La Loi andorrane sur le double usage s’inscrit dans une refonte stratégique du contrôle des exportations. Face aux nouvelles menaces hybrides, elle établit un socle juridique fondé sur le droit douanier, la souveraineté technologique et l’alignement partiel sur l’UE. Identification EORI, conformité UE, et encadrement cryptologique deviennent des piliers de cette sécurité réglementaire.
Le contrôle des exportations de biens à double usage devient un pilier de la souveraineté technologique andorrane. Face à la complexité croissante des chaînes de valeur, de la cryptologie exportée et des réglementations extraterritoriales, l’Andorre anticipe ces défis par une réforme stratégique de son cadre douanier et réglementaire. Cette analyse juridique explore : ✔ Comment l’Andorre articule conformité UE et autonomie souveraine à travers la Llei 10/2025. ✔ Pourquoi le régime EORI et l’accord douanier Andorre–UE offrent un levier pour les exportations à contrôle stratégique. ✔ Comment structurer une doctrine andorrane du double usage, en cohérence avec le Règlement (UE) 2021/821. ✔ Quels sont les défis futurs : IA, cybersécurité matérielle, souveraineté des chaînes critiques.
À propos de l’auteur — Inventeur de technologies à double usage et fondateur de Freemindtronic Andorre, Jacques Gascuel développe des solutions de protection des données et de contre-espionnage à vocation civile et militaire. Il analyse ici les enjeux stratégiques de la loi andorrane sur le double usage dans une approche « privacy by design » conforme aux exigences réglementaires internationales.
Le Conseil Général d’Andorre a adopté la Llei 10/2025 le 13 mai 2025, ensuite publiée au BOPA n°68 du 4 juin 2025. Cette loi marque une étape déterminante dans l’évolution du droit douanier andorran, puisqu’elle vise à aligner la législation nationale sur le Code des douanes de l’Union européenne, tel qu’établi par le Règlement (UE) n°952/2013 du 9 octobre 2013 (EUR-Lex – CELEX:32013R0952). En remplaçant la Llei 17/2020, cette réforme introduit une architecture moderne de la régulation douanière. Elle comprend 296 articles répartis en neuf titres. Plus précisément, elle facilite les procédures douanières, renforce la numérisation des opérations, et, surtout, elle établit un cadre juridique robuste pour le contrôle des flux sensibles, notamment ceux relatifs aux biens à double usage. Pour plus d’informations officielles, les textes sont consultables ici : Ainsi, cette nouvelle législation positionne Andorre dans une logique de conformité renforcée et d’intégration réglementaire progressive avec l’Union européenne. Avant d’aborder les dispositions spécifiques à la Loi andorrane double usage, il est utile de passer en revue les points structurants du nouveau Codi de Duana qui renforcent l’efficacité et la transparence du système douanier andorran. Le Code redéfinit des notions clés pour une meilleure sécurité juridique : Poursuivons notre exploration de la Loi andorrane double usage en examinant désormais la structure financière et procédurale qui encadre les flux douaniers. Ce pilier réglementaire, loin d’être secondaire, permet d’assurer la sécurité des recettes publiques, tout en apportant de la prévisibilité et de la fiabilité aux opérateurs économiques. Ainsi, cette partie du nouveau Code met en place un triptyque cohérent : gestion de la dette douanière, mise en œuvre de garanties, et dynamique d’autorisations administratives. Ces éléments assurent une gouvernance rigoureuse des flux commerciaux à risques, notamment ceux liés aux technologies sensibles. La Llei 10/2025 introduit un mécanisme cohérent de calcul, de paiement et de remboursement des droits de douane. En outre, elle prévoit des règles précises en matière de dette douanière et exige, dans certains cas, la constitution de garanties financières par les opérateurs. Cette structuration vise à instaurer une logistique plus fluide tout en maintenant un haut niveau de surveillance. La nouvelle loi instaure un système structuré de demandes, traitements et délivrances d’autorisations douanières, essentiel pour garantir la sécurité juridique des opérateurs économiques. L’administration douanière peut délivrer des autorisations générales ou spécifiques selon le type d’opération et le niveau de risque associé. Un registre numérique centralisé recense désormais toutes les autorisations émises, assurant leur traçabilité et leur vérifiabilité. Le code impose un délai maximum de réponse pour éviter tout blocage administratif. Entrons désormais dans le cœur du dispositif lié aux biens à double usage, qui constituent un volet sensible de la Llei 10/2025. Texte de référence : Règlement (UE) 2021/821 Cette disposition est entrée en vigueur immédiatement après publication de la loi, soit le 5 juin 2025, conformément à sa disposition finale. Le Décret 207/2025, publié le 12 juin 2025, précise les formalités associées à cette autorisation. Texte officiel : BOPA Andorre – GR_2025_06_11_13_27_27 Ce texte prévoit que : Avant même l’entrée en vigueur de la Loi andorrane double usage, Freemindtronic a initié une démarche exemplaire dès 2021. En anticipant les obligations réglementaires, l’entreprise a structuré ses flux commerciaux sensibles dans un cadre éthique et juridique rigoureux. Freemindtronic a proposé une Charte éthique, soutenue par une documentation formalisée dès 2022, pour encadrer l’usage et l’exportation de ses technologies cryptographiques sensibles. Les mesures concrètes incluent : Afin d’assurer une conformité juridique complète à l’export des technologies sensibles, Freemindtronic s’est également appuyée sur les exigences françaises en matière de contrôle des moyens de cryptologie. Les dossiers doivent être envoyés à : Le formulaire principal, à savoir l’annexe I, est téléchargeable ici : formulaire PDF. Ce document inclut notamment : Grâce à cette rigueur, Freemindtronic a pu exporter légalement les modules DataShielder NFC HSM, avec la validation de son partenaire exclusif AMG Pro. Afin d’assurer une conformité juridique complète à l’export des technologies sensibles, Freemindtronic s’est également appuyée sur les exigences françaises en matière de contrôle des moyens de cryptologie. Les dossiers doivent être envoyés à : Le formulaire principal, à savoir l’annexe I, est téléchargeable ici : formulaire PDF. Ce document inclut notamment : Grâce à cette rigueur, Freemindtronic a pu exporter légalement les modules DataShielder NFC HSM Defense, avec la validation de son partenaire exclusif AMG Pro (site officiel). Alors que la mise en œuvre de la Loi andorrane double usage ne fait que commencer, les acteurs publics et privés peuvent jouer un rôle stratégique dans la diffusion des bonnes pratiques. Cette dynamique constitue une opportunité majeure pour structurer un écosystème vertueux d’accompagnement réglementaire et de sensibilisation des opérateurs économiques. En particulier, l’Andorre bénéficie d’un potentiel de co-construction entre institutions et entreprises innovantes, dans le respect de leurs prérogatives respectives. Il devient ainsi pertinent de développer des outils d’aide à la compréhension de la réglementation et d’offrir une information claire et structurée aux professionnels concernés. La réglementation andorrane sur les biens à double usage, bien qu’entérinée par le BOPA, souffre actuellement d’un manque de documentation appliquée. Aucun guichet d’information spécialisé, tutoriel administratif ou guide de conformité n’a encore été publié par les institutions publiques. S’appuyant sur son expérience réglementaire, Freemindtronic a amorcé la rédaction d’un guide pratique de conformité, co-marquable avec des entités telles que la Douane andorrane (lien officiel). Cette initiative vise à : En parallèle, Freemindtronic a publié plusieurs ressources accessibles en ligne au sujet de la règlementation international des produits double usage, notamment : Ces ressources se présentent comme des compléments informatifs fiables aux textes officiels.7. Panorama international et effet extraterritorial Le régime andorran de contrôle des exportations de biens à double usage s’inscrit dans un cadre réglementaire mondial, où chaque juridiction impose des normes spécifiques pour la régulation et la surveillance des flux commerciaux sensibles. En raison de son accord douanier avec l’Union européenne, l’Andorre bénéficie de particularités qui influencent son approche des exportations et des exemptions applicables. Cependant, les réglementations en vigueur dans les grandes puissances économiques – Union européenne, États-Unis, Royaume-Uni, Suisse, Pays du Commonwealth – exercent une influence sur les obligations des exportateurs andorrans. Cette dynamique se traduit par : Afin de comparer ces régulations et d’évaluer leur impact sur les échanges intra-UE, le tableau ci-dessous présente une synthèse des réglementations internationales, leurs dates d’entrée en vigueur et leurs implications pour l’Andorre. L’effet extraterritorial des réglementations américaines (EAR) et européennes (Règlement UE 2021/821) impacte la gestion des exportations depuis l’Andorre. Toutefois, grâce à l’Accord douanier de 1990, l’Andorre bénéficie d’une union douanière partielle avec l’UE, permettant aux produits industriels (chapitres 25 à 97 du Tarif douanier) de circuler librement une fois introduits dans la chaîne européenne, sans formalités supplémentaires. Ainsi, une analyse approfondie suggère qu’il est possible d’exporter des biens à double usage de l’Andorre vers l’Union européenne sans autorisation préalable, sous réserve des conditions suivantes : Cette singularité réglementaire différencie l’Andorre des États membres de l’UE, qui doivent appliquer des régimes stricts de contrôle des exportations. Toutefois, une vigilance accrue reste nécessaire, notamment vis-à-vis des évolutions législatives internationales qui pourraient renforcer les exigences douanières. La promulgation de la Loi andorrane sur les biens à double usage (Llei 10/2025) marque une évolution majeure dans l’architecture normative du pays, en posant les premières pierres d’un contrôle export encadré. Cette section analyse la portée matérielle, les acteurs institutionnels impliqués et les effets concrets pour les opérateurs économiques, dans un contexte d’intégration progressive au dispositif européen. Le Règlement (UE) 2021/821 permet en général la libre circulation des biens à double usage à l’intérieur du marché intérieur de l’UE, à l’exception de produits particulièrement sensibles figurant à l’Annexe IV . Cela signifie que, dès lors qu’un bien fait partie de l’UE, sa ré-exportation vers un autre État membre ne nécessite pas d’autorisation supplémentaire, sauf cas particuliers. L’Accord du 1990 établit une union douanière partielle entre la Principauté d’Andorre et l’Union Européenne, couvrant les chapitres 25 à 97 du Tarif douanier commun. Cet accord permet une libre circulation des marchandises, supprimant les barrières tarifaires pour les produits concernés. D’après les analyses du CEPS, les produits préalablement importés en Andorre depuis un État tiers et bénéficiant d’un numéro EORI peuvent circuler librement dans l’UE sans formalités additionnelles, à l’exception des produits du tabac, qui restent soumis à des régulations spécifiques. Une conclusion à vérifier est de savoir si sur la base de l’accord douanier et du règlement européen, il devient possible d’exporter des biens à double usage d’Andorre vers l’UE sans autorisation préalable andorrane, sous certaines conditions : Si ces conditions sont remplies, cela représenterait une singularité notable par rapport aux réglementations des États membres de l’UE. La réforme douanière portée par la Llei 10/2025 et son décret d’application offre aux industriels andorrans des conditions opérationnelles stratégiques dans un environnement fortement régulé à l’échelle internationale. À ce titre, plusieurs dispositifs cryptographiques « made in Andorra » de la gamme DataShielder NFC HSM ou PGP HSM, bien qu’ils relèvent de la catégorie 5, partie 2 du Règlement (UE) 2021/821, ne sont pas inclus dans l’Annexe IV et bénéficient donc pleinement de cette exemption européen stipulé par cette nouvelle réglementation Andorran : À titre d’illustration, voici deux modèles de documents inspirés des annexes du Décret 207/2025 pour aider à la mise en conformité immédiate. DESTINATAIRE : Date, lieu, cachet et signature DESTINATAIRE : Je m’engage à : Date, lieu, signature, cachet, fonction du signataire Alors que l’Andorre a récemment renforcé son cadre législatif avec la Loi andorrane sur les biens à double usage, notamment à travers l’article 267, alinéa 3, lettre f de la Llei 10/2025, subsiste une zone grise préoccupante en matière de sanctions et d’embargos. En effet, bien que cette loi définisse les conditions d’autorisation d’exportation pour les biens sensibles cryptographiques, elle ne prévoit ni mécanisme de contrôle a posteriori, ni dispositif répressif autonome en cas de manquement aux obligations qu’elle instaure. Dans les juridictions européennes et nord-américaines, une telle carence réglementaire donnerait lieu à un encadrement détaillé, à la fois administratif et pénal. Par exemple, le règlement (UE) 2021/821 prévoit des procédures claires pour la répression des violations, tandis que les États-Unis disposent d’un arsenal robuste via l’EAR et les sanctions OFAC. En Suisse et en France, l’exportation non autorisée de technologies à double usage est passible de sanctions sévères, incluant la responsabilité pénale des dirigeants. À l’inverse, le cadre juridique export Andorre souffre encore de lacunes structurelles en matière de réponse aux infractions. Cette absence d’un régime de sanctions explicite ouvre un vide réglementaire pouvant exposer le pays à des risques d’abus, mais également à une remise en cause de sa coopération internationale, en particulier dans le contexte du règlement européen susmentionné. Face aux lacunes identifiées dans le régime actuel, une consolidation progressive de la gouvernance nationale andorrane du contrôle export apparaît souhaitable. Celle-ci pourrait utilement s’inspirer des dispositifs mis en place en France et en Espagne, sans transposition mécanique, mais dans le respect de la souveraineté juridique du pays. Exemple espagnol : La Secretaría de Estado de Comercio (SECOMS) et la Junta Interministerial Reguladora del Comercio Exterior de Material de Defensa y de Doble Uso (JIMDDU) assurent une coordination interministérielle centralisée pour statuer sur les exportations de matériel de défense et à double usage. 🔹 SECOMS : Chargée de l’application des régulations sur les exportations et importations sensibles. ➡ Ministère de l’Industrie, du Commerce et du Tourisme 🔹 JIMDDU : Organe intergouvernemental statuant sur les exportations stratégiques. ➡ Décret officiel BOE 2023-21672 🔹 Rapport semestriel sur les exportations de matériel de défense et biens à double usage : ➡ Statistiques et données (2024) Dans cette optique, l’Andorre pourrait instaurer un Comité intergouvernemental andorran du double usage, réunissant : Ce comité aurait pour mandat d’élaborer une doctrine d’exportation souveraine, d’adopter un décret d’application autonome pour définir les sanctions et contrôles, et de coordonner la coopération avec les partenaires européens. Cette inspiration trouve une légitimité particulière dans le fait que les deux États de référence – France et Espagne – sont également co-princes constitutionnels d’Andorre. Leur influence institutionnelle et leur ancrage historique confèrent à leurs pratiques un statut de référence compatible avec l’ordre juridique andorran. En parallèle de ces évolutions institutionnelles, les entreprises andorranes opérant dans les secteurs sensibles peuvent immédiatement renforcer leur conformité en adoptant les mesures suivantes : À la lumière des dispositions introduites par la Loi andorrane sur les biens à double usage et son décret d’application, il apparaît que le législateur andorran a franchi une étape structurante vers une convergence avec les standards européens, tout en préservant la spécificité juridique du Principat d’Andorra. L’articulation entre le droit interne, le droit de l’Union européenne, et les régimes extraterritoriaux internationaux (US EAR, UK, Wassenaar) appelle désormais une vigilance constante des opérateurs économiques, afin de garantir la conformité dynamique de leurs pratiques exportatrices. En ce sens, la trajectoire anticipatrice et éthique de Freemindtronic — illustrée par des démarches documentées et une doctrine de conformité consolidée — constitue un modèle transposable. Elle démontre que l’initiative privée peut contribuer utilement à l’édification d’un régime juridique cohérent, au bénéfice de l’État et des acteurs industriels. Il incombe désormais aux autorités andorranes compétentes de poursuivre l’effort d’accompagnement normatif, notamment par la production de doctrines administratives, de guides officiels, et par la mise en place de formations et de guichets spécialisés. En parallèle, les entreprises doivent institutionnaliser une veille réglementaire intégrée, articulée avec des matrices d’impact extraterritorial, pour faire de la conformité export un levier stratégique à part entière. Ainsi, la mise en œuvre effective et fluide de ce régime repose sur une synergie entre droit, technologie et responsabilité partagée. Elle trace les contours d’un nouveau pacte normatif andorran, fondé sur la transparence, la sécurité juridique et l’ambition d’un modèle économique ouvert mais rigoureusement encadré. La réforme du Codi de Duana par la Llei 10/2025, del 13 de maig, couplée au Règlement d’exécution sur les exportations de biens à double usage (Decret 207/2025), offre l’occasion inédite pour le Principat d’Andorra de structurer une doctrine propre en matière de contrôle stratégique, alignée mais différenciée des régimes européens (UE), français, espagnol et suisse. France : le régime français repose sur le Code de la défense, l’arrêté du 8 juillet 2015 pour les AIMG, et l’arrêté du 2 juin 2014 pour les LEMG, combinés à des décisions ponctuelles de suspension de dérogations. Il distingue rigoureusement les matériels classifiés (cat. ML) et les biens de double usage (cat. DU), et impose des procédures complexes et centralisées, y compris pour les importations temporaires de matériels à des fins d’exposition. Espagne : sous l’égide du Real Decreto 679/2014, l’Espagne applique également le Règlement (UE) 2021/821, avec une interprétation administrative souvent conservatrice. La classification en matière de cryptologie ou de composants électroniques est systématique, et l’exportation vers les pays tiers (hors UE) fait l’objet d’un suivi renforcé. Suisse : bien que non membre de l’UE, la Suisse adopte une politique d’équivalence fondée sur la Güterkontrollverordnung (GKV) et l’Ordonnance sur le matériel de guerre (OMG). L’autorité SECO supervise un régime fluide mais rigoureux, avec une emphase sur la transparence commerciale et la conformité extraterritoriale. Union européenne : le Règlement (UE) 2021/821 (version consolidée : eur-lex.europa.eu/legal-content/FR/TXT/?uri=CELEX:32021R0821) pose un socle harmonisé sur la base des listes de contrôle, des critères de sécurité internationale, et de l’analyse des risques pays. Enjeux spécifiques à Andorre : vers une doctrine nationale du double usage La Charte Éthique entre Freemindtronic et le Gouvernement d’Andorre préfigure cette doctrine, en intégrant les principes de transparence, non-prolifération, développement durable et souveraineté juridique. Elle constitue une base pertinente pour étendre la régulation aux segments technologiques émergents, comme les systèmes d’authentification distribuée, les moyens cryptologiques à usage cyber-défense, ou encore les technologies fondées sur l’ADN digital. L’UE envisage d’étendre le champ d’application du régime dual-use à des technologies critiques telles que l’intelligence artificielle, la cybersécurité et la chaîne de blocs, dans le cadre de la stratégie de sécurité économique européenne (Communication COM(2023) 249 final). Andorre devra anticiper ces mouvements pour maintenir l’équivalence règlementaire. La dynamique actuelle engage le pays à structurer une capacité nationale de doctrine, de supervision et d’innovation réglementaire sur le double usage, incluant :
Analyse juridique approfondie loi andorrane double usage Llei 10/2025 du Codi de Duana d’Andorre
1. Analyse stratégique de la Loi andorrane double usage : réforme du Codi de Duana 2025
2. Éléments structurants du nouveau Code douanier andorran
2.1 Extension du périmètre douanier
2.2 Précisions terminologiques essentielles
Terme
Définition (selon la loi)
Statut douanier
Caractère communautaire ou non d’une marchandise
Mise en libre pratique
Régime permettant l’entrée sur le marché andorran
Représentant douanier
Mandataire habilité à accomplir les formalités douanières au nom d’un tiers
2.3 Dématérialisation des procédures
3. Système andorran de droits, garanties et autorisations : vers un contrôle performant
3.1 Encadrement des dettes douanières et des garanties
3.2 Régimes douaniers économiques : fluidité sous conditions
3.3 Gestion des autorisations douanières : un tournant réglementaire
4. Réglementation spécifique de la Loi andorrane double usage
4.1 Article 267.3.f : cadre juridique essentiel
4.2 Décret d’application 207/2025 : modalités pratiques
4.3 Freemindtronic : un exemple de conformité proactive
4.4 Documentation de conformité internationale : modèle français et procédure ANSSI
4.4 Documentation de conformité internationale : modèle français et procédure ANSSI
5. Coopération andorrane et ressources pédagogiques : une ouverture stratégique
5.1 Absence de guides institutionnels : un vide à combler
5.2 Contribution de Freemindtronic : contenu pédagogique, guide pratique, et sensibilisation
5.3 Outils numériques disponibles
Alignement du régime andorran sur les réglementations internationales
Cadre réglementaire des principales juridictions
Juridiction
Réglementation
Date d’entrée en vigueur
Date de durcissement
Particularités intra-UE / nationales
Union européenne
Règlement (UE) 2021/821
Version consolidée EUR-Lex
Guide DGE – Biens à double usage
Note DS Avocats – Réforme 20219 septembre 2021
2022 (durcissement post-invasion Ukraine)
Régime harmonisé applicable dans tous les États membres :
• 4 types d’autorisations : générale, globale, individuelle, nationale
• Contrôle des exportations, du courtage, de l’assistance technique, du transit et des transferts
• Annexe I : liste commune des biens à double usage (mise à jour annuelle)
• Annexe IV : biens soumis à autorisation même en transfert intra-UE
• Clause attrape-tout (article 4) pour les utilisations militaires ou de prolifération
• Autorités nationales compétentes + coordination via le groupe Dual-Use de la Commission
États-Unis (EAR)
15 CFR Part 730+
Table des matières EAR (BIS)
Bureau of Industry and Security (BIS)
Formulaire 748-P (Demande de licence)
Checklist d’utilisation finale13 septembre 1979
2022 (Chine, Russie)
Régime extraterritorial renforcé :
• Règle de dé-minimis (<25 % contenu américain)
• Règle du produit direct étranger (FDP rule)
• Licence requise selon ECCN (Export Control Classification Number)
• Sanctions croisées OFAC/BIS
• Contrôles accrus sur IA, semi-conducteurs, cybersécurité et cryptographie
Suisse
Ordonnance OCB RS 946.202.1
Portail SECO – Contrôle des exportations
Annexes techniques (OCB)
Formulaires de demande de licence1er juillet 2012
2023–2025 (mise à jour des annexes 1 à 6)
Régime aligné sur les standards UE et Wassenaar :
• Autorité compétente : SECO (Secrétariat d’État à l’économie)
• Licences obligatoires pour les biens listés dans les annexes 1 à 6
• Mise à jour annuelle des annexes techniques (dernière : 1er mai 2025)
• Contrôle des exportations, du courtage, du transit et de l’assistance technique
• Coopération renforcée avec l’UE, tout en conservant une autonomie réglementaire
Israël
Portail Export Control – Ministère de l’Économie
Export Control Agency – Dual Use
DECA – Defence Export Control Agency (Ministère de la Défense)
Formulaires de demande de licence2016
2023 (renforcement IA, cybersécurité)
Régime dual coordonné par deux autorités :
• Ministère de l’Économie : contrôle des biens à double usage civil
• Ministère de la Défense (DECA) : contrôle des biens militaires et sensibles
• Licence obligatoire pour cryptologie, IA, cybersécurité, drones, optronique
• Alignement partiel sur les régimes Wassenaar, MTCR, NSG
• Sanctions civiles et pénales en cas de non-conformité
• Re-exportation également soumise à autorisation israélienne
Royaume-Uni
Export Control Order 2008
UK Export Control Guidance
Demande de licence via SPIRE
Amendement 2024 (NTE 2024/04)17 décembre 2008
2022–2024 (alignement UE/USA, technologies émergentes)
Régime autonome post-Brexit :
• Plateforme SPIRE obligatoire pour toute demande
• Contrôle des biens militaires et à double usage
• Nouvelles entrées 2024 : quantum, cryogénie, semi-conducteurs, IA
• Alignement sur les listes Wassenaar, MTCR, NSG, AG
• Autorité compétente : Export Control Joint Unit (ECJU)
Maroc
Loi n°42‑18
Décret n°2.21.346
Arrêté n°2353‑23
Arrêté n°2529‑24
Formulaire de licence
Certificat d’utilisation finale
Portail MCINET17 décembre 2020
1er janvier 2025
Licences obligatoires dès 2025. Phase transitoire de 3 mois.
BO n°6944
Suivi douanier via ADIL.
Ukraine
Décret n°549-2012
Texte consolidé (portail Rada)
Ministère de l’Économie – Contrôle des exportations
Service des douanes d’Ukraine27 juin 2012
2022 (durcissement post-invasion)
Régime strict de contrôle des exportations :
• Licence obligatoire pour les biens à double usage
• Alignement progressif sur les listes UE/USA
• Coopération renforcée avec les partenaires occidentaux
• Autorité compétente : Département du contrôle des exportations (Minéconomie)
Russie
Portail officiel russe
Note DGDDI (FR) – Mesures restrictives
Guide DGE – Sanctions Russie
Conseil de l’UE – Sanctions contre la Russie2003
2022 (invasion de l’Ukraine)
Régime de contrôle stratégique renforcé :
• Interdiction d’exportation de biens à double usage, technologies critiques, IA, semi-conducteurs, cryptographie
• 16 paquets de sanctions UE depuis 2022
• Coordination G7 / GECC pour limiter l’accès aux technologies occidentales
• Contrôle douanier renforcé, licences suspendues ou refusées
• Autorité compétente : Service fédéral russe du contrôle technique et des exportations (FSTEC)
Chine
MOFCOM – Loi sur le contrôle des exportations (2020)
Portail MOFCOM (FR)
Liste des biens à double usage (version chinoise)
Administration générale des douanes (GACC)1er décembre 2020
2023 (durcissement IA, semi-conducteurs)
Régime centralisé et strict :
• Contrôle des exportations via MOFCOM et GACC
• Restrictions sur IA, cybersécurité, quantum, semi-conducteurs
• Liste de contrôle nationale indépendante, partiellement alignée Wassenaar
• Licences obligatoires pour les technologies sensibles
• Sanctions administratives et pénales en cas de non-conformité
Singapour
SG Export Controls
Liste des biens contrôlés
Singapore Strategic Goods Control Act (SGCA)
Portail Strategic Goods Control – Singapore Customs2003
2022 (renforcement IA, semi-conducteurs)
Régime fondé sur le Strategic Goods (Control) Act (SGCA) :
• Autorité compétente : Singapore Customs
• Licence obligatoire pour les biens listés dans la liste des biens stratégiques
• Alignement sur les régimes Wassenaar, NSG, MTCR, AG
• Contrôle renforcé sur IA, cybersécurité, électronique avancée
• Notification préalable ou licence requise selon la sensibilité du bien
Brésil
MDIC – Exportação de Produtos Controlados
Portail officiel du MDIC
Documents requis (formulaires, certificats)
SISCOMEX – Portail unique du commerce extérieur2011
2024 (renforcement technologique)
Régime de contrôle géré par le Ministério do Desenvolvimento, Indústria, Comércio e Serviços (MDIC) :
• Licence obligatoire via la plateforme SISCOMEX
• Alignement partiel sur les régimes MTCR, NSG et Wassenaar
• Contrôle renforcé sur les technologies sensibles (cybersécurité, IA, électronique)
• Autorité compétente : Secrétariat du Commerce Extérieur (SECEX)
• Procédures électroniques centralisées, traçabilité des exportations sensibles
Australie (Commonwealth)
Export Control Act 2020
DAFF – Export legislation improvements
Department of Defence – Export Controls
Demandes de permis DEFENCE EXPORT CONTROL OFFICE (DECO)1er janvier 2021
2023–2024 (réforme administrative et technologique)
Régime dual :
• Export Control Act 2020 pour les produits agricoles, administré par le DAFF
• Defence Trade Controls Act 2012 pour les biens militaires et à double usage, administré par le DECO
• Contrôle des technologies sensibles (IA, quantum, cybersécurité)
• Licences obligatoires pour exportation, courtage, assistance technique
• Alignement sur les régimes Wassenaar, MTCR, NSG, AG
Andorre
Llei 10/2025
Décret 207/2025
Formulaire de demande d’autorisation
Departament de Duana i Comerç Exterior13 mai 2025
1er juillet 2025
Alignement partiel sur le Règlement (UE) 2021/821 dans le cadre de l’Accord Douanier Andorre–UE.
