La Russie bloque WhatsApp par étapes et menace désormais de « bloquer complètement » la messagerie, accusée de servir à organiser des actes terroristes, des sabotages et des fraudes massives. Derrière cette offensive, il ne s’agit pas seulement d’un conflit juridique entre Roskomnadzor et Meta : Moscou cherche à remplacer une messagerie globale chiffrée par un écosystème domestique intégralement surveillable, centré sur la superapp Max et l’architecture de l’Internet souverain russe.
Résumé express — Ce qu’il faut retenir de « Russie bloque WhatsApp
Lecture rapide ≈ 4 min — Le régulateur russe Roskomnadzor a déclaré qu’il pourrait aller jusqu’à un blocage complet de WhatsApp si la messagerie ne se conforme pas aux lois russes de lutte contre la criminalité, le terrorisme et l’« extrémisme ».
Contexte — De la tolérance à la rupture programmée
Pendant des années, Moscou a toléré WhatsApp malgré la classification de Meta (Facebook, Instagram) comme « organisation extrémiste ». L’application était devenue indispensable aux communications quotidiennes de dizaines de millions de Russes. Cependant, à mesure que l’Internet souverain russe se met en place, ce compromis devient de moins en moins tenable. Le blocage progressif des appels, puis la menace de blocage total, marquent le passage à une incompatibilité assumée entre chiffrement de bout en bout global et exigences de surveillance russes.
Fondement — Un droit pensé pour l’accès aux communications
En parallèle, la loi de localisation des données, le paquet Iarovaïa et la loi sur l’Internet souverain imposent que les opérateurs et les services de messagerie soient capables de remettre contenus, métadonnées et moyens de déchiffrement aux services de sécurité. Or, par conception, WhatsApp ne peut pas déchiffrer les messages de ses utilisateurs. Pour être « conforme » au droit russe, l’application devrait affaiblir son modèle de sécurité (backdoor, scanning côté client) ou accepter de quitter de facto le marché russe.
Principe — Remplacer WhatsApp par la superapp Max
Dans le même temps, la Russie pousse une alternative nationale, Max, développée par VK et présentée comme la messagerie nationale. Max ne propose pas de chiffrement de bout en bout vérifiable. Elle est conçue comme une superapp intégrant messagerie, paiements et e-administration.
Plus Moscou rend l’usage de WhatsApp difficile et risqué, plus elle pousse les Russes vers Max, où les services de sécurité disposent d’une visibilité maximale sur les flux.
Enjeu souverain — Du terrorisme au contrôle social
Officiellement, WhatsApp serait un vecteur majeur de fraude, de sabotage et de terrorisme. Pourtant, les données russes montrent que les appels téléphoniques classiques restent le canal principal de fraude. Surtout, dans un système où l’« extrémisme » englobe l’opposition, les ONG et le mouvement LGBT, exiger de WhatsApp qu’elle « exclue les activités criminelles » revient à réclamer une police politique intégrée à la messagerie. Ainsi, la séquence « Russie menace de bloquer complètement WhatsApp » devient le révélateur d’un choix stratégique : remplacer les services globaux chiffrés par des solutions nationales contrôlées, et redéfinir la souveraineté numérique autour de la surveillance plutôt que du chiffrement.
Paramètres de lecture
Résumé express : ≈ 4 min
Analyse centrale : ≈ 10–12 min
Chronique complète : ≈ 25–30 min
Date de publication : 2025-11-29
Dernière mise à jour : 2025-11-29
Niveau de complexité : Souverain & Géopolitique
Densité technique : ≈ 70 %
Langues disponibles : FR · EN
Focal thématique : Russie bloque WhatsApp, Roskomnadzor, Max, Internet souverain, chiffrement E2E
Type éditorial : Chronique — Freemindtronic Cyberculture Series
Niveau d’enjeu : 8.4 / 10 — souveraineté & communications chiffrées
Sommaire
- Résumé express — Ce qu’il faut retenir
- Contexte — De Meta « extrémiste » à la menace de blocage total
- Cadre juridique — Localisation, Iarovaïa et Internet souverain
- WhatsApp — Chiffrement de bout en bout et impasse technique
- Escalade programmée — Telegram, Meta, puis WhatsApp
- Max — Superapp domestique et remplacement de WhatsApp
- Fraude, terrorisme, extrémisme — Narratif officiel vs réalité
- Roskomnadzor — Pivot technique et politique du Runet
- Scénarios prospectifs — Vers quel Internet russe ?
- Signaux faibles — Balkanisation et superapps de contrôle
- Cas d’usage souverain — Messagerie hors juridiction
- À relier avec… (Cyberculture & Tech Fixes)
- FAQ — Russie bloque WhatsApp, Max et Internet souverain
- Ce que nous n’avons pas couvert
- Sources officielles et références
Points saillants — Lignes de force
- La séquence « Russie bloque WhatsApp » est l’aboutissement d’une stratégie graduelle : lois Iarovaïa, Internet souverain, mise au ban de Meta, puis pression sur les messageries chiffrées.
- La Russie reproche moins à WhatsApp de ne pas filtrer la criminalité que de ne pas être structurellement compatible avec une surveillance étatique intégrale.
- La superapp Max joue le rôle de remplacement domestique de WhatsApp, sans chiffrement de bout en bout vérifiable, intégrée aux paiements et à l’e-administration, sous le regard du FSB.
- Les chiffres officiels de fraude montrent que les appels téléphoniques classiques restent le vecteur principal, ce qui relativise le narratif centré sur WhatsApp comme problème numéro un.
