Recovery Phrase Backup by Jacques Gascuel This article will be updated with any new information on the topic, and readers are encouraged to leave comments or contact the author with any suggestions or additions.
Recovery Phrase Backup: a beginner’s guide
If you own a crypto wallet, you probably have heard of a recovery phrase backup. This is a series of words that allows you to access your crypto funds in case you lose or damage your wallet. It is one of the most important things you need to know and protect when dealing with cryptocurrencies. What is a seed phrase and how does it work? How to create and store it securely? What are the risks and challenges? And what are the best practices and tools to safeguard it?
This article will be updated with any new information on the topic, and readers are encouraged to leave comments or contact the author with any suggestions or additions.
How to make a physical backup of your secret phrase
The Mnemonic Phrase is the ultimate key to access your crypto assets. If you lose it or share it, you risk losing control of your funds. That’s why it’s essential to physically backup your seed phrase and store it in a safe and secret place. Here’s how to do it.
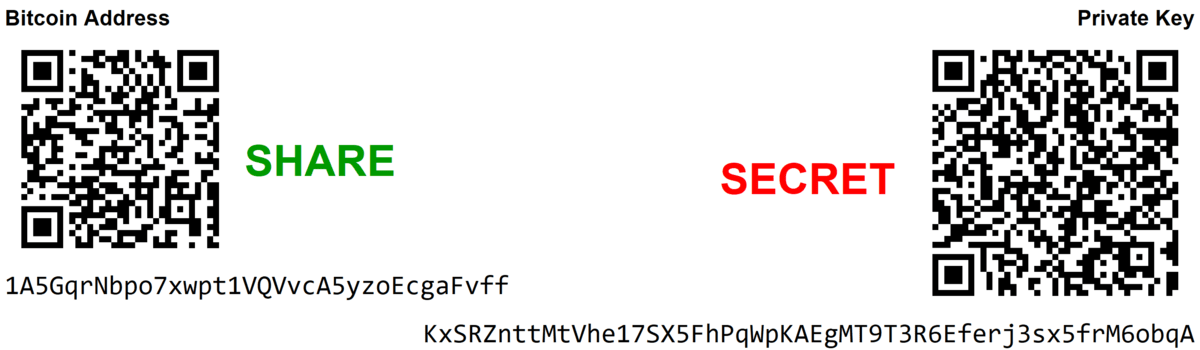
Recovery Phrase Backup vs Private Key
Before explaining what to do if you lose your seed phrase, let’s understand the difference between a seed phrase and a private key.
 |
A private key is a secret code that allows you to control your crypto-assets on the blockchain. It is generated from your seed phrase, which is a list of words that stores all the information needed to recover cryptographic funds on the blockchain. It consists of 12 to 24 randomly generated words that allow you to access or restore your wallet on another device. You must keep it in a safe place and never share it with anyone. |
What to do if you lose your Recovery Phrase? The solutions to recover your crypto-assets safely.
If you lose your seed phrase, you risk losing permanent access to your crypto-assets. It is used to create your private keys. You don’t need it to access your cryptocurrencies on a daily basis, but it is mainly a backup method. You can restore your crypto-assets in case of a problem with your device or wallet. However, if you lose your hardware wallets (cold wallets) and access to your online wallets (hot wallets), you will not be able to recover your cryptocurrencies without your seed phrase.In case you have correctly noted down your seed phrase, there are some possible recovery solutions:
• If you can still log in to your wallet with your password, you can find or export your seed phrase via the wallet.
• If you have lost your wallet but have your seed phrase, you can restore your wallet on a new hardware or software wallet. Enter the 12 to 24 words at startup.
• If you have forgotten or lost your seed phrase and have no other way to access your wallet, there are specialized services that can try to find it. They use a part of the words or other clues, but they are expensive and not always reliable.
Can you avoid using a Recovery Phrase?
You may wonder if there is a way to avoid using a seed phrase to secure your crypto-assets. The answer is no. The mnemonic Phrase is the only way to guarantee that you can always access your funds. Even if you lose or damage your device or wallet. Without a seed phrase, you depend entirely on the service or provider that you use to store your cryptocurrencies. If the service is hacked, closed or inaccessible for any reason, you also risk losing your assets. The seed phrase is an essential element to protect your financial independence and digital sovereignty.
Introduction: What is a recovery phrase and why is it important?
If you are new to the world of cryptocurrencies, you may have heard of the term “seed phrase” or “mnemonic phrase” or “backup phrase” or “seed recovery phrase” or “recovery phrase”. This is a set of words that allows you to access your crypto wallet and funds. It is one of the most important things you need to know and protect when dealing with cryptocurrencies.
How does a recovery phrase work and what are its formats?
But what exactly is a seed recovery phrasehrase and how does it work? How can you create and store it securely? What are the risks and challenges involved? And what are the best practices and tools to help you safeguard your recovery phrase backup?
This article answers these questions and more. It covers what a seed recovery phrase is, its importance, how it functions, and the steps to back it up and restore it. Additionally, it discusses the methods and materials to create and store physical backups (e.g., paper, metal, plastic, wood, or NFC devices). Furthermore, it explores the pros and cons of each option, along with some tips and tricks to make your backup easier and safer.
How to create a recovery phrase?
When you create a crypto wallet, a seed phrase is automatically generated for you. You do not need to choose or invent the words yourself. You just need to write them down and store them safely.
To create a recovery phrase backup, you can use any crypto wallet that supports the BIP39 standard, such as BitPay, Coinbase Wallet, Ledger, Trezor, or Trust Wallet. These wallets will generate a random sequence of 12 or 24 words for you, depending on the level of security you want.
You can also use an online tool like https://iancoleman.io/bip39/ to generate a seed phrase manually. However, this method is not recommended as it exposes your seed phrase to potential hackers or malware. You should only use this tool offline and on a trusted device.
What does a recovery phrase look like?
A recovery phrase backup looks like a list of simple words, such as:
- army
- energy
- fabric
- lucky
- opera
- stereo
- trash
- void
These are eight words out of the 2,048 possible words in the BIP39 standard. You can find the complete list of words here: https://www.bitcoinsafety.com/blogs/bitcoin/seed-phrase-list2.
The order of the words matters, as it determines the private keys that are derived from the seed phrase. You should never change or shuffle the words in your seed phrase.
The number of words in your seed phrase also matters, as it determines the level of security and entropy of your wallet. A 12-word seed phrase offers 128 bits of security, while a 24-word seed phrase offers 256 bits of security. The more words, the more secure.
What is the most common term for a recovery phrase?
A recovery phrase can also be called by different names, such as:
- recovery phrase
- mnemonic phrase
- backup phrase
- seed recovery phrase
These terms are interchangeable and mean the same thing. However, according to web search results, the most common term used for a seed phrase in the world is Recovery Phrase. This term emphasizes the fact that you can use your seed phrase to recover your wallet and your funds in case of loss or damage.
