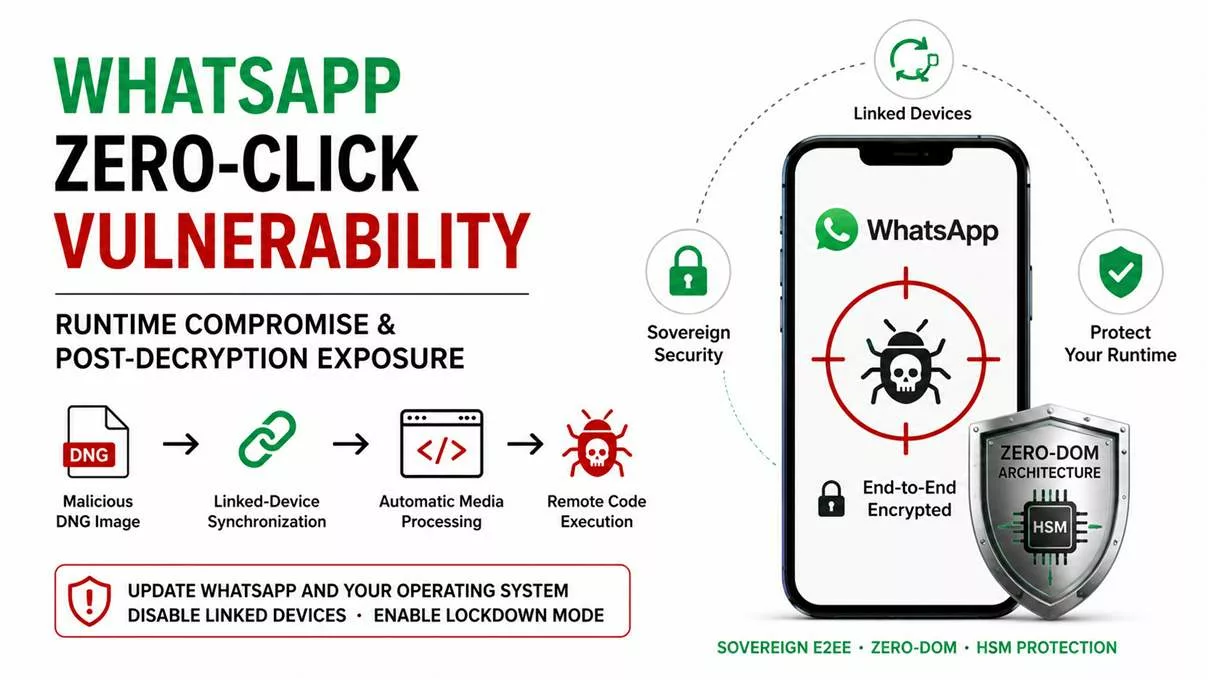
WhatsApp zero-click vulnerability — the critical flaw CVE-2025-55177, chained with Apple CVE-2025-43300, enables remote code execution through malicious DNG images abusing linked-device synchronization and automatic media processing. This attack highlights the limits of traditional E2EE once the mobile runtime itself becomes compromised. Update WhatsApp and your operating system immediately.
Executive Summary — WhatsApp Zero-Click Vulnerability, Runtime Compromise & Sovereign E2EE
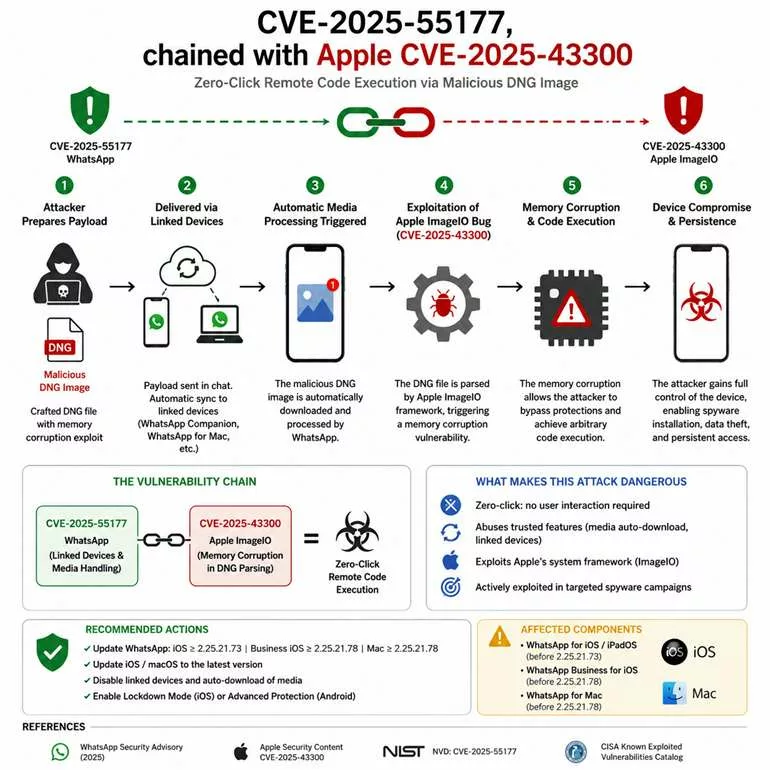
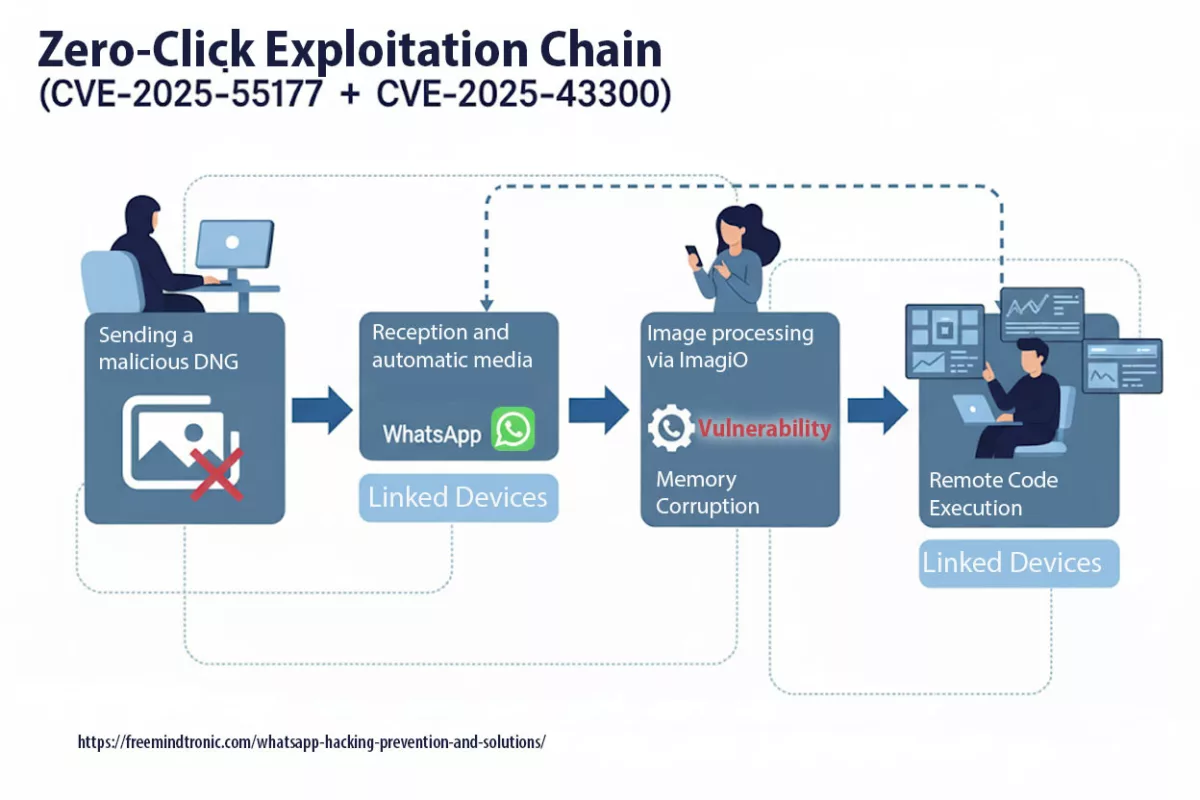
The WhatsApp zero-click vulnerability (CVE-2025-55177 chained with Apple CVE-2025-43300) enables arbitrary remote code execution through a specially crafted DNG image without requiring any user interaction. By abusing linked-device synchronization and automatic media processing, attackers can remotely trigger malicious parsing operations capable of compromising the runtime itself.