Licence préalable obligatoire pour cryptographie, IA et technologies sensibles.
Traçabilité exigée – contrôle douanier via identifiant EORI. Texte consolidé publié au BOPA (Butlletí Oficial del Principat d’Andorra).Effet extraterritorial et singularité andorrane
6. Cadre juridique andorran des biens à double usage
6.1 Circulation libre au sein de l’UE
6.2 Andorre et l’Union Douanière Partielle
6.3 Implications pour les biens à double usage
Accord de 1990 entre Andorre et l’UE : EUR-Lex – Accord douanier Andorre-UE
Informations sur le numéro EORI : Douane Europe – EORI6.4. Bénéfices directs pour les industriels andorrans du secteur dual et défense
Impacts concrets :
6.5 Illustrations pratiques : modèles de conformité
Modèle A – Formulaire de demande d’autorisation d’exportation de biens à double usage
Duana Andorrana – Despatx Central de Duana
Av. Fiter i Rossell, núm. 2, bloc A, Escaldes-Engordany, AD700
[ ] Exportation ponctuelle – Date estimée : ____
[ ] Exportation récurrente – Période : du ____ au ____
Nom/Raison sociale : ____
NRT : ____
Nom/Raison sociale : ____
Adresse complète : ____
Activité économique liée aux biens : ____
Site web : ____
Nom/Raison sociale : ____
Adresse complète : ____
Activité : ____
Site web : ____
Code TARIC (10 chiffres) : ____
Description : ____
Quantité/Unité : ____
Valeur (€) : ____
Pays d’origine : ____
Pays de provenance : ____
Date du contrat : ____
Code du régime douanier : ____
Usage final détaillé : ____
Documents joints : [ ] Déclaration de destination finaleModèle B – Déclaration de destination finale
Duana Andorrana – Despatx Central de Duana
Av. Fiter i Rossell, núm. 2, bloc A, Escaldes-Engordany, AD700
Nom/Raison sociale : ____
NRT : ____
Nom/Raison sociale : ____
Adresse complète : ____
Description : ____
Quantité/Unité : ____
Activité économique de l’acquéreur : ____
Utilisation/destination des biens : ____
– Utiliser les biens uniquement selon l’usage déclaré ;
– Ne pas les réexporter sans autorisation des autorités du pays de destination.6.6. Sanctions, embargos et vide réglementaire en Andorre
6.7. Vers une gouvernance andorrane du double usage : inspiration européenne et cadre opérationnel
Le contrôle des biens à double usage en France est assuré par la Sous-Direction du Commerce International des Biens Stratégiques (SBDU), rattachée à la Direction Générale des Entreprises (DGE). Cet organisme délivre les autorisations d’exportation en coordination avec la Douane et le Ministère des Armées via le Service de l’Information et de la Documentation (SID) pour un suivi renforcé post-exportation.🔹 SBDU : Autorité compétente en matière de contrôle et délivrance des licences.
➡ Ministère de l’Économie – Biens à double usage https://www.entreprises.gouv.fr/fr/biens-double-usage🔹 Coordination avec la Douane : Suivi des flux commerciaux sensibles et vérification de conformité.
➡ Direction Générale des Douanes et Droits Indirects (DGDDI) https://www.douane.gouv.fr/🔹 Ministère des Armées – SID : Analyse des risques et contrôle stratégique des exportations.
➡ Service de l’Information et de la Documentation (SID) https://www.defense.gouv.fr/
Actions pratiques à mettre en œuvre dès à présent
7. Portée normative et perspectives d’application
8. Approche comparative et prospective : vers une doctrine andorrane du double usage
Comparaisons doctrinales et cadres juridiques
Perspectives d’évolution réglementaire
Défis futurs et souveraineté technologique andorrane
Glossaire des sigles et termes spécialisés
The .NET DevExpress Framework is more than a UI toolkit—it is a security-driven solution designed to combat modern cyber threats. With increasing attacks targeting authentication systems, UI vulnerabilities, and APIs, developers need robust security architectures that seamlessly integrate zero-trust principles, encryption, and multi-factor authentication.
– Executive Summary
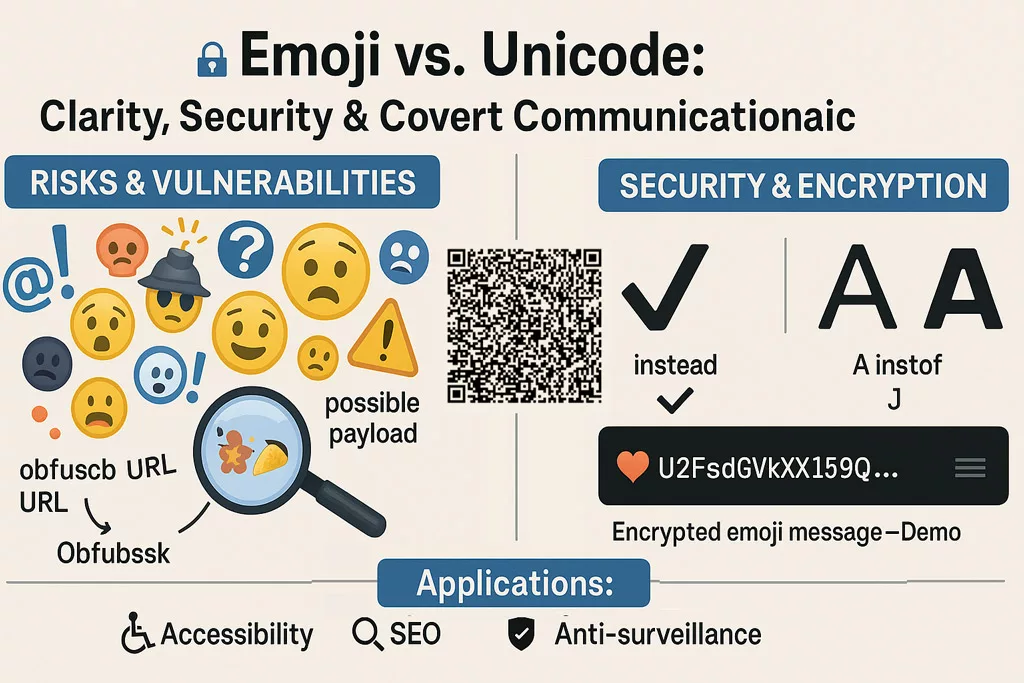
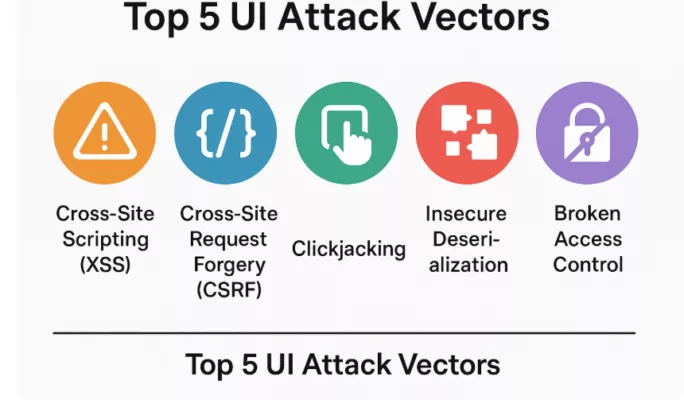
Cybersecurity in UI development has reached a critical juncture. With XSS attacks, SQL injection, and credential hijacking becoming more sophisticated, relying on traditional authentication methods is no longer enough. This article examines: ✔ How cybercriminals exploit UI vulnerabilities to compromise sensitive data. ✔ Why DevExpress integrates advanced security features to defend against modern threats. ✔ How developers can enforce zero-trust security models for UI frameworks. ✔ The future of UI security, driven by AI threat detection and hardware-based authentication.
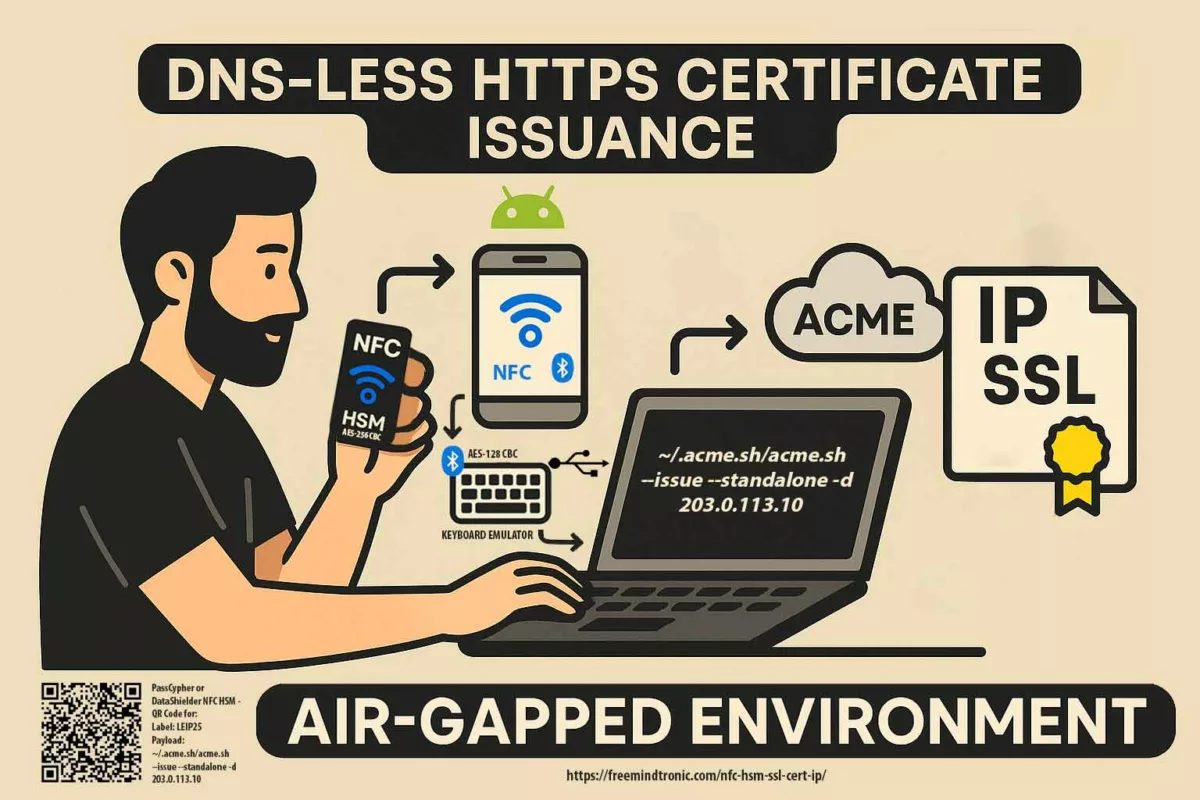
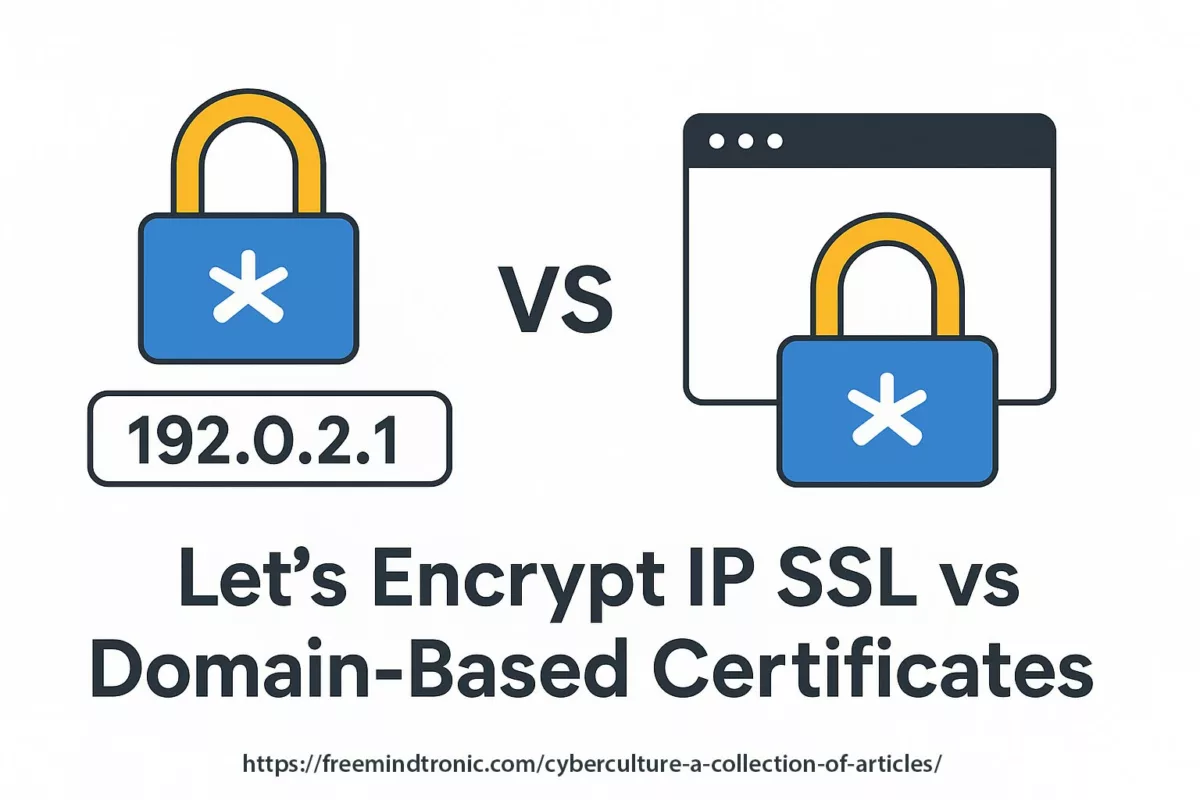
About the Author – Jacques Gascuel As the inventor of several security technologies and founder of Freemindtronic Andorra, Jacques Gascuel explores how cyberattacks target UI vulnerabilities, identity systems, and APIs in the modern threat landscape. This article reflects his ongoing work in developing privacy-by-design technologies that empower users to regain control over their digital interactions.
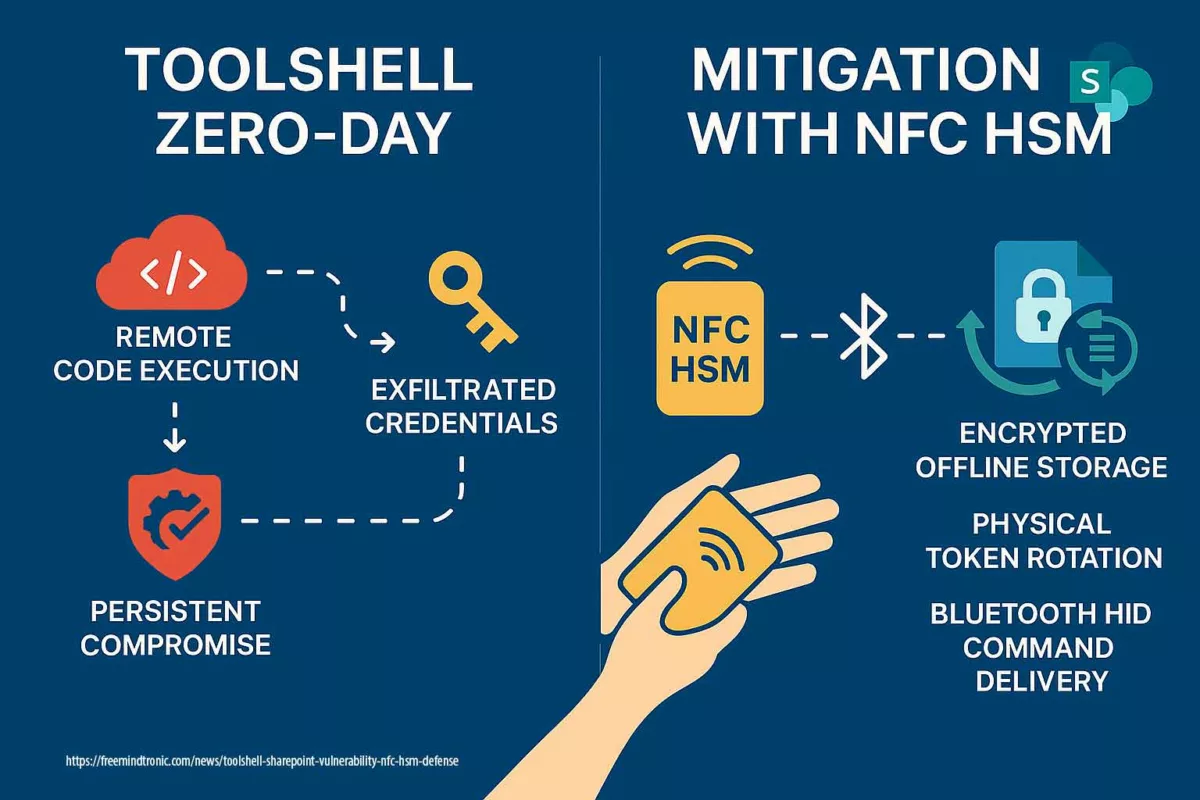
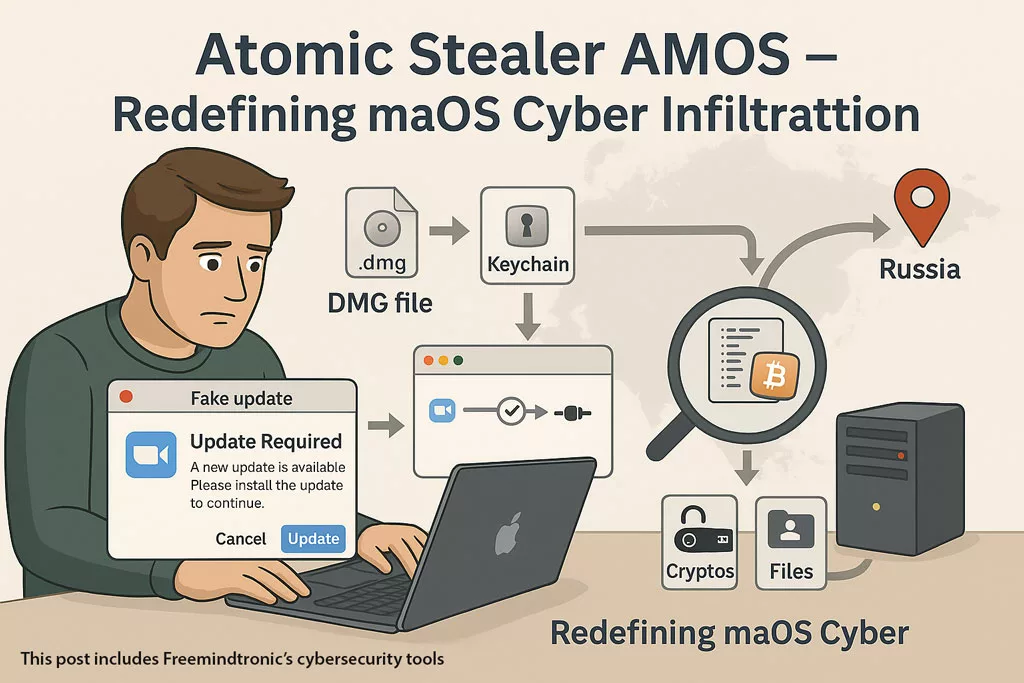
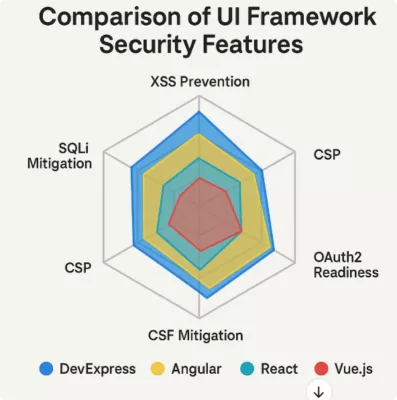
With cyber threats becoming more complex and pervasive, developers must rethink security beyond traditional defenses. A decade ago, UI security focused primarily on password complexity. Today, cybercriminals exploit front-end vulnerabilities, intercept API data, and bypass multi-factor authentication using AI-assisted attacks. As a result, secure application development requires a multi-layered defense, incorporating encryption, identity validation, and adaptive access control. The user interface (UI) has become a strategic entry point for cybercriminals. As applications shift toward rich, client-side logic with asynchronous API calls, attackers now bypass conventional perimeter defenses by targeting the visual and interactive surface of applications. Today’s most dangerous threats exploit weak client-side validation, misconfigured API endpoints, and session management flaws. Below are the most prevalent attack vectors used to compromise modern web UIs: ☑️ UI Threats Explained: XSS (Cross-Site Scripting): Malicious JavaScript injected into the UI to hijack user sessions and perform unauthorized actions. CSRF (Cross-Site Request Forgery): Tricks a legitimate user into unknowingly executing actions in a different security context. Clickjacking: Conceals UI elements under deceptive overlays to trick users into clicking harmful links. The DevExpress UI Framework addresses these threats through pre-validated components, hardened input controls, and secure API binding. ✦ Limited third-party plugin security ✦ Risk of outdated dependencies ✦ High dependency on third-party libraries ✦ Vulnerability risks from package updates ✦ XSS vulnerabilities from unsafe prop injection ✦ Uncontrolled component re-rendering ✦ Limited enterprise security options ✦ Potential validation gaps in directives With cyber threats becoming more complex and pervasive, developers must rethink security beyond traditional defenses. A decade ago, UI security focused primarily on password complexity. Today, cybercriminals exploit front-end vulnerabilities, intercept API data, and bypass multi-factor authentication using AI-assisted attacks. As a result, secure application development requires a multi-layered defense, incorporating encryption, identity validation, and adaptive access control. In sectors such as defense, finance, healthcare, or critical infrastructure, user interface (UI) security must comply with strict regulatory requirements. When deploying applications built with the .NET DevExpress Framework, it becomes crucial to choose tools and architectures that are not only technically robust, but also fully compliant with international legal standards. ✅ Regulatory Readiness Highlights: PassCypher HSM PGP and the DataShielder NFC HSM ecosystem ensure that your .NET DevExpress Framework applications meet today’s most demanding compliance, privacy, and sovereignty requirements—without compromising usability or integration capabilities. The user interface (UI) has become a strategic entry point for cybercriminals. As applications shift toward rich, client-side logic with asynchronous API calls, attackers now bypass conventional perimeter defenses by targeting the visual and interactive surface of applications. In environments built with the .NET DevExpress Framework, these risks are particularly relevant, as the high interactivity of components can expose vulnerabilities if not properly secured. Today’s most dangerous threats exploit weak client-side validation, misconfigured API endpoints, and session management flaws. Below are the most prevalent attack vectors used to compromise modern web UIs: ☑️ UI Threats Explained: XSS (Cross-Site Scripting): Malicious JavaScript injected into the UI to hijack user sessions and perform unauthorized actions. CSRF (Cross-Site Request Forgery): Tricks a legitimate user into unknowingly executing actions in a different security context. Clickjacking: Conceals UI elements under deceptive overlays to trick users into clicking harmful links. The .NET DevExpress Framework addresses these threats through pre-validated components, hardened input controls, and secure API binding. Its architecture allows developers to enforce strong client-side policies while maintaining high-performance and interactive user interfaces — a critical advantage in modern threat landscapes. In the sections that follow, we explore a range of advanced UI security paradigms specifically tailored to the .NET DevExpress Framework. First, we introduce foundational principles through comparative analysis, then progressively transition to hands-on demonstrations involving secure interface development. This includes practical use cases featuring encryption with PassCypher HSM PGP and air-gapped authentication with DataShielder NFC HSM devices. Moreover, we examine real-world vulnerabilities and provide mitigation strategies adapted to cloud, serverless, and edge environments. Ultimately, this collection of modules aims to guide developers, architects, and cybersecurity professionals in fortifying front-end resilience, improving authentication workflows, and integrating zero-trust architectures—all critical aspects for those seeking robust, future-proof UI security within enterprise-grade .NET DevExpress applications. DevExpress offre une approche plus robuste contre les attaques XSS et les injections SQL grâce à des composants pré-validés côté serveur. Try these best practices with live examples: DevExpress integrates security-first principles across ASP.NET Core, Blazor, and .NET MAUI, ensuring UI components are hardened against attacks. Key security enhancements include: PassCypher HSM PGP is the world’s first hybrid Hardware Security Module combining offline, passwordless authentication with advanced encryption containers (PGP AES-256 CBC) and a segmented key architecture. Unlike traditional HSMs, it merges physical isolation with software cryptography in a sovereign, tamper-resistant system. It supports OTP (TOTP/HOTP) auto-injection, sandboxed credential workflows, and real-time PIN management, making it ideal for securing UI components built with the .NET DevExpress Framework. ⚠️ Immune to the CLOUD Act and external surveillance, PassCypher is designed for the most demanding use cases—defense, critical infrastructure, classified systems—by offering post-quantum resilient protection today, without relying on future PQC standards. Not available Supported Supported Not available Not available Not available Requires server Supported Supported Not available Not available Not available Hybrid HSM, offline-native Supported Multi-Factor Authentication Auto-injected TOTP/HOTP Post-Quantum Ready * Fully serverless A military-grade classified .NET DevExpress Framework-based dashboard requires fully offline access control without risk of credential exposure. Solution: PassCypher HSM PGP + DataShielder NFC HSM Not available Supported Supported Not available Not available Not available Requires server Supported Supported Not available Not available Not available Hybrid HSM, offline-native Supported Multi-Factor Authentication Auto-injected TOTP/HOTP Post-Quantum Ready * Fully serverless “We implemented a Zero Trust UI using DevExpress Role-Based Access Control combined with server-side validation. The biggest challenge was API session hardening.” – Lead Engineer, FinTech Startup “The most common mistake? Relying on client-side MFA enforcement. With DevExpress, we moved it entirely server-side.” – Cybersecurity Architect Best practices include isolating UI logic from identity services and implementing strict CORS & RBAC. To mitigate modern security threats, DevExpress and cybersecurity experts recommend: 🛡 Hardware Security Modules (HSMs) – Protecting cryptographic keys from software-based exploits. 🛡 AI-Driven Threat Detection – Identifying malicious behaviors using anomaly-based analysis. 🛡 Secure API Gateway with Rate-Limiting – Preventing denial-of-service attacks. ☑️ Key Security Mechanisms: Integrating these with the DevExpress Framework ensures your UI resists injection-based exploits and access control bypass attempts. For developers seeking maximum UI security and data sovereignty, DataShielder HSM PGP offers a breakthrough: PGP-grade encryption and signature workflows directly within the browser, fully offline and serverless. DataShielder enables a sovereign Zero Trust architecture with quantum-resilient cryptography, ideal for air-gapped or critical systems using DevExpress-based interfaces. Learn more about DataShielder HSM PGP Data Encryption By 2030, UI frameworks will be self-healing, capable of automatically mitigating threats before they escalate: As cyber threats evolve, DevExpress-compatible platforms must adopt proactive architectures to remain resilient. The landscape of UI security is shifting rapidly, and developers cannot afford to be passive observers. Implementing DevExpress security features, enforcing Zero Trust authentication, and staying ahead of AI-assisted cyber threats will shape the resilience of tomorrow’s applications. Actions to take now: Get started with security-driven UI development: DevExpress security solutions For projects demanding advanced physical security and air-gapped compatibility, the DataShielder NFC HSM Starter Kit provides a sovereign, offline solution for encryption, authentication, and credential protection. ☑️ What is an NFC HSM? • NFC HSM: A tamper-proof, contactless device storing cryptographic secrets offline. • Hardware-level security: All encryption, decryption, and authentication are performed inside the device. • No data exposure: Secrets are never exposed to the OS, browser, or any connected software. This architecture ensures full offline cryptographic isolation—ideal for DevExpress UI integration in hostile environments. ☑️ Segmented Key System Explained • Key splitting: Encryption keys are broken into multiple independent parts. • Distributed trust: Each segment is useless alone, eliminating single points of failure. • Quantum resilience: Designed to resist post-quantum and brute-force attacks. This patented technique enhances confidentiality and mitigates future-proof threats in DevExpress-integrated infrastructures. This patented anti-espionage technology was developed and manufactured in Europe (France / Andorra), and supports both civilian and military-grade use cases. The optional Bluetooth Keyboard Emulator ensures air-gapped usability, bypassing vulnerable OS environments via direct wireless input from an Android NFC device. Learn more about DataShielder NFC HSM Starter Kit
.NET DevExpress Framework: Reinventing UI Security in an Age of Cyber Threats
Table of Contents
– Rethinking Security in UI Frameworks
– Security in UI Frameworks
– Cyber Attacks Targeting UI and Authentication Systems
– DevExpress vs Other UI Frameworks: A Security Comparison
– Advanced UI Security Paradigms Compared
– Interactive Security Challenge
– Future of Cybersecurity in UI Development
– Next Steps for DevelopersRethinking Security in UI Frameworks
Cyber Attacks Targeting UI and Authentication Systems
Attackers now bypass conventional security layers using targeted exploits such as:
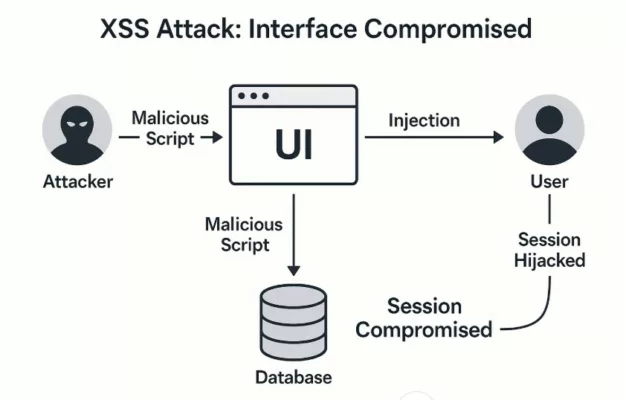
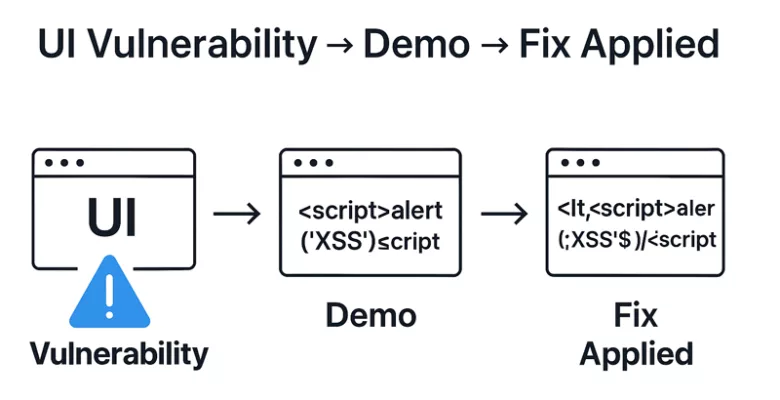
A visual breakdown of a Cross-Site Scripting (XSS) attack, showing how an injected script compromises both the UI and the user’s session.DevExpress vs Other UI Frameworks: A Security Comparison
Framework
Security Features
Known Vulnerabilities
DevExpress
Angular
React
Vue.js
Rethinking Security in UI Frameworks
🛡 Compliance Shield for .NET DevExpress Framework
Cyber Attacks Targeting UI and Authentication Systems
Attackers now bypass conventional security layers using targeted exploits such as:
DevExpress vs Other UI Frameworks: A Security Comparison
Advanced UI Security Paradigms Compared
Hands-On: Securing a DevExpress UI in .NET
Interactive DevExpress UI Security Challenge for .NET Interface Developers
Fortifying UI Security in .NET User Interfaces Built with DevExpress
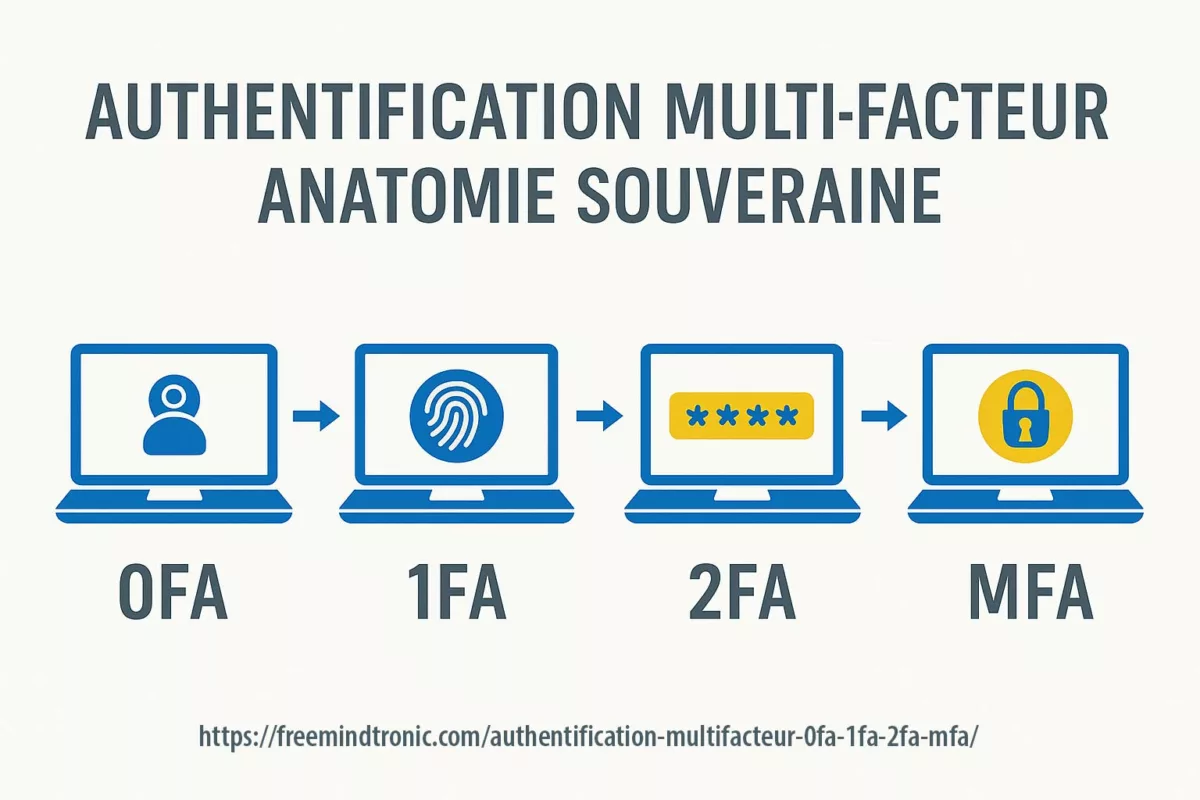
• Multi-Factor Authentication (MFA) MFA requires users to verify their identity using two or more independent factors—typically something they know (password), something they have (token), or something they are (biometrics). → This drastically reduces the risk of credential-based attacks.
