PassCypher
Une fois le mot de passe ou la passphrase haute entropie généré via le module ASCII-95, l’utilisateur peut exporter le secret au format QR Code chiffré. Ce code peut ensuite être scanné depuis un smartphone Android NFC utilisant l’application Freemindtronic embarquant PassCypher NFC HSM. Cette interopérabilité souveraine permet le transfert d’un secret du HSM logiciel vers le HSM matériel sans exposition réseau ni enregistrement sur disque. Ensuite vous pouvez utiliser PassCypher NFC HSM avec l’émulateur de clavier Bluetooth pour saisir le mot de passe ou la passphrase haute entropie.
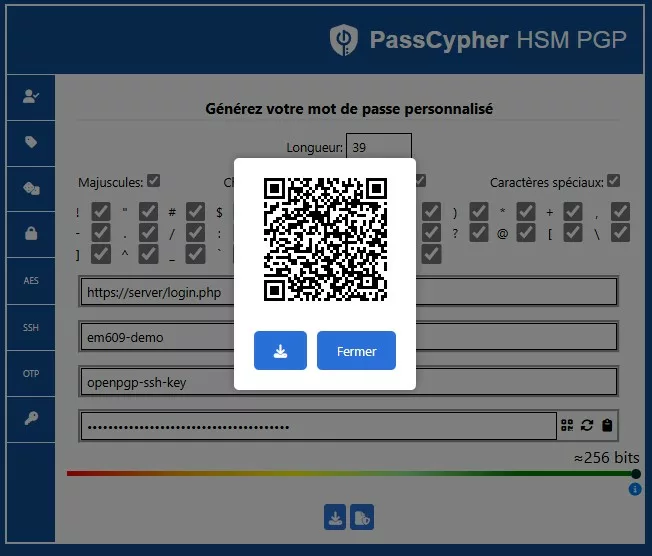
Exemple réel — Clé privée RSA 4096 bits protégée par passphrase
Même une clé RSA 4096 bits, si stockée en clair, reste vulnérable. Dans PassCypher HSM PGP, elle est encapsulée et protégée par une passphrase de 141 bits d’entropie par défaut, rendant toute exfiltration ou brute-force mathématiquement irréaliste.
Voici à quoi ressemble une clé privée SSH RSA 4096 bits encapsulée au format OpenSSH, chiffrée par passphrase :
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAACmFlczI1Ni1jdHIAAAAGYmNyeXB0AAAAGAAAABA+ghFLmp
Oiw0Z3A4NKn2gHAAAAGAAAAAEAAAIXAAAAB3NzaC1yc2EAAAADAQABAAACAQDK4d0ntIeb
... (contenu tronqué pour lisibilité) ...
55XA==
-----END OPENSSH PRIVATE KEY-----BEGIN OPENSSH PRIVATE KEY, suivie d’un bloc base64 chiffré. Le champ b3BlbnNzaC1rZXktdjE= indique une version OpenSSH v1 avec chiffrement activé. Le mot-clé aes256-ctr ou aes256-cbc est implicite selon la configuration du moteur.Intégration sur VPS (ex. OVH Debian 12)
L’intégration d’une clé SSH PassCypher HSM PGP à un VPS s’effectue en insérant la clé publique (.pub) dans le fichier authorized_keys du serveur. OVH permet de le faire directement lors de la création du VPS via son tableau de bord.
Insertion manuelle post-déploiement
ssh -p 49152 debian@IPVPS "mkdir -p ~/.ssh && chmod 700 ~/.ssh && cat >> ~/.ssh/authorized_keys" < id_ed25519.pub
Ensuite, déchiffrez localement la clé privée depuis son conteneur chiffré :
ssh-keygen -p -f ~/.ssh/id_ed25519
chmod 600 ~/.ssh/id_ed25519
ssh -i ~/.ssh/id_ed25519 -p 49152 debian@IPVPS
~/.ssh est en 700 et authorized_keys en 600. Les ACL Linux ne sont généralement pas nécessaires ici, mais toute ACL résiduelle doit rester au moins équivalente aux permissions POSIX strictes.Le fichier déchiffré n’existe que temporairement : il peut être auto-effacé à la fin de la session SSH, ou conservé dans la RAM si l’environnement est chiffré (tmpfs). Cette approche « zero-clear-text » garantit
qu’aucune donnée sensible ne subsiste sur disque.
Compatibilité multi-OS — Authentification universelle
Le format OpenSSH utilisé par PassCypher HSM PGP assure une compatibilité complète avec les principaux systèmes d’exploitation. L’approche souveraine repose sur des standards ouverts sans dépendance cloud ni service tiers.
| OS | Client SSH | Particularités |
|---|---|---|
| Debian / Ubuntu | OpenSSH | Support natif de la clé privée chiffrée. |
| macOS | OpenSSH intégré | Gestion par ssh-add ou injection BLE-HID. |
| Windows 10 / 11 | PuTTY / OpenSSH | Conversion facultative via PuTTYgen. |
| Android | Termux / JuiceSSH | Support injection HID (smartphone couplé NFC). |
| iOS | Blink Shell | Injection BLE-HID automatique (si appairage valide). |
authorized_keys, administrators_authorized_keys).Référence officielle — Microsoft : Authentification par clé SSH sous Windows (30 juin 2025)
En juin 2025, Microsoft a publié une mise à jour majeure sur l’authentification basée sur les clés SSH (Key-based authentication) intégrée nativement à Windows. Ce guide décrit la création et la gestion de paires de clés publiques/privées et recommande l’usage d’algorithmes cryptographiques asymétriques (Ed25519, ECDSA, RSA, DSA).
Cette mise à jour s’applique à Windows Server 2025 / 2022 / 2019, ainsi qu’à Windows 11 et Windows 10. Elle intègre OpenSSH et ses outils : ssh-keygen, ssh-agent, ssh-add, scp / sftp.
- Publication : 10 mars 2025 — Microsoft Learn
- Objet : gestion et protection des clés SSH via OpenSSH intégré à Windows et PowerShell
- Bonnes pratiques : stockage local chiffré, passphrase obligatoire, ACL restrictives sur
authorized_keysetadministrators_authorized_keys
C:\ProgramData\ssh\administrators_authorized_keys pour stocker les clés publiques SSH autorisées.Protégé par des ACL NTFS — accès Administrators et SYSTEM uniquement.
Les droits peuvent être attribués via leur SID :
*S-1-5-32-544 (groupe Administrators).Documentation officielle Microsoft
Extension souveraine du modèle
- La passphrase est injectée matériellement via BLE-HID ou NFC, sans saisie clavier.
- Le chiffrement AES-256 OpenPGP empêche toute sortie de clé privée hors mémoire éphémère.
Ainsi, le flux Microsoft « Key-based authentication » devient, grâce à PassCypher, une authentification SSH matériellement souveraine, compatible Windows/Linux, conforme au modèle Zero-Trust et aux exigences post-quantiques.
PowerShell SSH
Depuis Windows Server 2025 et Windows 11, PowerShell intègre nativement le module PowerShell-SSH, permettant l’exécution distante de commandes via le moteur OpenSSH.
Couplé à PassCypher HSM PGP, il exécute des opérations sans exposer la passphrase en mémoire, assurant une automatisation auditable et souveraine.
Sovereign SSH
La mise en œuvre hybride et matérielle via PassCypher HSM PGP incarne le modèle de gestion SSH souveraine.
Elle combine génération locale, chiffrement des clés privées en AES-256 OpenPGP, dérivation KDF durcie et rotation typologique, sans dépendance cloud ni identité fédérée.
Ce modèle renforce la chaîne de confiance Microsoft OpenSSH par une couche souveraine, auditable et post-quantique.
Intégration Git for Windows
PassCypher HSM PGP exploite Git for Windows pour générer et gérer les paires de clés SSH compatibles avec OpenSSH.
Git for Windows intègre ssh-keygen.exe pour créer des clés SSH protégées par passphrase, stockées par défaut dans C:\Users\<username>\.ssh\.
Ce mode garantit la compatibilité totale avec PowerShell SSH et OpenSSH pour Windows, tout en ajoutant une couche de chiffrement matériel souveraine (Zero-Clear-Key).
Clé d’authentification : utilisée exclusivement pour établir des connexions SSH sécurisées vers des serveurs distants. Injectée la passphrase de la clé privé SSH matériellement via BLE-HID depuis un NFC HSM PassCypher ou saisi manuel ou copier/coller par l’utilisateur, elle ne s’affiche ni ne transite jamais en clair ni sur disque ni en mémoire persistante.
Séparation fonctionnelle des clés SSH — authentification vs signature
Dans une architecture souveraine, chaque clé SSH doit être affectée à un usage précis afin de limiter les risques d’exposition et renforcer la traçabilité. PassCypher HSM PGP met en œuvre cette séparation typologique en chiffrant individuellement chaque clé privée dans un conteneur OpenPGP (AES-256 + KDF durci), avec label et empreinte distincts selon la fonction :
- Clé d’authentification : utilisée pour établir des connexions SSH sécurisées. La passphrase est injectée via BLE-HID depuis un HSM NFC PassCypher, saisie manuellement ou collée localement. Elle n’est jamais exposée en clair — ni sur disque, ni en mémoire persistante — conformément au principe Zero-Clear-Key. L’utilisateur reste responsable en cas de saisie ou collage manuel.
- Clé de signature : dédiée à la validation cryptographique de fichiers, scripts ou commits Git. Elle est encapsulée dans un conteneur OpenPGP distinct, traçable et révoquable sans impact sur les accès SSH actifs.
Cette séparation chiffrée permet :
- Une révocation ciblée sans perturber les connexions SSH actives (la gestion des dates de révocation figure parmi les évolutions prévues du module SSH PassCypher)
- Une auditabilité renforcée via les labels fonctionnels et l’historisation locale
- Une interopérabilité native avec les workflows DevSecOps (Git, CI/CD, pipelines signés)
ssh-keygen -C "auth@vps" ou sign@repo) afin de faciliter la gestion dans les fichiers authorized_keys et les registres append-only de PassCypher.Durcissement et bonnes pratiques SSH Key PassCypher HSM PGP
Même avec une clé SSH PassCypher HSM PGP, la sécurité globale dépend du durcissement serveur. Voici les recommandations clés pour une posture souveraine :
- Désactiver l’accès root :
PermitRootLogin no - Interdire les connexions par mot de passe :
PasswordAuthentication no - Limiter les utilisateurs SSH :
AllowUsers admin - Changer le port SSH : (ex.
49152) et bloquer le 22 par firewall - Configurer UFW/iptables : politique
DROPpar défaut + exceptions ciblées - Installer Fail2ban : (maxretry=3, bantime=30m) pour bloquer le brute-force
- Activer les journaux d’audit :
journalctl -u ssh, rotation et ledger des connexions - ACL / permissions strictes : sur Linux,
~/.ssh=700,authorized_keys=600; sur Windows, restreindre via ACL NTFS (Administrators, SYSTEM) pourauthorized_keysetadministrators_authorized_key.
FIDO vs SSH — Deux paradigmes, deux postures
Dans le paysage actuel de la cybersécurité, la confusion entre FIDO2/WebAuthn et SSH persiste, alors que ces technologies reposent sur des modèles d’authentification et de confiance fondamentalement différents. FIDO sécurise une identité humaine dans le navigateur. SSH, lui, sécurise une identité machine dans le réseau.Leur finalité, leur surface d’exposition et leur posture souveraine s’opposent dans la conception même.
FIDO2 / WebAuthn — Authentification centrée sur l’humain
- ↳ Conçu pour authentifier un utilisateur auprès d’un service Web (navigateur ↔ serveur via WebAuthn) ;
- ↳ La clé privée reste enfermée dans un authenticator matériel (YubiKey, TPM, Secure Enclave, etc.) ;
- ↳ Chaque site ou domaine crée une paire de clés unique — isolation des identités ;
- ↳ Dépendance à un serveur d’authentification (RP) et à l’écosystème navigateur ;
- ↳ Présence humaine obligatoire (biométrie, geste, contact) ;
- ↳ Clé non exportable : excellente sécurité, mais portabilité quasi nulle ;
- ↳ Pas de journal d’audit local ni de rotation autonome.
SSH — Authentification centrée sur la machine
- ↳ Conçu pour authentifier un système client auprès d’un hôte distant (VPS, serveur, cluster) ;
- ↳ Utilise une clé persistante, réutilisable sur plusieurs hôtes selon la politique de confiance ;
- ↳ Fonctionne sans navigateur : protocole SSH natif, échanges chiffrés machine ↔ machine ;
- ↳ Permet la duplication et la sauvegarde des clés (si chiffrées correctement) ;
- ↳ L’authentification repose sur une passphrase ou sur un HSM matériel (injection ou saisie locale) ;
- ↳ Journalisation native possible (logs SSH), rotation et révocation maîtrisées ;
- ↳ Indépendant du cloud, sans serveur d’identité tiers.
⮞ Ce que fait PassCypher HSM PGP avec EviSSH
La solution SSH Key PassCypher HSM PGP étend le modèle SSH classique en y intégrant des éléments de sécurisation matérielle et de traçabilité analogue à FIDO, mais dans une approche souveraine et sans cloud :
- → Génération locale de la paire SSH via PassCypher Engine / EviSSH ;
- → Clé privée encapsulée dans un conteneur OpenPGP (AES-256 + KDF Argon2id/PBKDF2) ;
- → Clé toujours chiffrée sur disque, jamais en clair : le déchiffrement est éphémère, en mémoire volatile uniquement ;
- → Injection matérielle de la passphrase via PassCypher NFC HSM ou émulateur BLE-HID (canal AES-128 CBC sécurisé) ;
- → Présence physique facultative mais possible : le NFC HSM devient l’équivalent d’un “geste FIDO” souverain ;
- → Compatibilité totale multi-OS : Linux, macOS, Windows, Android, iOS ;
- → Aucune dépendance à un navigateur, un serveur WebAuthn, ou un compte cloud ;
- → Orchestration, rotation et sauvegarde via EviSSH pour usage industriel et défense.
Synthèse stratégique
- FIDO2 : modèle cloud-centré et non-exportable — pour les services Web, mais limité hors navigateur ; SSH PassCypher : modèle souverain et portable — idéal pour les accès serveurs, VPS, ou environnements critiques ;
- PassCypher combine la sécurité matérielle d’un authenticator et la souplesse du SSH natif ;
- Les passphrases (≥ 256 bits) injectées via BLE-HID assurent une résistance post-quantique symétrique ;
- Les journaux d’audit et la rotation de clés offrent une traçabilité locale — hors des clouds FIDO ;
- Une même finalité : la confiance numérique, mais deux chemins : dépendance vs souveraineté.
Note comparative : Le canal BLE-HID chiffré AES-128 CBC de PassCypher HSM PGP offre un niveau d’assurance équivalent à un authenticator FIDO2 niveau L2, mais sans dépendance au navigateur ni serveur d’identité. Cette approche hybride, matérielle et logicielle, fait de PassCypher une solution SSH véritablement <strong>post-WebAuthn.
Modèle de menace ⇢ comprendre les risques liés à SSH
Les connexions SSH classiques reposent sur des fichiers locaux contenant des clés privées. Sans protection matérielle, ces fichiers peuvent être copiés, exfiltrés ou utilisés à distance. Le modèle souverain mis en œuvre par SSH Key PassCypher HSM PGP vise à neutraliser ces risques par une approche dite zéro-clé-en-clair et une segmentation stricte des secrets.
Menaces identifiées
- Vol de clé privée → exfiltration du fichier
~/.ssh/id_*ou de ses copies cloud. - Dump mémoire → récupération en RAM d’une clé temporairement déchiffrée.
- Keylogger → capture de la passphrase lors d’une saisie clavier classique.
- MITM BLE → interception du signal lors d’un appairage “Just Works”.
- Sauvegarde non chiffrée → duplication accidentelle du conteneur sans contrôle d’accès.
- Erreur humaine → réutilisation ou diffusion non intentionnelle d’une clé.
⮞ Observation: ⮞ Observation : la plupart des attaques réussies exploitent un seul facteur : la présence d’une clé privée en clair sur disque, en mémoire ou pendant la saisie.
Compromissions de clés SSH — Cas européens et français & leçons tirées
⮞ Incidents documentés en Europe (2021–2025)
- Vulnérabilités critiques dans OpenSSH (France – février 2025) — Deux failles majeures (CVE-2025-26465 et CVE-2025-26466) ont été identifiées par le CERT-FR, exposant les serveurs SSH à des attaques par déni de service (DoS) et à des détournements de session (MitM).
- Les versions antérieures à OpenSSH 9.9p2 sont vulnérables. Avis CERT-FR
- Ces failles permettent de contourner la vérification des clés hôtes et de perturber les connexions SSH.
Leçon : même les implémentations de confiance peuvent contenir des failles latentes.
Protection PassCypher : la clé privée reste chiffrée dans un conteneur OpenPGP et n’est jamais exposée en clair, même en cas d’attaque MitM.
- Fuite de clés SSH dans des pipelines CI/CD open source (Europe – T2 2025) — Plusieurs projets hébergés sur GitHub ont accidentellement publié des fichiers `.env` contenant des clés privées SSH dans leurs workflows.
- Des serveurs de staging ont été compromis suite à l’utilisation de ces clés exposées.
- Les logs publics ont révélé des secrets non chiffrés.
Leçon : les clés privées ne doivent jamais être stockées en clair dans des environnements CI/CD.
Protection PassCypher : même si le fichier est publié, le conteneur OpenPGP (*.key.gpg) reste inutilisable sans la phrase secrète injectée par HSM.
- Campagne Ebury en Europe (2024) — Le malware Ebury a compromis plus de 400 000 serveurs Linux en Europe, insérant des portes dérobées SSH pour voler des identifiants.
- Analyse complète par ESET : ESET / WeLiveSecurity
Leçon : les clés chargées en mémoire vive peuvent être détournées par des malwares persistants.
Protection PassCypher : la clé est déchiffrée uniquement en RAM, de manière éphémère, et jamais persistée — même en cas de compromission système.
Conclusion opérationnelle : Aucun des cas recensés n’impliquait une protection par chiffrement OpenPGP ni une injection matérielle de la phrase secrète. Tous ont exploité des vecteurs classiques : clés en clair, logs non filtrés, mémoire persistante ou failles protocolaires.
Une architecture PassCypher HSM PGP — combinant chiffrement OpenPGP AES-256, KDF renforcé (Argon2id), et injection de phrase secrète via HSM NFC/BLE-HID — aurait neutralisé ces vecteurs :
- Clé privée toujours chiffrée au repos
- Déchiffrement uniquement en mémoire vive, jamais sur disque
- Phrase secrète injectée par matériel, jamais tapée ni loggée
- Même si le fichier est volé, il reste inutilisable sans le HSM physique
Ce modèle garantit une authentification SSH souveraine, conforme aux exigences de résilience post-quantique et aux directives européennes (NIS2, DORA).
Mécanismes de protection SSH Key PassCypher HSM PGP — OpenPGP, KDF et BLE-HID
Le modèle SSH Key PassCypher HSM PGP repose sur une défense en profondeur articulée autour de trois piliers : chiffrement asymétrique robuste, dérivation de clé renforcée et injection physique sécurisée. Ces mécanismes agissent conjointement pour garantir qu’aucune clé privée ne puisse être exfiltrée, même sur un poste compromis.
Conteneur OpenPGP et intégrité
Le fichier de clé privée (id_rsa, id_ecdsa, id_ed25519) est chiffré directement par OpenSSH via passphrase (AES-256 + bcrypt KDF). Aucun conteneur OpenPGP n’est impliqué :
- Chiffrement : AES-256 (CBC ou GCM selon implémentation) ;
- Intégrité : MDC (Modification Detection Code) actif ;
- Salt unique : généré par le moteur lors du chiffrement initial ;
- Compression : optionnelle, pour réduire les empreintes mémoire.
Dérivation de clé (KDF) et résistance symétrique
La clé de session OpenPGP découle d’une passphrase issue du HSM via :
- Argon2id : configuration par défaut (m=512 MB, t=3, p=4), résistant aux attaques GPU ;
- Fallback PBKDF2 : 250 000 itérations SHA-512 si Argon2id indisponible ;
- Posture PQ-aware : entropie ≥ 256 bits → résistance symétrique équivalente à 2¹²⁸ (Grover).
⚠ Cette protection ne rend pas le système « post-quantum proof » : seules les primitives asymétriques PQC (CRYSTALS-Dilithium, Kyber) le permettront à terme.
Canal d’injection BLE-HID — Sécurisation de la passphrase
La passphrase est transmise via un canal Bluetooth Low Energy HID, émulant un clavier sécurisé.
- Appairage sécurisé : mode Secure Connections avec code PIN ou authentification par code numérique obligatoire, et bonding activé pour verrouiller l’association.
- Chiffrement des communications BLE : AES-128 CBC, appliqué au niveau de l’application HID.
- Stockage de la première clé AES-128 CBC : conservée dans une enclave électronique sécurisée intégrée à l’émulateur de clavier Bluetooth USB.
- Stockage de la seconde clé AES-128 CBC : protégée dans le Keystore Android (Android ≥ 10), via l’application PassCypher NFC HSM embarquée dans l’application Android Freemindtronic.
- Risque résiduel : une vulnérabilité MITM subsiste si le mode d’appairage « Just-Works » est autorisé — ce mode est strictement interdit dans la posture souveraine.
Rotation et révocation — cycle de vie des clés SSH Key PassCypher HSM PGP
La rotation d’une clé SSH Key PassCypher HSM PGP ne repose pas sur une commande de rotation de PassCypher Engine. Elle s’effectue selon un processus opératoire en quatre temps : régénérer, déployer, valider, retirer. Le tout en maintenant l’approche zero-clear-key (clé privée toujours chiffrée au repos, déverrouillage éphémère en RAM).
1) Régénération (nouvelle paire)
Depuis l’interface EviSSH intégrée à PassCypher HSM PGP, l’utilisateur régénère une paire de clés SSH via Git, encapsulée et chiffrée automatiquement par le moteur PassCypher. Voici comment :
- Sélectionner l’algorithme souhaité (recommandé :
ed25519pour robustesse et compatibilité ;rsa-4096en cas de contrainte spécifique). - Définir un label distinctif pour la paire (ex. :
pc-hsm-ssh-2025-10) afin de faciliter la traçabilité et la révocation future. - la clé privée est générée au format natif OpenSSH (id_rsa, id_ecdsa, id_ed25519), directement chiffrée par passphrase lors de sa création.
- La clé publique (
*.pub) est générée séparément et annotée avec un commentaire unique (ex. :pc-hsm-ssh-2025-10) pour identification dansauthorized_keys.
2) Déploiement contrôlé (ajout sans coupure)
Ajouter la nouvelle .pub dans ~/.ssh/authorized_keys sur chaque serveur, sans supprimer l’ancienne (phase de chevauchement).
# Exemple de déploiement “append-only” (port 49152, utilisateur debian)
scp -P 49152 ~/.ssh/id_ed25519_2025-10.pub debian@IPVPS:/tmp/newkey.pub
ssh -p 49152 debian@IPVPS 'umask 077; mkdir -p ~/.ssh; touch ~/.ssh/authorized_keys
&& grep -qxF -f /tmp/newkey.pub ~/.ssh/authorized_keys || cat /tmp/newkey.pub >> ~/.ssh/authorized_keys
&& rm -f /tmp/newkey.pub && chmod 600 ~/.ssh/authorized_keys'
3) Validation (canary)
Tester la connexion avec la nouvelle clé (passphrase injectée via BLE-HID) :
ssh -o IdentitiesOnly=yes -i ~/.ssh/id_ed25519_2025-10 -p 49152 debian@IPVPSConserver les deux clés en parallèle sur une période courte (T + 24–72 h) pour absorber les aléas opérationnels.
4) Retrait de l’ancienne clé (révocation effective)
Retirer l’ancienne ligne d’authorized_keys par commentaire/label :
# Exemple : suppression par label de fin de ligne
ssh -p 49152 debian@IPVPS "sed -i.bak '/ pc-hsm-ssh-2025-04$/d' ~/.ssh/authorized_keys"Répéter sur l’ensemble des hôtes cibles (bastion / nœuds). Archiver les fichiers authorized_keys.bak pour traçabilité.
Journal d’audit (append-only, côté admin)
Tenir un registre horodaté des opérations (empreintes, labels, hôtes) — simple, lisible, diff-able.
mkdir -p ~/audit && touch ~/audit/ssh-keys-ledger.tsv
printf "%stNEWt%st%sn" "$(date -Iseconds)"
"$(ssh-keygen -lf ~/.ssh/id_ed25519_2025-10.pub | awk '{print $2}')" "pc-hsm-ssh-2025-10"
>> ~/audit/ssh-keys-ledger.tsv
printf "%stREVOKEt%st%sn" "$(date -Iseconds)"
"$(ssh-keygen -lf ~/.ssh/id_ed25519_2025-04.pub | awk '{print $2}')" "pc-hsm-ssh-2025-04"
>> ~/audit/ssh-keys-ledger.tsv
La rotation est procédurale : on ne “rotate” pas dans PassCypher Engine par commande, on régénère une nouvelle paire, on déploie la clé publique, on valide l’accès, puis on retire l’ancienne — le tout tracé dans un journal d’audit local. L’utilisateur n’a jamais à interagir avec le moteur : tout est piloté via l’extension web PassCypher HSM PGP.
Script d’orchestration (multi-hôtes, sans outil tiers)
#!/usr/bin/env bash
set -euo pipefail
PORT=49152
USER=debian
NEWPUB="$HOME/.ssh/id_ed25519_2025-10.pub"
OLD_LABEL="pc-hsm-ssh-2025-04"
while read -r HOST; do
echo "[*] $HOST :: install new key"
scp -P "$PORT" "$NEWPUB" "$USER@$HOST:/tmp/newkey.pub"
ssh -p "$PORT" "$USER@$HOST" '
umask 077
mkdir -p ~/.ssh
touch ~/.ssh/authorized_keys
grep -qxF -f /tmp/newkey.pub ~/.ssh/authorized_keys || cat /tmp/newkey.pub >> ~/.ssh/authorized_keys
rm -f /tmp/newkey.pub
chmod 600 ~/.ssh/authorized_keys
'
done < hosts.txt
echo "[] Validate the new key on all hosts, then retire the old key:"
while read -r HOST; do
echo "[] $HOST :: remove old key by label"
ssh -p "$PORT" "$USER@$HOST" "sed -i.bak '/ ${OLD_LABEL}$/d' ~/.ssh/authorized_keys"
done < hosts.txt
Méthodes souveraines de récupération d’une passphrase ou d’un mot de passe (QR, NFC HSM, BLE-HID, saisie de mémoire)
La récupération d’une passphrase ou d’un mot de passe dans PassCypher HSM PGP repose sur plusieurs mécanismes souverains, complémentaires et adaptés à différents contextes d’usage :
- QR code chiffré (GIF/PNG) — Permet d’importer une passphrase sans affichage à l’écran. Idéal pour les sauvegardes imprimées ou les rotations planifiées. → Injection directe dans le champ sécurisé, sans saisie ni exposition.
- Lecture NFC depuis un HSM PassCypher — Récupération sans contact depuis un support matériel souverain (EviKey / EviPass). → Injection automatique et chiffrée via canal BLE-HID sécurisé.
- Émulateur de clavier Bluetooth ou USB (BLE-HID) — Simulation de saisie clavier chiffrée AES-128 CBC. Fonctionne sur Linux, macOS, Windows, Android, iOS, y compris en environnement isolé (air-gapped). → Zéro trace persistante, aucune frappe réelle.
- Saisie manuelle de mémoire — Option ultime pour utilisateurs avancés : saisie directe dans le champ sécurisé (pinentry). → Reste souveraine si sans autocomplétion ni log clavier.
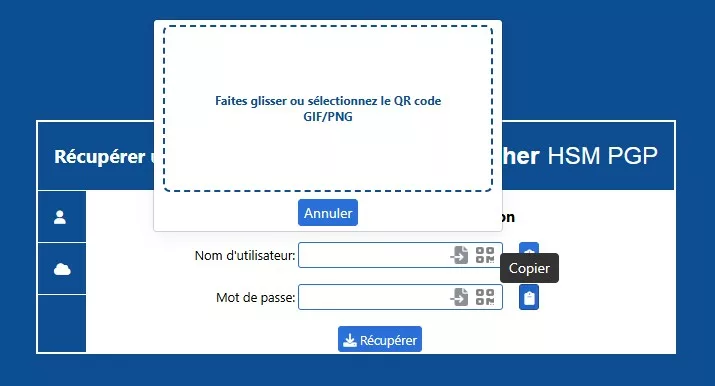
Procédé recommandé — Restaurer une passphrase depuis un QR de sauvegarde
- Ouvrir l’interface Récupération de PassCypher (hors ligne de préférence).
- Importer l’image QR (GIF/PNG) — le déchiffrement est local, sans connexion distante.
- Choisir l’option d’usage : injection BLE-HID dans le champ sécurisé, ou copie dans un presse-papier éphémère (auto-effacement).
- Valider, puis purger immédiatement le presse-papier. Consigner l’opération dans le ledger (horodatage, empreinte, origine QR).
Attention : ne jamais coller la passphrase dans un éditeur ou un terminal. Utiliser exclusivement des mécanismes éphémères et auditables.
Exemple CLI « FIFO » (option avancée — pour utilisateurs Linux expérimentés)
Utiliser cette méthode uniquement si l’interface BLE-HID n’est pas disponible. Cette méthode n’écrit jamais la passphrase sur disque (FIFO = pipe) et interdit l’enregistrement dans l’historique shell.
# 1. Créer un FIFO sécurisé
mkfifo /tmp/pc_pass.fifo
chmod 600 /tmp/pc_pass.fifo
# 2. Dans un shell, lancer gpg en lisant la passphrase depuis le FIFO (ne pas laisser d’espace)
# Remplacez les chemins par les vôtres
gpg –batch –yes –passphrase-fd 0 –decrypt –output ~/.ssh/id_ed25519 ~/.ssh/id_ed25519.key.gpg < /tmp/pc_pass.fifo & # 3. Dans un autre terminal (ou via l’interface de récupération), écrire la passphrase dans le FIFO # IMPORTANT: écriture ponctuelle puis suppression immédiate du FIFO printf ‘%s’ “LA_PASS_POUR_GPG” > /tmp/pc_pass.fifo
# 4. Supprimer le FIFO et s’assurer qu’aucune trace ne subsiste
shred -u /tmp/pc_pass.fifo || rm -f /tmp/pc_pass.fifo
⚠️ Remarques sécurité CLI
- Ne jamais écrire la passphrase dans une variable d’environnement ou dans l’historique du shell.
- Préférer l’injection BLE-HID (pinentry) : aucune exposition dans les processus ni le presse-papier.
- Consigner chaque opération dans un registre d’audit local (empreinte de clé, hôte, opérateur, horodatage).
Flux opérationnel — de la génération à l’authentification (SSH Key PassCypher HSM PGP)
On entend par flux opérationnel l’étape et la façon opérationnelle, de réaliser le flux réel utilisé par PassCypher Engine + PassCypher HSM PGP et éventuelement PassCypher NFC HSM et son l’émulateur de clavier bluetooth (BLE-HID) pour produire, protéger, transporter et utiliser une clé SSH dont la clé privée reste chiffrée et n’est déverrouillée qu’éphémèrement en RAM.
⮞ Résumé en une ligne: Génération → clé privée OpenSSH protégée par passphrase → export .pub → stockage de la clé privée chiffrée sur le support souhaité → injection sécurisée de la passphrase (PassCypher NFC HSM via BLE-HID ou saisie) → déverrouillage éphémère en mémoire → connexion SSH → purge immédiate.
Étapes détaillées (flow)
Génération (EviSSH intégré à PassCypher HSM PGP, orchestré par PassCypher Engine)
▸ L’utilisateur lance PassCypher Engine / extension → « SSH Key Generator ».
▸ Choix de l’algorithme (recommandé : ed25519).
▸ Définit un label et la méthode de passphrase (générée aléatoirement par le HSM ou fournie par l’utilisateur).
▸ Résultat : une paire → id_ed25519 (clé privée OpenSSH chiffrée par passphrase) + id_ed25519.pub (clé publique OpenSSH).
▸ EviSSH, via PassCypher Engine, propose l’emplacement d’enregistrement (dossier local, EviKey, NAS). Il n’effectue aucun déverrouillage automatique.
Export & stockage
▸ Exportez uniquement la clé publique (.pub) vers le serveur (ex. : OVH cloud panel ou copie manuelle dans ~/.ssh/authorized_keys).
▸ Stockez la clé privée chiffrée (bloc PEM OpenSSH protégé par passphrase) où vous voulez : EviKey NFC, NAS chiffré, clé USB chiffrée. Le fichier reste chiffré au repos.
Préparation client avant usage
▸ Copier (si nécessaire) la clé privée chiffrée sur la machine client dans un dossier contrôlé : ex. ~/secure/id_ed25519.
▸ Créer un tmpfs pour réduire la persistance sur disque si un déchiffrement temporaire est nécessaire :
sudo mkdir -p /mnt/ssh-tmp && sudo mount -t tmpfs -o mode=700 tmpfs /mnt/ssh-tmp▸ S’assurer que le swap est chiffré ou désactivé si possible : sudo swapoff -a.
Injection de la passphrase (PassCypher NFC HSM → BLE-HID)
▸ L’utilisateur déclenche l’injection : rapprocher le PassCypher NFC HSM du smartphone/appairer le BLE HID si non déjà apparié.
▸ IMPORTANT — sécurité BLE : n’autorisez pas le pairing « Just-Works ». Exiger Secure Connections (Numeric Comparison / authentification par code numérique) ou pairing par PIN ; forcer bonding et stockage sécurisé de la clé d’appairage. Le canal BLE transporte des paquets chiffrés (AES-128 CBC dans l’implémentation actuelle du HID) : le dispositif présente la passphrase au système client comme une saisie clavier virtuelle, sans frappe physique.
Déverrouillage éphémère en RAM
▸ L’invite OpenSSH demande la passphrase ; PassCypher BLE-HID injecte la passphrase dans la boîte de dialogue (ou dans pinentry).
▸ Le client OpenSSH déchiffre la clé privée en mémoire volatile (RAM) uniquement pour l’utilisation immédiate. Le fichier de clé privée encapsulé (*.key.gpg) reste inchangé et chiffré ; seul son contenu est déchiffré en mémoire volatile (RAM) pour la session SSH.
▸ Vérifier permissions : chmod 600 /mnt/ssh-tmp/id_ed25519 si un fichier temporaire est créé. Préférer rester en RAM (pinentry/ssh prompt) plutôt que d’écrire sur disque.
Authentification SSH
▸ L’appel SSH utilise la clé déverrouillée en RAM :
ssh -i /chemin/vers/id_ed25519 -p 49152 user@IPVPS▸ Après l’authentification, la clé en mémoire doit être purgée immédiatement (cf. point suivant).
Purge & post-usage
▸ Si une copie temporaire (chiffrée) de la clé privée a été montée sur un volume RAM (tmpfs) pour un usage isolé, la supprimer et démonter après utilisation. Aucune version déchiffrée ne doit être écrite sur disque. :
shred -u /mnt/ssh-tmp/id_ed25519 || rm -f /mnt/ssh-tmp/id_ed25519 sudo umount /mnt/ssh-tmp▸ Effacer l’agent si utilisé : ssh-add -D et arrêter l’agent : eval "$(ssh-agent -k)".
▸ Réactiver swap si nécessaire : sudo swapon -a.
Points de sécurité critiques et recommandations
- Jamais utiliser BLE pairing en « Just-Works ». Forcer Secure Connections / authentification par code numérique / PIN et bonding.