How to physically save your mnemonic Phrase
The Mnemonic Phrase is the ultimate key to accessing your crypto assets. If you lose it or share it, you risk losing control of your funds. That’s why it’s essential to physically back up your seed phrase and store it somewhere safe and secret. Here’s how
The role and mechanism of a secret phrase
Your cryptocurrency wallet generates a set of 12 or 24 words, also known as a seed phrase, using a cryptographic algorithm. A seed phrase is a series of words generated by your crypto wallet that gives you access to the crypto associated with that wallet. For example, if you use the BitPay wallet, you will receive a 12-word seed phrase when you create your wallet. These words are drawn from a list of 2,048 English words called the BIP39 standard1, which offers 128-bit encryption.The seed phrase can derive all the private keys that are associated with your crypto addresses and acts as a master key. You can send or spend your crypto from your wallet with a secret code called a private key.
A standard format such as BIP39 or SLIP39, which uses a predefined list of words that are easy to spell and recognize, forms the basis of the seed phrase. The words have a unique and random order and combination, and they represent a very large number that is virtually impossible to guess or crack. The seed phrase can have different representations, such as QR codes or NFC tags, but it usually appears in a human-readable form, such as “army energy fabric lucky opera stereo trash void”.
This phrase is the ultimate backup for your crypto wallet. If you have your seed phrase, you can restore your wallet and access your funds on any compatible device or platform. You can also migrate your wallet from one service or device to another, or create multiple copies of your wallet for redundancy or convenience with your seed phrase.
However, the seed phrase also comes with great responsibility. Only you know your seed phrase and can access your funds with it. If you forget lose or share your seed phrase with someone else you will lose control over your crypto assets and no one can help you recover them. That’s why backing up your seed phrase physically and storing it safely is necessary.
How to test your recovery phrase backup
After you physically backup your seed phrase, you should test it to make sure it works and you can restore your wallet with it. To test your recovery phrase backup, you can use a different device or platform than the one you used to create your wallet. For example, if you created your wallet with a hardware wallet, you can test your Mnemonic phrase with a software wallet or another hardware wallet. You should also test your backup phrase periodically, especially if you use a paper or metal backup that can degrade over time.
To test your recovery phrase backup, follow these steps:
- Install or launch a compatible wallet on a different device or platform than the one you used to create your wallet.
- Choose the option to restore or import a wallet from a seed phrase.
- Enter your seed phrase exactly as you wrote it down, including the order and spelling of the words.
- Verify that the wallet shows the same balance and addresses as your original wallet.
- If everything matches, your recovery phrase backup works and you can safely delete or close the test wallet.
- If something doesn’t match, check for errors in your recovery phrase backup and try again.
Why you need a physical backup of your seed phrase
A digital backup has several disadvantages compared to a physical backup of your seed phrase. An electronic device such as a computer, smartphone or USB drive stores a copy of your seed phrase as a digital backup. A digital backup can be convenient and easy to access, but it also comes with some risks.
Hackers, malware or phishing attacks can access your device and steal your seed phrase by compromising your digital backup. Fire, water, power surge or hardware failure can also render your device unusable by losing or damaging your digital backup. Authorities or third parties can also access your device and demand your seed phrase by confiscating or seizing your digital backup.
Being offline and disconnected from any network or device helps a physical backup avoid these risks. Hacking, destroying or confiscating a physical backup is harder than a digital backup. You have more control and ownership over your seed phrase with a physical backup than with a digital backup.
However, you need to be aware of some drawbacks that a physical backup also has. Failing to store it in a safe and secret place can result in losing, stealing, or forgetting your physical backup. Additionally, without using a durable material or protecting it from environmental factors, your physical backup can be damaged by fire, water, corrosion, or wear and tear. Furthermore, not writing it down clearly or using a standard format can make your physical backup illegible or unreadable.
Following some best practices and using some tools is necessary when creating and storing your physical backup.
How to Divide Your recovery phrase backup for Enhanced Security
Using SSSS adds security and flexibility to your backup, as you do not need all the shares to recover it. You can also create share combinations for different scenarios or purposes (e.g. for yourself, your family or your lawyer). EviSeed technology also achieves this by sharing trust criteria among people in segments.
However, SSSS also has drawbacks, like more complexity and errors in your backup process. You need to use a compatible wallet that supports SSSS, such as Spectre or Unchained Capital. You should also regularly test your actions and ensure that you remember the threshold number and the location of the shares. By following these best practices, you can divide your recovery phrase backup for enhanced security and peace of mind.
How to cipher your secret phrase
To physically secure it and protect your privacy, encrypt your backup with a code or cipher. However, encryption also has risks and challenges, like choosing a secure and memorable code or cipher, following the method correctly, and avoiding errors.
You can encrypt your backup using various methods, like numbers, symbols, colors, or images. Cryptographic techniques such as BIP38 or BIP39 secret phrase encryption also work. They encrypt your private keys or seed phrase with a password. For example, BIP38 encrypts your private keys with a password and stores them on a paper wallet. Or BIP39 secret phrase encryption adds a password to your seed phrase and generates a different wallet.
Encryption adds privacy and security to your backup, as you need the encrypted seed phrase and password to access your funds. You can also create passwords for different scenarios or purposes (e.g. for yourself, your family or your lawyer). Freemindtronic’s EviSeed technology makes this possible.
However, encryption also has drawbacks, like more complexity and errors in your backup process. You also need a compatible wallet that supports encryption and regular tests of your encrypted backup, as well as the password and method. Freemindtronic’s EviSeed technology avoids these inconveniences by using NFC devices that natively feature two AES-256 encryption systems with keys over 256 bits and manage RSA-4096 keys.
How to Choose a Secure Wallet for Your Seed Phrase
Choose a secure wallet that generates and manages your starting phrase to physically safeguard it. A wallet is software or hardware that lets you create, store, and use your addresses and keys. You can choose from many types of wallets, such as online, mobile, desktop, or hardware wallets and hot wallets. Each wallet type has its pros and cons for security, convenience, and functionality.
A hardware wallet is the most secure type. It is a device that stores your keys offline and protects them from threats. It physical device also have features like PIN codes, secret phrases, recovery phrases, and some add trust criteria through segmented key systems for more security.
However, virtual and hardware wallets are not perfect and can have problems. That is why backing up your starting phrase physically and storing it safely is important. You should also pick a reputable and compatible hardware wallet that supports standard formats like BIP39 or SLIP39.Storage devices like the NFC module with Freemindtronic’s EviSeed technology also do this. They are secure for several reasons. Mainly, they are offline. They ensure end-to-end encryption of seed phrases from the module using AES 256 contactless and post-quantum encryption. Additionally, trust criteria can be added for each backup starting phrase, along with individual security measures. A user-defined multi-factor authentication system is also available to access the module.
