La Llei andorrana sobre el doble ús s’inscriu en una reforma estratègica del control de les exportacions. Davant les noves amenaces híbrides, es crea una base jurídica centrada en el dret duaner, la sobirania tecnològica i l’alineament parcial amb la UE. Identificació EORI, compliment UE i regulació criptogràfica esdevenen pilars d’aquesta seguretat reglamentària, convertint aquesta anàlisi en una referència en català per al control estratègic de la tecnologia.
El control de les exportacions de béns de doble ús esdevé un pilar de la sobirania tecnològica andorrana. Davant la complexitat creixent de les cadenes de valor, la criptologia exportada i les regulacions extraterritorials, Andorra anticipa aquests desafiaments mitjançant una reforma estratègica del seu marc duaner i reglamentari. Aquesta anàlisi jurídica especialitzada explora: ✔ Com Andorra articula el compliment UE i al mateix temps la autonomia sobirana a través de la Llei 10/2025.
Sobre l’autor — Inventor de tecnologies de doble ús i fundador de Freemindtronic Andorra, Jacques Gascuel desenvolupa solucions de protecció de dades i contraespionatge amb vocació civil i militar. Analitza aquí els aspectes estratègics de la llei andorrana sobre el doble ús des d’una perspectiva «privacy by design» conforme a les exigències reglamentàries internacionals.
El Consell General d’Andorra va aprovar la Llei 10/2025 el 13 de maig de 2025, publicada posteriorment al BOPA núm. 68 del 4 de juny de 2025. Aquesta llei suposa un punt d’inflexió clau en l’evolució del dret duaner andorrà, ja que busca l’alineació de la legislació nacional amb el Codi Duaner de la Unió Europea, segons estableix el Reglament (UE) núm. 952/2013 de 9 d’octubre de 2013 (EUR-Lex – CELEX:32013R0952). En substitució de la Llei 17/2020, aquesta reforma introdueix una arquitectura moderna per a la regulació duanera. Consta de 296 articles repartits en nou títols. Concretament, facilita els tràmits duaners, impulsa la digitalització de les operacions i, sobretot, estableix un marc jurídic sòlid per al control dels fluxos sensibles, especialment pel que fa als béns de doble ús. Per a més informació oficial, els textos són consultables aquí: Així, aquesta nova legislació posiciona Andorra en una lògica de compliment reforçat i integració reguladora progressiva amb la Unió Europea. Abans d’abordar les disposicions específiques de la Llei andorrana de doble ús, és útil revisar els punts estructurants del nou Codi de Duana, que reforcen l’eficiència i la transparència del sistema duaner andorrà. El Codi redefineix conceptes clau per millorar la seguretat jurídica: Continuem l’anàlisi de la Llei andorrana de doble ús examinant ara l’estructura financera i procedimental que regula els fluxos duaners. Aquest pilar normatiu, lluny de ser secundari, assegura la seguretat dels ingressos públics i aporta previsibilitat i fiabilitat als operadors econòmics. Aquesta part del nou Codi estableix un triplet coherent: gestió del deute duaner, implementació de garanties i disseny d’autoritzacions administratives. Aquests elements asseguren una governança rigorosa dels fluxos comercials de risc, especialment els relacionats amb tecnologies sensibles. La Llei 10/2025 introdueix un mecanisme coherent de càlcul, pagament i reemborsament dels drets de duana. A més, estableix normes precises sobre el deute duaner i exigeix, en determinats casos, garanties financeres dels operadors. Aquesta estructuració pretén establir una logística més fluïda tot mantenint un alt nivell de supervisió. La nova llei estableix un sistema estructurat per a les sol·licituds, tramitació i emissió d’autoritzacions duaneres, fonamental per garantir la seguretat jurídica dels operadors econòmics. L’administració duanera pot atorgar autoritzacions generals o específiques segons el tipus d’operació i el nivell de risc associat. Un registre digital centralitzat recull totes les autoritzacions emeses, assegurant-ne la traçabilitat i verificabilitat. El codi imposa un termini màxim de resposta per evitar bloquejos administratius. Ara entrem al nucli del dispositiu legal relatiu als béns de doble ús, un aspecte sensible de la Llei 10/2025. Text de referència: Reglament (UE) 2021/821 Aquesta disposició va entrar en vigor immediatament després de la publicació de la llei, el 5 de juny de 2025, segons la seva disposició final. El Decret 207/2025, publicat el 12 de juny de 2025, especifica els tràmits associats a l’autorització. Text oficial: BOPA Andorra – GR_2025_06_11_13_27_27 Aquest text preveu que: Abans fins i tot de l’entrada en vigor de la Llei andorrana de doble ús, Freemindtronic ja havia iniciat, des de 2021, una acció exemplar. Avançant-se a les obligacions reguladores, l’empresa va estructurar els seus fluxos comercials sensibles dins un marc ètic i jurídic rigorós. Freemindtronic va proposar una Carta Ètica, acompanyada d’una documentació formalitzada des de 2022, per regular l’ús i exportació de les seves tecnologies criptogràfiques sensibles. Mesures concretes: Per garantir una conformitat jurídica total en l’exportació de tecnologies sensibles, Freemindtronic també s’ha recolzat en els requisits francesos pel que fa al control dels mitjans de criptologia. Els expedients s’han d’enviar a: El formulari principal, Annexe I, és disponible aquí: formulari PDF. Aquest document inclou: Gràcies a aquest rigor, Freemindtronic ha pogut exportar legalment els mòduls DataShielder NFC HSM Defense, amb la validació del seu soci exclusiu AMG Pro. Mentre l’aplicació de la Llei andorrana sobre els béns de doble ús tot just comenca, els actors públics i privats poden tenir un paper estratègic en la difusió de bones pràctiques. Aquesta dinàmica representa una gran oportunitat per estructurar un ecosistema virtuós d’acompanyament normatiu i de sensibilització dels operadors econòmics. En particular, Andorra disposa d’un potencial de co-construcció entre institucions i empreses innovadores, amb respecte a les seves prerrogatives respectives. En aquest context, esdevé pertinent desenvolupar eines d’ajuda per a la comprensió de la regulació i oferir informació clara i estructurada als professionals implicats. La regulació andorrana sobre els béns de doble ús, tot i estar publicada al BOPA, pateix actualment una manca de documentació aplicada. Encara no s’han publicat punts d’informació especialitzats, tutorials administratius o guies de conformitat per part de les institucions públiques. Basant-se en la seva experiència reguladora, Freemindtronic ha iniciat la redacció d’una guia pràctica de conformitat, co-marcable amb entitats com la Duana Andorrana (enllaç oficial). Aquesta iniciativa té per objectiu: Paral·lelament, Freemindtronic ha publicat diversos recursos accessibles en línia sobre la regulació internacional dels productes de doble ús, en particular: Aquests recursos es presenten com a complements informatius fiables als textos oficials i contribueixen a la implementació de la Llei andorrana sobre els béns de doble ús. El règim andorrà de control de les exportacions de doble ús forma part d’un marc regulador global, on cada jurisdicció imposa estàndards específics per a la regulació i el seguiment dels fluxos comercials sensibles. A causa del seu acord duaner amb la Unió Europea, Andorra es beneficia de peculiaritats que influeixen en el seu enfocament de les exportacions i les exempcions aplicables. No obstant això, la normativa vigent a les grans potències econòmiques – la Unió Europea, els Estats Units, el Regne Unit, Suïssa, els països de la Commonwealth – influeix en les obligacions dels exportadors andorrans. Aquesta dinàmica es reflecteix en: Per tal de comparar aquestes regulacions i avaluar el seu impacte en el comerç intracomunitari, a la taula següent es presenta un resum de la normativa internacional, les seves dates d’entrada en vigor i les seves implicacions per a Andorra. Marc normatiu de les principals jurisdiccions Efecte extraterritorial i singularitat andorrana L’ efecte extraterritorial de la normativa nord-americana (AEOI) i europea (Reglament UE 2021/821) afecta la gestió de les exportacions d’Andorra. No obstant això, gràcies a l’Acord Duaner de 1990, Andorra es beneficia d’una unió duanera parcial amb la UE, que permet la lliure circulació de productes industrials (capítols 25 a 97 de l’aranzel duaner) un cop introduïts a la cadena europea, sense tràmits addicionals. Així, una anàlisi en profunditat suggereix que és possible exportar productes de doble ús d’Andorra a la Unió Europea sense autorització prèvia, subjecte a les condicions següents: Aquesta peculiaritat normativa diferencia Andorra dels Estats membres de la UE, que han d’aplicar estrictes règims de control de les exportacions. No obstant això, encara cal una major vigilància, especialment pel que fa als desenvolupaments legislatius internacionals que podrien reforçar els requisits duaners. La promulgació de la Llei andorrana sobre els béns de doble ús (Llei 10/2025) marca una evolució significativa dins de l’arquitectura normativa del país, en establir les primeres bases per a un control d’exportació reglamentat. Aquesta secció analitza l’abast material, els actors institucionals implicats i els efectes concrets per als operadors econòmics, en un context d’integració progressiva al marc europeu. El Reglament (UE) 2021/821 permet, en general, la lliure circulació dels béns de doble ús dins del mercat interior de la UE, excepte per a productes especialment sensibles inclosos a l’Annex IV. Això implica que, un cop un bé forma part de l’àmbit de la UE, la seva reexportació cap a un altre Estat membre no requereix autorització addicional, llevat de casos particulars. L’Acord del 1990 estableix una unió duanera parcial entre el Principat d’Andorra i la Unió Europea, que cobreix els capítols 25 a 97 del Tarifa Duaner Comuna. Aquest acord permet la lliure circulació de mercaderies, suprimint barreres aranzelàries per als productes concernits. Segons les anàlisis del CEPS, els productes prèviament importats a Andorra des d’un Estat tercer i que disposin d’un número EORI poden circular lliurement per la UE sense formalitats addicionals, excepte els productes del tabac, que resten sotmesos a regulacions específiques. Una conclusió a verificar és si, sobre la base de l’acord duaner i el reglament europeu, esdevé possible exportar béns de doble ús des d’Andorra cap a la UE sense autorització prèvia andorrana, sota certes condicions: Si aquestes condicions es compleixen, representaria una singularitat notable en relació amb les regulacions dels Estats membres de la UE. Recursos oficials: La reforma duanera impulsada per la Llei 10/2025 i el seu decret d’aplicació proporciona als industrials andorrans condicions operatives estratègiques en un entorn altament regulat a escala internacional.. En aquest sentit, diversos dispositius criptogràfics “fabricats a Andorra” de la gamma DataShielder NFC HSM o PGP HSM, malgrat estar classificats dins de la categoria 5, part 2 del Reglament (UE) 2021/821, no estan inclosos a l’Annex IV i per tant es beneficien plenament de l’exempció europea contemplada per aquesta nova normativa andorrana: Impactes concrets: A tall d’il·lustració, es presenten dos models de documents inspirats en les annexes del Decret 207/2025 per facilitar l’adaptació immediata. DESTINATARI: Data, lloc, segell i signatura DESTINATARI: Em comprometo a: Data, lloc, signatura, segell, funció del signant Tot i que Andorra ha reforçat recentment el seu marc legislatiu amb la Llei andorrana sobre els béns de doble ús, en particular a través de l’article 267, paràgraf 3, lletra f de la Llei 10/2025, persisteix una zona grisa preocupant pel que fa a sancions i embargaments. Aquesta llei defineix les condicions d’autorització d’exportació per als béns sensibles criptogràfics, però no preveu cap mecanisme de control a posteriori ni dispositiu repressiu autònom en cas d’incompliment de les seves obligacions. A les jurisdiccions europees i nord-americanes, aquesta mancança donaria lloc a un sistema detallat tant administratiu com penal. Per exemple, el Reglament (UE) 2021/821 estableix procediments clars per a la repressió d’infraccions, mentre que els Estats Units disposen d’un arsenal normatiu sòlid a través de l’EAR i de les sancions de l’OFAC. A Suïssa i a França, l’exportació no autoritzada de tecnologies de doble ús és objecte de sancions severes, inclosa la responsabilitat penal dels directius. A l’inrevés, el marc jurídic exportador andorrà encara presenta mancances estructurals quant a la resposta davant infraccions. Aquesta absència d’un règim sancionador explícit obre un buit normatiu que pot exposar el país a riscos d’abús i posar en qüestió la seva cooperació internacional, especialment en el marc del Reglament europeu esmentat. Davant les mancances detectades en el règim actual, sembla oportú consolidar progressivament una governança nacional andorrana del control d’exportació. Aquesta podria inspirar-se útilment en els dispositius implantats a França i Espanya, sense fer una transposició mecànica, sinó amb respecte per la sobirania jurídica d’Andorra. En aquest context, Andorra podria instaurar un Comitè intergovernamental andorrà del doble ús, integrat per: Aquest comitè tindria el mandat d’elaborar una doctrina sobirana d’exportació, adoptar un decret d’aplicació autònom que defineixi sancions i controls, i coordinar la cooperació amb els socis europeus. Aquesta inspiració té una legitimació especial, ja que els dos estats de referència – França i Espanya – són també coprínceps constitucionals d’Andorra. La seva influència institucional i arrelament històric confereixen a les seves pràctiques un estatus de referència compatible amb l’ordre jurídic andorrà. A la llum de les disposicions introduïdes per la Llei andorrana sobre els béns de doble ús i el seu decret d’aplicació, sembla evident que el legislador andorrà ha fet un pas estructurant cap a una convergència amb els estàndards europeus, tot preservant l’especificitat jurídica del Principat d’Andorra. L’articulació entre el dret intern, el dret de la Unió Europea i els règims extraterritorials internacionals (US EAR, UK, Wassenaar) exigeix a partir d’ara una vigilància constant per part dels operadors econòmics, a fi de garantir la conformitat dinàmica de les seves pràctiques exportadores. En aquest sentit, la trajectòria anticipadora i ètica de Freemindtronic — il·lustrada per actuacions documentades i una doctrina de conformitat consolidada — constitueix un model transferible. Demostra que la iniciativa privada pot contribuir útilment a la construcció d’un règim jurídic coherent, en benefici tant de l’Estat com dels actors industrials. Correspon ara a les autoritats andorranes competents continuar amb l’esforç d’acompanyament normatiu, en particular mitjançant la producció de doctrines administratives, guies oficials i la posada en marxa de formacions i finestretes especialitzades. En paral·lel, les empreses han d’institucionalitzar una vigilància reguladora integrada, articulada amb matrius d’impacte extraterritorial, per fer de la conformitat exportadora un veritable eix estratègic. Així, la implementació efectiva i fluida d’aquest règim es fonamenta en una sinergia entre dret, tecnologia i responsabilitat compartida. Traça els contorns d’un nou pacte normatiu andorrà basat en la transparència, la seguretat jurídica i l’ambició d’un model econòmic obert però rigorosament regulat. La reforma del Codi de Duana mitjançant la Llei 10/2025, del 13 de maig, juntament amb el Reglament d’execució sobre l’exportació de béns de doble ús (Decret 207/2025), ofereix una oportunitat inèdita per al Principat d’Andorra de construir una doctrina pròpia en matèria de control estratègic, alineada però diferenciada dels règims europeus (UE), francès, espanyol i suís. França: el règim francès es fonamenta en el Codi de la defensa, l’ordre del 8 de juliol de 2015 per a les AIMG i l’ordre del 2 de juny de 2014 per a les LEMG, combinats amb decisions puntuals de suspensió de derogacions. Distingix rigorosament entre materials classificats (cat. ML) i béns de doble ús (cat. DU), i imposa procediments complexos i centralitzats, incloses les importacions temporals de materials amb finalitats d’exhibició. Espanya: sota l’empara del Reial decret 679/2014, Espanya també aplica el Reglament (UE) 2021/821, amb una interpretació administrativa sovint conservadora. La classificació en matèria de criptologia o de components electrònics és sistemàtica, i l’exportació cap a països tercers (fora de la UE) està subjecta a un seguiment reforçat. Suïssa: tot i no ser membre de la UE, Suïssa adopta una política d’equivalència basada en la Güterkontrollverordnung (GKV) i l’Ordenança sobre el material de guerra (OMG). L’autoritat SECO supervisa un règim fluid però rigorós, amb èmfasi en la transparència comercial i la conformitat extraterritorial. Unió Europea: el Reglament (UE) 2021/821 (versió consolidada) estableix una base harmonitzada fonamentada en les llistes de control, els criteris de seguretat internacional i l’anàlisi de risc per país. Reptes específics per a Andorra: cap a una doctrina nacional del doble ús La Carta Ètica entre Freemindtronic i el Govern d’Andorra prefigura aquesta doctrina, integrant els principis de transparència, no proliferació, desenvolupament sostenible i sobirania jurídica. Constitueix una base rellevant per estendre la regulació a segments tecnològics emergents, com ara sistemes d’autenticació distribuïda, mitjans criptològics d’ús ciberdefensiu, o tecnologies fonamentades en ADN digital. La UE preveu ampliar l’àmbit d’aplicació del règim de doble ús a tecnologies crítiques com la intel·ligència artificial, la ciberseguretat i la cadena de blocs, en el marc de l’estratègia de seguretat econòmica europea (Comunicació COM(2023) 249 final). Andorra haurà d’anticipar aquests moviments per mantenir l’equivalència reguladora. La dinàmica actual impulsa el país a estructurar una capacitat nacional de doctrina, supervisió i innovació reguladora sobre el doble ús, incloent:
Anàlisi jurídica profunda de la llei andorrana de doble ús Llei 10/2025 del Codi de Duana d’Andorra
✔ Per què el règim EORI i l’acord duaner Andorra–UE ofereixen un avantatge per a les exportacions estratègiques.
✔ Com estructurar una doctrina andorrana del doble ús, en coherència amb el Règim (UE) 2021/821.
✔ Quins són els futurs reptes: IA, ciberseguretat hardware, sobirania de cadenes crítiques.1. Anàlisi estratègica de la Llei andorrana de doble ús: reforma del Codi de Duana 2025
2. Elements estructurants del nou Codi de Duana andorrà
2.1 Ampliació del perímetre duaner
2.2 Precisió terminològica essencial
Terme
Definició (segons la llei)
Estatut duaner
Caràcter comunitari o no d’una mercaderia
Posada en lliure pràctica
Règim que permet l’entrada al mercat andorrà
Representant duaner
Mandatari autoritzat per realitzar els tràmits duaners en nom d’un tercer
2.3 Digitalització dels procediments
3. Sistema andorrà de drets, garanties i autoritzacions: cap a un control eficaç
3.1 Regulació dels deutes duaners i garanties
3.2 Règims econòmics duaners: fluïdesa amb condicions
3.3 Gestió de les autoritzacions duaneres: un gir normatiu
4. Regulació específica de la Llei andorrana de doble ús
4.1 Article 267.3.f: marc jurídic essencial
4.2 Decret d’aplicació 207/2025: modalitats pràctiques
4.3 Freemindtronic: un exemple de conformitat proactiva
4.4 Documentació de conformitat internacional: model francès i procediment ANSSI
5. Cooperació andorrana i recursos pedagògics: una obertura estratègica
5.1 Absència de guies institucionals: un buit a omplir
5.2 Contribució de Freemindtronic: contingut pedagògic, guia pràctica i sensibilització
5.3 Eines digitals disponibles
Alineació del règim andorrà amb la normativa internacional
Jurisdicció
Regulació
Data d’entrada en vigor
Data de curació
Particularitats per a la
Unió Europea
Reglament (UE) 2021/821
9 de setembre de 2021
Des del 2022 amb la guerra d’Ucraïna
Lliure circulació dins de la UE, excepte l’article IV per a determinades mercaderies.
Estats Units (EAR)
15 CFR 730 i següents.
13 de setembre de 1979
2022 – Reforç de les sancions contra Rússia i la Xina
Regla de minimis, extraterritorialitat, sancions de l’OFAC. Oficina d’Indústria i Seguretat
El Regne Unit
Ordre de control d’exportacions 2008
17 de desembre de 2008
2022 – Alineació amb les sancions de la UE i els EUA contra Rússia
Llicència a través de SPIRE, règim nacional post-Brexit. Control d’exportacions del Regne Unit
Suïssa
Ordenança OCB, SR 946.202
1 de juliol de 2012
2023 – Adopció de sancions selectives
Alineació amb la UE, però amb autoritzacions específiques. SECO suïssa
El Marroc
Llei nº 42-18
17 de desembre de 2020
1 de gener de 2025
Llicència obligatòria a partir de l’1 de gener de 2025, amb una fase transitòria de tres mesos.
Ucraïna
Llei d’Ucraïna sobre control d’exportacions
27 de juny de 2012
2022 – Sancions generalitzades contra Rússia
Regulació estricta de les exportacions i control millorat de les mercaderies sensibles.
Israel
Regulacions israelianes de doble ús
2016
2023 – Reforç dels controls militars d’exportació
Estricte control de les exportacions, alineació parcial amb els estàndards de Wassenaar.
Rússia
Regulacions russes sobre exportacions sensibles
2003
2022 – Enduriment de les restriccions a causa de les sancions internacionals
Control estricte de les exportacions estratègiques.
Xina
Regulacions de doble ús de la Xina
2020
2023 – Més dur amb les exportacions de semiconductors i IA
Estricte règim de control i restriccions tecnològiques.
Singapur
Normativa de control d’exportacions
2003
2022 – Augment de les restriccions a les tecnologies estratègiques
Regulació estricta dels articles de doble ús.
Brazil
Normativa brasilera sobre exportacions estratègiques
2011
2024 – Reforç de sancions i controls tecnològics
Control d’exportacions a través del Ministeri de Comerç Exterior.
6. Alineació del règim andorrà amb les regulacions internacionals
6.1 Lliure circulació dins de la UE
6.2 Andorra i la Unió Duanera Parcial
6.3 Implicacions per als béns de doble ús
6.4. Beneficis directes per als industrials andorrans del sector dual i defensa
6.5 Il·lustracions pràctiques: models de conformitat
Model A – Formulari de sol·licitud d’autorització d’exportació de béns de doble ús
Duana Andorrana – Despatx Central de Duana
Av. Fiter i Rossell, núm. 2, bloc A, Escaldes-Engordany, AD700
[ ] Exportació puntual – Data estimada: ____
[ ] Exportació recurrent – Període: del ____ al ____
Nom/Raó social: ____
NRT: ____
Nom/Raó social: ____
Adreça completa: ____
Activitat econòmica relacionada amb els béns: ____
Lloc web: ____
Nom/Raó social: ____
Adreça completa: ____
Activitat: ____
Lloc web: ____
Codi TARIC (10 dígits): ____
Descripció: ____
Quantitat/Unitat: ____
Valor (€): ____
País d’origen: ____
País de procedència: ____
Data del contracte: ____
Codi del règim duaner: ____
Ús final detallat: ____
Documents adjunts: [ ] Declaració de destinació finalModel B – Declaració de destinació final
Duana Andorrana – Despatx Central de Duana
Av. Fiter i Rossell, núm. 2, bloc A, Escaldes-Engordany, AD700
Nom/Raó social: ____
NRT: ____
Nom/Raó social: ____
Adreça completa: ____
Descripció: ____
Quantitat/Unitat: ____
Activitat econòmica del comprador: ____
Ús/destinació dels béns: ____
– Utilitzar els béns exclusivament segons l’ús declarat;
– No reexportar-los sense autorització de les autoritats del país de destinació.6.6. Sancions, embargaments i buit regulador a Andorra
6.7. Cap a una governança andorrana del doble ús: inspiració europea i marc operatiu
El control dels béns de doble ús a França és competència de la Subdirecció de Comerç Internacional de Béns Estratègics (SBDU), vinculada a la Direcció General d’Empreses (DGE). Aquest organisme concedeix autoritzacions d’exportació en coordinació amb la Duana i el Ministeri de les Forces Armades a través del Servei d’Informació i Documentació (SID) per a un seguiment reforçat postexportació.
🔹 SBDU: Autoritat competent en matèria de control i emissió de llicències.
➡ Ministeri d’Economia – Béns de doble ús
🔹 Coordinació amb la Duana: Seguiment dels fluxos comercials sensibles i verificació de conformitat.
➡ Direcció General de Duanes i Drets Indirectes (DGDDI)
🔹 Ministeri de Defensa – SID: Anàlisi de riscos i control estratègic de les exportacions.
➡ Servei d’Informació i Documentació (SID)
🔹 SECOMS: Responsable de l’aplicació de regulacions sobre exportacions i importacions sensibles.
➡ Ministeri d’Indústria, Comerç i Turisme
🔹 JIMDDU: Òrgan intergovernamental competent sobre exportacions estratègiques.
➡ Decret oficial BOE 2023-21672
🔹 Informe semestral sobre exportacions de material de defensa i béns de doble ús:
➡ Estadístiques i dades (2024)
Accions pràctiques a implementar des d’ara
7. Abast normatiu i perspectives d’aplicació
8. Enfocament comparatiu i prospectiu: cap a una doctrina andorrana del doble ús
Comparacions doctrinals i marcs jurídics
Perspectives d’evolució reguladora
Reptes futurs i sobirania tecnològica andorrana
Glossari d’acrònims i termes especialitzats
Category Archives: News
French IT Liability Case: A Historic Legal Precedent
The French IT Liability Case has established a historic precedent, redefining the legal obligations of IT providers under French law. The Rennes Court of Appeal condemned MISMO to pay €50,000 in damages for failing its advisory obligations, highlighting the vital importance of proactive cybersecurity measures to safeguard clients against ransomware attacks. This case not only reshapes IT provider responsibilities but also offers valuable insights into the evolving relationship between technology and the law.
French IT Accountability Case: Jacques Gascuel provides the latest insights and analysis on the evolving legal landscape and cybersecurity obligations for IT providers. Your comments and suggestions are welcome to further enrich the discussion and address evolving cybersecurity challenges.
Table of Contents
🔹 Introduction: The Context of the Case🔹Timeline of the Case 🔹French IT Liability Case: A Historic Legal Precedent🔹 Obligations in IT Contracts Highlighted by the French IT Liability Case🔹 International Reactions: A Global Perspective🔹 Comparative Table: Types of Obligations🔹 Civil Code Connections for IT Obligations🔹 Context and Historical Background🔹 Technical Insights: What Went Wrong🔹 SMEs: Cybersecurity Challenges and Protection Strategies🔹 Best Practices for IT Providers to Avoid Legal Disputes🔹 Frequently Asked Questions🔹 Product Solutions for IT Providers and Clients🔹 Conclusion: Redefining IT Responsibilities
Specific deliverables and associated timelines.
Protocols for incident response and recovery.
Engage an independent expert to audit the system.
Compare the provider’s actions to industry standards.
Firewalls: Fortinet, Palo Alto Networks.
Email filtering: Barracuda, Proofpoint.
Offer advanced security options and explain their benefits.
Regularly update systems with security patches and tools.
Product Solutions for IT Providers and Clients
Aligning Obligations with PassCypher and DataShielder
The French IT Liability Case highlights the critical need for IT providers to meet their advisory obligations and implement robust cybersecurity measures. Freemindtronic’s PassCypher and DataShielder product lines provide comprehensive tools that directly address these legal and operational requirements, helping providers and clients mitigate risks effectively.