This attack is strategically important because it demonstrates a growing reality in modern cybersecurity: end-to-end encryption protects communications during transport, but it does not necessarily protect already decrypted data once the runtime environment becomes compromised.
Meta confirmed active exploitation against high-risk targets. Patched versions are available:
- WhatsApp for iOS ≥ 2.25.21.73
- WhatsApp Business iOS ≥ 2.25.21.78
- WhatsApp for Mac ≥ 2.25.21.78
Critical advisory — immediate action required
This vulnerability should not be viewed solely as a messaging application flaw, but as a runtime compromise threat capable of exposing already decrypted information.
High-risk users should:
- update WhatsApp and the operating system immediately;
- temporarily disable linked devices and automatic media downloads;
- enable Apple Lockdown Mode or Android Advanced Protection;
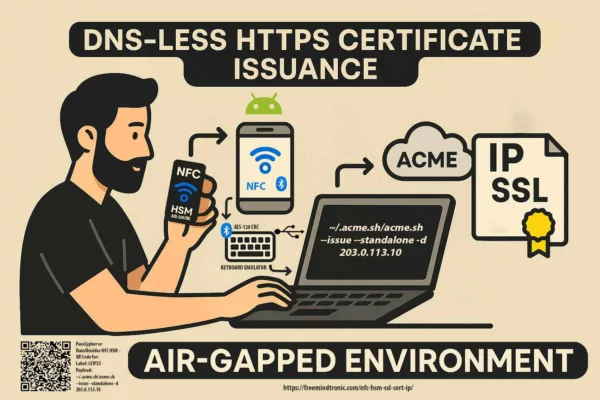
- isolate sensitive communications using sovereign Zero-DOM architectures and NFC/HSM segmented-key protection.
Reading Parameters
Executive summary reading time: 3 minutes
Full article estimated reading time: 18 minutes
Initial publication: 30 September 2025
Last update: 26 May 2026
Complexity level: Expert
Languages available: FR · EN · ES · CAT
Editorial format: Strategic cybersecurity analysis
Primary topic: WhatsApp zero-click vulnerability
Secondary topics: runtime compromise, sovereign E2EE, post-decryption security, Zero-DOM
About the author: Jacques Gascuel, inventor and founder of Freemindtronic®, architect of sovereign cybersecurity infrastructures and creator of NFC & PGP HSM technologies dedicated to Zero-DOM protection of critical secrets.
Key takeaways
The WhatsApp zero-click vulnerability reveals a much broader evolution in mobile cybersecurity. Modern attacks increasingly target the runtime environment itself rather than the encrypted transport channel alone.
Once a runtime becomes compromised, already decrypted information may become exposed through memory buffers, synchronization mechanisms, media parsers or local caches.
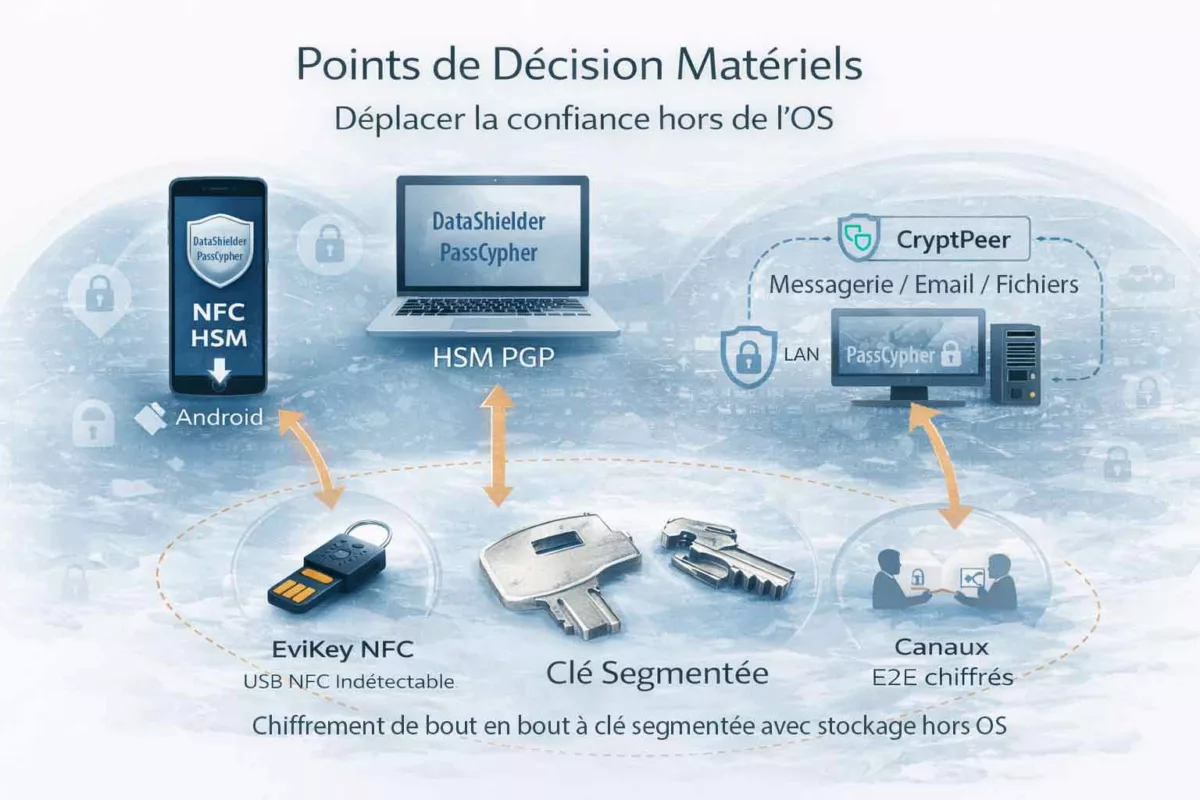
This fundamentally changes the security model of modern E2EE communications and validates the growing importance of:
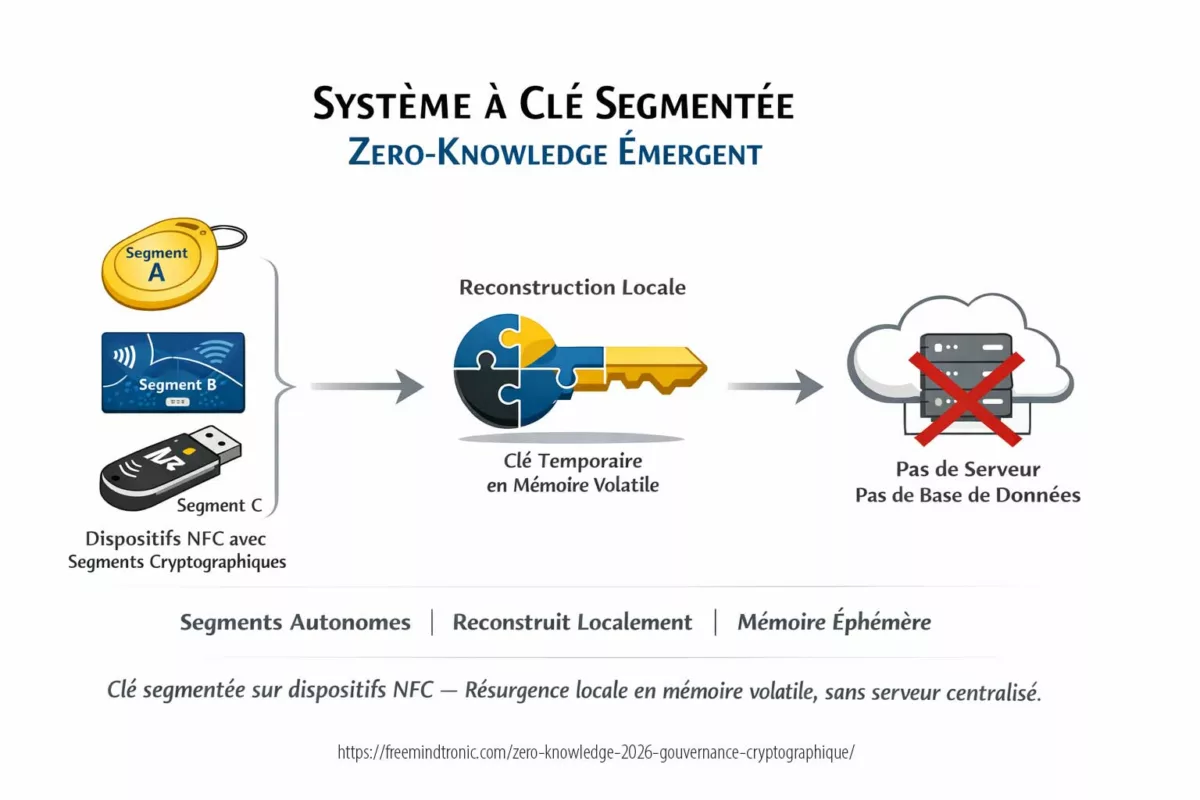
- Zero-DOM architectures;
- segmented key infrastructures;
- offline HSM protection;
- post-decryption security models;
- sovereign runtime trust architectures.