- La clé privée reste chiffrée sur le support ; seul le déchiffrement éphémère en RAM est utilisé. Ceci réduit fortement le risque mais n’annule pas l’exposition si la machine cliente est déjà compromise (dump mémoire, rootkit).
- ssh-agent augmente la fenêtre d’exposition (clé en mémoire plus longtemps). Si confort nécessaire → limiter la durée (-t) et purger systématiquement.
- Protéger swap et empêcher core dumps :
sudo swapoff -a,ulimit -c 0, vérifier politique de dump système. - Journalisation & audit : journaliser les opérations de rotation et les injections (rotation.log, known_hosts.audit). Note : PassCypher Engine orchestre la génération et l’enregistrement des fichiers privés chiffrés ; l’audit applicatif doit rester côté serveur/administration (journalisation SSH / Fail2ban / rotation).
- Cryptographie : utiliser un KDF durci (Argon2id si disponible, sinon PBKDF2 avec paramètres élevés) et AES-256 pour le conteneur OpenSSH. Une passphrase aléatoire ≥ 256 bits augmente la résistance symétrique (Grover) mais n’élimine pas la nécessité de primitives asymétriques post-quantiques pour la couche signature à terme.
Exemples rapides de commandes utiles
# Example: temporary RAM decryption
sudo mkdir -p /mnt/ssh-tmp && sudo mount -t tmpfs -o mode=700 tmpfs /mnt/ssh-tmp
cp /media/evikey/id_ed25519 /mnt/ssh-tmp/id_ed25519
ssh -i /mnt/ssh-tmp/id_ed25519 -p 49152 user@vps.example.com
shred -u /mnt/ssh-tmp/id_ed25519 || rm -f /mnt/ssh-tmp/id_ed25519
sudo umount /mnt/ssh-tmpEviSSH — Gestion et orchestration intégrée
EviSSH n’est pas un outil externe ; il fait partie intégrante de PassCypher HSM PGP. Sa fonction est d’automatiser la génération, la gestion et la rotation des clés SSH locales, tout en assurant leur compatibilité universelle avec les environnements Linux, macOS et Windows. Il repose sur EviEngine pour orchestrer les actions du navigateur et du système, sans dépendance cloud ni service centralisé.
Fonctions principales
- Génération de clés SSH via Git, directement depuis l’interface PassCypher HSM PGP.
- Encapsulation automatique de la clé privée dans un conteneur chiffré OpenPGP (AES-256 + Argon2id/PBKDF2).
- Stockage souverain sur le support choisi : disque local, EviKey NFC HSM, NAS chiffré, etc.
- Rotation simplifiée : création, déploiement et révocation manuelle sans manipulation de fichier sensible.
- Interopérabilité totale : clés compatibles OpenSSH pour toutes plateformes majeures.
Sécurité et intégrations matérielles
- Injection de passphrase via PassCypher NFC HSM et canal BLE-HID chiffré (AES-128 CBC).
- Stockage matériel optionnel sur EviKey NFC HSM : les conteneurs chiffrés y sont inaccessibles sans la passphrase définie dans PassCypher.
💡Note : Contrairement à une solution serveur, EviSSH</strong> n’exécute ni déchiffrement distant ni gestion centralisée des clés. Tout est local, auditable et compatible avec une posture de souveraineté numérique complète.
Cas d’usage souverain — PassCypher HSM PGP · PassCypher NFC HSM & HID BLE
Ce scénario illustre un usage souverain complet de PassCypher HSM PGP dans un environnement multi-OS et multi-site :
- ✓ PassCypher HSM PGP génère une paire SSH au format OpenSSH (id_*), directement chiffrée par passphrase (AES-256-CTR + bcrypt KDF). Aucune encapsulation OpenPGP n’est utilisée.
- ✓ PassCypher NFC HSM stocke et protège la passphrase souveraine, permettant son injection sécurisée sur tout système compatible via son émulateur BLE-HID.
- ✓ L’émulateur Bluetooth HID agit comme un clavier virtuel chiffré (AES-128 CBC) injectant la passphrase localement sans frappe physique, éliminant tout risque de keylogger.
- ✓ Usage concret : un administrateur se connecte à un VPS Debian depuis macOS ou Android en approchant simplement son PassCypher NFC HSM — la passphrase est transmise via le lien BLE-HID sécurisé et le déchiffrement s’effectue en RAM uniquement.
- ✓ Bénéfice opérationnel : authentification SSH souveraine, portable et sans saisie, fonctionnant sur Linux, Windows, macOS, Android et iOS, sans dépendance cloud.
Cette intégration PassCypher HSM PGP × PassCypher NFC HSM & BLE-HID constitue la base du modèle “zero-clear-key</strong>” de Freemindtronic : aucune clé privée n’existe jamais en clair sur disque ou réseau, et l’accès est conditionné à la possession physique du HSM et à l’appairage BLE sécurisé.
Points clés
- PassCypher HSM PGP → zéro clé privée en clair sur disque, même temporairement.
- Injection BLE-HID AES-128 → neutralise les keyloggers et les scripts d’injection clavier.
- OpenSSH AES-256 + bcrypt KDF → chiffrement natif robuste, posture souveraine et portable.
- Rotation, audit et registre horodaté → traçabilité complète des identités machine.
- EviSSH orchestration → multi-HSM souveraine sans dépendance cloud ni serveur tiers.
Fuites et compromissions documentées — Pourquoi la souveraineté logicielle compte
Depuis 2021, plusieurs incidents majeurs ont montré la fragilité des systèmes reposant sur des secrets stockés ou manipulés en clair. Ces compromissions, souvent issues de chaînes d’intégration continue (CI/CD), de dépôts publics ou de scripts non isolés, ont mis en évidence la nécessité d’adopter des architectures « zéro-clé-en-clair ».
- Codecov (janvier–avril 2021) — modification du script Bash Uploader pour exfiltrer des variables d’environnement et des identifiants depuis les pipelines CI des clients.
Post-mortem officiel Codecov – Alerte CISA - Campagne Ebury / SSH backdoor (2009 → 2024) — plus de 400 000 serveurs Linux et BSD compromis. Les attaquants interceptaient les clés privées SSH présentes en mémoire ou sur disque.
Rapport ESET / WeLiveSecurity 2024 - Fuites de clés sur GitHub (2023–2024) — plusieurs fournisseurs ont révélé des erreurs de commits contenant des clés ou certificats privés. Ces cas illustrent l’importance d’empêcher toute exposition en clair.
GitHub Secret Scanning – Push Protection</li>
Ces exemples démontrent que la simple génération sécurisée d’un secret ne suffit pas : c’est toute la chaîne de vie du secret (génération, utilisation, stockage, destruction
Vecteurs d’exfiltration assistés par IA — et pourquoi la souveraineté matérielle compte
⮞ Contexte
Les assistants d’IA intégrés aux IDE, navigateurs et outils de productivité (Copilot, CodeWhisperer, etc.) indexent et analysent le contenu local pour générer des suggestions.
En accédant aux fichiers ouverts, sorties de terminal ou logs, ils créent un nouveau vecteur d’exfiltration potentielle de secrets — parfois sans interaction humaine directe.
Accroissement de la surface d’exfiltration
Tout assistant capable de lire l’éditeur, le presse-papier ou le terminal devient un canal de sortie supplémentaire. Une requête mal formulée ou un prompt partagé peut révéler du contenu sensible.
Risque de compromission
Un plugin IA compromis peut être détourné pour extraire automatiquement des secrets présents dans le workspace ou injecter du code de surveillance passif.
Exemples concrets
Suggestion de code contenant des clés API, affichage de variables d’environnement ou réinjection accidentelle de secrets dans des templates publics.
Pourquoi la souveraineté matérielle change le modèle de menace
Une architecture purement logicielle laisse les secrets exposés aux processus de l’OS. En revanche, une approche ancrée matériellement (HSM, NFC, BLE-HID) isole le secret opérationnel de tout accès logiciel non autorisé.
Conteneur chiffré + HSM
Le secret stocké (fichier chiffré OpenPGP) est inutilisable sans la passphrase détenue dans le HSM souverain. Même exfiltré, il reste cryptographiquement inerte.
Injection physique (BLE-HID / NFC)
La passphrase n’est jamais tapée ni copiée : elle est injectée comme entrée matérielle éphémère, réduisant les risques de keyloggers ou d’interception logicielle.
Éphémérité
Le déchiffrement ne s’effectue qu’en mémoire volatile. Aucun secret n’est écrit sur disque, même temporairement.
Application concrète : PassCypher Secure Passgen WP est déjà 100 % client-side et offline-ready. Couplé à un HSM PassCypher (ou EviKey), il devient la première brique d’un écosystème de génération et d’usage de secrets totalement souverain.
Bonnes pratiques immédiates
- Évitez tout stockage de secrets en clair dans dépôts, CI ou logs.
- Considérez les assistants IA comme des composants privilégiés et restreignez leurs accès.
- Privilégiez les conteneurs chiffrés et l’usage d’un HSM pour toute clé persistante.
Signaux faibles — tendances à surveiller
– Adoption croissante de BLE-HID dans les workflows DevSecOps multi-OS ;
– Expérimentations d’Argon2id matériellement accéléré dans certains HSM ;
– Émergence de projets OpenPGP v6 intégrant des modules PQC hybrides ;
– Pression normative croissante autour de NIS2/DORA → journalisation obligatoire des accès machine ;
– Vers une convergence SSH / FIDO2 / PQC dans les architectures souveraines d’accès distant.
Ce que nous n’avons pas couvert au sujet SSH Key PassCypher HSM PGP
⧉ Ce que nous n’avons pas couvert
Cette chronique s’est concentrée sur l’usage de SSH Key PassCypher HSM PGP pour la sécurisation des connexions VPS et la gestion de la clé privée. Nous n’avons pas abordé :
- l’intégration directe dans des pipelines CI/CD ;
- les extensions FIDO2 ou post-quantum en préparation ;
- l’audit automatisé de la chaîne BLE sur systèmes mobiles ;
- les mécanismes de synchronisation inter-HSM en temps réel.
Ces aspects feront l’objet d’une étude complémentaire dans la série Tech Fixes & Security Solutions.
FAQ — SSH Key PassCypher HSM PGP
Un HSM hybride pour une sécurité souveraine
PassCypher HSM PGP est un module de sécurité matériel/logiciel développé par Freemindtronic. Il permet de générer, chiffrer et protéger des clés SSH et OpenPGP via AES-256 et KDF mémoire-dur (PBKDF2 ou Argon2id). Grâce à ses interfaces NFC et BLE-HID, il injecte les passphrases sans jamais exposer la clé privée en clair. Cette approche garantit une posture zero-trust et une souveraineté numérique totale.
Duplication sécurisée sans perte de souveraineté
Oui. Le fichier chiffré *.key.gpg peut être copié sur plusieurs supports souverains (EviKey NFC, NAS chiffré, QR code imprimé). Toutefois, il reste inutilisable sans la passphrase et le KDF, ce qui garantit une sécurité forte même en cas de fuite physique ou de compromission matérielle.
Résilience cryptographique face aux menaces quantiques
Une passphrase aléatoire ≥ 256 bits, combinée à un KDF mémoire-dur et à un chiffrement AES-256, offre une résistance élevée aux attaques symétriques, y compris celles basées sur l’algorithme de Grover. Cela dit, elle ne remplace pas les futurs algorithmes asymétriques post-quantiques nécessaires pour contrer les attaques de type Shor. En somme, c’est une protection robuste mais non exhaustive.
Récupération souveraine sans dépendance cloud
Si vous avez sauvegardé le fichier *.key.gpg (via QR imprimé, EviKey ou autre support sécurisé), vous pouvez restaurer la clé en injectant la passphrase via PassCypher HSM. Cette architecture permet une récupération sans perte, à condition que les backups aient été correctement gérés et conservés hors ligne.
Usage local recommandé pour préserver la posture souveraine
Bien que `ssh-agent` puisse améliorer le confort d’usage, il augmente la surface d’exposition en mémoire. Il est donc préférable de privilégier l’injection directe via PassCypher HSM PGP (BLE-HID), garantissant un déchiffrement éphémère, local et conforme à la logique zéro-clé-en-clair.
Opérations locales, zéro export
Oui. Comme tout HSM souverain, PassCypher HSM PGP ne transmet jamais la clé privée au client. Les opérations sensibles (signature, déchiffrement partiel) sont exécutées localement dans le moteur ou l’extension. Le client ne reçoit que le résultat chiffré, à l’image des HSM utilisés pour TLS ou PKI.
Incompatibilité avec la logique zéro-clé-en-clair
Le forwarding SSH-agent est incompatible avec la posture souveraine de PassCypher. La passphrase et la clé privée ne doivent jamais quitter le client ni transiter vers un hôte distant. Dans cette architecture, l’agent SSH reste strictement local à la session. Il est donc recommandé d’éviter le forwarding et de privilégier l’injection directe via BLE-HID sécurisé.
Appairage BLE sécurisé : bonnes pratiques
Même si PassCypher impose le mode Secure Connections Only, certaines plateformes (Android, iOS) ou piles Bluetooth peuvent être vulnérables à des attaques de rétrogradation vers un mode moins sûr comme Just Works.
Il est donc essentiel de :
- exiger une authentification par code numérique (saisie ou comparaison) ;
- forcer le bonding et stocker la clé d’appairage dans un coffre sécurisé (Secure Enclave / Android Keystore) ;
- vérifier que le canal BLE-HID utilise bien le chiffrement AES-128 CBC ;
- surveiller la liste des périphériques appairés et supprimer tout appareil inconnu ou inactif.
Comparez toujours les codes affichés avant validation. Cette étape garantit un canal chiffré de bout en bout.
Sauvegarde multi-supports sans compromis
Oui, à condition que la passphrase et le KDF restent confidentiels. Le fichier *.key.gpg peut être stocké sur EviKey NFC, NAS chiffré, USB ou QR code imprimé. Cette approche permet un “cold backup” souverain, sans aucune dépendance à un service cloud.
Vérification d’empreinte et confiance croisée
Avant d’insérer une clé publique dans authorized_keys, comparez son empreinte SHA-256 à celle affichée dans l’interface PassCypher. Pour renforcer la confiance, vous pouvez également vérifier le label/commentaire ou utiliser le ledger d’audit local.
Fonctionnement 100 % hors ligne
Oui. PassCypher HSM PGP est conçu pour fonctionner en environnement totalement déconnecté. Toutes les opérations (génération, chiffrement, injection, rotation) sont locales, garantissant une posture zero-trust et une souveraineté absolue.
Compatibilité universelle avec les VPS SSH
Oui. La clé publique est copiée sur le serveur distant (authorized_keys), tandis que la clé privée reste chiffrée localement. L’authentification s’effectue via injection BLE-HID, sans jamais exposer le secret.
Comparatif souverain : FIDO vs PassCypher
FIDO est adapté à l’authentification web sans mot de passe, mais ne permet ni usage SSH natif ni duplication. PassCypher HSM PGP, en revanche, offre une authentification SSH souveraine, avec clé exportable chiffrée, injection matérielle, et audit local. C’est la solution idéale pour les environnements critiques et multi-OS.
Rotation souveraine en 4 étapes
La rotation s’effectue en quatre étapes :
- Générer une nouvelle paire via PassCypher HSM PGP
- Déployer la nouvelle clé publique sur les serveurs
- Valider l’accès avec la nouvelle clé
- Retirer l’ancienne clé de
authorized_keys
Chaque action est consignée dans un ledger d’audit local, assurant une traçabilité complète.
Automatisation sécurisée dans les workflows DevOps
Oui. Grâce à l’orchestration par EviSSH, il est possible d’intégrer PassCypher HSM PGP dans un pipeline CI/CD sans compromettre la sécurité. La clé privée reste encapsulée dans son conteneur OpenPGP, et seule la passphrase est injectée via BLE-HID ou NFC. Cette méthode permet d’exécuter des actions cryptographiques à distance, tout en respectant la logique zéro-clé-en-clair et en maintenant une traçabilité locale.
Gestion des identités et cloisonnement des accès
Oui. PassCypher HSM PGP permet de gérer plusieurs identités cryptographiques sur un même terminal, chacune encapsulée dans son propre conteneur chiffré. Cela facilite le cloisonnement des accès SSH, la rotation des clés par utilisateur, et la journalisation indépendante des opérations. Cette modularité est particulièrement utile dans les environnements partagés ou administrés à distance.
Journalisation locale et vérification manuelle
Oui. Chaque opération (génération, rotation, révocation) peut être consignée dans un journal d’audit local, sous forme de fichier append-only. Ce fichier contient les empreintes, labels, horodatages et hôtes cibles. Il peut être vérifié manuellement ou intégré dans un système de supervision souverain. Cette approche garantit une traçabilité sans dépendance à un service tiers.
Transmission sécurisée sans clavier physique
L’injection BLE-HID simule une saisie clavier, mais via un canal Bluetooth sécurisé. La passphrase est transmise depuis le HSM vers le terminal, sans passer par le clavier physique ni par le système d’exploitation. Cela permet d’éviter les keyloggers, les hooks système et les interceptions réseau. Le canal est chiffré en AES-128 CBC, et l’appairage est validé par code numérique.
Fonctionnement hors ligne et autonomie complète
Oui. PassCypher HSM PGP est entièrement fonctionnel dans un environnement isolé du réseau. Toutes les opérations (génération, injection, rotation, sauvegarde) sont locales et ne nécessitent aucune connexion Internet. Cela en fait une solution idéale pour les infrastructures critiques, les serveurs sensibles ou les environnements militaires.
Rotation périodique et stratégie de révocation
La durée de vie dépend du contexte d’usage. En général, une rotation tous les 6 à 12 mois est recommandée pour les accès administratifs. PassCypher facilite cette rotation via un processus en quatre étapes : génération, déploiement, validation, retrait. Chaque étape est documentée et peut être automatisée via EviSSH. La révocation est effectuée par suppression ciblée dans authorized_keys.
Interopérabilité native et conformité technique
Oui. Les clés générées par PassCypher HSM PGP sont compatibles avec OpenSSH, PuTTY, Termux, Git Bash et autres clients SSH standards. Le format de la clé publique respecte les spécifications OpenSSH, et la clé privée encapsulée peut être utilisée après déchiffrement local. Cela garantit une compatibilité multi-OS sans adaptation technique.
Gestion typologique sans agent ni cloud
La gestion souveraine des clés SSH repose sur une architecture locale, sans agent ssh-agent, ni dépendance à un service cloud. PassCypher HSM PGP encapsule la clé privée dans un conteneur OpenPGP chiffré, injecté à la demande via NFC ou BLE-HID. Cette approche garantit une traçabilité complète, une rotation maîtrisée et une posture zéro-clé-en-clair.
Rotation typologique avec journal local append-only
La rotation s’effectue par régénération d’une nouvelle paire, déploiement de la clé publique, validation de l’accès, puis révocation de l’ancienne clé. Chaque étape est consignée dans un journal local append-only (ssh-keys-ledger.tsv), assurant une traçabilité horodatée et vérifiable.
Récupération sans affichage via QR, NFC ou BLE-HID
PassCypher HSM PGP propose plusieurs méthodes souveraines de récupération : QR chiffré (GIF/PNG), lecture NFC depuis un HSM physique, ou injection via émulateur de clavier BLE-HID. Aucune de ces méthodes n’expose la passphrase en clair, garantissant une restauration sécurisée sans saisie manuelle.
Accès multi-OS via clé OpenPGP encapsulée
La clé publique est copiée sur le VPS distant (OVH, Scaleway, etc.), tandis que la clé privée reste encapsulée localement. L’authentification s’effectue via injection matérielle (BLE-HID ou NFC), sans forwarding ni exposition du secret. Compatible Linux, Windows, macOS, Android, iOS.
Injection sans saisie clavier ni clipboard
PassCypher HSM PGP permet l’injection directe de la passphrase via NFC ou émulateur BLE-HID, simulant une saisie clavier sécurisée. Cette méthode évite toute saisie manuelle, tout stockage en mémoire vive, et tout usage du presse-papiers. Elle est idéale pour les environnements critiques ou air-gapped.
Conformité renforcée avec les standards cryptographiques
Oui. PassCypher HSM PGP intègre les meilleures pratiques SSH : usage de clés ed25519 ou RSA ≥4096 bits, encapsulation OpenPGP AES-256, KDF mémoire-dur (Argon2id), rotation typologique, journalisation locale, et injection matérielle. Il dépasse les standards classiques en proposant une posture souveraine et post-quantique.
Glossaire — SSH Key PassCypher HSM PGP & OpenSSH pour Windows / Linux VPS
ACL (liste de contrôle d’accès)
Définit les autorisations d’accès à un fichier ou répertoire. Sous Windows, les fichiers authorized_keys et administrators_authorized_keys doivent être limités à Administrators et SYSTEM. Sous Linux (Debian / VPS OVH), les droits 600 sont requis pour les clés SSH.
Air-gapped
Environnement totalement déconnecté du réseau. Les modules EviSSH et PassCypher HSM PGP peuvent fonctionner en mode air-gapped, garantissant qu’aucune clé ni flux BLE/NFC ne quitte le périmètre matériel souverain.
Authentification par clé publique
Méthode d’accès SSH reposant sur une paire de clés asymétriques (publique/privée). Supportée par OpenSSH pour Windows et Debian, elle supprime la nécessité d’un mot de passe et renforce la sécurité des VPS OVH.
Authentification par code numérique
Appairage sécurisé BLE fondé sur la saisie d’un code à six chiffres. Garantit un canal chiffré AES-CCM (niveau link layer) conforme à Bluetooth LE Secure Connections, évitant le mode non sécurisé “Just Works”.
BLE-HID (Bluetooth Low Energy — Human Interface Device)
Canal Bluetooth émulant un clavier physique. Dans PassCypher, il sert à injecter des passphrases chiffrées, réduisant les risques de keylogger matériels, mais ne protégeant pas un poste déjà compromis (hook clavier ou rootkit).
Bonding
Association persistante entre périphériques BLE. Dans PassCypher, permet la reconnexion sécurisée sans réappairage manuel.
Clé privée SSH
Fichier confidentiel d’authentification SSH stocké sous C:\Users\username\.ssh (Windows) ou ~/.ssh/id_ed25519 (Linux Debian VPS). Chiffré directement par OpenSSH lors de sa création via passphrase (bcrypt KDF + AES-256), ou protégé matériellement via HSM PassCypher.
Clé publique SSH
Fichier partageable copié sur le serveur dans authorized_keys (utilisateur standard) ou administrators_authorized_keys (administrateur). Utilisé pour valider les connexions SSH sans mot de passe.
Clé SSH OpenSSH chiffrée
Fichier natif (id_rsa, id_ecdsa, id_ed25519) protégé par passphrase via chiffrement interne OpenSSH (AES-256 + bcrypt KDF). Aucune encapsulation OpenPGP n’est utilisée.
EviEngine
Moteur cryptographique local développé par Freemindtronic. Orchestre la génération, la dérivation et la rotation des clés sans dépendance cloud.
EviKey NFC HSM
Clé matérielle NFC Freemindtronic servant de coffre-fort portable. Permet le stockage sécurisé des identités et passphrases SSH, PGP ou système. Peut injecter des secrets de manière souveraine via NFC sans contact.
EviSSH
Module intégré à PassCypher HSM PGP dédié à la gestion des clés SSH (génération, rotation, auditabilité). Compatible Windows et Linux.
Empreinte
Hash SHA-256 identifiant une clé SSH. Vérifiable par ssh-keygen -lf dans OpenSSH. Sert à valider la correspondance entre clé privée et clé publique avant déploiement.
Gestion des clés SSH
Processus d’administration des identités SSH sur Windows, Debian ou VPS OVH. PassCypher gère les clés SSH au format OpenSSH natif, chiffrées par passphrase, et injecte les passphrases via NFC ou BLE-HID souverain. Aucune encapsulation OpenPGP n’est utilisée.
KDF (Key Derivation Function)
Fonction de dérivation cryptographique (Argon2id, PBKDF2). Transforme une passphrase en clé robuste contre les attaques GPU/ASIC.
Ledger
Journal d’audit append-only des clés SSH générées, déployées ou révoquées. Permet la traçabilité complète dans PassCypher.
Linux Debian / VPS OVH
Environnement serveur courant pour héberger des services SSH. Compatible OpenSSH, PassCypher et EviSSH. Les fichiers clés se trouvent dans /home/username/.ssh avec droits stricts.
Man-in-the-Middle (MITM)
Attaque d’interception des communications. Neutralisée par vérification d’empreinte et chiffrement BLE sécurisé.
OpenSSH pour Windows
Version native d’OpenSSH intégrée à Windows 10, 11 et Server 2019–2025. Inclut ssh-keygen, ssh-agent, ssh-add, scp, sftp, et PowerShell SSH.
Pairing / Secure Connections
Procédure d’appairage Bluetooth sécurisée par ECDH (P-256) et chiffrement AES-CCM 128 bits au niveau du link layer.
PassCypher HSM PGP
HSM hybride (logiciel + matériel) développé par Freemindtronic pour générer, chiffrer et injecter des clés SSH au format OpenSSH natif, ainsi que des passphrases ou clés PGP, via canaux NFC ou BLE-HID souverains.
Passphrase (phrase secrète)
Phrase longue utilisée pour chiffrer la clé privée SSH. Demandée par ssh-keygen ou stockée via ssh-add. Composant essentiel de l’authentification à deux facteurs OpenSSH / PassCypher.
PBKDF2 / Argon2id
Algorithmes de dérivation de clé servant à durcir les passphrases. Argon2id est privilégié pour sa résistance aux attaques GPU.
Posture PQ-aware
Approche Freemindtronic anticipant les menaces quantiques par l’usage d’algorithmes symétriques résistants (≥ AES-256) et de passphrases à haute entropie. Les primitives asymétriques SSH (RSA, ECDSA, Ed25519) restent classiquement vulnérables à Shor — cette posture est donc symétrique-robuste, non PQC complète.
PowerShell SSH
Interface de commande native Windows permettant d’administrer OpenSSH (ssh-keygen, ssh-agent, scp) et d’automatiser la gestion des clés par script.
Rotation des clés SSH
Cycle de renouvellement souverain des clés (génération, déploiement, validation, retrait). Dans PassCypher, chaque action est consignée dans le ledger.
scp / sftp
Utilitaires OpenSSH servant à transférer des clés ou fichiers entre client et serveur. Compatibles avec Windows, Debian et OVH VPS.
Secure Enclave / Android Keystore
Modules matériels sécurisés pour le stockage des clés d’appairage BLE ou AES sur terminaux mobiles.
Service sshd
Service Windows gérant les connexions SSH entrantes. Peut être configuré pour démarrer automatiquement via PowerShell : Set-Service -Name sshd -StartupType Automatic.
SID (Security Identifier)
Identifiant unique Windows des comptes ou groupes utilisateurs. Recommandé pour configurer des ACL précises sur administrators_authorized_keys.
Sovereign SSH
Modèle souverain d’administration SSH fondé sur le chiffrement matériel, la traçabilité et l’indépendance cloud. Les clés SSH sont chiffrées nativement par OpenSSH avec passphrase, sans encapsulation OpenPGP. Compatible OpenSSH sur Debian, Windows et OVH VPS.
ssh-add
Commande OpenSSH qui charge une clé privée dans ssh-agent. Permet les connexions automatiques sans ressaisie de passphrase.
ssh-agent
Service en mémoire stockant temporairement les clés privées chargées. Dans PassCypher, remplacé par un déchiffrement éphémère local pour usage hors ligne.
ssh-keygen
Outil de génération de paires de clés SSH (RSA, ECDSA, Ed25519). Chiffre directement la clé privée avec une passphrase (bcrypt KDF + AES-256). Recommandé d’utiliser Ed25519 avec passphrase forte et stockage HSM souverain.
Tmpfs
Système de fichiers temporaire en RAM. Utilisé pour éviter toute écriture persistante de clés déchiffrées.
Windows 10 / 11
Systèmes d’exploitation intégrant nativement OpenSSH Client et Server. Compatibles avec les solutions HSM PassCypher et EviSSH.
Windows Server 2019 / 2022 / 2025
Versions serveur prenant en charge OpenSSH et PowerShell SSH. Permettent la configuration d’accès sans mot de passe via ACL et SID sécurisés.
Zero-clear-key
Principe souverain interdisant toute clé privée en clair sur disque ou réseau. Implémenté dans PassCypher et conforme aux standards OpenSSH.
Zero-trust
Approche de sécurité consistant à valider chaque action même dans un environnement maîtrisé. Appliquée à l’ensemble des solutions Freemindtronic.
Strategic Outlook — vers une souveraineté post-quantique
L’approche SSH Key PassCypher HSM PGP préfigure la convergence entre sécurité d’accès et résilience post-quantique.
En combinant stockage matériel, chiffrement symétrique renforcé et injection physique souveraine, elle construit un pont entre la cryptographie classique et les architectures hybrides PQC à venir.
Les prochaines itérations intégreront :
- des primitives hybrides (ed25519 + Dilithium) ;
- un canal BLE 5.3 avec chiffrement AES-256 GCM ;
- un support natif des journaux signés sur blockchain interne ;
- une compatibilité FIDO2 pour unifier SSH et authentification Web.
En attendant la généralisation des algorithmes PQC, la posture zero-clear-key demeure la défense la plus efficace : ne jamais laisser une clé privée exister ailleurs qu’en RAM chiffrée et temporaire.
Secure SSH key for VPS with PassCypher — Deploy a key-only posture from first boot using PassCypher NFC HSM PGP, port 22 blocking, Fail2ban jail, DROP-first iptables policy, and upstream firewall hardening for audit-ready SSH access.
Executive Summary
⚡ Goal
Deploy an auditable key-only posture from the very first boot: PasswordAuthentication no, public key injection, blocking port 22, Fail2ban jail, host firewall, and upstream firewall (e.g. OVH Network Firewall). Dedicated port: 49152.
💥 Scope
Server vps-d39243a8 (Debian). Root access via debian (public key injected). HSM used: PassCypher NFC HSM PGP. Optional hardware storage with EviKey NFC (hardware lock, no imposed encryption). Multi-cloud compatible: OVH, AWS, GCP, Proxmox, bare-metal.
🔑 Doctrine
Hardware trust chain: private keys encrypted with PGP (AES-256) via PassCypher, ephemeral local decryption, public-only injection on the VPS side, systematic logging (known_hosts.audit, rotation.log).
Zero trust posture: zero passwords, zero plaintext private keys, zero implicit trust. Portability: NFC, QR Code, JSON, BLE HID.
Key rotation: HSM generation, testing, injection, atomic replacement, sovereign traceability.
🌍 Strategic Differentiator
PassCypher NFC HSM PGP adopts a zero cloud, zero disk, zero DOM posture, with multi-format portability (QR, JSON, NFC) and multi-mode usage (NFC, BLE HID, camera). Up to 100 passphrases can be injected via a secure Bluetooth HID keyboard emulator (AES-128 CBC), and the number of SSH key pairs that can be created is unlimited — extremely cost-effective compared to competing solutions.
Summary reading time: ~1 minute
Full reading time: ~19 minutes
Test & verification time (commands included): 10–15 minutes
Total reading time (with tests): ~30–35 minutes
Level: Infra / SecOps
Posture: Key-only, defense-in-depth
Section: Tech Fixes & Security Solutions
Available in: FR · EN ·
Editorial type: Note
About the author: Jacques Gascuel, Freemindtronic® inventor — sovereign HSM architectures, key segmentation, and offline resilience.
PasswordAuthentication, run SSH on 49152, inject the public key generated by PassCypher NFC HSM PGP, block TCP/22, enable Fail2ban (3 attempts/5 min, 30 min ban), enforce iptables with default DROP policy allowing only 49152 + ESTABLISHED, and filter upstream via network firewall. Log everything: host fingerprints, SSH/Fail2ban logs, key rotation ledger.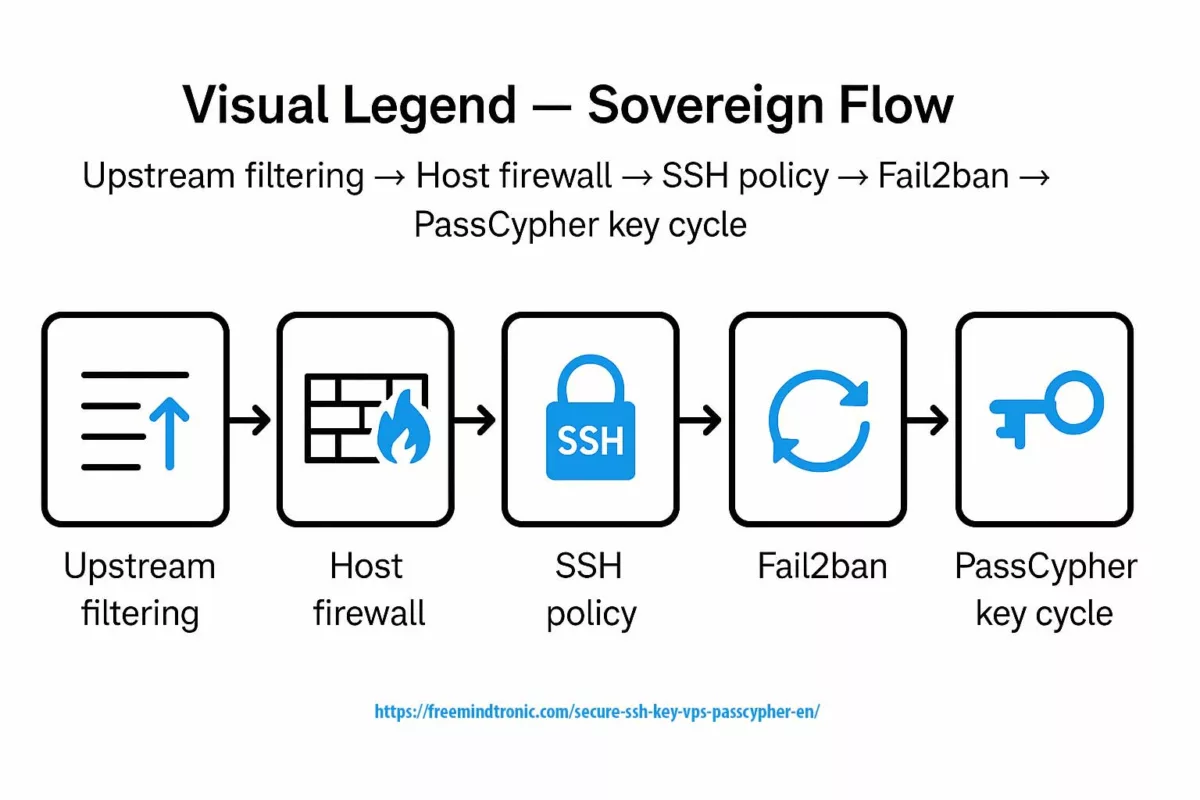
✺ Sovereign flow: upstream filtering → host firewall → SSH policy → Fail2ban → PassCypher key cycle
In infrastructure cybersecurity ↑ this note belongs to the Tech Fixes & Security Solutions section and is part of Freemindtronic’s sovereign operational toolkit (HSM, key segmentation, audit).