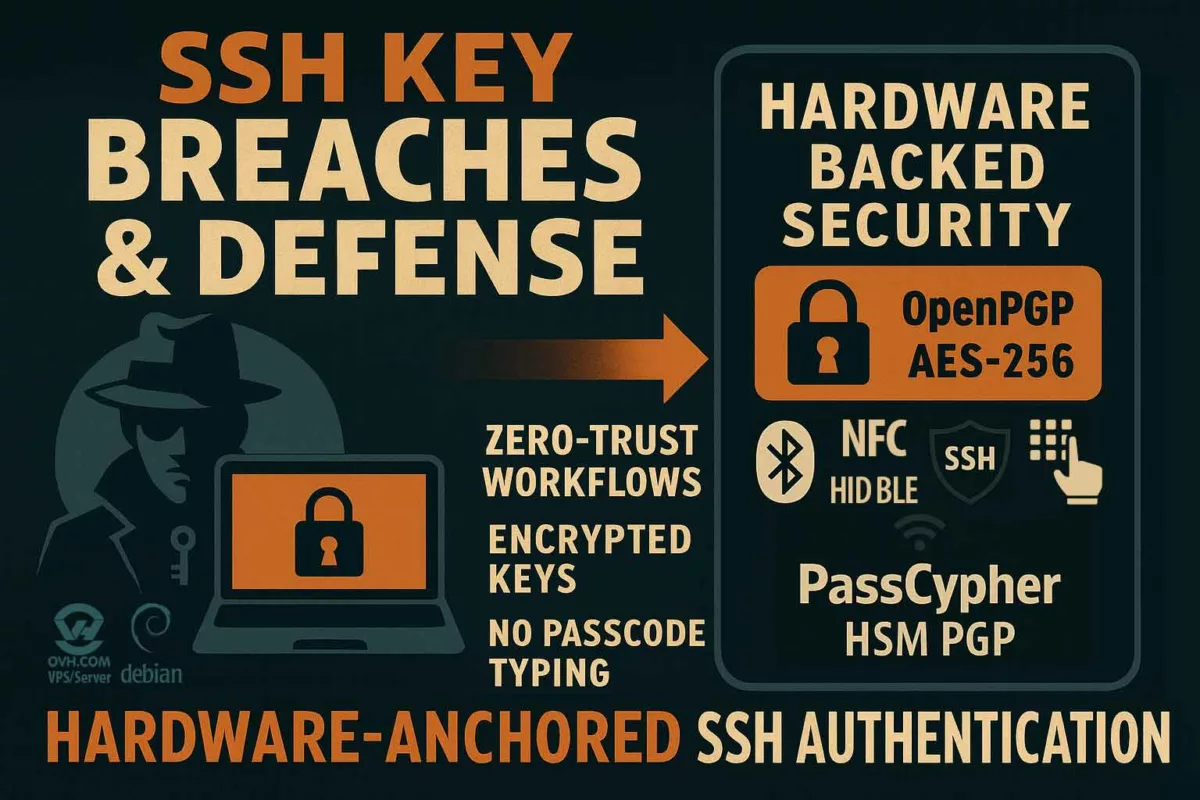
PassCypher NFC HSM and PassCypher HSM PGP: Reinforcing Authentication and Email Security
- Passwordless Security: Eliminating traditional passwords reduces the risk of credential compromise, a key entry point for ransomware attacks. PassCypher solutions enable one-click, encrypted logins without ever displaying credentials on-screen or storing them in plaintext.
- Sandboxing and Anti-BITB: Advanced protections proactively block phishing attempts, typosquatting, and malicious attachments, mitigating risks from email-based threats—the initial attack vector in the case.
- Zero Trust and Zero Knowledge: Operating entirely offline, these solutions ensure that credentials are managed securely, anonymized, and never stored on external servers or databases.
- Legal Compliance: PassCypher aligns with GDPR and the NIS2 Directive by providing secure, documented processes for authentication and email security.
DataShielder NFC HSM and DataShielder HSM PGP: Advanced Encryption and Backup Security
- Disconnected Backups: DataShielder enables the management of secure, air-gapped backups, a key safeguard against ransomware. This approach aligns with best practices emphasized in the court decision.
- End-to-End Encryption: With AES-256 and RSA 4096-bit encryption, DataShielder ensures the confidentiality and integrity of sensitive data, mitigating risks from unauthorized access.
- Proactive Risk Management: DataShielder allows IT providers to recommend tailored solutions, such as isolated backup systems and encrypted key sharing, ensuring compliance with advisory obligations.
- Compliance Documentation: Providers can generate secure, encrypted reports demonstrating proactive measures, fulfilling legal and contractual requirements.
Combined Benefits for IT Providers and Clients
- Transparency and Trust: By adopting PassCypher and DataShielder, IT providers can deliver clear, documented solutions addressing unique cybersecurity challenges.
- Client Confidence: These tools demonstrate a commitment to protecting client operations, enhancing trust and long-term partnerships.
- Litigation Protection: Meeting advisory obligations with advanced tools reduces liability risks, as emphasized in the French IT Liability Case.
- Holistic Protection: Combined, these solutions provide comprehensive protection from the initial compromise (emails) to ensuring business continuity through secure backups.
PassCypher and DataShielder represent proactive, integrated solutions that address the cybersecurity gaps highlighted in the French IT Liability Case. Their adoption enables IT providers to safeguard client operations, fulfill legal obligations, and build resilient, trusted partnerships.
In-Depth Analysis of Authentication Time Across Methods
Time Spent on Authentication is critical to digital security. This study explores manual methods, password managers, and tools like PassCypher NFC HSM or PassCypher HSM PGP, analyzing their efficiency, security, and impact. It highlights economic, environmental, and behavioral implications, emphasizing the role of advanced technologies in shaping faster, secure, and sustainable authentication practices globally.
Study Overview: Objectives and Scope
Understanding the cost of authentication time is crucial to improving productivity and adopting advanced authentication solutions.
This study examines the time spent on authentication across various methods, highlighting productivity impacts and exploring advanced tools such as PassCypher NFC HSM or PassCypher HSM PGP for secure and efficient login processes. It provides insights into manual and automated methods and their global adoption.
Objective of the Study
- Quantify the time required to log in with pre-existing credentials stored on physical or digital media, with or without MFA.
- Evaluate all authentication methods, including manual logins, digital tools, and advanced hardware solutions such as PassCypher NFC HSM or PassCypher HSM PGP.
- Compare professional and personal contexts to highlight global productivity impacts
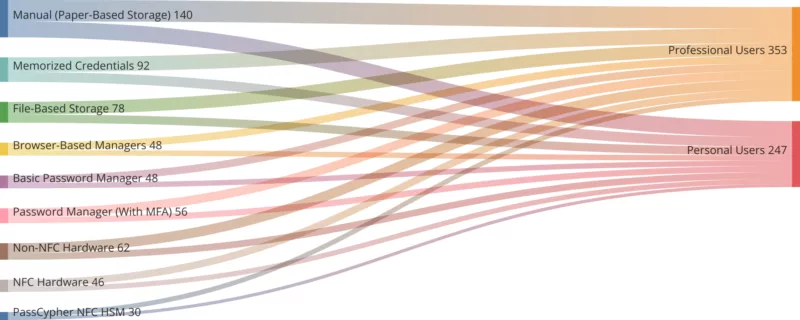
Authentication Methods Analyzed
Manual Methods
- Paper-based storage: Users read passwords from paper and manually enter them.
- Memorized credentials: Users rely on memory for manual entry.
Digital Manual Methods
- File-based storage: Credentials stored in text files, spreadsheets, or notes, used via copy-paste.
- Browser-based managers (no MFA): Autofill tools integrated into browsers.
Password Managers
- Basic password manager (no MFA): Software tools enabling autofill without additional security.
- Password manager (with MFA): Software requiring a master password and multi-factor authentication.
Hardware-Based Authentication
- Non-NFC hardware managers: Devices requiring physical connection and PIN entry.
- NFC-enabled hardware managers: Tools like PassCypher NFC HSM, utilizing contactless authentication.
Modern Authentication Methods
- Passkeys and FIDO: Passwordless solutions using biometrics or hardware tokens.
Time Spent on Password Changes
Corporate Cybersecurity Policies and the Cost of Authentication Time
| Policy | Time Per Change (Minutes) | Frequency (Per Year) |
|---|---|---|
| Monthly Password Changes | 10 | 12 |
| Quarterly Changes | 10 | 4 |
| Ad Hoc Changes (Forgotten) | 15 | 2 |
Time-Intensive Scenarios
Denial of Service (DoS) Impact
Extended login delays during attacks lead to significant downtime:
- Professional Users: 15–30 minutes per incident.
- Personal Users: 10–20 minutes per incident.
Forgotten Passwords
Password recovery processes average 10 minutes but can extend to 30 minutes if additional verification is required.
Regional Comparisons of Credential Use and Time
Credential Usage Across Regions
| Region | Average Personal Credentials | Average Professional Credentials |
| North America | 80 | 120 |
| Europe | 70 | 110 |
| Asia | 50 | 90 |
| Africa | 30 | 50 |
| South America | 40 | 60 |
Regional Credential Usage: A Heatmap Overview
This diagrame present the differences in credential usage across global regions. This heatmap highlights the number of credentials used for personal and professional purposes, revealing regional trends in authentication practices and the adoption of advanced methods.
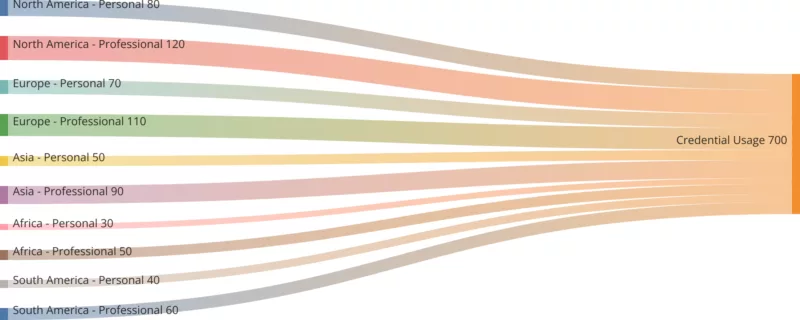
Cultural and Infrastructural Influences
In Asia, biometric solutions dominate due to advanced mobile ecosystems. North America shows a preference for NFC and password managers, while Africa and South America rely on manual methods due to slower technological adoption.
Behavioral Insights and Frustrations
Behavioral insights provide critical understanding of how users perceive and respond to the cost of authentication time.
Credential Change Frequency
Organizations enforce frequent password changes to meet cybersecurity standards, with monthly resets common in sectors like finance. Ad hoc changes often occur when users forget credentials.
MFA and DoS Impact
Complex MFA processes frustrate users, causing abandonment rates to rise. DoS attacks lead to login delays, resulting in significant productivity losses of up to 30 minutes per incident.
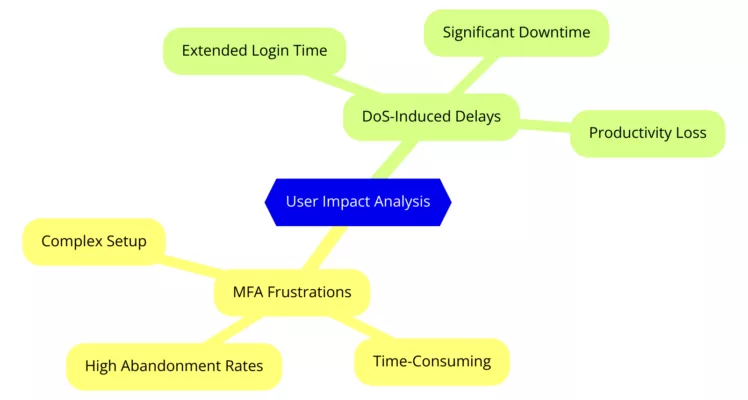
User Impact Analysis: MFA vs DoS Challenges
This mindmap explores the frustrations caused by complex multi-factor authentication (MFA) processes and delays from denial-of-service (DoS) attacks. Learn how these challenges affect user productivity and time spent on authentication.
Daily and Annual Time Allocation
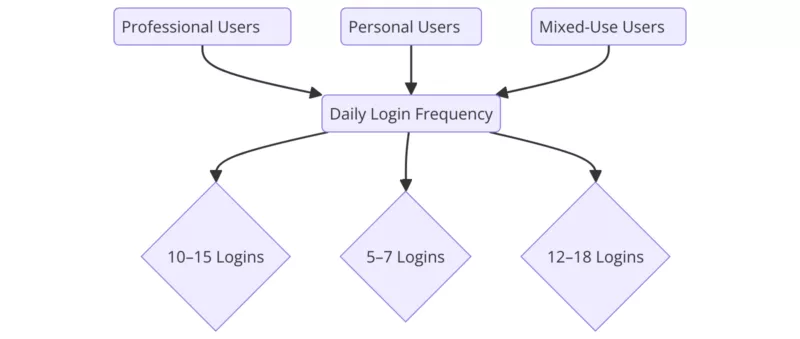
Daily Login Frequency
| User Type | Logins/Day |
| Professional Users | 10–15 |
| Personal Users | 5–7 |
| Mixed Use (Both) | 12–18 |
Daily Login Frequency: Comparing User Habits
Beyond the time spent on authentication, it’s crucial to consider its financial implications, especially in business or remote work contexts.
Accounting for the Cost of Authentication Time in Professional and Personal Contexts
The cost of authentication time is often underestimated, but when scaled across organizations, these delays translate into significant financial losses.
Overview: Time Is Money
Time spent on authentication, whether in professional, personal, or remote work contexts, often feels insignificant. However, scaled across an organization, these seemingly minor tasks translate into substantial financial losses. This section highlights the cost of time spent identifying oneself, managing passwords, and handling secure devices. We explore daily, monthly, and annual impacts across professional, private, and telework scenarios, demonstrating the transformative value of advanced solutions like PassCypher NFC HSM and PassCypher HSM PGP.
Key Scenarios for Time Allocation
| Scenario | Time Spent (Minutes) | Frequency (Per Day) | Monthly Total (Hours) | Annual Total (Hours) |
|---|---|---|---|---|
| Searching for stored passwords | 5 | 2 | 5 | 60 |
| Manual entry of memorized credentials | 3 | 5 | 7.5 | 90 |
| Copy-pasting from files or managers | 2 | 5 | 5 | 60 |
| Unlocking secure USB devices | 5 | 1 | 2.5 | 30 |
| Recovering forgotten passwords | 15 | 0.5 | 3.75 | 45 |
| Total (Typical Professional User) | 23.75 | 285 |
Financial Costs of Authentication Time
According to a study by Gartner companies dedicate up to 30% of IT tickets to password resets, with an average cost of $70 per request. By integrating solutions like PassCypher, these costs could be halved.
Based on industry reports and wage data from sources such as Gartner and the Bureau of Labor Statistics, the estimated average hourly wage for IT professionals ranges between $30 and $45, depending on experience, location, and sector. Considering a conservative estimate of $30 per hour, the financial impact of time spent on authentication becomes significant:
| User Type | Monthly Cost ($) | Annual Cost ($) |
|---|---|---|
| Single Professional | 712.50 | 8,550 |
| Small Business (50 users) | 35,625 | 427,500 |
| Medium Enterprise (1,000 users) | 712,500 | 8,550,000 |
Common References (2024–2025)
| Geographic Area | Approximate Gross Hourly Wage | Source |
|---|---|---|
| USA (Gartner) | $31.06/h (April 2025) | Trading Economics |
| Eurozone (OECD) | €30.2/h (2022, estimate) | INSEE |
| France (INSEE 2024) | €28.4/h average gross wage | INSEE |
| UK | ~£22/h → ~€26/h (weekly average wage of £716) | Trading Economics |
| Global (IT sector) | Between $30–$45/h depending on level | BDM |
Insight:
For a medium-sized enterprise, authentication time alone can lead to more than $8.5 million per year in lost productivity. This estimate does not include potential financial risks associated with security breaches, human errors, or compliance issues, which could significantly amplify overall costs.
Comparing Traditional and Advanced Authentication Solutions
Traditional authentication methods significantly increase costs due to inefficiencies, whereas advanced authentication solutions like PassCypher NFC HSM and PassCypher HSM PGP streamline processes, enhance security, and reduce expenses.
Traditional Authentication
- Cumulative Costs: High due to time-intensive processes such as searching, memorizing, and manually entering passwords.
- Risk Factors: Frequent errors, delays, and forgotten credentials lead to operational inefficiencies and increased support costs.
Advanced Authentication with PassCypher Solutions
- Cumulative Costs: Significantly reduced with modern authentication tools.
- Auto-Connection with PassCypher NFC HSM: Login times drop to less than 10 seconds, improving efficiency in high-frequency authentication tasks.
- One-Step Login with PassCypher HSM PGP: Even single-step logins are completed in just 1 second, minimizing delays.
- Dual-Stage Login with PassCypher HSM PGP: Two-step logins, including OTP validation, are completed in only 3 seconds, ensuring security without compromising speed.
Cost Reduction Example
A 50% decrease in authentication time for a 1,000-employee enterprise results in $4.25 million in annual savings, demonstrating the financial advantages of streamlined authentication solutions.
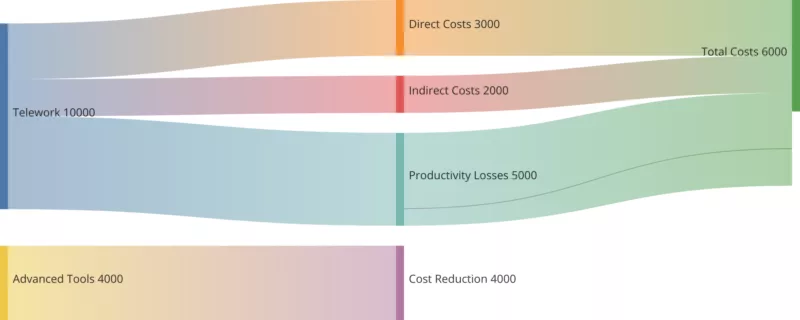
Telework and the Cost of Authentication Time
Remote work amplifies the cost of authentication time, with teleworkers spending considerable time accessing multiple systems daily. Advanced authentication solutions mitigate these delays.
Example: Remote Work
- A teleworker accesses 10 different systems daily, spending 30 seconds per login.
- Annual Cost Per Employee:
- Time: ~21 hours (~1,250 minutes).
- Financial: $630 per employee.
Enterprise Impact:
For a company with 1,000 remote workers, telework-related authentication costs can reach $630,000 annually.
Telework Costs and Authentication: Time Spent on Authentication
This diagram provides a detailed view of telework’s financial impacts, highlighting direct, indirect, and productivity-related costs. It emphasizes the significant savings in time spent on authentication achievable with advanced tools like PassCypher, reducing costs and enhancing productivity.
Solutions to Reduce Costs
Adopt Advanced Tools:
- PassCypher NFC HSM: Offers auto-connection on Android NFC devices for login in <10 seconds, streamlining the process and eliminating manual input delays.
- PassCypher HSM PGP: Enables one-click logins in <1 second, reducing dual-stage authentication to just 3 seconds.
- Bluetooth Keyboard Emulator: Enhances NFC HSM devices by enabling universal credential usage across any system supporting USB HID Bluetooth keyboards, reducing login times to under 9 seconds.
Consolidate Authentication:
- Single Sign-On (SSO): Minimize the need for multiple logins across platforms.
Train Employees:
- Efficient password management practices help staff save time and reduce frustration.
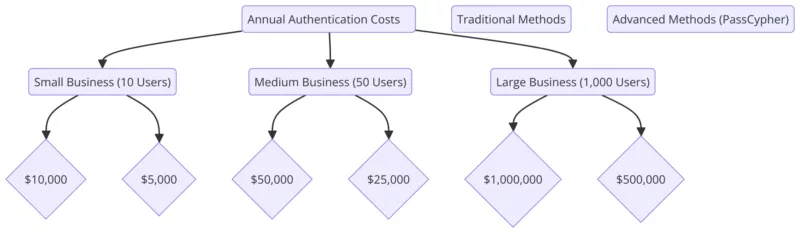
Annual Authentication Costs for Businesses
This diagram compares the annual authentication costs for small, medium, and large businesses. It highlights the financial savings achieved with advanced methods like PassCypher NFC HSM, showcasing their cost-effectiveness compared to traditional solutions.
Example of PassCypher NFC HSM in Action
With PassCypher NFC HSM:
- Scenario: A professional logs in 15 times daily.
- Time Saved: Traditional methods take 5 minutes daily (~20 seconds/login); NFC HSM reduces this to 15 seconds daily (~1 second/login).
- Annual Time Saved: ~24 hours/user.
- Financial Savings: $720/user annually; $720,000 for 1,000 users.
This showcases the transformative impact of modern tools in reducing costs and boosting productivity.
Annual Time Spent on Authentication
| Authentication Method | Professional (Hours/Year) | Personal (Hours/Year) |
| Manual (paper-based storage) | 80 | 60 |
| Manual (memorized credentials) | 55 | 37 |
| File-based storage (text, Word, Excel) | 47 | 31 |
| Browser-based managers (no MFA) | 28 | 20 |
| Password manager (basic, no MFA) | 28 | 20 |
| Password manager (with MFA) | 33 | 23 |
| Non-NFC hardware password manager | 37 | 25 |
| NFC-enabled hardware password manager | 27 | 19 |
| PassCypher NFC HSM (Auto-Connection) | 18 | 12 |
| PassCypher NFC HSM (TOTP with MFA) | 24 | 15 |
| PassCypher HSM PGP (Segmented Key) | 7 | 5 |
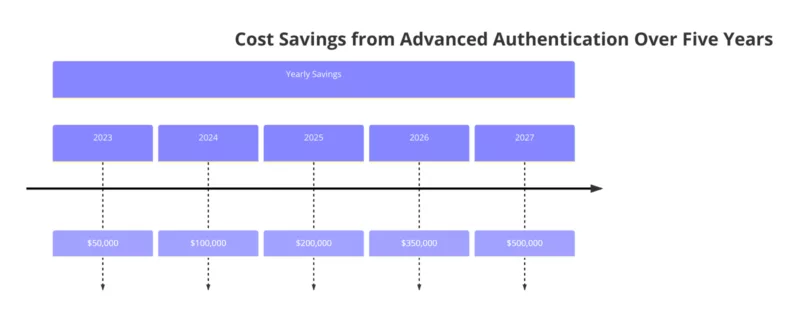
IT Cost Savings Through Advanced Authentication
Adopting advanced authentication methods can reduce IT costs significantly. This line graph illustrates potential savings over five years, emphasizing the value of transitioning to modern tools like NFC and passwordless solutions.
Economic Impact of Advanced Authentication Solutions
This suject highlights the economic implications of authentication practices, focusing on how advanced authentication solutions reduce the cost of authentication time and improve productivity.
IT Cost Reduction
Password resets account for up to 30% of IT tickets, costing $70 each. A 50% reduction could save companies with 1,000 employees $350,000 annually.
Productivity Gains
Switching to advanced methods like Passkeys or NFC saves 50 hours per user annually, translating to 50,000 hours saved for a 1,000-employee company, valued at $1.5 million annually.
Five-Year Cost Savings with Advanced Authentication
This diagram visualizes the financial benefits of adopting advanced authentication solutions. Over five years, companies can achieve significant cost savings, reflecting the economic advantages of modernizing authentication methods.
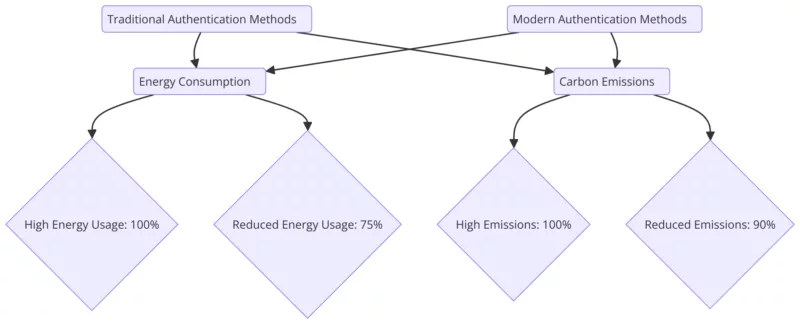
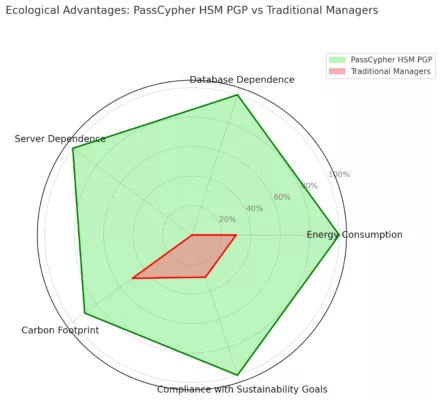
Environmental Impacts
The environmental impact of authentication processes is often underestimated. According to analysis from the Global e-Sustainability Initiative (GeSI), password resets place an additional load on data centers, significantly increasing energy consumption. Optimizing processes with modern tools like PassCypher NFC HSM can reduce this consumption by up to 25%, thereby cutting associated CO2 emissions.
Data Center Energy Costs
Extended authentication processes increase server workloads. Password resets alone involve multiple systems, significantly impacting energy use.
Global Energy Savings
Data centers represent a significant share of CO2 emissions from digital processes. According to the Global e-Sustainability Initiative (GeSI), optimizing authentication processes could reduce their carbon footprint by 10,000 metric tons annually
Energy and Carbon Footprint of Authentication Methods
Explore the environmental impact of authentication processes. This diagram compares energy usage and carbon emissions between traditional and modern methods, showcasing how advanced solutions can lead to a more sustainable future.
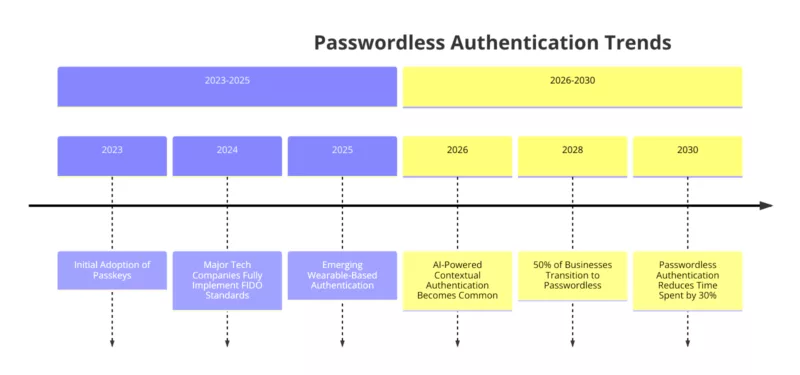
Future Trends in Advanced Authentication Solutions
Emerging technologies and advanced authentication solutions, such as AI-driven tools and passwordless methods, promise to further reduce the cost of authentication time.
Emerging Technologies
AI-driven authentication tools predict user needs and streamline processes. Wearables like smartwatches offer instant, secure login capabilities.
Passwordless Solution Adoption
Passkeys and FIDO technologies are expected to reduce global authentication time by 30% by 2030, marking a shift toward enhanced security and efficiency.
Key Trends in Passwordless Authentication
This diagram provides a detailed timeline of the evolution of passwordless authentication from 2023 to 2030. It outlines major advancements like the adoption of passkeys, the rise of wearable-based and AI-powered authentication, and the significant time savings these methods offer by 2030.
Statistical Insights and Visualizations
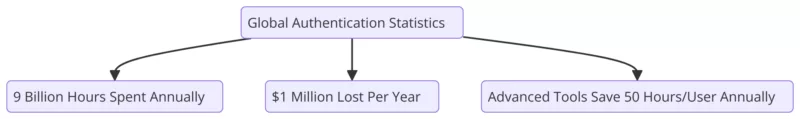
Authentication consumes 9 billion hours annually, with inefficient methods costing businesses over $1 million per year in lost productivity. Advanced tools like PassCypher NFC HSM can save users up to 50 hours annually.