In conclusion, pick a secure wallet to store your backups and protect your starting phrase.
How to Choose the Best Material for Your recovery phrase backup
You can use various materials to back up your seed phrase. Paper, metal, plastic, and wood are common. Now, hardened and waterproof NFC devices also exist. Each material has its pros and cons for cost, availability, quality, and security. Paper is cheap and easy to use, but easily damaged. Metal is strong and durable, but expensive and hard to write on. Plastic is lightweight and waterproof, but degrades over time. Wood is natural and biodegradable, but rots or burns.
However, hardened NFC devices (e.g. Freemindtronic’s IP89K NFC modules) are great. These devices resist many environmental factors and are durable. They don’t need a battery and preserve data for 40 years. The modules have EviSeed technology that controls errors through checksums when writing, reading, sharing or using. They are also affordable, available and secure (hardware and digital).
You can encrypt your backups in AES-256 by cloning or copying them between NFC modules (nearby or remotely via RSA-4096 encryption from the module) if you use NFC modules. You can also back up your seed phrases through RSA-4096 from the device in the cloud (via email USB key or other digital media) or on paper (by printing the encrypted QR Code in RSA-4096). The Freemindtronic Android NFC phone app scans the encrypted QR Code backup seed phrase easily.
An encrypted QR Code backup seed phrase is advantageous as it protects from prying eyes and brute force decryption. Your preferences budget and storage conditions determine the best material for your backup. You should also consider using multiple materials for redundancy and diversity. For example, you can use paper for a quick and easy backup, metal or NFC modules for secure and long-term backup, and plastic, wood, or NFC Tag for a backup that you can hide or disguise as an RFID door opening tag.
The best technique to backup the recovery phrase
Secret phrases, also known as recovery phrases or seed phrases, are key elements to use a physical wallet for cryptocurrencies. They consist of a set of 24 words randomly chosen, which serve as a backup for all the crypto-assets managed by the wallet. In case of loss or theft of the wallet, it is possible to restore access to the private keys by using the secret phrase.
There are different techniques to backup your secret phrase and protect it from risks related to loss, theft or deterioration. Here is an overview of the main options available:
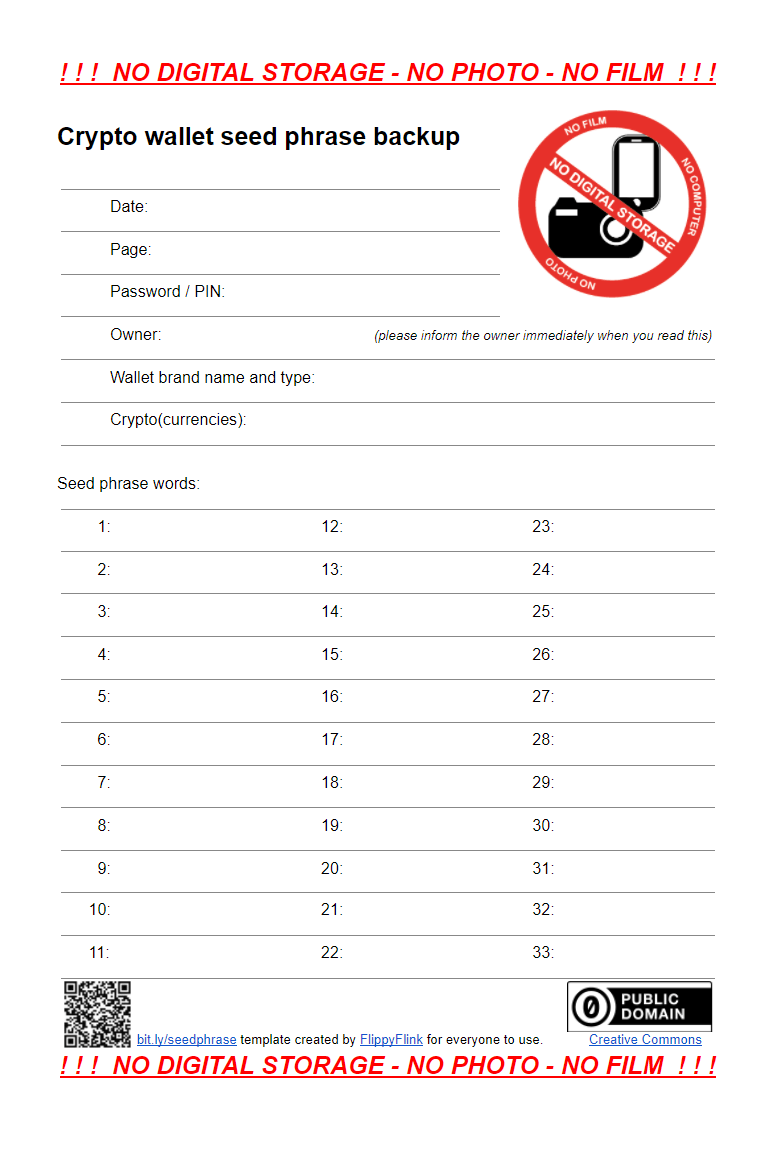
Write down the secret phrase on a sheet of paper
This technique consists of writing the words of the secret phrase on a sheet of paper and keeping it in a safe place. You need to make sure that the phrase is correctly spelled, numbered and readable. You also need to avoid making a digital copy of the phrase, sharing it with anyone or entering it into a computer or smartphone.
Advantages and disadvantages
- Advantages: this technique is simple, free and does not require any specific equipment. It allows you to keep full control over your secret phrase and your crypto-assets.
- Disadvantages: this technique is vulnerable to physical hazards (fire, water, wear, etc.) and human errors (loss, theft, bad writing, etc.). It does not allow you to easily verify if the secret phrase is correct or compatible with the wallet.
Risks related to cyber security and cyber espionage
- Risks related to cyber security: this technique does not involve exposure to networks or computer systems, so the risk of cyber security is low.
- Risks related to cyber espionage: this technique involves physical exposure to malicious or indiscreet third parties, so the risk of cyber espionage is high.
The legal aspect and protection of sensitive data
- Legal aspect: this technique does not pose any particular legal problem, unless the possession or use of crypto-assets is prohibited or regulated in the country concerned.
- Protection of sensitive data: this technique does not guarantee optimal protection of sensitive data, as the secret phrase can be seen, copied or stolen by unauthorized third parties.
Another aspect that you need to consider when backing up your secret phrase is the legal aspect and protection of sensitive data. Depending on where you live and where you store your secret phrase, you may be subject to different laws and regulations regarding data privacy and security.
Data privacy refers to the right of individuals to control how their personal information is collected, used and shared by others. Data security refers to the technical measures taken to protect data from unauthorized access or disclosure.