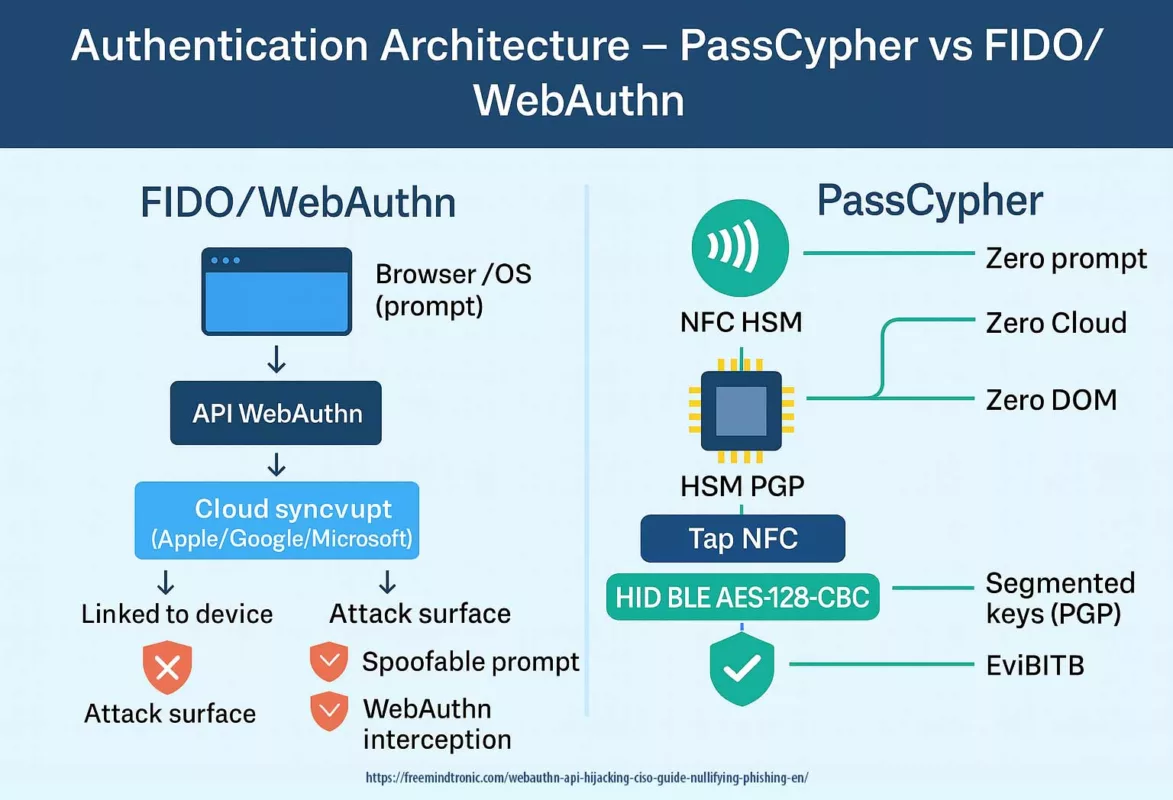
- Les architectures sans clé de déchiffrement côté serveur — HSM locaux hors serveur (DataShielder NFC HSM, DataShielder HSM PGP) et serveur relais auto-hébergeable sans clé (CryptPeer) — offrent une alternative où aucun État ne peut exiger une backdoor centrale exploitable.
Contexte — De Meta « extrémiste » à la menace de blocage total de WhatsApp
En 2025, le blocage des appels et le durcissement de l’Internet souverain changent l’équation.
Roskomnadzor évoque désormais la possibilité d’un blocage complet de WhatsApp.
Cette évolution ne relève pas du hasard.
Elle clôt une phase de tolérance contrainte et ouvre une phase de rupture programmée.
2022 — Meta classée « extrémiste », WhatsApp épargnée
En mars 2022, au début de l’invasion de l’Ukraine, un tribunal russe déclare Meta « organisation extrémiste ».
Facebook et Instagram sont alors bloqués en Russie.
Pourtant, un point attire immédiatement l’attention : la décision précise qu’elle ne s’applique pas à WhatsApp.
L’application reste la principale messagerie du groupe Meta en Russie.
Une messagerie devenue centrale dans la vie quotidienne
À ce moment-là, WhatsApp est omniprésente dans la société russe.
Elle sert aux familles, aux petites entreprises et aux administrations locales.
Écoles, universités et certains services publics l’utilisent aussi pour coordonner l’information courante.
Bloquer brutalement la messagerie provoquerait une rupture massive dans le quotidien de millions de personnes.
À ce stade, aucune alternative nationale crédible n’est encore prête à prendre pleinement le relais.
Montée en puissance de l’Internet souverain russe
Progressivement, cependant, le contexte technique et politique change.
D’une part, l’architecture de l’Internet souverain russe se met en place.
Les opérateurs déploient des équipements de Deep Packet Inspection et des capacités de routage centralisé.
Ils mettent aussi en place des mécanismes techniques permettant d’isoler le Runet du reste de l’Internet.
D’autre part, le discours politique se durcit autour de la « guerre de l’information ».
Les autorités invoquent l’« extrémisme » et la lutte contre des plateformes étrangères jugées hostiles.
2025 — Du blocage des appels à la menace de coupure
Le 13 août 2025, la Russie franchit un seuil dans cette stratégie graduelle.
Les appels audio et vidéo sur WhatsApp et Telegram sont bloqués.
Officiellement, la mesure vise la lutte contre la fraude et le terrorisme.
Les messages textuels restent possibles, mais l’usage est déjà dégradé dans de nombreuses régions.
Trois mois plus tard, Roskomnadzor évoque publiquement la possibilité d’un blocage complet de WhatsApp.
Le régulateur explique que la messagerie doit se conformer au droit russe ou accepter ce scénario.
Un tournant politique plus qu’un simple incident technique
Autrement dit, la formule « Russie bloque WhatsApp » ne relève plus d’un simple scénario prospectif.
Elle décrit désormais un horizon politique assumé par les autorités russes.