Global Insights: Authentication Trends and Productivity
Explore the global trends in authentication, including the staggering time spent, productivity losses, and the savings achieved with advanced tools. This infographic provides a comprehensive overview of the current and future state of authentication practices.
Sources and Official Studies
- NIST SP 800-63B : Authoritative guidelines on authentication and credential lifecycle management, including best practices for reducing password reset costs.
- Global e-Sustainability Initiative (GeSI) : Analysis of the environmental and energy implications of data centers, emphasizing sustainability in digital infrastructures.
- Greenpeace : Research highlighting energy-saving strategies and their role in reducing the carbon footprint of IT systems.
- FIDO Alliance : Insights into the rapid adoption of passwordless solutions, with statistics on the time saved and enhanced user convenience.
- PassCypher NFC HSM Lite : A lightweight, secure solution for managing credentials and passwords with contactless ease.
- PassCypher NFC HSM Master : Advanced features for managing contactless credentials and ensuring secure login processes across various environments.
- Bluetooth Keyboard Emulator : An innovative device that allows secure, contactless use of credentials from NFC HSM devices across any system supporting USB HID Bluetooth keyboards. It ensures sub-9-second authentication, making it a universal tool for diverse systems, including proprietary software and IoT devices.
- PassCypher HSM PGP : A secure, end-to-end encrypted password manager with advanced PGP support, enabling robust credential security.
- Freemindtronic: Passwordless Password Manager : A detailed overview of Freemindtronic’s passwordless solutions, focusing on their ease of use and high security standards.
Passwordless Password Manager: Secure, One-Click Simplicity to Redefine Access by Jacques Gascuel – Discover how advanced encryption, combined with innovative licensing and eco-friendly design, transforms PassCypher HSM PGP into a true game-changer in modern password management. Share your thoughts or suggestions!
PassCypher at a Glance: Revolutionizing Passwordless Password Managers
- Passwordless Authentication: Experience seamless access with a fully offline and serverless system.
- Quantum Resistance: Safeguard your data against current and future threats using AES-256 CBC encryption and patented segmented key technology.
- Eco-Friendly Design: Minimize your carbon footprint with a serverless and databaseless architecture that consumes less energy.
- Universal Compatibility: Works effortlessly with any system, requiring no updates, plugins, or complex integrations.
- Data Sovereignty: Ensure full control over your data with local storage, fully compliant with GDPR, NIS2, and other international standards.
Ideal for: Businesses, government agencies, critical industries, and any organization seeking a secure, scalable, and sustainable solution.
PassCypher HSM PGP: The Ultimate Passwordless Password Manager for 2025
This cutting-edge solution eliminates traditional passwords, replacing them with robust, AES-256 encrypted containers and segmented key authentication. Operating entirely offline without servers or databases, PassCypher provides unmatched data sovereignty and resilience against cyber threats. Ideal for organizations seeking compliance with regulations like NIS2 or GDPR, it ensures quantum-resistant security while simplifying access with one-click authentication. Whether you’re protecting enterprise systems or personal accounts, PassCypher delivers secure, eco-friendly, and future-proof password management.
PassCypher HSM PGP goes beyond traditional password management by integrating advanced cryptographic tools directly into its platform. These features include the secure creation of SSH key pairs and AES-256 encryption keys, empowering users to streamline security processes while maintaining maximum control over sensitive data. Ideal for modern organizations, PassCypher adapts to the evolving needs of professionals and teams working in dynamic environments.
Passwordless Cybersecurity Tailored for Businesses of All Sizes
PassCypher HSM PGP provides unmatched security for businesses, whether you’re a startup, an SME, or a multinational corporation:
- Small Businesses: Benefit from affordable, flexible licensing and streamlined access management.
- Large Enterprises: Ensure secure, scalable access for teams, with compliance-ready features and robust protection against ransomware.
- Critical Industries: Protect sensitive data with quantum-resistant encryption and zero-server architecture.
Hardware-Based Licensing for SMEs: PassCypher’s hardware licenses offer cost-effective, scalable solutions, enabling SMEs to enhance security without overstretching budgets. These licenses are ideal for dynamic teams requiring secure, flexible access.
👉 Learn how PassCypher transforms security for businesses of all sizes: Read more.
Why Businesses Need a Passwordless Password Manager?
- Simplify Access: Say goodbye to complex credentials and reduce login frustrations.
- Enhance Security: Protect against phishing, keyloggers, and other cyber threats.
- Boost Productivity: With one-click simplicity, employees can focus on what matters
Ready to secure your enterprise? Get started with PassCypher today!
Explore More Digital Security Insights
🔽 Discover related the other articles on cybersecurity threats, advanced solutions, and strategies to protect sensitive communications and critical systems.
The Ultimate Passwordless Password Manager
In today’s digital landscape, where cyber threats grow more sophisticated, having a robust password manager is essential. The PassCypher HSM PGP transforms access control with seamless, secure, and innovative management.
How PassCypher HSM PGP Redefines Passwordless Security
PassCypher HSM PGP introduces groundbreaking advancements that redefine what it means to be a Passwordless Password Manager. By seamlessly combining security, efficiency, and compatibility, PassCypher stands out as the most innovative solution for today’s evolving cybersecurity landscape.
Advanced Technologies Empowering Passwordless Security
- Segmented Key Technology: Unlike traditional multi-factor authentication (MFA), PassCypher uses segmented keys that eliminate reliance on vulnerable servers. This ensures enhanced data protection by distributing the key components securely.
- Complete Offline Operation: PassCypher operates entirely without servers or centralized databases. This serverless, databaseless design ensures total data sovereignty and eliminates risks associated with cloud dependency.
- Quantum-Resistant Encryption: Equipped with AES-256 CBC encryption, PassCypher is built to resist quantum computing threats, offering unparalleled security for decades to come.
- Universal Compatibility: Designed to work seamlessly with existing websites, applications, and systems, PassCypher eliminates the need for updates, plugins, or specialized integrations.
- Integrated Cryptographic Tools: Seamlessly generate secure SSH key pairs and AES-256 encryption keys, empowering professionals to maintain secure workflows with ease.
Revolutionary Auto-Login and Step-Up Authentication
PassCypher HSM PGP redefines secure access with its two-step and one-click authentication method. This cutting-edge approach combines speed, simplicity, and end-to-end security, streamlining the login process like never before.
How It Works:
PassCypher offers two streamlined methods for different security scenarios:
- Two-Step Auto-Login:
- Step 1: The user clicks the small arrow icon next to the login field. This action automatically completes and validates the username or email securely.
- Step 2: After validation, the user clicks the arrow icon next to the password field to auto-fill and validate the password, completing the login.
This method is ideal for platforms requiring both username and password for access.
- One-Click Authentication:
For services requiring only one credential (e.g., username or email), a single click on the arrow icon fills and validates the required field instantly.
Key Advantages:
- Ultra-Simple Workflow: A seamless process requiring just one or two clicks ensures effortless access without sacrificing security.
- End-to-End Security: Credentials are decrypted exclusively in volatile memory during auto-fill. The encrypted containers stored on the hardware remain untouched and fully secure.
- No Data Exposure: Credentials are never stored or transmitted in plaintext, eliminating risks of interception or compromise.
Why It Matters:
PassCypher HSM PGP revolutionizes the traditionally cumbersome two-factor authentication process by automating it with segmented key technology. All operations are conducted offline within encrypted containers, ensuring absolute protection against phishing, brute-force attacks, and other cyber threats.
Result: A streamlined, ultra-secure user experience that takes seconds to complete while safeguarding your most sensitive information.
Validate Password Strength in Real Time with Entropy Metrics
PassCypher HSM PGP includes a Shannon-based entropy gauge, enabling users to assess password strength in real time. This gauge calculates the entropy of each password, ensuring compliance with security best practices and protecting against brute-force attacks.
Why It Matters:
- Robust Passwords: The entropy gauge ensures that passwords meet the highest security standards by evaluating their randomness and complexity.
- Proven Methodology: Based on the renowned Shannon entropy formula, this feature relies on mathematically sound principles to assess and enforce password security.
- User-Friendly Design: Provides clear visual feedback, guiding users to create stronger passwords effortlessly.
This innovative feature positions PassCypher as a forward-thinking solution for password security.
Advanced Auto-Login and Step-Up Authentication
Streamlined Two-Step Authentication for Modern Needs
PassCypher HSM PGP revolutionizes security workflows by integrating Step-Up Authentication, a widely used method that adds an extra layer of protection. Here’s how it works:
- The login field is completed and validated first.
- Only after successful validation does the password field appear, allowing the user to input and validate the password separately.
With PassCypher, these steps are automated using segmented key technology:
- Auto-Fill Efficiency: Users simply click the auto-fill arrow twice—once for the login and once for the password—streamlining the process while maintaining enterprise-grade 2FA compatibility.
- Enhanced Security: This dual-step process aligns with modern authentication protocols while preserving the simplicity of passwordless workflows.
By merging ease of use with robust security, PassCypher bridges the gap between traditional 2FA and the future of passwordless authentication, offering a solution that meets the needs of both individuals and enterprises.
SSH Key Management for Developers
A New Standard in Secure Authentication and Encryption
PassCypher HSM PGP sets a new benchmark for passwordless security by integrating essential tools for secure authentication and encryption directly into its platform. These built-in capabilities simplify the creation and management of cryptographic keys, ensuring robust protection for sensitive systems and services.
SSH Key Pair Creation:
Generate password-protected SSH key pairs with an integrated real-time entropy gauge based on Shannon’s formula. This ensures the creation of strong, secure keys resistant to phishing, brute-force attacks, and unauthorized access attempts.
AES-256 Encryption Key Generation:
Easily create AES-256 CBC encryption keys in `.pem` format, secured by passwords. This feature provides an additional layer of flexibility for encrypting sensitive data and securing communications, meeting enterprise-grade security standards.
Secure SSH Key Authentication with Entropy Validation:
PassCypher enhances security by ensuring that passwords used for securing SSH key pairs meet the highest security standards. The built-in Shannon-based entropy gauge provides real-time feedback, empowering developers and IT professionals to create robust, uncrackable passwords with confidence.
Why These Features Matter:
- Simplified Security: All essential cryptographic tools are available within a single platform, eliminating the need for additional software or integrations.
- Enhanced Productivity: Streamline workflows by unifying secure key creation, passwordless access management, and advanced encryption tools in the same intuitive interface.
- Future-Ready Design: PassCypher’s built-in tools are tailored to meet the evolving needs of professionals and organizations demanding cutting-edge security solutions for tomorrow’s challenges.
Key Features of PassCypher HSM PGP as a Passwordless Password Manager
- Zero Trust and Zero-Knowledge Architecture: Data remains encrypted and inaccessible to unauthorized parties.
- Segmented Key Sharing: Enables secure collaboration without compromising data integrity.
- Eco-Friendly Design: Serverless architecture reduces energy consumption while aligning with sustainability goals.
- Universal Compatibility: Functions with existing systems, requiring no updates or prior integrations.
- Quantum-Resistant Encryption: AES-256 encryption ensures protection against current and future threats.
- Built-in Cryptographic Tools: Generate SSH key pairs and AES-256 encryption keys with ease, empowering users to manage security workflows directly within the PassCypher platform.
- Customizable Algorithms: Choose from RSA (2048, 3072, 4096), ECDSA (256, 384, 521), and ed25519 to tailor encryption strength and meet specific security requirements.
- Password Protection with Entropy Control: Ensure robust security with a real-time Shannon-based entropy gauge, allowing users to create and validate strong passwords based on proven mathematical principles.
PassCypher HSM PGP vs. FIDO2/Passkeys
While both PassCypher HSM PGP and FIDO2/Passkeys aim to eliminate traditional passwords, their architectures differ significantly:
| Feature | PassCypher HSM PGP | FIDO2/Passkeys |
|---|---|---|
| Cryptographic Key Strength | AES-256, quantum-resistant | AES-256 (non-quantum safe) |
| Server Dependence | Fully offline | Relies on cloud servers |
| Compatibility | Universal | Platform-specific |
| Data Sovereignty | Full local control | Cloud-based storage |
| Ease of Use | One-click, segmented keys | Requires integration |
PassCypher surpasses FIDO2 by offering offline operation, universal compatibility, and quantum-resistant encryption.
Visual Comparison
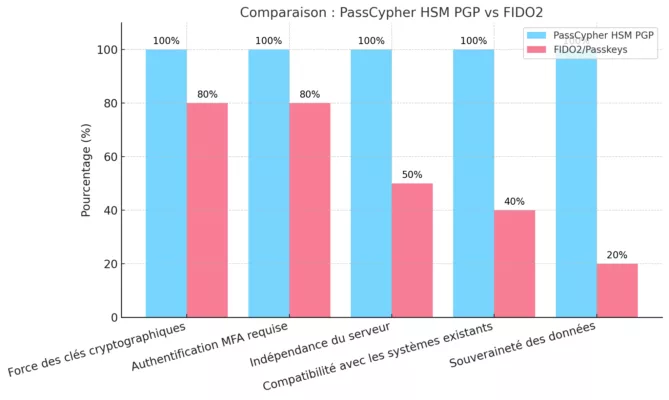
This chart highlights how PassCypher outperforms FIDO2 on critical criteria like compatibility, data sovereignty, and cryptographic strength.
Tailored Solutions for Every Industry
PassCypher adapts to the unique challenges of various industries:
- Financial Services: Prevent targeted attacks with serverless design and quantum-resistant encryption.
- Healthcare: Ensure compliance with data privacy laws such as GDPR and HIPAA.
- Technology: Protect intellectual property and sensitive data from emerging quantum threats.
- Sovereign and Regalian Needs: With its serverless and databaseless architecture, PassCypher ensures full data sovereignty, end-to-end anonymization, and compliance with national security standards for government agencies and critical infrastructure.
Why PassCypher Outperforms Traditional and FIDO2 Passwordless Solutions
PassCypher HSM PGP revolutionizes cybersecurity with its unique databaseless and serverless architecture. Unlike traditional password managers and FIDO2/Passkeys, it offers unmatched security, universal compatibility, and compliance with global regulations like GDPR and NIS2—all while maintaining eco-friendly efficiency.
| Criterion | PassCypher HSM PGP | FIDO2/Passkeys | Traditional Managers |
|---|---|---|---|
| Server Independence | Fully serverless | Requires cloud servers | Requires cloud servers |
| Data Sovereignty | Full local control | Cloud-dependent | Centralized storage |
| Quantum-Resistant Keys | AES-256 CBC + segmented keys | Limited protection | No quantum resistance |
| Ease of Use | One-click, secure logins | Integration-dependent | Manual input |
| Environmental Impact | Reduced energy use, no data centers | High due to cloud reliance | High due to cloud reliance |
| Compliance (GDPR/NIS2) | Simplified by offline design | Complex, cloud-based storage | Requires additional safeguards |
Key Advantages of PassCypher HSM PGP
-
Complete Server Independence
PassCypher operates entirely offline, eliminating reliance on cloud servers or centralized databases. This ensures total data sovereignty and enhances resilience against server outages or cyberattacks targeting cloud infrastructures.
-
Universal Compatibility
PassCypher works seamlessly with both legacy and modern systems without requiring updates, prior integrations, or ecosystem-specific dependencies. Unlike FIDO2/Passkeys, it delivers immediate functionality across diverse IT environments.
-
Enhanced Security with Quantum Resistance
- PassCypher Combines Advanced Encryption with Patented Segmented Key Technology
PassCypher HSM PGP delivers unmatched security by combining AES-256 CBC encryption with a patented segmented key system. This innovative design generates encryption keys by concatenating multiple cryptographic segments stored independently on secure hardware. As a result, it creates a robust defense mechanism that stops unauthorized access, even in the face of quantum computing advancements. - Why Quantum Computers Struggle to Break PassCypher’s Security
While quantum algorithms like Grover’s can theoretically speed up brute-force attacks, real-world limitations significantly reduce their effectiveness. Grover’s steps cannot be parallelized, and quantum hardware remains resource-intensive. Additionally, PassCypher’s segmented key design introduces extra layers of complexity. Each segment functions independently, ensuring the combined key is far more challenging to compromise than traditional AES-256 implementations.
👉 Learn more from the NIST Post-Quantum Cryptography FAQ: NIST FAQ - Patented Technology Redefines Security Standards
Unlike conventional encryption methods, PassCypher’s patented system secures encryption keys by storing them in distinct segments across multiple devices. These segments are concatenated to form a final encryption key, adding an extra level of defense that surpasses the standard AES-256 algorithm. This approach not only withstands classical attacks but also introduces a groundbreaking method to mitigate quantum threats effectively.
👉 Explore additional resources: The Quantum Resistance of AES-256 and IJARCS AES-256 Quantum Resistance - Future-Ready for Evolving Threats
PassCypher’s segmented key technology is specifically designed to address current and future cybersecurity challenges. This system strengthens enterprise-level protection while ensuring compliance with global standards like GDPR and NIS2. With a focus on scalability and adaptability, PassCypher offers peace of mind for organizations looking to safeguard their most sensitive data.
- PassCypher Combines Advanced Encryption with Patented Segmented Key Technology
-
Simplified Regulatory Compliance
The databaseless architecture of PassCypher aligns perfectly with GDPR, NIS2, and similar global regulations by storing all data locally on user devices. This approach eliminates risks tied to cloud-based breaches and simplifies regulatory audits.
-
Streamlined User Experience
With one-click authentication powered by segmented key technology, PassCypher reduces login friction and accelerates secure access, improving productivity for enterprise teams.
-
Uncompromised Sovereignty
PassCypher guarantees complete independence by operating without servers, databases, or account creation. This aligns with the highest standards for national and enterprise-level data sovereignty, making it ideal for critical industries and government entities.
-
Eco-Friendly and Energy Efficient
PassCypher’s serverless architecture reduces reliance on energy-intensive data centers, minimizing its carbon footprint. This makes it a sustainable cybersecurity solution for businesses prioritizing environmental responsibility.
-
One-Click Authentication
PassCypher simplifies secure access for employees and teams, reducing login times while ensuring robust protection.
-
Seamless Auto-Login and Auto-Fill with Two-Step Validation
PassCypher HSM PGP enhances productivity with its auto-login and auto-fill functionality, streamlining access to online accounts while maintaining robust security:
- Two-Step Validation Simplified: This feature mimics common two-factor authentication (2FA) workflows, where the user first validates their login credentials (username) and then their password. PassCypher automates this process with a two-click system, making it both fast and secure.
- Visual Assistance: A small arrow icon appears in login fields, guiding the user to complete the process effortlessly. Click once to fill in the username, and again to auto-fill and validate the password.
- Enhanced Security Against Phishing: With sandbox validation of URLs and seamless segmented key authentication, users are safeguarded against common online threats.
Key Takeaways:
- Advanced Patented Technology: PassCypher’s segmented key design creates an encryption system that is resilient to both classical and quantum threats.
- Proven Quantum Resistance: Backed by research from NIST and other credible sources, PassCypher incorporates AES-256 encryption to ensure long-term security.
- Optimized for Enterprises: The system offers a seamless, scalable solution tailored to meet the needs of businesses seeking durable and compliant cybersecurity strategies.
Comparative Table: PassCypher HSM PGP vs. FIDO2/Passkeys
| Criterion | PassCypher HSM PGP | FIDO2/Passkeys |
|---|---|---|
| Server Independence | Yes | No |
| Data Sovereignty | Fully local | Cloud-dependent |
| Compatibility | Universal, works with all systems | Requires integrations |
| Quantum-Resistant Encryption | Yes | No |
| Ease of Deployment | Immediate, no updates required | Requires ecosystem support |
Streamlined Visual Comparison
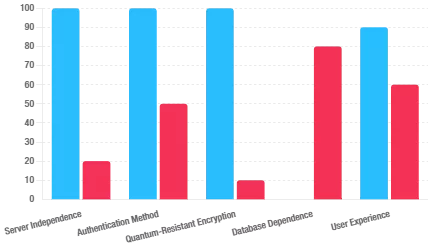
A consolidated view comparing the critical features of PassCypher HSM PGP and traditional password managers highlights its unique strengths in security, independence, and resilience.
Discover how PassCypher HSM PGP can revolutionize your cybersecurity infrastructure.
Contact us for tailored enterprise solutions today!
Technical Superiority: Segmented Encryption and Passwordless Serverless Design
Why Segmented Encryption Matters
PassCypher HSM PGP introduces two segmented keys, which are concatenated to form a final AES-256 encryption key. This method ensures:
- Elimination of weak passwords: No user-generated passwords mean brute-force attacks are obsolete.
- Mitigation of centralized vulnerabilities: Serverless design avoids database breaches.
Key Advantages:
- Quantum-Resistant Security: AES-256 protects against emerging quantum threats.
- Zero Cloud Reliance: All operations are localized, ensuring total privacy.
- One-Click Authentication: Simplifies access with segmented keys.
Zero Trust and Zero-Knowledge Architecture in a Passwordless Password Manager
PassCypher HSM PGP embraces the foundational principles of a passwordless password manager. Its zero trust and zero-knowledge architecture not only ensure that data remains encrypted but also make it inaccessible to all unauthorized parties—even the system itself. This design enforces strict verification protocols for every interaction, eliminating trust assumptions and guaranteeing data integrity.
Passwordless Authentication and Zero Trust Architecture
Passwordless authentication is more than just a trend—it’s the future of secure access. PassCypher HSM PGP integrates a Zero Trust Architecture that demands strict verification for every access attempt. By eliminating assumptions of trust, it ensures data remains encrypted and inaccessible to unauthorized parties. Transitioning to passwordless solutions not only strengthens security but also simplifies workflows, making your systems more efficient.
Centralized Security Without SSO
Traditional single sign-on systems often become points of vulnerability. PassCypher redefines centralized security by introducing segmented key sharing, which is a critical feature of its passwordless password manager. This ensures robust management while eliminating the risks of centralized failure points, providing seamless yet secure access.
Segmented Key Sharing for Passwordless Password Manager
Collaboration without compromise. With segmented key sharing, PassCypher allows authorized users to securely access encrypted data while maintaining strict compartmentalization. Unique key pairs not only ensure secure collaboration but also align perfectly with the principles of a passwordless password manager. This approach demonstrates how PassCypher HSM PGP surpasses traditional password managers by offering unparalleled security.
Segmented Key Sharing: Essential for Modern Passwordless Password Managers
Segmented key sharing isn’t just a feature—it’s the cornerstone of modern passwordless password managers. PassCypher HSM PGP uses segmented keys stored on separate devices, ensuring data remains uncompromised even in the face of advanced threats. This approach enables secure collaboration, granting access only to authorized users while maintaining strict data compartmentalization. By adopting segmented key sharing, businesses can strengthen security without sacrificing flexibility.
Hardware-Based Licensing for Enhanced Security
PassCypher’s hardware-based licensing breaks away from identity-driven models. Users can securely share a single device while maintaining unique segmented keys, offering unmatched flexibility for dynamic, multi-user environments. Moreover, this innovative approach aligns with the ethos of a passwordless password manager by providing both security and simplicity.
Advanced Container and Key Management
Most importantly, PassCypher supports virtually unlimited secure storage across USB drives, SSDs, and cloud solutions. Each container is pre-encrypted using AES-256, offering unparalleled protection for sensitive information. This flexibility cements its place as a leading passwordless password manager for organizations needing advanced data management. For those seeking a guide on implementing passwordless security solutions for small businesses, PassCypher offers an excellent starting point.
Eco-Friendly Design: A Sustainable Approach to a Passwordless Password Manager
In a world where sustainability is key, PassCypher takes the lead with its serverless architecture. By eliminating reliance on energy-intensive data centers, it not only offers an eco-friendly passwordless password manager but also prioritizes both security and environmental responsibility. The PassCypher HSM PGP is designed with sustainability in mind. With its energy-efficient serverless architecture, PassCypher champions sustainable security without compromising on protection.
Passwordless Authentication Redefined
The foundation of PassCypher’s innovation lies in eliminating traditional passwords. By eliminating traditional credentials, it replaces passwords with AES-256 encrypted containers and segmented keys. As a premier As a leader in password-free access solutions, it guarantees password manager, it ensures:
- No Typing Risks: Keyloggers and screen captures are rendered obsolete.
- Silent, Secure Authentication: Seamless processes with no audible or visible risks.
- Instant Access: Single-click authentication without compromising security.
These features collectively redefine what it means to be a passwordless password manager, showcasing how it simplifies security while surpassing traditional methods.
Protection Against Common Threats
PassCypher neutralizes a wide range of cyber threats, including phishing, replay attacks, and keylogging. By encrypting data in containers and, at the same time, preventing plaintext password exposure, it delivers multi-layered protection. That underscores its status as a top-tier passwordless cybersecurity solution. These benefits highlight the advantages of a passwordless password manager in modern cybersecurity.
Flexible Licensing Options for the Leading Passwordless Password Manager
Furthermore, PassCypher’s innovative pricing model ties licenses to hardware, thereby providing both flexibility and anonymity. Whether for short-term use or long-term projects, its hardware-based licensing makes it the most adaptable passwordless password manager available.
Table: Sliding scale of fees
| License Type | 1 to 9 licenses | 10 to 49 licenses | 50 to 99 licenses | 100 to 249 licenses | 250 and over |
| Day (7 €/day) | 7 € | €6.50 | 6 € | €5.50 | On quote |
| Week (10 €/week) | 10 € | 9 € | €8.50 | 8 € | On quote |
| Month (15 €/month) | 15 € | €13.50 | €12.50 | 12 € | On quote |
| One Year (129 €/year) | 129 € | 119 € | 109 € | 99 € | On quote |
| Two Years (€199/2 years) | 199 € | 179 € | 169 € | 159 € | On quote |
Tailored to meet unique business requirements, custom licenses enhance the versatility of this passwordless password manager.
Eliminate Servers: The Future of Password Management
In a world where centralized data storage creates significant vulnerabilities, PassCypher HSM PGP takes a revolutionary approach by operating without servers or databases. Its databaseless and serverless architecture sets a new standard for secure and resilient cybersecurity solutions.
Key Advantages of Databaseless and Serverless Design:
- Elimination of Central Points of Failure
- Without relying on centralized databases or servers, PassCypher removes critical failure points. This ensures uninterrupted functionality even during server outages or targeted cyberattacks.
- Simplified Regulatory Compliance
- By storing all data locally on the user’s device, PassCypher makes compliance with stringent regulations like GDPR and NIS2 straightforward. No cross-border data transfer means enhanced privacy and sovereignty.
- Enhanced Resilience Against Cyber Threats
- Traditional centralized systems are frequent targets for cyberattacks, including ransomware and database breaches. PassCypher’s decentralized design eliminates these risks, safeguarding sensitive data from exploitation.
- Uncompromised User Privacy
- With no external databases or servers to access, user data remains entirely private, ensuring that even service providers cannot intercept sensitive information.
- Performance Benefits
- A databaseless design eliminates the need for database queries, delivering faster authentication and encryption processes for a seamless user experience.
Why It Matters
The serverless and databaseless architecture of PassCypher HSM PGP isn’t just an innovation; it’s a necessity in today’s cybersecurity landscape. By removing reliance on external infrastructure, PassCypher provides businesses and individuals with unparalleled security, privacy, and performance.
This serverless, databaseless architecture positions PassCypher HSM PGP as the ideal solution for individuals and enterprises seeking the best cybersecurity solutions for 2025.
Comparison with popular password managers
Before diving into the comparison, here’s an overview: The following table highlights the standout features of PassCypher HSM PGP compared to other password managers. It demonstrates how PassCypher sets a new benchmark in passwordless security.