New warning — local runtime exposure and unencrypted chat concerns
Recent analyses suggest that some WhatsApp conversations may become locally accessible without effective encryption in specific runtime contexts associated with the Meta ecosystem.
This does not directly break transport-layer E2EE. However, it confirms a critical strategic reality, the WhatsApp zero-click vulnerability becomes dramatically more dangerous once a compromised runtime gains access to already decrypted data.
Transport encryption alone is no longer sufficient when the operating environment itself can become hostile.
The chronicles displayed above ↑ belong to the Digital Security section. They extend the analysis of zero-click exploits, mobile spyware, runtime compromise, sovereign E2EE and post-decryption security. This selection complements the present chronicle dedicated to the WhatsApp zero-click vulnerability, CVE-2025-55177, Apple CVE-2025-43300 and the systemic risks linked to linked-device synchronization, malicious DNG media processing and compromised mobile runtimes.
- Executive Summary
- Runtime compromise & post-decryption exposure
- Critical advisory
- Affected versions
- Immediate defensive actions
- Human error & social engineering
- Modern attack techniques
- Weak signals observed
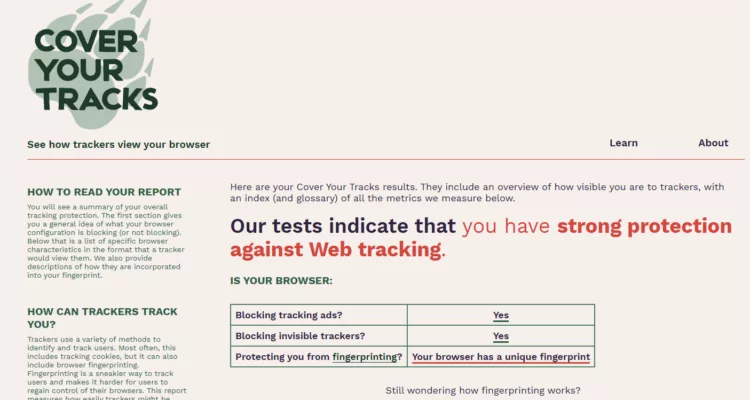
- Monitoring tools & misuse risks
- Sovereign countermeasures
- Why Zero-DOM matters
- Related vulnerabilities
- FAQ
- Strategic outlook
- Toward sovereign E2EE
Why the WhatsApp Zero-Click Vulnerability Goes Beyond Traditional E2EE
What makes this attack exceptional?
Unlike traditional phishing campaigns, victims may never see the malicious payload. A single crafted DNG image processed automatically through linked-device synchronization can silently trigger runtime compromise without any click, download confirmation or visible warning.
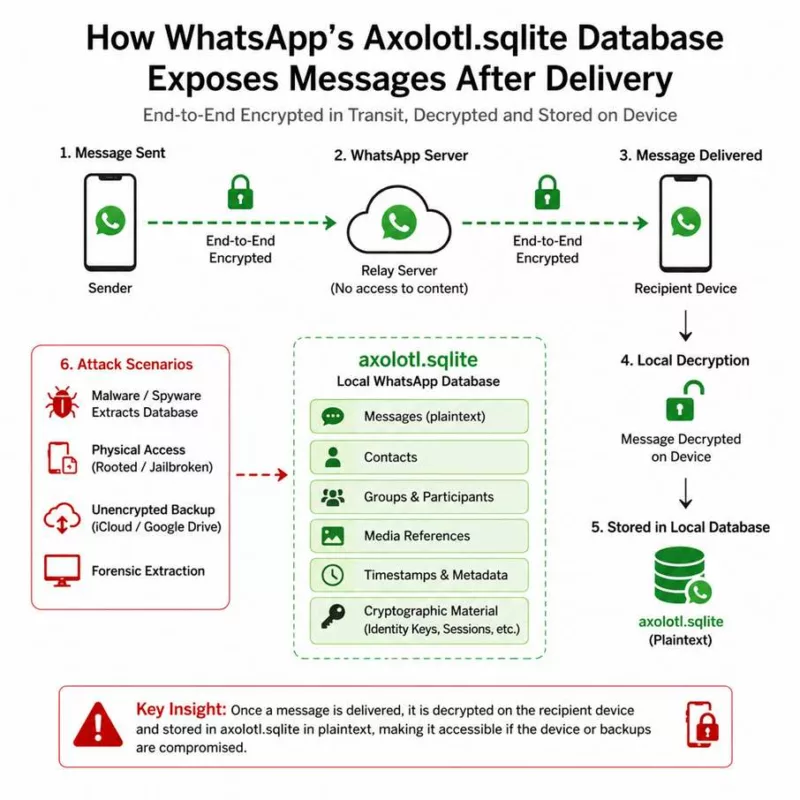
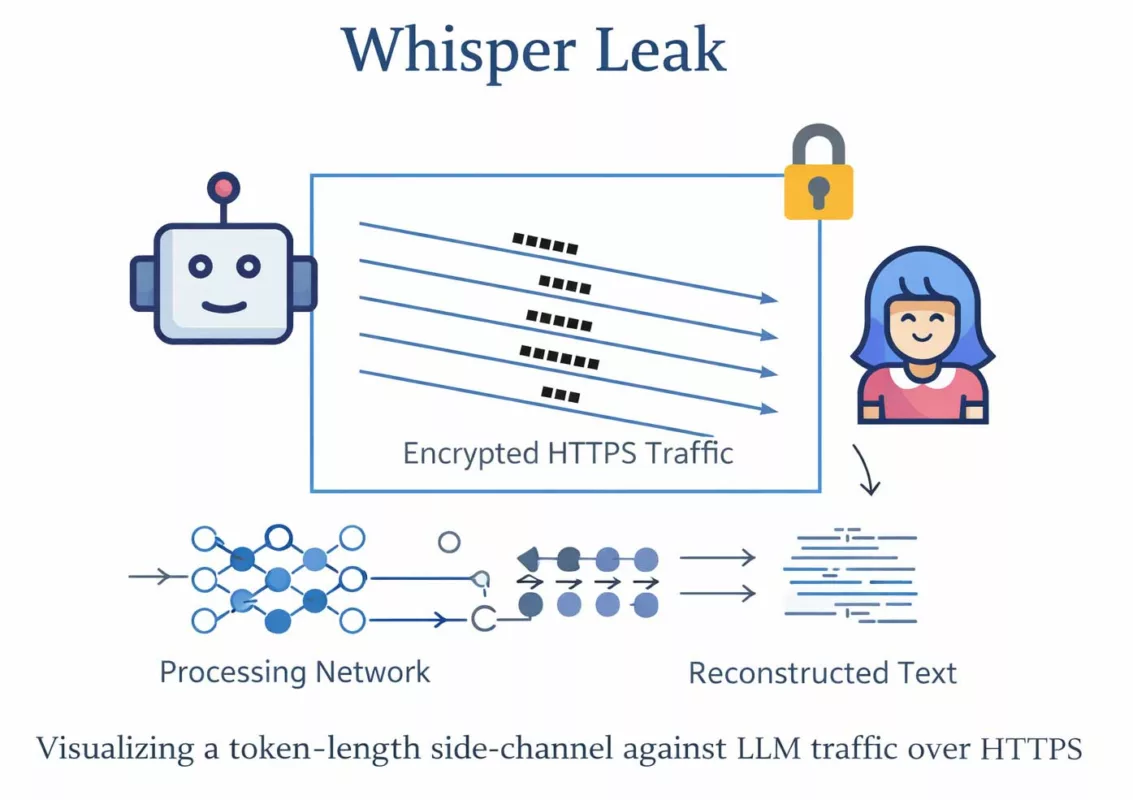
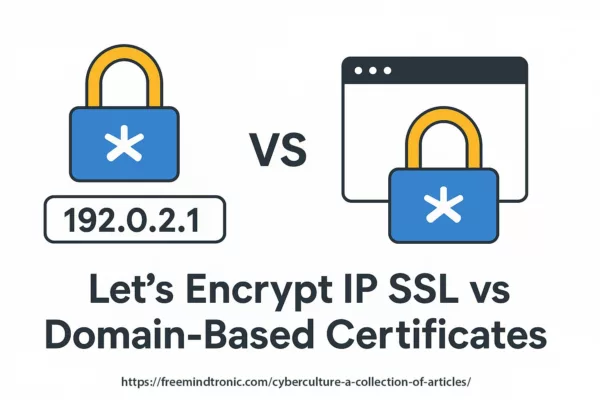
The WhatsApp zero-click vulnerability demonstrates a fundamental limitation of modern messaging architectures: end-to-end encryption primarily protects data during transport, but not necessarily once information has already been decrypted inside the runtime environment.