- Introduction — SSH and Access Hardening
- Threat Model — Attack Surface
- Weak Signals — Early Warnings
- Secure SSH key for VPS with PassCypher — key-only on 49152
- Secure VPS SSH Keys with PassCypher HSM PGP
- Fail2ban: jail sshd
- SSH keys with PassCypher NFC HSM PGP
- System Firewall (iptables)
- Upstream Firewall (provider level)
- Logging & Audit Doctrine
- Secure SSH key for VPS with PassCypher — PGP AES-256 Encrypted Private Key
- EviKey NFC Note (Hardware Locking)
- Sovereign Countermeasures
- What We Didn’t Cover
- Appendix: Key Commands
- FAQ — Frequently Asked Questions
Introduction — SSH and access hardening
For more than two decades, SSH (Secure Shell) has been the backbone of remote administration. Born in 1995 to replace Telnet and rlogin (RFC 4251), SSH brought encrypted traffic, strong authentication, and session integrity. Quickly adopted across GNU/Linux distributions and hosting providers, SSH has become the standard tool to manage dedicated servers, VPS, and cloud infrastructures.
SSH has evolved alongside the threat landscape. Initially focused on transport encryption, it soon integrated asymmetric key authentication. While passwords can be intercepted, reused, or brute-forced, an SSH key relies on a cryptographic pair (public/private). The server never stores the private key — it only keeps the authorized public key (authorized_keys). Authentication comes from a mathematical proof, not a reusable secret.
This paradigm shift has immediate impact:
- Resistance to brute force — an RSA 4096 or ECC P-384 key cannot be dictionary-attacked like a password.
- Passwordless posture — enabling
PasswordAuthentication noensures the server refuses any password attempt.
- Cryptographic proof — every session is signed uniquely with the private key.
- Auditability — each registered public key is traceable and can be revoked instantly.
In practice, using SSH keys turns a VPS into a stronger bastion, especially when combined with complementary measures like Fail2ban, a DROP-first iptables firewall, or a provider-level filter (e.g., OVHcloud Network Firewall).
This Tech Fixes & Security Solutions note focuses on a Debian VPS hosted by OVHcloud, illustrating the use of Secure SSH key for VPS with PassCypher. The same methods apply to any remote server, regardless of platform: an AWS VPS, a self-hosted LXC container, a Proxmox VM, or a physical server in a data center. The principle remains: no passwords, no implicit trust, no private keys in the clear.
Threat Model — Attack surface
Before deploying a key-only SSH VPS, it is essential to map out the threats. Any Internet-facing server becomes an immediate target for automated scans. Attackers don’t need to know who you are: botnets probe your IP as soon as it goes live. Understanding this threat model helps size a defense with sovereign controls.
- SSH bots & brute force ⛓ — Millions of dictionary attempts hit port 22 every day. Within 30 minutes of exposure, a weak VPS is already under attack. Mitigation: PasswordAuthentication no, a non-standard port (49152), and private key stored in PassCypher HSM.
- Software compromise (browser, password manager) ⚠ — Cloud password managers and browser extensions live in the DOM, making them prone to exfiltration via phishing, redressing, or XSS injection. Moving key generation and storage to an NFC/PGP HSM removes this vector.
- Private key leakage client-side ⎔ — A cleartext key in
~/.sshor cloud vault is a gift to malware. PassCypher encrypts the key with AES-256 (PGP), decrypts only on demand, and never leaves it in persistent memory.
- Insider & supply chain threats ⚯ — Whether from a malicious employee, a compromised provider, or a tainted build pipeline, insider risk is real. Hardware segmentation (key in PassCypher NFC HSM, backup in EviKey NFC) adds a provider-independent barrier.
Most attacks target SSH first. With Secure SSH key for VPS PassCypher, the private key never exists unencrypted, reducing client- and server-side risk.
Weak Signals — Early warnings
Defense doesn’t stop at today’s threats. Weak signals highlight tomorrow’s risks. Ignoring them means suffering what could have been anticipated.
- Smarter brute force ⚠ — Scanners no longer blindly hit 22/tcp. They now detect custom ports like 49152 and adapt their wordlists. Going key-only with an HSM becomes vital since port-hopping is not enough.
- Ransomware staging on VPS ⛓ — More APT groups use compromised VPS as relays, staging servers, or exfiltration nodes. A weak VPS can be weaponized against others without your knowledge.
- Regulatory pressure (NIS2 / DORA) ⚯ — EU regulations demand strict traceability and segmentation of privileged access. Soon, critical SSH keys will be required to be off-cloud, audited, and segmented. What is best practice today will soon be mandatory.
- Industrialized SSH phishing ⎔ — Dark web kits now deliver fake SSH login prompts to trap admins. If the private key stays inside an HSM rather than in a vulnerable client, phishing loses its bite.
Weak signals converge: smarter brute force, ransomware staging, regulatory push, and phishing kits. Sovereign response: PassCypher HSM PGP for off-cloud SSH keys, auditable rotation, and defense-in-depth through layered hardware and compliance.
Secure SSH key for VPS with PassCypher — key-only on 49152
The first lock: completely disable password authentication. As long as the server accepts a password, even a long one, it remains vulnerable to credential leaks and dictionary attacks. With a key-only SSH setup, the password is out of the equation, and the server only validates cryptographic proofs (OpenSSH man page). Combined with port 49152, this greatly reduces the attack surface.
1. sshd configuration
Edit the cloud-init drop-in to disable password logins:
/etc/ssh/sshd_config.d/50-cloud-init.conf
PasswordAuthentication no
Restart the service:
sudo systemctl restart sshd
2. Block port 22
Port 22 is the first target for bots. Don’t just change ports — explicitly block 22:
sudo iptables -A INPUT -p tcp --dport 22 -j DROP
This prevents rollback by mistake: even if someone re-enables PasswordAuthentication on 22, traffic is dropped upstream.
3. Password lock test
Once applied, test the lock yourself:
ssh -o PreferredAuthentications=password -p 49152 debian@51.75.200.82
# Expected: Permission denied (publickey)
This forced test confirms that the server rejects passwords, even if bots hammer it.
With PasswordAuthentication no and port 22 blocked, the server disappears from dictionary radars. Combined with port 49152 and keys generated in a PassCypher NFC HSM PGP, access becomes a bastion: no password attempts possible, only a valid hardware key can open the session.
Secure VPS SSH Keys with PassCypher HSM PGP
An SSH key is not just a file in ~/.ssh. When generated hastily on a laptop, it can leak, be copied into a cloud backup, or remain in plain text on a disk. With PassCypher NFC HSM PGP, the logic changes completely: the private key is born inside an offline Hardware Security Module (HSM), encrypted with AES-256 via PGP, and never leaves in clear form. Only the public part exits the HSM.
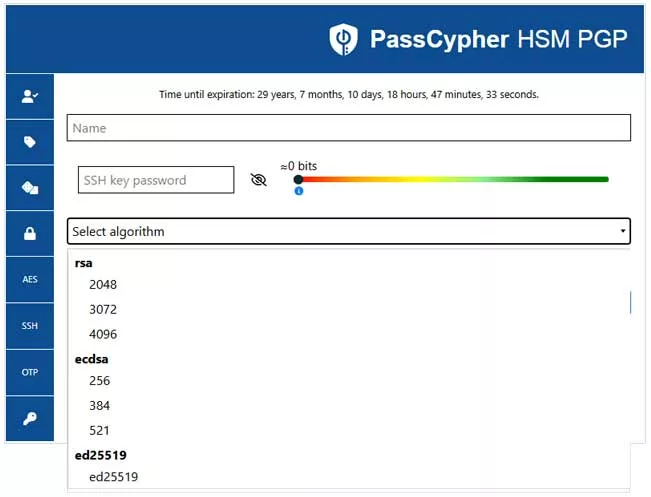
1. RSA / ECC Key Generation
Depending on your needs, you can choose:
RSA 2048 / 3072 / 4096for maximum compatibility.ECC P-256 / P-384 / P-521ored25519for modern, compact, and resilient keys.
In both cases, the private key is immediately encapsulated in *.key.gpg, protected by a sovereign passphrase defined by the user, entropy-checked in real time (Shannon), and requested via NFC.
2. Multi-format Exports
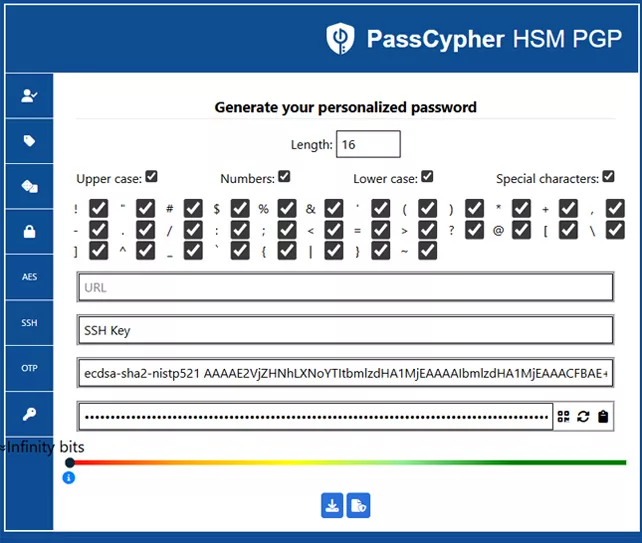
PassCypher offers several export modes to fit different environments:
*.pub: standard OpenSSH public key (to inject inauthorized_keys).*.key.gpg: PGP AES-256 encrypted private key, for daily use.- QR Code: temporary scannable container for quick injection into another NFC HSM.
- Segmented JSON: encrypted multi-fragment export, ideal for distributed storage or air-gapped vaults.
With PassCypher HSM PGP, the SSH pair can be encapsulated in an encrypted QR Code (public key + private key encrypted with passphrase).
Encryption relies on PGP AES-256 (OpenPGP); the passphrase is validated with real-time Shannon entropy checks.
This QR Code becomes a sovereign artifact: portable backup online or offline (air-gap), controlled restoration, and traceability — aligned with the Secure SSH key VPS PassCypher doctrine.
3. Step-by-Step Sovereign Workflow
- Step 1 — Sovereign Input: label name, login = SSH public key (.pub), password = PGP AES-256 encrypted private key.
- Step 2 — Encoded QR: sovereign backup artifact, storable online or offline (air-gap).
- Step 3 — Restoration: read QR Code via “Retrieve Label”, reuse via NFC HSM or BLE HID keyboard emulator (CLI included).
- Step 4 — Multi-mode Use: NFC HSM (physical read), QR → NFC (camera transfer), BLE HID emulator (inject passphrase and key locally).
- Step 5 — Air-gap Doctrine: keep the key encrypted, portable, and usable without network. Store it on EviKey NFC, export in encrypted JSON, or scan a temporary QR. Always encrypted, never in the cloud.
AES-256-CFB (Cipher Feedback) mode for data streams, with a session key derived via S2K SHA-256/512, plus a Modification Detection Code (MDC) to detect tampering. This follows the OpenPGP RFC 4880 standard.With PassCypher NFC HSM PGP, an SSH key is no longer just a sensitive file but a sovereign artifact: generated offline, encrypted with AES-256-CFB and sovereign passphrase, exportable as QR or segmented JSON, and usable via NFC or BLE HID.
Zero password storage, zero cloud, zero leakage.
Fail2ban: jail sshd
Changing the port and disabling password authentication already reduces the noise. But bots will still keep scanning and trying. Fail2ban acts here like an automated security guard: it watches logs, detects repeated failures, and bans the offending IP on the spot. A simple, efficient, and indispensable shield.
1. Installation & configuration
Install the package:
sudo apt install fail2ban
Create the file /etc/fail2ban/jail.local with a dedicated SSH block:
[sshd]
enabled = true
port = 49152
filter = sshd
logpath = %(sshd_log)s
maxretry = 3
findtime = 5m
bantime = 30m
2. Cleanup, activation & verification
Before enabling, clean any duplicates in [DEFAULT] and convert the file if needed:
sudo dos2unix /etc/fail2ban/jail.local
Start and check:
sudo systemctl restart fail2ban
sudo fail2ban-client status
3. Alert thresholds
By default, maxretry is often too permissive. Here, after 3 failures in 5 minutes, the IP is banned for 30 minutes.
On a sensitive bastion, you can increase bantime to several hours, or even set permanent bans.
Fail2ban monitors your SSH logs, enforces your thresholds, and bans abusive IPs automatically.
With 3 attempts max / 5 min on port 49152, automated scans stop cold.
Result: less noise, clearer logs, and a complementary defensive layer to the key-only + PassCypher HSM approach.
Every Secure SSH key for VPS with PassCypher becomes traceable, logged, and auditable.
SSH keys with PassCypher NFC HSM PGP
- Type: RSA 4096 or ECC P-384 generated on an air-gapped NFC HSM.
- Export:
FMT-VPS.pub(OpenSSH), private encrypted as*.key.gpg(PGP AES-256, passphrase via NFC). - Local decryption (usage):
gpg --decrypt --output ~/.ssh/FMT-VPS ~/.ssh/vps-fmt-ad-08-2025/FMT-VPS.key.gpg chmod 600 ~/.ssh/FMT-VPS - Public key injection into the VPS:
cat ~/.ssh/vps-fmt-ad-08-2025/FMT-VPS.pub | ssh -p 49152 debian@51.75.200.82 "mkdir -p ~/.ssh && chmod 700 ~/.ssh && cat >> ~/.ssh/authorized_keys && chmod 600 ~/.ssh/authorized_keys" - OVHcloud command: during VPS creation, paste
FMT-VPS.pubinto the “public SSH key” field for immediate key-only boot.
Keys created on HSM, private always encrypted at rest, only the public key is transferred to the server; OVH provisioning = security from the very first boot.
System firewall (iptables)
Here’s the step-by-step logic: first, block absolutely all incoming traffic. Then, open only what is essential — your custom SSH port (49152) and already established connections. This so-called DROP-first model (Netfilter.org) is a sovereign best practice: it drastically reduces the attack surface and turns your VPS into a key-only SSH bastion.
1. Default policy (DROP-first)
Block everything inbound, except what you explicitly allow:
# Default policy
sudo iptables -P INPUT DROP
sudo iptables -P FORWARD DROP
sudo iptables -P OUTPUT ACCEPT
2. Minimal exceptions (49152 + ESTABLISHED)
Next, add survival rules:
# Loopback
sudo iptables -A INPUT -i lo -j ACCEPT
# SSH on 49152
sudo iptables -A INPUT -p tcp --dport 49152 -j ACCEPT
# Established connections
sudo iptables -A INPUT -m conntrack --ctstate ESTABLISHED,RELATED -j ACCEPT
Result: 49152 is the only open door, and any unexpected traffic is dropped by default.
3. Persistence with netfilter-persistent
Without persistence, your rules vanish after a reboot. Save them properly:
sudo apt install iptables-persistent
sudo netfilter-persistent save
At every restart, the system reloads your rules automatically, ensuring defensive consistency.
A VPS without a firewall is an unintentional honeypot. With a DROP-first strategy + a single SSH exception on 49152, your attack surface collapses and reinforces the use of Secure SSH key for VPS with PassCypher. Combined with Fail2ban and the upstream firewall, iptables becomes the second barrier in a true defense-in-depth doctrine.
Upstream firewall (provider level)
Your VPS doesn’t live in a vacuum — it’s plugged into the global Internet, constantly swept by scanners and bots. Letting everything reach your server is like trying to filter a storm with a colander. That’s where the upstream firewall comes in, offered by most providers (OVHcloud, AWS Security Groups, Proxmox datacenter firewall, etc.).
1. Dashboard configuration
With OVHcloud, you can enable a network firewall (OVHcloud docs) directly from the customer panel. This is an upstream filter that blocks traffic before it even reaches the VPS public IP. It reduces background noise and shields your system resources from endless scans.
2. TCP/49152 filtering
The baseline rule:
- Allow only
TCP/49152(your custom SSH port). - Optional: allow ICMP (ping) if monitoring is required.
- Block everything else: no default openings beyond this.
With this policy, even if someone runs a massive scan, the traffic never reaches your VPS. It’s your first layer of hardware defense.
3. Upstream + iptables = defense-in-depth
The upstream firewall doesn’t replace iptables — it complements it. The sovereign logic is simple:
- Layer 1 — provider: filters traffic before it hits the VM.
- Layer 2 — system: iptables only allows 49152 and established connections.
- Layer 3 — application: Fail2ban bans abusive IPs based on log analysis.
This is the very definition of defense-in-depth: multiple independent walls, absorbing the attack before it becomes critical.
An upstream firewall (OVH or equivalent) acts as an external shield: it blocks global Internet noise before it ever hits your VPS. Combined with iptables and Fail2ban, your architecture effectively shifts into bastion mode.
Logging & audit doctrine
Securing a server is one step — continuously auditing it is what ensures resilience. In other words, logging becomes your digital surveillance system: SSH host key fingerprinting, Fail2ban jail activity, and system diagnostics. Every recorded line is a sovereign artifact. This way, you can always prove your VPS compliance with regulatory frameworks (NIS2, DORA) and align with a zero-trust security posture.
1. Server fingerprint (ssh-keyscan)
Document your VPS public fingerprint at first contact:
ssh-keyscan -p 49152 51.75.200.82 >> ~/.ssh/known_hosts.audit
This creates a host key fingerprinting registry. If the fingerprint ever changes, you know something is wrong (Man-in-the-Middle attack, unexpected rebuild, etc.).
2. SSH & Fail2ban logs
Export logs regularly:
sudo journalctl -u ssh > ~/ssh-access.log
sudo journalctl -u fail2ban > ~/fail2ban.log
These files tell the story of who connected, who failed, and who was banned. They form your incident black box and your ongoing audit trail.
3. Config diagnostics (sshd & jail.local)
A proactive audit helps you avoid simple mistakes:
# Check for stray PasswordAuthentication yes
sudo grep -Ri password /etc/ssh/sshd_config.d/
# Debug active Fail2ban jails
sudo fail2ban-client -d
# Continuously read Fail2ban events
sudo journalctl -u fail2ban -l --no-pager
With this, you detect conflicting directives, duplicate ports, and broken jails.
4. Security artifact ledger
The Freemindtronic doctrine recommends recording every event into a dedicated ledger:
known_hosts.audit→ host key fingerprintsssh-access.log→ SSH connectionsfail2ban.log→ Fail2ban jail bansrotation.log→ SSH key rotation history
This isn’t paperwork — it’s sovereign proof. If tomorrow someone asks “who had access and when was the key rotated”, you open the ledger, not your memory. It effectively acts as your SSH key rotation ledger for zero-trust audit.
No audit, no trust. With host key fingerprinting, exported logs, and a security artifact ledger, every key is traceable, every ban verifiable, and every anomaly detectable. This forms a continuous audit trail, the backbone of a zero-trust doctrine and the foundation of Secure SSH key for VPS with PassCypher.
Secure SSH key for VPS with PassCypher — PGP AES-256 Encrypted Private Key
An SSH key, even when generated in a sovereign HSM, is never permanent. At regular intervals — or as soon as doubt arises — it must be replaced. This is the principle of operational rotation: generate a new pair, test it, inject it, then log the event. In a VPS secured with PassCypher HSM, this rotation is the equivalent of changing the cryptographic locks of your infrastructure.
⮞ Outcome
No obsolete key remains active, and the entire system stays aligned with the defense-in-depth doctrine, with built-in traceability and resilience.
⮞ Next Step
To maintain the cryptographic posture of a VPS secured with PassCypher HSM, each rotation must be paired with rigorous generation and sovereign export of the new keys.
Secure SSH key for VPS with PassCypher — PGP AES-256 Encrypted SSH Private Key, Zero Exposure with HSM
In a VPS secured with PassCypher HSM, each private key is generated inside an NFC HSM, then immediately encrypted with PGP AES-256. It never exists in cleartext, except during a temporary decryption in RAM for local use. This posture guarantees sovereign security — cloud-free and disk-free.
1. Generation & Export
From your HSM, generate a new pair:
# OpenSSH public key + encrypted private key
FMT-VPS-new.pub
FMT-VPS-new.key.gpg
The private key is immediately encrypted with PGP AES-256. It never exists in cleartext unless you decrypt it temporarily in RAM for usage.
2. Temporary Local Decryption
To use the new key, decrypt it only into RAM:
gpg --decrypt --output ~/.ssh/FMT-VPS-new ~/.ssh/vps-fmt-ad-08-2025/FMT-VPS-new.key.gpg
chmod 600 ~/.ssh/FMT-VPS-new
The passphrase is entered via NFC, and the key is removed from disk if auto-purge is enabled.
3. Atomic authorized_keys Replacement
Connect with the old key while still valid, then overwrite the file:
echo "$(cat ~/.ssh/vps-fmt-ad-08-2025/FMT-VPS-new.pub)" > ~/.ssh/authorized_keys
chmod 600 ~/.ssh/authorized_keys
This is an atomic replacement: the old key is eliminated in a single step, leaving no duplicates.
4. Testing & Logging
Validate access immediately:
ssh -i ~/.ssh/FMT-VPS-new -p 49152 debian@51.75.200.82
Then log the operation:
ssh-keyscan -p 49152 51.75.200.82 >> ~/.ssh/known_hosts.audit
echo "# SSH Rotation - $(date)" >> ~/.ssh/rotation.log
The ledger (rotation.log) keeps a record: which key, on which day, with which justification.
⮞ Summary
Sovereign SSH key rotation prevents operational drift: each new key is generated in the HSM, tested, injected, and logged. Result: complete traceability and security always aligned with the zero trust doctrine.
Rotation is not optional but a sovereign routine. Generation in HSM, temporary local usage, atomic replacement, and logging: each cycle becomes a traceable artifact, ensuring infrastructure remains up to date and immune to obsolete keys.
EviKey NFC Note (Hardware Locking)
EviKey NFC is neither a software manager nor just an encrypted vault. It is first and foremost a sovereign hardware USB key, relying on NFC-based physical locking. While locked, the operating system doesn’t even see it: it is literally invisible. Once unlocked via NFC, it behaves like a standard USB drive, but with a programmable auto-lock (30s, 2min, etc.), reducing the risks of forgetfulness or compromise.
In practice, within our security doctrine, the SSH private key is already encrypted by PassCypher HSM PGP (AES-256). There is therefore no need for double encryption. EviKey adds two decisive guarantees: physical control (no NFC unlock = no access) and offline air-gap resilience.
Outcome: EviKey becomes the ideal tool to transport a sovereign SSH private key already encrypted (*.key.gpg file, temporary QR Code, or segmented JSON), without fearing cleartext leakage. It acts as a portable hardware firewall, perfectly integrated into Freemindtronic’s sovereign doctrine.
Complementary Use
- Hardware storage: private key already encrypted (e.g.
*.key.gpg) stored on EviKey. - Physical lock: invisible until unlocked by NFC.
- Auto-lock: automatic isolation after use.
- Optional layer: not a replacement for PassCypher, but a complement for portability and resilience.
⮞ Summary
EviKey NFC adds a physical layer of locking and auto-lock, ideal for transporting your encrypted artifacts. It complements PassCypher: the key remains protected with AES-256, while EviKey ensures hardware invisibility when not in use.
📖 Related Resource
For a full guide on using EviKey NFC for secure SSH key storage (instructions, use cases, sovereign doctrine), see: Secure SSH key storage with EviKey NFC HSM.
Appendix: key commands
Here are the essential commands to harden a Debian VPS with key-only SSH on port 49152, a fail2ban jail, and a DROP-first iptables policy. Each commented line (#) explains its role:
# 1. Block port 22 for defense-in-depth
sudo iptables -A INPUT -p tcp --dport 22 -j DROP
# 2. Test forced password login (must fail)
ssh -o PreferredAuthentications=password -p 49152 debian@51.75.200.82
# Expected result: Permission denied (publickey)
# 3. Export SSH logs for audit
sudo journalctl -u ssh > ~/ssh-access.log
# 4. Export fail2ban logs
sudo journalctl -u fail2ban > ~/fail2ban.log
These commands are your survival kit: port 22 blocking, forced password test, and log export. Simple but vital, they guarantee instant verification of your sovereign posture and provide traceability in case of incident.
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAACmFlczI1Ni1jdHIAAAAGYmNyeXB0AAAAGAAAABB188vMKS
[... truncated for readability ...]
-----END OPENSSH PRIVATE KEY-----
A modern OpenSSH private key always appears in this base64-wrapped form. When protected by a passphrase, it is readable only if the user provides that secret.
With Secure SSH key for VPS with PassCypher, this private key never exists in cleartext: it is encapsulated and protected by PGP AES-256 encryption, with the passphrase stored sovereignly inside the NFC HSM.
⮞ Result: even if a *.key file leaked, it would remain unusable without both the HSM and the passphrase.
Sovereign Countermeasures
Software password managers (Bitwarden, 1Password, LastPass…) do not handle the hardware creation of SSH keys. They only store private keys in encrypted vaults, often exposed to the browser or the cloud. This widens the attack surface and introduces software dependency. The LastPass incidents proved it: once a vault is compromised, the whole ecosystem collapses.
By contrast, PassCypher HSM PGP enforces sovereign custody. The SSH private key is not a vulnerable file: it is generated directly inside an HSM, encrypted with PGP AES-256, and never circulates in cleartext. It becomes a sovereign artifact, tamper-proof and portable.
Sovereign Advantages
- Multi-format portability: export as
*.key.gpg, QR Code, or segmented JSON container. - Multi-mode usage: NFC HSM, QR camera import, Bluetooth HID keyboard injection.
- Air-gap doctrine: offline usability, NFC physical unlocking mandatory.
- Zero DOM / Zero Cloud: no secret exposed in the browser, no server dependency.
- Resilience: backup possible on EviKey NFC (auto-lock hardware protection) or QR → NFC HSM transfer.
Zero Trust & Zero Knowledge Doctrine — zero password, zero plaintext key
- Zero Trust: no external actor (cloud provider, hypervisor, admin) ever has access to the private key.
- Zero Knowledge: the private key never exists in cleartext outside the HSM enclave.
Strategic Differentiator — why choose PassCypher
Unlike cloud HSMs (AWS CloudHSM, Azure Key Vault) or proprietary keys (Yubikey, Nitrokey, SoloKeys), PassCypher NFC HSM PGP is built on a zero cloud, zero disk, zero DOM architecture. No third-party software required, no secrets exposed to the browser, no server dependency.
Its multi-format portability (QR, JSON, NFC), multi-mode usage (NFC, BLE HID, camera), and full air-gap compatibility make it a unique, sovereign, and auditable solution — tailored for critical, self-hosted, or multi-cloud environments.
⮞ Cost-effectiveness and Scalability
The PassCypher NFC HSM can store up to 100 secure passphrases for SSH private keys, injectable via a secure Bluetooth keyboard emulator (BLE HID in AES-128 CBC). These passphrases can inject SSH keys, passwords, or secrets — without ever exposing the private key in cleartext.
The number of SSH private key pairs generated with PassCypher HSM PGP is unlimited, with no per-key cost, since this functionality is natively included in its passwordless secret and password management services. This makes PassCypher particularly cost-effective for high-rotation infrastructures, multi-user environments, or role-segmented architectures.
⮞ Outcome
A sovereign, portable, scalable, and independent solution, designed for architectures requiring security, traceability, and operational autonomy. PassCypher HSM PGP enables unlimited SSH key pair generation, secure injection via BLE HID, and the storage of 100 passphrases without per-key cost — ensuring built-in ROI and seamless multi-cloud compatibility without software dependency.
⮞ Summary
Unlike software password managers, PassCypher HSM PGP generates and stores your SSH keys outside the cloud, outside the disk, and outside the DOM. The private key never exists in cleartext, not even locally. With its multi-format portability (QR, JSON, NFC), multi-mode usage (NFC, BLE HID, camera), and zero trust doctrine, PassCypher delivers sovereign independence, complete traceability, and uncompromised operational security.
What We Didn’t Cover
Note — outside the scope of this guide:
- Kernel hardening (sysctl.conf, AppArmor, SELinux) — complementary measures but not treated here.
- IDS/IPS (Snort, Suricata) — real-time intrusion detection, outside minimal SSH + firewall scope.
- Reverse proxy / HAProxy — application flow management (HTTP/HTTPS), deliberately excluded.
- Resilience snapshots & backups — OVHcloud provides snapshot/backup mechanisms not covered here.
The objective here is to focus exclusively on the SSH chain: sovereign key generation, system hardening, and defense-in-depth layers.
FAQ — Frequently Asked Questions
This FAQ compiles recurring questions from sysadmins and SecOps across forums, tickets, and field feedback.
It evolves with weak signals and sovereign operational practices.
Why choose port 49152?
It doesn’t replace key-based auth, but it reduces noise and trivial attempts.
Pair it with a fail2ban jail config for custom SSH port 49152 and a DROP-first iptables policy.
What happens if I lose my HSM?
From creation, your SSH private key is a PGP AES-256 encrypted OpenSSH private key with NFC HSM,
protected by your sovereign passphrase. You may keep as many encrypted copies as needed on different media
without exposing the raw key. Recovery works via a QR code compatible with NFC HSM or segmented JSON.
How do I back up and restore a sovereign SSH key?
⮞ In practice, PassCypher HSM PGP lets you multiply encrypted backups as needed:
- Passphrase for the SSH private key: QR → PassCypher NFC HSM.
- Online archive (secure, encrypted SSH key): Cloud, NAS, email, etc.
- Offline archive (secure, encrypted SSH key): USB, SD, SSD, HDD, CD.
- Contactless media: NFC NDEF Cardokey™ Pro, EviKey® NFC USB, or EviDisk® NFC SSD.
- Digital media: QR codes readable by any scanner, including PassCypher’s recovery UI.
Log each step in rotation.log to preserve traceability.
Result: access remains blocked by design for an attacker, yet fully recoverable by you via a
QR code backup for SSH keys air-gapped recovery.
Does PassCypher replace software password managers?
where software managers remain exposed to the browser surface. They can coexist, but sensitive SSH keys should remain in the HSM.
Do these Secure SSH keys work on any VPS (OVH, AWS, GCP, Proxmox, bare-metal)?
The principle is the same: generate in PassCypher NFC HSM PGP → inject the public key →
enforce
PasswordAuthentication no → filter with provider firewall + iptables.Why not just rely on FIDO/WebAuthn?
PassCypher’s hardware-rooted guard (OpenPGP AES-256-CFB, segmented key options, Zero DOM)
avoids browser exposure and preserves an air-gapped workflow.
Are the QR code and segmented JSON container safe?
The QR code is a portable vector (air-gap); segmented JSON requires controlled reconstruction.
Without the decryption phrase (via NFC/PassCypher), the content is unusable.
Daily-use compatibility (Windows/macOS/Linux)?
Injection can leverage NFC/QR or a BLE HID keyboard emulator for passphrase entry on any host that accepts USB HID.
How do I rotate keys without risking a lock-out?
Keep a rescue session open. Log each step in
rotation.log and known_hosts.audit.This feeds your SSH key rotation ledger for zero-trust audit.
What is StrictHostKeyChecking for in SSH?
if the server fingerprint changed. With known_hosts.audit, you maintain a registry of
host key fingerprinting. Setting
StrictHostKeyChecking yes blocks MITM,but requires disciplined, manual validation on any fingerprint change.
Do NIS2/DORA audits require SSH key rotation?
That implies regular SSH key rotation, usage journals (
rotation.log), and the ability to revoke keys on the fly.PassCypher’s hardware-rooted generation, multi-format cycle (QR, JSON, NFC), and native audit support this doctrine.
What if ransomware hits my VPS?
With Secure SSH key for VPS with PassCypher, your private keys stay off-server (HSM, encrypted QR, segmented JSON).
If compromised, you can restore access on a fresh instance by re-injecting the public key from sovereign backups.⮞ Doctrine: keep at least one offline backup (printed QR or air-gapped encrypted JSON) for rapid recovery.
SSH VPS sécurisé avec PassCypher HSM — posture key-only dès le boot via NFC HSM PGP, blocage du port 22, Fail2ban, iptables DROP-first et filtrage amont OVH
Résumé Exécutif
⚡ Objectif
Mettre en production une posture key‑only auditable dès le premier boot : PasswordAuthentication no, injection de la clé publique, blocage du port 22, jail Fail2ban, pare‑feu système et pare‑feu amont (ex. OVH Network Firewall). Port dédié : 49152.
💥 Portée
Serveur vps-d39243a8 (Debian). Accès root via debian (clé publique injectée). HSM utilisé : PassCypher NFC HSM PGP. Stockage matériel optionnel sur EviKey NFC (verrouillage matériel, pas de chiffrement imposé). Compatible multi-cloud : OVH, AWS, GCP, Proxmox, bare-metal.
🔑 Doctrine
Chaîne de confiance matérielle : clés privées chiffrées PGP (AES‑256) via PassCypher, déchiffrement local éphémère, injection publique uniquement côté VPS, journalisation systématique (known_hosts.audit, rotation.log).
Posture zero trust : zéro mot de passe, zéro clé privée en clair, zéro confiance implicite. Portabilité : NFC, QR Code, JSON, HID BLE.
Rotation des clés : génération HSM, test, injection, remplacement atomique, traçabilité souveraine.
🌍 Différenciateur stratégique
PassCypher NFC HSM PGP adopte une posture zero cloud, zero disque, zero DOM, avec portabilité multi-format (QR, JSON, NFC) et usage multi-mode (NFC, HID BLE, caméra). Jusqu’à 100 passphrases peuvent être injectées via un émulateur de clavier Bluetooth sécurisé en AES‑128 CBC (HID BLE), et le nombre de paires de clés SSH créables est illimité — une rentabilité extrême face aux solutions concurrentes.
Temps de lecture (résumé) : ~1 minute
Temps de lecture (intégral) : ~19 minutes
Temps de test & vérification (commandes incluses) : 10–15 minutes
Temps de lecture total (avec tests) : ~30–35 minutes
Niveau : Infra / SecOps
Posture : Key-only, defense-in-depth
Rubrique : Tech Fixes & Security Solutions
Langues disponibles : FR · EN ·
Type éditorial : Note
À propos de l’auteur : Jacques Gascuel, inventeur Freemindtronic® — architectures HSM souveraines, segmentation de clés et résilience hors-ligne.