Technical Features
| Feature | PassCypher HSM PGP | LastPass | Dashlane | 1Password | Bitwarden |
|---|---|---|---|---|---|
| Server Independence | Fully offline and serverless | Server-dependent | Server-dependent | Server-dependent | Server-dependent |
| Authentication Method | Segmented key-based MFA | Password/Biometric | Password/Biometric | Password/Biometric | Password/Biometric |
| Security Framework | AES-256 + sandbox validation | AES-256, password encryption | AES-256, password encryption | AES-256, password encryption | AES-256, password encryption |
| Quantum-Resistant Encryption | Yes | No | No | No | No |
| Database Dependence | None—databaseless architecture | Centralized database storage | Centralized database storage | Centralized database storage | Centralized database storage |
Key Takeaways
The technical superiority of PassCypher HSM PGP is clear—it operates entirely offline, ensuring full independence from servers while offering quantum-resistant encryption. With no database dependency, it guarantees unmatched security for enterprises and individuals alike.
User Experience and Flexibility
| Feature | PassCypher HSM PGP | LastPass | Dashlane | 1Password | Bitwarden |
|---|---|---|---|---|---|
| User Experience | One-click, segmented keys | Manual password input | Manual password input | Manual password input | Manual password input |
| Data Sovereignty | Full local control (no third-party ties) | Tied to servers | Tied to servers | Tied to servers | Tied to servers |
| Eco-Friendly Design | Serverless, reduced energy consumption | Requires cloud servers | Requires cloud servers | Requires cloud servers | Requires cloud servers |
| Pricing Model | Flexible, hardware-based: licenses for a day, week, month, or year | Subscription-based | Subscription-based | Subscription-based | Subscription-based |
| Protection Against Keylogging | Full (no password entry required) | Partial (relies on input security) | Partial (relies on input security) | Partial (relies on input security) | Partial (relies on input security) |
| Multi-User Flexibility | Yes—unlimited users per hardware license | No—licenses tied to individual users | No—licenses tied to individual users | No—licenses tied to individual users | No—licenses tied to individual users |
Key Takeaways
PassCypher redefines user convenience with one-click authentication and segmented key-sharing. Its hardware-based licensing model and eco-friendly design make it a leader in passwordless security solutions for businesses and individuals in 2025.
How does a databaseless architecture simplify compliance?
A databaseless architecture eliminates the risks associated with centralized storage by ensuring that all sensitive data is stored locally on the user’s device. This design minimizes the attack surface for data breaches, making it easier for businesses to comply with regulations such as GDPR and NIS2. Additionally, it simplifies audit and reporting processes by removing complex data management systems, ensuring total data sovereignty for enterprises.
Why PassCypher HSM PGP’s Pricing Model Stands Out
PassCypher’s revolutionary hardware-based pricing model is decoupled from personal or organizational identities, ensuring anonymity and flexibility, key aspects of a passwordless password manager. Users can purchase licenses by the day, week, month, or year, with no financial commitments. Unlike competitors that tie licenses to individual users, PassCypher’s licenses are bound to the hardware, allowing multiple people to securely share the same device. This innovative pricing model supports an infinite number of users, making it ideal for teams or enterprises needing scalable cybersecurity solutions. With no need for recurring subscriptions and the ability to buy short-term licenses, PassCypher offers unmatched affordability for individuals and businesses alike.
- Unlimited Users: Multiple users can securely share a single license.
- No Engagement: Flexible durations adapt to any need without long-term commitments.
- Transparent Costs: Simple, hardware-bound pricing eliminates hidden fees.
This ensures that the pricing model directly ties into the comparison, highlighting why PassCypher offers greater flexibility and affordability compared to competitors. Choose the placement based on where you’d like to emphasize the pricing model’s role in differentiating PassCypher.
Key Insights: Why PassCypher HSM PGP Stands Out in 2025
Server Independence
Unlike competitors such as LastPass or Dashlane, which rely on cloud infrastructure, PassCypher HSM PGP operates entirely offline. Its serverless architecture guarantees total data sovereignty, eliminating risks associated with server breaches, downtimes, or data leaks.
Advanced Authentication
PassCypher employs segmented key-based multi-factor authentication (MFA). This approach offers superior security compared to traditional password or biometric methods, providing robust protection for sensitive data without relying on fragile systems.
Quantum-Resistant Security
Designed for future threats, PassCypher incorporates encryption technologies resilient to quantum computing attacks—a critical feature missing in most competitors. This ensures long-term security for individuals and enterprises.
Streamlined, Secure Access for Teams and Enterprises
PassCypher redefines usability by replacing manual password input with one-click authentication using segmented keys. This approach not only reduces user friction but also eliminates keylogging risks, offering a seamless and secure experience. Balancing security and usability is critical for teams and enterprises. PassCypher achieves this balance with a seamless, one-click authentication process, simplifying secure access across the board.
Hardware-Based Licensing for SMEs
PassCypher’s flexible hardware licenses provide affordable, scalable solutions tailored for small and medium enterprises (SMEs). This ensures secure, streamlined access without breaking budgets, making it an ideal choice for organizations of all sizes.
Database-Free Design
PassCypher is a truly databaseless solution, storing all user data locally. In contrast, traditional password managers like 1Password and Bitwarden rely on centralized databases, which are vulnerable to breaches. With PassCypher, there are no central points of failure, ensuring enhanced privacy and security.
Eco-Friendly and Sustainable
With its serverless architecture, PassCypher consumes significantly less energy compared to cloud-based solutions that require constant server operations. This makes it a sustainable choice aligned with modern environmental goals.
Unparalleled Sovereignty
With no reliance on servers or databases, PassCypher ensures complete independence. This is particularly advantageous for businesses and governments prioritizing data sovereignty, regulatory compliance, and national security. The end-to-end anonymity it offers makes it uniquely positioned for critical industries and sensitive operations.
End-to-End Anonymity
PassCypher delivers complete anonymity by eliminating the need for user accounts, personal information, or master passwords. This approach ensures unparalleled privacy and prevents any third-party access to sensitive data, setting a new standard in the industry.
Supports NIS2 Compliance for Essential and Important Entities
The NIS2 Directive sets stringent cybersecurity requirements for essential and important entities across the European Union, including sectors like finance, healthcare, energy, and telecommunications. PassCypher HSM PGP addresses these needs with:
- Robust Encryption: AES-256 encryption and segmented key authentication meet the directive’s requirements for strong cybersecurity measures.
- Serverless Design: Its fully offline architecture eliminates vulnerabilities associated with centralized servers and databases, ensuring resilience against cyber threats.
- Data Sovereignty: By operating entirely locally, PassCypher simplifies compliance with NIS2’s focus on securing sensitive data.
- Simplified Risk Management: PassCypher reduces the complexity of incident response and regulatory reporting through its zero-trust architecture and lack of centralized failure points.
For organizations striving to meet NIS2 compliance, PassCypher HSM PGP offers a future-ready, secure solution that aligns with the directive’s key objectives.
The Impact of PassCypher’s Unique Features on Modern Cybersecurity
PassCypher HSM PGP’s unique combination of serverless, database-free design, quantum-resistant encryption, and end-to-end anonymity ensures that it stands apart from traditional password managers. Whether you’re a business seeking the best passwordless solutions for enterprises or an individual prioritizing secure authentication without relying on centralized databases, PassCypher offers an unmatched cybersecurity solution.
This updated section highlights databaseless architecture, server independence, and the innovative features that make PassCypher the most advanced passwordless password manager for 2025.
With cybersecurity evolving rapidly, every feature of PassCypher is designed to address the challenges of today’s digital landscape. Let’s explore how these innovations transform modern cybersecurity for businesses and individuals alike.
Future-Proof Quantum-Resistant Encryption
PassCypher redefines security by integrating quantum-resistant AES-256 CBC encryption with its patented segmented key technology. This innovative combination delivers unparalleled protection against current and emerging threats, including quantum computing. Designed for scalability and durability, PassCypher ensures your data remains secure for decades, setting a new standard for passwordless password managers in 2024 and beyond.
Preparing for the Quantum Computing Era
PassCypher’s advanced encryption and segmented key approach provide a robust defense against quantum threats. While algorithms like Grover’s aim to expedite brute-force attacks, real-world limitations—such as the inability to parallelize steps effectively—significantly reduce their impact. PassCypher takes this a step further by introducing additional layers of complexity with segmented key design, making unauthorized access exponentially more challenging.
Learn More About Quantum-Resistant Encryption
Explore detailed insights on protecting data against quantum threats:
- 👉 Quantum Computing Risks to AES and RSA Encryption
- 👉 How to Create and Protect Quantum-Resistant Passwords
Why Passwordless Password Managers Are the Future of Cybersecurity
Passwordless password managers are the future of cybersecurity, and PassCypher HSM PGP is leading the way. By eliminating traditional credentials, it neutralizes vulnerabilities like phishing and brute-force attacks. Moreover, its quantum-resistant encryption ensures long-term protection against emerging threats. With PassCypher, organizations can confidently transition to a security model that anticipates and mitigates future risks, providing unparalleled peace of mind.
Future-Proof Security Against Quantum Computing Threats
As quantum computing evolves, traditional encryption faces new risks. PassCypher addresses these challenges with innovative, quantum-resistant technologies.
👉 Understand the impact of quantum computing on traditional encryption.
👉 Discover best practices for quantum-resistant password creation.
Resilience Against Ransomware Attacks
Ransomware attacks pose a critical threat to modern businesses. PassCypher ensures data security through AES-256 CBC encrypted containers and its serverless architecture, making sensitive information inaccessible to attackers.
- Encrypted Containers: Protect critical data from unauthorized encryption or tampering.
- Serverless Architecture: Eliminates centralized vulnerabilities, ensuring continuity even during attacks.
👉 Learn more about resilience against ransomware.
Passwordless Security Redefined with PassCypher
PassCypher HSM PGP fully embraces passwordless principles by replacing traditional passwords with AES-256 encrypted containers and segmented keys. This innovative approach eliminates the need for users to manage passwords while enhancing security and maintaining simplicity.
PassCypher HSM PGP vs. FIDO2/Passkeys: Key Compatibility Advantages
PassCypher HSM PGP stands out by offering universal compatibility with existing systems, requiring no prior integration or updates, unlike FIDO2/Passkeys. This flexibility ensures seamless deployment across all environments without ecosystem-specific constraints.
Distinct Advantages:
- Immediate Functionality: No dependency on website or application updates.
- Universal Compatibility: Works with legacy and modern systems alike.
Unmatched Data Sovereignty
PassCypher HSM PGP ensures complete control over cryptographic keys and user data through its offline, serverless design. Unlike FIDO2/Passkeys, which often rely on cloud storage, PassCypher eliminates third-party dependencies, simplifying compliance with regulations like GDPR.
Core Benefits:
- Local Key Storage: Cryptographic keys are stored entirely on the user’s device.
- Regulatory Compliance: No data crosses borders, ensuring privacy and sovereignty.
Enhanced User Experience
PassCypher combines strong security with ease of use:
- One-Click Authentication: Simplifies secure access for users and teams.
- CAPTCHA v3 Compatibility: Ensures smooth workflows without unnecessary interruptions.
Comparative Table: PassCypher vs. FIDO2
| Criterion | FIDO2 Passkeys | PassCypher HSM PGP |
|---|---|---|
| Server Independence | No | Yes |
| Data Sovereignty | Cloud-dependent | Fully local |
| Compatibility | Requires integration | Immediate and universal |
By combining segmented key technology with complete offline functionality, PassCypher HSM PGP surpasses traditional passwordless solutions, providing an unmatched blend of security, compatibility, and sovereignty.
In a world where traditional passwords are increasingly vulnerable, PassCypher introduces a groundbreaking approach to redefine access control. Discover how this passwordless solution sets new benchmarks in secure authentication.
How Does PassCypher HSM PGP, the Most Innovative Passwordless Manager 2025, Work
Understanding how PassCypher HSM PGP operates highlights its status as a premier passwordless password manager. The system leverages segmented keys stored securely on hardware, enabling seamless authentication and encryption. By eliminating the need for traditional credentials, users experience a simplified yet secure process. Explore how PassCypher HSM PGP works to see its innovative technology in action.
Explore how PassCypher can revolutionize your business. Contact us for enterprise solutions.
Why It Matters
PassCypher HSM PGP isn’t just another product; it’s a transformative passwordless password manager. By combining advanced encryption, sustainability, and user-centric innovation, it sets a new standard for data security. Experience the future of cybersecurity today.
What is PassCypher HSM PGP, and why is it a Passwordless Password Manager?
In addition to replacing traditional passwords, PassCypher HSM PGP introduces advanced segmented key authentication and AES-256 encrypted containers. Unlike traditional solutions, it operates with a databaseless and serverless design, ensuring robust security and complete data sovereignty.
How does PassCypher HSM PGP outperform traditional password managers?
PassCypher HSM PGP surpasses traditional password managers in several ways:
- It eliminates password vulnerabilities by replacing them with segmented key authentication.
- Moreover, it operates entirely offline, which ensures total data sovereignty.
- It simplifies access with single-click authentication.
In comparison to popular password managers, PassCypher provides unmatched security and independence.
Why is segmented key technology crucial for modern cybersecurity?
Segmented key technology divides encryption keys into parts stored on separate devices. Consequently, this prevents a single point of failure and enhances data protection. This innovation ensures PassCypher HSM PGP stands out as a leader among passwordless solutions.
How can small businesses implement a passwordless password manager cybersecurity solution?
To integrate PassCypher HSM PGP:
- Transition from conventional password managers to segmented key-based systems.
- Train your team on how to use hardware-based authentication.
- Gradually replace outdated methods with PassCypher’s eco-friendly and scalable solutions.
This practical guide simplifies how to implement a passwordless password manager effectively.
For a detailed guide, explore our Practical Guide to Passwordless Security Solutions for Small Businesses.
What are the key advantages of a passwordless password manager?
A passwordless password manager like PassCypher HSM PGP offers:
- Enhanced protection against phishing and keylogging.
- Streamlined user experiences with single-click access.
- Full independence from cloud servers.
- Scalability for small businesses and enterprises alike.
These features make it one of the most advanced cybersecurity solutions for 2025.
How does PassCypher protect against common cyber threats?
PassCypher protects against:
- Phishing attacks: By validating URLs within a secure sandbox.
- Replay attacks: Through encrypted segmented key sharing.
- Keylogging risks: By removing the need for typed passwords.
Its robust defense mechanisms solidify PassCypher’s position as the leading passwordless solution for enterprises.
What licensing options does PassCypher offer?
PassCypher provides flexible plans, including:
- Ephemeral Licenses: Day (7 €), Week (10 €), Month (15 €).
- Annual Licenses: One Year (129 €), Two Years (199 €).
- Custom Licenses: Designed for unique business needs.
This flexibility ensures businesses can scale their passwordless password manager effortlessly.
What makes PassCypher eco-friendly?
PassCypher’s serverless design reduces reliance on energy-intensive data centers. By using local hardware and segmented keys, it minimizes its environmental impact, combining sustainability with advanced passwordless authentication methods.
How does a databaseless architecture simplify compliance?
A databaseless architecture eliminates the risks associated with centralized storage by ensuring that all sensitive data is stored locally on the user’s device. This design minimizes the attack surface for data breaches, making it easier for businesses to comply with regulations such as GDPR and NIS2. Additionally, it simplifies audit and reporting processes by removing complex data management systems, ensuring total data sovereignty for enterprises.
Which industries benefit most from passwordless cybersecurity?
Industries such as finance, healthcare, technology, and government gain the most from PassCypher’s passwordless framework. Its advanced segmented key technology ensures optimal security, even for enterprises handling sensitive data.
How does PassCypher prepare for quantum computing threats?
PassCypher uses AES-256 CBC encryption and segmented keys to remain resilient against quantum computing attacks. This forward-thinking approach makes it one of the most advanced cybersecurity solutions to protect enterprise data in the future.
Why should businesses adopt Passwordless Password Manager in 2025?
- Robust defenses against emerging threats.
- Simplified user workflows, improving productivity.
- Future-proof encryption technologies for long-term security.
PassCypher demonstrates why it is the best choice for businesses aiming to transition to secure authentication solutions.
What is PassCypher HSM PGP, and why is its database-free design significant?
PassCypher HSM PGP is a passwordless password manager that operates without relying on any databases. By storing all information locally, it ensures maximum privacy, security, and performance.
How does PassCypher’s database-free design protect against cyber threats?
With no centralized database to target, PassCypher eliminates vulnerabilities associated with server breaches, ensuring unmatched resilience against cyberattacks.
What are the benefits of a databaseless and serverless architecture?
PassCypher’s zero-database and no-server architecture ensures:
- No central points of failure: Resilience against server outages and database breaches.
- Enhanced compliance: Full alignment with regulations like GDPR, thanks to its privacy-first design.
- Improved performance: Faster, localized encryption and authentication processes.
- Eco-friendly security: Minimal energy consumption without reliance on cloud-based infrastructures.
Why is PassCypher’s databaseless architecture the future of cybersecurity?
With cyber threats targeting centralized systems more aggressively than ever, the databaseless architecture of PassCypher ensures:
- Greater privacy: No data leaves the device, reducing exposure to third-party breaches.
- Higher adaptability: Perfect for industries like healthcare, finance, and government that demand stringent security.
- Long-term scalability: Operates without costly server infrastructure or database maintenance.
What are the benefits of a passwordless manager for small businesses
A passwordless manager like PassCypher HSM PGP helps small businesses improve productivity, enhance security, and reduce the risk of cyberattacks. It offers cost-effective, flexible licensing and a user-friendly experience tailored for teams of any size.
How does PassCypher protect against phishing and ransomware attacks?
PassCypher uses sandbox URL validation to block phishing attempts and prevents ransomware by encrypting data in secure containers. Its databaseless architecture ensures no centralized vulnerabilities can be exploited.
Is PassCypher compatible with GDPR and FIDO2 standards?
Yes, PassCypher is fully compliant with GDPR, as it ensures complete data sovereignty and user privacy. While it offers alternatives to FIDO2 passkeys, its offline architecture provides a more secure and independent solution.
What industries can benefit most from PassCypher?
Industries such as healthcare, finance, government, and technology can greatly benefit from PassCypher’s robust passwordless solutions. More importantly, its unparalleled security for sensitive data makes it a preferred choice for organizations with high compliance and privacy standards.”
How does PassCypher address common business challenges?
To begin with, PassCypher simplifies access management, which helps businesses save time and resources. Additionally, it reduces operational costs and strengthens cybersecurity against emerging threats. This combination of benefits makes it an ideal solution for both small businesses and large enterprises looking to modernize their security frameworks.
What sets PassCypher apart from FIDO2 solutions?
First and foremost, unlike FIDO2-based systems that rely heavily on cloud infrastructure, PassCypher operates entirely offline. As a result, it ensures full data sovereignty, enhanced privacy, and robust protection against centralized breaches, providing an unmatched level of independence for users.
Can PassCypher HSM PGP be integrated with existing systems?
Yes, PassCypher seamlessly integrates with existing IT infrastructures. Furthermore, this integration enables businesses to enhance their cybersecurity without disrupting workflows, ensuring a smooth transition to passwordless authentication solutions.
What is the environmental impact of PassCypher?
When it comes to sustainability, PassCypher’s serverless architecture significantly reduces energy consumption. This not only minimizes environmental impact but also provides a sustainable cybersecurity solution for environmentally conscious organizations seeking to balance security and eco-friendliness.
Why is PassCypher HSM PGP completely independent of servers and databases?
PassCypher HSM PGP is built on a serverless and database-free architecture to ensure:
- Maximum Security: By eliminating centralized servers and databases, PassCypher removes critical failure points often targeted by cyberattacks like data breaches.
- Total Privacy: All data is stored locally on the user’s device, ensuring complete data sovereignty and strict compliance with privacy regulations like GDPR.
- Increased Resilience: Unlike server-dependent solutions, PassCypher continues to operate seamlessly, even during network outages or cloud service disruptions.
- Eco-Friendly Design: The absence of server infrastructure significantly reduces energy consumption, minimizing its environmental footprint.
By embracing these principles, PassCypher redefines password and access management with a solution that is resilient, private, and sustainable.
How does PassCypher help with ISO27001 or GDPR compliance?
PassCypher HSM PGP is designed with a databaseless and serverless architecture, ensuring total data sovereignty. All information is stored locally on the user’s device, eliminating risks associated with centralized databases.
- ISO27001: PassCypher meets strict information security requirements through its segmented key authentication model and AES-256 encryption.
- GDPR: By removing the need for servers or databases, PassCypher guarantees data privacy and minimizes the risk of personal data breaches.
Can it be used with mobile devices?
PassCypher HSM PGP is not directly compatible with mobile devices. However, it works seamlessly with PassCypher NFC HSM (Lite or Master), which is compatible with Android phones.
With the Freemindtronic Android application integrating PassCypher, a pairing system allows hybrid use:
- On mobile with PassCypher NFC HSM: Manage credentials and passwords directly on an Android device.
- Paired with PassCypher HSM PGP: A QR code system enables transferring credentials and passwords between the two systems without transferring entire containers, ensuring the security of sensitive data.
Learn more about:
How does PassCypher HSM PGP align with the NIS2 Directive?
PassCypher HSM PGP’s serverless and databaseless architecture significantly reduces energy consumption compared to cloud-reliant competitors. By operating entirely offline and avoiding energy-intensive data centers, it aligns with corporate sustainability goals, offering a cybersecurity solution that combines robust protection with environmental responsibility.
How does PassCypher HSM PGP align with the NIS2 Directive?
PassCypher HSM PGP replaces traditional passwords with randomly generated credentials that are at least equivalent in security to FIDO/Passkey standards. These high-strength passwords are stored within an AES-256 CBC-encrypted container and accessed via a segmented key pair, ensuring top-tier security. Users benefit from one-click authentication, where the system retrieves and applies these credentials automatically, enabling secure logins in under one second. This streamlined process enhances both security and user experience, making it ideal for enterprise environments.
2024 MFA Price Comparison: Affordable 2FA for Businesses and Best OTP Solutions for Secure Management
The Best 2FA MFA Solutions, including affordable 2FA for businesses, are essential for securing your digital life in 2024. From managing TOTP/HOTP keys offline to ensuring end-to-end anonymity, discover the top tools that provide advanced security features without relying on cloud storage. Explore how these solutions safeguard your accounts with ease and reliability.
Stay informed with our posts dedicated to Technical News to track its evolution through our regularly updated topics.

Best TOTP/HOTP Management Solutions for 2024
In this post, we’ll compare the best OTP solutions in 2024, highlighting their ability to store, manage, and share OTP keys securely. The unique advantage of solutions like PassCypher NFC HSM is their ability to manage keys offline, ensuring air-gapped security and quantum-resistant encryption for long-term protection.
Top Authentication Tools for Secure OTP Management
PassCypher NFC HSM stands out as a hybrid hardware and software solution that manages both TOTP and HOTP keys. Its AES-256 CBC encryption ensures that secret OTP keys and login credentials are stored securely, using segmented keys and customizable trust criteria (e.g., geographical zones, PINs, or fingerprints).
In addition to secure key management, PassCypher NFC HSM simplifies the process of generating and managing PINs. Users can generate a PIN automatically by simply clicking on the secret key label via their NFC-enabled phone. This interaction remains contactless, making it incredibly convenient to copy and paste the PIN directly into their device or manually input it on their computer. This user-friendly feature allows for quick and secure access without compromising on security.
RSA-4096 encryption is utilized only for secure sharing of these secrets between NFC HSM modules, making it versatile for sharing via proximity or remote communication, including SMS, email, or even physical printouts.
- Supports TOTP/HOTP: Yes
- Technologies: EviOTP NFC HSM, AES-256 CBC encryption (segmented keys)
- Key Sharing: RSA-4096 encryption for secure sharing between devices
- Offline Capabilities: Yes (full air-gapped security)
- No Account Creation: No cloud accounts or databases; zero-trust system
- Backup/Key Sharing: Yes, using RSA-4096 encryption
- Phishing Protection: URL sandbox to prevent typosquatting
- Setup Speed: Add keys in under 5 seconds by scanning QR codes
- Zero Trust and Zero Knowledge: No user identification or cloud storage
Protectimus SHARK: Robust and Simple Hardware Token
Protectimus SHARK is a straightforward hardware token designed for TOTP and HOTP management, supporting high-level security through SHA-256 encryption. However, it lacks advanced sharing and backup features, limiting its use for users who need to manage or share multiple OTP keys.
- Supports TOTP/HOTP: Yes
- Key Sharing: No sharing or backup options
- Offline Capabilities: Yes (fully offline)
- No Account Creation: Yes
- Use Case: Best for single users needing basic TOTP/HOTP management
Token2 TOTP/HOTP: Versatile Hardware and CLI Solution
Token2 provides hardware tokens and a CLI tool for managing OTP keys across different platforms. While versatile, it doesn’t support secure sharing or key backup between devices.
- Supports TOTP/HOTP: Yes
- Key Sharing: No key-sharing functionality
- Offline Capabilities: Yes
- No Account Creation: Yes
- Use Case: Suitable for technical users needing command-line control of OTPs
This table focuses on hardware-based solutions, offering robust security for enterprise environments. These devices are typically used in organizations requiring offline OTP management and enhanced security features like air-gapped operation and physical key backup.
| Solution | Type | Supports TOTP | Supports HOTP | Offline Capabilities | Backup & Storage | Key Sharing | Special Features |
|---|---|---|---|---|---|---|---|
| PassCypher NFC HSM | Hybrid (Hardware + App) | Yes | Yes | Yes (Air-gapped) | Yes (RSA-4096) | Yes (RSA-4096) | AES-256 CBC, phishing protection, password manager |
| SafeNet OTP 110 | Hardware | Yes | Yes | Yes | No | No | Largely used in enterprise |
| RCDevs RC200/RC300 | Hardware | Yes | Yes | Yes | No | No | E-Ink display for enterprise use |
Detailed Analysis and Key Insights
PassCypher NFC HSM stands out as the most advanced solution in this comparison. Its end-to-end anonymity, air-gapped operation, and AES-256 CBC encryption with segmented keys make it ideal for users prioritizing high-level security and privacy. This solution allows secure RSA-4096 key sharing and supports both TOTP and HOTP keys, making it suitable for enterprises or high-security environments like finance or defense.
Form Factors and Durability
PassCypher NFC HSM also offers durable form factors: it is available as a credit card-sized PVC or as a rugged ABS resin tag. Both versions are waterproof and designed to withstand extreme temperatures ranging from -40°C to 85°C. Additionally, with 40-year memory retention and over 1 million write cycles, this hardware ensures long-term reliability. Weighing less than 9 grams, the tag is portable and features a chrome carabiner for added convenience.
Comparison with Other Solutions
On the other hand, Protectimus SHARK and Token2 offer simpler hardware-based solutions without the advanced backup and sharing features. They are suitable for users needing basic OTP management but lack the advanced functionality of PassCypher NFC HSM.
Software Solutions
Software solutions like Google Authenticator, Authy, and Microsoft Authenticator offer ease of use, though they rely heavily on cloud services and account creation, raising potential privacy concerns. These are best suited for individuals looking for free and easy-to-use OTP management options but come with limitations compared to hardware solutions.
Why PassCypher NFC HSM Lite is the Most Cost-Effective 2FA Solution for 2024
After comparing some of the leading 2FA/MFA solutions available in 2024, PassCypher NFC HSM Lite clearly outperforms its competitors in terms of cost-effectiveness and feature set.