For the first time, a mainstream messaging ecosystem demonstrates at scale how transport-layer E2EE can remain technically intact while already decrypted information becomes exposed through runtime compromise.
Recent findings concerning potentially unencrypted local WhatsApp chat exposure reinforce this issue. A compromised runtime may potentially access:
- memory buffers;
- temporary cryptographic material;
- local caches;
- media processing pipelines;
- linked-device synchronization mechanisms.
This vulnerability also illustrates a broader phenomenon: the gradual collapse of implicit trust in modern mobile runtimes.
Smartphones now integrate:
- complex media parsers;
- cloud synchronization layers;
- cross-application communication;
- persistent session management;
- AI-assisted processing pipelines.
- AI-assisted media classification;
As a result, protecting communications alone is no longer sufficient. Security architectures must also protect the operational environment manipulating sensitive information after decryption.
Critical distinction — software vulnerability vs structural runtime exposure
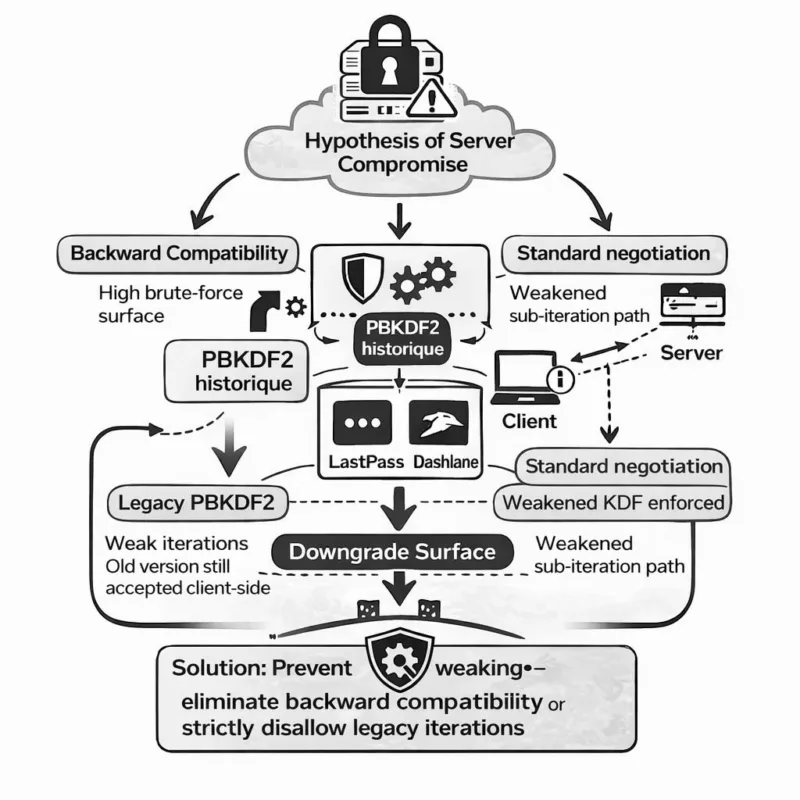
A software vulnerability and a runtime exposure problem are not the same category of risk.
For example, macOS CVE-2026-28910 involved a genuine sandbox bypass vulnerability requiring active exploitation of a software flaw.
By contrast, analyses such as the Mysk findings reveal a structural trust problem: already decrypted data may remain exposed because of runtime assumptions, local storage models and application-level permissions.
A fully patched system may therefore still expose sensitive information if runtime memory and local processing mechanisms remain accessible.
Critical Update — WhatsApp Zero-Click Vulnerability CVE-2025-55177
The vulnerability chain combines WhatsApp CVE-2025-55177 with Apple CVE-2025-43300 through malicious DNG media processing. By abusing linked-device synchronization and automatic media parsing, attackers can remotely trigger runtime compromise without any user interaction. Meta confirmed active exploitation in real-world spyware campaigns targeting high-risk profiles. The vulnerability is also listed in the CISA Known Exploited Vulnerabilities catalog, confirming its operational relevance.
Affected versions
- WhatsApp for iOS prior to 2.25.21.73
- WhatsApp Business for iOS prior to 2.25.21.78
- WhatsApp for Mac prior to 2.25.21.78
Immediate defensive actions
The first priority remains immediate patching of WhatsApp and the operating system. For sensitive environments, additional measures are recommended:
- disable linked-device synchronization temporarily;
- disable automatic media downloads;
- activate Apple Lockdown Mode or Android Advanced Protection;
- rotate critical credentials from a clean environment;
- monitor suspicious linked-device activity.
Forensics & Incident ResponseIf compromise is suspected:
- preserve logs, timestamps, filenames and suspicious URLs;
- capture affected network traces and DNS resolutions;
- revoke WhatsApp Web sessions immediately;
- rotate sensitive credentials from a clean device;
- perform forensic acquisition before any factory reset.
Human Error Remains a Persistent Attack Vector
Social-engineering attacks requesting six-digit verification codes remain extremely effective. Trusted-contact impersonation and fake support operations continue enabling account takeover despite modern security improvements. Two-step verification reduces the risk but cannot eliminate social-engineering exposure entirely.
Modern Attack Techniques Behind WhatsApp Zero-Click Campaigns
Modern zero-click attacks no longer target messaging applications alone. They increasingly seek to compromise the mobile runtime itself in order to access already decrypted information, active sessions and memory-resident secrets. Attackers now exploit:
- linked-device synchronization abuse;
- trusted-group delivery and auto-download trust abuse;
- malicious DNG image parsing;
- automatic media processing;
- runtime memory corruption;
- remote arbitrary URL fetching;
- cross-runtime spyware delivery chains.
Some campaigns also targeted Samsung image parsers through DNG files delivered via WhatsApp, demonstrating that the attack surface extends far beyond the messaging application itself. Other campaigns abuse official WhatsApp pairing mechanisms through so-called GhostPairing techniques, silently attaching remote browsers or systems to an active victim session.