• OAuth2 and OpenID Connect OAuth2 separates authentication from authorization. Combined with OpenID Connect, it enables secure access delegation to APIs without exposing user credentials. → DevExpress integrates these standards for secure Single Page Applications (SPAs).
• Zero Trust Security This model assumes no user or system is trusted by default—even inside the corporate network. → DevExpress implements this through role-based access control (RBAC), continuous validation, and secure-by-default UI behavior.
• AES-256 and RSA Encryption AES-256 ensures fast, strong encryption for data at rest and in transit, while RSA handles secure key exchange and token signing. → Together, they offer robust cryptographic protection across UI interactions.
🛡 Enhance DevExpress UI Security with PassCypher HSM PGP
✓ 100% serverless, database-free, and accountless
✓ Quantum-resilient by design: AES-256 CBC + segmented key system + no attack surface
✓ Native multi-factor authentication: 2 keys are required to access identity containers
✓ Phishing, typosquatting, and BITB-proof via sandboxed URL validation
✓ SSH, AES, RSA, ed25519 key generation with entropy feedback
✓ Fully air-gapped via NFC HSM or secure QR key importComparative Snapshot: Air-Gapped Security for .NET DevExpress Framework
Solution
Fully Air-Gapped
Passwordless
MFA
OTP with PIN Injection
PQC-Ready
Serverless
⌂ HID Injection + URL Sandbox ⌂
Bitwarden
⨉
✓
✓
⨉
⨉
⨉
⨉ Not available
FIDO2 Key
⨉
✓
✓
⨉
⨉
⨉
⨉ Not available
PassCypher HSM PGP
✓
✓
✓
(2FA via segmented key)✓
✓
✓
✓ Sandbox-based authentication
Use Case Spotlight: Air-Gapped DevExpress ApplicationContext
Solution
Fully Air-Gapped
Passwordless
MFA
OTP with PIN Injection
PQC-Ready
Serverless
⌂ HID Injection + URL Sandbox ⌂
Bitwarden
⨉
✓
✓
⨉
⨉
⨉
⨉ Not available
FIDO2 Key
⨉
✓
✓
⨉
⨉
⨉
⨉ Not available
PassCypher HSM PGP
✓
✓
✓
(2FA via segmented key)✓
✓
✓
✓ Sandbox-based authentication
Expert Insights: Lessons from the Field
Securing UI in Cloud and Serverless Environments
Essential Defense Mechanisms Against Cyber Threats
Advanced Client-Side Encryption with DataShielder HSM PGP
Future of Cybersecurity in UI Development
Test Your Skills: UI Security Challenge
Use OWASP Juice Shop or a DevExpress sandbox app to simulate these challenges.
Disruptive Trends in UI Security
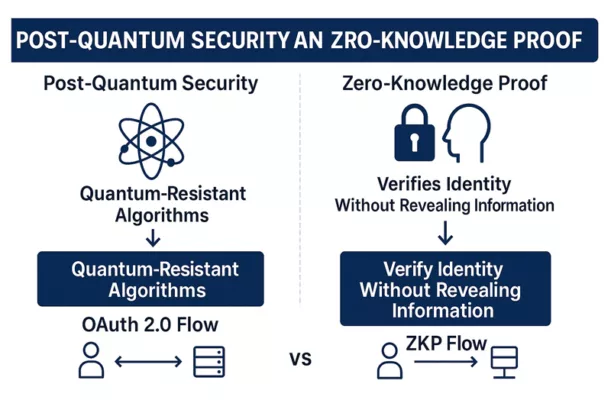
• PQC (Post-Quantum Cryptography): Uses quantum-resistant algorithms to future-proof UI encryption.
• ZKP (Zero-Knowledge Proofs): Verifies user authenticity without revealing credentials—ideal for Web3 UI.
• Adversarial AI: Malicious models that mimic UI behavior to bypass authentication layers.Next Steps for Developers: Strengthening UI Security Today
Offline Key Management for DevExpress UI Framework with NFC HSM
Glossary for the .NET DevExpress Framework
Passwordless Security Trends in 2025: Navigating the Digital Landscape
Explore the key passwordless security trends, challenges, and innovative solutions shaping our online security. This interactive report delves into user password habits, the escalating impact of cyber threats, and the critical transition towards more secure digital authentication methods. According to the Digital 2024 Global Overview Report by We Are Social and Hootsuite [Source A], over 5 billion people are connected to the Internet, spending an average of 6 hours and 40 minutes online daily.
423+ Billion
active online accounts worldwide, highlighting the immense scale of modern digital identity management.
The Burden of Passwords: Why Traditional Security Falls Short
This section examines prevalent user password habits, the fatigue they generate, and the resulting risky practices. Understanding these behaviors is crucial for grasping the full extent of the current password security problem and the need for passwordless authentication solutions.
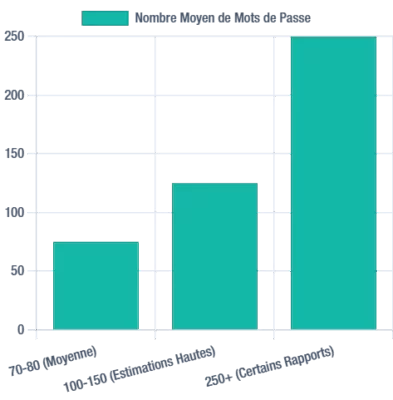
How Many Passwords Do Users Manage?
Individuals typically manage an average of 70 to 80 passwords, with some reports indicating figures as high as 100-150, or even over 250. According to Statista, a 2020 study estimated the average number of online accounts per internet user worldwide to be 90. This proliferation significantly contributes to password fatigue, pushing users towards less secure management methods.
Estimates of the average number of passwords per user, highlighting the scale of password management challenges.
Common & Risky Password Management Methods
Despite known security risks, many users opt for insecure password management methods: 54% rely on memory, 33% use pen and paper, 10% use sticky notes, and 15% use Excel or Notepad files. These practices underscore the urgent need for stronger authentication solutions.
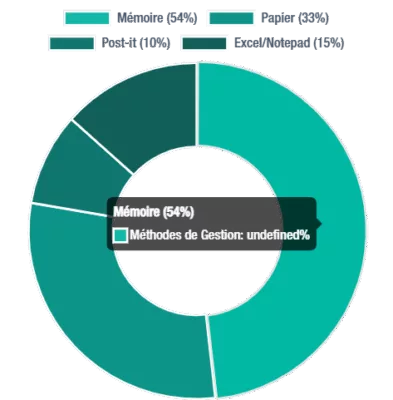
Distribution of password management methods, revealing widespread insecure password habits.
78%
of people admit to reusing passwords across multiple accounts, and 52% use the same one on at least three accounts, a significant security vulnerability.
76%
of users find password management stressful, contributing to password fatigue and poor security practices.
5-7 / 10-15
daily logins for private users and professionals respectively, highlighting the continuous authentication burden.
1 in 3
IT support tickets are related to password resets, indicating a major operational inefficiency.
Password Fatigue and Weakness: A Persistent Cyber Risk
The proliferation of online accounts leads to “password fatigue,” which encourages risky practices such as using weak passwords (e.g., “123456”, “password”, used by over 700,000 people) or widespread reuse. Nearly 60% of employees, including security personnel, admit to reusing passwords, and 48% reuse them on professional platforms. Furthermore, 59% of US adults include personal information in their passwords. This situation is worsened by the fact that 44% of internet users rarely or never change their passwords, creating gaping security flaws. Institutions like ANSSI and CISA consistently emphasize the importance of unique and complex passwords to mitigate these risks and enhance digital security in 2025.
The FBI’s Annual Internet Crime Report consistently highlights the devastating impact of password-related vulnerabilities, linking them to billions in financial losses due to various cybercriminal activities. This data underscores the urgent need for robust cybersecurity solutions beyond traditional passwords.
A related study, Time Spent on Login Method , explores the efficiency and security trade-offs of different authentication methods, underscoring the significant impact of time spent on login processes. User trust often remains disconnected from their actual practices: 60% feel confident in identifying phishing attempts, yet risky behaviors persist, reinforcing the need for phishing-resistant authentication.
Cybersecurity’s Financial Impact and Emerging Threats in 2025
Password-related vulnerabilities have direct and significant financial consequences for organizations and pave the way for increasingly sophisticated cyberattacks. This section explores the rising cost of data breaches and the new tactics cybercriminals are employing, including AI-driven cyber threats.
Rising Cost of Data Breaches and Credential Exposure
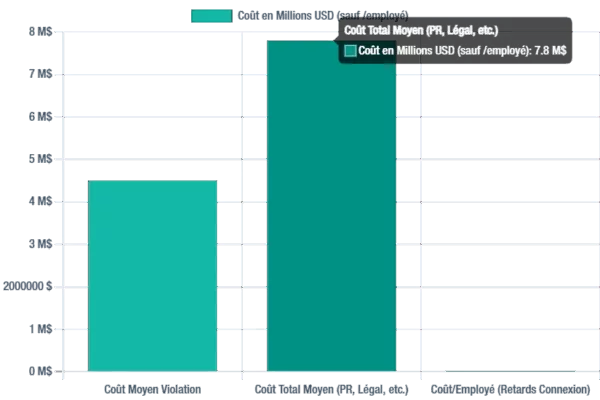
Data leaks related to passwords represent a significant financial burden for organizations. The average cost of a data breach in 2025 is projected to be $4.5 million, potentially reaching $7.8 million when including public relations, legal fees, and downtime. These figures highlight the critical need for robust data protection strategies.
Average financial impact of data breaches, illustrating the significant cybersecurity risks
3.8 Billion
credentials leaked in the first half of 2025. A broader study reveals 19 billion exposed passwords, of which 94% are reused or duplicated, creating massive credential stuffing vulnerabilities.
81%
of breaches involve weak or stolen passwords. 68% of breaches are directly attributable to human factors, emphasizing the need for user-centric security solutions.
41%
increase in DDoS attacks in 2024, costing up to $22,000/minute in downtime. SMEs suffer 198% more attacks than large enterprises, highlighting SME cybersecurity challenges.
Emerging Threats: AI, Deepfakes, and Advanced Phishing Attacks
Cybercriminals are increasingly leveraging advanced methods such as AI-assisted phishing and deepfakes to deceive users. Generative AI (GenAI) enables more sophisticated and large-scale attacks, with 47% of organizations citing GenAI-powered adversarial advancements as their primary concern. In 2024, 42% of organizations reported phishing or social engineering incidents. These threats exploit human psychology, making the distinction between legitimate and malicious communications increasingly difficult. Gartner predicts that by 2026, 30% of companies will consider identity verification solutions unreliable due to AI-generated deepfakes. Furthermore, IoT malware attacks increased by 400% in 2023, signaling growing vulnerabilities in connected devices and the broader IoT security landscape.
Toward a Passwordless Future: Adapting to New Authentication Models
Facing the inherent limitations of traditional passwords, the industry is rapidly moving towards passwordless authentication solutions. This section highlights the significant rise of passkeys, advancements in *biometric security, and the crucial integration of AI for enhanced security and a superior user experience.
Growth of the Passwordless Authentication Market
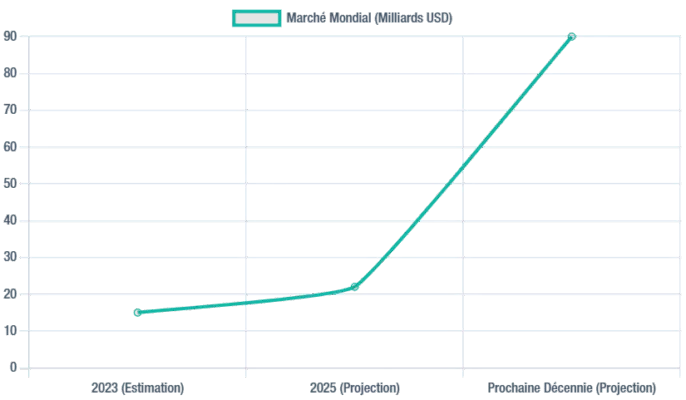
Projected growth of the global passwordless authentication market, demonstrating its rapid adoption.
15+ Billion
online accounts are now compatible with passkeys, marking a significant milestone in phishing-resistant authentication adoption.
550%
increase in daily passkey creation (end of 2024, Bitwarden), with over a million new passkeys created in the last quarter of 2024, underscoring rapid user acceptance.
70%
of organizations are planning or implementing passwordless authentication. Furthermore, customer support costs related to passwords can be reduced by 50%, offering substantial operational benefits.
57%
of consumers are now familiar with passkeys, a notable increase from 39% in 2022, indicating growing public awareness of new authentication methods.
Benefits of Passkeys and Biometrics in Passwordless Security
Passkeys, based on FIDO standards, offer inherently superior security as they are phishing-resistant and unique to each site. They significantly improve user experience with faster logins (e.g., Amazon 6 times faster, TikTok 17 times faster) and boast a 98% success rate (Microsoft, compared to 32% for traditional passwords). The NIST updated its guidelines for 2025, now requiring phishing-resistant multi-factor authentication (MFA) for all federal agencies, a critical step towards secure digital identity.
Biometric authentication (facial recognition, fingerprints, voice, behavioral biometrics) is continuously gaining accuracy thanks to AI. Multimodal and contactless approaches are developing rapidly. Behavioral biometrics, which analyzes subtle patterns like typing rhythm or mouse movement, enables continuous background identity verification, offering advanced user authentication capabilities. Privacy protection remains a major concern, leading to designs where biometric data primarily stays on the user’s device or is stored in a decentralized manner (e.g., using blockchain for decentralized identity).
Innovative Solution: PassCypher NFC HSM and HSM PGP – A Secure Alternative for Advanced Passwordless Authentication
The PassCypher NFC HSM and PassCypher HSM PGP solutions represent a major advancement in authentication management. They fundamentally differ from traditional FIDO/Passkey systems in their security architecture, offering a truly secure alternative for digital identity.
Passkeys: Security Model and Potential Vulnerabilities
Passkeys rely on private keys that are encrypted and inherently securely stored in integrated hardware components of the device. These are true hardware security modules (integrated HSMs):
- TPM 2.0 (Trusted Platform Module) on Windows and Linux systems.
- Secure Enclave (Apple) and TEE (Trusted Execution Environment) on Apple and Android devices. These are dedicated and isolated hardware elements on the SoC, not just software areas of the OS.
Using a passkey requires local user authentication (biometrics or PIN). It is crucial to note that this human authentication is not a direct decryption key for the private key. It serves to authorize the secure hardware component (TPM/Secure Enclave) to use the key internally to sign the authentication request, without ever exposing the private key. More information can be found on Passkeys.com [Source L].
However, a vulnerability remains: if an attacker manages to obtain physical access to the device *and* bypass its local authentication (e.g., via a keylogger for the PIN, or a sophisticated biometric spoofing technique), they could then instruct this same secure component to use the passkeys stored on the device. Furthermore, although TPM 2.0 is used for FIDO keys, its NVRAM memory is limited and not designed to directly store thousands of “master keys,” rather protecting keys linked to user profiles. This highlights a potential area for enhanced authentication security.
PassCypher: A Revolutionary Hybrid Architecture for Advanced Passwordless Security
PassCypher adopts a fundamentally different architecture, offering significant independence from hardware and software flaws of a single device, including zero-days or espionage threats. This system positions itself as a hybrid HSM, combining external physical storage with secure volatile memory computation, making it an ideal next-gen authentication solution.
PassCypher HSM PGP: Ultimate Authentication for PC/Mac/Linux Environments
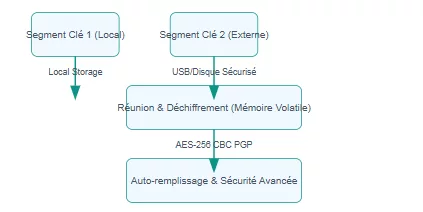
Operational Diagram: PassCypher HSM PGP for Enhanced PC/Mac/Linux Security
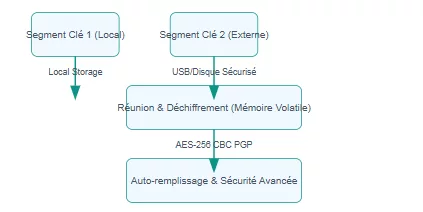
Key Segment 1 (Local)
Key Segment 2 (External)
Segments Recombination & Decryption (Volatile Memory)
Secure Auto-fill & Advanced Security
Browser Local Storage
USB/Secure Disk Enclave
AES-256 CBC PGP
- Segmented Keys and Robust Encryption: Uses a pair of 256-bit segmented keys. One is securely stored in the browser’s local storage, the other on a user-preferred external medium (USB drive, SD card, SSD, encrypted cloud, or even an enclave on a partitioned disk secured by BitLocker). Encryption and decryption are performed with a single click via AES-256 CBC secured by PGP, by concatenating the two segmented keys only in volatile memory and only for the duration of direct field auto-filling (without copy-pasting). This ensures robust data protection and key management.
- Advanced Protection against Cyberattacks: Integrates an anti-typosquatting URL sandbox and an anti-Browser-in-the-Browser (BITB) attack function, configurable in manual, semi-automatic, or automatic mode. Furthermore, with each connection, the “pwned” API is queried to check if the login and/or password have been compromised, displaying a visual alert message to the user (with a red hacker icon) if so. This provides proactive threat detection.
- Speed and Convenience: All these operations are performed in one click, or two clicks if two-factor authentication is required (including for complex accounts like Microsoft 365 with different redirection URLs). This emphasizes user experience in cybersecurity.
PassCypher NFC HSM: Mobile and Connected Passwordless Security
Operating Diagram: PassCypher NFC HSM
NFC HSM Module (EEPROM)
Android Phone (Freemindtronic App)
Website / App
Segmented Keys & Criteria (Volatile Memory)
Secure Auto-fill
PassCypher HSM PGP (Optional)
Encrypted Keys
NFC Communication
AES-256 Segmented
Via Secure Local Network
Login
- Multi-Segment Encrypted Containers: Stores encrypted containers via multiple segmented keys. By default, this includes a unique pairing key to the Android phone’s NFC device, a secure 128-bit signature key preventing HSM module counterfeiting, and the administrator password. This ensures robust mobile security.
- Encapsulation by Trust Criteria: Each container can be re-encrypted by encapsulation through the addition of supplementary trust criteria, such as:
- One or more geographical usage zones.
- One or more BSSIDs (Wi-Fi network identifiers).
- A password or fingerprint.
- A segmented key via QR code or barcode.
All this information, including access passwords to secure memory blocks of the EEPROM (e.g., M24LR64K from STM), is encrypted in the module’s memory, providing adaptable contextual authentication.
- Connectivity and Interoperability: Enables secure connection from an Android phone defined as a password manager, by filling login/password fields with a simple tap of the PassCypher NFC HSM module. A secure pairing system via the local network between the phone (with the Freemindtronic app embedding PassCypher NFC HSM) and PassCypher HSM PGP also allows auto-login from containers stored in NFC HSM modules, ensuring seamless and secure access.
- Secure Communication: All operations are performed in volatile memory via an innovative system of AES 256 segmented key encrypted communication between the phone and the extension, crucial for data integrity and privacy.
These PassCypher solutions, delivered internationally, offer unparalleled security and exceptional convenience, effectively addressing current and future cybersecurity challenges as a complete MFA authentication management solution. This segmented key system is protected by patents issued in the USA, Europe (EU), the United Kingdom (UK), Spain (ES), China, South Korea, and Japan, showcasing its innovative cybersecurity technology..
Global Cybersecurity Challenges in 2025: Beyond Passwordless
The AI Paradox and Emerging Quantum Threat
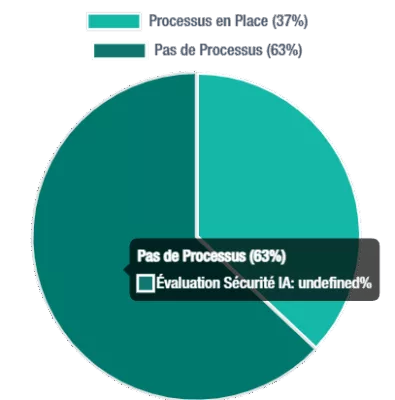
Organizational readiness for AI security assessment, revealing areas for improvement in cybersecurity preparedness.
Supply Chain Vulnerabilities and Third-Party Cybersecurity Risks
The increasing complexity of supply chains is now recognized as a primary cyber risk. A concerning 54% of large organizations view it as the biggest obstacle to their cyber resilience. A pervasive lack of visibility and control over supplier security creates systemic failure points, making the entire ecosystem vulnerable. Furthermore, 48% of CISOs cite third-party compliance as a major challenge in implementing crucial cyber regulations, complicating risk management strategies.
48%
of CISOs cite third-party compliance as a major challenge, highlighting the complexity of supply chain security management.
Skills Shortage and Regulatory Fragmentation in Cybersecurity
The global cybersecurity skills gap has grown by 8% in just one year. Two-thirds of organizations report critical shortages in cybersecurity talent, and only 14% feel they have the necessary expertise to address modern threats. In the public sector, 49% of organizations lack the talent required to achieve their cybersecurity goals, exacerbating talent retention issues.