Key Takeaways:
Competitive Pricing per Key: PassCypher NFC HSM Lite offers a low cost per key, especially for larger key counts. This pricing advantage becomes particularly evident when compared to hardware solutions like SafeNet OTP or RCDevs, where the cost per key is significantly higher.
| Solution | Price | Number of Keys | Cost per OTP Key (€): Affordable MFA Solutions for 2024 |
|---|---|---|---|
| PassCypher NFC HSM Lite 25 | 99 € | 25 | 3.96 |
| PassCypher NFC HSM Lite 50 | 178 € | 50 | 3.56 |
| PassCypher NFC HSM Lite 100 | 315 € | 100 | 3.15 |
| SafeNet OTP 110 | 79 € | 1 | 79.00 |
| RCDevs RC200/RC300 | 99 € | 1 | 99.00 |
| Protectimus Flex | 19.99 € | 1 | 19.99 |
| Authy (Twilio Verify) | Pay-per-use ($0.05 + fees) | Unlimited | Varies on usage |
| Google Authenticator | Free | Unlimited | 0.00 |
| Microsoft Authenticator | Free | Unlimited | 0.00 |
As shown in the table, PassCypher NFC HSM Lite offers significant savings for businesses that need to manage a large number of OTPs, with the cost per key dropping to as low as 3.15 €/key when managing 100 keys.
Total Cost for Managing Multiple OTPs
If you need to manage multiple OTPs, the total cost of some hardware competitors becomes prohibitively expensive. In contrast, PassCypher NFC HSM Lite remains very affordable.
| Solution | Total Cost for 25 OTPs | Total Cost for 50 OTPs | Total Cost for 100 OTPs |
|---|---|---|---|
| PassCypher NFC HSM Lite 25 | 99 € | – | – |
| PassCypher NFC HSM Lite 50 | 99 € | 178 € | – |
| PassCypher NFC HSM Lite 100 | 99 € | 178 € | 315 € |
| SafeNet OTP 110 | 1,975 € | 3,950 € | 7,900 € |
| RCDevs RC200/RC300 | 2,475 € | 4,950 € | 9,900 € |
| Protectimus Flex | 499.75 € | 999.50 € | 1,999 € |
| Authy (Twilio Verify) | Depends on usage | Depends on usage | Depends on usage |
| Google Authenticator | Free | Free | Free |
| Microsoft Authenticator | Free | Free | Free |
The table shows that PassCypher NFC HSM Lite is the clear winner in terms of managing multiple OTPs, costing only 315 € for 100 OTPs, compared to 7,900 € for SafeNet OTP and 9,900 € for RCDevs. This makes it an extremely cost-effective solution for businesses managing large volumes of OTPs.
Added Value with Password Management: A Key Feature of Cost-Effective MFA Solutions
Not only does PassCypher NFC HSM manage OTPs, but it also doubles as a password manager, a feature that most hardware-based competitors lack. This integration eliminates the need for purchasing two separate tools, saving costs and simplifying management.
Profitability of Cost-Effective MFA Solutions: 2024 OTP and Password Management Comparison
Let’s compare the profitability or cost-effectiveness of PassCypher NFC HSM based on the total cost for managing 100 OTPs alongside password management functionality:
| Solution | Total Cost for 100 OTPs | Password Management Included? | Overall Cost-Effectiveness |
|---|---|---|---|
| PassCypher NFC HSM Lite 100 | 315 € | Yes | Highly cost-effective |
| SafeNet OTP 110 | 7,900 € | No | Very expensive |
| RCDevs RC200/RC300 | 9,900 € | No | Very expensive |
| Protectimus Flex | 1,999 € | No | Moderately expensive |
| Authy (Twilio Verify) | Pay-per-use | No | Depends on usage |
| Google Authenticator | Free | No | Very cost-effective |
| Microsoft Authenticator | Free | No | Very cost-effective |
PassCypher NFC HSM Lite proves to be the most cost-effective choice, with the added bonus of integrated password management. Its low cost, combined with multiple functionalities, makes it highly profitable for businesses needing secure OTP and password solutions.
Conclusion
PassCypher NFC HSM Lite is not only cost-effective when managing multiple OTPs but also adds extra value with its password management feature, significantly increasing its overall profitability for users looking for a hybrid solution.
Competitors like SafeNet OTP and RCDevs are significantly more expensive, particularly when managing multiple keys, and do not offer integrated password management, making PassCypher NFC HSM Lite a superior choice for most businesses and individuals.
PassCypher NFC HSM Lite offers great value for users managing a large number of OTPs while benefiting from additional functionalities like password management and phishing protection, all at a much lower price point than hardware alternatives. This makes it a highly attractive and cost-effective solution in today’s market for securing digital assets.
Comprehensive Guide: Navigating Cryptographic Means Authorization
ANSSI cryptography authorization: Learn how to navigate the regulatory landscape for importing and exporting cryptographic products in France. This comprehensive guide covers the necessary steps, deadlines, and documentation required to comply with both national and European standards. Read on to ensure your operations meet all legal requirements.
Stay informed with our posts dedicated to Cyberculture to track its evolution through our regularly updated topics.
Complete Guide: Declaration and Application for Authorization for Cryptographic Means
In France, the import, export, supply, and transfer of cryptographic products are strictly regulated by Decree n°2007-663 of 2 May 2007. This decree sets the rules to ensure that operations comply with national and European standards. At the same time, EU Regulation 2021/821 imposes additional controls on dual-use items, including cryptographic products.
This guide explains in detail the steps to correctly fill in the declaration or authorization request form, as well as the deadlines and documents to be provided to comply with the ANSSI cryptography authorization requirements.
Download the XDA Form
Click this link to Download the declaration and authorization application form
Regulatory Framework: Decree No. 2007-663 and Regulation (EU) 2021/821
Decree No. 2007-663 of 2 May 2007 regulates all operations related to the import, export, supply, and transfer of cryptographic means. It clearly sets out the conditions under which these operations may be carried out in France by defining declaration and authorization regimes. To consult the decree, click this link: Decree n°2007-663 of 2 May 2007.
At the European level, Regulation (EU) 2021/821 concerns dual-use items, including cryptographic products. This regulation imposes strict controls on these products to prevent their misuse for military or criminal purposes. To view the regulation, click this link: Regulation (EU) 2021/821.
By following these guidelines, you can ensure that your operations comply with both national and European standards for cryptographic products. If you need further assistance or have any questions, feel free to reach out!
Fill out the XDA PDF Form
The official form must be completed and sent in two copies to the ANSSI. It is essential to follow the instructions carefully and to tick the appropriate boxes according to the desired operations (declaration, application for authorisation or renewal).
Address for submitting forms
French National Agency for the Security of Information Systems (ANSSI)Regulatory Controls Office51, boulevard de La Tour-Maubourg75700 PARIS 07 SP.
Contact:
- Phone: +33 (0)1 71 75 82 75
- Email: controle@ssi.gouv.fr
This form allows several procedures to be carried out according to Chapters II and III of the decree.
You can download the official form by following this PDF link.
- Declaration of supply, transfer, import or export from or to the European Union or third countries.
- Application for authorization or renewal of authorization for similar operations.
Paperless submission: new simplified procedure
Since 13 September 2022, an electronic submission procedure has been put in place to simplify the formalities. You can now submit your declarations and authorisation requests by email. Here are the detailed steps:
Steps to submit an online application:
- Email address: Send your request to controle@ssi.gouv.fr.
- Subject of the email: [formalities] Name of your company – Name of the product. Important: The object must follow this format without modification.
- Documents to be attached:
- Completed form (electronic version).
- Scanned and signed form.
- All required attachments (accepted formats: .pdf, .xls, .doc).
- Large file management: If the size of the attachments exceeds 10 MB, divide your mailing into several emails according to the following nomenclature:
- [Formalities] Name of your company – Product name – Part 1/x
- [Formalities] Your Company Name – Product Name – Part 2/x
1. Choice of formalities to be carried out
The form offers different boxes to tick, depending on the formalities you wish to complete:
- Reporting and Requesting Authorization for Any Cryptographic Medium Operation: By ticking this box, you submit a declaration for all supply, transfer, import or export operations, whether inside or outside the European Union. This covers all types of operations mentioned in the decree.
- Declaration of supply, transfer from or to a Member State of the European Union, import and export to a State not belonging to the European Union of a means of cryptology: Use this box if you are submitting only a simple declaration without requesting authorisation for the operations provided for in Chapter II of the Decree.
- Application for authorisation to transfer a cryptographic method to a Member State of the European Union and export to a State that does not belong to the European Union: This box is specific to operations that require prior authorisation, pursuant to Chapter III of the Decree.
- Renewal of authorisation for the transfer to a Member State of the European Union and for the export of a means of cryptology: If you already have an authorization for certain operations and want to renew it, you will need to check this box.
1.1 Time Limits for Review and Notification of Decisions
This section should begin by explaining the time limits for the processing of applications or declarations based on the operation being conducted. Each subsequent point must address a specific formal procedure in the order listed in your request.
1.1.1 Declaration and Application for Authorization of Any Transaction Relating to a Means of Cryptology
This relates to general declarations for any cryptographic operation, whether it involves supply, transfer, import, or export of cryptographic means.
- Examination Period: ANSSI will review the declaration or application for 1 month (extended to 2 months for cryptographic services or export to non-EU countries).
- Result: If the declaration is compliant, ANSSI issues a certificate.
- In Case of Silence: You may proceed with your operation and request a certificate confirming that the declaration was received if no response is provided within the specified time frame.
1.1.2 Declaration of Supply, Transfer, Import, and Export to Non-EU Countries of a Means of Cryptology
This section involves simple declarations of cryptographic means being supplied, transferred within the EU, imported, or exported outside the EU.
- Examination Period: For supply, transfer, import, or export operations, ANSSI has 1 month to review the file. For services or exports outside the EU, the review period is 2 months.
- Result: ANSSI will issue a certificate if the file is compliant.
- In Case of Silence: After the deadlines have passed, you may proceed and request a certificate confirming compliance.
1.1.3 Application for Authorization to Transfer Cryptographic Means within the EU and Export to Non-EU Countries
This applies to requests for prior authorization required for transferring cryptographic means within the EU or exporting them to non-EU countries.
- Examination Period: ANSSI will examine the application for authorization within 2 months.
- Notification of Decision: The Prime Minister will make a final decision within 4 months.
- In Case of Silence: If no response is provided, you receive implicit authorization valid for 1 year. You can also request a certificate confirming this authorization.
1.1.4 Application for Renewal of Authorization for Transfer within the EU and Export of Cryptographic Means
This relates to renewing an existing authorization for the transfer of cryptographic means.
- Review Period: ANSSI will review the renewal application within 2 months.
- Notification of Decision: The Prime Minister will issue a decision within 4 months.
- In Case of Silence: If no decision is made, an implicit authorization valid for 1 year is granted. You can request a formal certificate to confirm this authorization.
1.1.5 Example Response from ANSSI for Cryptography Authorization Requests
When you submit a declaration or request for authorization, ANSSI typically provides a confirmation of receipt, which includes:
- Subject: Confirmation of Receipt for Cryptography Declaration/Authorization
- Date and Time of Submission: For example, “Monday 23 October 2022 13:15:13.”
The response confirms that ANSSI has received the request and outlines the next steps for review.
A: Information on the Registrant and/or Applicant, Person in charge of the administrative file and Person in charge of the technical elements.
This section must be filled in with the information of the declarant or applicant, whether it is a legal person (company, association) or a natural person. You should include information such as:
- The name and address of the entity or individual.
- Company name and SIRET number for companies.
- Contact details of the person responsible for the administrative file and the person in charge of the technical aspects of the cryptology product.
Person in charge of technical aspects: This person is the direct contact with the ANSSI for technical questions relating to the means of cryptology.
B: Cryptographic Medium to which the Declaration and/or Application for Authorization Applies
This part concerns the technical information of the cryptology product:
B.2.1 Classify the medium into the corresponding category(ies)
You must indicate whether the product is hardware, software, or both, and specify its primary role (e.g., information security, network, etc.).
B.2.2 General description of the means
The technical part of the form requires a specific description of the cryptographic means. You will need to provide information such as:
- Generic name of the medium (photocopier, telephone, antivirus software, etc.).
- Brand, trade number, and product version .
- Manufacturer and date of release.
Comments in the form:
- The cryptographic means must identify the final product to be reported (not its subsets).
- Functional description: Describe the use of the medium (e.g., secure storage, encrypted transmission).
B.2.3 Indicate which category the main function of the means (tick) relates to
- Information security (means of encryption, cryptographic library, etc.)
- Computer (operating system, server, virtualization software, etc.)
- Sending, storing, receiving information (communication terminal, communication software,
- management, etc.)
- Network (monitoring software, router, base station, etc.)
- If yes, specify:
B.3. Technical description of the cryptology services provided
B.3.2. Indicate which category(ies) the cryptographic function(s) of the means to be ticked refers to:
- Authentification
- Integrity
- Confidentiality
- Signature
B.3.3. Indicate the secure protocol(s) used by:
- IPsec
- SSH
- VoIP-related protocols (such as SIP/RTP)
- SSL/TLS
- If yes, specify:
Comments in the form:
- Cryptographic functionality: Specify how the product encrypts data (e.g., protection of files, messages, etc.).
- Algorithms: List the algorithms and how they are used. For example, AES in CBC mode with a 256-bit key for data encryption.
B.3.4. Specify the cryptographic algorithms used and their maximum key lengths:
Table to be filled in: Algorithm / Mode / Associated key size / Function
This section requires detailing the cryptographic services that the product offers:
- Secure protocol (SSL/TLS, IPsec, SSH, etc.).
- Algorithms used and key size (RSA 2048, AES 256, etc.).
- Encryption mode (CBC, CTR, CFB).
C: Case of a cryptographic device falling within category 3 of Annex 2 to Decree No. 2007-663 of 2 May 2007
This section must be completed if your product falls under category 3 of Annex 2 of the decree, i.e. cryptographic means marketed on the consumer market. You must provide specific explanations about:
- Present the method of marketing the means of cryptology and the market for which it is intended
- Explain why the cryptographic functionality of the medium cannot be easily changed by the user
- Explain how the installation of the means does not require significant subsequent assistance from the supplier
D: Renewal of transfer or export authorization
If you are applying for the renewal of an existing authorisation, you must mention the references of the previous authorisation, including the file number, the authorisation number and the date of issue.
E: Attachments (check the boxes for the attachments)
To complete your file, you must provide a set of supporting documents, including:
- General document presenting the company (electronic format preferred)
- extract K bis from the Trade and Companies Register dated less than three months (or a
- equivalent document for companies incorporated under foreign law)
- Cryptographic Medium Commercial Brochure (electronic format preferred)
- Technical brochure of the means of cryptology (electronic format preferred)
- User manual (if available) (electronic format preferred)
- Administrator Guide (if available) (electronic format preferred)
All of these documents must be submitted in accepted electronic formats, such as .pdf, .xls, or .doc.
F: Attestation
The person representing the notifier or applicant must sign and attest that the information provided in the form and attachments is accurate. In the event of a false declaration, the applicant is liable to sanctions in accordance with Articles 34 and 35 of Law No. 2004-575 on confidence in the digital economy.
G: Elements and technical characteristics to be communicated at the request of the national agency for the security of information systems (preferably to be provided in electronic format)
In addition, the ANSSI may request additional technical information to evaluate the cryptology product, such as:
- The elements necessary to implement the means of cryptology:
- two copies of the cryptographic medium;
- the installation guides of the medium;
- devices for activating the medium, if applicable (license number, activation number, hardware device, etc.);
- key injection or network activation devices, if applicable.
- The elements relating to the protection of the encryption process, namely the description of the measures
Techniques used to prevent tampering with encryption or management associated keys.
- Elements relating to data processing:
- the description of the pre-processing of the clear data before it is encrypted (compression, formatting, adding a header, etc.);
- the description of the post-processing of the encrypted data, after it has been encrypted (adding a header, formatting, packaging, etc.);
- three reference outputs of the means, in electronic format, made from a clear text and an arbitrarily chosen key, which will also be provided, in order to verify the implementation of the means in relation to its description.
- Elements relating to the design of the means of cryptology:
- the source code of the medium and the elements allowing a recompilation of the source code or the references of the associated compilers;
- the part numbers of the components incorporating the cryptology functions of the medium and the names of the manufacturers of each of these components;
- the cryptology functions implemented by each of these components;
- the technical documentation of the component(s) performing the cryptology functions;
- the types of memories (flash, ROM, EPROM, etc.) in which the cryptographic functions and parameters are stored as well as the references of these memories.
Validity and Renewal of ANSSI Cryptography Authorization
When ANSSI grants an authorization for cryptographic operations, it comes with a limited validity period. For operations that require explicit authorization, such as the transfer of cryptographic means within the EU or exports outside the EU, the certificate of authorization issued by ANSSI is valid for one year if no express decision is made within the given timeframe.
The renewal process must be initiated before the expiry of the certificate. ANSSI will review the completeness of the application within two months, and the decision is issued within four months. If ANSSI remains silent, implicit authorization is granted, which is again valid for a period of one year. This renewal ensures that your cryptographic operations remain compliant with the regulations established by Decree n°2007-663 and EU Regulation 2021/821, avoiding any legal or operational disruptions.
For further details on how to initiate a renewal or first-time application, refer to the official ANSSI process, ensuring all deadlines are respected for uninterrupted operations.
Legal Framework for Cryptographic Means: Key Requirements Under Decree No. 2007-663
Understanding the legal implications of Decree No. 2007-663 is crucial for any business engaged in cryptology-related operations, such as the import, export, or transfer of cryptographic products. This section outlines the legal framework governing declarations, authorizations, and specific cases for cryptographic means. Let’s delve into the essential points:
1. Formalities Under Chapters II and III of Decree No. 2007-663
Decree No. 2007-663 distinguishes between two regulatory regimes—declaration and authorization—depending on the nature of the cryptographic operation. These formalities aim to safeguard national security by ensuring cryptographic means are not misused.
- Chapter II: Declaration Regime
This section requires businesses to notify the relevant authorities, particularly ANSSI, when cryptographic products are supplied, transferred, imported, or exported. For example, when transferring cryptographic software within the European Union, companies must submit a declaration to ANSSI. This formality ensures that the movement of cryptographic products adheres to ANSSI cryptography authorization protocols. The primary goal is to regulate the flow of cryptographic tools and prevent unauthorized or illegal uses. - Chapter III: Authorization Regime
Operations involving cryptographic means that pose higher security risks, especially when exporting to non-EU countries, require explicit authorization from ANSSI. The export of cryptographic products, such as encryption software, outside the European Union is subject to strict scrutiny. In these cases, companies must obtain ANSSI cryptography authorization, which evaluates potential risks before granting permission. Failure to secure this authorization could result in significant legal consequences, such as operational delays or penalties.
2. Request for Authorization or Renewal
If your operations involve cryptographic means that require prior approval, the Decree mandates that you apply for authorization or renewal. This is particularly relevant for:
- Transfers within the EU: Even though the product remains within the European Union, if the cryptographic tool is sensitive, an authorization request must be submitted. This helps mitigate risks associated with misuse or unauthorized access to encrypted data.
- Exports outside the EU: Exporting cryptographic means to non-EU countries is subject to even stricter controls. Businesses must renew their authorization periodically to ensure that all their ongoing operations remain legally compliant. This step is non-negotiable for companies dealing with dual-use items, as defined by EU Regulation 2021/821.
3. Category 3 Cryptographic Means (Annex 2)
Category 3 cryptographic means, outlined in Annex 2 of the Decree, apply to consumer-facing products that are less complex but still critical for security. These are often products marketed to the general public and must meet specific criteria:
- Unmodifiable by End-Users: Cryptographic products under Category 3 must not be easily altered by end-users. This ensures the integrity of the product’s security features.
- Limited Supplier Involvement: These products should be user-friendly, not requiring extensive assistance from the supplier for installation or continued use.
An example of a Category 3 product might be a mobile application that offers end-to-end encryption, ensuring ease of use for consumers while adhering to strict cryptographic security protocols.
Regulatory Framework and Implications
Decree No. 2007-663, alongside EU Regulation 2021/821, sets the groundwork for regulating cryptographic means in France and the broader European Union. Businesses must comply with these regulations, ensuring they declare or obtain the proper ANSSI cryptography authorization for all cryptographic operations. Compliance with these legal frameworks is non-negotiable, as they help prevent the misuse of cryptographic products for malicious purposes, such as espionage or terrorism.
Displaying ANSSI Cryptography Authorization: Transparency and Trust
Publicly showcasing your ANSSI cryptography authorization not only demonstrates regulatory compliance but also strengthens your business’s credibility. In fact, there are no legal restrictions preventing companies from making their authorization certificates visible. By displaying this certification, you reinforce transparency and trustworthiness, especially when dealing with clients or partners who prioritize data security and regulatory adherence.
Moreover, doing so can provide a competitive edge. Customers and stakeholders are reassured by visible compliance with both French and European standards, including Decree No. 2007-663 and EU Regulation 2021/821. Displaying this certificate prominently, whether on your website or in official communications, signals your business’s proactive stance on cybersecurity.
Final Steps to Ensure Compliance
Now that you understand the steps involved in ANSSI cryptography authorization, you are better equipped to meet the regulatory requirements for importing and exporting cryptographic means. By diligently completing the necessary forms, submitting the required documentation, and adhering to the outlined deadlines, you can streamline your operations and avoid potential delays or penalties. Moreover, by staying up-to-date with both French and European regulations, such as Decree No. 2007-663 and EU Regulation 2021/821, your business will maintain full compliance.
For any additional guidance, don’t hesitate to reach out to the ANSSI team or explore their resources further on their official website. By taking these proactive steps, you can ensure that your cryptographic operations remain fully compliant and seamlessly integrated into global standards.
Unveil Microsoft’s Enhanced Uninstallable Recall for Total Data Security
Microsoft Uninstallable Recall: Learn how Microsoft has significantly upgraded the security of its Recall activity journal, now featuring an easy-to-use uninstall option and protection through a secure enclave with stronger authentication. Read the full article to explore these advanced security features and improvements.
Stay informed with our posts dedicated to Technical News to track its evolution through our regularly updated topics.
Microsoft’s Revamped Recall System
Microsoft recently overhauled its Recall feature, which had faced criticism for security and privacy issues. The new version delivers enhanced protection and better control over personal data, responding directly to concerns raised by users and privacy experts.
Key Features of Microsoft’s New Uninstallable Recall
Recall is an activity journal that allows users to retrieve information based on past actions, utilizing AI-analyzed screenshots. In its first iteration, the tool faced backlash because data was stored insecurely, making it easily accessible to others sharing the same device.
Microsoft responded by overhauling the architecture of Recall. Now, all data processing occurs within a Trusted Platform Module (TPM)-protected secure enclave. Access to information requires Windows Hello authentication or a PIN, ensuring that only authorized users can unlock the encrypted data.
Enhanced Data Protection with Microsoft’s Uninstallable Recall
Microsoft significantly improved the security architecture of Recall. All data is now encrypted and stored within the TPM chip, and multi-factor authentication further protects user information. Recent updates to Recall ensure that sensitive information is automatically filtered out, including passwords, personal identification numbers, and credit card details.
These changes align with the security mechanisms found in BitLocker, which also uses TPM to safeguard encryption keys. Freemindtronic has noted the similarities between Recall and BitLocker’s multi-layer encryption and user-focused security enhancements.
How to Enable and Remove Microsoft’s New Recall
With the updated Uninstallable Recall, Microsoft gives users full control over the feature. Recall is opt-in—it remains off unless activated by the user, and it can be uninstalled easily at any time. Microsoft has confirmed that when Recall is uninstalled, all related data is permanently deleted, further addressing privacy concerns.
Additional Security Measures
Microsoft also introduced several improvements to Recall, including:
- Private browsing compatibility: Users can now prevent Recall from saving sessions during private browsing.
- Sensitive content filtering: By default, Recall filters out sensitive data such as passwords and personal details.
- Custom permissions: Users can choose what data Recall tracks and restrict it to specific apps or activities.
These updates reflect Microsoft’s commitment to providing robust data protection, and as seen in similar tools like BitLocker, Microsoft emphasizes TPM-based encryption to secure user data. Freemindtronic highlighted that BitLocker uses multi-layer encryption and TPM to secure sensitive information from unauthorized access.
Business and Consumer Advantages of Microsoft’s Enhanced Recall
These enhancements have significant implications for both businesses and individual users. Companies can benefit from the enhanced data protection, especially when managing sensitive information across multiple devices. Users working in shared environments can rest assured knowing their personal data is encrypted and secured, even if the device is shared.
Moreover, this follows a pattern of Microsoft’s continuous security efforts, as seen in the resolution of BitLocker access issues caused by a faulty Crowdstrike update. The incident demonstrated the importance of robust encryption and key management tools like PassCypher NFC HSM.
Availability of the Uninstallable Recall Feature
The new Recall feature will be available to Windows Insiders in October 2024. It is integrated with Copilot+ PCs, designed to provide comprehensive security without sacrificing usability.
Why Microsoft’s Recall Is a Step Forward in Data Security
With the Uninstallable Recall, Microsoft demonstrates its commitment to developing tools that balance user privacy and productivity. The integration of TPM-encrypted data storage, biometric authentication, and flexible permissions makes Recall one of the most secure data management systems available today, alongside established solutions like BitLocker.
Digital Authentication Security by Jacques gascuel This article will be updated with any new information on the topic, and readers are encouraged to leave comments or contact the author with any suggestions or additions.
How Digital Authentication Security Shields Our Data
Digital authentication security is essential in today’s connected world. Whether accessing bank accounts, social media, or work emails, authentication ensures that only authorized individuals can access sensitive information. With the growing sophistication of cyberattacks, securing our identity online has become critical. This article will explore the evolution of authentication methods, from simple passwords to multi-factor authentication, and how these technologies are essential for protecting both personal and professional data.
Digital Authentication Security: The Guardian of Our Digital World
In today’s digital life, authentication has become a vital process. Whether you are accessing your bank accounts, social media, or work emails, you are constantly required to prove your identity. But what is authentication exactly, and why has it become so essential in our digital world?
Authentication is the process of verifying a person’s or device’s identity before granting access to specific resources. While often seen as a simple formality, it plays a crucial role in protecting both personal and professional data.
The Stakes of Security
In a world where cyberattacks are becoming increasingly sophisticated and frequent, securing information systems has become a top priority. The consequences of a compromised account can be disastrous—identity theft, fraud, financial loss. The most common threats include phishing, brute force attacks, dictionary attacks, and injection attacks.
To combat these threats, authentication methods have evolved significantly. From the simple password, often considered an easy barrier to breach, we have transitioned to multi-factor authentication systems that are much more robust.
The Evolution of Digital Authentication Security Methods
Over the years, authentication methods have continuously evolved to meet the growing security demands. We have moved from simple password-based authentication, which relies on something you know, to methods that combine several factors:
- Something you know (password)
- Something you possess (security key)
- Something you are (biometrics)
Let’s dive into the various authentication methods, their pros, cons, and applications. We’ll also see how these methods enhance the security of our online accounts and protect our personal data.
Fundamentals of Authentication
Password Authentication: The Historical Pillar
Password authentication is undoubtedly the oldest and most widespread method of verifying a user’s identity. This simple system, which associates a username with a secret password, was long considered enough to secure access to our online accounts.
Advantages:
- Simplicity: Easy to implement and understand for users.
- Universality: Used by almost all online services.
Disadvantages:
- Vulnerability: Passwords can be easily compromised by brute force, dictionary attacks, or phishing.
- Frequent Forgetfulness: Users tend to forget their passwords or create weak ones for easier memorization.
- Reuse: Users often reuse the same password across multiple accounts, increasing the risk of data breaches.
Best Practices for Creating Strong Passwords
To enhance the security of your accounts, it is essential to create strong and unique passwords. Here are some tips:
- Length: A password should ideally be at least 12 characters long.