Some examples of laws and regulations that may affect how you backup your secret phrase are:
- GDPR (General Data Protection Regulation): A European Union law that aims to protect the personal data of EU citizens and residents by imposing strict rules on how data controllers and processors handle their data.
- CCPA (California Consumer Privacy Act): A California state law that gives California consumers more control over their personal information by granting them rights such as access, deletion and opt-out.
- HIPAA (Health Insurance Portability and Accountability Act): A US federal law that protects the privacy and security of health information by setting standards for how health care providers and other entities handle their data.
To comply with these laws and regulations, you need to be aware of:
- The type of data that you backup: Is it personal data (such as name, email address or phone number) or sensitive data (such as health records, biometric data or financial information)?
- The location where you backup your data: Is it within your country or jurisdiction, or is it in another country or region that may have different laws or standards?
- The purpose for which you backup your data: Is it for personal use only, or is it for business or professional purposes?
- The consent that you obtain from others: If you backup data that belongs to someone else (such as a client or a partner), do you have their permission and agreement on how you will use and protect their data?
To ensure that you respect the legal aspect and protection of sensitive data when backing up your secret phrase, you need to:
- Choose a technique that suits your needs and preferences in terms of privacy and security.
- Check the laws and regulations that apply to your situation and follow their requirements.
- Inform yourself about the risks and responsibilities involved in backing up your secret phrase.
- Respect the rights and interests of others whose data may be affected by your backup.
Use a metal device resistant to fire, water and corrosion
This technique consists of using a metal device resistant to fire, water and corrosion, such as a capsule or a plate, to engrave or insert the words of the secret phrase. This device can then be hidden or sealed in a safe place.
Advantages and disadvantages
- Advantages: this technique offers better protection against natural elements, but it requires a higher financial investment and can attract the attention of malicious people.
- Disadvantages: this technique requires a higher financial investment and can attract the attention of malicious people.
Risks related to cyber security and cyber espionage
- Risks related to cyber security: this technique does not involve exposure to networks or computer systems, so the risk of cyber security is low.
- Risks related to cyber espionage: this technique involves physical exposure to malicious or indiscreet third parties, so the risk of cyber espionage is high.
The legal aspect and protection of sensitive data
- Legal aspect: this technique does not pose any particular legal problem, unless the possession or use of crypto-assets is prohibited or regulated in the country concerned.
- Protection of sensitive data: this technique offers better protection of sensitive data than paper, as the metal device is more durable and less visible.
Another aspect that you need to consider when backing up your secret phrase is the legal aspect and protection of sensitive data. Depending on where you live and where you store your secret phrase, you may be subject to different laws and regulations regarding data privacy and security.
Data privacy refers to the right of individuals to control how their personal information is collected, used and shared by others. Data security refers to the technical measures taken to protect data from unauthorized access or disclosure.
Some examples of laws and regulations that may affect how you backup your secret phrase are:
- GDPR (General Data Protection Regulation): A European Union law that aims to protect the personal data of EU citizens and residents by imposing strict rules on how data controllers and processors handle their data.
- CCPA (California Consumer Privacy Act): A California state law that gives California consumers more control over their personal information by granting them rights such as access, deletion and opt-out.
- HIPAA (Health Insurance Portability and Accountability Act): A US federal law that protects the privacy and security of health information by setting standards for how health care providers and other entities handle their data.
To comply with these laws and regulations, you need to be aware of:
- The type of data that you backup: Is it personal data (such as name, email address or phone number) or sensitive data (such as health records, biometric data or financial information)?
- The location where you backup your data: Is it within your country or jurisdiction, or is it in another country or region that may have different laws or standards?
- The purpose for which you backup your data: Is it for personal use only, or is it for business or professional purposes?
- The consent that you obtain from others: If you backup data that belongs to someone else (such as a client or a partner), do you have their permission and agreement on how you will use and protect their data?
To ensure that you respect the legal aspect and protection of sensitive data when backing up your secret phrase, you need to:
- Choose a technique that suits your needs and preferences in terms of privacy and security.
- Check the laws and regulations that apply to your situation and follow their requirements.
- Inform yourself about the risks and responsibilities involved in backing up your secret phrase.
- Respect the rights and interests of others whose data may be affected by your backup.
Use an online service to backup your seed phrase
One of the techniques to backup your seed phrase is to use an online service that connects it to your verified identity. This way, you can recover your keys with your ID and a selfie, and still keep control of your money. In this article, we will explore the advantages and disadvantages of this technique, as well as the risks and legal aspects involved.
Advantages and disadvantages of online seed phrase backup
- Advantages: online seed phrase backup is easy and convenient. You don’t need to worry about storing or protecting a physical device or a paper backup. You can access your backup from anywhere with an internet connection and a compatible device. You can also benefit from the encryption and security features of the online service provider.
- Disadvantages: online seed phrase backup exposes your secret phrase to risks of hacking, censorship or confiscation by third parties who can access the servers or the identification process. You need to trust that the online service provider and its servers are reliable, honest and secure. You also need to trust that your identity information is safe and not misused. You may face legal or regulatory issues depending on where you live and where the servers are located. You may also have to pay fees or subscriptions for using the online service.
Risks related to cyber security and cyber spying in online seed phrase backup
- Risks related to cyber security: online seed phrase backup makes you use networks and computers, so the risk of cyber attacks is high. You need to trust that the online service and its servers protect your secret phrase and data well. You may face hackers, malware, ransomware, denial-of-service attacks or other threats that could compromise your backup or access to it. You may also face human errors, technical glitches or natural disasters that could damage or destroy the servers or your device.
- Risks related to cyber spying: online seed phrase backup makes you use networks and computers, so the risk of cyber spying is high. You need to trust that the online service and its servers keep your secret phrase and data private. You may face spies, snoops, trackers, advertisers or other parties that could monitor, collect, analyze or share your backup or activity data. You may also face government agencies, law enforcement or courts that could request, subpoena or seize your backup or data for legal or national security reasons.
- Risks related to phishing: online seed phrase backup makes you face fake messages and tricks that may make you give up your secret phrase or other information. Phishing is when someone pretends to be someone else, such as the online service or your wallet, to trick you into giving them your data or money. For example, you may receive an email that looks like it comes from the online service provider, asking you to verify your account or update your payment details by clicking on a link that leads to a fake website.