Meanwhile, 76% of CISOs believe regulatory fragmentation significantly affects their ability to maintain compliance, creating “regulatory fatigue” and diverting resources from essential risk-based strategies. For comprehensive cyber threat landscape information, consult ENISA’s official publications. Geopolitical tensions also increasingly impact global cybersecurity strategies, with nearly 60% of organizations reporting such effects, adding another layer of complexity to national cybersecurity efforts.
Strategic Recommendations for Enhanced Passwordless Security in 2025
Actively explore and implement passkeys and advanced biometric authentication solutions. Emphasize the strong security benefits (especially phishing resistance) and improved user experience (faster, easier logins). Position passwordless technology as a strategic necessity to reduce support costs and enhance overall user satisfaction. Crucially, consider dedicated Hardware Security Module (HSM) solutions like PassCypher for optimal private key security and universal compatibility without extensive infrastructure adaptation.
Actively explore and implement passkeys and advanced biometric authentication solutions. Emphasize the strong security benefits (especially phishing resistance) and improved user experience (faster, easier logins). Position passwordless technology as a strategic necessity to reduce support costs and enhance overall user satisfaction. Crucially, consider dedicated Hardware Security Module (HSM) solutions like PassCypher for optimal private key security and universal compatibility without extensive infrastructure adaptation.
Actively explore and implement passkeys and advanced biometric authentication solutions. Emphasize the strong security benefits (especially phishing resistance) and improved user experience (faster, easier logins). Position passwordless technology as a strategic necessity to reduce support costs and enhance overall user satisfaction. Crucially, consider dedicated Hardware Security Module (HSM) solutions like PassCypher for optimal private key security and universal compatibility without extensive infrastructure adaptation.
Invest strategically in AI-driven defenses and thoroughly evaluate the security of all AI tools before deployment. Implement rigorous monitoring and enforce clear security requirements for the entire supply chain. Proactively anticipate and prepare for emerging threats from quantum computing, which could disrupt current encryption standards.
Actively support comprehensive cybersecurity training programs and leverage AI to augment human capabilities, addressing the critical skills shortage. Adopt “identity fabric” approaches to simplify access governance and streamline regulatory compliance, even amidst increasing fragmentation.
Introduction
References
- Zscaler, Check Point, HP Threat Research
- Freemindtronic APT36 Analysis
- Download the full APT36 Cyberespionage Group reference document (PDF)
- APT36 साइबर जासूसी समूह तकनीकी दस्तावेज़ हिंदी में डाउनलोड करें (PDF)
Legal Notice:
The content provided herein is for informational and educational use only. Freemindtronic S.L. Andorra disclaims all liability for direct or indirect consequences arising from the use or interpretation of this document. The information is shared without any warranty, and its use is under the full responsibility of the reader.
Any reproduction, adaptation, or redistribution must preserve the original attribution to Freemindtronic Andorra and include this legal disclaimer.
APT36 Cyberespionage Group Documentation
APT36 Cyberespionage Group is the focus of this technical reference, designed as a public documentation annexed to related posts published by Freemindtronic.
This document is a comprehensive technical reference on the APT36 Cyberespionage Group, freely downloadable for research and awareness purposes.It is part of Freemindtronic’s ongoing commitment to sharing threat intelligence and promoting proactive defense practices against advanced persistent threats (APT).
APT36 (Transparent Tribe / Mythic Leopard) Cyberespionage Group
Last Updated: May 16, 2025
Version: 1.1
Source: Freemindtronic Andorra
Introduction to the APT36 Cyberespionage Group
The Advanced Persistent Threat (APT) group known as APT36, Transparent Tribe, and Mythic Leopard has been an active cyber espionage actor for several years. Primarily targeted at India, APT36 is notorious for its persistent campaigns to collect sensitive intelligence from a variety of organizations, including government, military, and potentially the research and education sectors. Their operations are often characterized by the use of sophisticated spearphishing techniques and bespoke malware, such as Poseidon, Crimson RAT, ElizaRAT, and CapraRAT. The purpose of this reference document is to compile and analyze the available information about APT36, its tactics, techniques, and procedures (TTPs), infrastructure, and recommended mitigation measures.
History and Evolution of the APT36 Cyberespionage Group
Freemindtronic Andorra focuses its initial analysis on recent IOCs (2023-2025), but APT36 has been active for several years. Reports from other security organizations confirm that cyber espionage campaigns targeting Indian entities began as early as 2016. Over time, APT36 has continuously adapted its TTPs, refining techniques to bypass security measures and develop new infiltration tools. For example, the emergence of Android RATs like CapraRAT expands their reach to mobile devices, increasing the risk for smartphone users. Meanwhile, leveraging platforms such as Telegram for C2 operations (ElizaRAT) indicates an attempt to exploit less monitored communication channels, enhancing their stealth capabilities.
Cybersecurity experts continue to debate APT36’s precise attribution. Although its primary targets are in India, certain indicators suggest possible connections to Pakistani state interests. The choice of decoy themes and the sectors under attack reinforce this hypothesis. However, formal attribution remains challenging, requiring deeper analysis and more conclusive evidence. In the complex world of cyber threat intelligence, determining the true origin of APT groups demands a meticulous and multi-layered approach.
Techniques, Tactics and Procedures (TTPs) Employed by APT36
Reconnaissance: APT36 likely conducts careful reconnaissance of its targets, collecting publicly available information (OSINT) on employees, organizational structures, and sensitive projects. Social media profiles and official websites are potential sources of information. Social engineering can also be used to obtain information from employees.
Initial point of entry:
- Spearphishing: This is APT36’s preferred attack vector. Emails are meticulously designed to mimic legitimate communications (e.g., government notifications, invitations to academic events, security app updates). Malicious attachments (Word documents, PDFs, executables, RTF files, screensavers) or links to compromised websites are used to distribute the initial payloads. Identified filenames (e.g., Briefing_MoD_April25.docx, Alert_Kavach_Update.exe) illustrate this tactic by targeting topical themes or topics relevant to potential victims.
- Exploiting Vulnerabilities: Although not explicitly mentioned in the initial IOCs, it is possible that APT36 could exploit known software vulnerabilities in commonly used applications (e.g., Microsoft Office) to gain initial access. RTF files are often used in such attempts.
- Website Compromise: It is possible, although not directly proven by IOCs, that APT36 could compromise legitimate websites to host payloads or to redirect victims to phishing pages.
Persistence:
Once a system is compromised, APT36 puts mechanisms in place to maintain access even after a reboot. IOCs reveal the use of specific Windows registry keys (HKEY_CURRENT_USERSoftwareCrimsonRAT, HKEY_LOCAL_MACHINESYSTEMElizaRATPersistence, HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsCurrentVersionRunCapraStart) to ensure the automatic execution of malware. On Android, persistence is often achieved by masquerading as legitimate app updates (com.kavach.update.apk).
Lateral Movement:
After obtaining an initial foothold, APT36 attempts to move laterally within the victim’s network to reach more sensitive systems. This can involve exploiting network shares, using stolen credentials (potentially obtained via keylogging), and executing remote commands via deployed RATs.
Command and Control (C2)
The malware used by APT36 communicates with attacker-controlled C2 servers to receive instructions and exfiltrate data. The identified IP addresses (45.153.241.15, 91.215.85.21, etc.) potentially represent this C2 infrastructure. ElizaRAT’s use of TelegramBot suggests leveraging popular messaging platforms for C2, which can make detection more difficult. HTTP and HTTPS are likely used for C2 traffic, potentially hidden within legitimate web traffic.
Data exfiltration
Since APT36’s primary focus is espionage, data exfiltration is a crucial step. The types of data targeted likely include sensitive documents (military, government, research), credentials (usernames, passwords), and other strategic information. Data can be exfiltrated through established C2 channels, potentially compressed, or encrypted to avoid detection.
APT36 Malware and Tools
The APT36 Cyberespionage Group relies on various Remote Access Trojans (RATs) for espionage operations, especially on Indian targets.
- Poseidon malware: A sophisticated RAT with extensive espionage and data theft capabilities. Its hash (3c2cfe5b94214b7fdd832e00e2451a9c3f2aaf58f6e4097f58e8e5a2a7e6fa34) allows it to be identified on compromised systems.
- Crimson RAT: Another RAT commonly associated with APT36, offering keylogging, screen capture, and remote command execution features. Its mutex (GlobalCrimsonRAT_Active) and registry key (HKEY_CURRENT_USERSoftwareCrimsonRAT) are important indicators.
- ElizaRAT: This RAT appears to be using Telegram for C2 communication, which is a potential evasion tactic. Its loader (9f3a5c7b5d3f83384e2ef98347a6fcd8cde6f7e19054f640a6b52e61672dbd8f) and its mutex (LocalElizaRATSession) are key IOCs.
- CapraRAT (Android): Indicates APT36’s ability to target mobile devices. Its features can include stealing SMS, contacts, audio recording, and location tracking. Its package name (com.kavach.update.apk) and mutex (SessionsBaseNamedObjectsCapraMobileMutex) are specific flags.
Obfuscation and Evasion: APT36 uses a variety of techniques to make its malware and communications more difficult to detect and analyze. Examples of these tactics include Base64 encoding of sensitive information (bXlQYXNzd29yZDEyMw==, JAB1c2VyID0gIkFkbWluIg==) and obfuscation of JavaScript code (eval(decodeURIComponent(‘%75%70%64%61%74%65’))) are examples of these tactics.
APT36 Cyberespionage Group Infrastructure
APT36’s infrastructure includes the command and control (C2) servers used to direct malware deployed on victims’ systems. The identified IP addresses (45.153.241.15, 91.215.85.21, 185.140.53.206, 192.241.207.45, 103.145.13.187) are focal points for blocking and monitoring. Analysis of these IP addresses can reveal information about the hosting providers used and potentially other related activities. Malicious domains (kavach-app[.]com, indiapost-gov[.]org, gov-inportal[.]org, indian-ministry[.]com, securekavach[.]in) are used in phishing campaigns to host fake login pages or to distribute malware. These domains often imitate legitimate websites to trick victims. Analyzing the registration information of these domains can sometimes provide clues about the actors behind these activities. It is also possible that APT36 is using compromised servers as relays to hide the origin of its attacks and make tracing more difficult.
Motivations and Targets of the APT36 Cyberespionage Group
The main motivation for APT36 appears to be cyber espionage, with a particular interest in gathering strategic intelligence related to India. Typical targets include:
- Indian government entities (ministries, agencies).
- Military and defense organizations.
- Research institutes and universities.
- Telecommunications companies.
- Potentially other sectors considered strategically important.
The themes of phishing lures (defense, foreign affairs, security updates of government applications) reinforce this assessment of targets and motivations.
Indicators of Compromise (IOCs) Associated with APT36
IP addresses of C2 Servers (2023–2025):
- 45.153.241.15: Observed in C2 communications related to APT36 malware samples.
- 91.215.85.21: Frequently associated with command and control activities for Crimson and Eliza RATs.
- 185.140.53.206: Used as a point of contact for data exfiltration.
- 192.241.207.45: Server potentially hosting malicious web infrastructure components (phishing pages).
- 103.145.13.187: IP address involved in the distribution of malicious payloads.
File Hashes (SHA-256):
- 3c2cfe5b94214b7fdd832e00e2451a9c3f2aaf58f6e4097f58e8e5a2a7e6fa34 (Poseidon malware): Identifies a specific strain of the Poseidon RAT.
- bd5602fa41e4e7ad8430fc0c6a4c5d11252c61eac768835fd9d9f4a45726c748 (Crimson RAT) : Signature unique d’une variante de Crimson RAT.
- 9f3a5c7b5d3f83384e2ef98347a6fcd8cde6f7e19054f640a6b52e61672dbd8f (ElizaRAT loader): Allows you to detect the initial ElizaRAT deployment program.
- 2d06c1488d3b8f768b9e36a1a5897cc6f87a2f37b8ea8e8d0e3e5aebf9d7c987 (CapraRAT APK) : Hash de l’application Android malveillante CapraRAT.
Malicious domains:
- kavach-app[.]com: Imitation of the security application “Kavach”, probably used to distribute CapraRAT.
- indiapost-gov[.]org: Impersonates the Indian Postal Service site, used for phishing or distributing malicious attachments.
- gov-inportal[.]org: Attempt to imitate an Indian government portal to target civil servants.
- Indian-Ministry[.]com: Generic but credible domain name to target Indian ministries.
- securekavach[.]in: Another attempt to imitate “Kavach”, aimed at appearing legitimate to Indian users.
Suspicious URLs:
- http://kavach-app.com/update: Fake update URL for the “Kavach” app, potential distribution point for CapraRAT.
- http://gov-inportal.org/download/defense-docs.exe: Link to a malicious executable disguised as a defense document.
- http://securekavach.in/assets/login.php: Potential phishing page to steal credentials.
- https://indiapost-gov.org/track/status.aspx: A sophisticated phishing page that mimics package tracking to trick sensitive information into entering or downloading malware.
Phishing File Names:
- Briefing_MoD_April25.docx: Decoy potentially targeting the Ministry of Defense.
- Alert_Kavach_Update.exe: False update alert for “Kavach” probably distributing a RAT.
- IndiaDefense2025_strategy.pdf: Decoy containing strategic information on Indian defense.
- MoEA_internal_memo_23.rtf: Fake internal memo from the Ministry of Foreign Affairs.
- academic-research-invite.scr: Malicious screensaver masquerading as an academic invite.
Fake Android Application Package Names:
- com.kavach.update.apk: Malicious package masquerading as an update of “Kavach”.
- com.defensebriefing.alert.apk: Malicious Android app related to defense.
- com.india.education.portal.apk: Fake app linked to an Indian educational portal.
Mutexes:
- GlobalCrimsonRAT_Active: Indicates the active presence of the Crimson RAT on a Windows system.
- LocalElizaRATSession: Indicates an active Eliza RAT session.
- SessionsBaseNamedObjectsCapraMobileMutex: A Mutex specific to the Android version of CapraRAT.
Registry Keys (Windows):
- HKEY_CURRENT_USERSoftwareCrimsonRAT: Key used by Crimson RAT to store its configuration.
- HKEY_LOCAL_MACHINESYSTEMElizaRATPersistence: A key indicating a persistence mechanism for ElizaRAT.
- HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindowsCurrentVersionRunCapraStart: Automatic startup key for CapraRAT.
Known User-Agents:
- Mozilla/5.0 (Windows NT 10.0; Win64; x64) APT36Client/1.0: User-agent potentially used by a communication tool or an APT36-specific implant.
- TelegramBot-ElizaRAT/2.5: Indicates the use of the Telegram API by the Eliza RAT for C2 communication.
- CapraAndroidAgent/1.4: User-agent identifying the Capra malicious agent on Android devices.
Encoded/Obfuscated Strings Used in Payloads:
- bXlQYXNzd29yZDEyMw==: A Base64-encoded string, decoding as “myPassword123”, potentially hard-coded identifiers or configuration strings.
- JAB1c2VyID0gIkFkbWluIg==: Another Base64 string, decoding to $user=”Admin”, suggesting the use of PowerShell for malicious operations.
- eval(decodeURIComponent(‘%75%70%64%61%74%65’)): Obfuscated JavaScript code that, when de-encoded and evaluated, executes the “update” function, potentially indicating a malicious update or dynamic code execution feature.
Mitigation and Detection Measures Against the APT36 Cyberespionage Group
Mitigating threats from the APT36 Cyberespionage Group requires layered defenses, active monitoring, and awareness training.
General recommendations:
- Awareness of the threat of spearphishing: Train employees to identify suspicious emails, verify the authenticity of senders, and not click on links or open attachments from unknown or unsolicited sources.
- Implement multi-factor authentication (MFA): Strengthen account security by requiring a second form of authentication in addition to the password.
- Keeping systems and software up to date: Regularly apply security patches for operating systems, applications, and web browsers to reduce the risk of vulnerability exploitation.
- Network segmentation: Limit the spread of threats by segmenting the network and enforcing strict access control policies.
- Network traffic and log monitoring: Implement monitoring systems to detect suspicious network activity, communications to known IP addresses and C2 domains, and unusual access attempts. Regularly analyze system and application logs.
- Use robust security solutions: Deploy and maintain anti-virus solutions, endpoint detection and response (EDR) systems, and intrusion prevention and detection (IDS/IPS) systems.
Specific measures based on IOCs:
- IOC Blocking: Integrate identified IP addresses, domains, and file hashes into firewalls, DNS servers, antivirus solutions, and web filtering systems to block communications and malware associated with APT36.
- Rule-Based Detection: Implement Yara and Sigma rules (if available) to identify patterns and characteristics of malware and APT36 activities on systems and in logs.
- Traffic Inspection: Configure security systems to inspect network traffic for suspicious user agents (APT36Client/1.0, TelegramBot-ElizaRAT/2.5, CapraAndroidAgent/1.4).
- Registry and Mutex Monitoring: Use endpoint monitoring tools to detect the creation of registry keys and mutexes associated with RATs used by APT36.
- Email Scanning: Implement spam filters and email scanning solutions to identify and block messages containing known file names and phishing URLs.
- Mobile device security: Deploy mobile security solutions and educate users about the risks of installing apps from unknown sources. Monitor Android devices for the presence of malicious package names.
Incident response strategies:
- Response Plan: Develop and maintain a cybersecurity incident response plan specific to APT threats, including steps to follow in the event of detection of APT36-related activity.
- Isolation: In the event of a suspected compromise, immediately isolate the affected systems from the network to prevent the spread of the attack.
- Forensic Analysis: Perform in-depth forensic analysis to determine the scope of the breach, identify compromised data, and understand the tactics used by attackers.
- Eradication: Completely remove malware, persistence mechanisms, and tools used by attackers from compromised systems.
- Restore: Restore systems and data from clean, verified backups.
- Lessons learned: After an incident, analyze causes and processes to improve security measures and response procedures.
References
- https://www.zscaler.com/blogs/security-research/transparent-tribe-apt-targeting-india
- https://research.checkpoint.com/2023/transparent-tribe-evolution-of-a-cyber-espionage-threat/
- https://threatresearch.ext.hp.com/transparent-tribe-apt-group/
- This technical reference document is based on the original analysis published by Freemindtronic Andorra, available at: https://freemindtronic.com/apt36-spearphishing-india/
Strengthening Security Posture: The Freemindtronic HSM Ecosystem Against APT36
The table below summarizes how each threat vector used by APT36 is mitigated by Freemindtronic’s sovereign tools — whether mobile or desktop, fixed or remote, civilian or military-grade. It compares threat by threat how DataShielder and PassCypher mitigate attacks — whether on mobile, desktop, or air-gapped infrastructure.
To facilitate adoption and use by organizations in India, the interfaces and documentation for our DataShielder and PassCypher solutions are also available in Hindi.
| APT36 Tactic / Malware | DataShielder NFC HSM (Lite/Auth/M-Auth) | DataShielder HSM PGP (Win/macOS) | PassCypher NFC HSM (Android) | PassCypher HSM PGP (Win/macOS) |
|---|---|---|---|---|
| Spearphishing (India Post, Kavach) | ✔ QR-code encryption + sandbox | ✔ Signature check + offline PGP | ✔ URL sandbox + no injection | ✔ Sandboxed PGP container |
| Crimson RAT | ✔ NFC avoids infected OS | ✔ No system-stored keys | ✔ Secrets off-device | ✔ No memory exposure |
| CapraRAT | ✘ | ✘ | ✔ Not stored in app | ✔ Desktop-paired use only |
| Telegram C2 | ✔ 100% offline | ✔ No cloud | ✔ Offline | ✔ Offline |
| ApolloStealer | ✔ Credentials never exposed | ✔ Key never loaded in system | ✔ Immune to clipboard steal | ✔ Phishing-proof login |
| Poseidon (Fake Kavach on Linux) | ✔ NFC-only: bypasses compromised OS | ✘ Not Linux-compatible | ✘ Not on Android | ✔ No OS dependency |
| ClickFix (command injection) | ✔ No shell interaction possible | ✔ PGP validation | ✔ No typing / no pasting | ✔ No terminal interaction |
| CEO Fraud / BEC | ✔ Auth/M-Auth modules encrypt orders | ✔ Digital signature protection | ✔ No spoofing possible | ✔ Prevents impersonation |
Outlook and Next Steps Regarding APT36
APT36 (Transparent Tribe / Mythic Leopard) embodies a persistent and structured threat, primarily targeting strategic Indian entities for cyberespionage purposes. Its campaigns rely on sophisticated decoys, custom RATs, and an agile C2 infrastructure. A thorough understanding of their tactics, techniques, and procedures (TTPs), as well as the currently known Indicators of Compromise (IOCs), provides a solid foundation to guide detection, defense, and response policies. Faced with the constant evolution of the techniques used by this group, a posture of continuous vigilance is essential. This document is produced in an evolving manner. We believe it is essential to keep it up to date with new threats and tools observed in order to maintain a proactive security posture aligned with the latest available APT36 intelligence.
APT36 SpearPhishing India is one of the most persistent cyberespionage threats targeting India. This article by Jacques Gascuel investigates its methods and how to protect against them.
APT36 SpearPhishing India: Inside Pakistan’s Persistent Cyberespionage Campaigns
APT36 SpearPhishing India represents a serious and persistent cyber threat targeting Indian entities. This article explores their spear-phishing techniques, malware arsenal, and defensive responses.
Understanding Targeted Attacks of APT36 SpearPhishing India
APT36 cyberespionage campaigns against India represent a focused and enduring threat. Actors likely linked to Pakistan orchestrate these attacks. This group, also known as Transparent Unit, ProjectM, Mythic Leopard, and Earth Karkaddan, has been active since at least 2013. Throughout its operations, APT36 has consistently targeted Indian government entities, military personnel, defense organizations, research institutions, diplomats, and critical infrastructure.
Unlike threat actors with broader targets, APT36’s operations primarily focus on gathering intelligence relevant to Pakistani strategic interests, especially concerning its relationship with India. This article analyzes APT36’s attack methods, its specific targeting of Indian entities, technical indicators, and proactive security measures for defense. Understanding their evolving tactics allows cybersecurity professionals to develop tailored countermeasures and strengthen resilience against persistent threats.
Purpose of this Brief: This report aims to provide a detailed understanding of APT36’s tactics, their priority targets in India, and their evolving malware arsenal (e.g., Crimson RAT, Poseidon, ElizaRAT, CapraRAT). It also covers recent techniques such as ClickFix attacks and the abuse of legitimate cloud services, offering insights into how Indian organizations can strengthen their cyber defense against this persistent cyberespionage threat.
The Espionage Model of APT36 SpearPhishing India: Focused Infiltration
The operational model of APT36 features a specific focus on Indian targets, persistence, and adaptability. Their main goal isn’t widespread disruption. Instead, they aim for sustained infiltration of Indian networks to exfiltrate sensitive information over time. Their campaigns often last a significant duration, showing a commitment to long-term access. While they may not always use the most advanced zero-day exploits, their consistent refinement of social engineering and malware deployment proves effective against Indian organizations.
Furthermore, APT36 frequently uses publicly available or slightly modified tools. Alongside these, they also deploy custom-developed malware. This malware is specifically tailored to evade common detection mechanisms within Indian organizations.
Main Targets of APT36 SpearPhishing India
APT36 primarily focuses its attacks on a range of Indian entities, including:
- Indian government ministries, with a particular emphasis on the Ministry of Defence and the Ministry of External Affairs.
- The Indian armed forces and organizations within the defense industrial sector.
- Educational institutions and students.
- Users of government services, such as those utilizing the Kavach authentication application.
These targets align with recent warnings, such as the May 2025 advisory from the Chandigarh Police citing government institutions, defense personnel, research centers, diplomats, and critical infrastructure as primary targets.
The group frequently employs social engineering techniques, including the use of lure documents and the creation of fake websites mimicking legitimate portals, to trick victims into downloading and executing their malware.
APT36’s Malware Arsenal: Types and Evolution (2013–2025)
APT36 relies on a diverse and evolving malware arsenal tailored to espionage operations against Indian entities. Their tools include widely-used Remote Access Trojans (RATs) and more recent, customized malware. ElizaRAT malware analysis highlights its evolution into a stealthy .NET-based trojan leveraging Telegram for covert C2, as seen in multiple campaigns since late 2023.
- Crimson RAT: In use since 2013 for data exfiltration and surveillance.
- ElizaRAT: A .NET-based RAT communicating via Telegram, with enhanced C2 capabilities.
- Poseidon: Targets Linux via fake Kavach app installations.
- CapraRAT: Android malware for mobile surveillance.
- ApolloStealer: Data harvester targeting government systems.
ClickFix: APT36’s Deceptive New Attack Technique
APT36 has adopted “ClickFix”-style campaigns to trick users into copying malicious commands from websites that impersonate legitimate Indian portals. This bypasses email filters and endpoint protections by relying on user interaction via terminal or shell.
Exploitation of Cloud Services for C2: A Detection Challenge
APT36 leverages popular platforms like Telegram, Google Drive, and Slack for Command & Control. These services allow attackers to blend in with normal encrypted traffic and evade firewall detection.
Why India is APT36’s Primary Target
The cyber activities of APT36 are deeply intertwined with the complex geopolitical dynamics between Pakistan and India. Their consistent focus on targeting Indian government, military, and strategic assets strongly suggests their role in directly supporting Pakistan’s intelligence-gathering efforts.
Furthermore, APT36’s operations often show increased activity during periods of heightened tension or significant political events between the two nations. Their primary objectives appear to center on acquiring sensitive information. This includes data related to India’s defense capabilities, its foreign policy decisions, and its internal security measures.
To illustrate, notable examples of their activity include:
- Sustained campaigns specifically target Indian military personnel. These campaigns often involve sophisticated social engineering combined with malware-laden documents.
- Attacks directed against Indian government organizations involved in policy making and national security. The aim is likely to gain insights into strategic decision-making and sensitive communications.
- Targeting of research institutions and defense contractors. This suggests an interest in acquiring knowledge about India’s technological advancements in defense.
- The strategic use of topical lures in their phishing campaigns. These lures often relate to current events, such as cross-border incidents or diplomatic discussions, to make their malicious emails more relevant.
In essence, APT36 functions as a significant cyber arm within the broader geopolitical context. The intelligence they successfully gather can be leveraged for strategic planning, diplomatic maneuvering, and potentially to gain an advantage in the intricate relationship between India and Pakistan. Therefore, a thorough understanding of this geopolitical context is crucial for developing effective cyber defense strategies within India.
Indian Government and Security Responses to APT36 Cyberespionage

- India’s layered response to APT36 SpearPhishing campaigns — from real-time monitoring to public cybersecurity advisories and professional capacity building.
The Indian government and its security agencies have increasingly focused on detecting, attributing, and mitigating the persistent threats posed by APT36 cyberespionage. Indian government phishing alerts, such as those issued by CERT-In and regional cyber cells, underscore the urgency of countering targeted APT36 spearphishing attacks.
Responses often include:
- Issuing public advisories and alerts regarding APT36’s tactics and indicators of compromise (IOCs).
- Enhancing monitoring and detection capabilities within government and critical infrastructure networks.
- Conducting forensic analysis of attacks to understand APT36’s evolving TTPs and develop better defenses.
- Collaboration between different security agencies and sharing of threat intelligence.
- Efforts to raise cybersecurity awareness among potential targets, particularly within government and military sectors.
- Capacity building initiatives to train cybersecurity professionals within India to better defend against sophisticated threats like APT36.
While direct legal or retaliatory actions are less publicly discussed, the focus remains on strengthening India’s cyber resilience and deterring future attacks through enhanced detection and response.
Potential Impact of Undetected APT36 Cyberespionage
The prolonged and undetected operations of APT36 cyberespionage could have significant ramifications for India’s national security and strategic interests:
- Loss of Sensitive Information: Unfettered access could lead to the exfiltration of classified military plans, diplomatic communications, and sensitive government policies.
- Compromise of Critical Infrastructure: Persistent access to critical infrastructure networks could potentially be exploited for disruptive purposes in the future.