Dans ce contexte, il devient nécessaire d’examiner le socle juridique qui rend ce scénario plausible.
Ce socle éclaire aussi la logique profonde de la confrontation avec WhatsApp.
Il permet de comprendre la trajectoire choisie par le pouvoir russe.
Cadre juridique — Localisation des données, loi Iarovaïa et Internet souverain
Pour comprendre pourquoi la Russie peut menacer de blocage complet de WhatsApp, il faut maintenant examiner l’architecture juridique construite depuis une décennie. Celle-ci repose sur trois piliers complémentaires.
Localisation des données — Garder les PII « à portée de main »
Tout d’abord, la loi de localisation des données impose que les données personnelles de citoyens russes soient stockées sur des serveurs situés en Russie. Un service qui refuse de localiser ses données s’expose à des amendes, voire à un blocage total. Roskomnadzor tient la liste des contrevenants et orchestre les sanctions techniques.
Pour une messagerie globale comme WhatsApp, cette exigence est déjà problématique. Son infrastructure est répartie, mutualisée, conçue pour un Internet sans frontières nettes. Forcer une stricte segmentation « données russes / données non russes » revient à remettre en cause le modèle même de la plateforme.
Paquet Iarovaïa — Stockage massif et obligation de déchiffrement
Ensuite, le paquet Iarovaïa, voté en 2016, va beaucoup plus loin. Il impose aux opérateurs et aux « organisateurs de diffusion d’information » de :
- stocker le contenu des communications pendant plusieurs mois,
- conserver les métadonnées pendant une période plus longue encore,
- et surtout, fournir aux services de sécurité les moyens de déchiffrer les communications, y compris la remise des clés de chiffrement.
En clair, une messagerie utilisée massivement en Russie doit être capable, au moins en théorie, de remettre le contenu des conversations en clair aux autorités qui en font la demande. Cette exigence n’est pas compatible, par construction, avec un chiffrement de bout en bout où le fournisseur ne détient aucune clé de déchiffrement.
Internet souverain — DPI et contrôle central du Runet
Enfin, la loi sur l’Internet souverain complète le dispositif :
- les fournisseurs d’accès doivent installer des équipements de Deep Packet Inspection (DPI) contrôlés par Roskomnadzor ;
- l’État peut rediriger, filtrer, ralentir ou couper des services ciblés ;
- le segment russe de l’Internet (Runet) peut être isolé du reste du réseau mondial en cas de crise ou de décision politique.
Ainsi, ce triptyque (« localisation des données », « Iarovaïa », « Internet souverain ») converge vers un modèle où, sur le papier, aucun service de communication de masse ne devrait être hors de portée : ni du point de vue de l’hébergement, ni du point de vue du chiffrement, ni du point de vue de l’acheminement réseau.
Dans un tel univers normatif, une messagerie globale chiffrée de bout en bout comme WhatsApp devient une anomalie juridique et technique. Cette anomalie explique en grande partie pourquoi la séquence « Russie bloque WhatsApp » n’est pas une simple crise d’humeur, mais l’expression d’un conflit structurel entre deux philosophies du chiffrement.
WhatsApp — Chiffrement de bout en bout et impasse technique pour le FSB
Meta ne peut pas déchiffrer leur contenu, même si l’État le demande.
Pour devenir « conforme » aux lois russes, la messagerie devrait renoncer à son modèle de sécurité.
Elle devrait accepter un affaiblissement majeur ou quitter purement et simplement le marché russe.
C’est le cœur de la tension derrière l’expression « Russie bloque WhatsApp ».
Un modèle technique fondé sur le chiffrement de bout en bout
D’abord, une fois ce cadre juridique posé, il faut revenir au modèle technique de WhatsApp.
La messagerie repose sur un chiffrement de bout en bout (E2E).
Concrètement :
- les messages sont chiffrés sur le terminal de l’expéditeur ;
- ils ne peuvent être déchiffrés que sur le terminal du destinataire ;
- Meta n’a pas accès au contenu en clair, seulement aux métadonnées.
Une demande russe incompatible avec la conception de WhatsApp
Ensuite, il faut confronter ce modèle aux exigences des lois russes.
Dans un tel modèle, les lois russes exigent la remise des clés ou du contenu en clair.
Une telle demande est techniquement impossible sans modifier la conception même du service.
La tension ne vient donc pas d’un simple refus politique.
Elle résulte surtout d’une incompatibilité de design entre messagerie et cadre légal russe.
Trois issues théoriques pour WhatsApp en Russie
Pour se mettre en conformité avec la Russie, WhatsApp n’a que trois options théoriques :
- Introduire une backdoor ou de l’analyse côté client : scanner les messages sur le téléphone avant chiffrement.
Le système détecterait certains contenus ou comportements interdits et enverrait des rapports aux autorités. - Abandonner le chiffrement de bout en bout pour tout ou partie des utilisateurs russes.
Le serveur pourrait alors lire les messages et les remettre aux services de sécurité. - Refuser et accepter un blocage complet, avec un service réduit à une application de niche.
Dans ce cas, WhatsApp resterait accessible surtout via VPN et autres contournements techniques.
Deux modèles irréconciliables de souveraineté sur les communications
Pour l’instant, Meta continue de défendre publiquement le chiffrement E2E.
Selon l’entreprise, ce chiffrement reste indispensable à la protection des communications privées.
Dès lors, la formule « Russie bloque WhatsApp » décrit moins une simple provocation.
Elle marque surtout un point de collision entre deux modèles de sécurité des communications.
Le premier modèle pense le chiffrement comme une protection forte contre tous les États.
Le second modèle refuse qu’un service de masse puisse échapper à la surveillance étatique.
À partir de là, il devient nécessaire de replacer cette impasse dans une chronologie claire.
Cette chronologie retrace les principales tentatives russes de contrôle des messageries chiffrées.