Emerging account-hijacking techniques targeting trusted mobile sessions
Recent security reports describe increasingly sophisticated WhatsApp account hijacking campaigns targeting mobile users through linked-device abuse, trusted-session persistence and runtime manipulation techniques.
These reports should be distinguished from the officially documented vulnerability chain involving WhatsApp CVE-2025-55177 and Apple CVE-2025-43300, which concerns malicious DNG media processing, linked-device synchronization abuse and runtime compromise.
While distinct from officially documented zero-click CVEs, these operations reinforce a broader strategic trend:
modern messaging attacks increasingly target synchronization trust mechanisms and runtime exposure rather than transport-layer encryption itself.
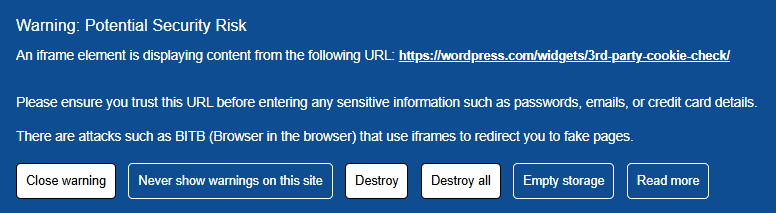
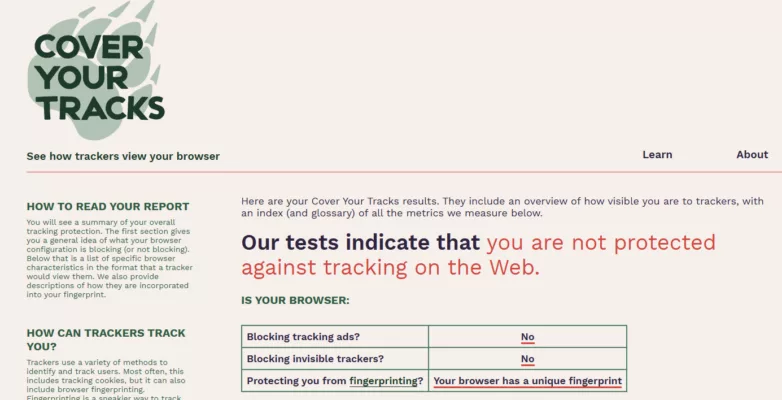
Weak Signals Observed
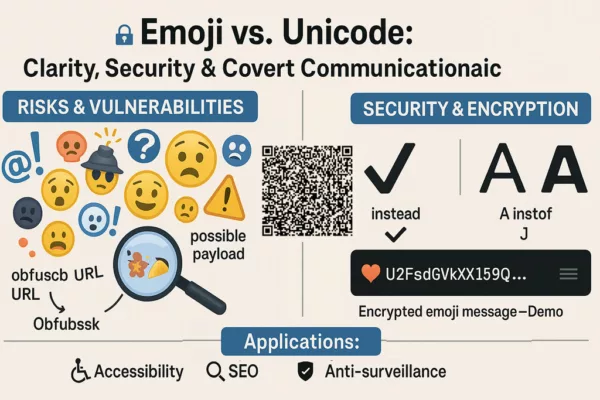
- Steganographic payloads embedded inside DNG/RAW media targeting mobile parsers.
- QR-to-Web attack loops abusing trusted redirect wrappers.
- Growing demand for zero-days targeting messaging media-processing pipelines.
Legitimate Monitoring Tools and Misuse Risks
Some parental-control and monitoring applications may also be abused for covert surveillance or privacy violations. Examples include:
- mSpy
- FlexiSPY
- Spyera
- Hoverwatch
- KidsGuard
While some uses may be legitimate under legal supervision frameworks, these ecosystems increasingly intersect with spyware, credential theft and covert runtime surveillance practices.
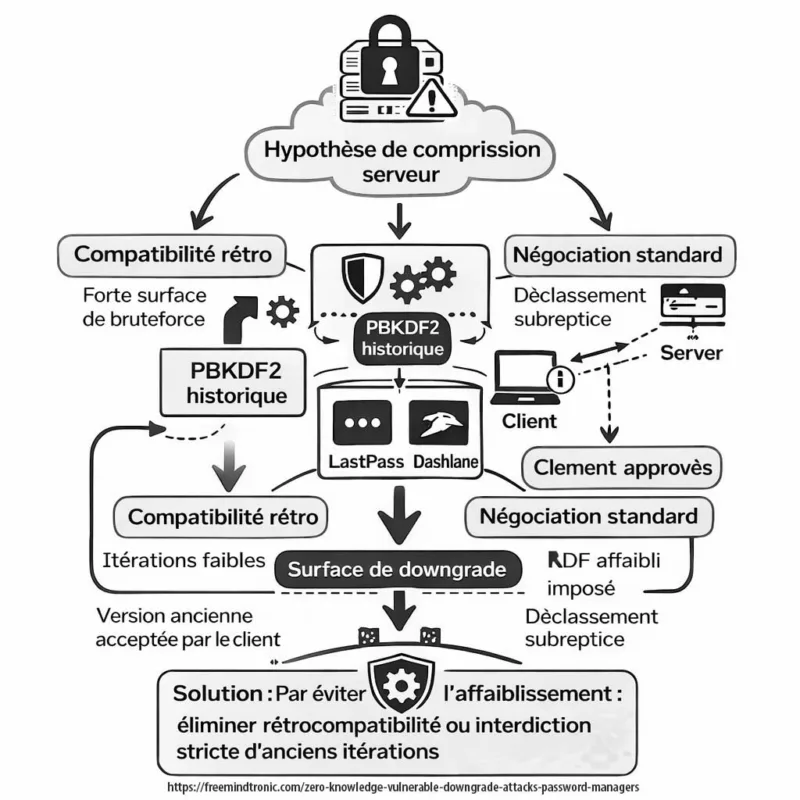
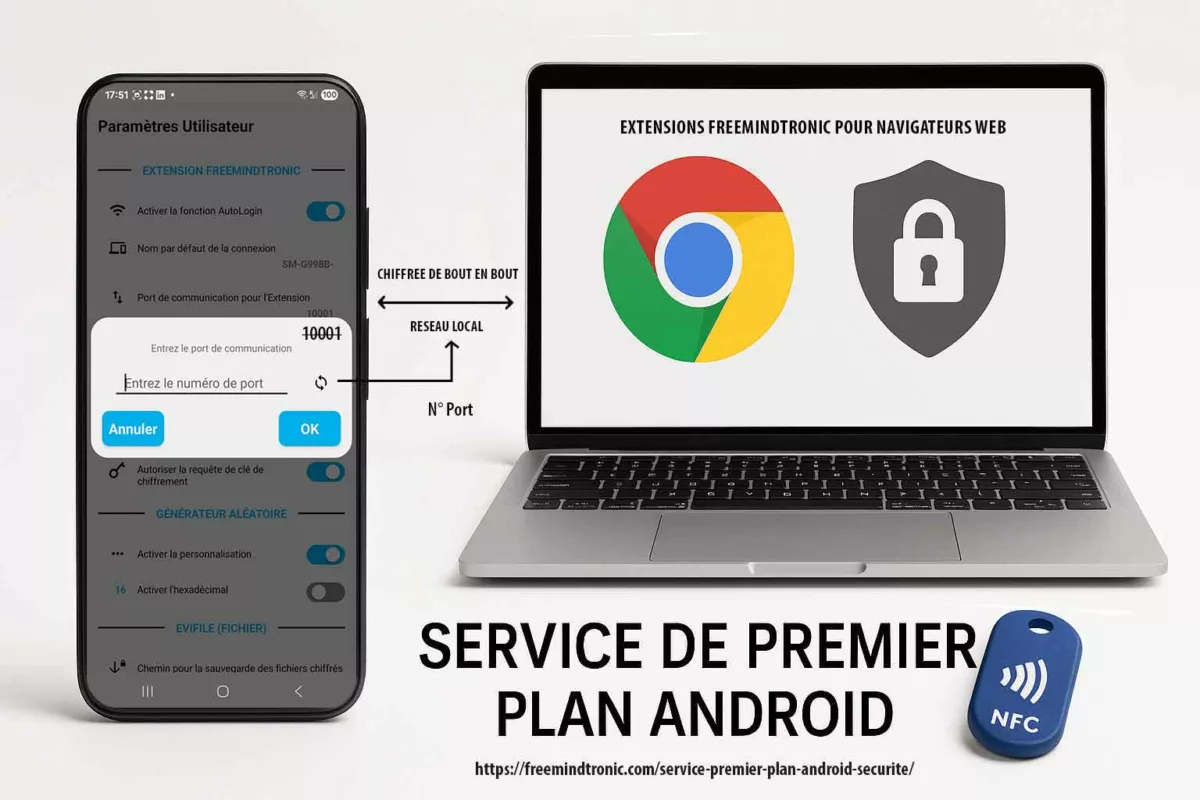
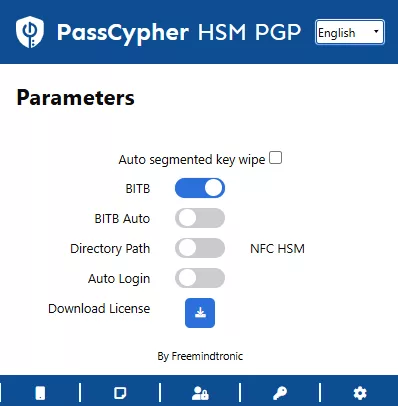