- Erosion of Trust: Successful and undetected breaches could undermine trust in the security of government and defense systems.
- Strategic Disadvantage: The intelligence gathered could provide Pakistan with a strategic advantage in diplomatic negotiations or during times of conflict.
- Impact on International Relations: Compromise of diplomatic communications could strain relationships with other nations.
This underscores the critical importance of robust cybersecurity measures and proactive threat hunting to detect and neutralize APT36’s activities before they can cause significant harm through their cyberespionage.
Notable APT36 Cyberespionage Incidents Targeting India
| Date (Approximate) | Campaign/Malware | Target | Observed Tactics |
|---|---|---|---|
| 2013 onwards | Crimson RAT | Indian Government, Military | Spearphishing with malicious attachments. |
| 2018-2019 | Transparent Group Campaigns | Defense Personnel, Government Officials | Social engineering, weaponized documents. |
| 2020-2021 | Abuse of Cloud Services | Various Indian Entities | C2 via Telegram, Google Drive. |
| 2022-2023 | ElizaRAT | Government, Research Institutions | Evolved RAT with enhanced evasion techniques. |
| 2024-2025 | ClickFix Campaigns | Government Portals | Tricking users into executing malicious commands. |
Timeline Sources & Attribution of APT36 SpearPhishing India Attacks

- APT36 SpearPhishing India: Visual timeline of APT36 cyberespionage campaigns and malware used against Indian entities from 2013 to 2025.
This infographic is based on analysis and reports from various cybersecurity firms, threat intelligence sources, and official advisories, including:
- Ampcus Cyber on APT36 Insights: Ampcus Cyber.
- Athenian Tech Analysis on APT-36: Athenian Tech.
- Brandefense Analysis on APT-36 Poseidon Malware: Brandefense.
- CERT-In Security Advisories: CERT-In.
- Chandigarh Police Advisory (May 2025) on APT36 Threats (via Indian Express): Indian Express.
- Check Point Research on the Evolution of the Transparent Group: Check Point.
- CloudSEK Threat Intelligence: CloudSEK.
- CYFIRMA Research on APT36 Targeting via Youth Laptop Scheme: CYFIRMA.
- Reco AI Analysis of ElizaRAT: Reco AI.
- SentinelOne Labs on APT36 Targeting Indian Education: SentinelOne.
- The Hacker News on APT36 Spoofing India Post: The Hacker News.
- Zscaler ThreatLabz Analysis of APT36’s Updated Arsenal: Zscaler ThreatLabz.
- Kaspersky Cybermap (General Threat Landscape): Kaspersky.
These sources collectively indicate that APT36 remains a persistent and adaptive threat actor with a clear focus on espionage against Indian interests through cyber means.
APT36 vs. APT29, APT41, APT33: Strategic Comparison of Cyberespionage Groups
| Tactic/Group | APT36 (also known as ProjectM, Mythic Leopard, Earth Karkaddan, “Transparent Tribe” — researcher-assigned alias) | Other APT Groups (e.g., APT29, APT41, APT33) |
| Primary Target | Predominantly focuses on entities within India. | Employs a broader targeting strategy, often including Europe, the United States, and various other regions depending on the group’s objectives. |
| Suspected Affiliation | Believed to have strong links to Pakistan. | Attributed to various state-sponsored actors, including Russia (e.g., APT29), China (e.g., APT41), and Iran (e.g., APT33). |
| Main Objective | Primarily cyberespionage with a specific focus on gathering intelligence relevant to Indian affairs. | Objectives can vary widely, including espionage, disruptive attacks, and financially motivated cybercrime, depending on the specific group. |
| Favored Techniques | Relies heavily on spearphishing attacks, the use of commodity Remote Access Trojans (RATs) such as Crimson and ElizaRAT, social engineering tactics, abuse of cloud services, malicious Office documents, fake websites, and “ClickFix” campaign techniques. | Often employs more sophisticated and custom-developed malware, and in some cases, utilizes zero-day exploits to gain initial access. The level of sophistication varies significantly between different APT groups. |
| Stealth and Sophistication | While their social engineering tactics can be quite effective, their malware development is generally considered less sophisticated compared to some other advanced persistent threat groups. However, they continuously adapt their existing tools for their cyberespionage efforts. | Varies significantly. Some groups utilize highly advanced and stealthy custom malware with sophisticated command and control infrastructure, while others may rely on more readily available tools. |
| Resource Allocation | Likely operates with fewer resources compared to state-sponsored groups from larger nations. | Variable, with some groups having significant state backing and extensive resources, enabling more complex and persistent campaigns. |
| Geopolitical Context | Primarily driven by the geopolitical relationship and tensions between India and Pakistan. | Driven by broader national interests and complex geopolitical strategies that extend beyond a single bilateral relationship. |
Key Indicators and Detection of APT36 Cyberespionage
Security teams targeting APT36 should be vigilant for the following indicators:
- Spearphishing emails with themes relevant to the Indian government, military, or current affairs.
- Attachments containing weaponized documents (e.g., malicious DOC, RTF, or executable files).
- Network traffic to known C2 infrastructure associated with APT36.
- Unusual use of cloud services (Telegram, Google Drive, Slack) for data transfer.
- Execution of suspicious commands via command-line interfaces, potentially linked to ClickFix attacks.
- Presence of known APT36 malware like Crimson RAT, ElizaRAT, ApolloStealer, Poseidon (particularly on Linux systems), and CapraRAT (on Android devices).
- Use of domains and URLs mimicking legitimate Indian government or military websites.
- Use of domains and URLs mimicking legitimate Indian government or military websites.
- Suspicious emails with subject lines or content related to recent sensitive events like the April 2025 Pahalgam terror attack.
- Network traffic to or from websites mimicking the India Post portal or other legitimate Indian government services.
◆ Known Indicators of Compromise (IOCs) – APT36
The following Indicators of Compromise have been observed across multiple APT36 campaigns, including those involving Crimson RAT, ElizaRAT, Poseidon, and CapraRAT. Use them to improve detection and defense mechanisms:
- C2 IP addresses (2023–2025): 45.153.241.15, 91.215.85.21, 185.140.53.206 (ElizaRAT / Telegram-based C2)
- File hashes (SHA-256):
3c2cfe5b94214b7fdd832e00e2451a9c3f2aaf58f6e4097f58e8e5a2a7e6fa34 (Poseidon)
bd5602fa41e4e7ad8430fc0c6a4c5d11252c61eac768835fd9d9f4a45726c748 (Crimson RAT) - Malicious domains: kavach-app[.]com, indiapost-gov[.]org, gov-inportal[.]org
- Suspicious file names: Briefing_MoD_April25.docx, Alert_Kavach_Update.exe
◆ Additional IOCs: Linux & Android Malware in APT36 SpearPhishing India
APT36 increasingly targets Linux and Android environments with deceptive filenames and cloud-distributed payloads.
- Linux-specific hashes (MD5):
65167974b397493fce320005916a13e9 (approved_copy.desktop)
98279047a7db080129e5ec84533822ef (pickle-help)
c86f9ef23b6bb200fc3c0d9d45f0eb4d (events-highpri) - Fake .desktop file names: Delegation_Saudi_Arabia.desktop, Meeting_agenda.desktop, approved_copy.desktop
- Linux-focused C2 servers: 108.61.163[.]195:7443, 64.176.40[.]100:7443, 64.227.138[.]127, 134.209.159[.]9
- Android malware package names: com.chatspyingtools.android, com.spyapp.kavachupdate
- Deceptive download URLs:
http://103.2.232[.]82:8081/Tri-Service-Exercise/Delegation_Saudi_Arabia.pdf
https://admin-dept[.]in/approved_copy.pdf
https://email9ov[.]in/VISIT_OF_MEDICAL/
Sources: Brandefense, Zscaler ThreatLabz, Reco AI, CYFIRMA, Check Point Research
◆ Download the Full IOC Report for APT36
To strengthen your spearphishing defense in India and enhance detection capabilities against APT36 cyberespionage, you can download the full list of enriched Indicators of Compromise (IOCs) used by the group.
This includes:
- Command & Control (C2) IP addresses
- SHA-256 hashes of known malware samples (e.g. Crimson RAT, ElizaRAT, Poseidon)
- Fake domains and URLs (Kavach, India Post…)
- Malicious file names and Android package names
- Registry keys, mutexes, user-agents and encoded payload strings
⇩ Download APT36 Cyberespionage IOC & TTP Report by Freemindtronic (PDF – English)
◆ APT36 साइबर जासूसी समूह तकनीकी दस्तावेज़ डाउनलोड करें
भारत में अपने स्पीयरफ़िशिंग बचाव को मजबूत करने और APT36 साइबर जासूसी के खिलाफ पहचान क्षमताओं को बढ़ाने के लिए, आप समूह द्वारा उपयोग किए गए समृद्ध संकेतकों की पूरी सूची डाउनलोड कर सकते हैं।
इसमें शामिल हैं:
- कमांड एंड कंट्रोल (C2) आईपी एड्रेस
- ज्ञात मैलवेयर नमूनों के SHA-256 हैश (जैसे क्रिमसन आरएटी, एलिजारैट, पोसीडॉन)
- फर्जी डोमेन और यूआरएल (कवच, इंडिया पोस्ट…)
- दुर्भावनापूर्ण फ़ाइल नाम और एंड्रॉइड पैकेज नाम
- रजिस्ट्री कुंजियाँ, म्युटेक्स, उपयोगकर्ता-एजेंट और एन्कोडेड पेलोड स्ट्रिंग
⇩ APT36 साइबर जासूसी समूह तकनीकी दस्तावेज़ डाउनलोड करें (PDF – हिंदी)
Compiled from: Brandefense, Zscaler, Check Point, Reco AI, SentinelOne, CYFIRMA, and CERT-In reports
APT36 SpearPhishing India in 2025: Updated Arsenal and Emerging Linux Threats
APT36 continues to evolve its tactics in 2025, expanding its targeting scope beyond Windows environments. Recent reports highlight sophisticated ClickFix-style attacks on Linux systems, where users are tricked into pasting terminal commands disguised as harmless instructions. This represents a critical shift, bypassing traditional endpoint security solutions.
- ClickFix Linux Variant: In 2025, APT36 began testing ClickFix-style social engineering attacks on Linux by embedding dangerous commands inside fake support messages and screenshots. [BleepingComputer Report]
- New Linux-based Payloads: Building on their 2023 campaigns, APT36 now weaponizes .desktop files with inflated size (1MB+), obfuscated base64 commands, and deceptive PDF decoys. These payloads deploy cross-platform backdoors with persistence via cron jobs.
- Advanced C2 Infrastructure: They continue to abuse trusted cloud services like Telegram, Google Drive, and now Indian TLDs (e.g.,
.indomains) to mask origins and evade attribution. These deceptive techniques align with past OPSEC failures such as the “Nand Kishore” Google Drive account.
For a full technical breakdown, we recommend reading the excellent deep-dive analysis by Zscaler ThreatLabz: Peek into APT36’s Updated Arsenal (2023).
Countering APT36 with Sovereign Zero-Trust Solutions
APT36 targets India through spearphishing, remote access malware, and cloud abuse. To counter such advanced persistent threats, Freemindtronic offers patented, sovereign, and fully offline security tools that eliminate traditional attack surfaces.
DataShielder & PassCypher: Zero-Trust Hardware-Based Protection
To further support organizations in India against threats like APT36, the user interfaces and relevant documentation for our DataShielder and PassCypher solutions are also available in Hindi, ensuring ease of use and accessibility.
- DataShielder NFC HSM (Lite, Auth, Master, M-Auth)
Offline AES-256 encryption with RSA 4096 key exchange (M-Auth), ideal for fixed (Auth) and mobile (M-Auth) use. No RAM, no OS access, no server. - DataShielder HSM PGP
Browser-integrated, offline PGP encryption/decryption. Compatible with air-gapped systems. Private keys never leave the HSM. - PassCypher NFC HSM
Offline password & OTP manager (TOTP/HOTP) using a contactless HSM. Injects credentials only on verified domains. No clipboard, no RAM exposure. - PassCypher HSM PGP
Secure, passwordless login + PGP + OTP autofill, browser-integrated. 100% offline. No secrets exposed to the system.
📘 Learn more about the DataShielder NFC HSM Starter Kit
APT36 Tactics vs. Freemindtronic Defense Matrix
| APT36 Tactic | Freemindtronic Defense | Compatible Products |
|---|---|---|
| Spearphishing / Fake Portals | Sandboxed URL validation; no credential injection on spoofed sites | PassCypher NFC HSM, PassCypher HSM PGP |
| Credential Theft (ElizaRAT, ApolloStealer) | No copy/paste, no secrets in RAM, no browser storage | All products |
| Remote Access Tools (Crimson RAT, Poseidon) | 100% offline operation, NFC/QR key exchange, no OS exposure | DataShielder NFC HSM Lite, Auth, Master, M-Auth |
| Fake Apps & ClickFix Commands | Credential injection via NFC or container — no terminal input | PassCypher NFC HSM, PassCypher HSM PGP |
| Cloud-based C2 (Telegram, Google Drive) | No connectivity, no browser plug-in, no C2 callbacks possible | All NFC HSM and HSM PGP solutions |
🛡️ Why Choose These Solutions?
- 🛠 No server • No database • No RAM exposure • No clipboard
- ⚖️ GDPR / NIS2 / ISO 27001 compliant
- 🎖️ Built for air-gapped and sovereign systems (civil + defense use)
- 🔐 Licensed HSM PGP on Windows/macOS, NFC HSM works on all OS (via Android NFC)
Comparative Threat Mitigation Table: APT36 vs. Freemindtronic HSM Ecosystem
This table summarizes how each threat vector used by APT36 is mitigated by Freemindtronic’s sovereign tools — whether mobile or desktop, fixed or remote, civilian or defense-grade.
🧩 How does each solution stand against APT36’s arsenal?
The table below compares threat-by-threat how DataShielder and PassCypher mitigate attacks — whether on mobile, desktop, or air-gapped infrastructure.
| APT36 Tactic / Malware | DataShielder NFC HSM (Lite/Auth/M-Auth) |
DataShielder HSM PGP (Win/macOS) |
PassCypher NFC HSM (Android) |
PassCypher HSM PGP (Win/macOS) |
|---|---|---|---|---|
| Spearphishing (India Post, Kavach) | ✔ QR-code encryption + sandbox |
✔ Signature check + offline PGP |
✔ URL sandbox + no injection |
✔ Sandboxed PGP container |
| Crimson RAT | ✔ NFC avoids infected OS |
✔ No system-stored keys |
✔ Secrets off-device |
✔ No memory exposure |
| ElizaRAT | ✔ No cloud or RAM access |
✔ PGP keys isolated in HSM |
✔ No RAM / no clipboard |
✔ OTP only if URL matches |
| ApolloStealer | ✔ Credentials never exposed |
✔ Key never loaded in system |
✔ Immune to clipboard steal |
✔ Phishing-proof login |
| Poseidon (Fake Kavach on Linux) | ✔ NFC-only: bypasses compromised OS |
✘ Not Linux-compatible |
✔ No OS dependency |
✘ Desktop only |
| CapraRAT (Android) | ✘ (Not on Android) |
✘ | ✔ Secrets never stored in app |
✔ With desktop pair only |
| ClickFix (command injection) | ✔ No shell interaction possible |
✔ PGP validation |
✔ No typing / no pasting |
✔ No terminal interaction |
| Telegram / Cloud C2 Abuse | ✔ No cloud usage at all |
✔ Fully offline |
✔ 100% offline |
✔ 100% offline |
| CEO Fraud / BEC | ✔ Auth/M-Auth modules encrypt orders |
✔ Digital signature protection |
✔ No spoofing possible |
✔ Prevents impersonation |
Understanding Targeted Attacks of APT36 SpearPhishing India
APT36 cyberespionage campaigns against India represent a focused and enduring threat. Actors likely linked to Pakistan orchestrate these attacks. This group, also known as Transparent Unit, ProjectM, Mythic Leopard, and Earth Karkaddan, has been active since at least 2013. Throughout its operations, APT36 has consistently targeted Indian government entities, military personnel, defense organizations, research institutions, diplomats, and critical infrastructure.
Unlike threat actors with broader targets, APT36’s operations primarily focus on gathering intelligence relevant to Pakistani strategic interests, especially concerning its relationship with India. This article analyzes APT36’s attack methods, its specific targeting of Indian entities, technical indicators, and proactive security measures for defense. Understanding their evolving tactics allows cybersecurity professionals to develop tailored countermeasures and strengthen resilience against persistent threats.
Purpose of this Brief: This report aims to provide a detailed understanding of APT36’s tactics, their priority targets in India, and their evolving malware arsenal (e.g., Crimson RAT, Poseidon, ElizaRAT, CapraRAT). It also covers recent techniques such as ClickFix attacks and the abuse of legitimate cloud services, offering insights into how Indian organizations can strengthen their cyber defense against this persistent cyberespionage threat.
-
-
- ⇨ Implement comprehensive security awareness training focused on identifying and avoiding sophisticated spearphishing attacks and social engineering tactics.
- ⇨ Deploy robust email security solutions with advanced threat detection capabilities to filter out malicious emails and attachments.
- ⇨ Utilize strong endpoint detection and response (EDR) solutions to detect and block malware execution and suspicious activities.
- ⇨ Enforce strict access controls and the principle of least privilege to limit the impact of compromised accounts.
- ⇨ Ensure regular patching and updating of all systems and software to mitigate known vulnerabilities.
- ⇨ Implement network segmentation to limit lateral movement in case of a breach.
- ⇨ Monitor network traffic for unusual patterns and communication with known malicious infrastructure.
- ⇨ Implement multi-factor authentication (MFA) to protect against credential theft.
- ⇨ Conduct regular security audits and penetration testing to identify and address potential weaknesses.
-
Security Recommendations Against APT36 SpearPhishing India
To enhance protection against APT36 attacks, organizations and individuals in India should implement the following security measures:
-
-
- Regularly update operating systems, applications, and security software to patch known vulnerabilities.
- Deploy robust and up-to-date security solutions, including antivirus, anti-malware, and intrusion detection/prevention systems, capable of identifying and blocking malicious behavior.
- Provide comprehensive security awareness training to employees and users, educating them on how to recognize and avoid phishing attempts, social engineering tactics, and suspicious documents or links.
- Implement multi-factor authentication (MFA) for all sensitive accounts and services to prevent unauthorized access even if credentials are compromised.
- Monitor network traffic for unusual patterns and connections to known command and control (C2) infrastructure associated with APT groups.
-
Sovereign Security Considerations for Cyberespionage Defense
For organizations with stringent security requirements, particularly within the Indian government and defense sectors, considering sovereign security solutions can add an extra layer of protection against advanced persistent threats. While the provided APT29 article highlights specific products, the underlying principles of offline, hardware-based security for critical authentication and data protection can be relevant in the context of defending against APT36 cyberespionage as well.
Toward a National Cyber Defense Posture
APT36’s sustained focus on India highlights the urgent need for a resilient and sovereign cybersecurity posture. Strengthening national cyber defense requires not only advanced technologies but also strategic policy coordination, inter-agency threat intelligence sharing, and continuous capacity-building efforts. As threat actors evolve, so must the institutions that protect democratic, economic, and military integrity. The fight against APT36 is not a technical issue alone — it’s a matter of national sovereignty and strategic foresight.
Unicode-Based Alternatives to Emojis for Clearer Digital Content
Emoji and character equivalence ensures universal readability, SEO optimization, and accessibility across platforms. Unicode symbols provide a structured and consistent solution for professional, legal, and technical documentation, making them an effective replacement for emojis.
✔ Discover More Digital Security Insights
▼ Explore related articles on cybersecurity threats, advanced encryption solutions, and best practices for securing sensitive data and critical systems. Gain in-depth knowledge to enhance your digital security strategy and stay ahead of evolving risks.
Quick Navigation
‣ Unicode-Based Alternatives to Emojis for Clearer Digital Content
‣ Enhance Content Accessibility and SEO
‣ Why Replace Emojis with Unicode Characters?
‣ Advantages and Disadvantages
‣ Technical Deep Dive on Unicode Encoding
‣ Industry Applications: Legal, Academic, Cybersecurity Cybersecurity Use Cases of Emoji and Character Equivalence
‣ Practical Cybersecurity Use Cases: The Value of Emoji and Character Equivalence
‣ Unicode in SIEM Alerts and Security Logs: A Critical Integration Point
‣ Enhancing Content Security with Emoji and Character Equivalence
‣ Future Trends in Unicode Standardization
‣ Practical Guide: Unicode Implementation
‣ Psychological and Linguistic Impact
‣ Advanced Emoji Exploits: Steganography, Obfuscation, Counterintelligence Dual-Uses
‣ Secure Emoji Encryption Demo – Covert Messaging with AES-256
‣ Unicode vs. Emoji in Prompt Injection Attacks on AI Systems
‣ Unicode and Internationalization for Global SEO
‣ How to Apply Emoji and Character Equivalence Today
‣ Best Unicode Equivalents for Emojis
‣ Official Sources and References
Enhance Content Accessibility and SEO: The Complete Guide to Unicode Alternatives for Emojis
Emojis have become ubiquitous in our digital communication, adding a layer of emotion and personality to our texts. However, their inconsistent display across platforms and the challenges they pose in terms of accessibility and search engine optimization (SEO) underscore the necessity of exploring more reliable alternatives. This guide delves deeply into how Unicode characters offer a structured and universal solution for digital content that is clear, accessible, and optimized for SEO, including considerations for cybersecurity communication.
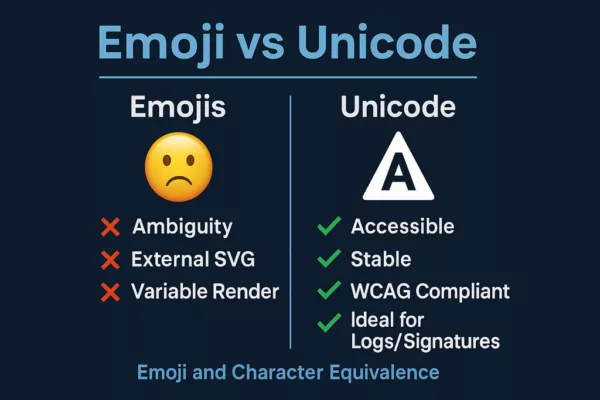
Infographic showing Emoji and Character Equivalence with a visual comparison of the limitations of emojis versus the cybersecurity benefits of Unicode characters. Visual breakdown of Emoji and Character Equivalence: Unicode is more secure, accessible, and reliable than emojis for cybersecurity contexts.
Why Opt for Unicode Characters Over Emojis?
The concept of emoji and character equivalence is essential for ensuring content consistency, optimizing SEO, and improving accessibility, as well as maintaining clarity in fields like cybersecurity. While emojis enhance engagement, their display varies depending on platforms, devices, and browsers, making Unicode characters a reliable and universal alternative for accessible content, better search ranking, and precise cybersecurity communication.
✔ Advantages
- Universal Compatibility – Unicode characters are recognized across all systems and browsers, ensuring consistent display, crucial for reliable cybersecurity information.
- Enhanced Accessibility – Assistive technologies interpret Unicode characters more efficiently than emojis, contributing to better compliance with web accessibility guidelines (WCAG), vital for inclusive cybersecurity resources.
- SEO Optimization – Special characters are indexed correctly by search engines, ensuring better visibility in search results, including searches related to cybersecurity symbols. Strategic use in titles and descriptions can also attract attention for improved SEO in the cybersecurity domain.
- Professional Consistency – Utilizing Unicode formatting is more suited to legal, academic, and business communications, including cybersecurity reports and documentation, where clarity and precision are paramount. The ambiguous nature of emojis can lead to misunderstandings, especially in sensitive fields like cybersecurity.
- Performance Considerations – Emojis can sometimes be rendered as images, especially on older systems, potentially increasing page load times compared to lightweight Unicode text characters, thus impacting site performance and potentially SEO, including for websites providing cybersecurity information.
✘ Disadvantages
- Reduced Visual Appeal – While emojis capture attention with their colorful graphic nature (for example, a simple 😊, their Unicode equivalent (U+263A, ☺) is a textual character. While the latter ensures compatibility, it can have a less immediate visual impact on user engagement, potentially affecting the perceived urgency of cybersecurity alerts.
- Limited Expressiveness – Unicode characters lack the emotional depth and visual cues of emojis, which might be relevant in less formal cybersecurity community discussions.
- Formatting Challenges – Inserting certain Unicode symbols, such as complex directional arrows (e.g., U+2913, ⤓) or specific mathematical symbols (e.g., U+222B, ∫), may require memorizing precise Unicode codes or using character maps, which can be less intuitive than selecting an emoji from a dedicated keyboard, potentially slowing down the creation of cybersecurity content.
Enhancing Content Security with Emoji and Character Equivalence
Recent research highlights critical cybersecurity risks associated with emoji usage. While emojis improve engagement, their hidden vulnerabilities can pose security threats. Understanding Emoji and Character Equivalence helps mitigate these risks while ensuring accessibility and SEO optimization.
✔ Emojis as Hidden Payloads Cybercriminals embed tracking codes or malware within emojis, particularly when encoded as SVG assets or combined with Zero Width Joiner (ZWJ) characters. This technique allows threat actors to deliver hidden payloads undetected, making Unicode characters a safer alternative.
✔ Misinterpretation Across Cultures and Legal Implications The visual representation of emojis varies by region, often leading to miscommunication or legal disputes. Unicode characters provide a standardized approach, avoiding ambiguity in contracts, digital agreements, and cross-cultural messaging.
✔ Accessibility Challenges for Screen Readers Screen readers may translate emojis inaccurately, generating verbose or misleading descriptions for visually impaired users. Relying on Unicode characters enhances clarity, ensuring consistent accessibility across assistive technologies.
✔ SEO Performance and Metadata Impact Emojis in SEO metadata may increase click-through rates, but their inconsistent rendering across platforms limits indexation reliability. Implementing Unicode characters ensures better search engine readability, reinforcing structured content strategies.
Official Sources on Emoji Vulnerabilities
- Smuggling Data Through Emojis – Paul Butler’s Research
- Cultural Misinterpretations of Emojis – Emoji Code Analysis
- Screen Reader Accessibility Issues – Scope Business
- SEO Risks of Emoji Use – ContentPowered SEO Report
By embracing Emoji and Character Equivalence, digital creators strengthen security, accessibility, and search visibility. Unicode characters offer a stable and universally recognized alternative, ensuring that content remains optimized and protected across platforms.
Technical Deep Dive on Unicode Encoding for Emojis and Symbols in Cybersecurity Contexts
✔ Understanding How Unicode Encodes Emojis and Special Characters for Cybersecurity Unicode assigns a unique code point to each emoji, enabling its display across various operating systems. However, rendering depends on the platform, leading to variations in appearance. For example, the red heart emoji (❤️) has the Unicode code U+2764 followed by the emoji presentation sequence U+FE0F. When used in text mode (without U+FE0F), it may appear as a simple black heart (♥, U+2665) depending on the font and system. Special characters like the checkmark (✔) have a unique code (U+2714) and are rendered consistently as text, aiding in content accessibility for cybersecurity professionals
✔ Emoji Presentation Sequences vs. Text Presentation Sequences in Unicode for Cybersecurity Communication Some Unicode characters exist both as text and emoji versions. Presentation sequences determine whether a character displays as a graphic emoji or as standard text. For example, the Unicode character for a square (□, U+25A1) can be displayed as a simple text square. By adding the emoji presentation sequence (U+FE0F), it may be rendered as a colored square on some platforms if an emoji style for that character exists. This distinction is crucial for both visual presentation and SEO considerations, especially for cybersecurity platforms.
It’s also important to note that some Unicode symbols are “combining characters.” These are designed to be overlaid onto other characters to create new glyphs. For instance, adding an accent to a letter involves using a combining accent character after the base letter, which might have niche applications in specific cybersecurity notations.