Escalade programmée — Telegram, Meta, puis WhatsApp
Pour mesurer la portée de la menace actuelle, il faut remonter le fil des épisodes précédents.
Tentative de blocage de Telegram (2018–2020)
En 2018, la Russie tente de bloquer Telegram pour refus de fournir les clés de chiffrement. Roskomnadzor bloque des millions d’adresses IP, y compris celles d’Amazon et de Google. Les dégâts collatéraux sont considérables. Malgré tout, Telegram reste largement accessible via des contournements. En 2020, le régulateur renonce officiellement au blocage.
Cette tentative ratée montre deux choses. D’abord, sans Internet souverain pleinement opérationnel, bloquer une messagerie populaire est techniquement difficile et politiquement coûteux. Ensuite, la simple pression réglementaire ne suffit pas si l’État ne dispose pas d’une alternative crédible à proposer.
Meta « extrémiste », WhatsApp tolérée (2022)
En 2022, la Russie franchit un nouveau cap en classant Meta comme « organisation extrémiste ». Facebook et Instagram sont bloqués. Cependant, la décision précise que l’interdiction ne concerne pas WhatsApp. Ce choix traduit une forme de réalisme pragmatique : frapper les réseaux sociaux considérés comme politisés, tout en ménageant la messagerie utilisée par la population.
Internet souverain, durcissement légal et blocage des appels (2024–2025)
Entre 2024 et 2025, la situation évolue à nouveau. Les équipements de DPI sont généralisés, la notion d’« extrémisme » s’étend, et de nouvelles dispositions pénalisent déjà la recherche en ligne de contenus qualifiés d’« extrémistes », tandis qu’un projet de loi vise explicitement les accès à ces contenus via des VPN.
Le 13 août 2025, Roskomnadzor annonce des restrictions ciblées sur les appels audio et vidéo via WhatsApp et Telegram. Officiellement, il s’agit d’une mesure « anti-fraude » et « anti-terroriste ». Dans la pratique, la qualité des communications vocales se dégrade au point de devenir inutilisable dans de nombreuses régions.
Quelques mois plus tard, la menace de blocage complet de WhatsApp en Russie est brandie publiquement. Ainsi, la séquence « Russie bloque WhatsApp » ne tombe pas du ciel : elle prolonge une escalade graduelle, techniquement préparée et politiquement assumée.
Cette escalade n’a de sens que parce qu’une alternative domestique a été préparée en parallèle : la superapp Max, appelée à remplacer WhatsApp dans l’écosystème de l’Internet souverain russe.
Max — Superapp domestique et remplacement de WhatsApp
C’est une superapp qui agrège chat, paiements, e-administration et identité numérique.
Elle ne propose pas de chiffrement de bout en bout vérifiable.
Elle se place comme remplaçante « souveraine » de WhatsApp dans un Runet de plus en plus fermé.
Une superapp « tout-en-un » au cœur du Runet
Au moment où la Russie durcit le ton contre WhatsApp, une autre pièce essentielle est déjà en place.
Il s’agit de la superapp Max, développée par le groupe VK et promue comme « messenger national ».
Concrètement, Max se présente comme une application « tout-en-un » :
- messagerie individuelle et de groupe ;
- paiements, portefeuille numérique et transferts ;
- accès à certains services administratifs (Gosuslugi) ;
- intégration annoncée avec l’identité numérique et la signature électronique.
Un chiffrement limité et compatible avec l’Internet souverain
Par ailleurs, deux caractéristiques pèsent lourd dans la balance.
La première concerne le chiffrement.
Max ne propose pas de chiffrement de bout en bout vérifiable.
Les informations publiques et les analyses indépendantes indiquent que les échanges sont au mieux chiffrés en transit.
Ils restent toutefois lisibles par l’opérateur.
Ils demeurent aussi accessibles aux autorités sur demande.
Cette conception rend la superapp structurellement compatible avec les exigences de l’Internet souverain russe.
Préinstallation obligatoire et dépendance progressive
La deuxième caractéristique tient à son mode de diffusion.
À partir du 1er septembre 2025, la préinstallation de Max devient obligatoire sur tous les smartphones et tablettes vendus en Russie.
Dans le même temps, certaines administrations imposent déjà son usage.
Elles l’utilisent pour les communications avec les parents, les écoles ou les services publics.
Progressivement, Max devient donc un passage obligé de la vie quotidienne numérique.
De WhatsApp à Max : une stratégie assumée de substitution
Dans ce contexte, la formule « Russie bloque WhatsApp » ne décrit pas un simple blocage punitif.
Elle s’inscrit plutôt dans une stratégie de substitution.
En pratique, plus WhatsApp est pénible ou risqué à utiliser, plus Max s’impose.
Elle devient le point de passage obligé pour communiquer, payer et interagir avec l’État.
Le blocage potentiel de WhatsApp et l’essor de Max se renforcent ainsi mutuellement.
Cette dynamique oblige à s’interroger sur le narratif invoqué par Moscou pour justifier cette bascule : fraude, terrorisme, extrémisme.
Il convient donc d’examiner ce discours plus en détail dans la section suivante.
Ce sera la clé pour comprendre comment la séquence « Russie bloque WhatsApp » sert aussi un projet plus large de contrôle social.
Fraude, terrorisme, extrémisme — Narratif officiel vs réalité
Pourtant, les chiffres officiels montrent que les appels téléphoniques classiques restent le premier vecteur de fraude.
Surtout, la définition russe de ce qui est « criminel » est extrêmement large.
Elle inclut l’opposition, les ONG et le mouvement LGBT.
Un récit officiel centré sur la fraude et le terrorisme
Dans ses communiqués, Roskomnadzor affirme que WhatsApp et Telegram sont devenus des outils centraux.