PasswordAuthentication no, opérez SSH sur 49152, injectez la clé publique générée par PassCypher NFC HSM PGP, bloquez TCP/22, installez Fail2ban (3 tentatives/5 min, ban 30 min), imposez iptables en DROP par défaut avec exception 49152 + ESTABLISHED, et filtrez en amont via Network Firewall. Journalisez : empreinte serveur, logs SSH/Fail2ban, ledger de rotation de clés.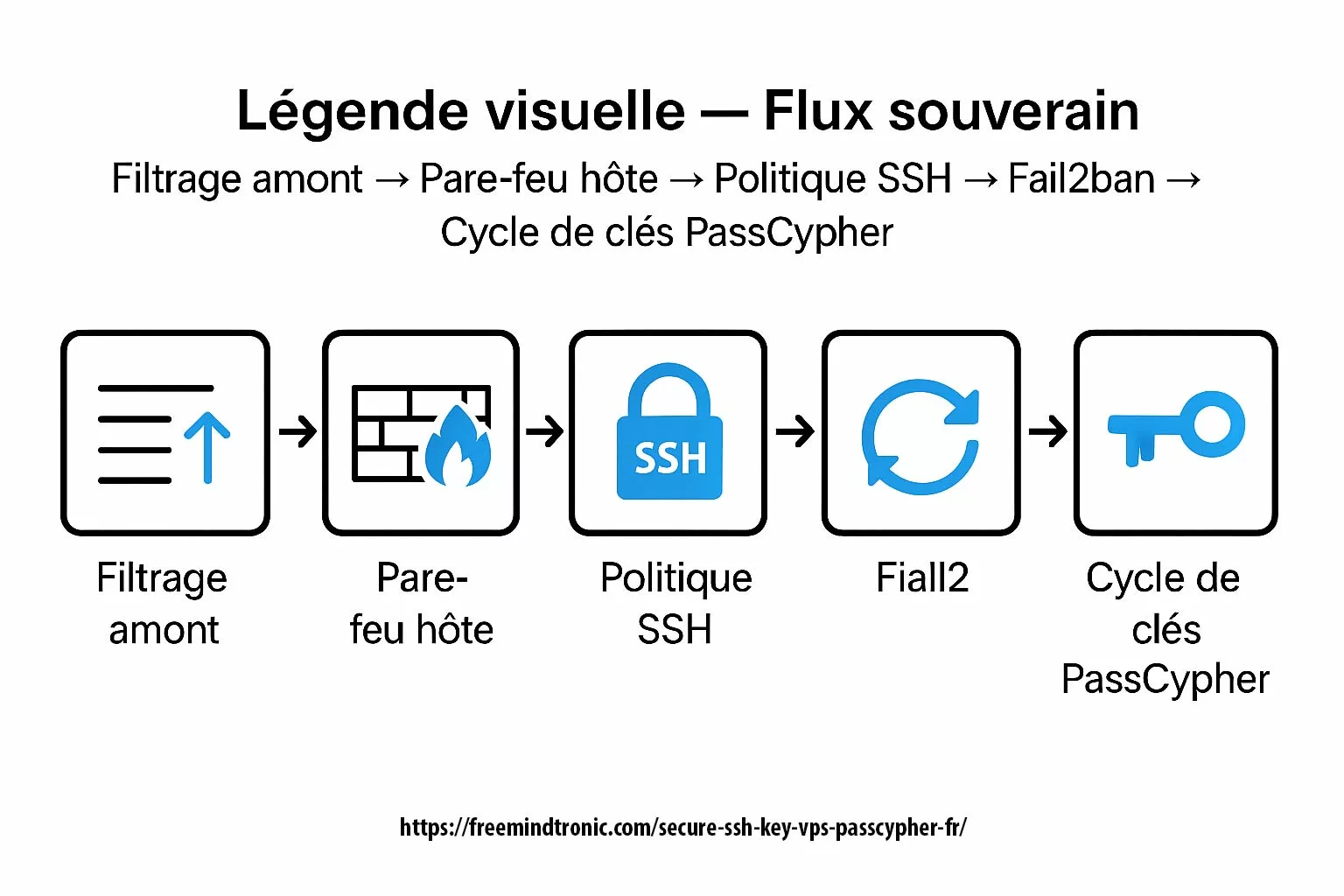
En cybersécurité d’infrastructure ↑ cette note appartient à la rubrique Tech Fixes & Security Solutions et s’inscrit dans l’outillage opérationnel souverain de Freemindtronic (HSM, segmentation de clés, audit).
- Résumé Exécutif
- Introduction — SSH et durcissement d’accès
- Threat Model — Modèle de menace
- Weak Signals — Signaux faibles
- Secure SSH key VPS PassCypher — key-only sur 49152
- Clés SSH VPS sécurisé avec PassCypher HSM PGP
- Fail2ban : jail
sshd - Pare‑feu système (iptables)
- Pare‑feu en amont (hébergeur)
- Journalisation & doctrine d’audit
- Rotation souveraine des clés SSH
- Note EviKey NFC (verrouillage matériel)
- Ressource associée
- Contre-mesures souveraines pour sécuriser les clés SSH
- Contre mesures souveraines
- What We Didn’t Cover
- FAQ — Questions fréquentes
Introduction — SSH et durcissement d’accès
Depuis plus de deux décennies, SSH (Secure Shell) est la colonne vertébrale de l’administration distante. Né en 1995 de la volonté de remplacer Telnet et rlogin (RFC 4251), il apporte chiffrement des flux, authentification robuste et intégrité des sessions. Rapidement adopté par les distributions GNU/Linux et les hébergeurs, SSH est devenu l’outil standard pour gérer serveurs dédiés, VPS et infrastructures cloud.
L’évolution de SSH a suivi la courbe des menaces. D’abord centré sur le chiffrement du transport, il a ensuite intégré l’authentification par clés asymétriques. Là où un mot de passe peut être intercepté, réutilisé ou brute-forcé, une clé SSH repose sur un couple cryptographique (publique/privée). Le serveur ne stocke jamais la clé privée : il ne conserve que la clé publique autorisée (authorized_keys). L’authentification résulte d’une preuve mathématique, pas d’un secret réutilisable.
Ce changement de paradigme a un impact immédiat :
- Résistance au brute force — une clé RSA 4096 ou ECC P-384 n’est pas attaquable par dictionnaire comme un mot de passe.
- Suppression du mot de passe — en activant
PasswordAuthentication no, le serveur n’accepte plus aucune tentative par mot de passe. - Preuve cryptographique — chaque session repose sur une signature unique générée par la clé privée.
- Auditabilité — chaque clé publique inscrite est traçable et peut être révoquée à chaud.
Dans la pratique, l’usage de clés SSH transforme un VPS en bastion plus difficile à corrompre, en particulier lorsqu’il est couplé à des mesures complémentaires comme Fail2ban, un pare-feu iptables ou un filtrage en amont par l’hébergeur (ex. OVHcloud Network Firewall).
Cette Tech Fixes & Security Solutions prend pour fil conducteur un VPS Debian hébergé chez OVHcloud. Elle illustre l’usage d’un SSH VPS sécurisé avec PassCypher HSM, applicable à tout environnement multi-cloud. Les méthodes décrites s’appliquent à tout serveur distant, quel que soit l’hébergeur ou la plateforme : un VPS chez AWS, un conteneur LXC auto-hébergé, une VM sur Proxmox ou un serveur physique en data center.
⮞ Doctrine constante
Dans un SSH VPS sécurisé avec PassCypher HSM, la posture cryptographique repose sur trois principes : zéro mot de passe, zéro confiance implicite, zéro clé privée en clair. Cette approche garantit une résilience native, même en cas de compromission totale.
⮞ Point clé :
SSH est universel, mais sa sécurité dépend du mode d’authentification choisi. Avec une clé privée gardée dans un HSM PassCypher NFC/PGP, on franchit un seuil : la clé n’existe jamais en clair sur le disque, elle n’est jamais exposée au navigateur ni au cloud, et elle reste utilisable en air-gap.
Threat Model — Modèle de menace
Avant de déployer un VPS avec SSH key-only, il faut cartographier les menaces. Un serveur exposé sur Internet devient immédiatement la cible de scans automatisés. Les attaquants n’ont pas besoin de savoir qui vous êtes : un botnet va tester votre IP dès qu’elle est active. Comprendre ce modèle de menace, c’est anticiper les attaques réelles et dimensionner une défense souveraine.
- Bots & brute force SSH ⛓ — Des millions de tentatives par dictionnaire frappent chaque jour les ports standards (22/tcp). En 30 minutes après mise en ligne, un VPS non durci reçoit déjà ses premières salves. La parade : PasswordAuthentication no, port non conventionnel (49152), clé privée en HSM PassCypher.
- Compromission logicielle (navigateur, gestionnaire) ⚠ — Les gestionnaires de mots de passe et les extensions de navigateur restent dans le DOM. Ils peuvent être exfiltrés par redressing, phishing ou injection XSS. Déporter la génération et le stockage dans un HSM NFC/PGP élimine ce vecteur.
- Fuite de clé privée côté client ⎔ — Une clé privée en clair dans
~/.sshou dans un gestionnaire cloud est un cadeau pour un malware. PassCypher chiffre la clé avec AES-256 (PGP), ne la déchiffre qu’à la demande et jamais en mémoire persistante. Sans HSM, la fuite devient quasi inévitable tôt ou tard. - Menaces internes & supply chain ⚯ — Qu’il s’agisse d’un employé malveillant, d’un fournisseur de cloud compromis ou d’une chaîne de build infectée, la menace interne reste une réalité. La segmentation matérielle (clé dans un PassCypher NFC HSM, sauvegarde sur EviKey NFC) introduit une barrière supplémentaire, indépendante du fournisseur.
⮞ Synthèse
Les attaques ciblent en priorité le service SSH. Dans un SSH VPS sécurisé avec PassCypher HSM, la clé privée n’existe jamais en clair, ce qui réduit drastiquement les risques côté client comme côté serveur.
Weak Signals — Signaux faibles
Une défense ne s’arrête pas à ce qu’on voit aujourd’hui. Les signaux faibles, eux, annoncent les risques de demain. Ignorer ces micro-tendances, c’est subir demain ce qu’on aurait pu anticiper aujourd’hui.
- Hausse des brute force SSH ciblés ⚠ — Les scanners ne se contentent plus de taper 22/tcp au hasard. Ils détectent désormais les custom ports comme 49152 et adaptent leurs dictionnaires. Le passage en key-only via HSM devient vital, car changer de port ne suffit plus.
- Exploitation des VPS dans les ransomwares ⛓ — De plus en plus de groupes APT utilisent des VPS compromis comme relais, staging ou nœud d’exfiltration. Un VPS faible devient non seulement une porte d’entrée, mais aussi une arme retournée contre d’autres. Votre machine peut servir à attaquer un tiers sans que vous le sachiez.
- Pression réglementaire (NIS2 / DORA) ⚯ — L’Europe impose une traçabilité et une segmentation stricte des accès. Les autorités exigent bientôt que les clés SSH critiques soient hors cloud, auditées et segmentées. Ce qui est aujourd’hui une bonne pratique deviendra demain un impératif légal.
- Industrialisation du phishing SSH ⎔ — Des kits vendus sur le darkweb proposent désormais de piéger les administrateurs SSH via fake login prompts. Si la clé privée reste dans un HSM et non dans un client vulnérable, le phishing perd son effet.
⮞ Synthèse
Les signaux faibles convergent : brute force intelligent, ransomware distribué, pression NIS2/DORA et phishing outillé. Réponse souveraine : PassCypher HSM PGP pour des clés SSH hors cloud, rotation auditable, et defense-in-depth par couches matérielles + réglementaires.
SSH VPS sécurisé avec PassCypher HSM — posture key-only sur le port 49152, auditabilité et résilience intégrée
Premier verrou : éteindre complètement l’authentification par mot de passe. Tant que le serveur accepte un mot de passe, même long, il reste vulnérable aux attaques par dictionnaire ou par fuite d’identifiants. Avec un key-only SSH, le mot de passe disparaît de l’équation et Le serveur ne reconnaît que des preuves cryptographiques (OpenSSH man page). Couplé au port 49152, on réduit la surface d’exposition.
1. Configuration sshd
Éditez le drop-in cloud-init pour désactiver toute tentative password :
/etc/ssh/sshd_config.d/50-cloud-init.conf
PasswordAuthentication no
Puis redémarrez le service :
sudo systemctl restart sshd
2. Blocage du port 22 — posture key-only pour SSH VPS sécurisé avec PassCypher HSM
Le port standard est la première cible des bots. Il faut non seulement changer de port, mais aussi bloquer explicitement le 22 :
sudo iptables -A INPUT -p tcp --dport 22 -j DROP
Cette règle empêche tout retour en arrière “par accident” : même si quelqu’un réactive PasswordAuthentication sur 22, le trafic sera bloqué en amont.
3. Test de verrouillage password
Une fois la bascule faite, testez vous-même pour être sûr :
ssh -o PreferredAuthentications=password -p 49152 debian@51.75.200.82
# Attendu : Permission denied (publickey)
Ce test forcé confirme que le serveur n’accepte plus de mot de passe, même si un bot tente en boucle.
⮞ Synthèse
Avec PasswordAuthentication no et blocage du port 22, le serveur sort du radar des dictionnaires. Couplé au port 49152 et aux clés générées dans PassCypher NFC HSM PGP, l’accès devient un bastion : aucune tentative password n’est possible, seule une clé matérielle valide peut ouvrir la session.
Clés SSH VPS sécurisé avec PassCypher HSM PGP
Une clé SSH n’est pas qu’un fichier dans ~/.ssh. Générée à l’arrache sur un laptop, elle peut fuiter, se retrouver copiée dans un backup cloud, ou dormir en clair sur un disque. Avec PassCypher NFC HSM PGP, la logique change radicalement : la clé privée naît dans un Hardware Security Module (HSM) hors ligne, chiffrée en AES-256 via PGP, et ne circule jamais en clair. Seule la partie publique quitte le HSM.
1. Génération RSA/ECC — clé SSH privée chiffrée PGP AES-256
Selon le besoin, on choisit :
RSA 2048 / 3072 / 4096pour la compatibilité maximale.ECC P-256 / P-384 / P-521oued25519pour des clés modernes, plus compactes et résistantes.
Dans les deux cas, la clé privée est immédiatement encapsulée en *.key.gpg, protégée par une passphrase souveraine définie par l’utilisateur, contrôlée en temps réel (entropie Shannon) et demandée via NFC.
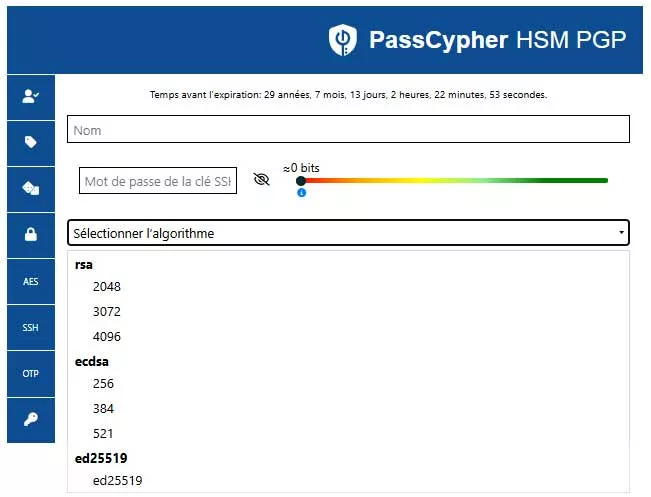
2. Exports multi-formats
PassCypher propose plusieurs modes d’export pour s’adapter aux environnements :
*.pub: clé publique OpenSSH classique (à injecter dansauthorized_keys).*.key.gpg: clé privée chiffrée PGP AES-256, usage quotidien.- QR Code : conteneur temporaire scannable pour injection rapide dans un autre HSM NFC.
- JSON segmenté : export chiffré multi-fragments, parfait pour stockage distribué ou coffre-fort air-gap.
Workflow QR Code — sauvegarde & restauration souveraines
Avec PassCypher HSM PGP, la paire SSH peut être encapsulée dans un QR Code chiffré (clé publique + clé privée chiffrée via passphrase). Le chiffrement repose sur PGP AES-256 (OpenPGP) ; la passphrase bénéficie d’un contrôle d’entropie temps réel (Shannon) lors de la saisie. Ce QR Code devient un artefact portable : sauvegarde en ligne ou hors-ligne (air-gap), restauration contrôlée et traçable — conforme à la doctrine SSH VPS sécurisé avec PassCypher HSM.
Étape 1 — Saisie souveraine
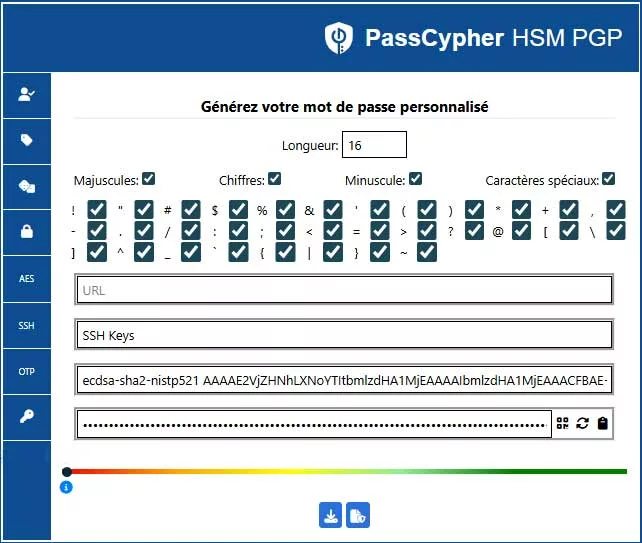
Étape 2 — QR Code codé
- Portabilité : le QR Code peut être imprimé, archivé offline ou stocké en coffre numérique.
- Audit : chaque artefact (QR, imports/exports) peut être journalisé dans votre
rotation.log.
Étape 3 — Restauration
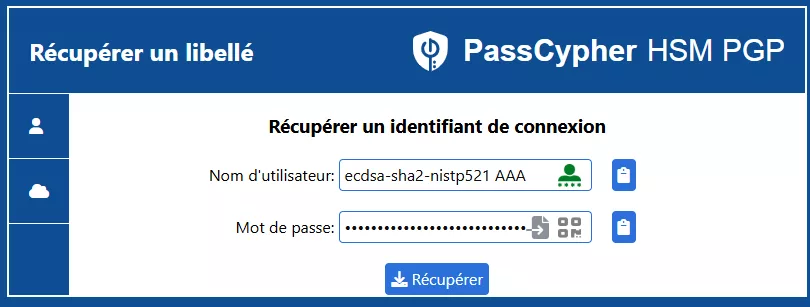
- Restauration : depuis PassCypher → Récupérer un libellé (scan/glisser-déposer), puis usage immédiat en NFC HSM ou via émulateur de clavier BLE HID pour saisir la passphrase partout (CLI comprise).
Étape 4 — Utilisation multi-mode : NFC, HID, QR
La clé privée chiffrée n’est utilisable qu’après déverrouillage matériel :
- NFC HSM : lecture physique par un terminal PassCypher.
- QR Code → NFC : transfert via caméra, utile pour mobilité ou restauration.
- Émulateur HID Bluetooth (BLE) : usage comme un “clavier matériel” injectant la passphrase et la clé localement, sur n’importe quel système acceptant un périphérique HID USB.
Étape 5 — Doctrine air-gap et portabilité d’un SSH VPS sécurisé multi-cloud
L’approche est simple : la clé reste chiffrée, portable et exploitable même sans réseau. Vous pouvez la stocker sur un support EviKey NFC verrouillé, l’exporter en JSON chiffré ou scanner un QR Code temporaire pour la restaurer. Dans tous les cas : jamais en clair, jamais dans le cloud.
ℹ️ Pour les initiés
AES-256-CFB (Cipher Feedback) pour le flux de données, avec une clé de session dérivée via S2K SHA-256/512, et un Modification Detection Code (MDC) pour détecter toute altération. C’est l’implémentation standard OpenPGP (RFC 4880).⮞ Synthèse
Avec PassCypher NFC HSM PGP, une clé SSH n’est plus un simple fichier sensible mais un artefact souverain : générée hors-ligne, chiffrée en AES-256-CFB avec passphrase souveraine, exportable en QR ou JSON segmenté, et utilisable en NFC ou HID BLE. Zéro mot de passe stocké, zéro cloud, zéro fuite.
Fail2ban : jail sshd
Changer de port et désactiver le mot de passe réduit déjà le bruit. Mais les bots continuent de scanner et d’essayer. Fail2ban agit ici comme un vigile automatique : il scrute les logs, détecte les échecs répétés et bannit l’IP à la volée. Un rempart simple, efficace et indispensable.
1. Installation & configuration
Installez le paquet :
sudo apt install fail2ban
Créez le fichier /etc/fail2ban/jail.local avec un bloc spécifique SSH :
[sshd]
enabled = true
port = 49152
filter = sshd
logpath = %(sshd_log)s
maxretry = 3
findtime = 5m
bantime = 30m
2. Nettoyage, activation & vérification
Avant d’activer, nettoyez les doublons éventuels dans [DEFAULT] et convertissez le fichier si nécessaire :
sudo dos2unix /etc/fail2ban/jail.local
Démarrez et vérifiez :
sudo systemctl restart fail2ban
sudo fail2ban-client status
3. Seuils d’alerte
Par défaut, maxretry est souvent trop permissif. Ici, après 3 échecs en 5 minutes, l’IP est bannie pendant 30 minutes. Sur un bastion sensible, vous pouvez allonger le bantime à plusieurs heures, voire opter pour un bannissement définitif.
⮞ Synthèse
Fail2ban surveille les journaux SSH, applique vos seuils personnalisés et bloque automatiquement les IP abusives. Avec une limite de 3 tentatives sur 5 minutes via le port 49152, les scans automatisés sont neutralisés dès l’amont. Résultat : moins de bruit, plus de clarté dans les logs, et un socle défensif robuste en complément de l’approche SSH VPS sécurisé avec PassCypher HSM. Chaque clé SSH générée est traçable, journalisée et auditable selon les standards de résilience et de souveraineté.
SSH VPS sécurisé multi-cloud avec PassCypher NFC HSM PGP (OVH, AWS, GCP, Proxmox)
- Type : RSA 4096 ou ECC P‑384 générée sur HSM NFC air‑gapped.
- Export :
FMT-VPS.pub(OpenSSH), privée chiffrée*.key.gpg(PGP AES‑256, mot de passe via NFC). - Déchiffrement local (usage) :
gpg --decrypt --output ~/.ssh/FMT-VPS ~/.ssh/vps-fmt-ad-08-2025/FMT-VPS.key.gpg chmod 600 ~/.ssh/FMT-VPS - Injection publique vers le VPS :
cat ~/.ssh/vps-fmt-ad-08-2025/FMT-VPS.pub | ssh -p 49152 debian@51.75.200.82 "mkdir -p ~/.ssh && chmod 700 ~/.ssh && cat >> ~/.ssh/authorized_keys && chmod 600 ~/.ssh/authorized_keys" - Commande OVHcloud : lors de la création, collez
FMT-VPS.pubdans le champ “clé SSH publique” pour un boot key-only immédiat.
⮞ Synthèse
Clés créées sur HSM, privée toujours chiffrée au repos, seule la publique transite vers le serveur ; provisioning OVH = sécurité dès le premier boot.
Pare-feu système (iptables)
Voici la logique, étape par étape : d’abord, on bloque absolument tout le trafic entrant. Ensuite, on ouvre uniquement l’essentiel, à savoir votre port SSH personnalisé (49152) et les connexions déjà établies. Ce modèle dit DROP-first (Netfilter.org) est une bonne pratique souveraine : il réduit drastiquement la surface d’attaque et transforme votre VPS en bastion SSH key-only.
1. Politique par défaut (DROP-first)
Bloquez tout en entrée, sauf ce que vous autorisez :
# Politique par défaut
sudo iptables -P INPUT DROP
sudo iptables -P FORWARD DROP
sudo iptables -P OUTPUT ACCEPT
2. Exceptions minimales (49152 + ESTABLISHED)
Ensuite, on ajoute les règles de survie :
# Loopback
sudo iptables -A INPUT -i lo -j ACCEPT
# SSH sur 49152
sudo iptables -A INPUT -p tcp --dport 49152 -j ACCEPT
# Connexions déjà établies
sudo iptables -A INPUT -m conntrack --ctstate ESTABLISHED,RELATED -j ACCEPT
Résultat : 49152 est la seule porte ouverte, et tout trafic inattendu est éjecté par défaut.
3. Persistance via netfilter-persistent
Sans persistance, vos règles disparaissent au redémarrage. Sauvegardez-les proprement :
sudo apt install iptables-persistent
sudo netfilter-persistent save
À chaque reboot, le système recharge automatiquement vos règles, garantissant la cohérence défensive.
⮞ Synthèse
Un VPS sans firewall est un honeypot involontaire. Avec une stratégie DROP-first + exception unique pour SSH sur 49152, vos surfaces d’attaque s’effondrent et renforcent l’usage d’un SSH VPS sécurisé avec PassCypher HSM. Couplé à Fail2ban et au pare-feu amont, iptables devient la seconde barrière de la doctrine defense-in-depth.
Pare-feu en amont (hébergeur)
Votre VPS ne vit pas dans un vide intersidéral : il est branché sur l’Internet global, balayé en permanence par des scanners et des bots. Laisser tout passer jusqu’au serveur revient à filtrer l’orage avec une passoire. D’où l’intérêt du pare-feu en amont, fourni par la plupart des hébergeurs (OVHcloud, AWS Security Groups, Proxmox avec firewall datacenter, etc.).
1. Configuration dashboard
Chez OVHcloud, vous pouvez activer un firewall réseau (OVHcloud docs) directement depuis l’espace client. C’est un filtre upstream qui bloque le trafic avant même d’atteindre l’IP publique du VPS. Cela réduit le bruit réseau et protège vos ressources système des flots de scans.
2. Filtrage TCP/49152
La règle de base :
- Autoriser uniquement
TCP/49152(votre port SSH customisé). - Optionnel : autoriser ICMP (ping) si vous avez besoin de monitoring.
- Bloquer tout le reste : aucune autre ouverture par défaut.
Avec cette politique, même si quelqu’un tente un scan massif, le trafic n’atteindra jamais votre VPS. C’est une première ligne de défense matérielle.
3. Cumul amont + iptables = defense-in-depth
Le firewall amont n’exclut pas iptables : il le complète. La logique souveraine est simple :
- Niveau 1 — hébergeur : filtre le trafic avant qu’il n’arrive à la VM.
- Niveau 2 — système : iptables ne laisse passer que 49152 et les connexions établies.
- Niveau 3 — applicatif : Fail2ban bannit les IP suspectes après analyse des logs.
C’est la définition même de la defense-in-depth : plusieurs murs successifs, indépendants, qui absorbent l’attaque avant qu’elle ne devienne critique.
⮞ Synthèse
Un pare-feu en amont (OVH ou autre) agit comme un bouclier extérieur : il bloque le bruit global du Net avant qu’il ne frappe votre VPS. Associé à iptables et Fail2ban, il fait passer votre architecture en mode bastion.
Journalisation & doctrine d’audit
Sécuriser un serveur est une étape, mais auditer en continu est ce qui garantit la résilience. En d’autres termes, la journalisation devient vos caméras de surveillance numériques : empreintes SSH, logs Fail2ban, diagnostics système… Chaque ligne enregistrée constitue un artefact souverain. Ainsi, vous pouvez prouver à tout moment la conformité de votre VPS face aux exigences réglementaires (NIS2, DORA) et aux doctrines de sécurité zero trust.
1. Empreinte serveur (ssh-keyscan)
Documentez l’empreinte publique de votre VPS dès le premier contact :
ssh-keyscan -p 49152 51.75.200.82 >> ~/.ssh/known_hosts.audit
Vous créez ainsi un registre des clés serveur. Si un jour l’empreinte change, vous savez que quelque chose cloche (attaque Man-in-the-Middle, rebuild inattendu…).
2. Logs SSH & Fail2ban
Exportez régulièrement les journaux :
sudo journalctl -u ssh > ~/ssh-access.log
sudo journalctl -u fail2ban > ~/fail2ban.log
Ces fichiers racontent qui s’est connecté, qui a échoué, et qui a été banni. C’est votre boîte noire d’incidents.
3. Diagnostic config sshd & jail.local
Un audit proactif vous évite des failles stupides :
# Vérifier qu’il n’y a pas de PasswordAuthentication yes qui traîne
sudo grep -Ri password /etc/ssh/sshd_config.d/
# Déboguer les jails actifs
sudo fail2ban-client -d
# Lire en continu les événements Fail2ban
sudo journalctl -u fail2ban -l --no-pager
Avec ça, vous détectez les directives contradictoires, les doublons de ports et les jails cassés.
4. Ledger des artefacts — auditabilité souveraine avec PassCypher HSM
La doctrine Freemindtronic recommande de consigner chaque événement dans un registre dédié :
known_hosts.audit→ empreintes serveurssh-access.log→ connexions SSHfail2ban.log→ bannissementsrotation.log→ historique des clés SSH
Ce n’est pas de la paperasse : c’est une preuve souveraine. Si demain on vous demande “qui avait accès et quand la clé a été changée”, vous ouvrez le ledger, pas un vieux souvenir.
⮞ Synthèse
Pas d’audit, pas de confiance. Avec des empreintes SSH, des logs exportés et un ledger des artefacts, chaque clé devient traçable, chaque bannissement vérifiable, chaque anomalie détectable. C’est la colonne vertébrale d’une doctrine zero trust.
Clé SSH privée chiffrée PGP AES-256 — sécurité souveraine
Une clé SSH, même générée dans un HSM souverain, n’est jamais définitive. À intervalles réguliers — ou dès qu’un doute surgit — elle doit être remplacée. C’est le principe de la rotation opérationnelle : générer une nouvelle paire, la tester, l’injecter, puis journaliser l’événement. Dans un SSH VPS sécurisé avec PassCypher HSM, cette rotation équivaut à changer les serrures cryptographiques de votre infrastructure.
⮞ Résultat
Aucune clé obsolète ne reste active, et l’ensemble du système reste aligné sur la doctrine defense-in-depth, avec traçabilité et résilience intégrées.
⮞ Étape suivante
Pour maintenir la posture cryptographique d’un SSH VPS sécurisé avec PassCypher HSM, chaque rotation doit s’accompagner d’une génération rigoureuse et d’un export souverain des nouvelles clés.
Clé SSH privée chiffrée PGP AES-256 — sécurité souveraine, zéro exposition avec PassCypher HSM
Dans un SSH VPS sécurisé avec PassCypher HSM, chaque clé privée est générée dans un HSM NFC, puis immédiatement chiffrée en PGP AES-256. Elle n’existe jamais en clair, sauf lors d’un déchiffrement temporaire en RAM pour usage local. Cette posture garantit une sécurité souveraine, hors cloud et hors disque.
1. Génération et export
Depuis votre HSM, générez une nouvelle paire :
# Clé publique OpenSSH + clé privée chiffrée
FMT-VPS-new.pub
FMT-VPS-new.key.gpg
1. Génération et export
Depuis votre HSM, générez une nouvelle paire :
# Clé publique OpenSSH + clé privée chiffrée
FMT-VPS-new.pub
FMT-VPS-new.key.gpg
La clé privée est immédiatement chiffrée en PGP AES-256. Elle n’existe jamais en clair, sauf si vous la déchiffrez temporairement en local pour l’usage.
2. Déchiffrement local temporaire
Pour utiliser la nouvelle clé, déchiffrez-la uniquement en RAM :
gpg --decrypt --output ~/.ssh/FMT-VPS-new ~/.ssh/vps-fmt-ad-08-2025/FMT-VPS-new.key.gpg
chmod 600 ~/.ssh/FMT-VPS-new
Le mot de passe est saisi via NFC, et la clé disparaît de votre disque si vous activez l’option auto-purge.
3. Remplacement atomique authorized_keys
Connectez-vous avec l’ancienne clé encore valide, puis écrasez le fichier :
echo "$(cat ~/.ssh/vps-fmt-ad-08-2025/FMT-VPS-new.pub)" > ~/.ssh/authorized_keys
chmod 600 ~/.ssh/authorized_keys
C’est un remplacement atomique : l’ancienne clé est éliminée en un coup, sans laisser de doublons.
4. Tests et journalisation
Validez immédiatement l’accès :
ssh -i ~/.ssh/FMT-VPS-new -p 49152 debian@51.75.200.82
Et consignez l’opération :
ssh-keyscan -p 49152 51.75.200.82 >> ~/.ssh/known_hosts.audit
echo "# Rotation SSH - $(date)" >> ~/.ssh/rotation.log
Le ledger (rotation.log) garde une trace : quelle clé, quel jour, quelle justification.
⮞ Synthèse
La rotation SSH souveraine évite la dérive opérationnelle : chaque nouvelle clé est générée dans le HSM, testée, injectée puis journalisée. Résultat : une traçabilité complète et une sécurité toujours alignée avec la doctrine zero trust.
La rotation n’est pas une option mais une routine souveraine. Génération sur HSM, usage local temporaire, remplacement atomique et journalisation : chaque cycle devient un artefact traçable, garantissant une infrastructure toujours à jour et hors d’atteinte des clés obsolètes.
Note EviKey NFC (verrouillage matériel)
EviKey NFC n’est pas un gestionnaire logiciel ni un simple coffre chiffré. C’est avant tout une clé USB matérielle souveraine, qui repose sur un verrouillage physique par NFC. Tant qu’elle reste verrouillée, le système d’exploitation ne la voit même pas : elle est littéralement invisible. Une fois déverrouillée via NFC, elle se comporte comme une clé USB classique, mais avec un auto-lock programmable (30 s, 2 min, etc.) qui réduit les risques d’oubli ou de compromission.
Concrètement, dans notre doctrine de sécurité, la clé privée SSH est déjà chiffrée par PassCypher HSM PGP (AES-256). Il n’y a donc aucun besoin de double chiffrement. EviKey vient en complément en apportant deux garanties décisives : un contrôle physique (pas de déverrouillage NFC = pas d’accès) et une résilience hors-ligne air-gap.
Résultat : EviKey devient l’outil idéal pour transporter une clé SSH souveraine chiffrée (fichier *.key.gpg, QR Code temporaire ou JSON segmenté), sans craindre une fuite en clair. Elle agit comme un pare-feu matériel portable, parfaitement intégré à la doctrine souveraine Freemindtronic.
Usage complémentaire
- Stockage matériel : clé privée déjà chiffrée (ex.
*.key.gpg) placée sur EviKey. - Verrouillage physique : invisible tant que non activée par NFC.
- Auto-lock : isolation automatique après usage.
- Couche optionnelle : pas un remplacement de PassCypher, mais un complément de portabilité et de résilience.
⮞ Synthèse
EviKey NFC ajoute une couche physique de verrouillage et d’auto-lock, idéale pour transporter vos artefacts chiffrés. Elle complète PassCypher : la clé reste protégée par AES-256, tandis qu’EviKey garantit l’invisibilité matérielle hors usage.
📖 Ressource associée
Pour un dossier complet sur l’usage d’EviKey NFC dans le stockage sécurisé des clés SSH (mode d’emploi, cas d’usage, doctrine souveraine), consultez : Secure SSH key storage with EviKey NFC HSM.
Annexe : commandes clés
Voici les commandes essentielles pour durcir un VPS Debian avec SSH key-only sur le port 49152, Fail2ban et iptables. Chaque ligne commentée (#) explique son rôle :
# 1. Bloquer le port 22 par défense en profondeur
sudo iptables -A INPUT -p tcp --dport 22 -j DROP
# 2. Tester une connexion forcée par mot de passe (doit échouer)
ssh -o PreferredAuthentications=password -p 49152 debian@51.75.200.82
# Résultat attendu : Permission denied (publickey)
# 3. Exporter les logs SSH pour audit
sudo journalctl -u ssh > ~/ssh-access.log
# 4. Exporter les logs Fail2ban
sudo journalctl -u fail2ban > ~/fail2ban.log
⮞ Synthèse
Ces commandes forment votre kit de survie : blocage de port 22, test forcé password et export de logs. Simples mais vitales, elles garantissent une vérification immédiate de votre posture souveraine et une traçabilité en cas d’incident.
Exemple pédagogique — Clé privée SSH (OpenSSH) —créé par PassCypher HSM PGP
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAACmFlczI1Ni1jdHIAAAAGYmNyeXB0AAAAGAAAABB188vMKS
[... tronqué pour lisibilité ...]
-----END OPENSSH PRIVATE KEY-----
Une clé privée OpenSSH moderne apparaît toujours sous cette forme encadrée.
Lorsqu’elle est chiffrée par une passphrase, le bloc base64 interne n’est lisible que si l’utilisateur fournit ce secret.
Une clé privée OpenSSH moderne apparaît toujours sous forme encadrée. Lorsqu’elle est protégée par une passphrase, le bloc base64 interne reste illisible sans ce secret. Dans un SSH VPS sécurisé avec PassCypher HSM, cette clé privée n’existe jamais en clair : elle est encapsulée et chiffrée en AES-256 via PGP, avec une passphrase stockée souverainement dans le HSM NFC.
⮞ Résultat : même si un fichier *.key fuitait, il resterait inutilisable sans le HSM et la passphrase.