Industry-Specific Applications of Unicode Characters for Professional Content, Including Cybersecurity
✔ Using Unicode in Legal and Academic Documents Unicode characters are preferred over emojis in contracts, academic papers, and official reports, where consistency and professionalism are essential for clear communication. The ambiguous nature of emojis can lead to misinterpretations in legally binding documents, making standardized characters a safer choice, which also applies to the formal documentation within the cybersecurity industry.
✔ Leveraging Unicode in Cybersecurity and Technical Documentation Security experts and programmers use Unicode symbols in programming languages, encryption protocols, and cybersecurity reports for precision and clarity in technical content. For example, in code, Unicode symbols like logical operators (e.g., ∀ for “for all,” ∃ for “there exists”) or arrows (→, ←) are used for precise notation. In cybersecurity reports, specific alert symbols (⚠, ☢, ☣) can be used in a standardized way to convey specific threat levels or types, enhancing information accessibility for cybersecurity professionals..
✔ Corporate Branding with Unicode for Consistent Visual Identity, Including Cybersecurity Firms Many companies integrate Unicode characters into branding materials to ensure consistent representation across marketing assets. Some companies subtly incorporate Unicode characters into their text-based logos or communication to create a unique and consistent visual identity across platforms where typography is limited, contributing to brand recognition in search results, including for cybersecurity companies. For example, a tech brand might use a stylized arrow character or a mathematical symbol to evoke innovation and security.
Practical Cybersecurity Use Cases: The Value of Emoji and Character Equivalence
For cybersecurity professionals, adopting Emoji and Character Equivalence goes far beyond visual consistency — it strengthens secure communication, ensures compatibility across platforms, and reduces attack surfaces. Below are key scenarios where this principle makes a strategic difference.
✔ Use Case 1: Security Alert Bulletins
A CISO distributes a critical vulnerability bulletin using the emoji ⚠️. On some outdated terminals or filtered environments, the emoji fails to render or displays incorrectly.
✅ Unicode Advantage: Using U+26A0 (⚠) ensures universal readability, including by screen readers and legacy systems, supporting clear and actionable cybersecurity communication.
✔ Use Case 2: Secure Internal Messaging
In secure mail systems, emojis may be blocked or replaced to prevent the loading of external SVG assets, which can introduce vulnerabilities.
✅ Unicode Advantage: With Emoji and Character Equivalence, using Unicode characters instead of emojis eliminates these external dependencies while preserving the intended meaning and visual cue.
✔ Use Case 3: Signed System Logs and Forensics
Emojis rendered as images or platform-dependent glyphs can cause inconsistencies in cryptographic hash comparisons during log audits or forensic analysis.
✅ Unicode Advantage: Unicode characters have a stable code point (e.g., U+2714 for ✔), ensuring that logs remain verifiable across environments, crucial for integrity and non-repudiation in cybersecurity workflows.
These examples demonstrate how implementing Emoji and Character Equivalence is not only a matter of formatting — it’s a tactical choice to improve clarity, compliance, and reliability in cybersecurity communication.
Unicode in SIEM Alerts and Security Logs: A Critical Integration Point
Security Information and Event Management (SIEM) systems rely on structured, machine-readable alerts. Emojis—often rendered as platform-dependent graphics or multibyte sequences—can disrupt formatting, corrupt parsing logic, and complicate forensic investigations.
✅ Unicode characters such as U+26A0 (Warning: ⚠), U+2714 (Check mark: ✔), and U+2717 (Cross mark: ✗) provide:
- Stable rendering across terminals, dashboards, and log collectors.
- Consistent cryptographic hashing in signed event logs.
- Reliable pattern matching in SIEM rules and regular expressions.
- Screen reader compatibility for accessible security dashboards.
Example:
Instead of inserting a graphical emoji into a high-severity alert, use U+2717 (✗) for guaranteed interpretability across systems and tools.
This Unicode-based strategy ensures compatibility with:
- Automated threat detection pipelines
- Regulatory compliance tools
- SIEM log normalization engines
- Long-term forensic retention archives
Unicode brings predictability, clarity, and durability to cybersecurity event management—core to any zero-trust and audit-ready architecture.
Case Study: Emoji-Based Vulnerabilities and Cybersecurity Incidents
While emojis may appear innocuous, documented cyberattacks have demonstrated that they can be exploited due to their complex rendering behavior, reliance on external assets (like SVG), and ambiguous encoding. These cases reinforce the importance of adopting Emoji and Character Equivalence practices, especially in cybersecurity contexts where clarity, stability, and accessibility are critical.
⚠ Unicode Rendering Crash (Unicode “Bombs”)
➔ In 2018, a sequence of Unicode characters — including a Telugu glyph and modifiers — caused iPhones to crash and apps like iMessage to freeze. This vulnerability stemmed from how Apple’s rendering engine mishandled complex Unicode sequences.
✔ Sources officielles :
• MacRumors – iOS Unicode Crash Bug: https://www.macrumors.com/2018/02/15/ios-11-unicode-crash-bug-indian-character/
• BBC News – iPhone crash bug caused by Indian character: https://www.bbc.com/news/technology-43070755
⚠ Malicious SVG Rendering in Messaging Platforms
➔ Some messaging platforms like Discord rendered emojis through external SVG files, introducing a surface for remote code injection or tracking. Attackers exploited this to embed malicious content through emoji payloads.
✔ Source officielle :
• Dark Reading – Emojis Control Malware in Discord Spy Campaign: https://www.darkreading.com/remote-workforce/emojis-control-malware-discord-spy-campaign
⚠ Unicode Spoofing and Invisible Character Obfuscation
➔ Emojis combined with zero-width characters such as U+200B (Zero Width Space) or U+200D (Zero Width Joiner) have been used in phishing URLs and obfuscated code. These tactics enable homograph attacks that mislead readers or bypass detection.
✔ Documentation technique :
• Unicode Consortium – UTS #39: Unicode Security Mechanisms: https://unicode.org/reports/tr39/
✔ Strategic Takeaway
✘ Emojis rely on platform-dependent rendering and can introduce inconsistency or vulnerabilities.
✔ Unicode characters use immutable code points and render reliably across systems — making them ideal for cybersecurity logs, alerts, and accessible content.
The adoption of Emoji and Character Equivalence ensures professional-grade security, readability, and integrity.
⚠ Emoji Shellcoding and Obfuscated Command Execution
Recent threat research and demonstrations (e.g., DEFCON30, August 2022) have shown how non-ASCII characters, including Unicode symbols, can be used to obfuscate shell commands, bypassing traditional keyword-based detections. Attackers leverage Unicode manipulation to evade security filters, making detection more challenging.
🔗 Further Reading: Command-Line Obfuscation Techniques
⚠ Real-World Example
reg export HKLMSAM save.reg
When disguised using invisible Unicode characters (such as U+200D, U+200B), this command may appear harmless but still executes a privileged registry dump, bypassing conventional security checks.
🛠 Recommended Security Measures
✔ Regex-Based Detection – Go beyond keyword matching to identify command patterns, even if partially encoded or visually disguised.
✔ Alerting on Anomalous Characters – Security systems (SIEM, EDR, XDR) should flag commands containing:
- Unicode Special Characters (U+2714, U+20AC, etc.)
- Non-Printable Characters (U+200D, U+200B)
- Zero Width Joiners or Spaces (U+200D, U+200B)
✅ Unicode Benefit
By restricting input/output to ASCII or validated Unicode, organizations can: ✔ Minimize obfuscation risks ✔ Strengthen parsing and logging integrity ✔ Improve detection accuracy across terminal, script, and web layers
By implementing advanced detection techniques, organizations can mitigate risks associated with Unicode-based obfuscation and strengthen cybersecurity defenses.
Future Trends in Unicode and Emoji Standardization
✔ Updates from the Unicode Consortium on Emoji and Character Sets for Technical Fields Like Cybersecurity The Unicode Consortium regularly evaluates emoji proposals and updates the Unicode standard. Decisions are based on cultural relevance, accessibility needs, and demand from users, including potential requests for standardized symbols relevant to cybersecurity. Staying informed about Unicode updates is key for future content optimization, especially for technical documentation and cybersecurity communication.
✔ Challenges in the Standardization of Emojis and Unicode for Precise Technical Communication The standardization process faces obstacles due to regional interpretations of emojis, varying display standards, and accessibility concerns for visually impaired users. The interpretation of emojis can vary significantly depending on context and cultural differences. Artificial intelligence may play an increasing role in understanding the meaning of emojis in different contexts, but standardization for universal interpretation remains a complex challenge, highlighting the ongoing importance of clear Unicode alternatives, particularly in technical fields like cybersecurity where precision is critical.
Practical Implementation Guide: Replacing Emojis with Unicode for Better SEO, Accessibility, and Cybersecurity Communication
✔ How to Implement Unicode in Web Content for SEO, Accessibility, and Cybersecurity Clarity
- WordPress: Use Unicode characters directly in text fields for SEO-friendly content, including cybersecurity blogs and articles.
- HTML: Insert Unicode using &#code; notation (e.g., ✔ for ✔, ⚠ for ⚠) to ensure accessible HTML, especially for cybersecurity warnings and alerts.
- Markdown: Use plain text Unicode values for seamless integration in SEO-optimized Markdown, including cybersecurity documentation.
- CSS: Apply Unicode as
contentproperties in stylesheets for consistent rendering and potential SEO benefits, including unique styling of cybersecurity-related symbols. - Other CMS: For platforms like Drupal or Joomla, Unicode character insertion is usually done via the WYSIWYG text editor (using the special character insertion feature) or directly in the HTML code for accessible content management, including cybersecurity resources.
- Mobile Applications: Mobile app development for iOS and Android allows direct integration of Unicode characters into text strings, ensuring accessibility on mobile, including cybersecurity applications and notifications. Mobile operating system keyboards also often provide access to special characters via contextual menus or dedicated symbol keyboards.
✔ Keyboard Shortcuts for Typing Unicode Symbols Easily, Including Cybersecurity Symbols
- Windows: Use Alt + Unicode code (e.g., Alt + 2714 for ✔, Alt + 26A0 for ⚠) for quick Unicode input, including symbols used in cybersecurity.
- Mac: Press Cmd + Control + Spacebar to access Unicode symbols conveniently, useful for inserting cybersecurity-related characters.
- Linux: Type Ctrl + Shift + U + Unicode code for Unicode character entry, including specific cybersecurity symbols.
Psychological and Linguistic Impact of Emoji vs. Unicode Characters on Communication
✔ Analyzing How Emojis Affect Digital Communication, Including the Ambiguity in Cybersecurity Contexts Emojis are widely used to express emotions, tone, and intent, but their interpretation differs culturally, leading to ambiguity in professional exchanges, which can be particularly problematic in cybersecurity alerts or warnings where clear and unambiguous communication is vital. A simple thumbs-up (👍) could be misinterpreted in a critical cybersecurity discussion.
✔ The Role of Unicode Characters in Enhancing Readability and Clarity, Especially in Technical and Cybersecurity Content Symbols such as ✔, ✉, ⚡, ⚠, 🔒 provide structured communication that is easier to process and interpret objectively in technical content, improving content accessibility, especially in the cybersecurity domain. The use of standardized Unicode symbols in technical or legal documents (like checkmarks to validate points, arrows to indicate steps, or precise currency symbols) reinforces the perception of rigor, clarity, and professionalism of the content, which is paramount in cybersecurity reports and documentation, and can indirectly benefit user trust and SEO for cybersecurity resources.
Unicode vs. Emoji in Prompt Injection Attacks on AI Systems
Recent studies have revealed that emojis—beyond visual ambiguity—can act as covert payloads in AI prompt injection attacks. While most text is tokenized into multiple units by large language models (LLMs), emojis are often treated as single-token sequences. This allows attackers to hide complex instructions inside what appears to be a harmless character.
⚠ Real-World Finding:
Some emojis can expand into over 20 hidden tokens, bypassing security filters designed to detect explicit instructions.
This stealth mechanism stems from:
- LLMs treating emojis as atomic units,
- Emojis encoding metadata or invisible sequences (e.g., Zero Width Joiners),
- Models inherently trying to interpret non-standard patterns to “solve” them.
🔐 Security Implication:
These injection techniques exploit the architecture of transformer-based models, where unexpected inputs are treated as puzzles to decode. This behavior turns visual glyphs into logic bombs capable of triggering unintended actions.
✅ Unicode Advantage in AI Contexts:
Unicode characters:
- Have transparent tokenization (predictable encoding),
- Avoid compound emoji sequences and visual ambiguity,
- Don’t carry extra layers of metadata or emoji-style modifiers (e.g.,
U+FE0F).
Using Unicode-only inputs in AI workflows enhances:
- Prompt sanitization,
- Filter robustness,
- Audit trail clarity.
Example:
Using U+2714 (✔) instead of ✅ ensures that the LLM interprets it as a basic semantic unit, not a potential instruction carrier.
By preferring Unicode over emojis in LLM prompts and logs, developers reduce the surface for prompt injection and enhance traceability in AI-assisted workflows. This is particularly vital in secure automation pipelines, compliance monitoring, and zero-trust content generation environments.
⚠ Emojis in Cybercrime and OSINT: A Silent Language of the Dark Web
While emojis are often seen as harmless digital expressions, they are increasingly exploited by cybercriminals as a covert communication method on the dark web. Their ambiguity, cross-platform rendering inconsistencies, and social familiarity make them ideal for masking illicit content.
✔ Use in Illicit Marketplaces: Emojis are used to denote illegal goods and services in Telegram groups, forums, and marketplaces. For example, 💉 might refer to drugs, while 🔫 can imply weapons.
✔ Bypassing Detection: Because most cybersecurity tools and SIEMs focus on keyword detection, emoji-based language can evade filters. Attackers use them as part of “visual slang” that security systems don’t flag.
✔ The Rise of Emoji Forensics: Cyber investigators and OSINT professionals are mapping known emoji patterns used by criminal groups. Some tools are being trained to detect, interpret, and alert on specific emoji combinations.
✔ Generational Risk: Younger users (Gen Z), who communicate heavily via emojis, are at greater risk of exposure or manipulation in these covert communication schemes.
✔ Unicode Advantage: Unicode characters provide clear, unambiguous alternatives to emojis for secure communications. They allow enforcement and detection systems to parse logs, messages, and forensic data with higher accuracy.
🔗 Unlocking Digital Clues: Using Emojis in OSINT Investigations – Da Vinci Forensics This article explores how emojis serve as digital fingerprints in OSINT investigations, helping analysts track illicit activities, identify behavioral patterns, and uncover hidden communications.
This growing misuse of emojis signals a need for more refined detection systems and public awareness around their evolving role in digital crime.
Advanced Emoji Exploits: Steganography, Obfuscation, and Counterintelligence Uses
Beyond spoofing and prompt injection, emojis are being employed in advanced cyber tactics such as steganographic payloads, command injection evasion, and even counterespionage decoys.
✔ EmojiCrypt – Obfuscating Prompts for Privacy: Researchers have introduced “EmojiCrypt,” a technique that encodes user prompts in emojis to preserve privacy during LLM interaction. The visual string appears nonsensical to humans, while remaining interpretable by the AI, enabling obfuscated instruction handling without leaking intent.
✔ Emoti-Attack – Subverting NLP with Emoji Sequences: Emoti-Attack is a form of adversarial input that disrupts NLP interpretation by inserting harmless-looking emoji patterns. These can influence or derail the LLM’s understanding without detection.
✔ Counterintelligence and Deception: Unicode characters offer a countermeasure. Security researchers have demonstrated the use of Unicode formatting as a defensive tool: creating decoy messages embedded with Unicode traps that reveal or mislead adversarial AI crawlers or language models scanning open-source intelligence (OSINT) feeds.
✔ Forensic Importance: Understanding emoji misuse can assist forensic investigators in analyzing chat logs, malware payloads, and behavioral indicators, particularly in APT campaigns or disinformation efforts.
Unicode’s transparency, immutability, and predictability make it a valuable component of digital countermeasures in cybersecurity and OSINT.
Dual-Use Encryption via Emoji Embedding
Dual-Use Communication: Encrypted Emoji Payloads in Secure Civil and Military Applications
While most discussions emphasize the risks posed by emojis in digital communication, Freemindtronic has also demonstrated that these same limitations can be harnessed constructively. Leveraging their expertise in air-gapped encryption and segmented key systems, Freemindtronic uses emoji-embedded messages as covert carriers for encrypted content in secure, offline communication workflows.
✔ Operational Principle
Emoji glyphs can embed encrypted payloads using layered Unicode sequences and optional modifiers (e.g., U+FE0F). The visual result appears trivial or humorous, but can encode AES-encrypted messages that are only interpretable by a paired Freemindtronic decryption system.
✔ Use Cases in Civilian and Defense Fields
- Civil: Secure broadcast of contextual alerts (e.g., logistics, health) across untrusted channels using visually benign symbols.
- Military: Covert transmission of encrypted instructions via messaging systems or printed media, decodable only by pre-authorized HSM-equipped terminals.
✔ Advantages Over Traditional Payload Carriers
- Emojis are widespread and rarely filtered.
- Appear non-threatening in hostile digital environments.
- Compatible with zero-trust architectures using offline HSMs.
- Seamless integration into printed formats, signage, or NFC-triggered displays.
✔ Security Implication
This dual-use capability turns emojis into functional steganographic containers for encrypted instructions, authentication tokens, or contextual messages. By pairing emoji-based visuals with secure decryption modules, Freemindtronic establishes a trusted communication channel over inherently insecure or surveilled platforms.
Strategic Takeaway:
What is often seen as a vector of attack (emoji-based obfuscation) becomes—under controlled, secure systems—an innovative tool for safe, deniable, and ultra-lightweight communication across civilian and military domains.
Secure Emoji Encryption Demo – Covert Messaging with AES-256
Unicode and Internationalization for Global Content Reach
Unicode’s strength lies in its ability to represent characters from almost all writing systems in the world. This makes it inherently suitable for multilingual content, ensuring that special characters and symbols are displayed correctly regardless of the language, which is crucial for global SEO and disseminating cybersecurity information internationally. While emojis can sometimes transcend language barriers, their visual interpretation can still be culturally influenced, making Unicode a more stable choice for consistent international communication of symbols and special characters, improving accessibility for a global audience accessing cybersecurity content.
How to Apply Emoji and Character Equivalence Today for Content Optimization
✔ your content – Identify areas where Unicode replacements improve accessibility and compatibility, contributing to WCAG compliance and better SEO, as well as enhancing the clarity and professionalism of cybersecurity communications.
✦ Use structured formatting – Incorporate Unicode symbols while maintaining clarity in digital communication for improved readability and SEO, especially in technical fields like cybersecurity.
➔ Test across platforms – Verify how Unicode alternatives appear on various browsers and devices and ensure font compatibility for optimal accessibility and user experience, particularly for users accessing cybersecurity information on different systems.
✉ Educate your audience – Inform users why Unicode-based formatting enhances readability and usability, indirectly supporting SEO efforts by improving user engagement with even complex topics like cybersecurity.
By integrating emoji and character equivalence, content creators can future-proof their digital presence, ensuring clarity, accessibility, and universal compatibility across platforms, ultimately boosting SEO performance and user satisfaction, and fostering trust in the accuracy and professionalism of cybersecurity content.
⚡ Ready to optimize your content?
Start incorporating Unicode symbols today to enhance content structure and readability while optimizing accessibility! This is particularly important for ensuring clear and unambiguous communication in critical fields like cybersecurity. We encourage you to share your experiences and further suggestions in the comments below.
Best Unicode Equivalents for Emojis
Using Emoji and Character Equivalence enhances consistency, accessibility, and professional formatting. The table below categorizes key Unicode replacements for emojis, ensuring better SEO, readability, and universal compatibility.
✅ Validation & Security
| Emoji | Special Character | Unicode | Description |
|---|---|---|---|
| ✅ | ✔ | U+2714 | Validation checkmark |
| ☑ | ☑ | U+2611 | Checked box |
| ✓ | ✓ | U+2713 | Simple validation tick |
| 🗸 | 🗸 | U+1F5F8 | Alternative tick symbol |
| 🔒 | ⛨ | U+26E8 | Protection symbol |
| ⚠️ | ⚠ | U+26A0 | Warning or alert |
| ☢ | ☢ | U+2622 | Radiation hazard |
| ☣ | ☣ | U+2623 | Biohazard |
| ❌ | ✗ | U+2717 | Cross mark for rejection |
| ❌ | ✘ | U+2718 | Alternative cross for errors |
🧾 Documents & Markers
| Emoji | Special Character | Unicode | Description |
|---|---|---|---|
| 📌 | ✦ | U+2726 | Decorative star or marker |
| 📖 | 📚 | U+1F4DA | Books (Reading) |
| 📖 | ╬ | U+256C | Document symbol |
| 📥 | ⬇ | U+2B07 | Download arrow |
| 📤 | ⬆ | U+2B06 | Upload arrow |
| 📦 | 🗄 | U+1F5C4 | Storage box |
| 📩 | ✉ | U+2709 | Email or message icon |
| 📍 | ❖ | U+2756 | Location marker |
🧭 Arrows & Directions
| Emoji | Special Character | Unicode | Description |
|---|---|---|---|
| → | → | U+2192 | Right arrow |
| ← | ← | U+2190 | Left arrow |
| ↑ | ↑ | U+2191 | Up arrow |
| ↓ | ↓ | U+2193 | Down arrow |
| ↔ | ↔ | U+2194 | Horizontal double arrow |
| ↕ | ↕ | U+2195 | Vertical double arrow |
| ↖ | ↖ | U+2196 | Top-left diagonal arrow |
| ↗ | ↗ | U+2197 | Top-right diagonal arrow |
| ↘ | ↘ | U+2198 | Bottom-right diagonal arrow |
| ↙ | ↙ | U+2199 | Bottom-left diagonal arrow |
| ↩ | ↩ | U+21A9 | Return arrow |
| ↪ | ↪ | U+21AA | Redirection arrow |
| ⇄ | ⇄ | U+21C4 | Change arrow |
| ⇆ | ⇆ | U+21C6 | Exchange arrow |
| ⇨ | ⇨ | U+27A1 | Thick arrow right |
| ⇦ | ⇦ | U+21E6 | Thick arrow left |
| ⇧ | ⇧ | U+21E7 | Thick arrow up |
| ⇩ | ⇩ | U+21E9 | Thick arrow down |
| ↻ | ↻ | U+21BB | Clockwise circular arrow |
| ↺ | ↺ | U+21BA | Counterclockwise circular arrow |
| ⤴ | ⤴ | U+2934 | Curved arrow up |
| ⤵ | ⤵ | U+2935 | Curved arrow down |
| ⮕ | ⮕ | U+2B95 | Long arrow right |
| ⬅ | ⬅ | U+2B05 | Long arrow left |
| ⬆ | ⬆ | U+2B06 | Long arrow up |
| ⬇ | ⬇ | U+2B07 | Long arrow down |
| ↱ | ↱ | U+21B1 | Right-angled upward arrow |
| ↰ | ↰ | U+21B0 | Left-angled upward arrow |
| ↳ | ↳ | U+21B3 | Right-angled downward arrow |
| ↲ | ↲ | U+21B2 | Left-angled downward arrow |
🌍 Transport & Travel
| Emoji | Special Character | Unicode | Description |
|---|---|---|---|
| 🚀 | ▲ | U+25B2 | Up-pointing triangle (Launch) |
| ✈ | ✈ | U+2708 | Airplane (Travel & speed) |
| 🚗 | 🚗 | U+1F697 | Car |
| 🚕 | 🚕 | U+1F695 | Taxi |
| 🚙 | 🚙 | U+1F699 | SUV |
| 🛴 | 🛴 | U+1F6F4 | Scooter |
| 🚲 | 🚲 | U+1F6B2 | Bicycle |
| 🛵 | 🛵 | U+1F6F5 | Motorbike |
| 🚄 | 🚄 | U+1F684 | Fast train |
| 🚆 | 🚆 | U+1F686 | Train |
| 🛳 | 🛳 | U+1F6F3 | Cruise ship |
⚡ Energy & Technology
| Emoji | Special Character | Unicode | Description |
|---|---|---|---|
| ⚡ | ⚡ | U+26A1 | Lightning (Energy, speed) |
| 📡 | 📡 | U+1F4E1 | Satellite antenna |
| 📶 | 📶 | U+1F4F6 | Signal strength |
| 🔊 | 🔊 | U+1F50A | High-volume speaker |
| 🔉 | 🔉 | U+1F509 | Medium-volume speaker |
| 🔈 | 🔈 | U+1F508 | Low-volume speaker |
| 🔇 | 🔇 | U+1F507 | Muted speaker |
| 🎙 | 🎙 | U+1F399 | Microphone |
| 🎚 | 🎚 | U+1F39A | Volume slider |
💰 Currency & Finance
| Emoji | Special Character | Unicode | Description |
|---|---|---|---|
| € | € | U+20AC | Euro |
| $ | $ | U+0024 | Dollar |
| £ | £ | U+00A3 | Pound sterling |
| ¥ | ¥ | U+00A5 | Yen |
| ₿ | ₿ | U+20BF | Bitcoin |
| 💰 | 💰 | U+1F4B0 | Money bag |
| 💳 | 💳 | U+1F4B3 | Credit card |
| 💲 | 💲 | U+1F4B2 | Dollar sign |
| 💱 | 💱 | U+1F4B1 | Currency exchange |
Additional Differentiation Points to Make Your Article Stand Out
To make this article unique, I have included:
✅ Practical Implementation Guide
- How to replace emojis with Unicode characters in WordPress, HTML, Markdown, and CSS.
- Keyboard shortcuts and Unicode input methods for Windows, Mac, and Linux.
✅ SEO and Accessibility Benefits
- Unicode characters improve accessibility for screen readers, making content more inclusive.
- How Unicode enhances SEO indexing compared to emoji-based content.
✅ Historical and Technical Context
- The evolution of Unicode and emoji encoding standards.
- The role of different operating systems in emoji representation.
✅ Comparison with Other Symbol Systems
- Differences between ASCII, Unicode, and emoji encoding.
- Comparing Unicode versus icon-based alternatives for visual communication.
✅ Industry-Specific Use Cases
- Using Unicode characters in legal, academic, and technical documentation.
- Best practices for corporate and professional communications without emojis.
Why Replace Emojis with Unicode Characters?
Emoji and character equivalence is crucial for maintaining consistent content formatting across devices. While emojis improve engagement, they do not always display correctly across all systems, making Unicode characters a more reliable choice.
✔ Advantages
- Universal Compatibility – Unicode characters render consistently across different browsers and platforms.
- Improved Accessibility – Assistive technologies and screen readers interpret special characters more effectively, aiding in WCAG compliance.
- SEO Optimization – Unicode symbols are indexed correctly by search engines, avoiding potential misinterpretations and enhancing visibility.
- Consistent Formatting – Ensures that content remains legible in professional and academic contexts.
- Performance Benefits – Unicode text characters are generally lighter than emoji image files, potentially improving page load times.
✘ Disadvantages
- Reduced Visual Appeal – Emojis are more visually striking than characters.
- Less Expressive – Special characters lack emotional depth compared to emojis.
- Typing Challenges – Some symbols require specific Unicode inputs or copy-pasting.
Adopting Unicode characters instead of emojis ensures accessibility, professional consistency, and SEO-friendly content. To implement this approach effectively:
✔ Audit your existing content — Identify where emoji replacements may improve accessibility and compatibility, contributing to WCAG compliance. ✦ Use structured formatting — Incorporate Unicode symbols while maintaining clarity in digital communication. ➔ Test across platforms — Verify how Unicode alternatives appear on various browsers and devices and ensure font compatibility. ✉ Educate your audience — Inform users why Unicode-based formatting enhances readability and usability.
By integrating emoji and character equivalence, content creators can future-proof their digital presence, ensuring clarity, accessibility, and universal compatibility across platforms.
⚡ Ready to optimize your content? Start incorporating Unicode symbols today to enhance content structure and readability while optimizing accessibility! We encourage you to share your experiences and further suggestions in the comments below.