Selon le régulateur, ces messageries serviraient notamment à :
- fraudes de masse et escroqueries financières ;
- recrutement pour le terrorisme et le sabotage ;
- coordination d’actions criminelles et d’« extrémisme ».
À première vue, l’argumentaire semble cohérent avec une logique de sécurité publique.
En réalité, les données officielles dessinent un paysage beaucoup plus nuancé.
Les chiffres de la Banque de Russie racontent une autre histoire
Les rapports de la Banque centrale de Russie dressent un constat différent.
Ils indiquent que :
- les appels téléphoniques classiques demeurent le canal principal de fraude ;
- les messageries chiffrées ne constituent qu’un vecteur parmi d’autres ;
- le blocage des appels sur WhatsApp et Telegram a surtout entraîné une reprise du trafic voix traditionnel, sans faire disparaître la fraude elle-même.
Autrement dit, la dimension « fraude » sert autant de narratif de légitimation que de justification technique.
Ce décalage ouvre sur un second glissement, plus politique encore.
Une définition extensible de ce qui est « criminel »
En parallèle, la référence permanente aux « activités criminelles » et à l’« extrémisme » joue un rôle structurant.
En 2025, ces catégories incluent en Russie :
- les structures liées à Alexeï Navalny, qualifiées d’« extrémistes » puis de « terroristes » ;
- le mouvement LGBT international, classé comme organisation extrémiste ;
- de nombreuses ONG, médias indépendants et organisations de défense des droits ;
- des formes d’expression anti-guerre ou critiques de l’armée.
Progressivement, la frontière entre criminalité réelle et dissidence politique devient floue.
Le vocabulaire pénal sert alors à encadrer l’espace public et non plus seulement à poursuivre des infractions.
De la lutte contre la fraude à la police politique embarquée
Dans ce cadre, exiger que WhatsApp « exclue les activités criminelles » signifie, concrètement, plusieurs choses.
Il s’agit de :
- censurer proactivement les conversations sur ces sujets ;
- identifier les personnes qui participent à ces échanges ;
- et orienter les données vers les services compétents.
Or, une messagerie chiffrée de bout en bout ne peut pas réaliser ce programme sans renoncer à son modèle de sécurité.
Introduire ces fonctions reviendrait à transformer l’application en outil de surveillance politique.
C’est précisément ce qui fait de la séquence « Russie menace de bloquer complètement WhatsApp » un révélateur.
L’État exige d’un outil global qu’il devienne une police politique embarquée, ce que WhatsApp ne peut ni ne veut être.
Ce constat renvoie directement au rôle pivot de Roskomnadzor.
L’organisme agit à la fois comme gendarme juridique, chef d’orchestre technique et narrateur officiel de cette confrontation.
Roskomnadzor — Pivot technique et politique du Runet
C’est le chef d’orchestre de l’Internet souverain russe.
Il gère la censure, pilote les équipements de DPI, supervise la localisation des données.
Il coordonne aussi la substitution progressive des services globaux par des solutions nationales.
Un régulateur au cœur de l’Internet souverain russe
Pour bien comprendre son rôle, il faut partir de ses fonctions opérationnelles.
Roskomnadzor cumule plusieurs responsabilités clés au sein de l’Internet souverain russe :
- il administre la liste noire des sites et services bloqués ;
- il contrôle l’application de la localisation des données ;
- il supervise le déploiement des équipements de DPI chez les FAI ;
- il coordonne les opérations de throttling ou de coupure de services étrangers (réseaux sociaux, VPN, plateformes vidéo, outils de mesure, etc.).
Autrement dit, il ne se contente pas d’édicter des règles.
Il orchestre aussi leur mise en œuvre technique sur l’infrastructure du Runet.
Un bras technique de la fermeture progressive du Runet
Dans le récit officiel, Roskomnadzor agit pour « protéger les citoyens ».
Il serait également chargé de garantir la « stabilité de l’infrastructure ».
Dans les faits, il est devenu le bras technique d’une politique de fermeture progressive du Runet.
À ce titre, ses communiqués sur WhatsApp ont une portée qui dépasse largement la messagerie elle-même.
Ils signalent l’orientation générale de la politique numérique russe.
La menace de blocage complet comme signal stratégique
La menace de blocage complet contre WhatsApp en est un bon exemple.
Elle s’inscrit dans un ensemble cohérent de signaux, parmi lesquels :
- pression sur les services étrangers jugés « non coopératifs » ;
- promotion active de la superapp Max comme alternative « patriotique » ;
- rappel régulier des obligations de partage de données, de localisation et de déchiffrement.
Ainsi, chaque prise de position de Roskomnadzor ne vise pas seulement une plateforme.
Elle contribue à redessiner le périmètre de ce qui est toléré ou non dans l’espace numérique russe.
Un triptyque qui redéfinit la liberté de communication
Le triptyque « Russie bloque WhatsApp », « Max comme superapp nationale », « Internet souverain » décrit, en creux, un nouveau modèle.
Dans ce modèle, la liberté de communication est conditionnée à la conformité au dispositif de surveillance.
Autrement dit, une messagerie de masse n’est légitime que si elle s’insère dans cette architecture de contrôle.
C’est ce modèle qu’il faut maintenant projeter dans l’avenir à travers plusieurs scénarios possibles.
Ces scénarios permettront d’évaluer jusqu’où peut aller la fermeture du Runet et la marginalisation des services globaux chiffrés.
Scénarios prospectifs — Vers quel Internet russe ?
À partir de la situation actuelle, plusieurs trajectoires réalistes peuvent être envisagées pour la relation entre la Russie, WhatsApp et l’Internet souverain.
Blocage progressif de facto
Premier scénario : il n’y a pas de « ban » brutal, mais une érosion continue de l’usage de WhatsApp.