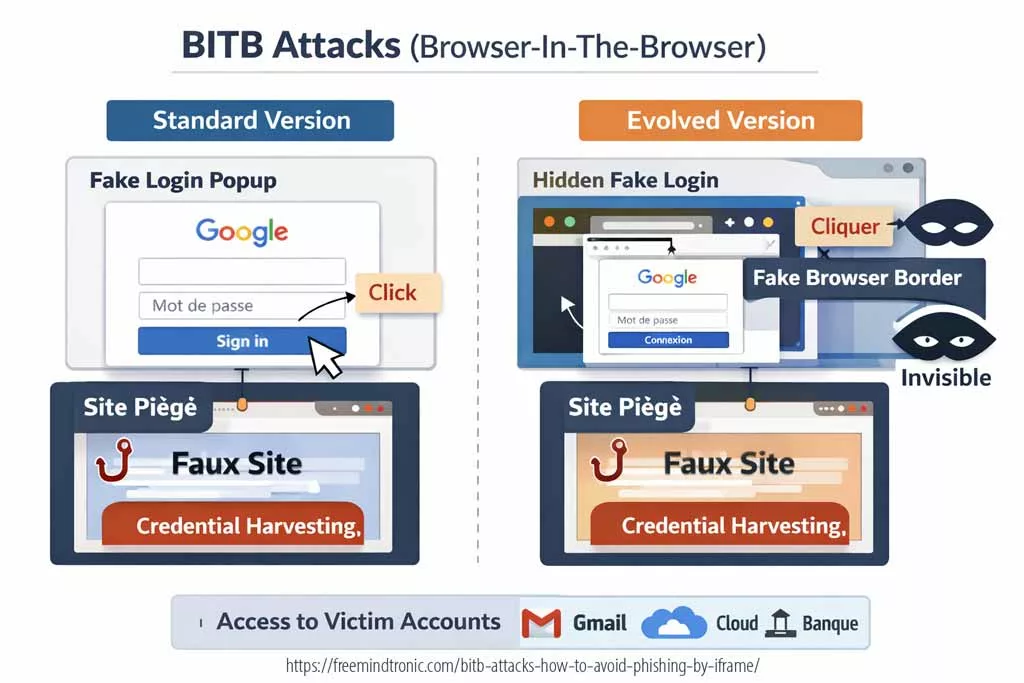
- Risks related to bitb: online seed phrase backup makes you face bad browser add-ons that may change or see your web activity and take your secret phrase or other data. Bitb is when someone adds malicious code to a browser extension that can spy on or modify what you do online. For example, you may install an extension that claims to enhance your browsing experience, but actually records your keystrokes, screenshots your screen or redirects you to malicious websites.
- Risks related to typosquatting: online seed phrase backup makes you face bad websites that look like the online service or your wallet, but have different spellings. Typosquatting is when someone registers a domain name that is similar to a legitimate one, but with a typo, to trick you into visiting their fake website. For example, you may type in www.onlineservice.com but end up on www.onlineservlce.com (with an L instead of an I), which looks identical but steals your login credentials or infects your device with malware.
The legal aspect and protection of sensitive data in online seed phrase backup
Online seed phrase backup may cause legal problems depending on the rules of the online service and its servers. You also need to think about the data privacy and security laws that affect you and follow them. Data privacy means the right of people to choose how their information is collected, used and shared by others. Data security means the ways to protect data from being seen or used by others who should not.
Some examples of laws and rules that may change how you backup your secret phrase are:
- GDPR (General Data Protection Regulation): A European Union law that protects the information of EU people by making strict rules on how data controllers and processors handle their data.
- CCPA (California Consumer Privacy Act): A California state law that gives California people more power over their information by giving them rights such as access, deletion and opt-out.
- HIPAA (Health Insurance Portability and Accountability Act): A US federal law that protects the privacy and security of health information by making standards for how health care providers and other groups handle their data.
To follow these laws and rules, you need to know:
- The kind of data that you backup: Is it personal data (such as name, email or phone) or sensitive data (such as health records, biometric data or money information)?
- The place where you backup your data: Is it in your country or area, or is it in another country or area that may have different laws or standards?
- The reason why you backup your data: Is it for yourself only, or is it for work or business purposes?
- The permission that you get from others: If you backup data that belongs to someone else (such as a client or a partner), do you have their OK and agreement on how you will use and protect their data?
To make sure that you respect the legal aspect and protection of sensitive data when backing up your secret phrase, you need to:
- Pick an online service that fits your needs and likes in terms of privacy and security.
- Learn about the risks and duties involved in backing up your secret phrase.
- Respect the rights and interests of others whose data may be affected by your backup.
Use a hybrid solution of cold wallet and online service
Another technique to backup your seed phrase is to use a hybrid solution of a cold wallet and an online service. A cold wallet is a device that stores your keys offline, such as a hardware wallet or a smart card. An online service is a platform that links your cold wallet to your verified identity and provides additional features, such as recovery, insurance or monitoring. This way, you can combine the security of a cold wallet with the convenience of an online service.
Advantages and disadvantages of hybrid seed phrase backup
- Advantages: hybrid seed phrase backup is secure and flexible. You can store your keys on a cold wallet that is resistant to hacking, malware or network attacks. You can also access your backup from an online service that offers recovery options, identity verification or other benefits. You can choose the level of security and convenience that suits your needs and preferences.
- Disadvantages: hybrid seed phrase backup is complex and costly. You need to buy and maintain a cold wallet device that is compatible with the online service. You also need to trust that the online service provider and its servers are reliable, honest and secure. You may face legal or regulatory issues depending on where you live and where the servers are located. You may also have to pay fees or subscriptions for using the online service or the cold wallet device. Some online services may also require you to renew your subscription annually or risk losing access to your backup. Some online services may also have access to your backup or keys, which could make them vulnerable to identity theft, fraud or coercion. Some online services may also split your backup into multiple servers or devices, which could increase the security but also the complexity of your backup.
Shamir’s Secret Sharing (SSS) method
Some online services use a technique called Shamir’s Secret Sharing (SSS) to split your seed phrase into multiple parts, called shares, that can be recombined to recover the original seed phrase. This technique allows you to distribute your backup across different locations, devices or people, and to set a threshold number of shares that are needed to restore your backup.
For example, you can split your seed phrase into 5 shares and store them on 5 different servers or devices. You can then set the threshold to 3, meaning that you need at least 3 out of 5 shares to recover your seed phrase. This way, you can protect your backup from being lost or stolen by one or two parties, but still be able to access it if you have 3 or more shares.
Some cold wallets use this technique to backup seed phrases in a secure way. They encrypt the parts of the seed phrase in a secure element in the device and send them to partners through a secure channel. When restoring, the parts are sent back by the partners and the seed phrase can be generated in the new device.
Advantages and disadvantages of SSS method
- Advantages: SSS method is secure and resilient. You can increase the security of your backup by splitting it into multiple parts that are stored separately. You can also increase the resilience of your backup by setting a lower threshold that allows you to recover it even if some parts are lost or damaged.
- Disadvantages: SSS method is complex and risky. You need to manage multiple parts of your backup and keep track of where they are stored and how they can be accessed. You also need to trust that the parties who hold the parts of your backup are reliable, honest and secure. You may face legal or regulatory issues depending on where the parts of your backup are located. You may also face technical or human errors that could compromise the integrity or availability of your backup.