- Complexity: Use a combination of uppercase and lowercase letters, numbers, and special characters.
- Originality: Avoid using easily found personal information (birth dates, family names, etc.).
- Variety: Use different passwords for each account.
Types of Attacks and How to Protect Yourself
Passwords are regularly targeted by cybercriminals. The main threats include:
- Brute Force Attacks: The hacker tries all possible character combinations until the correct password is found.
- Dictionary Attacks: The hacker uses a list of common words or phrases to guess the password.
- Phishing: The hacker sends fake emails or SMS messages to trick the user into revealing their login credentials.
To protect yourself from these attacks:
- Use a Password Manager: This tool allows you to generate and store strong, unique passwords securely for all your accounts.
- Activate Two-Factor Authentication (2FA): This method adds an extra layer of security by requiring an additional verification during login.
- Be Vigilant About Phishing Attempts: Do not click on suspicious links and always verify the sender’s email address.
Limitations of Password Authentication Alone
Despite following best practices, password authentication has inherent limitations. Passwords can be lost, stolen, or forgotten. Moreover, remembering many complex passwords is challenging for users.
To dive deeper into secure authentication best practices and how to defend against common attacks, refer to the OWASP Authentication Cheat Sheet.
In summary, password authentication has been a pillar of computer security for many years. However, its limitations have become more apparent as threats evolve. It is now necessary to combine passwords with other authentication factors to enhance the security of online accounts.
Now, let’s dive into multi-factor authentication methods that offer more robust protection than passwords alone.
Multi-Factor Authentication (MFA) and Digital Authentication Security
In the previous section, we discussed the limitations of password authentication. To strengthen security, both companies and individuals are increasingly turning to multi-factor authentication methods.
Two-Factor Authentication (2FA)
Two-factor authentication (2FA) is a method that requires the user to provide two distinct proofs of identity to access an account. This approach significantly enhances security by adding an extra layer of protection.
The Principle of 2FA:
2FA relies on combining two different authentication factors. These factors can be:
- Something you know: The password
- Something you possess: A mobile phone, security key, or smart card
- Something you are: A biometric characteristic (fingerprint, facial recognition)
Different Types of 2FA:
- SMS: A one-time code is sent via SMS to the phone number associated with the account.
- Authentication Apps: Apps like Google Authenticator or Microsoft Authenticator generate one-time passcodes.
- Security Keys: Physical devices (USB keys, U2F security keys) that must be inserted into a USB port for login.
Advantages of 2FA for Enhancing Security
Even if an attacker obtains your password, they cannot access your account without the second authentication factor. As a result, 2FA makes brute force and phishing attacks much more difficult.
Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) is an extension of 2FA. It uses more than two authentication factors to further enhance security.
Difference Between 2FA and MFA:
The primary difference between 2FA and MFA lies in the number of factors used. MFA can combine several factors, such as a password, an authentication app, and a fingerprint.
Common Factor Combinations:
- Password + SMS Code
- Password + Security Key
- Password + Fingerprint
- Password + Facial Recognition
Advantages of MFA for Strengthening Security
For comprehensive guidelines on implementing multi-factor authentication securely, consult the NIST Multi-Factor Authentication Guide.
MFA offers an even higher level of security than 2FA by making attacks more difficult.
Comparison Between 2FA and MFA
| Characteristic | 2FA | MFA |
|---|---|---|
| Number of Factors | 2 | 2 or more |
| Security | More secure than password alone | Even more secure than 2FA |
| Complexity | More complex than password alone | More complex than 2FA |
| User Experience | Can be less convenient than password alone | Can be less convenient than 2FA |
Let’s now explore other advanced authentication methods, such as biometric authentication and token-based systems.
Advanced Methods for Digital Authentication Security
Biometric Authentication: The Unique Signature of Each Individual
Biometric authentication is based on the idea that each individual has unique physical or behavioral traits that can serve as identification methods. These characteristics are known as biometric traits.
Different Biometric Technologies:
- Fingerprints: One of the most common methods, based on analyzing the ridges and valleys on the fingers.
- Facial Recognition: Uses unique facial features to identify a person.
- Iris Scans: The iris is a complex and unique structure that can be analyzed for authentication.
- Voice Recognition: Analyzes vocal characteristics like tone, rhythm, and timbre to identify a person.
- Hand Geometry: Analyzes hand shape, finger length, and joint position.
- Dynamic Signature: Analyzes how a person signs their name, including speed, pressure, and angle.
Advantages of Biometrics:
- Enhanced Security: Biometric traits are hard to falsify or steal.
- Ease of Use: Biometric authentication is often more convenient than typing a password or PIN.
- No Forgetfulness: It’s impossible to forget your face or fingerprint.
Disadvantages of Biometrics:
- Privacy Concerns: Storing and using biometric data raises significant privacy issues.
- Cost: Implementing biometric authentication systems can be expensive.
- Vulnerabilities: Although rare, security breaches can allow bypassing of biometric systems.
Security and Privacy Challenges
- Forgery: Techniques exist to forge biometric data, such as creating molds of fingerprints or using facial masks.
- Data Protection: Biometric data is considered sensitive information and must be protected from unauthorized access.
- Consent: Users must give informed consent before collecting and processing their biometric data.
EviOTP NFC HSM: Secure Device-Based Authentication
Another approach to strengthening authentication security involves using secure physical devices. EviOTP NFC HSM is an excellent example of this category. EviOTP NFC HSM technology is embedded in two key products: PassCypher NFC HSM Lite and PassCypher NFC HSM Master, both from Fullsecure Andorra. These products are equipped with quantum security features and are protected by two international invention patents, ensuring cutting-edge protection and international security compliance. These patents ensure a high level of security and protection across borders.This system combines several technologies to offer optimal protection and unmatched flexibility:
- NFC (Near Field Communication): Users can generate unique OTP codes simply by bringing their smartphone close to an NFC reader.
- HSM (Hardware Security Module): Cryptographic keys are securely stored in a dedicated hardware module, making software attacks much more difficult.
- TOTP and HOTP: These algorithms ensure the generation of one-time-use codes, making replay attacks nearly impossible.
- Advanced Customization: EviOTP NFC HSM allows customization of access to each secret key by adding passwords, fingerprints, geolocation, or other additional authentication factors.
- Autonomy: This system operates without servers, databases, or the need to create an account, ensuring absolute anonymity and maximum security.
Advantages of EviOTP NFC HSM:
- Maximum Security: Combining these technologies provides unparalleled security, especially through hardware key protection and customizable access.
- Ease of Use: NFC technology makes authentication simple and intuitive.
- Flexibility: This system can be adapted to different environments and easily integrates with many applications.
- Compliance: EviOTP NFC HSM often meets the strictest security standards, ensuring regulatory compliance.
- Anonymity and Privacy: Operating without servers or databases ensures user privacy.
- Versatility: EviOTP NFC HSM allows for the generation of all types of PIN codes, regardless of length.
Protection Against Common Attacks
Phishing is one of the biggest threats to online account security. By generating one-time-use OTP codes directly on the secure device, EviOTP NFC HSM makes these attacks far less effective. Even if a user is tricked into entering credentials on a fake website, the OTP code generated will be invalid a few seconds later. Additionally, storing cryptographic keys in an HSM makes software-based attacks much more difficult. Even if a device is compromised, the keys cannot be extracted.
In summary, EviOTP NFC HSM represents a cutting-edge authentication solution, ideal for organizations seeking maximum security and flexibility. This solution is particularly suited for sectors where data protection is critical, such as banking, healthcare, and industry. EviOTP NFC HSM offers a multi-layered defense that makes attacks extremely difficult, if not impossible, to carry out.
Comparison Table of Authentication Methods
| Method | Authentication Factors | Security | Ease of Use | Cost | Flexibility |
|---|---|---|---|---|---|
| Password | Something you know | Low | Very easy | Low | Very high |
| PIN | Something you know | Medium | Easy | Low | Medium |
| Security Key | Something you possess | Medium-High | Medium | Medium | Medium |
| Authenticator Apps | Something you possess | Medium | Medium | Low | Medium |
| SMS | Something you possess | Low | Easy | Low | Medium |
| Biometrics (fingerprint, facial) | Something you are | High | Very easy | Medium-High | Medium |
| EviOTP NFC HSM | Something you possess (NFC) | Very High | Very easy | Medium | High |
Specific Explanations for EviOTP NFC HSM:
- Very High Security: Thanks to secure key storage in an HSM, dynamic OTP generation, and the ability to customize access with passwords, fingerprints, or geolocation.
- Very High Ease of Use: NFC technology makes authentication simple and intuitive.
- Medium Cost: The cost depends on the number of licenses and additional features chosen.
- High Flexibility: EviOTP NFC HSM can be used in many contexts and adapted to various needs.
Other Advanced Authentication Methods
Token, Certificate, and Smart Card Authentication: Enhanced Security
These authentication methods rely on using physical or digital devices that contain secure identification information.
- Token Authentication: A token is a small physical device (often USB-sized) that generates one-time-use codes. These codes are used in addition to a password to access an account. Tokens are generally more secure than SMS codes, as they are not vulnerable to interception.
- Certificate Authentication: A digital certificate is an electronic file that links an identity to a public key. This public key can be used to verify the authenticity of a digital signature or encrypt data. Certificates are often stored on smart cards.
- Smart Card Authentication: A smart card is a small plastic card with an integrated circuit that can store secure digital information, such as private keys and certificates. Smart cards are widely used in banking and security.
Advantages of These Methods:
- Enhanced Security: Identification information is stored on a secure physical device, making it harder to compromise.
- Flexibility: These methods can be used for various applications, from corporate network access to digitally signing documents.
- Interoperability: Digital certificates are based on open standards, facilitating their interoperability with different systems.
Disadvantages and Challenges:
- Cost: Implementing an authentication infrastructure based on tokens, certificates, or smart cards can be expensive.
- Complexity: These methods can be more complex to implement and manage than traditional authentication methods.
- Loss or Theft: Losing a token or smart card can compromise account security.
Behavioral Authentication
Behavioral authentication analyzes an individual’s habits and behavior to verify their identity. This approach can complement traditional authentication methods.
Principle:
The system analyzes different aspects of the user’s behavior, such as typing speed, dynamic signature, browsing habits, etc. Any significant deviation from usual behavior can trigger an alert.
Advantages:
- Intrusion Detection: This method can detect suspicious activity, even if the attacker knows the user’s credentials.
- Adaptation: Behavioral authentication systems can adapt to changes in user behavior.
Disadvantages:
- False Positives: The system may trigger false alerts if the user’s behavior legitimately changes.
- Complexity: Implementing behavioral authentication systems can be complex and expensive.
In summary, token, certificate, smart card, and behavioral authentication methods offer high levels of security and can complement traditional methods. The choice of the most suitable authentication method will depend on the specific needs of each organization or individual.
Authentication Protocols
Authentication protocols define a set of standardized rules and procedures for verifying a user’s or system’s identity. They enable secure communication between different systems and applications.
Single Sign-On (SSO): One Access for All
Single Sign-On (SSO) is a protocol that allows a user to log in to multiple applications using a single authentication. Once authenticated, the user does not need to re-enter their credentials to access other applications.
How SSO Works:
During the first login, the user authenticates with an identity provider (IdP). The provider verifies the credentials and issues an authentication token. This token is then sent to the destination application (relying service), which validates it and grants the user access.
SSO Protocols (SAML, OAuth, OpenID Connect):
- SAML (Security Assertion Markup Language): A standard XML protocol for exchanging authentication information between an identity provider and a relying service.
- OAuth: An authorization protocol that allows third-party applications to access a user’s resources on another service without needing the user’s credentials.
- OpenID Connect: An authentication protocol based on OAuth 2.0 that provides an additional identity layer, enabling applications to know the user’s identity.
Advantages of SSO:
- Improved User Experience: Users only need to enter their credentials once.
- Increased Productivity: Users can access the applications they need faster.
- Enhanced Security: SSO centralizes identity and access management, making it easier to implement security policies.
Disadvantages of SSO:
- Single Point of Failure: If the identity provider is compromised, all connected services may be affected.
- Complexity: Implementing an SSO system can be complex, especially in heterogeneous environments.
OAuth/OpenID Connect: Third-Party Authentication
OAuth and OpenID Connect are two closely related protocols that allow third-party applications to access a user’s resources on another service.
Principle of Third-Party Authentication:
A user logs into a third-party application (such as Facebook or Google) using existing credentials. The third-party application then requests the user’s permission to access certain information. If the user agrees, the third-party application receives an access token that allows it to access the requested resources.
Differences Between OAuth and OpenID Connect:
- OAuth focuses on authorization, while OpenID Connect adds an identity layer, allowing applications to know the user’s identity.
Typical Use Cases:
- Social Login: Logging into an application using Facebook, Google, etc.
- Mobile App Development: Using authentication services from third-party providers to simplify the login process.
The Stakes of Authentication in the Modern Digital World
Authentication has become a central issue in our digital society. Threats are constantly evolving, regulations are multiplying, and user expectations regarding security are increasing.
Recent Threats
- Sophisticated Phishing: Phishing attacks are becoming increasingly sophisticated, using social engineering techniques and highly realistic fake websites to deceive users.
- Password Attacks: Brute force, dictionary, and password-spray attacks remain significant threats.
- Injection Attacks: Injection attacks (SQL injection, XSS) allow attackers to execute malicious code on servers.
- Session Hijacking: Attackers can steal session cookies to log into accounts without the legitimate user’s credentials.
Data Security Regulations
Many regulations have been put in place to protect personal data and strengthen information system security. Some of the most well-known include:
- GDPR (General Data Protection Regulation): This European regulation requires companies to implement appropriate technical and organizational measures to ensure a level of security adapted to the risks.
- CCPA (California Consumer Privacy Act): This Californian law grants consumers additional rights regarding the protection of their personal data.
Future Trends in Authentication
- Passwordless Authentication: As passwords are a prime target for attacks, many initiatives aim to replace them with more secure authentication methods like biometrics or security keys.
- Passkeys: Passkeys are a new authentication technology that allows users to log in to websites and apps without needing to create or remember passwords.
- Artificial Intelligence: AI can be used to improve fraud detection and personalize the user experience by adapting authentication methods based on context.
Summary of Authentication Methods
Authentication is a constantly evolving field. To combat growing threats, it is essential to adopt strong authentication methods and stay informed about the latest trends.
Summary of Various Methods:
Throughout this article, we’ve seen that many authentication methods exist, each with advantages and disadvantages. The choice of the most appropriate method will depend on factors such as:
- The required level of security
- Ease of use
- Implementation cost
- Regulatory constraints
Recommendations for Choosing the Most Appropriate Authentication Method
- Combine Multiple Authentication Factors: Combining multiple factors (something you know, something you possess, something you are) is the most effective way to enhance security.
- Use Strong Authentication Methods: Prioritize biometric authentication, security keys, and digital certificates.
- Implement Strict Security Policies: Set clear rules for creating and managing passwords, raising user awareness, and responding to security incidents.
- Stay Updated on the Latest Threats and Best Practices: Stay informed about the latest security trends and regularly update authentication systems.
Future Challenges in Authentication
The future challenges of authentication are numerous:
- Balancing Security and Usability: It is essential to find a balance between security and ease of use so that users adopt new authentication methods.
- Privacy Protection: Biometric authentication methods raise significant privacy concerns.
- Interoperability: Developing open standards to facilitate interoperability between different authentication systems is necessary.
Building a Future of Resilient Digital Authentication Security
The continuous evolution of threats in the digital landscape demands a proactive approach to Digital Authentication Security. Scientific research consistently highlights the importance of layered security systems, combining various authentication factors to mitigate vulnerabilities. By integrating advanced solutions such as multi-factor authentication (MFA), biometric systems, and hardware-based security like EviOTP NFC HSM, organizations and individuals can significantly reduce their exposure to cyber risks.
Understanding the science behind authentication algorithms, such as the cryptographic protocols securing biometric data or the OTP generation process, is essential for developing robust defenses. As future technologies like quantum computing emerge, the security models we rely on today will need adaptation and reinforcement. Hence, a commitment to ongoing research and technological advancements is crucial for maintaining resilient Digital Authentication Security systems.
Looking forward, the focus must shift toward creating secure, user-friendly authentication frameworks that also respect privacy concerns. This will ensure that as we move deeper into the digital age, our data remains secure without sacrificing convenience. Maintaining vigilance, investing in new technologies, and continuously refining our approaches will be key to staying ahead of the next wave of cyber threats.
Quantum Threats to Encryption: RSA, AES, ECC, post-quantum cryptography (PQC), Store Now Decrypt Later exposure, logical qubits, and sovereign segmented encryption under realistic quantum timelines. This Chronicle analyzes when quantum computers could realistically threaten RSA-2048, ECC, and AES-256, why fault-tolerant qubits remain the decisive bottleneck, and how sovereign cybersecurity architectures can reduce long-term exposure before cryptographically relevant quantum systems emerge. It explains the operational limits of Shor’s and Grover’s algorithms, clarifies the migration doctrines promoted by NIST, NSA CNSA 2.0, ENISA, ANSSI, and UK NCSC, and evaluates why hybrid cryptography and segmented key encryption matter now—not after a quantum breakthrough occurs.
Executive summary
Context
Quantum computing has entered a decisive strategic phase. Between 2024 and 2026, announcements from IBM Quantum, Google Quantum AI, Microsoft Quantum, and Chinese sovereign quantum programs intensified public concern regarding Quantum Threats to Encryption. Yet most public narratives confuse:
- experimental qubit demonstrations,
- marketing announcements,
- real cryptographic capability.
In practice, no current quantum system can operationally break RSA-2048 or AES-256 at industrial scale. However, the strategic issue no longer concerns immediate collapse. The strategic issue concerns:
- long-term exposure persistence.
Purpose
This Chronicle separates:
- scientific reality,
- engineering bottlenecks,
- geopolitical narratives,
- operational cybersecurity consequences.
It explains:
- why RSA and ECC remain structurally vulnerable to Shor’s algorithm,
- why AES-256 remains highly resilient under Grover’s algorithm,
- why logical qubits—not raw qubit counts—define real capability,
- why “Store Now, Decrypt Later” already changes intelligence strategy,
- why sovereign segmented architectures may become decisive.
Scope
Scope includes:
- RSA, ECC, AES-256, and PQC exposure models,
- Shor’s and Grover’s algorithms,
- logical versus physical qubits,
- NIST PQC standards and HQC diversification,
- NSA CNSA 2.0 migration doctrine,
- Store Now Decrypt Later operational reality,
- hybrid migration architectures,
- segmented key encryption doctrine,
- sovereign cybersecurity implications.
Out of scope:
- speculative AGI scenarios,
- classified offensive quantum programs,
- vendor marketing claims lacking reproducibility.
Design doctrine
This Chronicle treats confidentiality as:
not merely:
The decisive issue is not:
The decisive issue is:
Strategic differentiator
Many publications frame post-quantum security as:
- a migration timeline issue.
This Chronicle frames it differently:
- as a sovereignty and exposure problem.
Once encrypted archives, PKI chains, identity systems, diplomatic traffic, and strategic communications are harvested at scale:
- future decryption becomes irreversible.
Technical note
Express reading time: ≈ 3–4 minutes
Advanced reading time: ≈ 5–6 minutes
Full Chronicle: ≈ 35–40 minutes
Publication date: 2026-05-14
Level: Quantum Security / Cryptography / Sovereign Cybersecurity
Posture: Migration-aware, hybrid-PQC, sovereignty-oriented
Category: Digital Security
Available languages: EN · FR · CAT · ES
Impact level: 9.5 / 10 — long-tail cryptographic sovereignty risk
Editorial note — This Chronicle belongs to Digital Security. It extends Freemindtronic’s doctrine regarding:
- sovereign encryption,
- offline cybersecurity architectures,
- segmented key management,
- post-quantum resilience.
The issue addressed is not:
- immediate decryption collapse.
The issue addressed is:
- future retrospective exposure.
Specifically, this Chronicle documents why:
- Store Now, Decrypt Later strategies already transform intelligence collection doctrine long before practical quantum attacks become operational.
It also explains why:
- hybrid migration alone may prove insufficient if exposure persistence remains uncontrolled.
This work continues Freemindtronic publications regarding:
- cyber sovereignty,
- segmented encryption doctrine,
- AI-assisted cyber exposure,
- minimal-observability architectures.
Key takeaway
Quantum threats to encryption are real. However:
- practical cryptographic collapse remains constrained by fault-tolerant engineering, coherence stability, logical qubit scalability, and energy cost.
RSA and ECC face long-term structural exposure under Shor’s algorithm. AES-256 remains strategically resilient under Grover’s algorithm, especially when reinforced through:
- offline architectures,
- segmented key encryption,
- minimal metadata exposure,
- hybrid post-quantum migration.
The strategic mistake is neither panic nor denial. The strategic mistake is waiting too long before reducing long-term exposure.
- Executive summary
- Advanced summary — how real are quantum threats in 2026?
- Chronicle — quantum threats to encryption explained
- The timeline shift — why predictions keep moving
- Shor’s algorithm and asymmetric cryptography
- Grover’s algorithm and AES-256 resilience
- Logical vs physical qubits
- Store Now, Decrypt Later
- SNDL — operational reality
- Post-quantum migration acceleration
- NSA CNSA 2.0 and migration doctrine
- China’s sovereign quantum strategy
- Freemindtronic decentralized resilience doctrine
- AI-assisted cryptanalysis
- The environmental cost of quantum computing
- Signals watch — weak, medium, and strong indicators
- Weak signals
- Medium signals
- Strong signals
- Quantum honeypots
- Quantum threats to PKI infrastructures
- McEliece, HQC, and diversification
- When not to act
- Freemindtronic sovereign use cases
- Limitations and counter-arguments
- Glossary — quantum threats and PQC resilience
- FAQ — quantum threats to encryption
- What We Didn’t Cover
- Strategic outlook — preparing before the quantum threshold
Advanced summary — how real are quantum threats in 2026?
Quantum threats to encryption are simultaneously:
- real,
- misunderstood,
- strategically uneven.
Public debate often oscillates between:
- apocalyptic narratives,
- dismissive skepticism.
Both positions distort reality.
Shor’s algorithm genuinely threatens:
- RSA,
- ECC,
- Diffie-Hellman,
- traditional PKI ecosystems.
Mathematically, the danger is not speculative.
Under sufficiently large fault-tolerant universal quantum systems:
This fundamentally changes asymmetric cryptography.
However, the engineering challenge remains immense.
Real-world cryptographic attacks require:
- stable logical qubits,
- massive error correction,
- long-duration coherence,
- industrial-scale cryogenic infrastructure.
This is why timelines continue shifting.
By contrast, AES-256 behaves differently under quantum pressure.
Grover’s algorithm does not “break” AES mathematically.
Instead, it reduces brute-force complexity approximately from:
Even after that reduction:
- AES-256 remains operationally prohibitive to attack.
This distinction is critical.
The timeline shift — why quantum predictions keep moving
For more than three decades, quantum computing lived inside a paradox.
Physicists understood the mathematics. Cryptographers understood the implications. Intelligence agencies understood the strategic consequences. Yet industry lacked the engineering capability required to transform theoretical quantum computation into operational cryptanalytic power.
That distinction still defines the entire debate surrounding Quantum Threats to Encryption.
In 1994, Peter Shor introduced an algorithm capable of changing modern cryptography forever. At the time, the discovery appeared almost abstract because no quantum computer could execute it at meaningful scale. Classical encryption continued to dominate global infrastructure without immediate disruption.
Three decades later, the mathematics remains unchanged.
What changed is the geopolitical urgency surrounding its possible implementation.
When IBM Quantum published successive fault-tolerant roadmaps, public attention focused primarily on raw qubit counts. Shortly afterward, Google Quantum AI shifted the conversation toward logical qubits, coherence duration, and quantum error correction. Meanwhile, Microsoft Quantum pursued a radically different strategy through Majorana-based topological qubits designed to reduce fault-correction overhead itself.
At the same time, China accelerated sovereign deployment through hybrid quantum-secure infrastructure combining:
- quantum communication networks,
- state-operated telecom systems,
- post-quantum cryptography,
- centralized infrastructure governance.
The quantum race therefore evolved into something far more complex than a scientific competition.
It became:
- a sovereignty race,
- a cybersecurity race,
- an infrastructure race,
- and increasingly, an intelligence race.
Strategic inflection point
The quantum transition did not begin when quantum computers became operationally dangerous.
It began when governments, standards agencies, and critical infrastructures started behaving as if post-quantum migration had already become inevitable.
That psychological threshold may ultimately matter more than the first practical quantum attack itself.
Yet despite accelerating announcements, practical cryptographic collapse remains constrained by one decisive bottleneck:
fault-tolerant scalability.
The challenge is no longer proving that quantum mechanics works computationally.
The challenge is sustaining stable quantum operations long enough to execute cryptographically relevant workloads under industrial conditions.
That requirement introduces simultaneous constraints involving:
- logical qubit stability,
- continuous error correction,
- cryogenic coherence,
- electromagnetic isolation,
- and extreme synchronization precision.
Unlike classical processors, quantum systems cannot simply “scale upward” through transistor miniaturization. Every additional layer of error correction introduces energy cost, architectural complexity, and instability amplification.
This explains why quantum timelines constantly shift.
The mathematics behind quantum cryptanalysis already exists.
Industrial fault tolerance does not.
Mathematical perspective — RSA factorization complexity
RSA security fundamentally depends on one deceptively simple relationship:
N = p times q
where p and q are extremely large prime numbers.
Classically, factoring large integers remains computationally prohibitive at sufficient scale. However, Shor’s algorithm theoretically reduces the problem toward polynomial-time complexity under a sufficiently large fault-tolerant quantum computer:
O((log N)^3)
This theoretical transition explains why RSA, ECC, and Diffie-Hellman remain structurally exposed in long-term quantum scenarios.
Craig Gidney and Martin Ekerå significantly reshaped modern cryptographic forecasting when they estimated that practical RSA-2048 factorization would likely require:
- millions of physical qubits,
- thousands of stable logical qubits,
- and sustained coherent execution lasting several hours.
Their work transformed the conversation surrounding “Store Now, Decrypt Later” strategies because it reframed quantum threats as a long-term archival risk rather than an immediate operational collapse.
Read the Gidney & Ekerå quantum resource estimate study.
Why qubit announcements are frequently misunderstood
Public narratives often confuse raw qubit quantity with cryptographic capability.
That interpretation is deeply misleading.
A quantum processor containing several thousand noisy physical qubits does not automatically threaten RSA-2048 or ECC if:
- error rates remain unstable,
- logical coherence collapses rapidly,
- fault correction fails continuously,
- or Shor’s algorithm cannot execute reliably.
This is precisely why cybersecurity agencies increasingly evaluate quantum announcements according to:
- logical qubit maturity,
- coherence stability,
- fault-tolerant execution capability,
- and realistic cryptanalytic feasibility.
Error-correction scaling problem
The practical difficulty emerges from quantum error correction itself:
1 logical qubit gg 10^3 – 10^4 physical qubits
This ratio varies according to architecture, coherence quality, and error thresholds. Consequently, public announcements regarding raw physical qubit counts rarely translate into immediate cryptographic capability.
Quantum realism versus quantum marketing
The cybersecurity ecosystem increasingly suffers from a dangerous confusion between:
- laboratory milestones,
- commercial positioning,
- scientific experimentation,
- and operational cryptographic threat.
Quantum supremacy demonstrations may represent extraordinary scientific achievements without creating immediate cryptanalytic capability against:
- RSA-2048,
- ECC infrastructures,
- AES-256,
- or sovereign PKI ecosystems.