- les appels restent durablement bloqués ;
- les pièces jointes sont ralenties ou intermittentes ;
- certains nouveaux comptes peinent à s’enregistrer ;
- le service est officiellement présenté comme « peu fiable » ou « dangereux ».
Dans ce cas, WhatsApp ne disparaît pas complètement du Runet, mais son usage se concentre sur :
- les utilisateurs les plus technophiles, capables de manier VPN et contournements ;
- les communications transfrontières, notamment avec la diaspora ou des partenaires étrangers.
Ainsi, « Russie bloque WhatsApp » devient une réalité de facto, sans nécessité d’un ban spectaculaire. Max, de son côté, gagne mécaniquement les usages de masse.
Accord opaque et surveillance côté terminal
Deuxième scénario : un compromis discret où WhatsApp resterait accessible, mais au prix d’un scanning côté client ou d’intégrations imposées.
Par exemple :
- analyse automatique de certains contenus sur le terminal avant chiffrement ;
- signalement obligatoire de pattern associés à l’« extrémisme » ou à la fraude ;
- journalisation renforcée des métadonnées au profit des autorités.
Cette trajectoire ne casserait pas formellement le chiffrement de bout en bout, mais elle en viderait une large part de sa substance : la sécurité dépendrait moins de la cryptographie que de l’intégrité des mécanismes de contrôle imposés par l’État russe.
Rupture assumée et blocage complet
Troisième scénario : Moscou assume une rupture totale avec WhatsApp.
- la messagerie est pleinement bloquée au niveau réseau ;
- l’usage via VPN est criminalisé ou assimilé à un comportement suspect ;
- Max devient la porte d’entrée quasi exclusive pour les communications quotidiennes, l’e-administration et une partie des paiements.
Dans cette configuration, le Runet ressemble de plus en plus à un intranet d’État : les flux sont filtrés, les services globaux remplacés par des équivalents locaux, et les rares poches de chiffrement réel sont reléguées à des niches à haut risque.
Quel que soit le scénario retenu, une question demeure : comment préserver une souveraineté du chiffrement lorsque l’infrastructure de messagerie est sous contrôle d’un État qui rejette l’idée même d’opacité ? C’est précisément là qu’entrent en jeu les architectures souveraines hors plateformes.
Signaux faibles — Balkanisation et superapps de contrôle
Bloc signaux faibles
1. Balkanisation accélérée de l’Internet — La trajectoire russe renforce l’image d’un Internet découpé en sphères (Russie, Chine, bloc occidental, etc.), chacune avec ses propres plateformes, clouds « souverains » et règles de surveillance. La séquence « Russie bloque WhatsApp » devient un cas d’école de cette balkanisation.
2. Superapps comme vecteurs de contrôle — Après WeChat en Chine, Max en Russie illustre un modèle où une seule application concentre messagerie, paiements, e-administration et identité. Plus la superapp est centrale, plus la surface de contrôle étatique est large.
3. Narratif sécuritaire permanent — Lutte contre la fraude, protection des enfants, anti-terrorisme : ces registres, légitimes en soi, deviennent des leviers rhétoriques pour remettre en cause le chiffrement de bout en bout et normaliser les backdoors.
4. Lignes de fracture autour du chiffrement — La question du chiffrement ne se limite plus aux régimes autoritaires. Certaines démocraties débattent de « portes dérobées légales ». Ces débats offrent des arguments aux États qui veulent aller beaucoup plus loin.
5. Rôle stratégique des solutions hors plateformes — À mesure que les grandes messageries globales sont prises entre États aux exigences contradictoires, les solutions hors juridiction fondées sur le chiffrement local gagnent en importance : modèles sans serveur (DataShielder NFC HSM, DataShielder HSM PGP) et modèles avec serveur relais auto-hébergeable qui ne détient aucune clé (CryptPeer). Dans les deux cas, le serveur ne peut pas déchiffrer les messages, ce qui change radicalement le rapport de force.
En filigrane, ces signaux faibles indiquent que la réponse à la formule « Russie bloque WhatsApp » ne peut pas se limiter à un débat sur les seules messageries. Elle doit porter sur la conception même des architectures de chiffrement à l’échelle des États, des organisations et des individus.
Cas d’usage souverain — Messagerie hors juridiction et chiffrement local
Les architectures sans serveur, avec HSM et clés segmentées (DataShielder), ou avec serveur relais auto-hébergeable sans clé (CryptPeer), proposent une alternative.
Il n’y a alors aucune clé centrale à livrer et aucune base à saisir.
Un cas d’école : quand l’État contrôle la messagerie
L’affaire « Russie bloque WhatsApp » pose finalement une question plus large.
Que se passe-t-il quand un État exige d’un fournisseur de messagerie de livrer contenus, métadonnées ou clés de chiffrement ?
Tant que la sécurité repose sur une plateforme centrale, cette plateforme devient le point de pression évident.
Elle concentre les leviers techniques, juridiques et économiques.
Dans un modèle centralisé :
- la messagerie, même chiffrée, s’appuie sur des serveurs et des infrastructures qu’un État peut contraindre ;
- l’éditeur peut être poussé à introduire des exceptions, des backdoors ou des mécanismes de scanning côté client ;
- les utilisateurs ne contrôlent ni l’emplacement réel de leurs données, ni la manière dont elles circulent.
Autrement dit, la promesse de chiffrement reste fragile si la racine de confiance reste concentrée chez un acteur unique.
Limiter la confiance dans les plateformes grâce aux HSM à clés segmentées
Les architectures comme DataShielder et CryptPeer partent d’une autre hypothèse.
Elles visent à réduire au maximum la confiance accordée aux plateformes et aux réseaux.
Elles déplacent aussi la racine de sécurité au plus près des utilisateurs.
- DataShielder NFC HSM et DataShielder HSM PGP :
pas de serveur, pas de base de données centrale.
Le système peut fonctionner 100 % hors ligne, sans cloud ni compte.