Sovereign Countermeasures — CryptPeer & EviSKMS
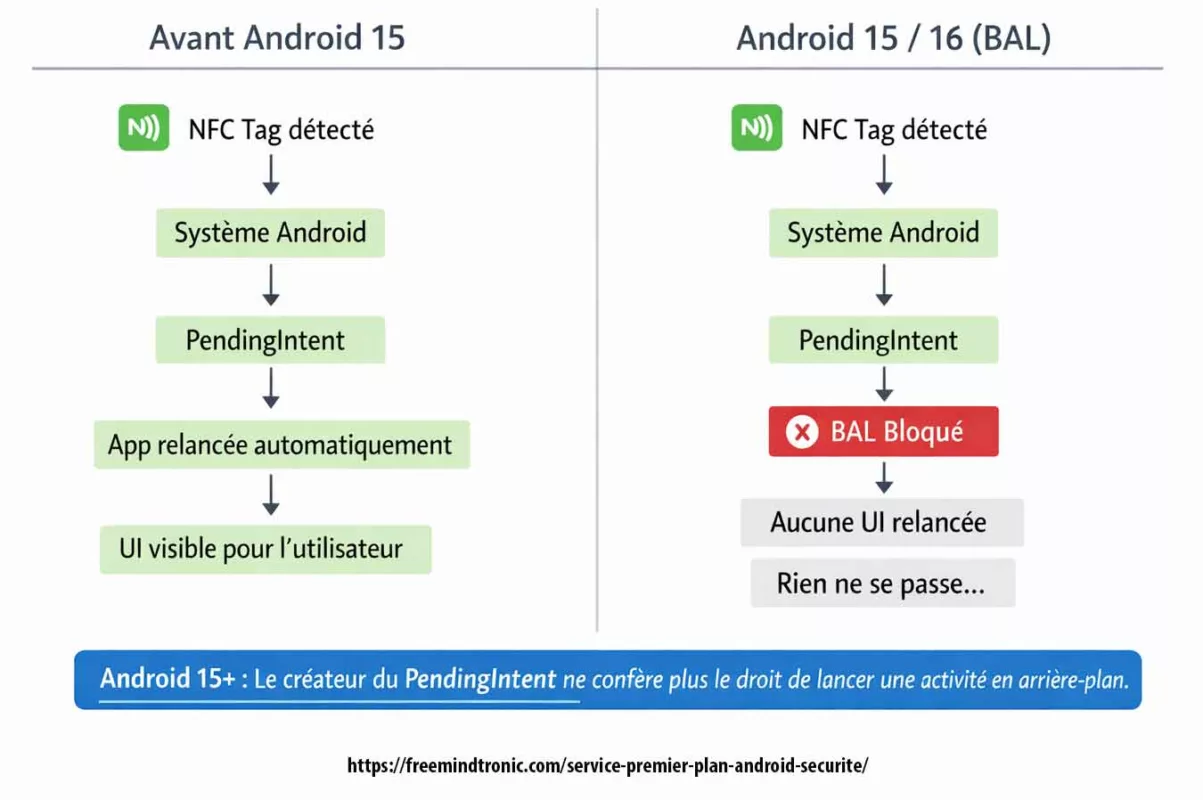
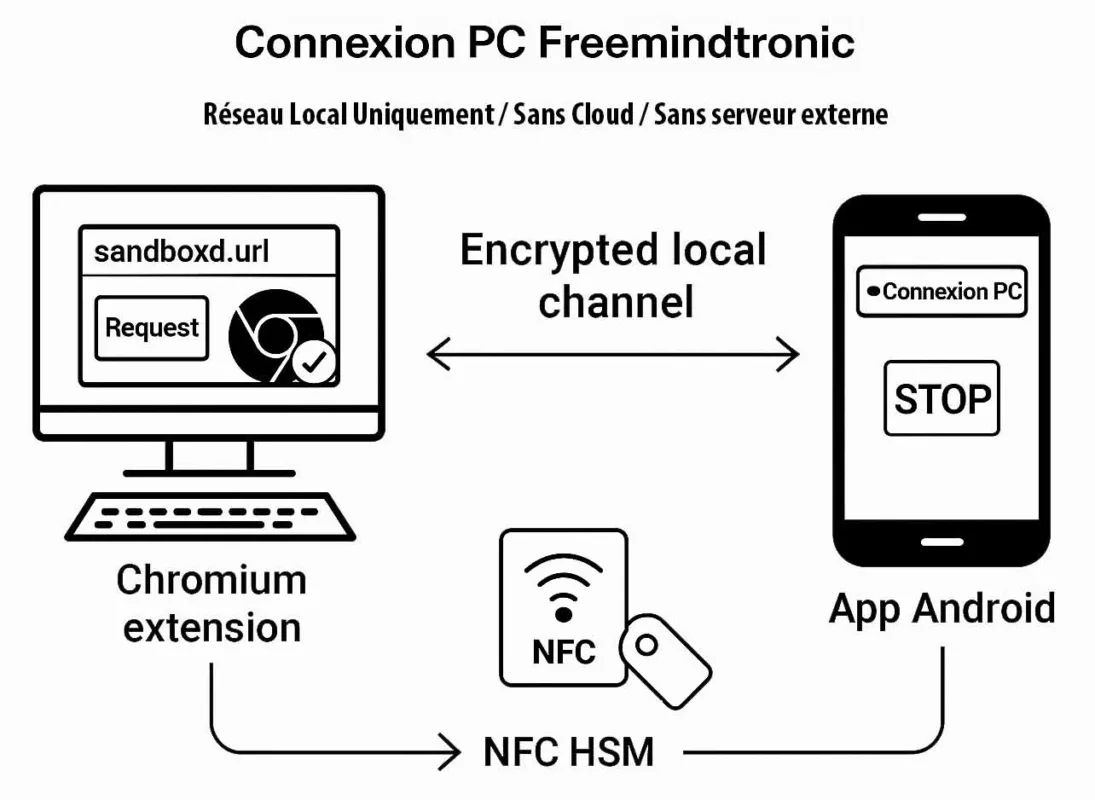
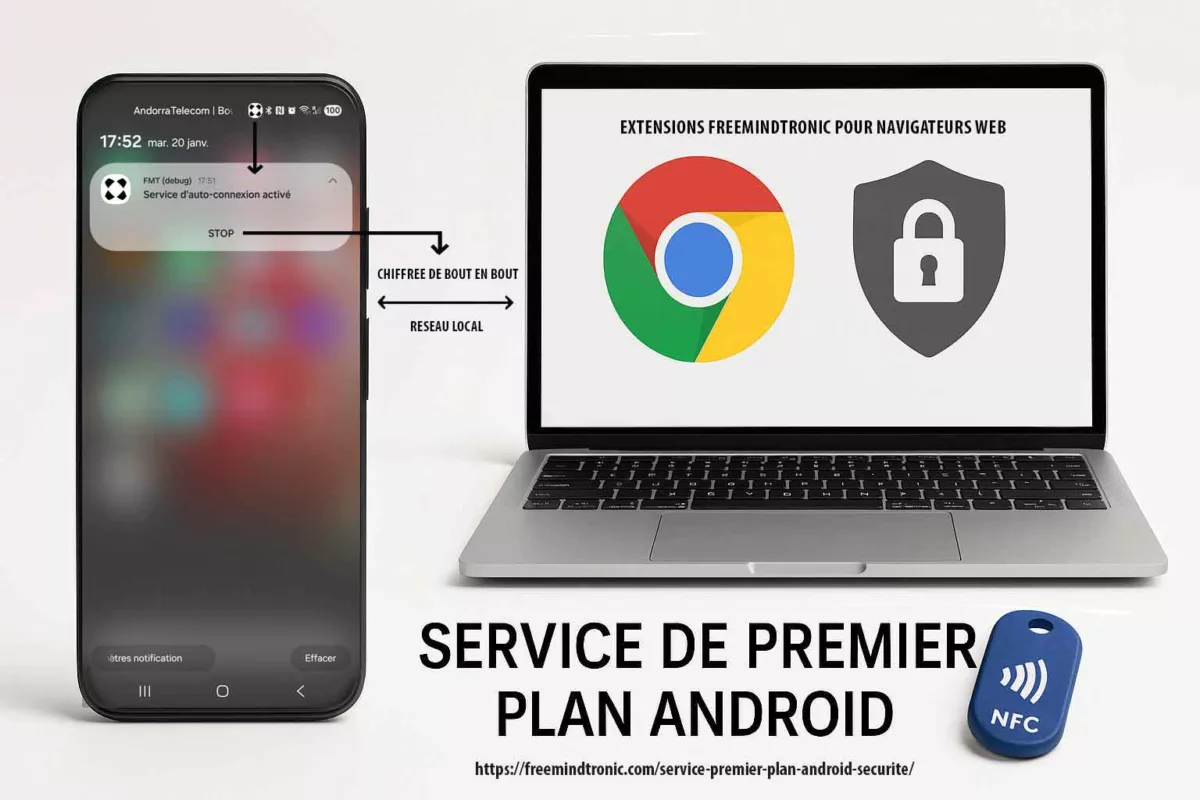
The WhatsApp zero-click vulnerability demonstrates why traditional application-layer E2EE is no longer sufficient against modern runtime compromise attacks. Traditional E2EE messaging platforms primarily secure communications during transport. However, once the runtime, operating system or application becomes compromised, already decrypted information may remain accessible through memory, caches or synchronization services.
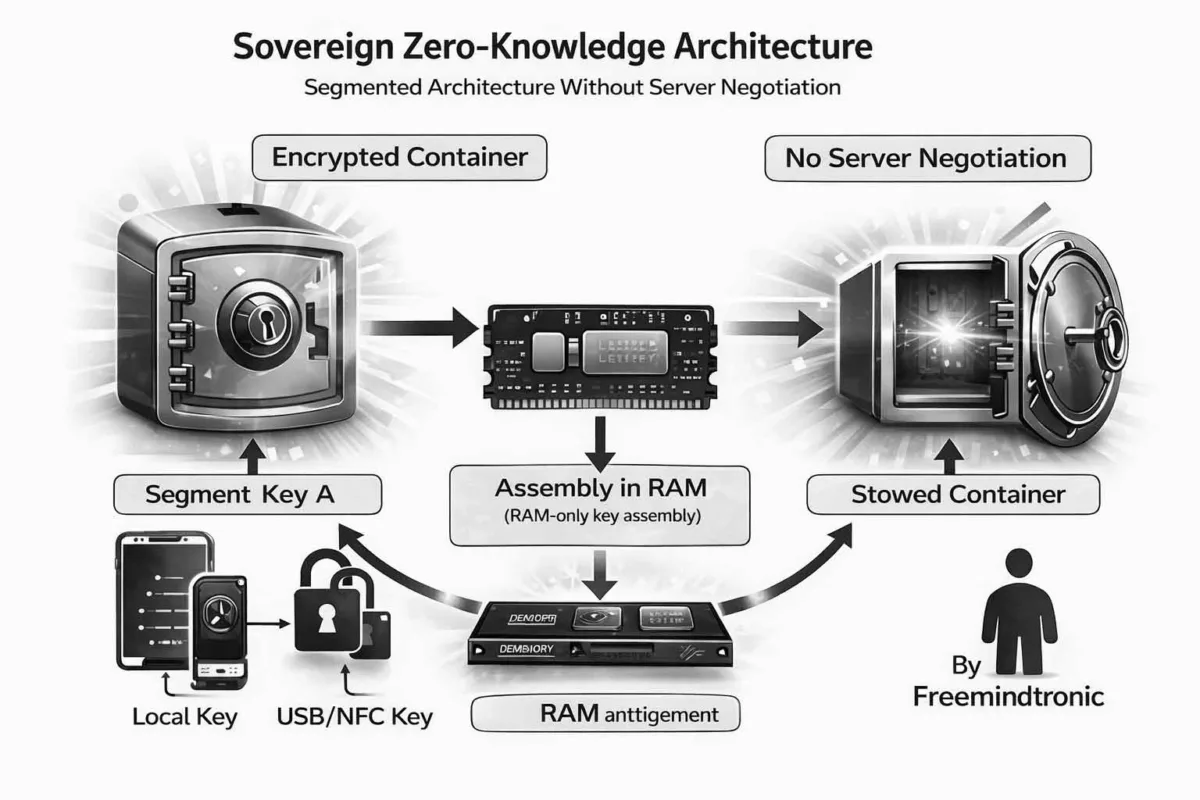
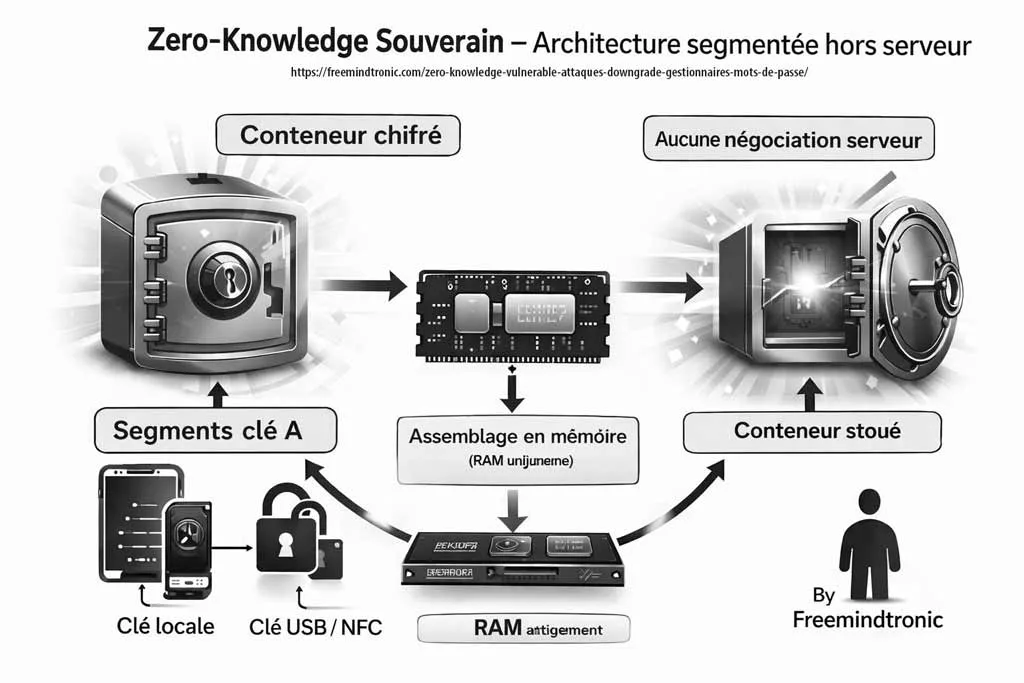
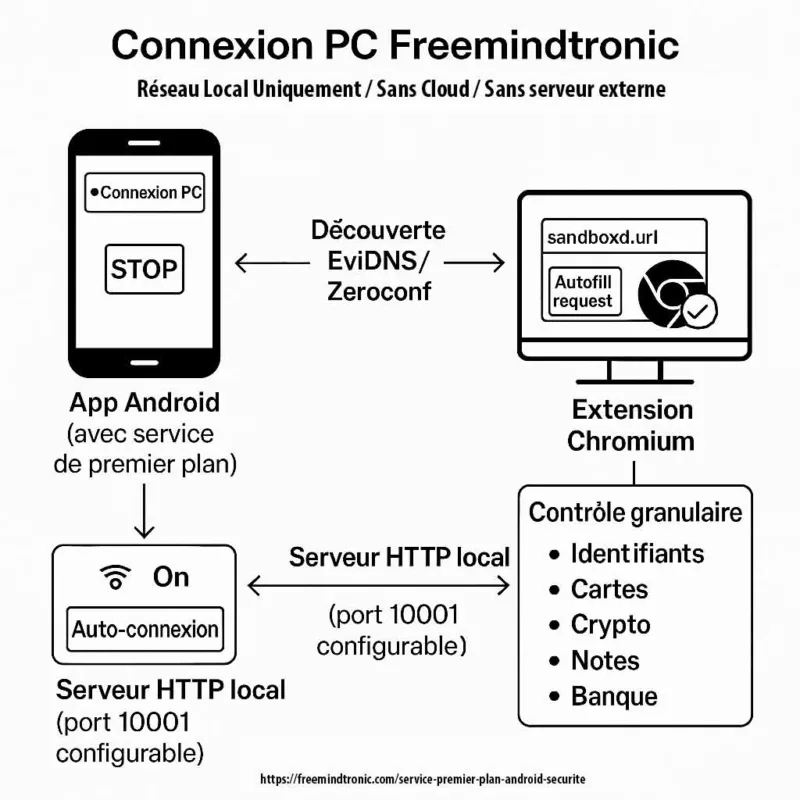
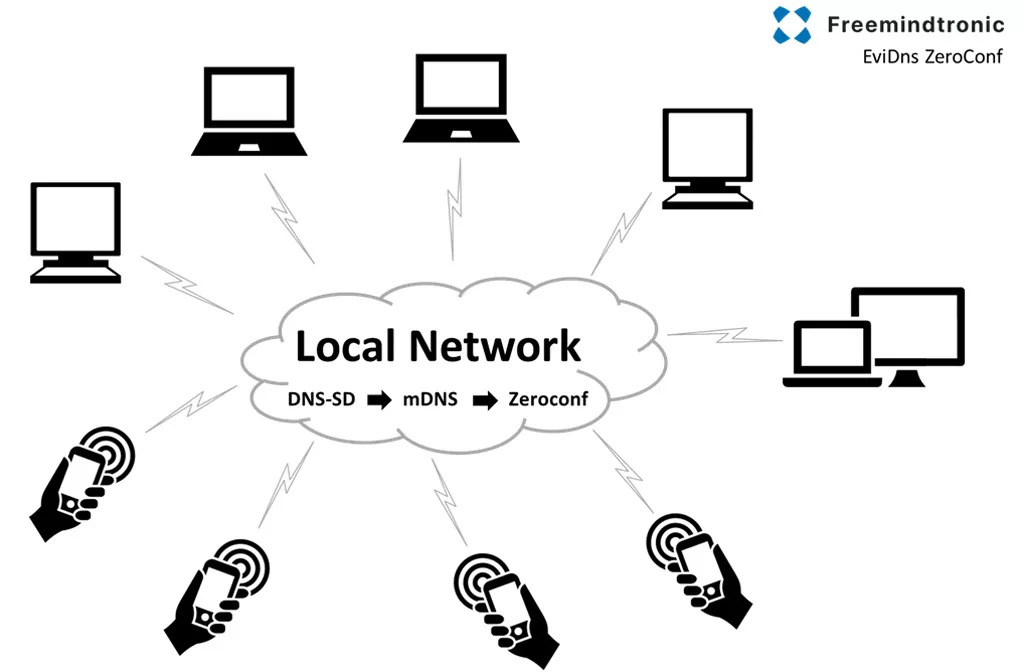
Why Zero-DOM Architectures Are Becoming Necessary
Zero-DOM architectures are not designed to replace traditional E2EE, but to address one of its fundamental limitations: once information has already been decrypted inside a compromised runtime, it may remain exploitable. The objective therefore shifts from protecting transport confidentiality alone toward materially limiting post-decryption exposure. CryptPeer/EviSKMS adopts a fundamentally different security model. Critical secrets never depend on a single software context. Keys are segmented, isolated and contextually validated through Zero-DOM architectures and NFC HSM infrastructures. Reconstruction only exists ephemerally in RAM without persistent exploitable storage. This architecture significantly reduces exposure to runtime compromise, memory exfiltration, linked-device abuse, post-decryption attacks and mobile spyware persistence.