Contre-mesures souveraines pour sécuriser les clés SSH VPS avec PassCypher HSM
Les gestionnaires de mots de passe logiciels (Bitwarden, 1Password, LastPass…) ne gèrent pas la création matérielle des clés SSH. Ils se contentent de stocker les clés privées dans des bases chiffrées, souvent exposées au navigateur ou au cloud. Cela élargit la surface d’attaque et introduit une dépendance logicielle. Les incidents LastPass l’ont démontré : un coffre compromis entraîne la chute de tout l’écosystème.
À l’inverse, PassCypher HSM PGP met en œuvre une garde souveraine. La clé privée SSH n’est pas un fichier vulnérable : elle est générée directement dans un HSM, chiffrée par PGP AES-256, et ne circule jamais en clair. Elle devient un artefact souverain, inviolable et portable.
Atouts souverains
- Multi-format portable : export en
*.key.gpg, QR Code, ou conteneur JSON segmenté. - Multi-mode usage : NFC HSM, import caméra QR, injection HID Bluetooth (émulation clavier).
- Doctrine air-gap : clé utilisable hors-ligne, déverrouillage physique NFC obligatoire.
- Zéro DOM / Zéro Cloud : aucun secret exposé dans le navigateur, aucune dépendance serveur.
- Résilience : sauvegarde possible sur EviKey NFC (verrouillage matériel auto-lock) ou transfert QR → NFC HSM.
Doctrine Zero Trust & Zero Knowledge — zéro mot de passe, zéro clé privée en clair
- Zero Trust : aucun acteur externe (hébergeur, cloud, hyperviseur) n’a accès à la clé privée.
- Zero Knowledge : la clé privée n’existe jamais en clair en dehors de l’enclave HSM.
Comparatif stratégique — pourquoi choisir PassCypher
Contrairement aux HSM cloud (AWS CloudHSM, Azure Key Vault) ou aux clés propriétaires (Yubikey, Nitrokey, SoloKeys), PassCypher NFC HSM PGP repose sur une architecture zero cloud, zero disque, zero DOM. Aucun logiciel tiers requis, aucun secret exposé au navigateur, aucune dépendance serveur.
Sa portabilité multi-format (QR, JSON, NFC), son usage multi-mode (NFC, HID BLE, caméra), et sa compatibilité air-gap en font une solution unique, souveraine et auditable — adaptée aux environnements critiques, auto-hébergés ou multi-cloud.
⮞ Rentabilité et scalabilité
Le HSM NFC PassCypher peut stocker jusqu’à 100 passphrases de sécurité d’accès aux clés privées SSH, injectables via un émulateur de clavier Bluetooth sécurisé (HID BLE en AES‑128 CBC). Ces passphrases permettent d’injecter des clés SSH, des mots de passe ou des secrets — sans jamais exposer la clé privée en clair.
Le nombre de paires de clés privées SSH générables par PassCypher HSM PGP est illimité, sans coût par clé, car cette fonctionnalité est intégrée nativement dans ses services de gestion de secrets et de mots de passe passwordless. Cette capacité rend PassCypher particulièrement rentable pour les infrastructures à haute rotation, les environnements multi-utilisateurs ou les architectures segmentées par rôle.
⮞ Résultat
Une solution souveraine, portable, scalable et indépendante, conçue pour les architectures exigeantes en sécurité, traçabilité et autonomie opérationnelle. PassCypher HSM PGP permet la génération illimitée de paires de clés SSH, l’injection sécurisée via HID BLE, et le stockage de 100 passphrases sans coût par clé — garantissant une rentabilité native et une compatibilité multi-cloud sans dépendance logicielle.
⮞ Synthèse
Contrairement aux gestionnaires logiciels, PassCypher HSM PGP génère et stocke vos clés SSH hors cloud, hors disque et hors DOM. La clé privée n’existe jamais en clair, même localement. Grâce à sa portabilité multi-format (QR, JSON, NFC), son usage multi-mode (NFC, HID BLE, caméra), et sa doctrine zero trust, PassCypher offre une indépendance souveraine, une traçabilité complète et une sécurité opérationnelle sans compromis.
What We Didn’t Cover
À noter — hors périmètre de cette note :
- Durcissement kernel (sysctl.conf, AppArmor, SELinux) — mesures complémentaires mais non traitées ici.
- IDS/IPS (Snort, Suricata) — détection en temps réel des intrusions, hors du scope minimal SSH + firewall.
- Reverse proxy / HAProxy — gestion des flux applicatifs (HTTP/HTTPS), volontairement exclu.
- Resilience snapshots & backups — OVHcloud offre des mécanismes de snapshot/backup non couverts ici.
L’objectif est de se concentrer exclusivement sur la chaîne SSH : génération souveraine des clés, hardening système et défense en profondeur.
FAQ — Questions fréquentes
Cette FAQ condense les questions récurrentes des admins système et SecOps sur forums, tickets et retours terrain.
Elle s’enrichit au fil des signaux faibles et des pratiques souveraines.
Pourquoi choisir le port 49152 ?
Cela ne remplace pas l’authentification par clé, mais réduit le bruit et les tentatives triviales.
Que se passe-t-il si je perds mon HSM ?
Dès la création, votre clé privée SSH est chiffrée en PGP AES‑256, protégée par un secret souverain que vous définissez.
Vous pouvez donc en conserver autant de copies chiffrées que nécessaire, sur différents supports, sans jamais exposer la clé brute.
La restauration est possible via un QR Code compatible NFC HSM ou un conteneur PGP AES‑256‑CBC incluant la clé.
Comment sauvegarder et restaurer ma clé SSH souveraine ?
⮞ En pratique, PassCypher HSM PGP permet de multiplier les sauvegardes chiffrées selon vos besoins :
- Passphrase de la clé privée SSH : QR → NFC HSM PassCypher.
- Archivage en ligne (clé SSH sécurisée et chiffrée) : SSH Sécurisé → Cloud, NAS, e‑mail, etc.
- Archivage hors ligne (clé SSH sécurisée et chiffrée) : SSH Sécurisé → USB, SD, SSD, HDD, CD.
- Supports sans contact : NFC NDEF Cardokey™ Pro, USB NFC EviKey® ou SSD NFC EviDisk®.
- Supports numériques : QR codes lisibles par tout lecteur, y compris via l’interface de récupération PassCypher HSM PGP.
Chaque étape doit être consignée dans un rotation.log pour garantir la traçabilité.
Résultat : l’accès reste bloqué by design pour un attaquant, mais demeure intégralement récupérable par vous.
PassCypher remplace-t-il complètement les gestionnaires logiciels ?
là où les gestionnaires logiciels restent exposés au navigateur.
Les deux peuvent coexister, mais la clé SSH sensible doit impérativement rester en HSM.
Les solutions SSH VPS sécurisées avec PassCypher HSM sont-elles compatibles avec tous les environnements VPS (OVH, AWS, GCP, Proxmox, bare-metal) ?
Le principe reste identique : générer la clé dans PassCypher HSM PGP → injecter la publique → forcer
PasswordAuthentication no.Pourquoi ne pas se contenter de FIDO/WebAuthn ?
De plus, la garde matérielle de PassCypher (PGP, clé segmentée, zéro DOM) évite toute exposition du navigateur.
Le QR Code ou le conteneur JSON segmenté est-il sûr ?
le JSON segmenté impose une reconstruction contrôlée.
Sans la phrase de déchiffrement (via NFC/PassCypher), le contenu est inutilisable.
Compatibilité OS (Windows/macOS/Linux) pour l’usage quotidien ?
L’injection via HID/QR/NFC est aussi possible selon le terminal.
Comment faire une rotation sans risque de lock-out ?
Gardez une session ouverte de secours. Journalisez chaque étape dans
rotation.log et known_hosts.audit.Faut-il utiliser ssh-agent avec PassCypher ?
Utiliser
ssh-agent peut améliorer le confort (pas besoin de retaper la phrase à chaque connexion),mais introduit aussi une surface mémoire.
Pour une posture souveraine, privilégiez l’usage direct ou un agent limité à la session courante.
À quoi sert StrictHostKeyChecking dans SSH ?
Avec known_hosts.audit, vous disposez d’un journal des empreintes serveurs.
Activer
StrictHostKeyChecking yes bloque les attaques de type man-in-the-middle,mais impose une discipline : valider chaque changement d’empreinte manuellement.
Les audits réglementaires (NIS2 / DORA) imposent-ils une rotation des clés SSH ?
Cela implique une rotation régulière des clés SSH, des journaux d’usage (
rotation.log) et la capacité de révoquer les clés à chaud.PassCypher HSM PGP facilite cette doctrine grâce à sa génération souveraine,
son cycle multi-support (QR, JSON, NFC) et son audit natif.
Que faire si mon VPS est touché par un ransomware ?
Un ransomware peut chiffrer le disque ou interrompre les sessions actives, mais il ne peut pas compromettre l’authentification par clé dans un SSH VPS sécurisé avec PassCypher HSM. Grâce au stockage hors ligne des clés privées — dans un HSM, un QR code chiffré ou un conteneur JSON segmenté — la résilience est immédiate. En cas de compromission, il suffit de réinjecter la clé publique depuis vos sauvegardes souveraines pour restaurer l’accès sur une nouvelle instance.
Les clés SSH sont exportables en multi-formats (NFC, QR, JSON), garantissant une portabilité native et une reprise rapide.
⮞ Doctrine : conservez au moins une sauvegarde hors-ligne (QR code imprimé ou JSON chiffré air-gapped). Cette mesure garantit une restauration opérationnelle même en cas d’attaque totale.
Comment gérer plusieurs administrateurs sans partager une seule clé privée ?
authorized_keys.Partager une clé privée est une mauvaise pratique.
Avec PassCypher HSM PGP, chaque admin génère sa propre clé souveraine dans son HSM.
Les publiques sont injectées sur le VPS, et les privées restent chiffrées (PGP AES-256).⮞ Doctrine : un compte VPS = plusieurs clés publiques autorisées. Chaque admin est lié à son artefact cryptographique, chaque rotation est journalisée dans
rotation.log.Les solutions SSH VPS sécurisées avec PassCypher HSM sont-elles compatibles multi-cloud (OVH, AWS, GCP, Proxmox, bare-metal) ?
Que vous déployiez un VPS chez OVH, une instance EC2 AWS, une VM GCP, un LXC Proxmox ou un serveur bare-metal,
la méthode reste identique.⮞ Doctrine : un seul cycle de génération PassCypher suffit pour tout environnement hybride. La clé privée ne circule jamais en clair, quel que soit l’hébergeur.
Puis-je utiliser PassCypher HSM PGP depuis un smartphone en mobilité ?
Sur Android NFC, vous pouvez stocker jusqu’à 100 clés SSH chiffrées dans le HSM.
L’accès nécessite un déverrouillage NFC.Usage multi-mode : QR Code (caméra), conteneur JSON segmenté, ou émulateur HID.
Ce dernier transforme le téléphone en clavier matériel sécurisé branché en USB sur n’importe quel ordinateur.⮞ Doctrine : portabilité + résilience hors-ligne : vos clés restent souveraines, transportables et utilisables partout, même en mobilité.
Puis-je déléguer l’accès temporaire à un consultant ?
Ensuite, injectez la clé publique sur le VPS, une seule fois.
Puis, au bout de sa validité, vous pouvez révoquer l’accès sans toucher aux clés maîtresses,
et journaliser l’événement dans
rotation.log.Est-ce que l’on peut configurer une clé série par environnement (prod, staging, dev) ?
Cela vous permet de segmenter les accès, limiter les blasts radius en cas de compromission,
et maintenir une traçabilité claire dans le ledger (
rotation.log).Comment éviter les collisions d’empreintes SSH entre plusieurs serveurs ?
ssh-keyscan pour collecter les empreintes de chaque serveur dans votre known_hosts.audit. Ensuite, activez StrictHostKeyChecking yes. Grâce à cela, dès que l’empreinte d’un serveur change (reinstall, MITM…), SSH vous alerte au lieu de se connecter, et vous gardez la maîtrise.Puis-je activer l’accès en lecture seule ou scp-only avec des clés SSH PassCypher ?
Executive Summary
This method of issuing a “NFC HSM SSL Cert IP” enhances sovereign cryptographic automation.This strategic chronique unveils a sovereign method to issue HTTPS certificates DNS-less, leveraging the patented PassCypher NFC HSM and DataShielder NFC HSM. These Freemindtronic devices, designed for air-gapped environments, embed full ACME commands within an encrypted Bluetooth USB keyboard emulator. As a result, the issuance of IP SSL certificates from Let’s Encrypt can be securely triggered on Linux or Windows terminals, without relying on domains or manual input. This implementation marks a significant advancement in cyber defense, DevSecOps automation, and critical infrastructure resilience.
Strategic Navigation Index
-
- Executive Summary
- Why Trigger HTTPS via NFC HSM?
- Sovereign Certificate Deployment
- ACME Command Injection
- Threat Modeling & Attack Surface Reduction
- Use Cases
- Advantages Over Conventional Certificate Deployment
- Market PKI Models vs. NFC HSM SSL Cert IP
- Strategic Differentiators
- Keyboard Emulation Security
- Web Interface Variant
- Create a Label in NFC HSM
- Step-by-Step Tutorial on Windows 11
- Linux Implementation Notes
- Screenshot: DNS-less ACME Trigger
- Beyond SSL: Generalized Command Triggering
- Visual Workflow
- FAQ
- Eliminating SPOF in Sovereign Certificate Issuance
- What We Didn’t Cover
About the Author – Jacques Gascuel, inventor of patented encryption devices and founder of Freemindtronic Andorra, specializes in sovereign cybersecurity. In this Tech Fixes & Security Solutions chronique, he demonstrates how trusted NFC HSMs and EviKeyboard BLE enable offline HTTPS provisioning via encrypted Bluetooth keyboard emulation.
Key Insights
Bluetooth Security & HID Injection Logic
Let’s Encrypt now actively provides free SSL/TLS certificates for public IP addresses, thereby eliminating any reliance on domain names. This evolution directly supports ACME automation and is valid for 6 days—making it ideal for sovereign DevOps workflows, air-gapped devices, and containerized staging setups.
Freemindtronic’s architecture reinforces this capability by introducing a critical layer of physical trust. Through the NFC HSM, each certificate issuance command becomes encrypted, deterministic, and physically validated before execution.
To secure this pathway, the integration of Bluetooth HID emulators based on InputStick, operating under AES-128 CBC, mitigates known vulnerabilities like CVE‑2023‑45866. These dongles neutralize spoofing and injection attempts that typically compromise HID interfaces.
While HID emulation minimizes exposure to keyloggers—particularly those relying on software vectors—it does not ensure universal protection. Since the command never appears on-screen or uses the clipboard, conventional surveillance tools often miss it. Still, firmware-based interception remains a realistic concern in sensitive contexts.
Another layer of protection stems from the consistent rhythm of injected keystrokes. This predictability inherently circumvents profiling methods like keystroke dynamics, which attackers use for behavioral fingerprinting.
Beyond SSL — Triggering Sovereign Automation
Most critically, this method extends well beyond HTTPS provisioning. The architecture permits any shell-level action to be securely triggered—whether toggling firewalls, initiating VPN connections, or unlocking OTP-based workflows.
Such command injection remains deterministic, reproducible, and physically scoped to authorized personnel. It aligns with zero-trust architectures and supports sovereign automation in environments where human error, remote compromise, or credential leakage must be structurally eliminated.
Why Trigger HTTPS via NFC HSM?
⮞ Summary</br />Triggering a NFC HSM SSL Cert IP from an NFC HSM enhances sovereignty, reduces exposure, and removes dependency on DNS infrastructure. It is especially relevant in constrained environments where trust, reproducibility, and minimal attack surface are paramount.
In conventional PKI workflows, HTTPS certificates are issued via domain-validated mechanisms. These involve online DNS challenges, public exposure of metadata, and centralized trust anchors. While suitable for general web hosting, such methods are problematic for air-gapped systems, sovereign networks, and critical infrastructures.
An NFC HSM—especially one like DataShielder or PassCypher—bypasses these limitations by embedding a pre-configured ACME command within a secure, tamper-resistant module. Upon physical NFC validation, it injects this command into a terminal using encrypted Bluetooth HID emulation, triggering immediate certificate issuance for a public IP address, DNS-less resolution or manual typing.
This process ensures:
- Full autonomy: No user interaction beyond NFC scan
- Domainless provisioning: Perfect for IP-only infrastructure
- Operational secrecy: No domain names to query or monitor
- Cryptographic trust: Execution only via validated hardware
Unlike browser-integrated certificate requests, this method is scriptable, repeatable, and isolated. It supports compliance with sovereign architecture principles, where infrastructure must operate without internet reliance, telemetry, or cloud-based identity.
– Eliminate DNS metadata exposure for sensitive endpoints
– Enforce HTTPS issuance via local NFC physical validation
– Minimize human input to reduce injection risks and keystroke profiling
Sovereign Certificate Deployment
Deploying HTTPS certificates through an NFC HSM enables a sovereign infrastructure free from DNS, browser, or cloud dependencies. This method ensures deterministic and auditable certificate generation, fully compliant with air-gapped or classified operational models.This guarantees reproducible NFC HSM SSL Cert IP issuance even in air-gapped infrastructure.
Traditional HTTPS deployment relies on central authorities, DNS records, and domain validation—all of which introduce third-party dependencies and potential metadata leaks. In contrast, Freemindtronic’s architecture leverages a hardware-controlled trigger (the NFC HSM) to initiate certificate issuance via a secure command injection mechanism. This reduces the trust surface to a physical, user-held device.
The key innovation lies in the out-of-band orchestration: The ACME client resides on the target host, while the initiation command is stored encrypted on the HSM. No intermediate server, cloud API, or domain registry is needed. The device injects the issuance command via Bluetooth HID over AES-128 CBC, ensuring both authenticity and confidentiality.
Such deployments are ideal for:
- Defense or classified networks under COMSEC restrictions
- Offline DevSecOps environments with no external exposure
- Critical systems requiring deterministic, reproducible PKI actions
The process supports issuance for public IP addresses using Let’s Encrypt’s new IP SSL policy (valid 6 days). Renewal can be re-triggered via the same HSM, ensuring cryptographic continuity under operator control.
– Host the ACME client in a hardened, offline container
– Store issuance commands in sealed HSM compartments
– Trigger issuance only upon physical presence (NFC + HID)
ACME Injection for NFC HSM SSL Cert IP
The NFC HSM securely injects a complete ACME command into the terminal, automating IP-based certificate issuance without keyboard input. This mechanism merges cryptographic determinism with physical-layer control.
The NFC HSM SSL Cert IP architecture ensures every issuance is deterministic and hardware-bound. At the heart of this architecture lies a simple yet powerful mechanism: the injection of an command into a terminal session using an emulated keyboard interface. The command itself is stored as a secure “password” inside the NFC HSM, encrypted with AES-128 CBC and transmitted via Bluetooth HID only upon NFC validation.acme.sh
Typical payload format:
~/.acme.sh/acme.sh --issue --standalone -d 198.51.100.12This command initiates the certificate issuance for a specific public IP, using the standalone HTTP challenge method. The NFC HSM handles the timing and structure of input, including the final “Enter” keystroke, ensuring that no user interaction is needed once the terminal is focused and ready.
Because the device behaves as a hardware keyboard, there is no software stack to compromise, and no plaintext command ever resides on disk or in clipboard memory. This prevents logging, injection, or interception from conventional malware or keyloggers.
The injected command can also include renewal or deployment flags, depending on operational needs:
~/.acme.sh/acme.sh --renew -d 198.51.100.12 --deploy-hook "systemctl reload nginx"This physical injection model aligns with sovereign DevSecOps practices: zero trust, physical validation, no telemetry.
– Avoid clipboard usage and on-screen input
– Limit exposure by using ephemeral ACME sessions
– Control terminal focus strictly to prevent accidental command leaks
ACME Command Injection
The NFC HSM securely injects a complete ACME command into the terminal, automating IP-based certificate issuance without keyboard input. This mechanism merges cryptographic determinism with physical-layer control.
At the heart of this architecture lies a simple yet powerful mechanism: the injection of an command into a terminal session using an emulated keyboard interface. The command itself is stored as a secure “password” inside the NFC HSM, encrypted with AES-128 CBC and transmitted via Bluetooth HID only upon NFC validation.acme.sh
Typical payload format:
~/.acme.sh/acme.sh --issue --standalone -d 198.51.100.12This command initiates the certificate issuance for a specific public IP, using the standalone HTTP challenge method. The NFC HSM handles the timing and structure of input, including the final “Enter” keystroke, ensuring that no user interaction is needed once the terminal is focused and ready.
Because the device behaves as a hardware keyboard, there is no software stack to compromise, and no plaintext command ever resides on disk or in clipboard memory. This prevents logging, injection, or interception from conventional malware or keyloggers.
The injected command can also include renewal or deployment flags, depending on operational needs:
~/.acme.sh/acme.sh --renew -d 198.51.100.12 --deploy-hook "systemctl reload nginx"This physical injection model aligns with sovereign DevSecOps practices: zero trust, physical validation, no telemetry.
– Avoid clipboard usage and on-screen input
– Limit exposure by using ephemeral ACME sessions
– Control terminal focus strictly to prevent accidental command leaks
Threat Modeling & Attack Surface Reduction
Injecting HTTPS issuance commands via NFC HSM significantly reduces exposure to credential theft, remote compromise, and biometric profiling. However, physical layer risks, firmware compromise, and misconfigured terminals remain key vectors.
In a typical PKI deployment, multiple layers expose the certificate lifecycle to threats: DNS hijacking, clipboard interception, keystroke logging, and man-in-the-browser attacks. By shifting the trigger mechanism to a sealed NFC HSM, most software vectors are eliminated.
Remaining risks include:
- Terminal pre-infection: If malware is already resident, it may capture the injected command output or intercept post-issuance files.
- HID spoofing attacks: Emulated keyboards can be impersonated unless verified through MAC binding or secure pairing protocols.
- Compromised firmware: If the InputStick or equivalent dongle is tampered with, it could alter the command or inject additional payloads.
Nonetheless, the attack surface is drastically narrowed by limiting interaction to a physical device performing a single-purpose task with no writable memory exposed to the host.
Further hardening strategies include:
- USB port control and filtering (e.g.,
usbguard) - Privilege isolation of ACME clients
- Separation between issuance terminal and production services
This model aligns with threat-aware infrastructure design, promoting predictability, reproducibility, and low-residue command execution.
– Bind InputStick to a single MAC address with secure pairing
– Use read-only terminals or ephemeral VMs for injection
– Monitor for unexpected keystroke patterns or USB device signatures
Use Cases
NFC-triggered HTTPS certificate deployment unlocks secure automation in domains where DNS is unavailable, interaction must be minimized, and reproducibility is critical. From DevSecOps to defense-grade SCADA, this architecture serves environments requiring absolute trust control.
The following scenarios illustrate how the NFC HSM method enables trusted and repeatable HTTPS certificate issuance workflows in constrained, regulated, or sensitive networks:
- Offline DevSecOps Pipelines
Teams managing infrastructure-as-code or staging environments without internet access can preconfigure NFC HSM SSL Cert IP workflows for staging environments to issue IP-based certificates, ensuring that test environments are reproducible and consistent without any external dependency. - SCADA / OT Infrastructure
Industrial systems often avoid DNS integration for security reasons. Using an NFC HSM allows localized HTTPS activation without exposing endpoints to domain-based resolution or remote management layers. - IoT / Embedded Systems
Devices in disconnected or partially isolated networks can still receive TLS credentials via NFC-triggered issuance, avoiding factory default certs or static keys, and ensuring field-level provisioning control. - Field Operations in Defense or Law Enforcement
Operators in sovereign or tactical contexts can generate valid HTTPS credentials on-site, without contacting centralized authorities, by physically carrying a validated HSM token with embedded commands. - Certificate Renewal for Local Services
NFC HSMs can be configured to perform periodic injections of commands, allowing HTTPS continuity in local-only networks or maintenance windows without login credentials.--renew
– Preload HSMs for field deployments without backend dependency
– Enforce HTTPS consistency in LANs without internal CA
– Avoid DNS logging and upstream certificate transparency exposure
Advantages Over Conventional Certificate Deployment
Triggering HTTPS certificates from an NFC HSM provides deterministic provisioning, DNS independence, and air-gapped compatibility—surpassing traditional PKI methods in sovereign, offline, or security-hardened contexts.
Unlike conventional HTTPS deployment—which relies on online DNS validation, interactive browser workflows, or centralized CA integrations—this method centers on physical validation and cryptographic command injection. The result is a sovereign architecture that avoids metadata leaks, limits dependencies, and enhances reproducibility.
Key comparative advantages:
- DNS-free issuance: Certificates can be requested directly for public IP addresses, eliminating exposure to DNS hijacking or telemetry.
- Zero manual typing: The NFC HSM delivers a pre-signed command via Bluetooth HID, reducing human error and eliminating clipboard use.
- Air-gapped operation: No need for internet connectivity during issuance—ideal for SCADA, OT, or classified zones.
- Cross-platform support: Works natively on Linux and Windows terminals with terminal focus, including GUI-less shells.
- Offline reproducibility: The same NFC HSM token can trigger identical issuance workflows across distinct devices or deployments.
– Avoid third-party telemetry via direct IP-based ACME workflows
– Use physical validation to remove keyboard input from trust equation
– Standardize issuance using sealed, immutable NFC HSM command blocks
Market PKI Models vs. NFC HSM SSL Cert IP
⮞ Summary
Commercial PKI models rely on centralized trust architectures, whereas Freemindtronic’s NFC HSM SSL Cert IP model decentralizes certificate control and aligns with offline sovereignty requirements.
Freemindtronic’s NFC HSM SSL Cert IP model contrasts with:
- AWS Certificate Manager (ACM) — automated domain validation and SSL provisioning for AWS workloads, but entirely cloud-tethered.
- Google CA Service — enterprise-focused PKI with global root distribution, but no local control over key injection.
- Entrust or GlobalSign PKIaaS — high-assurance certificate lifecycle services, but designed for regulated environments with consistent network access.
In contrast, the NFC HSM SSL Cert IP model is physically anchored, deterministic, and offline-capable, making it uniquely suited for air-gapped, sovereign, or classified environments where no telemetry or external PKI is permitted.
✓ Sovereign Countermeasures
- Replace centralized CA trust chains with localized issuance
- Avoid reliance on global DNS, root stores, and telemetry
- Use NFC-triggered hardware validation to control all issuance events
| Criteria | Conventional PKI (Cloud HSM) | NFC HSM SSL Cert IP (Freemindtronic) |
|---|---|---|
| Key Storage | HSMs in cloud datacenters (e.g., FIPS-certified Luna HSMs) | On-chip secure memory, per user device |
| Certificate Trigger | API-based orchestration from CA infrastructure | Physical NFC scan and Bluetooth HID injection |
| Metadata Exposure | Public domain names, DNS logs, CA telemetry | None — issues IP certs offline DNS-less |
| Operational Model | Centralized, requires internet connectivity | Decentralized, works in air-gapped contexts |
| Sovereign Control | Controlled by Certificate Authority | Fully under user and device holder control |
Strategic Differentiators — NFC HSM SSL Cert IP vs. Cloud HSM
Compared to conventional cloud-based HSM solutions, Freemindtronic’s NFC HSM SSL Cert IP model offers a fully offline, sovereign, and metadata-free method for issuing HTTPS certificates—making it unmatched in security, autonomy, and scalability.
| Criteria | NFC HSM SSL Cert IP (Freemindtronic) | Cloud HSM (AWS, Google, etc.) |
|---|---|---|
| Offline Capability | Fully functional in air-gapped environments | Impossible — internet connection mandatory |
| Sovereign Control | Full user-side control, no third-party reliance | CA or cloud provider retains authority |
| DNS Independence | Let’s Encrypt IP SSL triggered via NFC | Domain and DNS validation mandatory |
| Command Storage | Encrypted in EEPROM with AES-256 CBC | Cleartext in orchestration scripts or APIs |
| Bluetooth HID Security | AES-128 CBC (BLE), no software installation needed | Not applicable, not physically triggered |
| Telemetry Exposure | Zero telemetry, no cloud or DNS persistence | High — logs, DNS traces, CA activity trails |
| Scalability & Distribution | Up to 100 secure labels per NFC HSM | Requires scripts, APIs, and cloud orchestration |
The NFC HSM SSL Cert IP architecture is ideal for DevSecOps, critical infrastructure, IoT, and tactical IT deployments requiring deterministic control over certificate issuance—with no metadata footprint and no internet trust anchors.
All of these sovereign capabilities are natively included in both DataShielder NFC HSM and PassCypher NFC HSM. In addition to secure NFC-triggered SSL certificate issuance via Bluetooth HID, both devices embed advanced functionalities—offline password management, AES-256 CBC encrypted EEPROM, and air-gapped command injection—at no additional cost, unlike comparable single-feature commercial offerings.
Real-World Implementation Scenario
A sovereign DevSecOps team maintains an internal staging infrastructure composed of multiple servers, each accessible via public IP, but with no domain name assigned. To provision secure HTTPS endpoints, they adopt a physical key approach using a DataShielder NFC HSM. Each operator receives a token preconfigured with a validated ACME command such as:
~/.acme.sh/acme.sh --issue --standalone -d 203.0.113.10During server provisioning, the operator focuses a terminal session on the target system and activates the NFC HSM over Bluetooth. The secure command is injected in real time via HID emulation, initiating HTTPS certificate issuance locally, without relying on DNS or typing. The process results in:
- No secret stored on disk
- No manual interaction beyond physical validation
- No DNS contact or metadata exposure
Renewals follow the same offline procedure. Each NFC HSM can be reused cyclically, enforcing consistent operational workflows and reducing the attack surface associated with digital credentials or shared provisioning scripts.
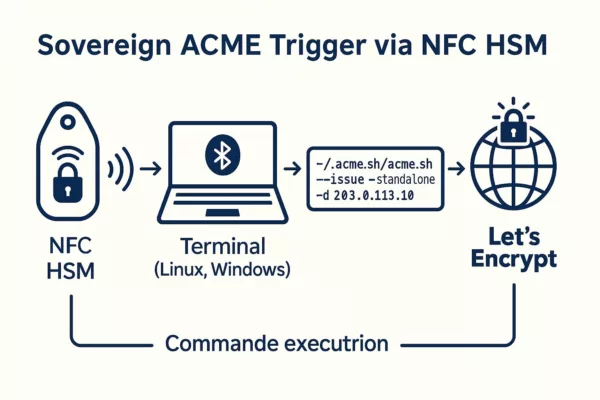
Keyboard Emulation Security
Secure NFC HSM SSL Cert IP provisioning relies on keyboard emulation via NFC-triggered HID injection, delivering encrypted commands without user interaction. While resilient against software-based keyloggers, this method still depends on dongle integrity, terminal focus, and strict physical access control.
The Freemindtronic architecture relies on Bluetooth HID keyboard emulation to input a pre-defined ACME command into a terminal. This approach avoids clipboard use, bypasses browser interfaces, and limits the attack surface to physical vectors. Communication is secured using AES-128 CBC encryption, typically via InputStick-compatible dongles.
Advantages:
- Bypasses traditional keystroke logging malware
- Works in both GUI and CLI-only contexts
- Evades behavioral profiling (e.g., typing speed, cadence)
- Injects full command strings deterministically
Limitations:
- Relies on terminal focus: any background app may intercept keystrokes if hijacked
- Cannot distinguish user intent—no dynamic validation layer
- Firmware-level compromise of the HID dongle remains a plausible threat
Despite these considerations, NFC-triggered HID input remains more secure than local typing or shell-based provisioning—especially in air-gapped networks. It minimizes cognitive load and human error while ensuring consistent syntax execution.
– Validate terminal window state before injection.
– Secure HID dongles using hardware-based pairing and trusted device filtering mechanisms.
– Physically isolate trusted input endpoints from internet-connected interfaces.
Web Interface Variant
In controlled environments requiring GUI validation, the NFC HSM can inject commands into a web interface with an autofocused field. This variant enables HTTPS provisioning through privileged backend scripts, maintaining traceability and physical-layer initiation.
While terminal-based workflows are ideal for sovereign and CLI-dominant deployments, some regulatory or enterprise environments require a graphical layer for auditability, accessibility, or operator ergonomics. To meet this need, Freemindtronic supports an alternative mode: NFC-triggered command injection into a local HTTPS web form.
This method involves a locally hosted, air-gapped web interface with an element. When the NFC HSM is scanned, its command is injected directly into this field via the Bluetooth HID emulator. The browser captures the string and relays it to a local backend daemon (e.g., Python Flask, Node.js) that executes the ACME command securely.<input autofocus>
Workflow highlights:
- No need for system-level terminal access
- Improves auditability and UX in regulated environments
- Allows integration with role-based web dashboards
This variant preserves the sovereign principle: no data leaves the machine, and execution still requires physical validation via NFC. It also opens the door to multistep approval flows, graphical logs, or on-screen HSM verification feedback.
– Host the web interface locally on loopback or hardened LAN
– Prevent remote form submission or cross-site injection
– Validate command syntax on server side before execution
Create a Secure NFC HSM Label
⮞ Summary
This step prepares your NFC HSM with a deterministic, DNS-less certificate command. You can either scan a secure QR code or manually input the command to harden the provisioning chain.

- Label: LEIP25 (6 characters max)
- Payload (55 characters max):
~/.acme.sh/acme.sh --issue --standalone -d 203.0.113.10 - Use PassCypher HSM to generate a QR code instantly (Evipass module).
- Optionally, insert the command manually for higher trust against keylogger vectors.
Step-by-Step Tutorial on Windows 11
⮞ Summary This guide shows how to trigger an NFC HSM SSL Cert IP securely from Windows 11 using a Bluetooth HID emulator and ACME, bypassing all DNS and clipboard dependencies.
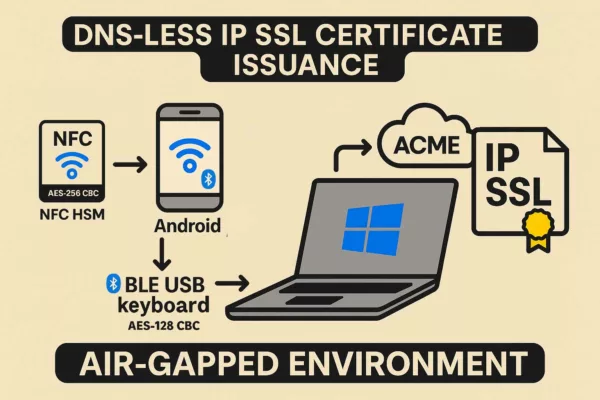
- Install Git for Windows: git-scm.com
- Install MSYS2: msys2.org Update with:
pacman -Syu - Install Socat: Check with:
pacman -S socatsocat -V - Install acme.sh: Verify with:
curl https://get.acme.sh | sh~/.acme.sh/acme.sh --help - Trigger NFC HSM: Activate Bluetooth HID, plug InputStick, scan the NFC HSM to inject the ACME command via keyboard emulation.
NFC HSM Trigger for HTTPS Certificate
This terminal output illustrates the sovereign automation of issuing an HTTPS certificate for a public IP using Freemindtronic’s NFC HSM and Bluetooth HID keyboard emulation. It confirms the ACME command injection without any DNS requirement.

~/.acme.sh/acme.sh --register-account -m your@email.comLinux Implementation Notes
Although not yet validated under Linux, this sovereign method for domainless HTTPS certificate issuance is inherently compatible with Unix-based systems. Thanks to standard CLI tools and terminal-centric workflows, its adaptation requires minimal adjustments.