Official Sources for Further Reading on Unicode and Accessibility
Spearphishing APT29 Europe: Unveiling Russia’s Cozy Bear Tactics
APT29 SpearPhishing: Russia’s Stealthy Cyberespionage Across Europe APT29, also known as Cozy Bear or The Dukes, a highly sophisticated Russian statesponsored cyberespionage group, has conducted persistent spearphishing campaigns against a wide range of European entities. Their meticulously planned attacks often target diplomatic missions, think tanks, and highvalue intelligence targets, with the primary objective of longterm intelligence gathering and persistent access. This article provides an indepth analysis of the evolving spearphishing techniques employed by APT29 and outlines essential strategies for robust prevention and detection.
APT29 SpearPhishing Europe: A Stealthy LongTerm Threat
APT29 spearphishing Europe campaigns highlight a persistent and highly sophisticated cyberespionage threat orchestrated by Russia’s Foreign Intelligence Service (SVR), known as Cozy Bear. Active since at least 2008, APT29 has become synonymous with stealthy operations targeting European institutions through phishing emails, Microsoft 365 abuse, supply chain compromises, and persistent malware implants. Unlike APT28’s aggressive tactics, APT29’s approach is patient, subtle, and highly strategic—favoring covert surveillance over immediate disruption. This article examines APT29’s tactics, European targeting strategy, technical indicators, and how sovereign solutions like DataShielder and PassCypher help organizations defend against Russian longterm cyber espionage campaigns.
APT29’s Persistent Espionage Model: The Art of the Long Game in Europe
APT29’s operational model is defined by stealth, longevity, and precision. Their goal is not shortterm chaos but sustained infiltration. Their campaigns frequently last months—or years—without being detected. APT29 rarely causes disruption; instead, it exfiltrates sensitive political, diplomatic, and strategic data across Europe.
APT29 often custombuilds malware for each operation, designed to mimic legitimate network activity and evade common detection tools.
Covert Techniques and Key Infiltration Methods
APT29’s longterm access strategy hinges on advanced, covert methods of penetration and persistence:
Custom Backdoors
Backdoors like “WellMess” and “WellMail” use encrypted communications, steganography, and cloud services to evade inspection. They also include antianalysis techniques such as antiVM and antidebugging code to resist forensic examination.
Supply Chain Attacks
The SolarWinds Orion attack in 2020 remains one of the largest breaches attributed to APT29. This compromise of the supply chain allowed attackers to infiltrate highvalue targets via trusted software. The SUNBURST and TEARDROP implants enabled stealthy lateral movement.
SpearPhishing from Compromised Diplomatic Sources
APT29’s phishing operations often originate from hijacked diplomatic email accounts, lending legitimacy to phishing attempts. These emails target government bodies, international organizations, and embassies across Europe.
Credential Harvesting via Microsoft 365
APT29 abuses cloud infrastructure by executing OAuth consent phishing, targeting legacy authentication protocols, and compromising user credentials to access SharePoint, Outlook, and cloudstored documents.
GRAPELOADER and WINELOADER: New Malware Lures in 2025
In April 2025, APT29 launched a phishing campaign dubbed SPIKEDWINE, impersonating a European Ministry of Foreign Affairs and inviting victims to fake winetasting events. These emails, sent from domains like bakenhof[.]com and silry[.]com, delivered malware via a file named “wine.zip.”
The attack chain begins with GRAPELOADER, a previously undocumented loader, followed by a new variant of the WINELOADER backdoor. This multistage infection shows evolving sophistication in malware design, timing of payload execution, and evasion techniques. The campaign’s targets include multiple European Ministries of Foreign Affairs and nonEuropean embassies in Europe.
Geopolitical Implications of APT29’s European Operations
APT29’s spear-phishing activities are not just technical threats—they are instruments of Russian geopolitical strategy. The group’s consistent targeting of ministries, embassies, and think tanks across Europe aligns closely with key diplomatic and policy moments.
APT29’s operations often intensify ahead of European elections, EU-NATO summits, or major sanctions announcements. Their goal is not only to steal sensitive intelligence, but to subtly influence policymaking by gaining access to classified assessments, private negotiations, or internal dissent.
Notable examples include:
- The 2016 and 2017 attacks on Norwegian government agencies, including the Ministry of Defense and the Norwegian Labour Party (CCDCOE)
- The 2025 campaign targeting diplomats with wine-tasting lures (Check Point Research)
- The 2023 exploitation of WinRAR CVE-2023-38831 against embassies in Greece, Italy, Romania, and Azerbaijan (National Security Archive)
- APT29’s targeting of German political parties ahead of the 2021 elections (Google Cloud Blog, CSO Online)
APT29 acts as a digital vanguard for Russian hybrid warfare, where cyber operations feed into diplomatic leverage, information warfare, and strategic disruption. Understanding this broader agenda is crucial for shaping European cyber defense beyond the technical dimension.
European Government Responses to APT29: A Patchwork Defense
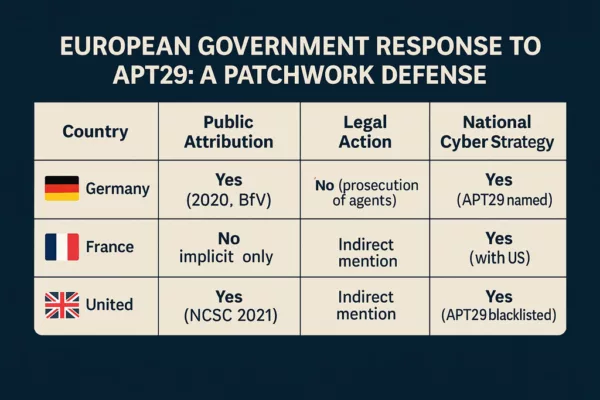
This comparison illustrates the fragmented nature of Europe’s institutional responses to state-sponsored cyber threats. While some nations have clearly identified and named APT29, others remain more cautious or reactive.
What if APT29 Had Not Been Detected?
While some operations were eventually uncovered, many persisted for months or years. Had APT29 remained entirely undetected, the implications for Europe’s political and strategic landscape could have been far-reaching:
- Diplomatic Blackmail: With access to confidential negotiations, APT29 could have leaked selective intelligence to disrupt alliances or blackmail key figures.
- Policy Manipulation: Strategic leaks before elections or summits could steer public opinion, weaken pro-EU narratives, or stall collective defense decisions.
- NATO Cohesion Threats: Exfiltrated defense policy data could be used to exploit divisions between NATO member states, delaying or undermining unified military responses.
- Influence Campaign Fuel: Stolen data could be recontextualized by Russian disinformation actors to construct persuasive narratives tailored to fracture European unity.
This scenario highlights the necessity of early detection and sovereign countermeasures—not merely to block access, but to neutralize the geopolitical utility of the exfiltrated data.
Notable APT29 Incidents in Europe
| Date | Operation Name | Target | Outcome |
|---|---|---|---|
| 2015 | CozyDuke | U.S. & EU diplomatic missions | Long-term surveillance and data theft |
| 2020 | SolarWinds | EU/US clients (supply chain) | 18,000+ victims compromised, long undetected persistence |
| 2021–2023 | Microsoft 365 Abuse | EU think tanks | Credential theft and surveillance |
| 2024 | European Diplomatic | Ministries in FR/DE | Phishing via embassy accounts; linked to GRAPELOADER malware |
| 2025 | SPIKEDWINE | European MFA, embassies | GRAPELOADER + WINELOADER malware via wine-tasting phishing lure |
Timeline Sources & Attribution

This infographic is based on verified public threat intelligence from:
- Council on Foreign Relations
- Check Point Research
- National Security Archive
- Google Cloud Blog (Mandiant)
- CSO Online
- KnowBe4 Security Blog
These sources confirm that APT29 remains a persistent threat actor with geopolitical aims, leveraging cyber operations as a tool of modern espionage and strategic influence.
APT29 vs. APT28: Divergent Philosophies of Intrusion
| Tactic/Group | APT28 (Fancy Bear) | APT29 (Cozy Bear) |
| Affiliation | GRU (Russia) | SVR (Russia) |
| Objective | Influence, disruption | Longterm espionage |
| Signature attack | HeadLace, CVE exploit | SolarWinds, GRAPELOADER, WINELOADER |
| Style | Aggressive, noisy | Covert, patient |
| Initial Access | Broad phishing, zerodays | Targeted phishing, supply chain |
| Persistence | Common tools, fast flux | Custom implants, stealthy C2 |
| Lateral Movement | Basic tools (Windows) | Stealthy tools mimicking legit activity |
| AntiAnalysis | Obfuscation | AntiVM, antidebugging |
| Typical Victims | Ministries, media, sports | Diplomacy, think tanks, intel assets |
Weak Signals and Detection Opportunities
European CERTs have identified subtle signs that may suggest APT29 activity:
- Unusual password changes in Microsoft 365 without user request
- PowerShell usage from signed binaries in uncommon contexts
- Persistent DNS beaconing to rare C2 domains
- Abnormal OneDrive or Azure file transfers and permission changes
- Phishing emails tied to impersonated ministries and fake event lures
Defensive Strategies: Building European Resilience
Effective defense against APT29 requires:
- ⇨ Hardwarebased MFA (FIDO2, smartcards) to replace SMS/app OTPs
- ⇨ Enforcing least privilege and strict access policies
- ⇨ Monitoring DNS traffic and lateral movement patterns
- ⇨ Deploying EDR/XDR tools with heuristic behavior analysis
- ⇨ Ingesting threat intelligence feeds focused on APT29 TTPs
- ⇨ Running regular threat hunts to detect stealthy TTPs early
Sovereign Protection: PassCypher & DataShielder Against APT29
To counter espionage tactics like those of APT29, Freemindtronic offers two offline, hardwarebased solutions:
- DataShielder NFC HSM: A fully offline, contactless authentication tool immune to phishing and credential replay.
- PassCypher HSM PGP: Stores passwords and cryptographic secrets in a hardware vault, protected from keylogging, memory scraping, and BITB attacks.
Both tools decrypt only in volatile memory, ensuring no data is written locally, even temporarily.
Regulatory Compliance
- ⇨ French Decree No. 20241243: Encryption devices for dualuse (civil/military)
- ⇨ EU Regulation (EU) 2021/821 (latest update 2024)
- ⇨ Distributed exclusively in France by AMG PRO:
Threat Coverage Table: PassCypher & DataShielder vs. APT29
This table evaluates sovereign cyber defenses against known APT29 TTPs.
| Threat Type | APT29 Presence | PassCypher Coverage | DataShielder Coverage |
|---|---|---|---|
| Targeted spearphishing | ✔ | ✔ Secure Input, No Leakage |
✔ Offline Authentication |
| Supply chain compromise | ✔ | ✔ Endtoend encrypted communication; passwords and OTPs decrypted in volatile memory only |
✔ Offline preencryption; data decrypted only in memory during reading |
| Microsoft 365 credential harvesting | ✔ | ✔ Offline Storage, BITB Protection |
✔ Offline Authentication |
| Trusted cloud abuse (OneDrive, Azure) | ✔ | ✔ URL Filtering, Secure Vault |
✔ Offline Authentication |
| Persistent implants | ✔ | ✔ Encrypted session use; keys and OTPs inaccessible without HSM |
✔ Offline encrypted data cannot be used even with full system compromise |
| Exploits via infected documents | ✔ | ✔ Encrypted Sandbox Links |
✔ Encrypted Key Context |
| Phishing via diplomatic accounts | ✔ | ✔ Secure Input, Spoofing Protection |
✔ Offline Credential Isolation |
| Lateral movement (PowerShell) | ✔ | ✔ Credentials isolated by HSM; attacker gains no usable secrets |
✔ Persistent encryption renders accessed data useless |
| DNS beaconing | ✔ | ✔ Decryption keys never online; exfiltrated data stays encrypted |
✔ Offline encrypted messages never intelligible without HSM |
Legend: ✔ = Direct mitigation | ⚠ = Partial mitigation | ✘ = Not covered
Note: PassCypher and DataShielder focus not on preventing all access, but on neutralizing its strategic value. Isolated credentials and persistently encrypted data render espionage efforts ineffective.
Towards a Sovereign and Proactive Defense Against the APT29 Threat in Europe
APT29’s quiet and persistent threat model demands proactive, sovereign responses. Passive, reactive security measures are no longer enough. European organizations must integrate national technologies like PassCypher and DataShielder to ensure digital sovereignty, compartmentalization, and offline security.
The adoption of segmented, resilient, and hardwarebacked architectures enables:
- Independence from cloudbased MFA
- Resistance to credential reuse and session hijacking
- Full data lifecycle control with no data remnants
CISOs, critical infrastructure operators, and government entities must evaluate the security coverage and complementarity of each tool to craft a cohesive strategy against persistent Russian cyber threats.
To explore our full methodology and technical breakdown APT29 read the complete article.
Glossary (for Non-Technical Readers)
- Spear-phishing: A targeted email attack that appears personalized to trick specific individuals into clicking malicious links or attachments.
- C2 (Command and Control) Infrastructure: A network of hidden servers controlled by attackers to manage malware remotely and exfiltrate stolen data.
- OAuth Consent Phishing: A technique where attackers trick users into granting access permissions to malicious applications through legitimate cloud services.
- Anti-VM / Anti-Debugging: Techniques used in malware to avoid being detected or analyzed by virtual machines or security researchers.
- Supply Chain Attack: An attack that compromises trusted software or service providers to distribute malware to their clients.
- Volatile Memory Decryption: A security method where sensitive data is decrypted only in the device’s memory (RAM), never stored unencrypted.
- Persistent Threat: An attacker who remains within a network for a long time without being detected, often for intelligence gathering.
Russian cyberattack on Microsoft by Midnight Blizzard (APT29) highlights the strategic risks to digital sovereignty. Discover how the group exploited password spraying, malicious OAuth applications, and legacy exposure — and the sovereign countermeasures offered by DataShielder and PassCypher.
Executive Summary — APT28 spear-phishing in Europe
⚡ Objective
Understand how APT28 spear-phishing campaigns exploit Outlook VBA macro phishing, the NotDoor backdoor, DLL side-loading via OneDrive.exe, and HeadLace loaders to achieve stealth access, data theft, and lateral movement across European infrastructures.
💥 Scope
Targets include French ministries, NATO-linked entities, critical infrastructure operators, research centers, BITD companies, and organizers of the Paris 2024 Olympics. The focus: Outlook-centric intrusion chains and their detection through behavioral monitoring.
🔑 Doctrine
APT28 favors short-lived, stealthy intrusions. Defenders must enforce Outlook hardening, disable macros, monitor anomalous OUTLOOK.EXE child processes and OneDrive.exe DLL loads, and inspect encrypted mail flows (e.g., Proton Mail covert exfiltration). Sovereign encryption HSMs ensure end-to-end protection.
🌍 Strategic Differentiator
Unlike cloud MFA or purely software-based solutions, DataShielder and PassCypher adopt a zero cloud, zero disk, zero DOM posture: offline encapsulation, volatile-memory decryption only, and offline credential custody.
Result ⮞ resilient spear-phishing defense, neutralization of Outlook backdoor channels, and data sovereignty across the European cyber landscape.
Technical Note
Reading time (summary): ≈ 4 minutes
Reading time (full): ≈ 30 minutes
Level: Cyber threat intelligence / SecOps
Posture: Behavior-first detection, sovereign authentication
Category: Digital Security
Available languages: FR · EN · CAT · ES
Editorial type: Chronicle
About the author: Jacques Gascuel — Inventor of Freemindtronic®, specialist in sovereign HSM architectures, offline key segmentation, and resilient communication security. He develops dual-use encryption technologies (civil/military) officially recognized in Europe, and publishes strategic chronicles on APT cyber-espionage and digital sovereignty.
This chronicle belongs to the Digital Security section and contributes to Freemindtronic’s sovereign operational toolbox (HSM, offline segmentation, resilient communication).
- Executive Summary — APT28 spear-phishing
- APT28 spear-phishing France: a persistent pan-European threat
- Other APT28 campaigns between CVE-2023-23397 and NotDoor
- Historical Context: The Evolution of APT28
- Priority targets for APT28 spear-phishing campaigns
- Spear-phishing and electoral destabilization in Europe
- NotDoor: Outlook backdoor
- APT28 malware matrix
- ANSSI’s operational recommendations
- Regulatory framework: French response
- Sovereign solutions: DataShielder & PassCypher
- Threat coverage: PassCypher & DataShielder
- Towards a European cyber-resilience strategy
- Evolution of APT28 spear-phishing campaigns (2014–2025)
- Sovereign Use Case — Outlook backdoor neutralized
- Official Report — CERTFR-2025-CTI-006
- What We Didn’t Cover — Next chapters
- Weak Signals — Trends to watch
APT28 spear-phishing France: a persistent pan-European threat
APT28 spear-phishing France now represents a critical digital security challenge on a European scale. Since 2021, several European states, including France, have faced an unprecedented intensification of spear-phishing campaigns conducted by APT28, a state-sponsored cyber-espionage group affiliated with Russia’s GRU. Also known as Fancy Bear, Sednit, or Sofacy, APT28 targets ministries, regional governments, defense industries, strategic research institutions, critical infrastructure, and organizations involved with the Paris 2024 Olympic Games. This analysis details an APT28 Outlook backdoor pathway and defensive countermeasures.
In a tense geopolitical context across Europe, APT28’s tactics are evolving toward stealthy, non-persistent attacks using malware like HeadLace and exploiting zero-day vulnerabilities such as CVE-2023-23397 in Microsoft Outlook. This vulnerability, detailed in a CERT-FR alert (CERTFR-2023-ALE-002), allows an attacker to retrieve the Net-NTLMv2 hash, potentially for privilege escalation. It is actively exploited in targeted attacks and requires no user interaction, being triggered by sending a specially crafted email with a malicious UNC link. This trend mirrors tactics used by APT44, explored in this article on QR code phishing, underscoring the need for sovereign hardware-based tools like DataShielder and PassCypher. European CISOs are encouraged to incorporate these attack patterns into their threat maps.
Historical Context: The Evolution of APT28
APT28 (Fancy Bear) has been active since at least 2004, operating as a state-sponsored cyber-espionage group linked to Russia’s GRU. However, its most heavily documented and globally recognized operations emerged from 2014 onward. That year marks a strategic shift, where APT28 adopted more aggressive, high-visibility tactics using advanced spear-phishing techniques and zero-day exploits.
Between 2008 and 2016, the group targeted several major geopolitical institutions, including:
• The Georgian Ministry of Defense (2008)
• NATO, the White House, and EU agencies (2014)
• The U.S. presidential election campaign (2016)
This period also saw extensive exposure of APT28 by cybersecurity firms such as FireEye and CrowdStrike, which highlighted the group’s growing sophistication and its use of malicious Word documents (maldocs), cloud-based command-and-control (C2) relays, and coordinated influence operations.
These earlier campaigns laid the foundation for APT28’s current operations in Europe — especially in France — and illustrate the persistent, evolving nature of the threat.
Priority targets for APT28 spear-phishing campaigns
Target typology in APT28 campaigns
APT28 targets include:
- Sovereign ministries (Defense, Interior, Foreign Affairs)
- Paris 2024 Olympics organizers and IT contractors
- Operators of vital importance (OIVs): energy, transport, telecoms
- Defense industrial and technological base (BITD) companies
- Research institutions (CNRS, INRIA, CEA)
- Local governments with strategic competencies
- Consulting firms active in European or sensitive matters
Historical Context: The Evolution of APT28
APT28 (Fancy Bear) has been active since at least 2004, operating as a state-sponsored cyber-espionage group linked to Russia’s GRU. However, its most heavily documented and globally recognized operations emerged from 2014 onward. That year marks a strategic shift, where APT28 adopted more aggressive, high-visibility tactics using advanced spear-phishing techniques and zero-day exploits.
Between 2008 and 2016, the group targeted several major geopolitical institutions, including:
- The Georgian Ministry of Defense (2008)
- NATO, the White House, and EU agencies (2014)
- The U.S. presidential election campaign (2016)
This period also saw extensive exposure of APT28 by cybersecurity firms such as FireEye and CrowdStrike, which highlighted the group’s growing sophistication and its use of malicious Word documents (maldocs), cloud-based command-and-control (C2) relays, and coordinated influence operations.
These earlier campaigns laid the foundation for APT28’s current operations in Europe — especially in France — and illustrate the persistent, evolving nature of the threat.
Spear-phishing and electoral destabilization in Europe
Political and geopolitical context of APT28 campaigns
APT28’s campaigns often precede key elections or diplomatic summits, such as the 2017 French presidential election, the 2019 European elections, or the upcoming Paris 2024 Olympic Games. These are part of a broader hybrid strategy aimed at destabilizing the EU.
Some spear-phishing attacks are synchronized with disinformation operations to amplify internal political and social tensions within targeted nations. This dual tactic aims to undermine public trust in democratic institutions.
Reference: EU DisinfoLab – Russia-backed disinformation narratives
Germany and NATO have also reported a resurgence of APT28 activities, particularly against NATO forces stationed in Poland, Lithuania, and Estonia. This strategic targeting of European institutions is part of a broader effort to weaken collective security in the EU.
Other APT28 campaigns between CVE-2023-23397 and NotDoor
Between the Outlook zero-day CVE-2023-23397 and the emergence of the NotDoor Outlook backdoor, APT28 sustained a steady cadence of precision intrusions. The group leveraged widely deployed enterprise software to deliver APT28 spear-phishing chains at scale, moving from classic maldocs to Outlook-centric compromise and covert exfiltration.
| Vulnerability | Attack type | Target | APT28 usage |
|---|---|---|---|
| CVE-2023-38831 | Malicious ZIP (WinRAR exploit) | Diplomatic & defense sectors | Weaponized archives in targeted phishing; payload staging and credential theft |
| CVE-2021-40444 | ActiveX exploit (MSHTML) | NATO-linked institutions | Malicious Word documents embedding ActiveX to gain initial code execution |
| CVE-2023-23397 | Outlook zero-day | Energy & transport operators | Zero-click NTLM material theft enabling relay and lateral movement |
Takeaway. These campaigns show a tactical progression from maldoc & archive abuse toward Outlook-centric backdoors, culminating with NotDoor’s Outlook VBA macro phishing, DLL side-loading via OneDrive.exe, and Proton Mail covert exfiltration.
NotDoor: a new Outlook backdoor in APT28’s toolchain
OneDrive.exe DLL side-loading and encrypted mail exfiltration. Detections pivot on Outlook child-process chains, macro creation, and anomalous OneDrive module loads.NotDoor represents a tactical leap in APT28 spear-phishing chains: instead of only abusing delivery vectors, the operators weaponize Microsoft Outlook itself. A malicious VBA macro hooks mailbox events, watches for keyword triggers in new mail, and—on match—executes commands, stages files, and exfiltrates data. This Outlook-centric backdoor blends with daily workflows, reduces telemetry noise, and undermines perimeter detections.
How the backdoor operates
- Initial foothold: Outlook VBA macro phishing seeded via targeted messages or trust-store abuse (macro-enabled project in the user profile).
- Mailbox surveillance: event handlers monitor incoming emails for operator tasking (e.g., “Daily Report”, “Timesheet”, summit- or exercise-themed lures).
- Tasking & execution: the macro launches system commands, enumerates files and mailbox items, compresses artifacts, and uploads follow-on payloads.
- Defense evasion: DLL side-loading via OneDrive.exe loads a malicious library behind a trusted Microsoft binary to degrade signature-based controls.
- Covert egress: Proton Mail covert exfiltration camouflages outbound traffic among legitimate encrypted flows.
Where NotDoor fits vs HeadLace & CVE-2023-23397
| Capability | HeadLace | CVE-2023-23397 (Outlook) | NotDoor |
|---|---|---|---|
| Primary role | Loader / C2 staging | Zero-click credential material theft | Outlook-resident backdoor (VBA) |
| Initial trigger | Spear-phishing + droppers | Crafted Outlook item (MAPI reminder) | Mailbox keyword match on new mail |
| Operator actions | Payload delivery, beaconing | NTLM relay → lateral movement | Command exec, file upload, selective exfiltration |
| Key evasions | Cloud relays; short-lived infra | Abuses client processing path | OneDrive.exe DLL side-loading; encrypted mail channel |
| Detections |
|
||
Detection & hunts (behavior-first)
- Macro exposure: disable Outlook VBA by policy; alert on macro project creation/enable in Office trust stores.
- Process chains: flag
OUTLOOK.EXEspawning script interpreters, archivers, or shells; correlate with mailbox event timing. - Side-loading: monitor
OneDrive.exemodule loads from non-system paths; detect unsigned or unexpected DLLs co-located with it. - Mailflow anomalies: DLP/heuristics for sudden encrypted egress to privacy providers from workstation hosts; compressed archives leaving via mail.
- Keyword intel: hunt for mailbox rules/macros using operational terms (e.g., “report”, “invoice”, exercise names, event code-words).
MITRE ATT&CK mapping (core techniques)
- T1204 — User Execution: malicious file/macro (Outlook VBA project)
- T1059 — Command & Scripting Interpreter (cmd/PowerShell/WScript)
- T1574.002 — Hijack Execution Flow: DLL Side-Loading (
OneDrive.exe) - T1041 — Exfiltration Over C2 Channel (encrypted mail channel)
Operational hardening (sovereign posture)
- Harden Outlook (disable macros by default; restrict trusted locations; block unsigned VBA).
- Instrument Outlook/OneDrive behaviors and alert on risky child-process or module-load patterns.
- Adopt sovereign email encryption HSM: use DataShielder HSM PGP for end-to-end encryption with volatile-memory decryption only; pair with PassCypher HSM PGP for offline OTP/credential custody.
APT28 attribution and espionage objectives
- Attribution: Main Intelligence Directorate (GRU), Unit 26165
- Key techniques: Targeted phishing, Outlook vulnerabilities, compromise of routers and peripheral devices
- Objectives: Data exfiltration, strategic surveillance, disruption of critical operations
APT28 also coordinates technical operations with information warfare: fake document distribution, disinformation campaigns, and exploitation of leaks. This “influence” component, though less covered in mainstream reports, significantly amplifies the impact of technical attacks.
Observed campaigns and methods (2022–2025)
| Date | Campaign | Targets | Impact |
|---|---|---|---|
| March 2022 | Diplomatic phishing | EU ministries | Theft of confidential data |
| July 2023 | Military campaign | French and German forces | Access to strategic communications |
| Nov. 2024 | HeadLace & CVE exploit | Energy sector | Risk of logistical sabotage |
| April 2025 | Olympics 2024 operation | French local authorities | Compromise of critical systems |
🔗 See also: ENISA Threat Landscape 2024 – Cyberespionage Section
Mapping APT28 to the Cyber Kill Chain
| Kill Chain Step | Example APT28 |
| Reconnaissance | DNS scanning, 2024 Olympic monitoring, WHOIS tracking |
| Weaponization | Doc Word piégé (maldoc), exploit CVE-2023-23397 |
| Delivery | Spear-phishing by email, fake ..fr/.eu domains |
| Exploitation | Macro Execution, Outlook Vulnerability |
| Installation | Malware HeadLace, tunnels cloud (Trello, Dropbox) |
| C2 | GitHub relay, DNS Fast Flux |
| Actions on Obj. | Exfiltration, disinformation coordinated with DCLeaks |
Tactics and Infrastructure: Increasing Sophistication
APT28 campaigns are distinguished by a high degree of stealth:
- Domain spoofing via homographs (e.g. gov-fr[.]net).
- Real-time payload encryption.
- Using legitimate cloud services like GitHub, Dropbox, or Trello as a C2 relay.
- Hosting on anonymized infrastructures (Fast Flux DNS, bulletproof hosting).
- Non-persistent attacks: ephemeral access, rapid exfiltration, immediate wipe. This approach makes detection particularly complex, as it drastically reduces the window of opportunity for forensic analysis, and the attacker’s infrastructure is often destroyed rapidly after compromise.
This mastery of technical obfuscation makes detection particularly complex, even for the most advanced SIEM systems and EDRs.
Evolution of APT28 spear-phishing campaigns (2014–2025)
This timeline highlights the major APT28 spear-phishing offensives in Europe, from early credential harvesting and the 2017 Macron campaign to Microsoft Outlook exploits in 2020 and large-scale energy sector intrusions culminating in 2025.