This distinction matters strategically because fear-driven migration can become as dangerous as delayed migration itself.
Poorly executed post-quantum deployment may:
- break trust chains,
- create interoperability failures,
- fragment infrastructure governance,
- or introduce immature cryptographic dependencies.
That is why agencies such as:
now promote measured migration strategies centered around:
- crypto agility,
- hybrid deployment,
- inventory visibility,
- and phased interoperability testing.
⮞ Summary
Quantum progress is real.
Quantum cryptographic collapse remains hypothetical.
The decisive variable is no longer whether quantum computation is scientifically possible.
The decisive variable is whether fault-tolerant quantum systems can sustain stable cryptanalytic execution at industrial scale before defensive migration fundamentally reshapes global cryptographic infrastructure.
The paradox of quantum cybersecurity is therefore profound.
The first practical quantum attack may occur long after institutions already transformed their infrastructures in anticipation of it.
Yet if organizations wait until operational attacks become publicly visible, migration may already be too late for archives harvested decades earlier.
That is why quantum resilience is no longer merely a mathematical discussion.
It has become a doctrine of time, exposure, sovereignty, and irreversible confidentiality preservation.
The timeline shift — why quantum predictions keep moving
For more than three decades, quantum computing lived inside a paradox.
Physicists understood the mathematics. Cryptographers understood the implications. Intelligence agencies understood the strategic consequences. Yet industry lacked the engineering capability required to transform theoretical quantum computation into operational cryptanalytic power.
That distinction still defines the entire debate surrounding Quantum Threats to Encryption.
In 1994, Peter Shor introduced an algorithm capable of changing modern cryptography forever. At the time, the discovery appeared almost abstract because no quantum computer could execute it at meaningful scale. Classical encryption continued to dominate global infrastructure without immediate disruption.
Three decades later, the mathematics remains unchanged.
What changed is the geopolitical urgency surrounding its possible implementation.
When IBM Quantum published successive fault-tolerant roadmaps, public attention focused primarily on raw qubit counts. Shortly afterward, Google Quantum AI shifted the conversation toward logical qubits, coherence duration, and quantum error correction. Meanwhile, Microsoft Quantum pursued a radically different strategy through Majorana-based topological qubits designed to reduce fault-correction overhead itself.
At the same time, China accelerated sovereign deployment through hybrid quantum-secure infrastructure combining:
- quantum communication networks,
- state-operated telecom systems,
- post-quantum cryptography,
- centralized infrastructure governance.
The quantum race therefore evolved into something far more complex than a scientific competition.
It became:
- a sovereignty race,
- a cybersecurity race,
- an infrastructure race,
- and increasingly, an intelligence race.
Strategic inflection point
The quantum transition did not begin when quantum computers became operationally dangerous.
It began when governments, standards agencies, and critical infrastructures started behaving as if post-quantum migration had already become inevitable.
That psychological threshold may ultimately matter more than the first practical quantum attack itself.
Yet despite accelerating announcements, practical cryptographic collapse remains constrained by one decisive bottleneck:
fault-tolerant scalability.
The challenge is no longer proving that quantum mechanics works computationally.
The challenge is sustaining stable quantum operations long enough to execute cryptographically relevant workloads under industrial conditions.
That requirement introduces simultaneous constraints involving:
- logical qubit stability,
- continuous error correction,
- cryogenic coherence,
- electromagnetic isolation,
- and extreme synchronization precision.
Unlike classical processors, quantum systems cannot simply “scale upward” through transistor miniaturization. Every additional layer of error correction introduces energy cost, architectural complexity, and instability amplification.
This explains why quantum timelines constantly shift.
The mathematics behind quantum cryptanalysis already exists.
Industrial fault tolerance does not.
Mathematical perspective — RSA factorization complexity
RSA security fundamentally depends on one deceptively simple relationship:
N = p times q
where p and q are extremely large prime numbers.
Classically, factoring large integers remains computationally prohibitive at sufficient scale. However, Shor’s algorithm theoretically reduces the problem toward polynomial-time complexity under a sufficiently large fault-tolerant quantum computer:
O((log N)^3)
This theoretical transition explains why RSA, ECC, and Diffie-Hellman remain structurally exposed in long-term quantum scenarios.
Craig Gidney and Martin Ekerå significantly reshaped modern cryptographic forecasting when they estimated that practical RSA-2048 factorization would likely require:
- millions of physical qubits,
- thousands of stable logical qubits,
- and sustained coherent execution lasting several hours.
Their work transformed the conversation surrounding “Store Now, Decrypt Later” strategies because it reframed quantum threats as a long-term archival risk rather than an immediate operational collapse.
Read the Gidney & Ekerå quantum resource estimate study.
Why qubit announcements are frequently misunderstood
Public narratives often confuse raw qubit quantity with cryptographic capability.
That interpretation is deeply misleading.
A quantum processor containing several thousand noisy physical qubits does not automatically threaten RSA-2048 or ECC if:
- error rates remain unstable,
- logical coherence collapses rapidly,
- fault correction fails continuously,
- or Shor’s algorithm cannot execute reliably.
This is precisely why cybersecurity agencies increasingly evaluate quantum announcements according to:
- logical qubit maturity,
- coherence stability,
- fault-tolerant execution capability,
- and realistic cryptanalytic feasibility.
Error-correction scaling problem
The practical difficulty emerges from quantum error correction itself:
1 logical qubit gg 10^3 – 10^4 physical qubits
This ratio varies according to architecture, coherence quality, and error thresholds. Consequently, public announcements regarding raw physical qubit counts rarely translate into immediate cryptographic capability.
Quantum realism versus quantum marketing
The cybersecurity ecosystem increasingly suffers from a dangerous confusion between:
- laboratory milestones,
- commercial positioning,
- scientific experimentation,
- and operational cryptographic threat.
Quantum supremacy demonstrations may represent extraordinary scientific achievements without creating immediate cryptanalytic capability against:
- RSA-2048,
- ECC infrastructures,
- AES-256,
- or sovereign PKI ecosystems.
This distinction matters strategically because fear-driven migration can become as dangerous as delayed migration itself.
Poorly executed post-quantum deployment may:
- break trust chains,
- create interoperability failures,
- fragment infrastructure governance,
- or introduce immature cryptographic dependencies.
That is why agencies such as:
now promote measured migration strategies centered around:
- crypto agility,
- hybrid deployment,
- inventory visibility,
- and phased interoperability testing.
⮞ Summary
Quantum progress is real.
Quantum cryptographic collapse remains hypothetical.
The decisive variable is no longer whether quantum computation is scientifically possible.
The decisive variable is whether fault-tolerant quantum systems can sustain stable cryptanalytic execution at industrial scale before defensive migration fundamentally reshapes global cryptographic infrastructure.
The paradox of quantum cybersecurity is therefore profound.
The first practical quantum attack may occur long after institutions already transformed their infrastructures in anticipation of it.
Yet if organizations wait until operational attacks become publicly visible, migration may already be too late for archives harvested decades earlier.
That is why quantum resilience is no longer merely a mathematical discussion.
It has become a doctrine of time, exposure, sovereignty, and irreversible confidentiality preservation.
Logical versus physical qubits — the engineering wall behind quantum mythology
One of the most damaging misconceptions in mainstream discussions about quantum computing concerns the word itself:
qubit.
Public communication often treats all qubits as equivalent.
They are not.
This confusion profoundly distorts the real state of quantum capability.
When technology headlines announce:
- 1,000 qubits,
- 5,000 qubits,
- or even 10,000 qubits,
many readers instinctively assume that practical cryptographic collapse is approaching.
That interpretation is incorrect.
The overwhelming majority of currently announced qubits remain:
- noisy,
- unstable,
- short-lived,
- and unsuitable for sustained fault-tolerant cryptographic computation.
The distinction between:
- physical qubits,
- and logical qubits
therefore becomes the central reality separating laboratory progress from operational quantum cryptanalysis.
Physical qubits are fragile quantum hardware elements
Physical qubits represent the raw hardware layer of quantum systems.
Depending on the architecture, they may rely on:
- superconducting circuits,
- trapped ions,
- photonic systems,
- neutral atoms,
- or experimental topological structures.
Unlike classical bits, qubits suffer from continuous instability.
They are vulnerable to:
- thermal fluctuations,
- electromagnetic interference,
- environmental noise,
- decoherence,
- measurement disturbance.
In practice, quantum information decays extremely rapidly unless sophisticated correction mechanisms stabilize the system continuously.
This creates a brutal engineering constraint:
raw qubit quantity alone means very little.
The decoherence problem
Quantum states remain usable only while coherence survives.
Quantum coherence time is typically represented as:
T_2
The longer the coherence time, the longer quantum operations can execute before information collapses into noise.
Cryptographically relevant quantum systems require:
- long coherence duration,
- extremely low error rates,
- continuous stabilization,
- and synchronized correction.
Without those conditions, Shor’s algorithm cannot execute reliably at operational scale.
Logical qubits are the real strategic resource
Logical qubits are fundamentally different.
A logical qubit is not a single hardware element.
It is a stabilized quantum abstraction created through:
- massive redundancy,
- continuous error correction,
- synchronized control systems,
- and fault-tolerant computation.
In many projected architectures:
- hundreds,
- thousands,
- or even tens of thousands
of physical qubits may be required to create one stable logical qubit.
This is the hidden reality rarely visible in marketing announcements.
The surface-code correction model
Most current fault-tolerant roadmaps rely heavily on surface-code error correction.
Its objective is simple in principle:
detect quantum errors faster than they accumulate.
The challenge is colossal in practice.
The logical error rate approximately depends on:
- physical error rate,
- code distance,
- measurement fidelity,
- synchronization precision.
The system must continuously detect and correct errors without destroying the quantum state itself.
That requirement transforms quantum computing into one of the most complex synchronization problems ever attempted in engineering history.
Why fault tolerance changes everything
A quantum computer capable of threatening RSA-2048 is not simply:
- a larger quantum computer.
It is:
- a stable,
- fault-tolerant,
- energy-sustainable,
- industrially synchronized quantum infrastructure.
That distinction explains why quantum timelines continue shifting despite continuous progress.
Why millions of qubits may still be insufficient
One of the most frequently misunderstood projections concerns RSA factorization estimates.
Studies from:
- Craig Gidney,
- Martin Ekerå,
- IBM Quantum researchers,
- Google Quantum AI teams
suggest that practical RSA-2048 attacks may require:
- millions of physical qubits,
- thousands of stable logical qubits,
- hours of coherent computation,
- continuous fault correction.
This estimate changes the public narrative completely.
The issue is no longer:
“Can quantum computation exist?”
The issue becomes:
“Can industrial-scale fault tolerance exist economically and sustainably?”
That engineering barrier remains unresolved.
Why D-Wave systems do not threaten RSA
Quantum communication frequently confuses:
- quantum annealers,
- and universal gate-based quantum computers.
They are not equivalent.
D-Wave systems specialize primarily in optimization problems using quantum annealing.
They do not execute universal fault-tolerant Shor-style cryptanalysis against RSA or ECC infrastructures.
This distinction matters enormously because:
- high qubit counts alone do not imply cryptographic capability,
- annealing architectures differ fundamentally from gate-based systems,
- universality remains essential for practical Shor execution.
Consequently, sensationalist headlines often exaggerate operational cryptographic risk by ignoring architectural differences entirely.
⚠ Strategic clarification
A 5,000-qubit noisy annealer may remain cryptographically irrelevant.
Meanwhile, a much smaller fault-tolerant universal system could become strategically transformative.
The decisive variable is not raw qubit quantity.
The decisive variable is stable logical capability.
Why Microsoft’s topological approach matters
Microsoft’s quantum strategy differs significantly from:
- IBM’s superconducting approach,
- Google’s coherence optimization strategy,
- IonQ’s trapped-ion systems.
Microsoft focuses heavily on:
topological qubits.
The objective is to reduce error-correction overhead directly at the hardware level.
If successful, topological architectures could dramatically lower:
- physical qubit requirements,
- correction complexity,
- synchronization burden,
- energy consumption.
However, practical implementation remains experimental and controversial.
This uncertainty explains why quantum roadmaps remain probabilistic rather than deterministic.
The energy reality behind cryptographically relevant quantum systems
Another overlooked issue concerns energy economics.
Fault-tolerant quantum systems require:
- cryogenic cooling near absolute zero,
- continuous stabilization,
- massive electrical precision,
- persistent synchronization layers,
- advanced fabrication environments.
As systems scale:
- cooling requirements increase,
- electrical stability constraints intensify,
- infrastructure concentration accelerates.
Consequently, practical quantum cryptanalysis may remain restricted to:
- major states,
- national laboratories,
- strategic intelligence agencies,
- or hyperscale technological coalitions.
Quantum supremacy therefore does not automatically imply universal attacker democratization.
The real timeline variable is engineering maturity
This is why predictions continuously move.
The mathematical theory already exists.
The engineering maturity does not.
Quantum cryptanalysis requires convergence between:
- fault tolerance,
- error correction,
- energy sustainability,
- industrial synchronization,
- and scalable manufacturing.
Any weakness inside one layer destabilizes the entire architecture.
That is why serious quantum-security analysts increasingly avoid deterministic dates.
The real issue is not whether quantum progress continues.
It certainly will.
The real issue is:
when fault-tolerant quantum systems become economically sustainable at cryptographically relevant scale.
✓ Strategic interpretation
Quantum cybersecurity is no longer constrained primarily by mathematics.
It is constrained by industrial physics.
That distinction explains why:
- migration urgency exists now,
- while operational cryptographic collapse may still remain years away.
The danger comes from the permanence of harvested exposure, not from tomorrow morning’s decryption capability.
Store Now, Decrypt Later — the silent accumulation of future exposure
Among all quantum-security concepts, none reshaped strategic thinking more profoundly than:
Store Now, Decrypt Later.
Often abbreviated:
SNDL.
The principle appears deceptively simple.
An adversary intercepts encrypted communications today:
- diplomatic traffic,
- VPN sessions,
- satellite communications,
- industrial archives,
- government exchanges,
- financial records.
The encrypted data may remain unreadable now.
However, if the attacker preserves:
- ciphertext,
- public keys,
- metadata,
- protocol context,
- identity traces,
future fault-tolerant quantum systems may eventually decrypt those archives retroactively.
This changes the entire philosophy of cybersecurity timing.
The threat begins before decryption becomes possible
Traditional cybersecurity logic assumed:
- if encrypted content survives today,
- confidentiality survives today.
Quantum reality changes that assumption.
The moment encrypted information becomes interceptable and permanently archivable, future exposure begins immediately.
That is why quantum migration urgency exists years before practical cryptographic collapse.
The threat timeline no longer begins at:
“successful decryption.”
The threat timeline begins at:
“successful collection.”
The strategic asymmetry of SNDL
Defenders must protect information continuously.
Attackers only need:
- one successful interception,
- one preserved archive,
- and enough patience.
Once archives are harvested permanently, future confidentiality becomes impossible to retroactively restore.
Logical versus physical qubits — the engineering wall behind quantum mythology
One of the most damaging misconceptions in mainstream discussions about quantum computing concerns the word itself:
qubit.
Public communication often treats all qubits as equivalent.
They are not.
This confusion profoundly distorts the real state of quantum capability.
When technology headlines announce:
- 1,000 qubits,
- 5,000 qubits,
- or even 10,000 qubits,
many readers instinctively assume that practical cryptographic collapse is approaching.
That interpretation is incorrect.
The overwhelming majority of currently announced qubits remain:
- noisy,
- unstable,
- short-lived,
- and unsuitable for sustained fault-tolerant cryptographic computation.
The distinction between:
- physical qubits,
- and logical qubits
therefore becomes the central reality separating laboratory progress from operational quantum cryptanalysis.
Physical qubits are fragile quantum hardware elements
Physical qubits represent the raw hardware layer of quantum systems.
Depending on the architecture, they may rely on:
- superconducting circuits,
- trapped ions,
- photonic systems,
- neutral atoms,
- or experimental topological structures.
Unlike classical bits, qubits suffer from continuous instability.
They are vulnerable to:
- thermal fluctuations,
- electromagnetic interference,
- environmental noise,
- decoherence,
- measurement disturbance.
In practice, quantum information decays extremely rapidly unless sophisticated correction mechanisms stabilize the system continuously.
This creates a brutal engineering constraint:
raw qubit quantity alone means very little.
The decoherence problem
Quantum states remain usable only while coherence survives.
Quantum coherence time is typically represented as:
T_2
The longer the coherence time, the longer quantum operations can execute before information collapses into noise.
Cryptographically relevant quantum systems require:
- long coherence duration,
- extremely low error rates,
- continuous stabilization,
- and synchronized correction.
Without those conditions, Shor’s algorithm cannot execute reliably at operational scale.
Logical qubits are the real strategic resource
Logical qubits are fundamentally different.
A logical qubit is not a single hardware element.
It is a stabilized quantum abstraction created through:
- massive redundancy,
- continuous error correction,
- synchronized control systems,
- and fault-tolerant computation.
In many projected architectures:
- hundreds,
- thousands,
- or even tens of thousands
of physical qubits may be required to create one stable logical qubit.
This is the hidden reality rarely visible in marketing announcements.
The surface-code correction model
Most current fault-tolerant roadmaps rely heavily on surface-code error correction.
Its objective is simple in principle:
detect quantum errors faster than they accumulate.
The challenge is colossal in practice.
The logical error rate approximately depends on:
- physical error rate,
- code distance,
- measurement fidelity,
- synchronization precision.
The system must continuously detect and correct errors without destroying the quantum state itself.
That requirement transforms quantum computing into one of the most complex synchronization problems ever attempted in engineering history.
Why fault tolerance changes everything
A quantum computer capable of threatening RSA-2048 is not simply:
- a larger quantum computer.
It is:
- a stable,
- fault-tolerant,
- energy-sustainable,
- industrially synchronized quantum infrastructure.
That distinction explains why quantum timelines continue shifting despite continuous progress.
Why millions of qubits may still be insufficient
One of the most frequently misunderstood projections concerns RSA factorization estimates.
Studies from:
- Craig Gidney,
- Martin Ekerå,
- IBM Quantum researchers,
- Google Quantum AI teams
suggest that practical RSA-2048 attacks may require:
- millions of physical qubits,
- thousands of stable logical qubits,
- hours of coherent computation,
- continuous fault correction.
This estimate changes the public narrative completely.
The issue is no longer:
“Can quantum computation exist?”
The issue becomes:
“Can industrial-scale fault tolerance exist economically and sustainably?”
That engineering barrier remains unresolved.
Why D-Wave systems do not threaten RSA
Quantum communication frequently confuses:
- quantum annealers,
- and universal gate-based quantum computers.
They are not equivalent.
D-Wave systems specialize primarily in optimization problems using quantum annealing.
They do not execute universal fault-tolerant Shor-style cryptanalysis against RSA or ECC infrastructures.
This distinction matters enormously because:
- high qubit counts alone do not imply cryptographic capability,
- annealing architectures differ fundamentally from gate-based systems,
- universality remains essential for practical Shor execution.
Consequently, sensationalist headlines often exaggerate operational cryptographic risk by ignoring architectural differences entirely.
⚠ Strategic clarification
A 5,000-qubit noisy annealer may remain cryptographically irrelevant.
Meanwhile, a much smaller fault-tolerant universal system could become strategically transformative.
The decisive variable is not raw qubit quantity.
The decisive variable is stable logical capability.
Why Microsoft’s topological approach matters
Microsoft’s quantum strategy differs significantly from:
- IBM’s superconducting approach,
- Google’s coherence optimization strategy,
- IonQ’s trapped-ion systems.
Microsoft focuses heavily on:
topological qubits.
The objective is to reduce error-correction overhead directly at the hardware level.
If successful, topological architectures could dramatically lower:
- physical qubit requirements,
- correction complexity,
- synchronization burden,
- energy consumption.
However, practical implementation remains experimental and controversial.
This uncertainty explains why quantum roadmaps remain probabilistic rather than deterministic.
The energy reality behind cryptographically relevant quantum systems
Another overlooked issue concerns energy economics.
Fault-tolerant quantum systems require:
- cryogenic cooling near absolute zero,
- continuous stabilization,
- massive electrical precision,
- persistent synchronization layers,
- advanced fabrication environments.
As systems scale:
- cooling requirements increase,
- electrical stability constraints intensify,
- infrastructure concentration accelerates.
Consequently, practical quantum cryptanalysis may remain restricted to:
- major states,
- national laboratories,
- strategic intelligence agencies,
- or hyperscale technological coalitions.
Quantum supremacy therefore does not automatically imply universal attacker democratization.
The real timeline variable is engineering maturity
This is why predictions continuously move.
The mathematical theory already exists.
The engineering maturity does not.
Quantum cryptanalysis requires convergence between:
- fault tolerance,
- error correction,
- energy sustainability,
- industrial synchronization,
- and scalable manufacturing.
Any weakness inside one layer destabilizes the entire architecture.
That is why serious quantum-security analysts increasingly avoid deterministic dates.
The real issue is not whether quantum progress continues.
It certainly will.
The real issue is:
when fault-tolerant quantum systems become economically sustainable at cryptographically relevant scale.
✓ Strategic interpretation
Quantum cybersecurity is no longer constrained primarily by mathematics.
It is constrained by industrial physics.
That distinction explains why:
- migration urgency exists now,
- while operational cryptographic collapse may still remain years away.
The danger comes from the permanence of harvested exposure, not from tomorrow morning’s decryption capability.
Store Now, Decrypt Later — the silent accumulation of future exposure
Among all quantum-security concepts, none reshaped strategic thinking more profoundly than:
Store Now, Decrypt Later.
Often abbreviated:
SNDL.
The principle appears deceptively simple.
An adversary intercepts encrypted communications today:
- diplomatic traffic,
- VPN sessions,
- satellite communications,
- industrial archives,
- government exchanges,
- financial records.
The encrypted data may remain unreadable now.
However, if the attacker preserves:
- ciphertext,
- public keys,
- metadata,
- protocol context,
- identity traces,
future fault-tolerant quantum systems may eventually decrypt those archives retroactively.
This changes the entire philosophy of cybersecurity timing.
The threat begins before decryption becomes possible
Traditional cybersecurity logic assumed:
- if encrypted content survives today,
- confidentiality survives today.
Quantum reality changes that assumption.
The moment encrypted information becomes interceptable and permanently archivable, future exposure begins immediately.
That is why quantum migration urgency exists years before practical cryptographic collapse.
The threat timeline no longer begins at:
“successful decryption.”
The threat timeline begins at:
“successful collection.”
The strategic asymmetry of SNDL
Defenders must protect information continuously.
Attackers only need:
- one successful interception,
- one preserved archive,
- and enough patience.
Once archives are harvested permanently, future confidentiality becomes impossible to retroactively restore.
Post-quantum migration — why the world already acts before quantum collapse exists
One of the most revealing transformations in cybersecurity since 2024 is not technological.
It is psychological.
For decades, post-quantum cryptography remained largely confined to:
- academic laboratories,
- mathematical conferences,
- government cryptographic agencies,
- and niche strategic research programs.
That period is over.
Today, governments, intelligence agencies, cloud providers, telecom operators, hyperscalers, defense contractors, and critical infrastructure organizations increasingly behave as if post-quantum migration is no longer optional.
This shift matters enormously.
Because it reveals a strategic consensus:
the risk is now considered inevitable enough to justify immediate preparation.
NIST changed the global cybersecurity timeline
The turning point accelerated when the National Institute of Standards and Technology (NIST) finalized major post-quantum cryptographic standards.
For the first time, governments and industries received standardized migration targets.
That decision transformed post-quantum cryptography from:
- a theoretical research field,
into:
- an operational governance issue.
The most important standards include:
- ML-KEM (FIPS 203) derived from CRYSTALS-Kyber,
- ML-DSA (FIPS 204) derived from CRYSTALS-Dilithium,
- SLH-DSA (FIPS 205) based on SPHINCS+,
- and the continued evaluation of HQC.
These standards now influence:
- government procurement,
- critical infrastructure compliance,
- future PKI design,
- long-term archival strategies,
- cloud security architectures.
Why standardization changes everything
Before standardization:
- organizations hesitated,
- vendors waited,
- migration remained speculative.
After standardization:
- roadmaps become enforceable,
- compliance frameworks evolve,
- procurement requirements shift,
- risk governance becomes measurable.
The strategic transition therefore begins long before practical quantum attacks exist.
NSA CNSA 2.0 accelerated sovereign awareness
Another major inflection point emerged through:
NSA CNSA 2.0.
The document profoundly influenced international cybersecurity doctrine because it effectively acknowledged:
- RSA and ECC face structural long-term exposure,
- migration requires years or decades,
- crypto agility becomes mandatory,
- inventory visibility becomes strategic.
This was not merely technical guidance.
It was a geopolitical signal.
Once major intelligence ecosystems publicly begin migration planning, the rest of the world inevitably follows.
The migration challenge is infrastructural, not mathematical
One of the greatest public misunderstandings concerns the nature of migration itself.
Replacing cryptography is not like updating a mobile application.
Modern cryptography is deeply embedded inside:
- industrial control systems,
- banking infrastructure,
- government identity ecosystems,
- embedded hardware,
- telecommunications,
- military systems,
- cloud trust architectures.
Many infrastructures were designed decades ago.
Some cannot be easily upgraded at all.
Others depend on:
- legacy firmware,
- fixed silicon,
- regulatory certification chains,
- vendor interoperability constraints.
Consequently, migration itself becomes one of the largest cybersecurity engineering transitions in modern history.
Why hybrid cryptography dominates real-world strategy
No serious organization expects instantaneous replacement of classical cryptography.
Instead, hybrid deployment increasingly dominates operational planning.
Hybrid cryptography combines:
- classical algorithms,
- post-quantum algorithms,
- parallel authentication paths,
- segmented transition models.
The objective is not immediate perfection.
The objective is continuity.
Organizations need to maintain:
- interoperability,
- trust persistence,
- operational stability,
- regulatory compliance.
during a transition that may span decades.
✓ Operational reality
The greatest near-term cybersecurity danger may not be quantum cryptanalysis itself.
It may be poorly executed migration:
- broken certificate chains,
- incompatible infrastructures,
- identity failures,
- operational fragmentation.
Migration discipline therefore matters as much as cryptographic strength.
Why PKI infrastructures face systemic pressure
Public Key Infrastructure represents one of the most exposed strategic layers in the quantum transition.
Modern PKI underpins:
- TLS authentication,
- software signing,
- government identity systems,
- enterprise authentication,
- secure email,
- mobile trust ecosystems.
Most current PKI deployments still rely heavily on:
- RSA,
- ECC.
This creates systemic migration pressure across virtually the entire digital economy.
The challenge is staggering because PKI migration affects simultaneously:
- certificate authorities,
- hardware security modules,
- browsers,
- mobile ecosystems,
- embedded systems,
- industrial hardware.
Failure inside one layer may cascade across entire trust ecosystems.
Why China follows a radically different quantum strategy
The geopolitical dimension becomes even clearer when examining China’s approach.
Unlike Western migration models centered primarily on standards and interoperability, China increasingly combines:
- Quantum Key Distribution (QKD),
- PQC deployment,
- state-operated infrastructure,
- centralized governance.
Projects associated with:
- China Telecom Quantum Group,
- Quantum Secret,
- Quantum Cloud Seal
illustrate this sovereign infrastructure strategy.
The Chinese model prioritizes:
- centralized resilience,
- national coordination,
- state-managed observability.
This creates a strategic paradox.
A system may become:
- quantum resistant,
while simultaneously becoming:
- fully centralized,
- highly observable,
- state-controlled.