The core architecture of this NFC-triggered SSL certificate method is platform-agnostic. It is built on command-line principles, which are foundational in Linux distributions. Tools such as and are widely available through most package managers, enabling seamless porting.socatacme.sh
Bluetooth HID support is also accessible under Linux, via and interfaces. Furthermore, USB HID emulation through InputStick or compatible AES-128-CBC Bluetooth dongles can be managed using rules or manually mounted as trusted devices in headless environments.bluezhidrawudev
Freemindtronic anticipates a CLI-only variant—entirely graphical-interface free—especially valuable in minimal server builds or embedded systems. This reinforces its utility in sovereign deployments and isolated networks.
⚠ Privileged access (root/sudo) will often be required for port binding (), USB device configuration, and real-time command injection via or ACME clients. This underscores the importance of trusted administrative control in production systems.443socat
Although no full test has been completed under native Linux environments as of this writing, technical compatibility is ensured by the universality of the tools involved. From a cyber-sovereignty standpoint, Linux remains a natural host for this methodology—offering deterministic, reproducible certificate issuance workflows DNS-less reliance.
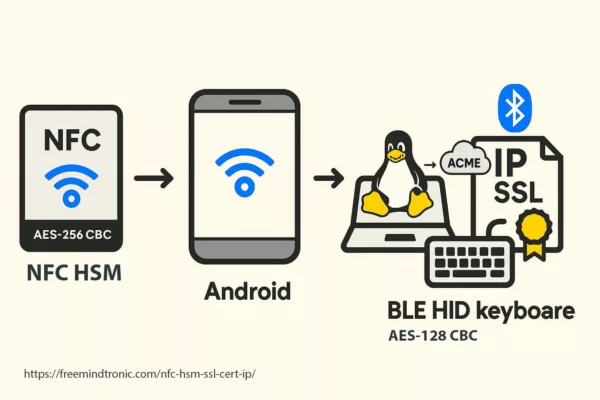
✓ Sovereign Countermeasures
– Bind certificate issuance to air-gapped Linux environments
– Use encrypted Bluetooth HID with physical validation
– Automate renewal via preloaded CLI command sets stored in the NFC HSM
Beyond SSL: Generalized Command Triggering
The NFC HSM method is not limited to HTTPS certificate issuance. Its architecture supports secure, offline triggering of any shell-level command—making it a versatile sovereign automation tool for sensitive or disconnected infrastructures.
While originally designed for issuing IP-based SSL certificates via , the NFC HSM trigger mechanism is fundamentally command-agnostic. Any shell instruction can be stored in the encrypted memory block and injected securely into a terminal or web input form, provided it respects length and syntax constraints.acme.sh
Generalized sovereign use cases:
- VPN toggles — trigger or commands in air-gapped environments
openvpnwg-quick - Firewall configuration — inject or rules for dynamic security postures
iptablesufw - System unlocks — initiate session-specific passwordless login scripts on hardened devices
- Credential rotation — execute PGP key rotation or 2FA OTP sync triggers without exposing tokens
- Audit commands — launch , , or integrity checkers during physical inspection
sha256sumjournalctl
This flexibility transforms the NFC HSM into a **sovereign hardware trigger for trusted automation**, particularly in high-assurance zones. Combined with contextual awareness (e.g. operator role, physical presence, device pairing), the method enables deterministic, reproducible and minimal-risk operations.
– Restrict accepted commands to a known safe set on receiving systems
– Use NFC validation only in controlled physical perimeters
– Pair each command with logging or cryptographic attestation to ensure accountability
Visual Workflow
This visual sequence illustrates the complete offline workflow of sovereign certificate issuance triggered by an NFC HSM device, from physical validation to HTTPS activation on a target system.
Understanding the interaction flow between hardware, host OS, and the ACME client is crucial to ensure deterministic outcomes and reproducible deployment in sovereign infrastructures.
The sequence includes:
- NFC validation of the operator’s credential (physical control)
- Bluetooth pairing and HID readiness handshake
- Command injection to the focused shell or input field
- ACME client execution with preconfigured flags
- Key + CSR generation by the ACME engine
- HTTP challenge response via localhost (port 80/443)
- Retrieval of IP SSL cert and optional post-processing
This architecture supports both CLI and GUI variants, and maintains air-gapped integrity by ensuring no secret or domain is ever transmitted or stored online.
⧉ What We Didn’t Cover While this Chronicle focused on triggering HTTPS certificate issuance via NFC HSM devices in IP-only environments, several adjacent topics remain open for deeper exploration:
- Zero-trust orchestration using chained HSM devices
- Integration with sovereign enclaves and TPM attestation models
- Secure destruction or rotation of command blocks after single use
- Long-term auditability in decentralized PKI contexts
- Legal implications of offline crypto orchestration under international law
These topics will be addressed in future sovereign chronicles.
FAQ
This section clarifies operational and technical concerns about triggering HTTPS certificate issuance DNS-less using sovereign NFC HSM devices such as PassCypher or DataShielder.
➤ Can you alter the ACME command stored inside the NFC HSM?
No, you cannot. Once the ACME command is encrypted and securely embedded in the NFC HSM’s sealed memory, it becomes immutable. Modifying it requires complete erasure and full reinitialization. Therefore, this approach ensures deterministic execution and robust tamper resistance.
➤ Does the AES-128 CBC Bluetooth HID channel resist replay attacks?
Yes, it does. Each communication session encrypts and synchronizes independently, using AES-128 CBC. The HSM transmits no data unless the NFC validation occurs again. Furthermore, the HID dongle enforces Bluetooth pairing, and each session expires automatically—greatly minimizing the window for replay exploitation.
➤ What happens if the terminal window lacks focus during injection?
In that case, the injected command could land in an unintended application or background process. To mitigate this, Freemindtronic strongly recommends sandboxed launchers or explicit terminal focus validation. These measures guarantee command redirection doesn’t compromise the system.
➤ Is Linux inherently more secure than Windows for sovereign NFC-triggered issuance?
In most sovereign cybersecurity architectures, yes. Linux offers greater auditability, native CLI environments, and fewer proprietary dependencies. That said, when properly hardened, both Linux and Windows provide comparable integrity for NFC HSM-based HTTPS provisioning.
➤ Can this method operate inside virtual machines, containers, or cloud platforms?
Absolutely. As long as the virtual environment presents a HID-compatible interface and supports direct terminal focus, the NFC HSM injection works seamlessly. This includes ephemeral VMs, containerized services, and CI/CD agents configured with sovereign command workflows.
Eliminating SPOF in Sovereign Certificate Issuance
| Centralized Component | SPOF Risk | Present? | How It’s Eliminated |
| DNS | Hijacking, downtime, telemetry leaks | ❌ | Direct issuance to IP (e.g. 203.0.113.10) with no domain validation |
| Cloud ACME servers | Outage, revocation, unilateral policy change | ❌ | Command issued offline from NFC HSM, no external authority |
| Keyboard input stack | Keyloggers, injection, human error | ❌ | Encrypted HID injection via Bluetooth emulator (AES-128-CBC) |
| Persistent cloud storage | Data exposure, lateral pivoting | ❌ | Payload stored encrypted in EEPROM (AES-256-CBC) |
| Auto-renewal daemons | Untraceable renewal failures | ❌ | Physically triggered per issuance by operator via NFC |
Every certificate issuance is traceable, deterministic, air-gapped, and governed by hardware. The use of up to 100 autonomous NFC HSM labels (AES-256-CBC) per device enables rotation per site, per operator, or per time slot — eliminating SPOFs and reinforcing cryptographic sovereignty.
What We Didn’t Cover
Executive Summary
Let’s Encrypt IP SSL now enables the issuance of SSL/TLS certificates directly for public IP addresses, without requiring a domain name or DNS configuration. This breakthrough unlocks secure HTTPS access for test labs, DevOps deployments, IoT devices, and local infrastructure. Valid for 6 days, these certificates support automated renewal via ACME clients like Certbot or acme.sh. Compared to self-signed alternatives, Let’s Encrypt IP SSL offers browser trust, automation, and a zero-cost advantage. This article explores practical use cases, technical constraints, WordPress integration, and alternatives for full HTTPS coverage on raw IP addresses.
Strategic Navigation Index
- Executive Summary
- Why Trigger HTTPS via NFC HSM?
- Sovereign Certificate Deployment
- ACME Command Injection
- Threat Modeling & Attack Surface Reduction
- Use Cases
- Keyboard Emulation Security
- Web Interface Variant
- Step-by-Step Windows 11 Tutorial
- Linux Implementation Notes
- Beyond SSL: Generalized Command Triggering
- Visual Workflow
- FAQ
- Image JSON-LD Metadata
About the Author – Jacques Gascuel is the inventor of several patented, hardware-based encryption and authentication technologies, and founder of Freemindtronic Andorra. A specialist in sovereign cybersecurity and offline cryptographic systems, he focuses on privacy-by-design solutions for environments with no internet or server dependency. In this article on Let’s Encrypt IP SSL, he explores the strategic potential of securing raw IP communications without DNS, offering insight into resilient digital architectures compatible with sensitive and constrained infrastructures.
Let’s Encrypt IP SSL: Secure an IP Address with HTTPS Without a Domain Name
Let’s Encrypt, the free and open-source certificate authority, now offers SSL/TLS certificates for IP addresses, without requiring a Fully Qualified Domain Name (FQDN). This innovation enables encrypted HTTPS communication on servers accessible via raw IP addresses, without relying on DNS. It’s ideal for DevOps pipelines, test labs, and local or self-hosted network appliances.
Let’s Encrypt IP SSL vs Domain-Based SSL
Let’s Encrypt primarily issues free SSL certificates for domain names, but it also supports securing public IP addresses directly through the ACME protocol. This article explores how Let’s Encrypt IP SSL differs from traditional domain-based certificates and when this approach makes sense.
Let’s Encrypt IP SSL vs Domain-Based Certificates
Let’s Encrypt is historically known for issuing domain-validated SSL/TLS certificates. However, it now also supports issuing certificates directly for public IP addresses. This removes the dependency on DNS and makes it possible to secure services by IP alone.
Unlike domain-based certificates, which require a Fully Qualified Domain Name (FQDN), IP SSL certificates use the SAN field to declare the IP address (IPv4 or IPv6). This change facilitates secure deployments in contexts like DevOps, IoT, or test environments without needing to register domains.
Official Let’s Encrypt Forum Post · ACME Protocol – RFC 8555
Why Use HTTPS on an IP Without a Domain?
- Test or Staging Environments: No need to register temporary domains—launch secure interfaces instantly.
- Cloud Instances & Containers: Secure dynamic or short-lived cloud workloads with HTTPS without DNS hassle.
- Internal or Local Networks: Access NAS devices, routers, DoH/DoT services, or IoT devices without browser warnings, even without a domain.
- Use in Security-Conscious or Air-Gapped Environments: Combine IP SSL certs with self-hosted ACME setups to create secure enclaves without domain exposure or internet reliance.
Key Use Cases
New use cases include securing DNS‑over‑HTTPS (DoH) endpoints, IoT/home‑lab devices, and ephemeral cloud workloads.
-
- NAS Admin Interfaces: Secure your NAS control panel accessed via public IP.
- Fast HTTPS for VMs or Bare Metal: Deploy secure servers on AWS, Azure, or OVHcloud with public IPs in seconds.
- CI/CD & DevOps Pipelines: Spin up HTTPS-enabled test servers with no DNS propagation.
- Self-Hosted DoH/DoT: Serve encrypted DNS traffic using a valid IP SSL cert.
- Internet-Facing Cameras: Protect IP-streamed video feeds without needing a domain.
- Industrial & SCADA Systems: Encrypt communication between web dashboards and IP-based industrial devices.
Let’s Encrypt IP SSL certificates can be autonomously issued via NFC HSM devices such as PassCypher NFC HSM and DataShielder NFC HSM. These devices integrate a secure Bluetooth USB keyboard emulator operating in AES 128 CBC mode, enabling fully offline and sovereign execution of commands.By embedding a complete ACME command (e.g.,
~/.acme.sh/acme.sh --issue --standalone -d 203.0.113.10) as a “password” (≤55 characters), the certificate issuance can be triggered securely on a Linux or Windows terminal without human typing. Combined with auto-enter, this setup ensures air-gapped, domainless HTTPS deployment for critical infrastructure, DevSecOps labs, or secure IoT environments.→ Full technical walkthrough: Trigger Let’s Encrypt IP SSL with NFC HSMSovereign Certificate Automation via NFC HSM
The diagram below demonstrates how a fully offline NFC HSM device can autonomously trigger HTTPS certificate issuance over raw IP — without DNS or manual typing. This approach, secured via AES-encrypted Bluetooth keyboard emulation, enables resilient deployments across air-gapped systems, DevSecOps pipelines, and critical infrastructure.
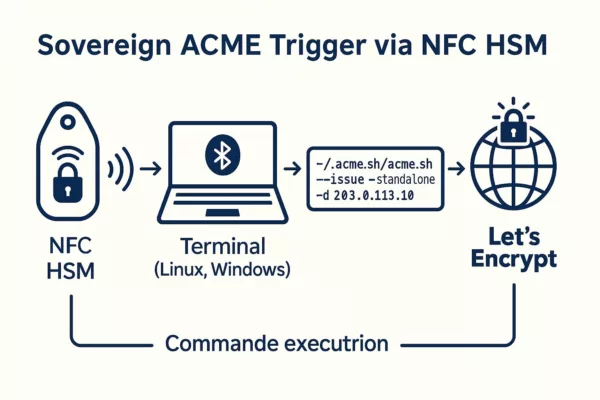
Other technical scenarios include:
- Landing page providers dynamically assigning IPs to tenants.
- DNS-over-HTTPS (DoH) endpoints using direct IP exposure.
- NAS and IoT devices offering direct web interfaces without FQDNs.
- Cloud back-end apps with ephemeral public IPs.
Source : Let’s Encrypt IP Announcement, July 2025
Validity and ACME Requirements
Let’s Encrypt IP certificates are valid for just 6 days. This short lifetime helps enhance security by quickly invalidating certificates in case of IP address changes or misconfigurations. Source: Let’s Encrypt Forum Post Certificate issuance requires the ACME protocol, defined in RFC 8555, using the http-01 or tls-alpn-01 challenges. DNS-based validation is not supported for IP certificates. Reference: Let’s Encrypt Challenge Types To automate certificate renewal, use compatible ACME clients such as:
⚠️ Rate Limit Notice: Let’s Encrypt enforces a rate limit of 50 certificates per IP address (or /64 IPv6 range) per 7-day window. You may also request up to 5 certificates per identical set of identifiers (IP + SAN/domain) per week. Let’s Encrypt currently restricts IP certificate access to allow-listed subscribers during the early access phase. Full production is scheduled to roll out by late 2025.
Source: Let’s Encrypt Rate Limits
Pros and Cons
| Criteria | Benefits | Drawbacks |
|---|---|---|
| No Domain Needed | Ideal for IP-only services | Not compatible with wildcard/domain combos |
| Valid Chain | Removes browser security alerts | Requires trusted CA, ACME setup |
| Full Automation | DevOps friendly | 6-day renewals are mandatory |
| Free of Charge | Cost-effective | No support for long-term issuance |
| In Staging Now | Available for tests | Not yet production-ready for all workflows |
DIY: Create Your Own SSL Certificate
For environments not requiring public trust, you can generate a free self-signed certificate with OpenSSL that works over an IP address.
Technical Note: Generating an IP-based certificate manually requires a Certificate Signing Request (CSR) or equivalent parameters, ensuring the IP address is declared in the SAN (Subject Alternative Name) field. Some modern browsers and systems will ignore the CN (Common Name) if the SAN is missing or incomplete.
openssl req -x509 -nodes -days 365 -newkey rsa:2048
-keyout server.key -out server.crt
-subj "/CN=203.0.113.10" -addext "subjectAltName=IP:203.0.113.10"⚠️ You’ll need to manually install this certificate in each client system or browser to avoid trust warnings.
OpenSSL directly builds this certificate inline, skipping the traditional CSR request step. Because it’s self-signed, a trusted certificate authority (CA) does not issue it. If you later decide to obtain a certificate from a CA, you’ll need to prepare a properly formatted CSR.
WordPress & IP SSL: Plugin Recommendation
In rare WordPress setups where the site is served over an IP:
- Generate an IP SSL certificate with
acme.sh - Modify
wp-config.phpto definesiteurlas the IP - Use the plugin Really Simple SSL to enforce HTTPS
⚠️ Some WordPress features may not function fully without a domain.
Comparison Table: Let’s Encrypt vs Other Free Alternatives
| Feature | Let’s Encrypt IP SSL | Self-Signed (OpenSSL) | mkcert |
| Trusted by Browsers | ✅ Yes | ❌ No | ⚠️ Dev only |
| Free of Cost | ✅ | ✅ | ✅ |
| Automation | ✅ (via ACME) | Manual | Limited |
| Certificate Lifetime | 6 days | Custom (e.g. 1 year) | Short/dev |
| Public IP Only | ✅ Required | ✅/❌ Any | Localhost |
Example: Benchmark with Shell Script
You can run a real benchmark Script using /usr/bin/time to compare performance between ACME and OpenSSL:
#!/bin/bash
echo "Benchmarking Let's Encrypt (acme.sh)..."
time acme.sh --issue --standalone -d 203.0.113.10 --server https://acme-staging-v02.api.letsencrypt.org/directory
echo "Benchmarking Certbot..."
time certbot certonly --standalone -d 203.0.113.10 --test-cert
echo "Benchmarking OpenSSL self-signed..."
time openssl req -x509 -nodes -days 365 -newkey rsa:2048
-keyout test.key -out test.crt
-subj "/CN=203.0.113.10" -addext "subjectAltName=IP:203.0.113.10"
Note:
- Replace
203.0.113.10with your actual public IP. - Root privileges and open ports 80/443 are required for ACME clients.
- Results can guide optimizations for secure, scalable deployments.
ACME vs OpenSSL — Performance Snapshot
ACME (Let’s Encrypt IP via acme.sh): ~6.4 seconds
ACME (Let’s Encrypt IP via Certbot): ~7.9 seconds
OpenSSL Self-Signed (RSA 2048): ~1.1 seconds
Tested on:
VPS OVHcloud – 2 vCPU – 4GB RAM
Ubuntu 22.04 LTS – Localhost Challenge
Tip: Self-signed is faster but not trusted by browsers. Use ACME for production and automation.
Live Benchmark Demo (Simulated)
Technical note: This benchmark runs as a simulated browser-side demo for educational purposes only. However, the displayed timing results reflect actual average measurements from real-world performance tests conducted under the following conditions:
- OVHcloud VPS — 2 vCPU, 4GB RAM
- Ubuntu 22.04 LTS with local ACME challenge
- ACME clients:
acme.shandcertbot - Execution timing measured via
/usr/bin/timeon shell scripts - OpenSSL version:
3.0.2
These metrics highlight practical performance differences between Let’s Encrypt ACME automation and self-signed OpenSSL certificates—especially relevant for DevOps pipelines and IP-only HTTPS deployments.
Click below to simulate certificate generation speed:
Waiting for input…
Cybersecurity Considerations for IP-Based SSL
Using Let’s Encrypt IP SSL certificates introduces new security and privacy considerations, especially when bypassing traditional DNS structures.
- Public Exposure via CT Logs: Every Let’s Encrypt certificate is publicly logged through Certificate Transparency. Even without a domain name, an exposed IP may leak infrastructure details.
- Passive Scanning: Tools like Shodan or Censys index IPs with SSL. Consider firewalls or geo-fencing to restrict access where applicable.
- No PTR Record ≠ Anonymity: An IP without a reverse DNS entry may still be fingerprinted through TLS metadata or service banners.
- Short Validity, Frequent Rotation: The 6-day lifetime improves security by reducing exposure, but make sure automated renewal is robust to avoid service interruption.
- Zero Trust Implications: In Zero Trust or segmented environments, use IP SSL certificates alongside mTLS or gateway-based access control.
- GDPR Compliance: IP addresses can be considered personal data under GDPR. Ensure lawful basis and appropriate controls are in place.
Best Practice: Combine IP SSL with firewall rules, strong client authentication, logging, and certificate monitoring tools to reduce the attack surface.
Technical Glossary
- ACME: Automatic Certificate Management Environment. A protocol (RFC 8555) used to automate the issuance and renewal of certificates.
- SAN: Subject Alternative Name. A field in SSL certificates allowing multiple identifiers (e.g. IPs or domains).
- FQDN: Fully Qualified Domain Name. A complete domain name including all subdomains and the root domain.
- TLS: Transport Layer Security. The protocol that provides HTTPS encryption.
- CSR: Certificate Signing Request. A block of encoded text used when applying for an SSL certificate.
- HTTP-01: ACME challenge using a file served over HTTP.
- TLS-ALPN-01: ACME challenge using a temporary TLS certificate.
- SSL: Secure Sockets Layer. A deprecated cryptographic protocol once used for securing HTTP (HTTPS). Modern HTTPS uses TLS instead of SSL, but the term “SSL” is still commonly used to refer to HTTPS certificates.
- Benchmark Script: A shell-based automation script used to compare the performance of multiple certificate issuance methods (e.g. ACME clients vs OpenSSL) by measuring execution time and resource usage.
What This Article Didn’t Cover (Yet)
We should explore these topics in greater depth, and plan to revisit them in a future update.
- Wildcard + IP Certs: Exploring mixed SANs (domain + IP) and use cases.
- IP Certificates on Shared Infrastructures: Managing certs across virtual hosts or reverse proxies.
- Commercial vs. Free IP Certificates: Durability, legal liability, SLAs, and compatibility audits.
- Integration with Appliances and Industrial Hardware: Are SASE, ZTNA, and IoT ecosystems fully compatible?
Timeline Highlights
- January 2025: Launch of short-lived certificate support (6–7 days).
- July 1st, 2025: Let’s Encrypt issues the first SSL certificate for a public IP address in staging.
- Q3–Q4 2025 (est.): Planned production rollout of IP certificate issuance.
– Trend: Domainless HTTPS adoption accelerating for containerized apps
– Pattern: ACME automation spreading to staging and test environments
– Vector: First real IP SSL use cases emerging in industrial edge networks
Strategic Wrap-up: A Game Changer for HTTPS Adoption
The ability to secure raw IPs without domains makes HTTPS easier to adopt in automation, IoT, and internal infrastructures. DevOps teams benefit from agile deployments, while local services gain privacy and security.
Want to go further?
- Build CI/CD pipelines with auto-renewing IP certs
- Deploy encrypted services in air-gapped environments
- Explore compatibility with reverse proxies and smart gateways
- Benchmark ACME certificate issuance times vs OpenSSL self-signing
- Consider legal implications of public IP exposure without DNS
Legal & Security Considerations
Deploying SSL on raw IP addresses may have implications depending on jurisdiction, network policies, or data protection regulations:
- GDPR Compliance: Ensure IP-based SSL usage complies with data protection laws. See CNIL (France) or GDPR.eu.
- Network Trust Models: Some corporate firewalls and proxies might distrust certificates not tied to domains.
- Audit & Logging: Ensure secure logging and identity verification where ACME automation is involved.
- Certificate Transparency: All Let’s Encrypt certificates are public. Don’t expose sensitive IPs without awareness.
- Best Practices: Refer to NIST Cybersecurity Framework and ENISA Guidelines for secure deployment.
- Reverse DNS leaks: Serving an IP SSL without PTR can still expose servers via Certificate Transparency logs.
- Passive scanning: Some tools index IPs with SSL enabled, which can be a privacy concern (e.g., Shodan, Censys).
- Phishing via IP URLs: Untrusted users may be misled by IP‑based links with trusted padlocks; monitor Certificate Transparency and educate users.
FAQ
Let’s Encrypt IP SSL & NFC HSM
Can I extend the 6-day certificate validity?
Let’s Encrypt enforces this policy, and users cannot modify it.
Can I issue a certificate via an NFC HSM device?
Yes. You can trigger the issuance of a Let’s Encrypt IP SSL certificate fully offline using a sovereign NFC HSM device such as <strong>PassCypher NFC HSM</strong> or <strong>DataShielder NFC HSM</strong>. These devices emulate a secure AES 128 CBC encrypted Bluetooth USB keyboard. By storing a complete ACME command (e.g. <code>~/.acme.sh/acme.sh –issue –standalone -d 203.0.113.10</code>) as a secure string (≤55 characters), the device injects it into the terminal of a Linux or Windows machine, triggering certificate generation without any manual typing or internet dependency.
→ <a href=”https://freemindtronic.com/nfc-hsm-ssl-cert-ip/” target=”_blank” rel=”noopener”>Learn more: NFC HSM triggered HTTPS certificate over IP</a>
Can I issue certificates for private IPs (192.168.x.x)?
No. Only public, globally routable IP addresses are eligible.
Is a self-signed certificate a valid alternative?
Yes, in closed or dev environments, but clients must trust it manually.
Can I use both a domain and an IP in a single cert?
Not yet supported. You must issue separate certificates.
Chrome 126+, Firefox 128+, Edge 124+, Safari 17.5+
Yes, as long as the browser trusts Let’s Encrypt’s root certificate. Modern browsers like Chrome, Firefox, Edge, and Safari are all compatible.
[accordion-item_inner title=”Can the NFC HSM trigger HTTPS certificate issuance from a web page?”]
[/accordion-item_inner]
Yes, it can. When combined with a properly designed local web interface, the NFC HSM — acting as a secure Bluetooth USB keyboard — can inject a complete ACME command directly into a focused input field. Although browsers cannot execute system commands on their own, this injected command can be immediately picked up by a local daemon or background script for execution.
This configuration enables sovereign HTTPS certificate issuance entirely offline, without DNS or manual typing. It proves especially useful for touchless deployments in isolated environments, where the web page acts as a bridge between the NFC-triggered command and the host system’s ACME client.
To ensure compatibility:
- Serve the interface over HTTPS (self-signed or IP SSL)
- Autofocus the input field targeted by the HSM
- Run a listener process that executes the received input securely
As a result, this setup empowers critical systems to deploy valid SSL certificates with minimal attack surface — and no internet dependency.
Can I extend the 6-day certificate validity?
Let’s Encrypt enforces this policy, and users cannot modify it.
Can I issue a certificate via an NFC HSM device?
Yes. You can trigger the issuance of a Let’s Encrypt IP SSL certificate fully offline using a sovereign NFC HSM device such as <strong>PassCypher NFC HSM</strong> or <strong>DataShielder NFC HSM</strong>. These devices emulate a secure AES 128 CBC encrypted Bluetooth USB keyboard. By storing a complete ACME command (e.g. <code>~/.acme.sh/acme.sh –issue –standalone -d 203.0.113.10</code>) as a secure string (≤55 characters), the device injects it into the terminal of a Linux or Windows machine, triggering certificate generation without any manual typing or internet dependency.
→ <a href=”https://freemindtronic.com/nfc-hsm-ssl-cert-ip/” target=”_blank” rel=”noopener”>Learn more: NFC HSM triggered HTTPS certificate over IP</a>
Can I issue certificates for private IPs (192.168.x.x)?
No. Only public, globally routable IP addresses are eligible.
Is a self-signed certificate a valid alternative?
Yes, in closed or dev environments, but clients must trust it manually.
Can I use both a domain and an IP in a single cert?
Not yet supported. You must issue separate certificates.
Chrome 126+, Firefox 128+, Edge 124+, Safari 17.5+
Yes, as long as the browser trusts Let’s Encrypt’s root certificate. Modern browsers like Chrome, Firefox, Edge, and Safari are all compatible.
[accordion-item_inner title=”Can the NFC HSM trigger HTTPS certificate issuance from a web page?”]
[/accordion-item_inner]
Yes, it can. When combined with a properly designed local web interface, the NFC HSM — acting as a secure Bluetooth USB keyboard — can inject a complete ACME command directly into a focused input field. Although browsers cannot execute system commands on their own, this injected command can be immediately picked up by a local daemon or background script for execution.
This configuration enables sovereign HTTPS certificate issuance entirely offline, without DNS or manual typing. It proves especially useful for touchless deployments in isolated environments, where the web page acts as a bridge between the NFC-triggered command and the host system’s ACME client.
To ensure compatibility:
- Serve the interface over HTTPS (self-signed or IP SSL)
- Autofocus the input field targeted by the HSM
- Run a listener process that executes the received input securely
As a result, this setup empowers critical systems to deploy valid SSL certificates with minimal attack surface — and no internet dependency.
Let’s Encrypt enforces this policy, and users cannot modify it.
Yes. You can trigger the issuance of a Let’s Encrypt IP SSL certificate fully offline using a sovereign NFC HSM device such as <strong>PassCypher NFC HSM</strong> or <strong>DataShielder NFC HSM</strong>. These devices emulate a secure AES 128 CBC encrypted Bluetooth USB keyboard. By storing a complete ACME command (e.g. <code>~/.acme.sh/acme.sh –issue –standalone -d 203.0.113.10</code>) as a secure string (≤55 characters), the device injects it into the terminal of a Linux or Windows machine, triggering certificate generation without any manual typing or internet dependency.
→ <a href=”https://freemindtronic.com/nfc-hsm-ssl-cert-ip/” target=”_blank” rel=”noopener”>Learn more: NFC HSM triggered HTTPS certificate over IP</a>
No. Only public, globally routable IP addresses are eligible.
Yes, in closed or dev environments, but clients must trust it manually.
Not yet supported. You must issue separate certificates.
Yes, as long as the browser trusts Let’s Encrypt’s root certificate. Modern browsers like Chrome, Firefox, Edge, and Safari are all compatible.
[accordion-item_inner title=”Can the NFC HSM trigger HTTPS certificate issuance from a web page?”]
[/accordion-item_inner]Yes, it can. When combined with a properly designed local web interface, the NFC HSM — acting as a secure Bluetooth USB keyboard — can inject a complete ACME command directly into a focused input field. Although browsers cannot execute system commands on their own, this injected command can be immediately picked up by a local daemon or background script for execution.
This configuration enables sovereign HTTPS certificate issuance entirely offline, without DNS or manual typing. It proves especially useful for touchless deployments in isolated environments, where the web page acts as a bridge between the NFC-triggered command and the host system’s ACME client.
To ensure compatibility:
- Serve the interface over HTTPS (self-signed or IP SSL)
- Autofocus the input field targeted by the HSM
- Run a listener process that executes the received input securely
As a result, this setup empowers critical systems to deploy valid SSL certificates with minimal attack surface — and no internet dependency.
Unicode-Based Alternatives to Emojis for Clearer Digital Content
Emoji and character equivalence ensures universal readability, SEO optimization, and accessibility across platforms. Unicode symbols provide a structured and consistent solution for professional, legal, and technical documentation, making them an effective replacement for emojis.
✔ Discover More Digital Security Insights
▼ Explore related articles on cybersecurity threats, advanced encryption solutions, and best practices for securing sensitive data and critical systems. Gain in-depth knowledge to enhance your digital security strategy and stay ahead of evolving risks.
Quick Navigation
‣ Unicode-Based Alternatives to Emojis for Clearer Digital Content
‣ Enhance Content Accessibility and SEO
‣ Why Replace Emojis with Unicode Characters?
‣ Advantages and Disadvantages
‣ Technical Deep Dive on Unicode Encoding
‣ Industry Applications: Legal, Academic, Cybersecurity Cybersecurity Use Cases of Emoji and Character Equivalence
‣ Practical Cybersecurity Use Cases: The Value of Emoji and Character Equivalence
‣ Unicode in SIEM Alerts and Security Logs: A Critical Integration Point
‣ Enhancing Content Security with Emoji and Character Equivalence
‣ Future Trends in Unicode Standardization
‣ Practical Guide: Unicode Implementation
‣ Psychological and Linguistic Impact
‣ Advanced Emoji Exploits: Steganography, Obfuscation, Counterintelligence Dual-Uses
‣ Secure Emoji Encryption Demo – Covert Messaging with AES-256
‣ Unicode vs. Emoji in Prompt Injection Attacks on AI Systems
‣ Unicode and Internationalization for Global SEO
‣ How to Apply Emoji and Character Equivalence Today
‣ Best Unicode Equivalents for Emojis
‣ Official Sources and References
Enhance Content Accessibility and SEO: The Complete Guide to Unicode Alternatives for Emojis
Emojis have become ubiquitous in our digital communication, adding a layer of emotion and personality to our texts. However, their inconsistent display across platforms and the challenges they pose in terms of accessibility and search engine optimization (SEO) underscore the necessity of exploring more reliable alternatives. This guide delves deeply into how Unicode characters offer a structured and universal solution for digital content that is clear, accessible, and optimized for SEO, including considerations for cybersecurity communication.
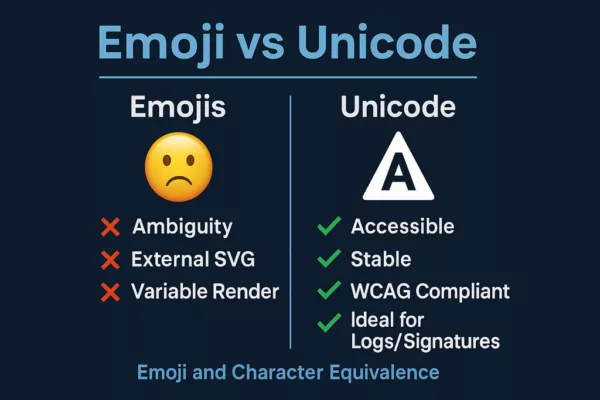
Infographic showing Emoji and Character Equivalence with a visual comparison of the limitations of emojis versus the cybersecurity benefits of Unicode characters. Visual breakdown of Emoji and Character Equivalence: Unicode is more secure, accessible, and reliable than emojis for cybersecurity contexts.
Why Opt for Unicode Characters Over Emojis?
The concept of emoji and character equivalence is essential for ensuring content consistency, optimizing SEO, and improving accessibility, as well as maintaining clarity in fields like cybersecurity. While emojis enhance engagement, their display varies depending on platforms, devices, and browsers, making Unicode characters a reliable and universal alternative for accessible content, better search ranking, and precise cybersecurity communication.
✔ Advantages
- Universal Compatibility – Unicode characters are recognized across all systems and browsers, ensuring consistent display, crucial for reliable cybersecurity information.
- Enhanced Accessibility – Assistive technologies interpret Unicode characters more efficiently than emojis, contributing to better compliance with web accessibility guidelines (WCAG), vital for inclusive cybersecurity resources.
- SEO Optimization – Special characters are indexed correctly by search engines, ensuring better visibility in search results, including searches related to cybersecurity symbols. Strategic use in titles and descriptions can also attract attention for improved SEO in the cybersecurity domain.
- Professional Consistency – Utilizing Unicode formatting is more suited to legal, academic, and business communications, including cybersecurity reports and documentation, where clarity and precision are paramount. The ambiguous nature of emojis can lead to misunderstandings, especially in sensitive fields like cybersecurity.
- Performance Considerations – Emojis can sometimes be rendered as images, especially on older systems, potentially increasing page load times compared to lightweight Unicode text characters, thus impacting site performance and potentially SEO, including for websites providing cybersecurity information.
✘ Disadvantages
- Reduced Visual Appeal – While emojis capture attention with their colorful graphic nature (for example, a simple 😊, their Unicode equivalent (U+263A, ☺) is a textual character. While the latter ensures compatibility, it can have a less immediate visual impact on user engagement, potentially affecting the perceived urgency of cybersecurity alerts.
- Limited Expressiveness – Unicode characters lack the emotional depth and visual cues of emojis, which might be relevant in less formal cybersecurity community discussions.
- Formatting Challenges – Inserting certain Unicode symbols, such as complex directional arrows (e.g., U+2913, ⤓) or specific mathematical symbols (e.g., U+222B, ∫), may require memorizing precise Unicode codes or using character maps, which can be less intuitive than selecting an emoji from a dedicated keyboard, potentially slowing down the creation of cybersecurity content.