Le chiffrement est réalisé dans un HSM matériel (NFC HSM ou HSM PGP).
Les clés (AES-256, RSA-4096 selon les cas) sont générées et stockées localement.
Un système de clés segmentées répartit enfin la confiance entre Main Operator et détenteurs de modules. - CryptPeer :
le chiffrement de bout en bout est géré côté pairs.
Un serveur relais auto-hébergeable et auto-portable ne reçoit que des données déjà chiffrées.
Il ne possède aucune clé de chiffrement ou de déchiffrement.
Le serveur ne fait qu’acheminer les paquets.
Il ne peut ni lire le contenu, ni reconstituer les secrets partagés entre les pairs.
Encapsulation de chiffrement — Un message chiffré dans un autre
Même lorsqu’on continue à utiliser une messagerie comme WhatsApp ou Telegram, il est possible de changer la donne.
Pour cela, on pratique l’encapsulation de chiffrement.
Concrètement :
- le contenu sensible est chiffré en local dans un HSM NFC (par exemple, DataShielder NFC HSM) ;
- ce qui transite dans WhatsApp n’est plus qu’un bloc chiffré opaque ;
- même si la messagerie ou l’infrastructure réseau sont compromises, l’attaquant ne récupère qu’un « chiffrement dans le chiffrement ».
Du point de vue d’un État, exiger des clés à l’éditeur de messagerie devient alors inopérant.
Les clés critiques ne sont pas chez ce fournisseur.
Elles résident dans des HSM matériels souverains ou dans des paires cryptographiques gérées au niveau des pairs, comme dans CryptPeer.
Pendant ce temps, le serveur relais ne voit que des données chiffrées qu’il ne peut pas ouvrir.
Souveraineté du chiffrement au-delà de WhatsApp et Max
Dans un monde où « Russie bloque WhatsApp » devient un précédent, ces architectures jouent un rôle de démonstrateur.
Elles montrent qu’il est possible de :
- continuer à utiliser des messageries grand public pour l’ergonomie ;
- rendre les données structurellement inexploitables sans le HSM ou sans la clé du pair, y compris en cas de saisie ou de blocage ;
- rester conforme à des cadres de contrôle à l’export de biens de chiffrement à double usage, comme celui qui encadre la solution DataShielder en Europe.
Autrement dit, la souveraineté réelle ne se joue pas uniquement dans le choix entre WhatsApp et Max.
Elle se mesure à la capacité d’architecturer des systèmes où ni Moscou ni aucun autre État ne peuvent exiger une backdoor centrale exploitable.
C’est là que se situe la véritable frontière entre sécurité nominale et souveraineté opérationnelle du chiffrement.
À relier avec…
À relier avec d’autres chroniques et publications Freemindtronic
- https://freemindtronic.com/digital-security-articles-freemindtronic/ — Collection de chroniques stratégiques sur la sécurité numérique.
- https://freemindtronic.com/cyberculture-a-collection-of-articles/ — Cyberculture et mutations géopolitiques de l’Internet.
- https://freemindtronic.com/technical-news/ — Actualités techniques et cryptographiques liées aux produits Freemindtronic.
- https://freemindtronic.com/tech-fixes-security-solutions/ — Solutions techniques de contre-espionnage et de résilience.
FAQ — Russie bloque WhatsApp, Max et Internet souverain
Questions fréquentes sur « Russie bloque WhatsApp »
Une incompatibilité entre chiffrement de bout en bout et Internet souverain
La menace de blocage complet de WhatsApp n’est pas un simple geste politique ponctuel. Elle découle d’un conflit structurel entre, d’un côté, une messagerie chiffrée de bout en bout que Meta ne peut pas déchiffrer, et de l’autre, un cadre légal russe (localisation des données, loi Iarovaïa, Internet souverain) qui exige que les services de communication puissent remettre contenus et moyens de déchiffrement aux autorités.
Tant que WhatsApp conserve son modèle de sécurité E2E, elle reste structurellement non conforme aux attentes de Moscou, ce qui rend la menace de blocage logique dans la doctrine de l’Internet souverain russe.
Blocage partiel aujourd’hui, menace de blocage total demain
À ce stade, la Russie a déjà bloqué les appels audio et vidéo sur WhatsApp (et sur Telegram), ce qui dégrade fortement l’usage de la messagerie dans la vie quotidienne.
Les messages textuels restent encore accessibles pour la majorité des utilisateurs, mais la menace de « blocage complet » est désormais explicite dans les déclarations de Roskomnadzor.
En pratique, on se dirige vers un scénario où :
- l’usage « normal » de WhatsApp devient de plus en plus pénible ;
- les fonctions clés (appels, fichiers) sont visées en priorité ;
- les usages résiduels se concentrent chez les personnes capables de gérer VPN et contournements, avec des risques juridiques croissants.
Max, superapp domestique et pivot de l’Internet souverain russe
Max, développée par VK, est présentée comme la messagerie nationale. Ce n’est pas seulement un clone de WhatsApp :
- elle combine messagerie, paiements, portefeuille numérique et accès à certains services administratifs ;
- elle est préinstallée sur les smartphones vendus en Russie et promue par des administrations ;
- elle ne propose pas de chiffrement de bout en bout vérifiable, ce qui la rend compatible avec les exigences de l’Internet souverain russe.
En rendant progressivement WhatsApp plus difficile à utiliser, l’État crée un effet de nasse : pour continuer à communiquer et interagir avec les services publics, les citoyens sont incités à basculer vers Max, où la visibilité de l’appareil d’État est maximale.