Risks related to SSS method
- Risks related to cyber security: SSS method makes you use networks and computers, so the risk of cyber attacks is moderate. You need to trust that the parties who hold the parts of your backup protect them well. You may face hackers, malware, ransomware, denial-of-service attacks or other threats that could compromise one or more parts of your backup or access to them. You may also face human errors, technical glitches or natural disasters that could damage or destroy one or more parts of your backup.
- Risks related to cyber spying: SSS method makes you use networks and computers, so the risk of cyber spying is moderate. You need to trust that the parties who hold the parts of your backup keep them private. You may face spies, snoops, trackers, advertisers or other parties that could monitor, collect, analyze or share one or more parts of your backup or activity data. You may also face government agencies, law enforcement or courts that could request, subpoena or seize one or more parts of your backup for legal or national security reasons.
- Risks related to collusion: SSS method makes you rely on multiple parties who hold the parts of your backup, so the risk of collusion is moderate. You need to trust that the parties who hold the parts of your backup do not cooperate with each other or with other parties to steal or misuse your backup. For example, if you split your seed phrase into 5 shares and set the threshold to 3, you need to trust that no 3 parties will collude to recover your seed phrase without your consent or knowledge.
- Risks related to fragmentation: SSS method makes you split your seed phrase into multiple parts, so the risk of fragmentation is moderate. You need to ensure that the parts of your backup are compatible and consistent with each other and with the original seed phrase. You may face errors in splitting or recombining the parts of your backup that could result in an invalid or corrupted seed phrase. You may also face changes in formats or standards that could make some parts of your backup obsolete or incompatible.
The legal aspect and protection of sensitive data in hybrid seed phrase backup
Hybrid seed phrase backup may cause legal problems depending on the rules of the online service and its servers. You also need to think about the data privacy and security laws that affect you and follow them. Data privacy means the right of people to choose how their information is collected, used and shared by others. Data security means the ways to protect data from being seen or used by others who should not.
Some examples of laws and rules that may change how you backup your secret phrase are:
- GDPR (General Data Protection Regulation): A European Union law that protects the information of EU people by making strict rules on how data controllers and processors handle their data.
- CCPA (California Consumer Privacy Act): A California state law that gives California people more power over their information by giving them rights such as access, deletion and opt-out.
- HIPAA (Health Insurance Portability and Accountability Act): A US federal law that protects the privacy and security of health information by making standards for how health care providers and other groups handle their data.
To follow these laws and rules, you need to know:
- The kind of data that you backup: Is it personal data (such as name, email or phone) or sensitive data (such as health records, biometric data or money information)?
- The place where you backup your data: Is it in your country or area, or is it in another country or area that may have different laws or standards?
- The reason why you backup your data: Is it for yourself only, or is it for work or business purposes?
- The permission that you get from others: If you backup data that belongs to someone else (such as a client or a partner), do you have their OK and agreement on how you will use and protect their data?
To make sure that you respect the legal aspect and protection of sensitive data when backing up your secret phrase, you need to:
- Pick an online service that fits your needs and likes in terms of privacy and security.
- Learn about the risks and duties involved in backing up your secret phrase.
- Respect the rights and interests of others whose data may be affected by your backup.
Use a contactless technology
This technique consists of using a contactless technology that allows you to store your secret phrase in an electronic device, such as a card or a keychain, that works with NFC (Near Field Communication) technology. This device can be used with a compatible smartphone to backup and share your private keys, passwords or secret phrases.
Advantages and disadvantages
- Advantages: this technique offers ease of transport and resistance to shocks. It also allows you to verify and restore your secret phrase at any time with your smartphone.
- Disadvantages: this technique requires a compatible smartphone and a dedicated app. It also exposes you to the risks of loss or theft of your device. This can be dangerous if the NFC Cold Wallet does not have a digital backup system encrypted that can allow restoration in another device and/or a cloning or copying system between NFC devices, such as the EviSeed technology.
Risks related to cybersecurity and cyberespionage
- Risks related to cybersecurity: this technique is not connected to networks, computer systems or servers in principle and has no database with the same properties as an HSM, so the cybersecurity risk is almost nil. You must ensure that your device and your smartphone are protected by PIN codes or passwords or a multi-authentication system, and that you use a reliable and secure app of origin.
- Risks related to cyberespionage: in principle, a cold wallet is not connected and cannot be exposed to espionage on networks and computer systems. However, the attack by listening to the NFC signal is possible if the device is not equipped with a security and encryption system. The risk of remote espionage is therefore almost nil. As for proximity cyberespionage, whether invasive or non-invasive, the risk is nil to moderate depending on the type of security and access control implemented. You should avoid sharing your secret phrase with unauthorized third parties or using it in public or insecure places. Some technologies such as EviSeed have an encrypted sharing system with trust criteria defined by the sender that the recipient cannot modify and must also have an NFC device to access the secret phrase.
The legal aspect and the protection of sensitive data
- Legal aspect: this technique does not pose any particular legal problem, unless the possession or use of crypto assets is prohibited or regulated in the country concerned.
- Protection of sensitive data: this technique depends on the encryption and security measures implemented by the electronic device and its NFC technology. You should inquire about the technical characteristics and guarantees offered by the manufacturer or supplier of the device.
Another aspect that you need to consider when backing up your secret phrase is the legal aspect and protection of sensitive data. Depending on where you live and where you store your secret phrase, you may be subject to different laws and regulations regarding data privacy and security.
Data privacy refers to the right of individuals to control how their personal information is collected, used and shared by others. Data security refers to the technical measures taken to protect data from unauthorized access or disclosure.
Some examples of laws and regulations that may affect how you backup your secret phrase are:
- GDPR (General Data Protection Regulation): A European Union law that aims to protect the personal data of EU citizens and residents by imposing strict rules on how data controllers and processors handle their data.
- CCPA (California Consumer Privacy Act): A California state law that gives California consumers more control over their personal information by granting them rights such as access, deletion and opt-out.
- HIPAA (Health Insurance Portability and Accountability Act): A US federal law that protects the privacy and security of health information by setting standards for how health care providers and other entities handle their data.
To comply with these laws and regulations, you need to be aware of:
- The type of data that you backup: Is it personal data (such as name, email address or phone number) or sensitive data (such as health records, biometric data or financial information)?
- The location where you backup your data: Is it within your country or jurisdiction, or is it in another country or region that may have different laws or standards?
- The purpose for which you backup your data: Is it for personal use only, or is it for business or professional purposes?
- The consent that you obtain from others: If you backup data that belongs to someone else (such as a client or a partner), do you have their permission and agreement on how you will use and protect their data?