Enhancing Content Security with Emoji and Character Equivalence
Recent research highlights critical cybersecurity risks associated with emoji usage. While emojis improve engagement, their hidden vulnerabilities can pose security threats. Understanding Emoji and Character Equivalence helps mitigate these risks while ensuring accessibility and SEO optimization.
✔ Emojis as Hidden Payloads Cybercriminals embed tracking codes or malware within emojis, particularly when encoded as SVG assets or combined with Zero Width Joiner (ZWJ) characters. This technique allows threat actors to deliver hidden payloads undetected, making Unicode characters a safer alternative.
✔ Misinterpretation Across Cultures and Legal Implications The visual representation of emojis varies by region, often leading to miscommunication or legal disputes. Unicode characters provide a standardized approach, avoiding ambiguity in contracts, digital agreements, and cross-cultural messaging.
✔ Accessibility Challenges for Screen Readers Screen readers may translate emojis inaccurately, generating verbose or misleading descriptions for visually impaired users. Relying on Unicode characters enhances clarity, ensuring consistent accessibility across assistive technologies.
✔ SEO Performance and Metadata Impact Emojis in SEO metadata may increase click-through rates, but their inconsistent rendering across platforms limits indexation reliability. Implementing Unicode characters ensures better search engine readability, reinforcing structured content strategies.
Official Sources on Emoji Vulnerabilities
- Smuggling Data Through Emojis – Paul Butler’s Research
- Cultural Misinterpretations of Emojis – Emoji Code Analysis
- Screen Reader Accessibility Issues – Scope Business
- SEO Risks of Emoji Use – ContentPowered SEO Report
By embracing Emoji and Character Equivalence, digital creators strengthen security, accessibility, and search visibility. Unicode characters offer a stable and universally recognized alternative, ensuring that content remains optimized and protected across platforms.
Technical Deep Dive on Unicode Encoding for Emojis and Symbols in Cybersecurity Contexts
✔ Understanding How Unicode Encodes Emojis and Special Characters for Cybersecurity Unicode assigns a unique code point to each emoji, enabling its display across various operating systems. However, rendering depends on the platform, leading to variations in appearance. For example, the red heart emoji (❤️) has the Unicode code U+2764 followed by the emoji presentation sequence U+FE0F. When used in text mode (without U+FE0F), it may appear as a simple black heart (♥, U+2665) depending on the font and system. Special characters like the checkmark (✔) have a unique code (U+2714) and are rendered consistently as text, aiding in content accessibility for cybersecurity professionals
✔ Emoji Presentation Sequences vs. Text Presentation Sequences in Unicode for Cybersecurity Communication Some Unicode characters exist both as text and emoji versions. Presentation sequences determine whether a character displays as a graphic emoji or as standard text. For example, the Unicode character for a square (□, U+25A1) can be displayed as a simple text square. By adding the emoji presentation sequence (U+FE0F), it may be rendered as a colored square on some platforms if an emoji style for that character exists. This distinction is crucial for both visual presentation and SEO considerations, especially for cybersecurity platforms.
It’s also important to note that some Unicode symbols are “combining characters.” These are designed to be overlaid onto other characters to create new glyphs. For instance, adding an accent to a letter involves using a combining accent character after the base letter, which might have niche applications in specific cybersecurity notations.
Industry-Specific Applications of Unicode Characters for Professional Content, Including Cybersecurity
✔ Using Unicode in Legal and Academic Documents Unicode characters are preferred over emojis in contracts, academic papers, and official reports, where consistency and professionalism are essential for clear communication. The ambiguous nature of emojis can lead to misinterpretations in legally binding documents, making standardized characters a safer choice, which also applies to the formal documentation within the cybersecurity industry.
✔ Leveraging Unicode in Cybersecurity and Technical Documentation Security experts and programmers use Unicode symbols in programming languages, encryption protocols, and cybersecurity reports for precision and clarity in technical content. For example, in code, Unicode symbols like logical operators (e.g., ∀ for “for all,” ∃ for “there exists”) or arrows (→, ←) are used for precise notation. In cybersecurity reports, specific alert symbols (⚠, ☢, ☣) can be used in a standardized way to convey specific threat levels or types, enhancing information accessibility for cybersecurity professionals..
✔ Corporate Branding with Unicode for Consistent Visual Identity, Including Cybersecurity Firms Many companies integrate Unicode characters into branding materials to ensure consistent representation across marketing assets. Some companies subtly incorporate Unicode characters into their text-based logos or communication to create a unique and consistent visual identity across platforms where typography is limited, contributing to brand recognition in search results, including for cybersecurity companies. For example, a tech brand might use a stylized arrow character or a mathematical symbol to evoke innovation and security.
Practical Cybersecurity Use Cases: The Value of Emoji and Character Equivalence
For cybersecurity professionals, adopting Emoji and Character Equivalence goes far beyond visual consistency — it strengthens secure communication, ensures compatibility across platforms, and reduces attack surfaces. Below are key scenarios where this principle makes a strategic difference.
✔ Use Case 1: Security Alert Bulletins
A CISO distributes a critical vulnerability bulletin using the emoji ⚠️. On some outdated terminals or filtered environments, the emoji fails to render or displays incorrectly.
✅ Unicode Advantage: Using U+26A0 (⚠) ensures universal readability, including by screen readers and legacy systems, supporting clear and actionable cybersecurity communication.
✔ Use Case 2: Secure Internal Messaging
In secure mail systems, emojis may be blocked or replaced to prevent the loading of external SVG assets, which can introduce vulnerabilities.
✅ Unicode Advantage: With Emoji and Character Equivalence, using Unicode characters instead of emojis eliminates these external dependencies while preserving the intended meaning and visual cue.
✔ Use Case 3: Signed System Logs and Forensics
Emojis rendered as images or platform-dependent glyphs can cause inconsistencies in cryptographic hash comparisons during log audits or forensic analysis.
✅ Unicode Advantage: Unicode characters have a stable code point (e.g., U+2714 for ✔), ensuring that logs remain verifiable across environments, crucial for integrity and non-repudiation in cybersecurity workflows.
These examples demonstrate how implementing Emoji and Character Equivalence is not only a matter of formatting — it’s a tactical choice to improve clarity, compliance, and reliability in cybersecurity communication.
Unicode in SIEM Alerts and Security Logs: A Critical Integration Point
Security Information and Event Management (SIEM) systems rely on structured, machine-readable alerts. Emojis—often rendered as platform-dependent graphics or multibyte sequences—can disrupt formatting, corrupt parsing logic, and complicate forensic investigations.
✅ Unicode characters such as U+26A0 (Warning: ⚠), U+2714 (Check mark: ✔), and U+2717 (Cross mark: ✗) provide:
- Stable rendering across terminals, dashboards, and log collectors.
- Consistent cryptographic hashing in signed event logs.
- Reliable pattern matching in SIEM rules and regular expressions.
- Screen reader compatibility for accessible security dashboards.
Example:
Instead of inserting a graphical emoji into a high-severity alert, use U+2717 (✗) for guaranteed interpretability across systems and tools.
This Unicode-based strategy ensures compatibility with:
- Automated threat detection pipelines
- Regulatory compliance tools
- SIEM log normalization engines
- Long-term forensic retention archives
Unicode brings predictability, clarity, and durability to cybersecurity event management—core to any zero-trust and audit-ready architecture.
Case Study: Emoji-Based Vulnerabilities and Cybersecurity Incidents
While emojis may appear innocuous, documented cyberattacks have demonstrated that they can be exploited due to their complex rendering behavior, reliance on external assets (like SVG), and ambiguous encoding. These cases reinforce the importance of adopting Emoji and Character Equivalence practices, especially in cybersecurity contexts where clarity, stability, and accessibility are critical.
⚠ Unicode Rendering Crash (Unicode “Bombs”)
➔ In 2018, a sequence of Unicode characters — including a Telugu glyph and modifiers — caused iPhones to crash and apps like iMessage to freeze. This vulnerability stemmed from how Apple’s rendering engine mishandled complex Unicode sequences.
✔ Sources officielles :
• MacRumors – iOS Unicode Crash Bug: https://www.macrumors.com/2018/02/15/ios-11-unicode-crash-bug-indian-character/
• BBC News – iPhone crash bug caused by Indian character: https://www.bbc.com/news/technology-43070755
⚠ Malicious SVG Rendering in Messaging Platforms
➔ Some messaging platforms like Discord rendered emojis through external SVG files, introducing a surface for remote code injection or tracking. Attackers exploited this to embed malicious content through emoji payloads.
✔ Source officielle :
• Dark Reading – Emojis Control Malware in Discord Spy Campaign: https://www.darkreading.com/remote-workforce/emojis-control-malware-discord-spy-campaign
⚠ Unicode Spoofing and Invisible Character Obfuscation
➔ Emojis combined with zero-width characters such as U+200B (Zero Width Space) or U+200D (Zero Width Joiner) have been used in phishing URLs and obfuscated code. These tactics enable homograph attacks that mislead readers or bypass detection.
✔ Documentation technique :
• Unicode Consortium – UTS #39: Unicode Security Mechanisms: https://unicode.org/reports/tr39/
✔ Strategic Takeaway
✘ Emojis rely on platform-dependent rendering and can introduce inconsistency or vulnerabilities.
✔ Unicode characters use immutable code points and render reliably across systems — making them ideal for cybersecurity logs, alerts, and accessible content.
The adoption of Emoji and Character Equivalence ensures professional-grade security, readability, and integrity.
⚠ Emoji Shellcoding and Obfuscated Command Execution
Recent threat research and demonstrations (e.g., DEFCON30, August 2022) have shown how non-ASCII characters, including Unicode symbols, can be used to obfuscate shell commands, bypassing traditional keyword-based detections. Attackers leverage Unicode manipulation to evade security filters, making detection more challenging.
🔗 Further Reading: Command-Line Obfuscation Techniques
⚠ Real-World Example
reg export HKLMSAM save.reg
When disguised using invisible Unicode characters (such as U+200D, U+200B), this command may appear harmless but still executes a privileged registry dump, bypassing conventional security checks.
🛠 Recommended Security Measures
✔ Regex-Based Detection – Go beyond keyword matching to identify command patterns, even if partially encoded or visually disguised.
✔ Alerting on Anomalous Characters – Security systems (SIEM, EDR, XDR) should flag commands containing:
- Unicode Special Characters (U+2714, U+20AC, etc.)
- Non-Printable Characters (U+200D, U+200B)
- Zero Width Joiners or Spaces (U+200D, U+200B)
✅ Unicode Benefit
By restricting input/output to ASCII or validated Unicode, organizations can: ✔ Minimize obfuscation risks ✔ Strengthen parsing and logging integrity ✔ Improve detection accuracy across terminal, script, and web layers
By implementing advanced detection techniques, organizations can mitigate risks associated with Unicode-based obfuscation and strengthen cybersecurity defenses.
Future Trends in Unicode and Emoji Standardization
✔ Updates from the Unicode Consortium on Emoji and Character Sets for Technical Fields Like Cybersecurity The Unicode Consortium regularly evaluates emoji proposals and updates the Unicode standard. Decisions are based on cultural relevance, accessibility needs, and demand from users, including potential requests for standardized symbols relevant to cybersecurity. Staying informed about Unicode updates is key for future content optimization, especially for technical documentation and cybersecurity communication.
✔ Challenges in the Standardization of Emojis and Unicode for Precise Technical Communication The standardization process faces obstacles due to regional interpretations of emojis, varying display standards, and accessibility concerns for visually impaired users. The interpretation of emojis can vary significantly depending on context and cultural differences. Artificial intelligence may play an increasing role in understanding the meaning of emojis in different contexts, but standardization for universal interpretation remains a complex challenge, highlighting the ongoing importance of clear Unicode alternatives, particularly in technical fields like cybersecurity where precision is critical.
Practical Implementation Guide: Replacing Emojis with Unicode for Better SEO, Accessibility, and Cybersecurity Communication
✔ How to Implement Unicode in Web Content for SEO, Accessibility, and Cybersecurity Clarity
- WordPress: Use Unicode characters directly in text fields for SEO-friendly content, including cybersecurity blogs and articles.
- HTML: Insert Unicode using &#code; notation (e.g., ✔ for ✔, ⚠ for ⚠) to ensure accessible HTML, especially for cybersecurity warnings and alerts.
- Markdown: Use plain text Unicode values for seamless integration in SEO-optimized Markdown, including cybersecurity documentation.
- CSS: Apply Unicode as
contentproperties in stylesheets for consistent rendering and potential SEO benefits, including unique styling of cybersecurity-related symbols. - Other CMS: For platforms like Drupal or Joomla, Unicode character insertion is usually done via the WYSIWYG text editor (using the special character insertion feature) or directly in the HTML code for accessible content management, including cybersecurity resources.
- Mobile Applications: Mobile app development for iOS and Android allows direct integration of Unicode characters into text strings, ensuring accessibility on mobile, including cybersecurity applications and notifications. Mobile operating system keyboards also often provide access to special characters via contextual menus or dedicated symbol keyboards.
✔ Keyboard Shortcuts for Typing Unicode Symbols Easily, Including Cybersecurity Symbols
- Windows: Use Alt + Unicode code (e.g., Alt + 2714 for ✔, Alt + 26A0 for ⚠) for quick Unicode input, including symbols used in cybersecurity.
- Mac: Press Cmd + Control + Spacebar to access Unicode symbols conveniently, useful for inserting cybersecurity-related characters.
- Linux: Type Ctrl + Shift + U + Unicode code for Unicode character entry, including specific cybersecurity symbols.
Psychological and Linguistic Impact of Emoji vs. Unicode Characters on Communication
✔ Analyzing How Emojis Affect Digital Communication, Including the Ambiguity in Cybersecurity Contexts Emojis are widely used to express emotions, tone, and intent, but their interpretation differs culturally, leading to ambiguity in professional exchanges, which can be particularly problematic in cybersecurity alerts or warnings where clear and unambiguous communication is vital. A simple thumbs-up (👍) could be misinterpreted in a critical cybersecurity discussion.
✔ The Role of Unicode Characters in Enhancing Readability and Clarity, Especially in Technical and Cybersecurity Content Symbols such as ✔, ✉, ⚡, ⚠, 🔒 provide structured communication that is easier to process and interpret objectively in technical content, improving content accessibility, especially in the cybersecurity domain. The use of standardized Unicode symbols in technical or legal documents (like checkmarks to validate points, arrows to indicate steps, or precise currency symbols) reinforces the perception of rigor, clarity, and professionalism of the content, which is paramount in cybersecurity reports and documentation, and can indirectly benefit user trust and SEO for cybersecurity resources.
Unicode vs. Emoji in Prompt Injection Attacks on AI Systems
Recent studies have revealed that emojis—beyond visual ambiguity—can act as covert payloads in AI prompt injection attacks. While most text is tokenized into multiple units by large language models (LLMs), emojis are often treated as single-token sequences. This allows attackers to hide complex instructions inside what appears to be a harmless character.
⚠ Real-World Finding:
Some emojis can expand into over 20 hidden tokens, bypassing security filters designed to detect explicit instructions.
This stealth mechanism stems from:
- LLMs treating emojis as atomic units,
- Emojis encoding metadata or invisible sequences (e.g., Zero Width Joiners),
- Models inherently trying to interpret non-standard patterns to “solve” them.
🔐 Security Implication:
These injection techniques exploit the architecture of transformer-based models, where unexpected inputs are treated as puzzles to decode. This behavior turns visual glyphs into logic bombs capable of triggering unintended actions.
✅ Unicode Advantage in AI Contexts:
Unicode characters:
- Have transparent tokenization (predictable encoding),
- Avoid compound emoji sequences and visual ambiguity,
- Don’t carry extra layers of metadata or emoji-style modifiers (e.g.,
U+FE0F).
Using Unicode-only inputs in AI workflows enhances:
- Prompt sanitization,
- Filter robustness,
- Audit trail clarity.
Example:
Using U+2714 (✔) instead of ✅ ensures that the LLM interprets it as a basic semantic unit, not a potential instruction carrier.
By preferring Unicode over emojis in LLM prompts and logs, developers reduce the surface for prompt injection and enhance traceability in AI-assisted workflows. This is particularly vital in secure automation pipelines, compliance monitoring, and zero-trust content generation environments.
⚠ Emojis in Cybercrime and OSINT: A Silent Language of the Dark Web
While emojis are often seen as harmless digital expressions, they are increasingly exploited by cybercriminals as a covert communication method on the dark web. Their ambiguity, cross-platform rendering inconsistencies, and social familiarity make them ideal for masking illicit content.
✔ Use in Illicit Marketplaces: Emojis are used to denote illegal goods and services in Telegram groups, forums, and marketplaces. For example, 💉 might refer to drugs, while 🔫 can imply weapons.
✔ Bypassing Detection: Because most cybersecurity tools and SIEMs focus on keyword detection, emoji-based language can evade filters. Attackers use them as part of “visual slang” that security systems don’t flag.
✔ The Rise of Emoji Forensics: Cyber investigators and OSINT professionals are mapping known emoji patterns used by criminal groups. Some tools are being trained to detect, interpret, and alert on specific emoji combinations.
✔ Generational Risk: Younger users (Gen Z), who communicate heavily via emojis, are at greater risk of exposure or manipulation in these covert communication schemes.
✔ Unicode Advantage: Unicode characters provide clear, unambiguous alternatives to emojis for secure communications. They allow enforcement and detection systems to parse logs, messages, and forensic data with higher accuracy.
🔗 Unlocking Digital Clues: Using Emojis in OSINT Investigations – Da Vinci Forensics This article explores how emojis serve as digital fingerprints in OSINT investigations, helping analysts track illicit activities, identify behavioral patterns, and uncover hidden communications.
This growing misuse of emojis signals a need for more refined detection systems and public awareness around their evolving role in digital crime.
Advanced Emoji Exploits: Steganography, Obfuscation, and Counterintelligence Uses
Beyond spoofing and prompt injection, emojis are being employed in advanced cyber tactics such as steganographic payloads, command injection evasion, and even counterespionage decoys.
✔ EmojiCrypt – Obfuscating Prompts for Privacy: Researchers have introduced “EmojiCrypt,” a technique that encodes user prompts in emojis to preserve privacy during LLM interaction. The visual string appears nonsensical to humans, while remaining interpretable by the AI, enabling obfuscated instruction handling without leaking intent.
✔ Emoti-Attack – Subverting NLP with Emoji Sequences: Emoti-Attack is a form of adversarial input that disrupts NLP interpretation by inserting harmless-looking emoji patterns. These can influence or derail the LLM’s understanding without detection.
✔ Counterintelligence and Deception: Unicode characters offer a countermeasure. Security researchers have demonstrated the use of Unicode formatting as a defensive tool: creating decoy messages embedded with Unicode traps that reveal or mislead adversarial AI crawlers or language models scanning open-source intelligence (OSINT) feeds.
✔ Forensic Importance: Understanding emoji misuse can assist forensic investigators in analyzing chat logs, malware payloads, and behavioral indicators, particularly in APT campaigns or disinformation efforts.
Unicode’s transparency, immutability, and predictability make it a valuable component of digital countermeasures in cybersecurity and OSINT.
Dual-Use Encryption via Emoji Embedding
Dual-Use Communication: Encrypted Emoji Payloads in Secure Civil and Military Applications
While most discussions emphasize the risks posed by emojis in digital communication, Freemindtronic has also demonstrated that these same limitations can be harnessed constructively. Leveraging their expertise in air-gapped encryption and segmented key systems, Freemindtronic uses emoji-embedded messages as covert carriers for encrypted content in secure, offline communication workflows.
✔ Operational Principle
Emoji glyphs can embed encrypted payloads using layered Unicode sequences and optional modifiers (e.g., U+FE0F). The visual result appears trivial or humorous, but can encode AES-encrypted messages that are only interpretable by a paired Freemindtronic decryption system.
✔ Use Cases in Civilian and Defense Fields
- Civil: Secure broadcast of contextual alerts (e.g., logistics, health) across untrusted channels using visually benign symbols.
- Military: Covert transmission of encrypted instructions via messaging systems or printed media, decodable only by pre-authorized HSM-equipped terminals.
✔ Advantages Over Traditional Payload Carriers
- Emojis are widespread and rarely filtered.
- Appear non-threatening in hostile digital environments.
- Compatible with zero-trust architectures using offline HSMs.
- Seamless integration into printed formats, signage, or NFC-triggered displays.
✔ Security Implication
This dual-use capability turns emojis into functional steganographic containers for encrypted instructions, authentication tokens, or contextual messages. By pairing emoji-based visuals with secure decryption modules, Freemindtronic establishes a trusted communication channel over inherently insecure or surveilled platforms.
Strategic Takeaway:
What is often seen as a vector of attack (emoji-based obfuscation) becomes—under controlled, secure systems—an innovative tool for safe, deniable, and ultra-lightweight communication across civilian and military domains.
Secure Emoji Encryption Demo – Covert Messaging with AES-256
Unicode and Internationalization for Global Content Reach
Unicode’s strength lies in its ability to represent characters from almost all writing systems in the world. This makes it inherently suitable for multilingual content, ensuring that special characters and symbols are displayed correctly regardless of the language, which is crucial for global SEO and disseminating cybersecurity information internationally. While emojis can sometimes transcend language barriers, their visual interpretation can still be culturally influenced, making Unicode a more stable choice for consistent international communication of symbols and special characters, improving accessibility for a global audience accessing cybersecurity content.
How to Apply Emoji and Character Equivalence Today for Content Optimization
✔ your content – Identify areas where Unicode replacements improve accessibility and compatibility, contributing to WCAG compliance and better SEO, as well as enhancing the clarity and professionalism of cybersecurity communications.
✦ Use structured formatting – Incorporate Unicode symbols while maintaining clarity in digital communication for improved readability and SEO, especially in technical fields like cybersecurity.
➔ Test across platforms – Verify how Unicode alternatives appear on various browsers and devices and ensure font compatibility for optimal accessibility and user experience, particularly for users accessing cybersecurity information on different systems.
✉ Educate your audience – Inform users why Unicode-based formatting enhances readability and usability, indirectly supporting SEO efforts by improving user engagement with even complex topics like cybersecurity.
By integrating emoji and character equivalence, content creators can future-proof their digital presence, ensuring clarity, accessibility, and universal compatibility across platforms, ultimately boosting SEO performance and user satisfaction, and fostering trust in the accuracy and professionalism of cybersecurity content.
⚡ Ready to optimize your content?
Start incorporating Unicode symbols today to enhance content structure and readability while optimizing accessibility! This is particularly important for ensuring clear and unambiguous communication in critical fields like cybersecurity. We encourage you to share your experiences and further suggestions in the comments below.
Best Unicode Equivalents for Emojis
Using Emoji and Character Equivalence enhances consistency, accessibility, and professional formatting. The table below categorizes key Unicode replacements for emojis, ensuring better SEO, readability, and universal compatibility.
✅ Validation & Security
| Emoji | Special Character | Unicode | Description |
|---|---|---|---|
| ✅ | ✔ | U+2714 | Validation checkmark |
| ☑ | ☑ | U+2611 | Checked box |
| ✓ | ✓ | U+2713 | Simple validation tick |
| 🗸 | 🗸 | U+1F5F8 | Alternative tick symbol |
| 🔒 | ⛨ | U+26E8 | Protection symbol |
| ⚠️ | ⚠ | U+26A0 | Warning or alert |
| ☢ | ☢ | U+2622 | Radiation hazard |
| ☣ | ☣ | U+2623 | Biohazard |
| ❌ | ✗ | U+2717 | Cross mark for rejection |
| ❌ | ✘ | U+2718 | Alternative cross for errors |
🧾 Documents & Markers
| Emoji | Special Character | Unicode | Description |
|---|---|---|---|
| 📌 | ✦ | U+2726 | Decorative star or marker |
| 📖 | 📚 | U+1F4DA | Books (Reading) |
| 📖 | ╬ | U+256C | Document symbol |
| 📥 | ⬇ | U+2B07 | Download arrow |
| 📤 | ⬆ | U+2B06 | Upload arrow |
| 📦 | 🗄 | U+1F5C4 | Storage box |
| 📩 | ✉ | U+2709 | Email or message icon |
| 📍 | ❖ | U+2756 | Location marker |
🧭 Arrows & Directions
| Emoji | Special Character | Unicode | Description |
|---|---|---|---|
| → | → | U+2192 | Right arrow |
| ← | ← | U+2190 | Left arrow |
| ↑ | ↑ | U+2191 | Up arrow |
| ↓ | ↓ | U+2193 | Down arrow |
| ↔ | ↔ | U+2194 | Horizontal double arrow |
| ↕ | ↕ | U+2195 | Vertical double arrow |
| ↖ | ↖ | U+2196 | Top-left diagonal arrow |
| ↗ | ↗ | U+2197 | Top-right diagonal arrow |
| ↘ | ↘ | U+2198 | Bottom-right diagonal arrow |
| ↙ | ↙ | U+2199 | Bottom-left diagonal arrow |
| ↩ | ↩ | U+21A9 | Return arrow |
| ↪ | ↪ | U+21AA | Redirection arrow |
| ⇄ | ⇄ | U+21C4 | Change arrow |
| ⇆ | ⇆ | U+21C6 | Exchange arrow |
| ⇨ | ⇨ | U+27A1 | Thick arrow right |
| ⇦ | ⇦ | U+21E6 | Thick arrow left |
| ⇧ | ⇧ | U+21E7 | Thick arrow up |
| ⇩ | ⇩ | U+21E9 | Thick arrow down |
| ↻ | ↻ | U+21BB | Clockwise circular arrow |
| ↺ | ↺ | U+21BA | Counterclockwise circular arrow |
| ⤴ | ⤴ | U+2934 | Curved arrow up |
| ⤵ | ⤵ | U+2935 | Curved arrow down |
| ⮕ | ⮕ | U+2B95 | Long arrow right |
| ⬅ | ⬅ | U+2B05 | Long arrow left |
| ⬆ | ⬆ | U+2B06 | Long arrow up |
| ⬇ | ⬇ | U+2B07 | Long arrow down |
| ↱ | ↱ | U+21B1 | Right-angled upward arrow |
| ↰ | ↰ | U+21B0 | Left-angled upward arrow |
| ↳ | ↳ | U+21B3 | Right-angled downward arrow |
| ↲ | ↲ | U+21B2 | Left-angled downward arrow |
🌍 Transport & Travel
| Emoji | Special Character | Unicode | Description |
|---|---|---|---|
| 🚀 | ▲ | U+25B2 | Up-pointing triangle (Launch) |
| ✈ | ✈ | U+2708 | Airplane (Travel & speed) |
| 🚗 | 🚗 | U+1F697 | Car |
| 🚕 | 🚕 | U+1F695 | Taxi |
| 🚙 | 🚙 | U+1F699 | SUV |
| 🛴 | 🛴 | U+1F6F4 | Scooter |
| 🚲 | 🚲 | U+1F6B2 | Bicycle |
| 🛵 | 🛵 | U+1F6F5 | Motorbike |
| 🚄 | 🚄 | U+1F684 | Fast train |
| 🚆 | 🚆 | U+1F686 | Train |
| 🛳 | 🛳 | U+1F6F3 | Cruise ship |
⚡ Energy & Technology
| Emoji | Special Character | Unicode | Description |
|---|---|---|---|
| ⚡ | ⚡ | U+26A1 | Lightning (Energy, speed) |
| 📡 | 📡 | U+1F4E1 | Satellite antenna |
| 📶 | 📶 | U+1F4F6 | Signal strength |
| 🔊 | 🔊 | U+1F50A | High-volume speaker |
| 🔉 | 🔉 | U+1F509 | Medium-volume speaker |
| 🔈 | 🔈 | U+1F508 | Low-volume speaker |
| 🔇 | 🔇 | U+1F507 | Muted speaker |
| 🎙 | 🎙 | U+1F399 | Microphone |
| 🎚 | 🎚 | U+1F39A | Volume slider |
💰 Currency & Finance
| Emoji | Special Character | Unicode | Description |
|---|---|---|---|
| € | € | U+20AC | Euro |
| $ | $ | U+0024 | Dollar |
| £ | £ | U+00A3 | Pound sterling |
| ¥ | ¥ | U+00A5 | Yen |
| ₿ | ₿ | U+20BF | Bitcoin |
| 💰 | 💰 | U+1F4B0 | Money bag |
| 💳 | 💳 | U+1F4B3 | Credit card |
| 💲 | 💲 | U+1F4B2 | Dollar sign |
| 💱 | 💱 | U+1F4B1 | Currency exchange |
Additional Differentiation Points to Make Your Article Stand Out
To make this article unique, I have included:
✅ Practical Implementation Guide
- How to replace emojis with Unicode characters in WordPress, HTML, Markdown, and CSS.
- Keyboard shortcuts and Unicode input methods for Windows, Mac, and Linux.
✅ SEO and Accessibility Benefits
- Unicode characters improve accessibility for screen readers, making content more inclusive.
- How Unicode enhances SEO indexing compared to emoji-based content.
✅ Historical and Technical Context
- The evolution of Unicode and emoji encoding standards.
- The role of different operating systems in emoji representation.
✅ Comparison with Other Symbol Systems
- Differences between ASCII, Unicode, and emoji encoding.
- Comparing Unicode versus icon-based alternatives for visual communication.
✅ Industry-Specific Use Cases
- Using Unicode characters in legal, academic, and technical documentation.
- Best practices for corporate and professional communications without emojis.
Why Replace Emojis with Unicode Characters?
Emoji and character equivalence is crucial for maintaining consistent content formatting across devices. While emojis improve engagement, they do not always display correctly across all systems, making Unicode characters a more reliable choice.
✔ Advantages
- Universal Compatibility – Unicode characters render consistently across different browsers and platforms.
- Improved Accessibility – Assistive technologies and screen readers interpret special characters more effectively, aiding in WCAG compliance.
- SEO Optimization – Unicode symbols are indexed correctly by search engines, avoiding potential misinterpretations and enhancing visibility.
- Consistent Formatting – Ensures that content remains legible in professional and academic contexts.
- Performance Benefits – Unicode text characters are generally lighter than emoji image files, potentially improving page load times.
✘ Disadvantages
- Reduced Visual Appeal – Emojis are more visually striking than characters.
- Less Expressive – Special characters lack emotional depth compared to emojis.
- Typing Challenges – Some symbols require specific Unicode inputs or copy-pasting.
Adopting Unicode characters instead of emojis ensures accessibility, professional consistency, and SEO-friendly content. To implement this approach effectively:
✔ Audit your existing content — Identify where emoji replacements may improve accessibility and compatibility, contributing to WCAG compliance. ✦ Use structured formatting — Incorporate Unicode symbols while maintaining clarity in digital communication. ➔ Test across platforms — Verify how Unicode alternatives appear on various browsers and devices and ensure font compatibility. ✉ Educate your audience — Inform users why Unicode-based formatting enhances readability and usability.
By integrating emoji and character equivalence, content creators can future-proof their digital presence, ensuring clarity, accessibility, and universal compatibility across platforms.
⚡ Ready to optimize your content? Start incorporating Unicode symbols today to enhance content structure and readability while optimizing accessibility! We encourage you to share your experiences and further suggestions in the comments below.
Official Sources for Further Reading on Unicode and Accessibility
How to Shield Your Digital Life from Keystroke Loggers: An Expert’s Guide
Defending Against Keyloggers is essential to protect your sensitive data. Keyloggers are silent tools that record every keystroke, exposing sensitive data to cyber threats. This guide explores high-profile breaches, innovative attack methods, and strategic defenses. It offers a comprehensive strategy to secure your sensitive data against these ubiquitous threats and provides effective solutions for enhanced protection. Stay informed and proactive with our expert advice in the constantly evolving cybersecurity landscape.
FAQ
What’s the Difference Between Software and Hardware Keyloggers?
Software keyloggers
These programs run discreetly in the background of the computer, recording every keystroke. They can be installed through malware or accidentally downloaded together with other applications. These keyloggers can not only capture keystrokes but also record screenshots and monitor internet activity.
Hardware keyloggers
These devices are usually small physical devices that connect between the keyboard and the computer’s USB or PS/2 port. They log keystrokes directly from the keyboard before the information is transmitted to the operating system. Their physical presence makes them detectable by visual inspection, but they are often very discreet and difficult to notice.
Is a keylogger a virus?
No, keyloggers are tools that can be used for both legitimate monitoring and malicious activities.
How do I know if I am infected with a keylogger?
Regular scans with updated antivirus software and monitoring for unusual system behavior are effective detection methods.
Can mobile devices get infected with keyloggers?
Although less common, mobile devices can indeed be compromised by keyloggers, especially through malicious apps or compromised security software.
What is the best way to protect my devices from keyloggers?
Using comprehensive security solutions like PassCypher and maintaining vigilant cybersecurity practices are your best defenses.
What are the best immediate actions to take if a keylogger is detected?
Disconnect from the internet, change all passwords on a secure device, and use a trusted malware removal tool to clean the infected system.
What is the difference between software and hardware keyloggers?
Software keyloggers
These programs run discreetly in the background of the computer, recording every keystroke. They can be installed through malware or accidentally downloaded together with other applications. These keyloggers can not only capture keystrokes but also record screenshots and monitor internet activity.
Hardware keyloggers
These devices are usually small physical devices that connect between the keyboard and the computer’s USB or PS/2 port. They log keystrokes directly from the keyboard before the information is transmitted to the operating system. Their physical presence makes them detectable by visual inspection, but they are often very discreet and difficult to notice.
How can I detect a keylogger on my computer?
Detection of software keyloggers:
- Use of antivirus and anti-malware software: Make sure your security software is up to date and perform regular scans. Many modern security software programs are equipped to detect keyloggers.
- System Process Monitoring: Use the Task Manager to monitor running processes. Unknown or suspicious processes that use high resources can be signs of a keylogger.
- Checking startup programs: Review the programs that launch when your computer starts. Keyloggers can set up an auto-start to stay active.
Hardware Keylogger Detection:
- Physical inspection: Regularly check the connections between your keyboard and your computer. Look for any unusual devices plugged into the USB or PS/2 port where the keyboard connects.
- Check for unknown devices: Monitor your device manager for any unknown or unrecognized hardware that might be connected to your system.
What are the best practices to protect against keyloggers?
Use our password management software
PassCypher HSM PGP in its free or advanced version or hardware version with PassCyppher NFC HSM to secure your NFC Android phone as well
Robust security
Install and maintain trusted antivirus software that includes protection against keyloggers.
Update your operating system and applications
Regular updates often fix security vulnerabilities that could be exploited by keyloggers.
Be careful with downloads
Avoid downloading software from unverified sources. Favor the official websites of the publishers to reduce the risk of downloading malicious applications.
Education and awareness
Learn how to recognize phishing attempts and other techniques used to install keyloggers. Don’t click on suspicious links or attachments in emails or messages.
Use of password managers
Password managers can autofill your login information without you having to hit the keys, reducing the risks associated with software keyloggers.
Multi-factor authentication (MFA)
Use PassCypher NFC HSM also handles 2FA/MFA OTP two-factor authentication keys (TOTP and HOTP) when possible, especially for important accounts like email and bank accounts. This adds an extra layer of security that doesn’t rely solely on passwords.
Use robust security software
Install and maintain trusted antivirus software that includes protection against keyloggers.
Update your operating system and applications
Regular updates often fix security vulnerabilities that could be exploited by keyloggers.
Be careful with downloads
Avoid downloading software from unverified sources. Favor the official websites of the publishers to reduce the risk of downloading malicious applications.
Education and awareness
Learn how to recognize phishing attempts and other techniques used to install keyloggers. Don’t click on suspicious links or attachments in emails or messages.