Even in the event of browser-side arbitrary code execution, zero-click compromise or encrypted blob exfiltration, attackers cannot reconstruct or operationally exploit secrets without sovereign hardware proof provided by the HSM environment.
Recent WhatsApp Vulnerabilities Related to Runtime Exposure
CVE-2025-55179
WhatsApp also patched CVE-2025-55179 affecting WhatsApp for iOS, WhatsApp Business for iOS and WhatsApp for Mac.
This vulnerability involved incomplete validation of rich response messages, potentially allowing arbitrary remote media processing through attacker-controlled URLs.
While Meta reported no active exploitation, the flaw remains strategically linked to:
- runtime exposure;
- automatic media processing;
- linked-device synchronization abuse.
CVE-2025-30401 — WhatsApp for Windows
WhatsApp also patched a spoofing vulnerability affecting WhatsApp for Windows.
An inconsistency between displayed MIME type and actual file handling behavior could lead users to execute arbitrary code disguised as benign content.
Even though this was not a pure zero-click attack, it further illustrates the growing risks associated with excessive trust in runtime content-processing mechanisms.
FAQ — WhatsApp Zero-Click Vulnerability
Yes. The attack chain abuses linked-device synchronization and automatic media parsing to trigger malicious processing without user interaction.
No. E2EE mainly protects communications during transport. Once the runtime itself becomes compromised, already decrypted information may become exposed.
For high-risk profiles and sensitive environments, temporarily disabling linked devices is strongly recommended.
Post-decryption security refers to the protection of sensitive information after it has already been decrypted inside a runtime environment.