To ensure that you respect the legal aspect and protection of sensitive data when backing up your secret phrase, you need to:
- Choose a technique that suits your needs and preferences in terms of privacy and security.
- Check the laws and regulations that apply to your situation and follow their requirements.
- Inform yourself about the risks and responsibilities involved in backing up your secret phrase.
- Respect the rights and interests of others whose data may be affected by your backup.
Use a mnemonic method
This technique consists of using a mnemonic method that consists of associating each word of the secret phrase with a mental image or a story. This method allows you to memorize your secret phrase more easily without having to write it down or store it. It requires however a good memory and regular repetition to not forget your secret phrase.
Advantages and disadvantages
- Advantages: this technique offers discretion and total independence, but it exposes the secret phrase to risks of amnesia, confusion or interference.
- Disadvantages: this technique exposes the secret phrase to risks of amnesia, confusion or interference.
Risks related to cyber security and cyber espionage
- Risks related to cyber security: this technique does not involve exposure to networks or computer systems, so the risk of cyber security is low.
- Risks related to cyber espionage: this technique does not involve exposure to networks or computer systems, so the risk of cyber espionage is low.
The legal aspect and protection of sensitive data
- Legal aspect: this technique does not pose any particular legal problem, unless the possession or use of crypto-assets is prohibited or regulated in the country concerned.
- Protection of sensitive data: this technique offers optimal protection of sensitive data as long as you do not reveal your mnemonic method or your secret phrase.
Another aspect that you need to consider when backing up your secret phrase is the legal aspect and protection of sensitive data. Depending on where you live and where you store your secret phrase, you may be subject to different laws and regulations regarding data privacy and security.
Data privacy refers to the right of individuals to control how their personal information is collected, used and shared by others. Data security refers to the technical measures taken to protect data from unauthorized access or disclosure.
Some examples of laws and regulations that may affect how you backup your secret phrase are:
- GDPR (General Data Protection Regulation): A European Union law that aims to protect the personal data of EU citizens and residents by imposing strict rules on how data controllers and processors handle their data.
- CCPA (California Consumer Privacy Act): A California state law that gives California consumers more control over their personal information by granting them rights such as access, deletion and opt-out.
- HIPAA (Health Insurance Portability and Accountability Act): A US federal law that protects the privacy and security of health information by setting standards for how health care providers and other entities handle their data.
To comply with these laws and regulations, you need to be aware of:
- The type of data that you backup: Is it personal data (such as name, email address or phone number) or sensitive data (such as health records, biometric data or financial information)?
- The location where you backup your data: Is it within your country or jurisdiction, or is it in another country or region that may have different laws or standards?
- The purpose for which you backup your data: Is it for personal use only, or is it for business or professional purposes?
- The consent that you obtain from others: If you backup data that belongs to someone else (such as a client or a partner), do you have their permission and agreement on how you will use and protect their data?
To ensure that you respect the legal aspect and protection of sensitive data when backing up your secret phrase, you need to:
- Choose a technique that suits your needs and preferences in terms of privacy and security.
- Check the laws and regulations that apply to your situation and follow their requirements.
- Inform yourself about the risks and responsibilities involved in backing up your secret phrase.
- Respect the rights and interests of others whose data may be affected by your backup.
How to update your backup phrase
Sometimes, you may need to update your Backup phrase if you change your wallet settings or switch to a different custody model. For example, if you add a passphrase to your singlesig wallet, you need to update your backup phrase with the new passphrase. Or if you migrate from singlesig to multisig, you need to create new recovery phrase backups for each of the multisig keys.
To update your recovery phrase backup, follow these steps:
- Make sure you have access to your current recovery phrase backup and any other information that may affect your wallet, such as a passphrase or a derivation path.
- Create a new physical backup of your updated seed phrase using the same methods and materials as before.
- Test your new recovery phrase backupusing a different device or platform than the one you used to create or update your wallet.
- If everything matches, your new recovery phrase backup works and you can safely destroy or erase your old recovery phrase backup.
- If something doesn’t match, check for errors in your new recovery phrase backup and try again.
Why and How to Share Your Recovery Phrase Backup with Trusted Parties.
In some cases, If you choose to share your backup seed phrase with trusted individuals, such as family, friends, or lawyers, to ensure your cryptographic assets remain accessible in emergencies, accidents, or death. However, sharing your backup seed phrase has risks and challenges, such as choosing trustworthy individuals, secure communication, and preventing conflicts or disputes.
If you want to share your approved seed phrase with others, follow these steps:
- Choose trusted individuals who have knowledge about cryptography to access your backup seed phrase. Explain to them the risks and responsibilities associated with accessing it, as well as what a seed phrase is and how it works.
- Select a secure communication method that protects your privacy and prevents unauthorized access or interception. You can use encrypted messaging apps, password-protected files, or face-to-face meetings. For an added layer of security, you can use Freemindtronic’s EviSeed technology. EviSeed allows you to share your encrypted seed phrases offline via the Near Field Communication (NFC) encrypted communication protocol between end-to-end encrypted NFC devices. You can also share your seed phrases via an RSA-4096 encrypted QR code, which can be generated from an NFC device and shared through any means of communication, including air gap (webcam, proximity, email, SMS, chat, face-to-face).
- Share your backup seed phrase with chosen individuals using the secure communication method selected. Include any relevant information for accessing or managing your cryptographic assets, such as a secret phrase, derivation path, or wallet instructions. Use EviSeed’s patented technology for higher security, including segmented key authentication by adding trust criteria.
For example, share one or more trust criteria to control access conditions to your AES-256 post-quantum encrypted seed phrases. Share a password associated with a unique geographic zone, which must be used in a specific location to decrypt your seed phrase. Provide this password to a trusted third party who does not know the geographic zone or who can only access it under complicated conditions, such as at a notary, sealed by a bailiff, or in a bank vault. - Once you have shared your backup seed phrase with your chosen individuals, ask them to confirm that they have received and understood it, as well as any other relevant information.</li>
- Keep their contact information in a safe place in case you need to contact them in the future.
- With EviSeed technology, you have other options for sharing backup seed phrases. You can clone your NFC device with all of your trust criteria onto another Freemindtronic NFC device. Then, you can entrust it to a trusted third party or keep it in an easily remembered location. Choose an extremely rugged and waterproof IP89KNFC device to limit the risk of damage. Your recovery phrase backups are also protected against the risk of theft or loss since the device is physically locked with multi-factor physical and digital authentication. Additionally, if you have added trust criteria, even if the access controls are compromised, your recovery phrase backups will remain secure until all the trust criteria you have defined are validated. You can also share your individually encrypted and protected seed phrases by trust criteria, which you can also share in a segmented manner among various individuals, as explained above.
- Lastly, make sure to periodically review and update your list of trusted individuals, as well as your communication and security methods, to ensure the ongoing protection and accessibility of your cryptographic assets.