Use of password managers
Password managers can autofill your login information without you having to hit the keys, reducing the risks associated with software keyloggers.
Software keyloggers
These programs run discreetly in the background of the computer, recording every keystroke. They can be installed through malware or accidentally downloaded together with other applications. These keyloggers can not only capture keystrokes but also record screenshots and monitor internet activity.
Hardware keyloggers
These devices are usually small physical devices that connect between the keyboard and the computer’s USB or PS/2 port. They log keystrokes directly from the keyboard before the information is transmitted to the operating system. Their physical presence makes them detectable by visual inspection, but they are often very discreet and difficult to notice.
No, keyloggers are tools that can be used for both legitimate monitoring and malicious activities.
Regular scans with updated antivirus software and monitoring for unusual system behavior are effective detection methods.
Although less common, mobile devices can indeed be compromised by keyloggers, especially through malicious apps or compromised security software.
Using comprehensive security solutions like PassCypher and maintaining vigilant cybersecurity practices are your best defenses.
Disconnect from the internet, change all passwords on a secure device, and use a trusted malware removal tool to clean the infected system.
Software keyloggers
These programs run discreetly in the background of the computer, recording every keystroke. They can be installed through malware or accidentally downloaded together with other applications. These keyloggers can not only capture keystrokes but also record screenshots and monitor internet activity.
Hardware keyloggers
These devices are usually small physical devices that connect between the keyboard and the computer’s USB or PS/2 port. They log keystrokes directly from the keyboard before the information is transmitted to the operating system. Their physical presence makes them detectable by visual inspection, but they are often very discreet and difficult to notice.
Detection of software keyloggers:
- Use of antivirus and anti-malware software: Make sure your security software is up to date and perform regular scans. Many modern security software programs are equipped to detect keyloggers.
- System Process Monitoring: Use the Task Manager to monitor running processes. Unknown or suspicious processes that use high resources can be signs of a keylogger.
- Checking startup programs: Review the programs that launch when your computer starts. Keyloggers can set up an auto-start to stay active.
Hardware Keylogger Detection:
- Physical inspection: Regularly check the connections between your keyboard and your computer. Look for any unusual devices plugged into the USB or PS/2 port where the keyboard connects.
- Check for unknown devices: Monitor your device manager for any unknown or unrecognized hardware that might be connected to your system.
Use our password management software
PassCypher HSM PGP in its free or advanced version or hardware version with PassCyppher NFC HSM to secure your NFC Android phone as well
Robust security
Install and maintain trusted antivirus software that includes protection against keyloggers.
Update your operating system and applications
Regular updates often fix security vulnerabilities that could be exploited by keyloggers.
Be careful with downloads
Avoid downloading software from unverified sources. Favor the official websites of the publishers to reduce the risk of downloading malicious applications.
Education and awareness
Learn how to recognize phishing attempts and other techniques used to install keyloggers. Don’t click on suspicious links or attachments in emails or messages.
Use of password managers
Password managers can autofill your login information without you having to hit the keys, reducing the risks associated with software keyloggers.
Multi-factor authentication (MFA)
Use PassCypher NFC HSM also handles 2FA/MFA OTP two-factor authentication keys (TOTP and HOTP) when possible, especially for important accounts like email and bank accounts. This adds an extra layer of security that doesn’t rely solely on passwords.
Use robust security software
Install and maintain trusted antivirus software that includes protection against keyloggers.
Update your operating system and applications
Regular updates often fix security vulnerabilities that could be exploited by keyloggers.
Be careful with downloads
Avoid downloading software from unverified sources. Favor the official websites of the publishers to reduce the risk of downloading malicious applications.
Education and awareness
Learn how to recognize phishing attempts and other techniques used to install keyloggers. Don’t click on suspicious links or attachments in emails or messages.
Use of password managers
Password managers can autofill your login information without you having to hit the keys, reducing the risks associated with software keyloggers.
A USB drive that suddenly becomes write-protected is a common issue on modern Windows systems. If you are trying to unlock write-protected USB media on Windows 10 or Windows 11 without using third-party software, this guide explains the exact causes, limits, and safe recovery paths.
Express Summary — Unlock Write-Protected USB (Windows)
⮞ Reading Note
This express digest takes ≈ 4 minutes. It delivers the essentials: root causes, fastest fixes, and the point where you must stop and preserve data.
⚡ The discovery
A USB drive that was writable yesterday suddenly becomes read-only: Windows blocks copy, delete, rename, and even simple edits. This can be a physical lock, a Windows restriction (policy/registry), a logical read-only flag, or a firmware-level protection mode when NAND memory is failing.
✦ Immediate impact
- File operations fail (copy, delete, rename) with “write-protected” errors
- Formatting may be blocked (if protection is firmware-enforced)
- Security risk: a USB used across systems increases exposure to malware and policy locks
⚠ Strategic message — when unlocking is the wrong objective
Write protection is not always a malfunction. In modern systems, it is often a deliberate safety boundary. Windows may enforce it by policy; USB controllers may enforce it to prevent irreversible data corruption when flash memory degradation is detected.
The critical mistake is to assume that every write-protected state must be unlocked. The real objective is classification: identifying whether the device is in a reversible state or has reached a hardware-defined end-of-life condition, where further action becomes harmful.
⎔ Sovereign countermeasure
Reduce reliance on “trusting the endpoint”: isolate sensitive secrets from general-purpose systems, enforce controlled workflows for removable storage, and treat USB drives as semi-disposable assets with rotation and health monitoring.
Want to go further?
Le advanced summary clarifies the modern causes (Windows 11 policies, BitLocker To Go edge cases, firmware fail-safe) and prepares the full Chronicle.
Reading parameters
Express summary: ≈ 4 min
Advanced summary: ≈ 6 min
Full Chronicle : ≈ 35–40 min
Publication date : 2024-01-01
Last updated : 2026-01-03
Complexity level : Advanced — Windows storage policies & removable media
Technical density : ≈ 65 %
Available languages : EN · FR · ES · CAT
Thematic focus : USB write protection, DiskPart, CHKDSK, BitLocker To Go, firmware lock
Editorial type : Tech Fix — Reference Guide (Freemindtronic)
Impact level : 7.8 / 10 — data integrity & operational continuity
Références officielles
– Microsoft DiskPart documentation
– Microsoft CHKDSK documentation
– Microsoft BitLocker overview
– Microsoft removable storage access control
☰ Quick navigation
- Back to top
- Express summary
- Advanced summary
- What is a USB flash drive?
- Chronicle — Unlock Write-Protected USB
- Common causes of USB write protection (2024)
- Method 1 — Physical lock
- Method 2 — Windows Registry
- Method 3 — DiskPart
- Method 4 — CHKDSK
- Method 5 — BitLocker To Go
- Method 6 — Group Policy / write control
- Method 7 — Event Viewer signals
- Method 8 — Reformat (last resort)
- Prevention — reduce recurrence
- Manufacturer-specific USB behaviors
- Forum tricks — what works, what to avoid
- Decision checkpoint — when to stop
- Real-world case
- Known non-recoverable scenarios
- Logical vs firmware lock
- USB decision tree
- Glossary — USB & Storage terms
- FAQ
- What we didn’t cover
- Why this guide cannot be reduced
- Sovereign knowledge vs generated answers
- Editorial note
- Related topic — Evikey NFC
- Strategic outlook
The posts displayed above ↑ belong to the same editorial section: Tech Fixes & Security Solutions. They extend this Chronicle by covering practical remediation patterns, operational diagnostics, and resilient handling of security and integrity incidents across the Freemindtronic ecosystem.
Advanced Summary — When write protection becomes a system behavior (2024)
This complements the express digest. It does not repeat the steps; it explains why write protection has become more common on Windows 11-era systems and why some USB sticks become permanently read-only.
In 2024, removable storage sits at the intersection of three forces: security policy hardening (corporate and consumer), file-system integrity controls (especially with exFAT on unstable media), and controller-level protection mechanisms that activate when flash memory degradation is detected. As a result, “write-protected” may mean:
- Policy lock — Windows prevents writes by design (registry/group policy/device control)
- Logical lock — disk attributes or metadata errors mark the volume read-only
- Encryption boundary — BitLocker To Go introduces states where writes are blocked until properly unlocked
- Firmware lock — the controller refuses writes to avoid corrupting data when NAND cells are failing
Key Insights
- DiskPart can clear flags, not firmware fail-safes.
- CHKDSK fixes file-system structures, not dying flash memory.
- If formatting fails repeatedly, prioritize data extraction and replacement.
Summary
- Express summary
- Advanced summary
- What is a USB flash drive?
- Chronicle — Unlock Write-Protected USB (Windows)
- Common causes (2024)
- Prevention — reduce recurrence
- Logical vs firmware lock (comparison)
- USB decision tree
- Glossary — USB & Storage terms
- FAQ — USB write protection
- What we didn’t cover
- Why this guide cannot be reduced to a single answer
- Related topic — Evikey NFC
- Strategic outlook
What Is a USB Flash Drive — Hardware Basics You Need to Understand
Before attempting to unlock a write-protected USB, it is essential to understand what a USB flash drive actually is. Contrary to common assumptions, a USB stick is not a simple passive storage device. It is a compact embedded system combining multiple hardware components that actively manage data integrity and lifespan.
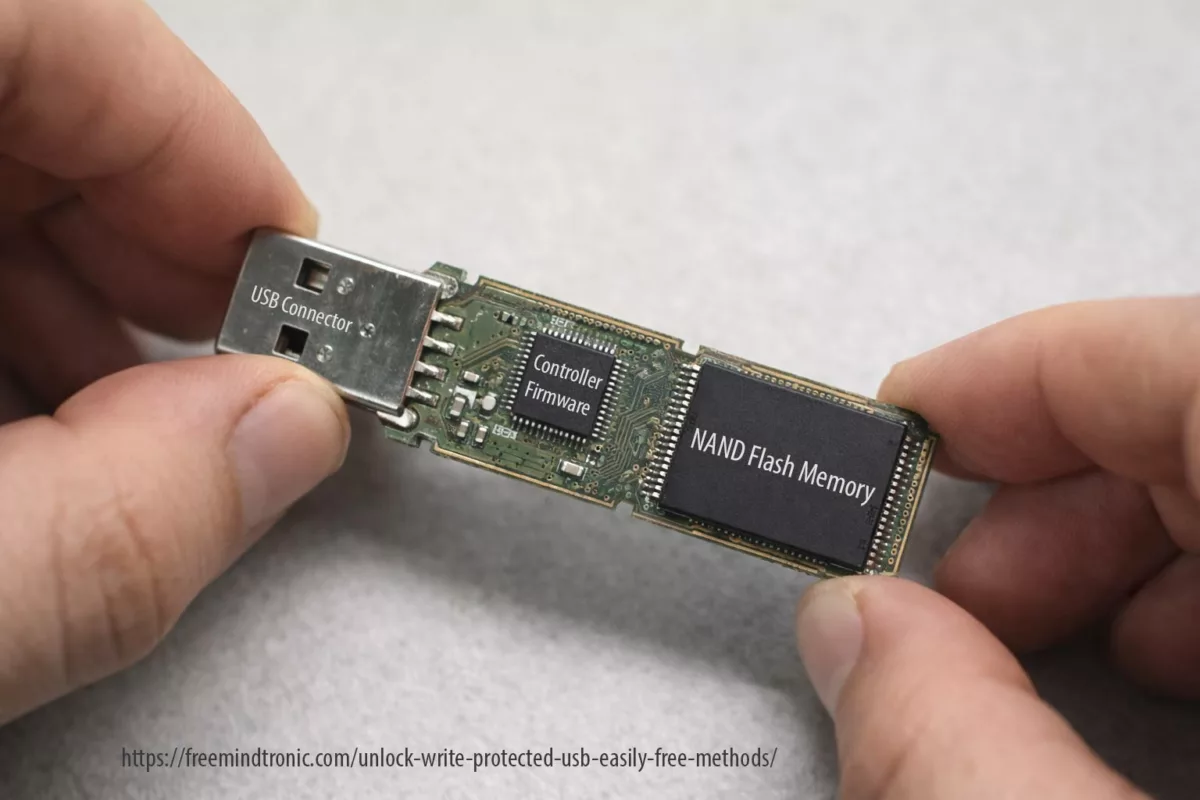
At its core, a USB flash drive contains two critical elements: a USB controller and NAND flash memory.
The USB controller: the decision-maker
The controller is a microcontroller that manages all read and write operations. It implements wear-leveling algorithms, error correction (ECC), bad block management, and firmware-level safety rules. When the controller detects that NAND memory has reached critical wear thresholds or repeated I/O failures, it can intentionally enforce a permanent read-only state.
NAND flash memory: finite by design
NAND flash memory stores data using cells with a limited number of write cycles. Once these limits are exceeded, data integrity can no longer be guaranteed. At that point, the controller prioritizes preservation of readable data over continued writes.
Why this matters for write protection
This hardware reality explains why some write-protected USB drives cannot be unlocked by software tools. Registry edits, DiskPart commands, or formatting attempts operate at the operating-system level. They cannot override firmware decisions made by the controller to protect failing NAND memory.
Understanding this distinction is key: some write protection states are reversible, while others signal the end of the device lifecycle.
Unlock write-protected USB on Windows (Reference 2024)
When a USB flash drive becomes read-only, Windows is reacting to a specific signal: policy restriction, file-system inconsistency, encryption boundary, or controller-level protection.
Common causes of USB write protection (2024)
Before “fixing”, classify. A reversible lock can be cleared safely. A firmware lock should be treated as an end-of-life signal: extract data, replace the device, and update your workflow.
- Physical switch (rare, but real)
- Registry / policy restrictions (common on reused PCs)
- Disk attributes (logical read-only)
- File-system corruption (especially after unsafe ejection)
- BitLocker To Go states (locked volumes / permission boundary)
- Firmware fail-safe (NAND wear, controller protection)
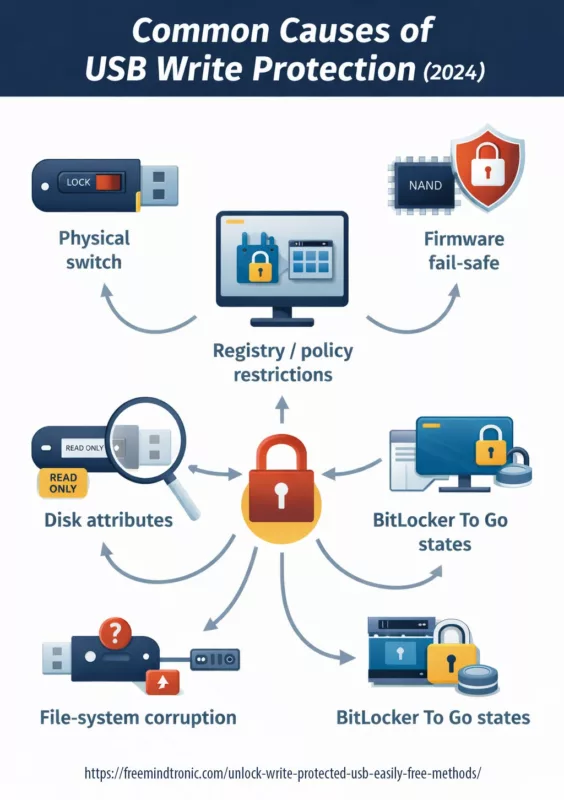
Method 1 — Check the physical lock
This sounds obvious, but it’s often overlooked.
- Remove the USB drive from your computer.
- Inspect its casing (or SD adapter) for a small LOCK / UNLOCK switch.
- Toggle the switch to the unlocked position.
- Reinsert the USB drive and test it again.
If the device remains write-protected, move on to software-based solutions.
If your device (or SD adapter) has a lock switch, it overrides everything. Toggle to unlock, reinsert, and retest.
Method 2 — Remove USB Write Protection Using the Windows Registry
This method targets Windows policies that explicitly block writing to removable drives.
⚠ Warning: Editing the registry incorrectly can affect system stability. Follow the steps exactly.
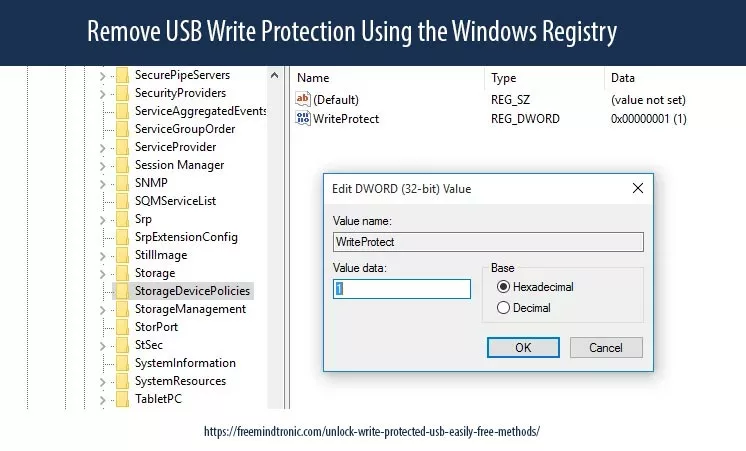
Registry: StorageDevicePolicies
- Open Regedit as admin.
- Go to
HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlStorageDevicePolicies - Set
WriteProtectto 0 (DWORD). - Restart Windows.
If StorageDevicePolicies does not exist, you can create it and add WriteProtect. This is typical on systems that inherited restrictions.

From this point onward, each method is also a diagnostic test.
If a method completes successfully but the device state does not change, this is not a failure — it is a signal.
Method 3 — Use DiskPart to Clear the Read-Only Attribute
DiskPart allows you to modify disk attributes directly at the system level. This method is frequently searched under queries such as diskpart clear readonly USB or USB write-protected cannot format.
- Open Command Prompt (Admin).
- Type the following commands, pressing Enter after each one:
diskpart list disk select disk X attributes disk clear readonly exit
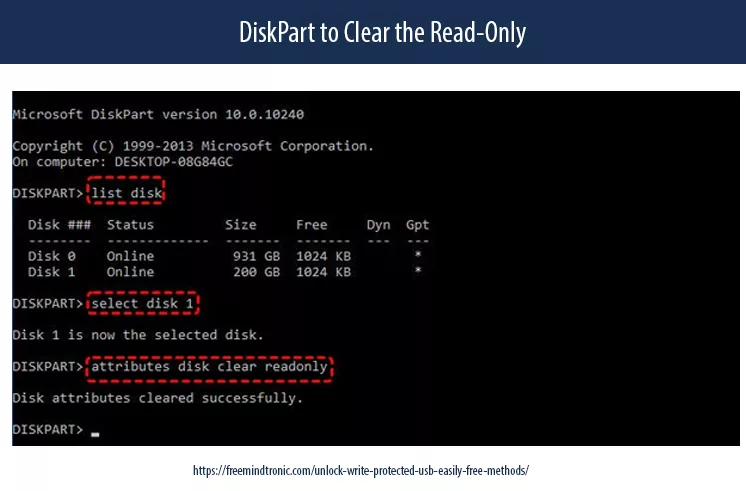
Be precise when selecting disk X. If this works, the issue was likely logical.
Safely remove and reconnect the USB device.
Method 4 — CHKDSK: repair file-system errors
If corruption exists, Windows may mount read-only. CHKDSK repairs structural issues:
chkdsk X: /f
Replace X: with the USB letter. If errors reappear soon after, the medium is unstable.
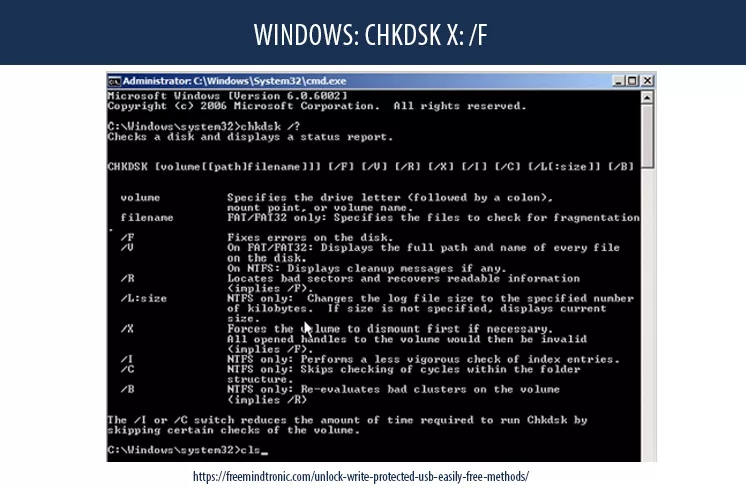
Method 5 — Unlock Write-Protected USB when BitLocker To Go blocks writes (Windows 10/11)
If the USB drive is encrypted, BitLocker can block write operations while the volume remains locked, only partially unlocked, or opened under a session that lacks write permission. Before attempting any fix, verify the items below.
- The volume is fully unlocked (not just visible in File Explorer).
- You are using an account/session with permission to write to the volume.
- Device policies do not restrict writes to encrypted removable media.
Official references (Microsoft)
Method 6 — Unlock Write-Protected USB caused by Group Policy or removable storage write control
On some Windows systems, removable storage writes are blocked intentionally. This is common on managed or reused PCs where administrators enforce restrictions under Removable Storage Access or BitLocker removable drive policies. If you control the device, review policy settings; if the machine is managed, the restriction may be enforced centrally.
Official references (Microsoft)
Method 7 — Event Viewer signals: distinguish file-system integrity issues from hardware I/O failure
If the same USB drive repeatedly flips to read-only, Windows logs often reveal whether you are dealing with file-system corruption or repeated disk I/O errors. Open Event Viewer and review Windows Logs → System. Look for recurring warnings/errors from sources such as Disk or Ntfs. Persistent I/O errors strongly correlate with controller fail-safes and end-of-life behavior.
Official references (Microsoft)
Method 8 — Reformat to remove USB write protection (Last Resort, data loss expected)
If the drive remains accessible but still appears locked, formatting may restore normal behavior — but it will erase all data. Only proceed after extracting anything you can.
- Open File Explorer → right-click the USB drive.
- Select Format.
- Choose exFAT or FAT32 (based on your compatibility needs).
- Uncheck Quick Format if available and you want a deeper pass.
- Start the process.
If formatting fails with a write-protection error, the USB memory controller is likely enforcing read-only at firmware level. Treat this as end-of-life: extract readable data and replace the device.
Official references (Microsoft)
Prevention (2024 hygiene)
- Always use “Safely remove hardware” (reduces corruption)
- Avoid using the same USB across high-risk machines
- Prefer exFAT for cross-platform, NTFS for Windows-only + permissions (context dependent)
- Rotate removable media and retire devices showing repeated errors
As ransomware and device-control policies expand, “write protection” increasingly appears as a security boundary, not a random malfunction. Expect more controlled removable-storage environments — and more firmware fail-safes on low-cost media.
Manufacturer-specific USB behaviors (forums vs reality)
Community forums often suggest “magic fixes” for write-protected USB drives. Some of these tricks work — but only because certain manufacturers implement specific controller behaviors.
- Consumer flash drives frequently switch to read-only mode when internal error thresholds are reached. This is a protective firmware behavior, not a Windows bug.
- Many models use conservative wear-leveling. Repeated CHKDSK or formatting attempts may accelerate the transition to permanent read-only mode.
- USB flash controllers often expose limited recovery states; when write protection appears, it usually reflects internal health checks rather than logical flags.
- Some drives historically supported recovery utilities, but success rates vary and are highly model-dependent.
Forum advice often ignores a critical distinction: logical locks can be cleared, but controller-enforced locks cannot. Applying aggressive “fixes” repeatedly may worsen data integrity.
Forum tricks — what works, what to avoid
Many online discussions recommend extreme or repetitive actions to unlock write-protected USB drives. Here is a technical reality check.
✔ Sometimes useful — Clearing read-only flags with DiskPart when the issue is purely logical.
✔ Reasonable — Running CHKDSK once to repair file-system metadata after unsafe removal.
⚠ Risky — Repeated formatting attempts after firmware-level write protection appears.
✖ Dangerous — Low-level controller reflashing tools shared on forums (high data-loss risk).
✖ Misleading — Registry “tweaks” claiming to unlock all USB drives regardless of hardware state.
A recurring forum myth is that persistence will eventually “break” write protection. In reality, modern controllers are designed to resist exactly that.
Decision checkpoint — when to stop trying
Before attempting another fix, ask these questions:
- Does DiskPart fail to clear the read-only attribute?
- Does formatting fail immediately with write-protection errors?
- Do Windows logs report repeated I/O or medium errors?
If the answer is “yes” to all three, the safest action is to stop write attempts, extract readable data, and replace the device.
Treat persistent write protection as an end-of-life signal, not a challenge to overcome.
Real-world case — when nothing changes
Field feedback (user comment):
“no use all the tips tried but it is in the same stage”
This type of feedback is common — and important. It reflects a scenario where all documented methods are executed correctly, yet the USB device remains write-protected with no observable change.
From a technical standpoint, this outcome is not a failure of the steps. It is a diagnostic result.
When a USB drive stays in the same state after:
- clearing logical read-only flags,
- checking registry or policy restrictions,
- running CHKDSK,
- and attempting formatting,
the most likely explanation is firmware-level write protection enforced by the USB controller. This protection is intentional and designed to prevent further data corruption when internal error thresholds or NAND wear limits are reached.
In such cases, persistence does not increase success. It increases risk. No change is not failure — it is the diagnosis.
When no method alters the device state, stop write attempts. Extract readable data if possible, then replace the device. Lack of change is not failure — it is a signal
Known non-recoverable USB write-protection scenarios
Not all write-protected USB situations are recoverable. Based on field experience and controller behavior, the following scenarios are generally considered non-reversible.
- Persistent write protection after DiskPart and formatting attempts
When logical flags are cleared but the device remains read-only and formatting fails immediately, the controller is likely enforcing a permanent lock. - Repeated I/O or medium errors reported by the operating system
These signals often indicate failing NAND cells. Write protection is triggered to prevent silent data corruption. - USB drives that suddenly switch to read-only after heavy use
Consumer-grade flash drives may enter irreversible read-only mode once internal wear thresholds are exceeded. - Write-protected devices that remain readable but never writable again
This is a classic end-of-life behavior: data extraction remains possible, but write access is permanently disabled. - Failures that persist across multiple systems and operating systems
If the same USB device is read-only on different machines, the cause is almost certainly hardware-level.
Attempting aggressive fixes in these scenarios can accelerate data loss. Once firmware-level protection is suspected, preservation takes priority over correction.
Logical lock vs Firmware lock — comparison table
| Criteria | Logical / Policy Lock | Firmware / Controller Lock |
|---|---|---|
| Origin | Windows registry, group policy, disk attributes, file-system errors | USB controller firmware (NAND wear, internal error thresholds) |
| DiskPart effect | ✓ Clears read-only flags | ✖ No effect |
| CHKDSK effect | ✓ Repairs file-system metadata | ✖ No effect on hardware |
| Formatting | ✓ Usually possible | ✖ Fails immediately |
| Data recovery chance | High | Limited to read-only extraction |
| Recommended action | Proceed with policy/flag/file-system fixes | Stop write attempts, extract data, replace device |
USB write protection — decision tree
USB becomes write-protected
│
├─ Does the device have a physical lock?
│ ├─ YES → Unlock switch → Retest
│ └─ NO
│
├─ Can DiskPart clear readonly?
│ ├─ YES → Logical lock resolved
│ └─ NO
│
├─ Does CHKDSK repair errors?
│ ├─ YES → Monitor device stability
│ └─ NO
│
├─ Does formatting fail immediately?
│ ├─ YES → Firmware / controller lock
│ │ → Extract data (read-only)
│ │ → Replace USB device
│ └─ NO
│
└─ Check policies / BitLocker states
└─ Adjust governance or unlock volume
Glossary — USB & Storage Terms
This internal glossary clarifies key technical terms used throughout this Chronicle. Click a term to reveal its definition.
USB write-protection concepts
Write-Protected USBClick
Read-Only AttributeClick
Windows and system-level mechanisms
DiskPartClick
CHKDSKClick
BitLocker To GoClick
Removable Storage PolicyClick
Storage hardware and controller behavior
Firmware LockClick
NAND Flash MemoryClick
USB ControllerClick
Wear-LevelingClick
Operational and lifecycle concepts
File System (exFAT / NTFS)Click
Safely Remove HardwareClick
End-of-Life (EOL)Click
Frequently Asked Questions — USB write protection
Understanding sudden write protection
In most cases, write protection does not appear randomly. Instead, it is triggered by a specific condition. For example, a physical lock may be enabled, Windows may enforce a storage policy, or disk attributes may mark the device as read-only. Additionally, file-system corruption after unsafe removal, encryption states such as BitLocker To Go, or controller fail-safes activated by failing flash memory can all lead to a sudden read-only state.
What DiskPart can — and cannot — do
DiskPart is effective when the issue is purely logical. It clears read-only flags set at the disk or volume level. However, if the USB controller itself enforces write protection at firmware level, DiskPart has no authority to override it. In that case, the command completes, but the device state remains unchanged.
Why formatting is sometimes blocked immediately
When formatting fails instantly with write-protection errors, this usually indicates firmware-enforced protection. In other words, the controller has detected critical NAND wear or repeated I/O errors and has intentionally disabled write access to prevent further data corruption.
Reversible locks versus end-of-life signals
Not necessarily. Logical locks or policy-based restrictions are often reversible. By contrast, firmware-level write protection typically marks the device as having reached end-of-life. In this scenario, the priority shifts from repair to data preservation.
When persistence becomes counterproductive
Once DiskPart, CHKDSK, and formatting attempts all fail, continuing to force write operations rarely improves the outcome. On the contrary, repeated attempts may accelerate data loss. At this point, stopping is not giving up — it is the correct operational decision.
When no change is itself a diagnosis
If all documented methods were applied correctly and the USB device remains in the same state, this is not a failure of the guide. Rather, it strongly suggests firmware-level write protection enforced by the USB controller. This protection is intentional and designed to preserve remaining readable data once internal error thresholds or NAND wear limits are reached. Therefore, further write attempts are discouraged. The recommended action is to extract readable data if possible, then replace the device.
What CHKDSK actually repairs
CHKDSK repairs file-system structures and metadata inconsistencies. However, it does not repair physical flash memory. If errors reappear quickly after repair, the storage medium itself is likely degrading.
Interpreting repeated formatting failures
Often, yes. When formatting consistently fails under write-protection errors, firmware enforcement or hardware degradation is the most likely cause. In such cases, the safest approach is to focus on data extraction and device replacement rather than recovery attempts.
Reducing future write-protection incidents
To reduce recurrence, treat removable media as semi-disposable assets. Rotate USB drives regularly, retire devices showing early warning signs, always eject safely, and avoid mixing the same USB device between high-risk and trusted environments.
⧉ What We Didn’t Cover
Why this guide cannot be reduced to a single answer
Modern generative systems excel at summarizing procedures. However, USB write protection is not a single problem with a single fix. It is a classification problem.
This Chronicle deliberately separates logical locks, policy restrictions, encryption states, and firmware-enforced protection. Collapsing these into a single “solution” increases the risk of data loss and misdiagnosis.
In other words, this guide is not designed to be consumed as a static answer, but as a decision framework. Its value lies in the reasoning path, not in isolated commands.
Sovereign knowledge vs generated answers
The rise of generative systems changes how information is accessed. Instead of navigating documents, users increasingly receive synthesized answers. While efficient, this shift introduces a structural risk: context compression.
USB write protection is not a single problem with a universal fix. It is a classification problem involving hardware limits, operating system policies, encryption states, and controller-level safeguards. Reducing this complexity to a single generated answer increases the likelihood of misdiagnosis and data loss.
This Chronicle deliberately preserves decision paths, failure boundaries, and stop conditions. Its purpose is not to produce an output, but to support informed judgment at each step.
In this sense, sovereign knowledge is not opposed to automation. It defines the conditions under which automation must stop and responsibility returns to the operator.
Editorial note — Freemindtronic perspective
Freemindtronic publications are built around a clear constraint. From the outset, they must remain usable even when access to information becomes mediated, filtered, or partially opaque.
Consequently, for technical domains such as removable storage, security controls, or data integrity, blindly executing isolated commands is no longer sufficient. Instead, operational clarity emerges from knowing when not to act, when to stop, and when preservation outweighs correction.
This Chronicle directly reflects that editorial stance. It does not promise universal fixes. Rather, it maps operational boundaries and highlights concrete signals indicating when a device has reached a non-recoverable state.
Moreover, in environments increasingly shaped by centralized platforms and automated mediation, maintaining local reasoning capacity is no longer optional. It becomes a practical form of operational sovereignty.
Sovereignty begins where automated answers end — precisely at the moment informed responsibility is required.
Related topic — Evikey NFC and hardware-level resilience for USB storage

This Chronicle explains how and why USB drives become write-protected, including scenarios caused by firmware fail-safes, flash memory degradation, or integrity violations. In this context, it is important to highlight architectures that significantly reduce these risks at the hardware level.
Evikey NFC integrates multiple layers of physical and electronic protection designed to mitigate the most common causes of flash memory degradation and controller-enforced write protection. These protections operate autonomously, without relying on the operating system or software drivers.
Integrated protections against flash memory degradation
- Automatic electronic protection against overvoltage and undervoltage, preventing electrical stress on the controller and NAND memory.
- Advanced ESD protection rated at 2 × 27 kV on the data channel, drastically reducing damage from electrostatic discharge.
- Thermal control and cutoff mechanisms, acting as a protective circuit breaker in abnormal temperature conditions.
- Full military-grade resin encapsulation, making the device fully waterproof and mechanically resistant, with durability comparable to hardened steel.
Embedded diagnostics and forensic traceability
Unlike conventional USB flash drives, Evikey NFC embeds an immutable internal black box that records security and operational events. This traceability can be consulted contactlessly via NFC using an Android device, without requiring the USB to be mounted by the operating system.
- Non-tamperable event logging of electrical, thermal, and security incidents.
- Self-diagnostic system reporting the operational health of the device.
- Tracking of flash memory write counts since first use, enabling objective assessment of NAND wear.
Impact on write-protection diagnosis
Because Evikey NFC eliminates most external causes of flash memory damage, any unexpected write-protection state can be analyzed with greater clarity. If a device becomes locked, the diagnostic process can quickly distinguish between:
- Write protection intentionally enforced by the Evikey NFC security model, or
- External or environmental factors unrelated to flash degradation.
Notably, the flash memory itself does not rely on traditional physical write-lock mechanisms, as access control is handled upstream through contactless authentication. This architectural choice removes an entire class of ambiguous failure states commonly encountered with standard USB drives.
As a result, Evikey NFC does not aim to unlock failing USB devices. Instead, it prevents most of the conditions that lead to irreversible firmware-level write protection and significantly simplifies diagnosis if a lock state occurs.
For readers interested in the technical foundations and concrete implementations of this architecture, the following official Freemindtronic resources provide detailed documentation:
- Evikey NFC technology for USB sticks — overview
- Evikey NFC features — hardware protections and access control mechanisms
- Evikey secure NFC USB drive — undetectable mode
Concrete implementations of this architecture are available as secure, contactless USB devices:
When recovery mechanisms reach their limits, resilient hardware design becomes the decisive factor.
Strategic Outlook
In 2024, a “write-protected USB” rarely represents an isolated malfunction. More often, it signals the visible edge of a deeper rule: a security policy, an integrity control, or a hardware fail-safe.
Therefore, the most effective response is not brute force. Instead, it relies on classification, data preservation, and disciplined operational hygiene. Once removable storage is treated as an asset with a defined lifecycle, the incident ceases to be surprising and becomes manageable.
This is why this Chronicle does not end with a fix, but with a boundary: a point where action stops and responsibility begins.
- 1
- 2