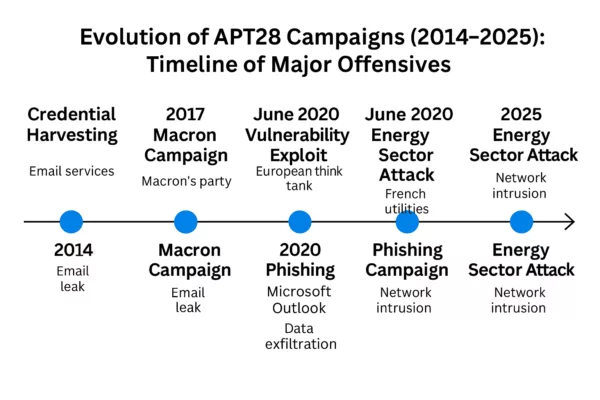
APT28 spear-phishing timeline (2014–2025) — Key campaigns include credential harvesting, the 2017 Macron leak, Outlook phishing exploits in 2020, and critical infrastructure attacks in the European energy sector through 2025.
APT28 malware matrix (Outlook-centric chains)
This matrix summarizes the Outlook-focused toolchain observed in APT28 spear-phishing campaigns, highlighting purpose, triggers, evasions, and succinct detections to operationalize hunts.
| Tool / Vector | Purpose | Initial trigger | Key evasions | Notes |
|---|---|---|---|---|
| CVE-2023-23397 (Outlook) | Zero-touch credential material theft | Crafted Outlook item (MAPI reminder) | Abuses client processing path; no user click | Enables NTLM relay & lateral movement |
| Detections | Outlook items with reminder props to UNC; anomalous NTLM right after item processing; spikes in external SMB/NTLM auth. | |||
| HeadLace | Loader / staging / C2 | Document lure or dropper delivered via spear-phishing | Cloud relays; short-lived infrastructure | Used for quick-strike access and payload delivery |
| Detections | Unusual OUTLOOK.EXE or user apps spawning LOLBins; beaconing to GitHub/Trello; transient staging dirs; signed-binary proxy exec. |
|||
| NotDoor (Outlook VBA) | Outlook-resident backdoor | Mailbox keyword match on new mail | OneDrive.exe DLL side-loading; encrypted mail channel | Command exec, file upload, selective exfiltration |
| Detections | Outlook macro enable/create events; OUTLOOK.EXE spawning cmd/powershell/wscript; OneDrive.exe loading DLLs from user-writable paths; encrypted egress to privacy providers (e.g., Proton Mail). |
|||
Official report — CERTFR-2025-CTI-006
Title: Targeting and compromise of French entities using APT28 tradecraft
Publisher: CERT-FR (ANSSI) — 29 April 2025
- Scope: Analysis of APT28 campaigns against French government, diplomatic and research bodies (2021–2024), with spillover to wider Europe.
- Attribution: APT28 (Fancy Bear / Sofacy), linked to Russia’s GRU Unit 26165.
- Key TTPs: Targeted spear-phishing, Outlook abuse (incl. CVE-2023-23397), short-dwell intrusions, cloud C2 relays, coordinated information ops.
- Operational risks: Credential theft → lateral movement; data exfiltration; disruption potential for critical operators.
- Defensive priorities: Patch hygiene; macro hardening; behavior monitoring for
OUTLOOK.EXE/OneDrive.exe; DLP on encrypted egress; ATT&CK mapping for hunts (T1204, T1059, T1574.002, T1041).
Links — Official page: CERTFR-2025-CTI-006 · Full PDF: download
Takeaway — The report corroborates the shift of APT28 spear-phishing toward Outlook-centric chains and reinforces the need for behavior-first detection and sovereign encryption/HSM controls.
ANSSI’s operational recommendations
OUTLOOK.EXE/OneDrive.exe, DLP on encrypted egress, and sovereign HSMs for sensitive exchanges and credentials.- Apply security patches (known CVEs) immediately.
- Audit peripheral equipment (routers, appliances).
- Deploy ANSSI-certified EDRs to detect anomalous behavior.
- Train users with realistic spear-phishing scenarios.
- Segment networks and enforce the principle of least privilege.
- Disable Outlook VBA macros by default via group policy; restrict Office trusted locations; block unsigned macros.
- Instrument Outlook & OneDrive process behavior: alert on
OUTLOOK.EXEspawning script interpreters and onOneDrive.exeloading DLLs from non-system paths. - Mailflow controls: DLP/heuristics for unexpected encrypted egress to privacy providers (e.g., Proton Mail) from workstation hosts.
- Sovereign channeling for sensitive comms: use DataShielder HSM PGP to end-to-end encrypt messages with volatile-memory decryption only; pair with PassCypher HSM PGP for offline OTP/credential custody.
- Threat hunting: search for anomalous Outlook rules/macros, compressed archives in sent items, and keyword-based mailbox automations.
- Map NotDoor hunts to MITRE ATT&CK: T1204 (User Execution: Malicious File/Macro), T1059 (Command and Scripting Interpreter), T1574.002 (Hijack Execution Flow: DLL Side-Loading), T1041 (Exfiltration Over C2 Channel).
For detailed guidance, refer to the ANSSI recommendations.
Regulatory framework: French response to spear-phishing
- Military Programming Law (LPM): imposes cybersecurity obligations on OIVs and OESs.
- NIS Directive and French transposition: provides a framework for cybersecurity obligations.
- SGDSN: steers the strategic orientations of national cybersecurity.
- Role of the ANSSI: operational referent, issuer of alerts and recommendations.
- EU-level Initiatives: Complementing national efforts like those led by ANSSI in France, the NIS2 Directive, the successor to NIS, strengthens cybersecurity obligations for a wider range of entities and harmonizes rules across European Union Member States. It also encourages greater cooperation and information sharing between Member States.
Sovereign solutions: DataShielder & PassCypher against spear-phishing
Sovereign solutions: DataShielder & PassCypher against spear-phishing
DataShielder NFC HSM: An alternative to traditional MFA authentication
Most of APT28’s spear-phishing publications recommend multi-factor authentication. However, this MFA typically relies on vulnerable channels: interceptable SMS, exposed cloud applications, or spoofed emails. DataShielder NFC HSM introduces a major conceptual breakthrough:
These controls provide a sovereign email encryption HSM approach for sensitive exchanges.
| Criterion | Classic MFA | DataShielder NFC HSM |
| Channel used | Email, SMS, cloud app | Local NFC, without network |
| Dependency on the host system | Yes (OS, browser, apps) | No (OS independent) |
| Resistance to spear-phishing | Average (Interceptable OTP) | High (non-repeatable hardware key) |
| Access key | Remote server or mobile app | Stored locally in the NFC HSM |
| Offline use | Rarely possible | Yes, 100% offline |
| Cross-authentication | No | Yes, between humans without a trusted third party |
This solution is aligned with a logic of digital sovereignty, in line with the recommendations of the ANSSI.
DataShielder HSM PGP can encrypt all types of emails, including Gmail, Outlook, Yahoo, LinkedIn, Yandex, HCL Domino, and more. It encrypts messages end-to-end and decrypts them only in volatile memory, ensuring maximum privacy without leaving a clear trace.
PassCypher HSM PGP enhances the security of critical passwords and TOTP/HOTP codes through:
- 100% offline operation without database or server
- Secure input field in a dedicated tamper-proof sandbox
- Protection native contre les attaques BITB (Browser-in-the-Browser)
- Automatic sandbox that checks original URLs before execution
- Secure management of logins, passwords, and OTP keys in a siloed environment
En savoir plus : BITB attacks – How to avoid phishing by iframe
These solutions fit perfectly into sovereign cyber defense architectures against APTs.
🇫🇷 Exclusive availability in France via AMG Pro (Regulatory Compliance)
To comply with export control regulations on dual-use items (civil and military), DataShielder NFC HSM products are exclusively distributed in France by AMG PRO.
These products are fully compliant with:
- French Decree No. 2024-1243 of December 7, 2024, governing the importation and distribution of dual-use encryption systems.
- Regulation (EU) 2021/821, establishing a Union regime for the control of exports, transfer, brokering and transit of dual-use items (updated 2024).
Why this matters:
- Ensures legal use of sovereign-grade encryption in France and across the EU.
- Guarantees traceability and legal availability for critical infrastructures, ministries, and enterprises.
- Reinforces the sovereignty and strategic autonomy of European cybersecurity frameworks.
DataShielder NFC HSM: a French-designed and Andorran-manufactured offline encryption and authentication solution, officially recognized under civil/military dual-use classification.
Threat coverage table: PassCypher & DataShielder vs APT groups
Evaluating sovereign cyber defenses against APT threats
Faced with the sophisticated arsenal deployed by APT groups such as APT28, APT29, APT31 or APT44, it is becoming essential to accurately assess the level of protection offered by cybersecurity solutions. The table below compares the tactics used by these groups with the defense capabilities built into PassCypher, HSM, PGP, and DataShielder. This visualization helps CISOs and decision-makers quickly identify the perimeters covered, residual risks, and possible complementarities in a sovereign security architecture.
| Threat Type | APT28 | APT29 | APT31 | APT44 | Couverture PassCypher | DataShielder Coverage |
| Targeted spear-phishing | ✅ | ✅ | ✅ | ⚠️ | ✅ | ✅ |
| Zero-day Outlook/Microsoft | ✅ | ✅ | ⚠️ | ❌ | ✅ (sandbox indirect) |
✅ (memory encryption) |
| Cloud relay (Trello, GitHub…) | ✅ | ⚠️ | ✅ | ❌ | ✅ (URL detection) |
✅ |
| QR code phishing | ❌ | ❌ | ❌ | ✅ | ✅ | ✅ |
| BITB (Browser-in-the-Browser) | ✅ | ⚠️ | ❌ | ❌ | ✅ | ✅ |
| Attacks without persistence | ✅ | ❌ | ⚠️ | ✅ | ✅ | ✅ |
| Disinformation / fake news | ✅ | ⚠️ | ❌ | ✅ | ✅ (scission login/data) |
⚠️ (via partitioning) |
| Compromise of peripheral equipment | ✅ | ✅ | ✅ | ⚠️ | ❌ | ✅ (via HSM) |
| Targeting elections/Olympics | ✅ | ⚠️ | ❌ | ❌ | ✅ | ✅ |
✅ = Direct protection / ⚠️ = Partial mitigation / ❌ = Not directly covered
Sovereign Use Case — Outlook backdoor neutralized
Context. A regional authority receives a themed spear-phish. A VBA project drops into Outlook. The macro watches for “weekly report”.
- Before: No macro hardening.
OUTLOOK.EXEspawnspowershell.exe;OneDrive.exeside-loads DLL; artifacts exfiltrated via encrypted mail to a privacy provider. - With DataShielder: Sensitive threads are end-to-end encrypted; decryption occurs only in volatile memory; exfiltration yields ciphertext with no reusable keys.
- With PassCypher: Admin/partner credentials and TOTPs are offline, outside browser/DOM; phishing-induced login prompts fail; anti-BITB sandbox blocks spoofed portals and checks original URLs before input.
- Detection: SOC rules flag
OUTLOOK.EXE → powershell.exeandOneDrive.exeloading non-system DLLs. DLP alerts on unexpected encrypted egress volume from workstations. - Outcome: Macro tasking is contained; no cleartext data loss; no credential replay; attacker’s window closes within minutes.
Towards a European cyber resilience strategy
APT28, APT29, APT44: these are all groups that illustrate an offensive escalation in European cyberspace. The response must therefore be strategic and transnational:
- Coordination by ENISA and the European CSIRT Network
- IOC sharing and real-time alerts between Member States
- Regulatory harmonization (NIS2 revision, Cyber Resilience Act)
- Deployment of interoperable sovereign solutions such as DataShielder and PassCypher
See also: Cyber Resilience Act – EU 🔗 See also: APT44 QR Code Phishing – Freemindtronic
CISO Recommendation: Map APT28 tactics in your security strategies. Deploy segmented, offline authentication solutions like DataShielder, combined with encrypted questionnaire tools such as PassCypher to counter spear-phishing attacks.
Related links — Russian APT actors
- APT29 — Spear-phishing in Europe: stealthy Russian espionage
SVR (Russia): low-noise campaigns, cloud relays, and minimal persistence. A natural complement to APT28’s Outlook-centric chains. - APT29 — Exploitation of app passwords
Access techniques bypassing traditional passwords (OAuth/app passwords), relevant to strengthening sovereign email controls. - APT44 — QR-code phishing & blended info-ops
Sandworm/GRU (Russia): mobile-first vectors and influence operations, converging with Outlook-focused tactics.
What We Didn’t Cover — Next chapters
- APT29: OAuth app-based persistence and cloud forensics pitfalls.
- APT31: Credential-phishing against diplomatic targets and router exploitation.
- APT44: Mobile-first QR-phishing and blended info-ops.
- Incident response playbooks: mailbox macro triage, OneDrive side-load scoping, encrypted-egress containment.
Weak Signals — Trends to Watch
- AI-generated lures at scale — Highly tailored spear-phish (meeting minutes, RFPs, summit agendas) produced by LLM pipelines, increasing click-through and bypassing traditional content heuristics.
- Malicious Outlook add-ins / COM supply chain — Pivot from VBA macros to signed-looking add-ins that survive macro hardening and blend with productivity tooling.
- OAuth consent phishing & token replay — App-based persistence without passwords; mailbox rules + Graph API automation to emulate “human” inbox behavior.
- Legacy VPN & SASE bypass — Reuse of stale creds, split-tunnel misconfigs, and coarse geofencing to reach O365/Outlook from “trusted” egress points.
- Encrypted DNS/DoH for staging — Low-signal C2 bootstrap and selector lookups hidden in privacy traffic; harder to baseline on egress.
- Deepfake-assisted vishing — Real-time voice cloning to legitimize urgent mailbox actions (“approve macro”, “send weekly report”).
- QR-code hybrid lures (desktop ↔ mobile) — Convergence with APT44 playbooks; cross-device session hijack and MFA coercion via mobile scanners. See also: APT44 QR code phishing.
- OneDrive.exe side-loading variants — New search-order tricks and user-writable paths; signed-binary proxying to evade EDR trust gates.
- SOHO/edge router staging — Short-lived hops and NAT-ed implants to mask operator infrastructure and rotate origins near targets.
- MFA friction exploits — Push-fatigue + number-matching workarounds; social sequences that time prompts to business rituals (shift changes, on-call handovers).
- ECH/TLS fingerprint hiding — Encrypted Client Hello + JA3 randomization to degrade domain/SNI-based detections on mailbox-adjacent exfiltration.
Worldwide Password Usage and Trends in 2025
User password statistics 2025 reveal that individuals manage 70–80 passwords on average, with global usage exceeding 417 billion accounts. Private users log in 5–7 times daily, while professionals reach 10–15. Discover key insights on password trends, frequency of use, and digital authentication habits worldwide.
Table of Contents
User Password Statistics 2025: A Global Study – Introduction
Methodology – Average Number of Passwords per User: Estimates and Statistical Evidence – Challenges in Measuring Password Usage – Historical Data and Recent Estimates – Supporting Evidence from Cybersecurity Institutions – Daily Password Usage Frequency: How Often Do Users Log In? – Estimating Daily Login Activity – Factors Influencing Login Frequency – Impact of Frequent Authentication –Time Spent on Login Methods and Its Impact on Users – Estimating the Total Number of Passwords Worldwide – Global Calculation – Key Considerations – Recommendations for Secure Password Management – Final Observations and Perspectives – Sources Used –
User Password Statistics 2025: Jacques Gascuel examines global password usage trends, revealing how users manage 70–80 passwords on average, with over 417 billion in use worldwide. This study explores login frequency, security challenges, and best practices shaping the future of authentication.
Password Statistics 2025: Global Trends in Usage and Security Challenges
The growing reliance on digital services has made passwords an essential component of online security. Every day, billions of users interact with various platforms and applications requiring authentication, creating a heavy dependency on passwords. This study aims to explore the scope of this phenomenon by analyzing, through reliable and non-commercial sources, the number of passwords users must manage, their usage habits, and the security challenges that arise on a global and regional scale.
According to the Digital 2024 Global Overview Report by We Are Social and Hootsuite, more than 5 billion people worldwide are now connected to the internet, spending an average of 6 hours and 40 minutes per day online. This increased reliance on digital platforms results in a complex management of credentials and passwords, affecting a significant portion of the global population.
Methodology
To ensure the rigor and neutrality of this study, we prioritize sources from recognized institutions known for their expertise and independence, such as government institutions, cybersecurity organizations, universities, and academic research centers. To complement our analysis and provide reliable quantitative estimates, we also incorporate data from established market research and statistical firms.
Research Approach
- Academic Literature Review: Examination of scientific publications (research articles, conference proceedings, theses) from universities and research laboratories specializing in cybersecurity, human-computer interaction, and behavioral sciences.
- Analysis of Official Reports: Collection and assessment of data from national and international cybersecurity agencies (ANSSI, CISA, NCSC, BSI, UIT, OECD, ENISA).
- Institutional Reference Sources: Exploration of publications and databases from organizations recognized for their cybersecurity expertise (Center for Internet Security, Internet Society).
- Integration of Statistical Data: Use of reliable figures from leading statistical organizations (Statista, We Are Social, eMarketer), with careful attention to methodological transparency and neutrality.
For each aspect of our research, we systematically prioritize sources that meet these criteria. This includes data on the average number of passwords per user, usage habits, and regional statistics. Where direct “official” data is unavailable, we rely on indirect indicators. We also consider converging estimates and logical deductions supported by the best available sources.
Average Number of Passwords per User: Estimates and Statistical Evidence
Challenges in Measuring Password Usage
Accurately quantifying the average number of passwords per user globally is a complex task due to the dynamic and private nature of this data. While some organizations conduct surveys and statistical research, the absence of universally standardized tracking methods means estimates can vary significantly.
Historical Data and Recent Estimates
According to Statista, a 2020 study estimated that the average number of online accounts per internet user worldwide was 90 (Statista – Average Number of Online Accounts per User, 2020). Although this data is somewhat dated, it provides an important benchmark.
More recent estimates from companies specializing in password management suggest that the number of online accounts per person in 2025 could range from 100 to 150. While these figures should be approached cautiously due to their commercial nature, they align with trends showing increased digital account creation worldwide.
Password Statistics: A Comparative Look (2020 vs. 2025)
Analyzing Password Statistics 2025 in isolation provides a snapshot, but comparing them to earlier years reveals crucial trends and the escalating nature of digital authentication challenges.
The Expanding Digital Footprint: Accounts Per User
In 2020, a Statista study indicated the average internet user managed approximately 90 online accounts. Fast forward to 2025, and estimates from password management specialists suggest this number has surged to between 100 and 150 accounts per person. This represents a minimum 11% increase in personal digital real estate over just five years, directly correlating with the proliferation of online services, apps, and digital interactions. This growth underscores the increased cognitive burden on users, driving the demand for more sophisticated password management solutions.
The Rise of Total Global Passwords
Building on these individual figures, the sheer volume of passwords in global circulation has also seen a dramatic increase. While specific global figures for earlier years are harder to consolidate perfectly, the internet user base itself has grown significantly. With 5.56 billion internet users at the start of 2025 (and now over 5.64 billion), compared to roughly 4.66 billion users in early 2021 (We Are Social, Hootsuite, 2021), the total number of digital accounts and corresponding passwords has inevitably expanded. This surge from an estimated 417 billion at the onset of 2025 to over 423 billion with the latest user count highlights the rapid acceleration of digital identity creation worldwide.
Evolving Threat Landscape and Security Awareness
Alongside the growth in accounts, the complexity and frequency of cyber threats have also intensified. While in 2020, password reuse and weak passwords were predominant concerns, by 2025, the focus has shifted to more sophisticated threats like AI-powered phishing, deepfakes for social engineering, and highly organized ransomware operations. This evolution necessitates a shift in user and organizational security practices, pushing for adoption of MFA and passwordless solutions at an unprecedented rate compared to half a decade ago.
Supporting Evidence from Cybersecurity Institutions
Independent cybersecurity agencies have long emphasized the importance of using unique and complex passwords for each account. As a result, this recommendation indirectly confirms that users manage a high volume of credentials. Furthermore, institutions such as ANSSI, CISA, and NCSC strongly advocate the use of password managers. Indeed, these tools help reduce the cognitive burden on users and significantly improve security.(ANSSI – Password Best Practices, CISA – Creating Secure Passwords).
Moreover, academic studies, such as “The Next Domino to Fall: Empirical Analysis of User Passwords Across Online Services” (USENIX Security Symposium), highlight the risks associated with password reuse. Consequently, these findings reinforce the idea that individuals are struggling to manage an increasing number of credentials securely.
Expert Insights on the Future of Authentication
Leading voices in cybersecurity consistently emphasize the evolving nature of digital defense. “The sheer volume of passwords users manage today is unsustainable from both a security and usability perspective,” states Dr. Evelyn Schmidt, a renowned cybersecurity researcher at the Global Institute of Digital Forensics. “We are at a pivot point where the industry must collectively push for more intuitive, yet highly secure, authentication mechanisms that reduce human error and fatigue.”
Echoing this sentiment, Marcus Thorne, CISO at SecureCorp Solutions, highlights the human element: “Even the strongest password can be compromised by phishing or poor user habits. Our focus in 2025 must shift from just ‘strong passwords’ to ‘resilient authentication frameworks’ that incorporate multi-factor capabilities and continuous adaptive security.” These expert perspectives underscore that while Password Statistics 2025 reveal current challenges, the path forward lies in systemic improvements beyond single credentials.
Evolving Cybersecurity Landscape & Authentication Trends in 2025
Beyond individual password management, the broader cybersecurity landscape is in constant flux, directly impacting the necessity for robust authentication strategies. The European Union Agency for Cybersecurity (ENISA), a leading authority in digital security, consistently highlights emerging threats that demand enhanced user protection. Their ongoing analyses indicate a projected rise in cybersecurity incidents throughout 2025, with sophisticated attacks like ransomware and those leveraging Artificial Intelligence (AI) becoming increasingly prevalent.
These escalating threats underscore the critical importance of moving beyond single-factor authentication. They reinforce the urgent need for individuals and organizations to adopt advanced security measures, including the widespread implementation of Multi-Factor Authentication (MFA) and the consistent use of secure password managers. Such measures are vital to mitigate the risks illuminated by the Password Statistics 2025 and to protect against the evolving threat landscape.
Official Source: For comprehensive and up-to-date information on the cybersecurity threat landscape and best practices, refer to ENISA’s official publications and reports:ENISA Publications
Beyond Passwords: The Role of Advanced Authentication in 2025
The Password Statistics 2025 clearly illustrate a critical juncture in digital security. As users grapple with an ever-increasing number of complex passwords and face sophisticated threats like AI-powered phishing, the limitations of traditional password-based authentication become starkly apparent. While password managers and MFA are vital steps, the future of robust digital identity verification lies in leveraging cutting-edge hardware-based security solutions.
This is where technologies like Hardware Security Modules (HSMs), particularly when integrated with user-friendly interfaces such as NFC (Near Field Communication), offer a paradigm shift. Solutions like PassCypher NFC HSM provide a highly secure, yet remarkably convenient, method for authentication. By moving cryptographic keys and authentication processes to a dedicated, tamper-resistant hardware device, the risk of software-based attacks (malware, keyloggers) is drastically reduced. Users gain unparalleled protection, and the inherent friction of managing numerous complex passwords is significantly minimized.
Furthermore, for data integrity and secure communication, the principles of PGP (Pretty Good Privacy) encryption, when combined with the robust security of an HSM, represent the gold standard. A solution like PassCypher HSM PGP ensures that digital signatures and encrypted communications are not only generated with strong, uncompromisable keys but also protected within a secure hardware environment. This level of cryptographic assurance is increasingly critical in 2025’s interconnected and threat-laden digital landscape, moving beyond mere password strength to foundational digital trust.
By embracing these advanced authentication methodologies, both individuals and organizations can overcome the persistent challenges highlighted by the latest Password Statistics 2025, securing their digital lives with confidence and unparalleled protection.
Deep Dive into User Behavior: The Weak Link in Password Security
Determining how frequently users enter their passwords each day presents a methodological challenge, as authentication behaviors vary significantly. However, industry research consistently indicates that private users typically log in 5 to 7 times per day, while professional users frequently reach 10 to 15 logins daily. Furthermore, while these password statistics 2025 reveal the sheer volume of credentials users manage and the frequency of interaction, understanding common user habits highlights even more significant vulnerabilities.
Specifically, many reports consistently show that password reuse remains a pervasive issue. For instance, studies from organizations like Verizon’s Data Breach Investigations Report frequently indicate that users often employ the same, or slightly modified, passwords across multiple accounts. Consequently, a single data breach can easily compromise numerous online identities. Moreover, the prevalence of weak and easily guessable passwords continues to plague security efforts, despite widespread awareness campaigns. Indeed, the FBI’s annual Internet Crime Report regularly highlights the devastating impact of such vulnerabilities, linking them to billions in financial losses from various cybercriminal activities. Therefore, these widespread poor password practices underscore the urgent need for more robust security solutions beyond mere user education, compelling a shift towards more secure authentication methods.
Related Study: Time Spent on Login Methods and Its Impact on Users
As password management becomes increasingly complex, the time users spend on authentication processes is a crucial factor to consider. A related study, Time Spent on Login Methods, explores the efficiency and security trade-offs of various authentication methods.
This research examines how different login approaches—such as traditional passwords, multi-factor authentication (MFA), and passwordless technologies—affect user experience and productivity. It also highlights the challenges of balancing security with convenience.
By integrating insights from both studies, we can better understand how password complexity, login frequency, and authentication methods impact users globally. Exploring alternative authentication mechanisms may provide valuable solutions for reducing login fatigue while maintaining high security standards.
Estimating the Total Number of Passwords Worldwide
Global Calculation
To estimate the total number of passwords in use worldwide, we multiply the number of internet users by the average number of passwords per user. This calculation provides a close approximation of global password usage*
- Total Internet Users in 2025:* As of the latest available reports, over 5.64 billion people now use the internet globally, accounting for approximately 68.7% of the world’s population. How Many People Use The Internet in 2025 (Latest Data) – Demand Sage
- Average Passwords per User: Based on prevailing industry estimates and observed user behavior, an average of 75 passwords per user remains a robust figure for this analysis.
This latest data yields an updated estimated total of over 423 billion passwords in use worldwide (5.64 billion users multiplied by 75 passwords per user).
Key Considerations
- Regional Differences: Internet penetration and digital habits affect password usage.
- Authentication Trends: The rise of biometrics and passwordless login solutions may alter future estimates.
Recommendations for Secure Password Management
To address the challenges outlined in this study, experts recommend the following:
- Use a Password Manager to store and generate complex passwords securely.
- Enable Multi-Factor Authentication (MFA) to add an extra security layer.
- Educate Users on Best Practices, such as avoiding password reuse and using passphrases instead of short passwords.
Final Observations and Perspectives
This study highlights the increasing complexity of password management and its global cybersecurity implications. Users handle a growing number of credentials while facing frequent authentication requirements. As a result, security solutions must continuously evolve.
Future research should examine authentication method evolution, artificial intelligence’s role in cybersecurity, and user-friendly security solutions. The shift toward passwordless authentication may redefine security practices in the coming years, making continuous monitoring of these trends essential.
Secure Your Digital Future Today
The Password Statistics 2025 present clear challenges, but they also highlight the increasing availability and necessity of advanced security measures. Don’t let password fatigue or outdated practices compromise your digital safety.
- Explore our comprehensive range of secure password management solutions designed for individuals and businesses.
- Contact us for a personalized cybersecurity audit to identify and strengthen your digital weak points.
Take proactive steps now to ensure your online presence is resilient against evolving threats.
Sources Used
- We Are Social – Digital 2024 Global Overview Report
- Statista – Internet Users in 2025
- ANSSI – Password Best Practices
- CISA – Creating Secure Passwords