Best practices for creating and storing your physical backup
Here are some best practices that you should follow when creating and storing your physical backup:
- Write down or engrave your seed phrase on a durable material such as paper, metal or plastic. Avoid using materials that can fade, rust, melt or degrade over time.
- Use a pen or a tool that produces clear and permanent marks on the material. Avoid using pencils, markers or stickers that can smudge, erase or peel off.
- Use a standard format for writing down your seed phrase such as BIP39 or SLIP39. These formats use a predefined list of words that are easy to spell and recognize. Avoid using abbreviations, acronyms or symbols that can cause confusion or errors.
- Make multiple copies of your physical backup and store them in different locations. This way, you can reduce the risk of losing all your backups in case of theft, loss or damage. You can also use different materials for each copy to increase the durability and diversity of your backups.
- Store your physical backups in a safe and secret place that only you know and can access. You can use a safe, a lockbox, a hidden compartment or any other secure container that can protect your backups from unauthorized access or environmental factors.
- Do not share your seed phrase with anyone or store it online. Your seed phrase is the key to your crypto wallet and funds. If you share it with anyone or store it online, you are exposing yourself to the risk of losing your funds to hackers, scammers or third parties.
Tools for Creating and Storing Your Physical Backups
Several tools help you create and store your physical backups easily and securely. These tools let you write or engrave your seed phrase on durable materials, protecting them from damage or tampering. Here are some examples:
CryptoSteel: This device engraves your seed phrase on stainless steel tiles that resist fire, water, and corrosion. The tiles assemble in a metal casing with a lock and a seal. CryptoSteel is compatible with BIP39 and SLIP39 formats and stores up to 24 words.
Billfodl: This device also engraves your seed phrase on stainless steel tiles that resist fire, water, and corrosion. The tiles arrange in a metal frame with a sliding cover and a seal. Billfodl is compatible with the BIP39 format and stores up to 24 words.
Cobo Tablet: This device also engraves your seed phrase on stainless steel tiles that resist fire, water, and corrosion. The tiles insert into a metal plate with holes for each word position. Cobo Tablet is compatible with the BIP39 format and stores up to 24 words.
Paper Wallet: This is the simplest way to create a physical backup. You just write your seed phrase on paper with a pen. You can also print your seed phrase if you prefer. However, paper wallets are not durable and can be damaged by fire, water, or wear and tear.
NFC Seed Backup: This device encrypts and saves your seed phrase on an NFC coin that resists fire, water, and corrosion. An app on your smartphone scans the NFC coin and views your seed phrase without leaving anything visible. NFC Seed Backup is compatible with the BIP39 format and stores up to 24 words.
EviSeed: EviSeed is a technology developed by Freemindtronic that allows you to save and share sensitive data such as private keys, recovery phrases, or passwords. It is integrated into physical devices such as electronic cards that work with NFC (Near Field Communication) technology. The EviSeed technology offers several advantages:</p>
- The EviSeed technology uses two patented systems of multifactor authentication and advanced access control.
- It encrypts data with the AES256 algorithm, ensuring a high level of security.
- It stores data in EPROM memory, ensuring long-term durability without a battery.
- It allows data sharing via QR code, NFC tag, NFC reader/writer, Bluetooth, Wi-Fi, SMS, email, etc.
- It supports multiple languages, formats, standards, protocols, etc.
- It protects data with patented physical blockchain technology, allowing user-defined access control, authentication, encryption, decryption, etc.
- EviSeed is compatible with BIP39, SLIP39, and IOTA formats and can store up to 100 recovery phrases.
- It protects data with two international patents on access control and segmented key authentication.
et=”_blank” rel=”noopener”>DataShielder HSM PGP: This device allows you to encrypt all your seed phrases using the EviSeed function</strong> for just €39 as a one-time cost. This enables users to duplicate the seed phrases multiple times and store them in different locations, ensuring cyber resilience.
et=”_blank” rel=”noopener”>SeedNFC HSM: This device incorporates advanced technologies such as AES-256 CBC to secure recovery phrases and an RSA 4096 key pair</strong> to share or duplicate them even remotely between NFC HSMs. This device can store up to 100 BIP39 seed phrases (12/15/18/21/24 words) in 8 languages: English, French, Italian, Spanish, Japanese, Korean, Simplified Chinese, and Traditional Chinese. It also manages up to 50 different wallets on the Bitcoin and Ethereum blockchains and is discreet and easy to carry.</p>
Keepser: Keepser is another product based on EviSeed technology created by Keepser Group. It allows you to store up to 100 recovery phrases on an electronic card embedded in military-grade resin. It offers the same features as EviSeed plus some additional benefits.
Understanding and Securing Your Recovery Phrase
In this article, we have explained what a recovery phrase is and how to secure it. A recovery phrase is a list of 12 or 24 words that can restore your crypto wallet and your private keys on any device. It is the ultimate key to access your crypto assets, so you need to keep it safe and secret.
Tips for Physically Backing Up and Storing Your Recovery Phrase
We have given some tips on how to physically back up your recovery phrase and store it in a safe and secret place. Some of the methods include:
- Writing it down on paper and keeping it in a fireproof and waterproof container.
- Engraving it on durable metals like stainless steel or titanium and hiding it in a secure location.
- Encrypting it with a strong password and storing it on an offline device or a cloud service that you trust.
- Using a legitimate and trustworthy hardware wallet and keeping it away from physical damage or malware.</p></li>
- Using a decentralized digital vault that offers a high level of security and privacy and does not require you to trust a third party.
- </p>
Introducing EviSeed Technology
We have introduced EviSeed, a technology developed by Freemindtronic that allows you to store and share your recovery phrase securely and contactlessly. EviSeed uses NFC technology to store your recovery phrase in a hardware device. This device can last for at least 40 years without a battery or maintenance. This provides a highly reliable method for securing your recovery phrase.
Furthermore, EviSeed employs its own patented segmented key technology to add criteria to the encryption keys of your recovery phrases. All segments must be reunited and validated to access your seed phrases. This gives you total control of the segmentation from end to end with your NFC HSM device by Freemindtronic. EviSeed is compatible with all BIP39 recovery phrases and offers several solutions for storing encrypted recovery phrases. These solutions include externalizing them from the NFC device. This ensures you can recover your recovery phrase in case of loss or theft.
In Summary
we hope this article has helped you understand the importance of securing your recovery phrase. Additionally, we have discussed the different options available to do so. Remember, your recovery phrase is the key to your crypto wealth. Therefore, treat it with care and respect.
Among the various solutions, we believe that EviSeed is the most innovative and reliable one. This solution combines the advantages of physical and digital backups. Furthermore, it adds an extra layer of security and convenience. With EviSeed, you can access your crypto funds with ease and confidence. Consequently, you won’t fear losing or compromising your recovery phrase.