Zero-DOM is a sovereign runtime security architecture designed to isolate secrets from browser DOMs, persistent application memory and cloud telemetry surfaces.
Strategic Doctrine
“The future of cybersecurity no longer depends exclusively on encrypted transport, but on preventing secret exploitation after decryption.”
Strategic Outlook — Toward Sovereign Runtime Security
The WhatsApp zero-click vulnerability illustrates a major transformation in cybersecurity doctrine. Modern attacks no longer primarily seek to break encryption itself. They increasingly target the runtime environments capable of manipulating already decrypted information. This evolution marks the emergence of post-decryption cybersecurity. Application memory, synchronization layers, temporary buffers and runtime processing pipelines have become critical exposure surfaces. Protecting only the transport channel is no longer sufficient. Security architectures must now survive partial runtime compromise.
Toward Sovereign E2EE and Post-Decryption Cybersecurity
The future of secure communications no longer depends exclusively on transport confidentiality, but on the ability to prevent secret exploitation after decryption. CryptPeer/EviSKMS addresses this shift through:
- segmented key infrastructures;
- Zero-DOM isolation;
- contextual hardware validation;
- ephemeral RAM-only decryption;
- distributed sovereign runtime trust.
Further Reading — Sovereign Runtime Trust Doctrine
The future of cybersecurity no longer relies solely on encrypting communications, but on preserving sovereign control over the runtime environment manipulating critical secrets.