VPN, contournements et risque croissant de criminalisation
Techniquement, un blocage de WhatsApp peut être partiellement contourné via des VPN, des proxies ou des outils d’anti-censure. Cependant :
- la Russie dispose d’un dispositif de DPI lui permettant de détecter et de perturber certains VPN ;
- la consultation de contenus interdits et l’usage de services bloqués peuvent être assimilés à des comportements suspects, et des lois récentes visent déjà la recherche de contenus qualifiés d’« extrémistes » en ligne ;
- la pression légale peut monter contre les fournisseurs de VPN eux-mêmes.
Autrement dit, le contournement reste possible sur le plan technique, mais il devient de plus en plus risqué et incertain sur le plan juridique et opérationnel, surtout dans un contexte où l’« extrémisme » est défini très largement.
Du simple encadrement à la capacité de couper, filtrer et isoler
La plupart des États régulent l’Internet : protection des données, lutte contre la criminalité, encadrement des plateformes. L’Internet souverain russe va plus loin en combinant :
- la localisation forcée des données et le stockage massif des communications ;
- l’installation d’équipements de Deep Packet Inspection chez les FAI, pilotés par Roskomnadzor ;
- la capacité légale et technique d’isoler le Runet du reste du réseau mondial en cas de décision politique.
On passe ainsi d’une simple régulation à une capacité d’intervention en temps réel sur les flux, les services et les architectures, avec la possibilité d’invalider de facto des modèles de sécurité comme le chiffrement de bout en bout à grande échelle.
Chiffrement local, HSM et serveurs relais sans clé
Lorsque l’infrastructure de messagerie est contrôlée par un État, la confidentialité ne peut plus reposer uniquement sur la bonne volonté du fournisseur de service. Deux grandes familles d’architectures se dégagent :
- Modèles sans serveur de déchiffrement comme DataShielder NFC HSM et DataShielder HSM PGP : le chiffrement est effectué dans un HSM matériel, sans cloud ni base centrale. Les clés sont générées et stockées localement, selon une logique de clés segmentées, ce qui rend impossible la remise d’une « clé maître » à un État.
- Modèles avec serveur relais sans clé comme CryptPeer : les pairs chiffrent entre eux, et un serveur relais auto-hébergeable et auto-portable ne voit que des données déjà chiffrées, sans détenir aucune clé de chiffrement ou de déchiffrement. Même en cas de saisie du serveur, les contenus restent inexploitables.
Ces approches ne dispensent pas du respect des lois locales, mais elles montrent qu’il est possible de concevoir des systèmes où aucune entité centrale ne détient les clés, ce qui limite fortement les effets d’une pression politique sur un fournisseur unique.
Une ligne de fracture globale autour du chiffrement
Non. Si la séquence « Russie bloque WhatsApp » est particulièrement brutale, le débat sur le chiffrement dépasse largement les régimes autoritaires. Dans plusieurs démocraties, des responsables politiques évoquent régulièrement des backdoors « légales » ou des « accès exceptionnels » aux messageries chiffrées pour la lutte antiterroriste ou la protection des mineurs.
L’exemple russe agit comme un miroir grossissant : il montre jusqu’où peut aller un État lorsqu’il dispose d’un Internet souverain, de superapps nationales et d’un narratif sécuritaire permanent. Il rappelle aussi qu’une fois que l’on accepte le principe d’une porte dérobée, la frontière entre usage légitime et usage politique devient très difficile à tracer.
Ce que nous n’avons pas couvert
Cette chronique se concentre sur la séquence « Russie bloque WhatsApp », l’architecture juridique et technique de l’Internet souverain russe, la montée de Max et les architectures souveraines de chiffrement.
Elle laisse volontairement de côté plusieurs axes qui pourraient faire l’objet de chroniques dédiées :
- une cartographie détaillée de l’écosystème des superapps et de leurs modèles de gouvernance (WeChat, Max, futures superapps dans d’autres zones géopolitiques) ;
- une comparaison fine des cadres juridiques sur le chiffrement (Europe, États-Unis, Russie, Chine) et de leurs convergences possibles autour de l’idée de backdoors « légales » ;
- une analyse opérationnelle des capacités de DPI russes (types d’équipements, fournisseurs, scénarios d’usage en temps de crise) ;
- une exploration détaillée des stratégies de chiffrement de surcouche (DataShielder, CryptPeer, autres modèles sans serveur ou sans clé côté serveur) adaptées à des contextes de plus en plus fragmentés.
Ces dimensions pourront être développées dans de futures chroniques de la série Cyberculture, avec un focus spécifique sur la souveraineté opérationnelle du chiffrement dans un Internet balkanisé.
Sources officielles et références
- Loi dite « Iarovaïa » — lois fédérales n° 374-FZ et 375-FZ du 06.07.2016, texte officiel (russe) disponible sur le portail juridique de l’État russe : http://pravo.gov.ru ; synthèse en anglais : https://en.wikipedia.org/wiki/Yarovaya_law
- Loi fédérale n° 90-FZ sur l’« Internet souverain » (modification de la loi sur les communications et sur l’information) — texte officiel consultable via le portail juridique : http://pravo.gov.ru ; analyses comparatives : rapports d’ONG (Access Now, Human Rights Watch).
- Communiqués de Roskomnadzor relatifs à WhatsApp, Telegram et Max (blocage des appels, menace de blocage complet, promotion de Max comme messagerie nationale) : https://rkn.gov.ru
- Banque de Russie — données sur la fraude et les pertes financières liées à l’ingénierie sociale et aux canaux de communication (rapports officiels et bulletins statistiques) : https://www.cbr.ru
- Décision de justice classant Meta comme « organisation extrémiste » et exclusion explicite de WhatsApp du champ d’interdiction — documents et communiqués accessibles via le Parquet général de Russie : https://genproc.gov.ru, complétés par les résumés de la presse internationale.
- Analyses de la superapp Max et de son rôle dans l’Internet souverain russe — presse russe spécialisée et observatoires de la souveraineté numérique (par exemple : Reporters sans frontières, Financial Times, etc.).