⮞ Sovereignty paradox
Quantum-safe infrastructure does not automatically guarantee digital freedom.
A cryptographically resilient system may still centralize:
- identity visibility,
- behavioral monitoring,
- institutional control.
Future cybersecurity competition therefore concerns both:
- encryption strength,
- and sovereignty architecture.
Why Freemindtronic’s doctrine diverges fundamentally
Freemindtronic’s sovereign approach follows a radically different philosophy.
Instead of maximizing centralized visibility, the doctrine prioritizes:
- offline operation,
- segmented key encryption,
- NFC HSM isolation,
- distributed trust,
- minimal metadata exposure.
This architecture assumes that future threats will increasingly combine:
- quantum acceleration,
- AI-assisted inference,
- mass metadata aggregation,
- behavioral correlation.
Consequently, resilience depends not only on stronger algorithms.
It depends on reducing observable attack surfaces themselves.
Why crypto agility becomes the decisive capability
One lesson increasingly dominates quantum-security strategy:
no algorithm should be treated as eternal.
History repeatedly demonstrates that:
- cryptographic assumptions evolve,
- new attacks emerge,
- mathematical certainty remains temporary.
This is precisely why:
- cryptographic diversity,
- layered defense,
- migration flexibility,
- segmented architectures
become strategically essential.
Future resilience may depend less on finding:
“the perfect algorithm”
and more on maintaining:
“the ability to evolve continuously without systemic collapse.”
Key strategic insight
The quantum transition is not a future event.
It is already underway operationally through:
- migration planning,
- inventory mapping,
- hybrid deployment,
- sovereign infrastructure redesign.
The organizations adapting earliest are not necessarily the ones expecting immediate quantum collapse.
They are the ones recognizing that cryptographic lifecycles now extend beyond the lifespan of current computational assumptions.
AI-assisted cryptanalysis — when quantum acceleration converges with machine-scale inference
Quantum computing is not the only force transforming future cryptographic risk.
Artificial intelligence increasingly changes the structure of cyber operations themselves.
This evolution matters because many future attacks may not depend exclusively on:
- breaking encryption mathematically.
Instead, they may depend on:
- correlating metadata,
- predicting behavior,
- mapping identities,
- reconstructing exposure patterns.
AI fundamentally amplifies those capabilities.
Why AI changes cybersecurity economics
Modern AI systems excel at:
- pattern recognition,
- correlation analysis,
- anomaly detection,
- behavioral inference,
- predictive modeling.
Those capabilities already transform:
- fraud detection,
- advertising systems,
- intelligence analysis,
- cyber threat monitoring.
The same mechanisms can also accelerate offensive operations dramatically.
Poorly segmented infrastructures become increasingly vulnerable to:
- credential mapping,
- identity correlation,
- behavioral fingerprinting,
- metadata exploitation.
Even before practical quantum decryption exists.
The future threat model is hybrid, not isolated
For years, cybersecurity discussions separated threats into categories:
- cryptography,
- artificial intelligence,
- network intrusion,
- identity compromise.
That separation increasingly disappears.
Future attack ecosystems will likely combine:
- AI-assisted reconnaissance,
- automated metadata analysis,
- large-scale behavioral profiling,
- and eventually quantum-assisted cryptanalysis.
This convergence changes the strategic landscape profoundly.
A future attacker may not need to break every encryption layer directly.
Instead, the attacker may:
- identify weak exposure points,
- predict user behavior,
- reconstruct fragmented identities,
- prioritize vulnerable archives automatically.
Quantum capability then becomes an accelerator inside a broader intelligence ecosystem.
Metadata becomes the real battlefield
One of the most underestimated realities of modern cybersecurity is that metadata often matters more than encrypted content itself.
Metadata reveals:
- who communicates,
- when communications occur,
- how often exchanges happen,
- which infrastructures interact,
- what behavioral patterns emerge.
Even perfectly encrypted content may still expose strategic intelligence through metadata continuity.
AI systems are exceptionally effective at exploiting those patterns.
This creates a dangerous asymmetry:
- encrypted content may survive,
- while strategic visibility collapses.
⚠ The hidden exposure problem
Future quantum resilience will not depend exclusively on:
- algorithmic robustness.
It will increasingly depend on:
- metadata minimization,
- behavioral fragmentation,
- reduced observability,
- distributed trust architectures.
A perfectly encrypted infrastructure that continuously leaks metadata may still become strategically transparent.
Why centralized cloud architectures amplify long-term exposure
Modern digital ecosystems increasingly centralize:
- identity management,
- authentication,
- communications,
- storage,
- behavioral telemetry.
This concentration improves:
- scalability,
- automation,
- service continuity.
However, it also creates unprecedented aggregation surfaces.
Large centralized infrastructures allow attackers to:
- harvest massive metadata volumes,
- correlate identities globally,
- build long-term behavioral models,
- archive cryptographic material continuously.
The strategic danger is cumulative.
Every year of uninterrupted centralized exposure strengthens future retrospective attack capability.
Why segmented architectures resist AI-scale inference
This is precisely where segmented key encryption becomes strategically important.
Freemindtronic’s doctrine assumes that future adversaries increasingly rely on:
- correlation capability,
- visibility continuity,
- data concentration,
- behavioral persistence.
Segmented architectures directly weaken those assumptions.
Instead of exposing:
- one centralized trust structure,
they fragment:
- authentication,
- storage,
- identity visibility,
- key reconstruction paths.
This transforms cybersecurity economics fundamentally.
The attacker no longer faces:
- a purely mathematical problem.
The attacker faces:
- an operational fragmentation problem.
Why offline infrastructures matter again
For years, cybersecurity favored:
- continuous connectivity,
- cloud synchronization,
- centralized orchestration.
Quantum-era threat models increasingly reverse that logic.
Offline infrastructures now regain strategic relevance because they reduce:
- continuous observability,
- mass interception capability,
- metadata aggregation,
- behavioral telemetry persistence.
This explains the growing strategic value of:
- offline NFC HSM systems,
- segmented authentication,
- local sovereign encryption,
- distributed trust architectures.
The objective is not technological nostalgia.
The objective is reducing:
persistent attack visibility.
✓ Sovereign architecture principle
The safest cryptographic surface is not necessarily the one using the newest algorithm.
The safest surface is often the one adversaries cannot:
- continuously observe,
- aggregate,
- profile,
- or archive at industrial scale.
The environmental cost of quantum computing — the overlooked limit to quantum supremacy
Quantum computing discussions frequently focus on:
- speed,
- cryptographic disruption,
- scientific breakthroughs.
Far fewer discussions examine:
energy sustainability.
Yet energy economics may become one of the decisive constraints limiting large-scale quantum deployment.
Quantum computing requires extreme physical conditions
Most modern quantum systems require:
- cryogenic cooling near absolute zero,
- continuous electromagnetic stabilization,
- ultra-precise synchronization,
- persistent error correction,
- highly specialized fabrication environments.
Superconducting systems often operate around:
15 text{ millikelvin}
which is colder than deep space itself.
Maintaining such environments continuously at industrial scale demands enormous infrastructure.
Error correction multiplies energy consumption
The energy problem intensifies dramatically under fault-tolerant architectures.
Every additional logical qubit requires:
- more physical qubits,
- more synchronization,
- more cooling,
- more correction cycles,
- more control electronics.
Consequently, practical cryptographically relevant systems may consume energy at scales far beyond current public expectations.
This creates a major strategic implication.
Even if quantum cryptanalysis becomes technically feasible:
- economic scalability may remain constrained,
- state concentration may intensify,
- deployment capability may remain limited to hyperscale infrastructures.
The quantum-energy paradox
Quantum systems promise computational acceleration.
Yet sustaining fault-tolerant quantum computation may require:
- massive electrical infrastructure,
- continuous cooling chains,
- specialized semiconductor ecosystems,
- rare industrial expertise.
This creates a paradox.
The same technology capable of accelerating cryptanalysis may also become:
- extremely expensive,
- ecologically demanding,
- strategically centralized.
In practice, future quantum capability may resemble:
- nuclear infrastructure,
- space launch systems,
- or strategic semiconductor fabrication.
Meaning:
- rare,
- state-level,
- and geopolitically concentrated.
⮞ Strategic implication
Quantum supremacy does not automatically imply universal attacker democratization.
The first cryptographically relevant quantum systems may remain accessible only to:
- major intelligence powers,
- state coalitions,
- or hyperscale sovereign infrastructures.
That distinction profoundly changes threat modeling priorities.
Why ecological resilience becomes a cybersecurity issue
Future cybersecurity competition may increasingly involve:
- cryptographic efficiency,
- energy sustainability,
- infrastructure resilience,
- decentralized operational cost.
This is where sovereign offline architectures gain additional relevance.
Freemindtronic’s doctrine intentionally minimizes:
- cloud dependency,
- continuous synchronization,
- massive centralized telemetry,
- persistent infrastructure overhead.
Offline segmented architectures therefore create:
- cryptographic resilience,
- operational resilience,
- and ecological resilience simultaneously.
Why sustainability may shape future cryptographic architectures
The future of cybersecurity may not belong exclusively to:
- the most powerful infrastructures.
It may belong to:
- the most sustainable infrastructures.
Systems requiring:
- minimal visibility,
- minimal energy concentration,
- minimal metadata persistence,
- minimal centralized exposure
may ultimately prove more resilient than infinitely scalable centralized ecosystems.
Strategic perspective
The future cybersecurity race may involve three simultaneous competitions:
- cryptographic competition,
- AI-scale intelligence competition,
- energy sustainability competition.
Quantum resilience therefore becomes:
- a technological issue,
- a geopolitical issue,
- and an ecological issue simultaneously.
Signals watch — how the quantum transition already reshapes global cybersecurity
Most technological revolutions do not arrive suddenly.
They emerge through signals.
Weak signals first.
Then operational indicators.
Then irreversible structural transformations.
Quantum cybersecurity now entered that transitional phase.
The decisive mistake would therefore be waiting for a spectacular “RSA collapse moment” before reacting.
History rarely works that way.
Cybersecurity transformations generally occur progressively:
- through procurement decisions,
- through infrastructure redesign,
- through migration doctrine,
- through silent shifts in strategic assumptions.
That evolution is already visible globally.
The first weak signal was linguistic
One of the earliest indicators appeared almost invisibly:
language itself changed.
For years, organizations discussed:
- encryption standards,
- certificate management,
- key rotation,
- traditional compliance.
Today, strategic documents increasingly emphasize:
- crypto agility,
- algorithmic flexibility,
- migration readiness,
- quantum resilience.
This linguistic shift matters.
Because institutions do not redesign vocabulary randomly.
They redesign vocabulary when assumptions change internally.
The rise of terms such as:
- “hybrid cryptography,”
- “post-quantum readiness,”
- “retrospective exposure,”
- “harvest now, decrypt later”
reveals that long-term cryptographic permanence is no longer considered guaranteed.
The second signal was inventory urgency
Another major signal emerged through cryptographic inventory programs.
Governments increasingly demand visibility regarding:
- where RSA remains deployed,
- which ECC systems persist,
- how certificates propagate,
- which archives possess long confidentiality lifecycles.
This evolution may appear administrative.
In reality, it is strategic.
Because organizations only begin mapping cryptographic dependencies when they expect future replacement to become unavoidable.
This explains why:
now repeatedly emphasize:
- inventory visibility,
- lifecycle analysis,
- crypto-agility governance.
Why inventory becomes geopolitical
An organization incapable of identifying:
- where vulnerable cryptography exists,
- which archives remain exposed,
- how trust chains propagate
cannot realistically migrate before future exposure accumulates irreversibly.
Quantum resilience therefore begins with visibility itself.
The third signal is hybrid deployment expansion
Another decisive indicator now appears operationally:
hybrid cryptography is no longer experimental.
Post-quantum algorithms increasingly enter:
- VPN infrastructures,
- TLS experimentation,
- cloud trust models,
- critical infrastructure pilots.
This trend matters because infrastructure operators rarely deploy immature cryptographic layers casually.
Hybrid deployment indicates:
- serious migration preparation,
- long-term transition planning,
- acceptance that RSA/ECC replacement eventually becomes necessary.
Even when practical quantum attacks remain distant.
The strongest signal is psychological normalization
Perhaps the most important transformation is psychological.
Until recently, quantum cybersecurity discussions often sounded speculative.
Today, the tone changed dramatically.
Major organizations increasingly speak as if:
- migration is inevitable,
- timelines remain uncertain,
- but preparation cannot wait.
That psychological normalization changes the global security ecosystem profoundly.
Because once institutions collectively accept:
- future cryptographic transition,
entire industries begin reorganizing around that expectation.
Why “Store Now, Decrypt Later” became strategically dominant
The acceleration of SNDL awareness may represent the strongest operational signal of all.
For years, cybersecurity focused primarily on:
- active intrusion,
- malware,
- ransomware,
- real-time compromise.
Quantum risk changed the timeline.
Now, strategic actors increasingly recognize that:
- future attacks begin through present interception.
This realization transformed:
- government archival strategy,
- military communications doctrine,
- critical infrastructure planning,
- long-term confidentiality governance.
Because the exposure horizon now extends decades into the future.
⚠ The irreversible asymmetry
If encrypted archives are harvested today and quantum capability emerges later:
- future confidentiality cannot be retroactively restored.
This is why migration urgency exists before cryptographic collapse itself.
The strategic danger is persistence of exposure over time.
China’s deployment strategy became a geopolitical signal
Another major signal emerged through sovereign infrastructure deployment.
China’s expansion of:
- quantum-safe telecom systems,
- QKD integration,
- state-managed quantum infrastructure
demonstrated that quantum security is no longer confined to laboratory experimentation.
It is now:
- an infrastructure race,
- a sovereignty race,
- a geopolitical trust race.
This development forced Western infrastructures to accelerate migration planning politically as much as technically.
The AI convergence signal is accelerating silently
Perhaps the least visible yet most dangerous signal concerns AI-assisted cyber operations.
Large-scale AI systems increasingly improve:
- metadata analysis,
- behavioral mapping,
- identity correlation,
- credential prediction.
This convergence matters because future quantum capability may not operate independently.
Instead, AI systems may identify:
- which archives matter most,
- which identities remain vulnerable,
- which infrastructures expose reusable trust chains.
Quantum computation then becomes:
- a selective accelerator inside a broader intelligence architecture.
Why sovereign architectures gain strategic legitimacy again
For years, cybersecurity favored:
- centralization,
- cloud concentration,
- global synchronization.
Quantum-era threat models increasingly reverse that trajectory.
Offline architectures.
Segmented trust models.
Distributed authentication.
Reduced metadata visibility.
Those approaches increasingly regain strategic legitimacy because they directly reduce:
- continuous observability,
- mass harvesting capability,
- AI-scale behavioral inference.
This explains why sovereign cybersecurity doctrines increasingly prioritize:
- exposure minimization,
- rather than pure computational resistance alone.
✓ Strategic interpretation
Weak signals indicate preparation.
Operational signals indicate transition.
Geopolitical signals indicate irreversible restructuring of digital trust architectures.
The quantum transition therefore already exists — not yet through cryptographic collapse, but through strategic behavior change worldwide.
Quantum honeypots — preparing to detect the first real quantum-assisted intrusions
One of the most fascinating evolutions in post-quantum defense no longer concerns encryption itself.
It concerns detection.
Historically, cybersecurity evolved through phases:
- prevention first,
- detection later,
- behavioral intelligence eventually.
Quantum cybersecurity now begins entering that same transition.
Because many researchers increasingly assume that:
the first operational quantum-assisted intrusions may not be publicly announced immediately.
They may instead appear first through:
- behavioral anomalies,
- unexpected decryption patterns,
- cryptographic irregularities,
- or abnormal trust-chain activity.
Why quantum detection matters strategically
Classical cybersecurity increasingly relies on:
- intrusion detection systems,
- behavioral telemetry,
- deception environments,
- forensic intelligence.
Quantum-era security will likely evolve similarly.
The objective becomes:
- detecting cryptographic anomalies before widespread compromise occurs.
This is where quantum honeypots emerge conceptually.
What quantum honeypots actually do
Quantum honeypots intentionally expose monitored cryptographic environments designed to:
- simulate vulnerable infrastructures,
- observe unusual decryption attempts,
- detect abnormal timing patterns,
- capture reconnaissance behavior.
Their objective is not necessarily blocking attacks directly.
Their objective is:
early warning.
Some experimental initiatives associated with:
- ETH Zurich,
- Stanford research groups,
- advanced blockchain security studies
already explore how exposed ECDSA structures may function as quantum-warning sensors.
The first quantum intrusions may initially resemble ordinary anomalies
One of the central difficulties of future quantum-assisted attacks is that they may not appear spectacular initially.
There may be:
- no public declaration,
- no visible “quantum weapon,”
- no cinematic moment where encryption suddenly collapses.
Instead, the first indicators may emerge indirectly through:
- unexpected certificate compromises,
- unusual signature reconstruction patterns,
- abnormal authentication behavior,
- or impossible cryptographic timing sequences.
This resembles earlier transitions in cybersecurity history.
Long before the public fully understood:
- APT operations,
- supply-chain attacks,
- nation-state cyber operations,
specialized analysts first detected:
- behavioral inconsistencies,
- silent persistence patterns,
- statistical irregularities.
Quantum-assisted attacks may evolve similarly.
Why ECDSA ecosystems attract particular attention
Researchers increasingly monitor ECDSA-based infrastructures because they combine several characteristics:
- massive public-key exposure,
- global visibility,
- persistent blockchain archives,
- reusable cryptographic structures.
This creates an ideal observation environment.
If future attackers begin experimenting with:
- partial quantum-assisted signature recovery,
- advanced probabilistic attacks,
- hybrid AI-quantum cryptanalysis,
blockchain ecosystems may reveal the earliest detectable operational traces.
That possibility explains why Bitcoin researchers increasingly debate:
- public-key exposure reduction,
- address reuse minimization,
- migration timing.
The intelligence dimension of quantum detection
Quantum honeypots also introduce a geopolitical dimension rarely discussed publicly.
Because once states suspect:
- another actor may possess early quantum-assisted capability,
detection itself becomes strategic intelligence.
The objective shifts toward:
- estimating adversary maturity,
- observing operational methodology,
- mapping cryptographic targeting priorities.
In that context, quantum telemetry becomes as important as encryption itself.
Why deception architectures may return massively
Cybersecurity repeatedly demonstrates that:
perfect prevention rarely exists.
Consequently, deception increasingly returns as a strategic defense doctrine.
Future quantum defense ecosystems may therefore combine:
- hybrid PQC migration,
- behavioral anomaly detection,
- segmented architectures,
- quantum honeypots,
- AI-assisted forensic analysis.
This evolution matters because future resilience may depend not only on resisting attacks—
but on identifying them before systemic compromise spreads.
Key insight
The first practical quantum-assisted intrusions may not initially be recognized publicly as “quantum attacks.”
They may first appear as unexplained cryptographic anomalies detected by specialized behavioral monitoring systems.
Quantum threats to decentralized identity systems
For years, decentralized identity systems promised a new digital trust model.
Instead of depending entirely on centralized authorities:
- individuals could theoretically regain control over credentials,
- authentication,
- digital sovereignty.
However, quantum computing now introduces a profound paradox.
Many decentralized identity ecosystems rely heavily on:
- ECC signatures,
- persistent public verification,
- distributed trust transparency.
Those same strengths may eventually become structural weaknesses under future quantum conditions.
Why decentralized identity creates long-term exposure
Traditional centralized infrastructures often rotate:
- certificates,
- keys,
- trust relationships.
By contrast, decentralized systems frequently emphasize permanence.
Public signatures may remain visible indefinitely.
Credential chains may remain archived permanently.
Trust relationships may remain mathematically observable for decades.
This persistence creates a dangerous asymmetry in a future Shor-capable environment.
Because once public cryptographic material becomes permanently exposed:
- future retrospective analysis becomes possible indefinitely.
The blockchain visibility paradox
Blockchain ecosystems illustrate this challenge clearly.
Their transparency provides:
- auditability,
- distributed verification,
- public integrity.
Yet transparency also creates:
- massive cryptographic observability.
Future adversaries may therefore possess:
- years of archived public keys,
- historical transaction graphs,
- signature relationships,
- identity correlations.
The issue is therefore no longer simply algorithmic resistance.
It becomes:
long-term exposure persistence.
Why reusable public keys matter so much
Many users underestimate a decisive operational detail.
In several blockchain ecosystems:
- public-key reuse dramatically increases exposure duration.
Once an address repeatedly exposes:
- the same public key,
future attackers gain:
- more observational time,
- more archival material,
- more behavioral continuity.
That continuity may eventually simplify:
- future cryptanalytic targeting,
- identity reconstruction,
- AI-assisted correlation analysis.
Why sovereign offline identity models become attractive again
This explains why sovereign cybersecurity doctrines increasingly favor:
- offline identity validation,
- segmented authentication,
- minimal metadata generation,
- reduced public observability.
The objective changes fundamentally.
Instead of maximizing global visibility:
- the goal becomes minimizing persistent exposure.
Freemindtronic’s offline NFC HSM doctrine follows precisely this logic.
Authentication occurs locally.
Key exposure decreases dramatically.
Metadata generation shrinks.
Continuous centralized observation becomes far more difficult.
The future identity war may concern visibility more than encryption
This evolution changes the philosophy of digital identity itself.
For decades, cybersecurity primarily asked:
- “Can identity systems resist forgery?”
Future quantum-era systems may increasingly ask:
- “How much identity information remains continuously observable over decades?”
That distinction is profound.
Because a mathematically secure identity system may still become strategically fragile if:
- its trust relationships remain permanently exposed to future intelligence analysis.
✓ Sovereign identity principle
Future identity resilience may depend less on permanent transparency—
and more on minimizing persistent cryptographic observability over time.
Quantum threats to PKI infrastructures — the silent fragility of digital trust
Most people rarely think about Public Key Infrastructure.
Yet PKI silently supports nearly every modern trust system.
Every day, billions of operations depend on:
- TLS certificates,
- software signing,
- enterprise authentication,
- government identity systems,
- secure communications.
And most of those infrastructures still depend primarily on:
- RSA,
- ECC.
That dependency creates one of the largest migration challenges in digital history.
Why PKI migration is far harder than replacing algorithms
Public discussions often simplify post-quantum migration.
As if organizations simply needed to:
- replace one algorithm with another.
Reality is dramatically more complex.
PKI infrastructures involve:
- certificate authorities,
- hardware security modules,
- embedded firmware,
- browsers,
- mobile operating systems,
- industrial devices,
- critical infrastructure controllers.
A failure inside one layer may cascade across entire ecosystems.
That is why migration timelines extend over many years.
Sometimes decades.
The hidden dependency problem
Another major difficulty concerns invisible dependencies.
Many organizations simply do not fully know:
- where cryptographic systems remain embedded.
Legacy infrastructures often contain:
- forgotten certificates,
- obsolete trust chains,
- unsupported hardware,
- unmaintained authentication logic.
Those hidden dependencies become dangerous during migration.
Because replacing cryptography inside one environment may unexpectedly disrupt:
- authentication continuity,
- industrial operations,
- critical service availability.
Why hybrid cryptography dominates the transition phase
This complexity explains why hybrid cryptography now dominates strategic planning globally.
Hybrid models combine:
- classical cryptography,
- post-quantum algorithms,
- parallel trust validation.
The objective is not elegance.
The objective is operational continuity.
Organizations need time to:
- test interoperability,
- identify hidden dependencies,
- avoid catastrophic trust failures.
The migration race already reshapes geopolitical strategy
Quantum migration is no longer confined to research laboratories.
It now influences:
- defense procurement,
- telecommunication policy,
- digital sovereignty planning,
- critical infrastructure modernization.
This shift became unmistakable once major institutions publicly acknowledged that:
post-quantum migration must begin before practical quantum attacks exist.
That statement alone changed the global cybersecurity doctrine.
NIST transformed post-quantum cryptography from theory into operational policy
For years, post-quantum cryptography remained largely academic.
Then the National Institute of Standards and Technology (NIST) fundamentally altered the landscape through its post-quantum standardization process.
The publication of:
- ML-KEM (FIPS 203),
- ML-DSA (FIPS 204),
- SLH-DSA (FIPS 205),
marked a historic transition.
Quantum resilience stopped being speculative research.
It became:
- an engineering roadmap,
- a procurement issue,
- a sovereignty issue.
Meanwhile, the continued evaluation of HQC reinforced another strategic principle:
cryptographic diversity matters.
Why no serious institution expects “one perfect algorithm”
One of the major lessons of cryptographic history is simple:
- every dominant standard eventually faces pressure.
DES collapsed.
SHA-1 weakened.
RSA itself now faces long-term quantum exposure.
Consequently, modern post-quantum strategy increasingly avoids:
- single-algorithm dependence.
That explains why:
- lattice-based cryptography,
- code-based cryptography,
- hash-based signatures,
are all being explored simultaneously.
The future will likely belong not to:
- one universally dominant primitive,
but to:
- crypto agility,
- algorithmic diversity,
- adaptive layered architectures.
The NSA CNSA 2.0 doctrine accelerated strategic urgency
The publication of the NSA CNSA 2.0 guidance represented another decisive moment.
Because the message became impossible to ignore.
The doctrine effectively acknowledged that:
- RSA and ECC face unavoidable long-term exposure,
- migration delays increase strategic risk,
- inventory visibility becomes essential.
This changed the behavior of:
- governments,
- critical infrastructure providers,
- telecommunications operators,
- financial institutions.
The discussion was no longer:
- “Will migration happen?”
The discussion became:
- “How can migration occur without operational collapse?”
Europe adopts a slower but sovereignty-oriented approach
European institutions evolved differently.
Organizations such as:
increasingly emphasize:
- migration governance,
- critical dependency visibility,
- resilience continuity,
- strategic autonomy.
The European posture generally appears more cautious than the American approach.
However, it increasingly prioritizes:
digital sovereignty and operational continuity.
China follows an entirely different philosophy
China’s strategy diverges fundamentally from Western models.
Rather than focusing primarily on decentralized interoperability, China increasingly combines:
- Quantum Key Distribution (QKD),
- PQC deployment,
- state-controlled telecom infrastructure,
- centralized governance.
Projects associated with:
- Quantum Secret,
- Quantum Cloud Seal,
- national quantum communication backbones,
illustrate this sovereign centralized posture.
This model may provide:
- high institutional resilience,
- rapid national deployment capability.
Yet it also increases:
- centralized observability,
- state visibility,
- institutional control.
The geopolitical fracture is becoming philosophical
Quantum migration increasingly reveals a deeper geopolitical divergence.
The United States emphasizes:
- standardization leadership,
- industrial coordination,
- hybrid migration.
Europe increasingly emphasizes:
- regulatory resilience,
- digital sovereignty,
- trust continuity.
China increasingly emphasizes:
- state-coordinated infrastructure control,
- centralized deployment capability.
Meanwhile, decentralized sovereign-security doctrines such as Freemindtronic’s approach prioritize:
- offline resilience,
- segmented key architectures,
- minimal metadata exposure.
These models do not simply reflect technical preferences.
They reflect fundamentally different visions of:
- trust,
- visibility,
- control,
- digital autonomy.
⮞ Strategic interpretation
The post-quantum transition is not merely a cryptographic migration.
It is becoming a geopolitical restructuring of global digital trust architectures.
Freemindtronic doctrine — decentralized quantum resilience and exposure minimization
Most cybersecurity strategies continue to focus primarily on:
- stronger algorithms,
- larger infrastructures,
- centralized monitoring.
Freemindtronic’s doctrine follows a radically different direction.
The objective is not only to resist future decryption.
The objective is to reduce observable exposure itself.
That distinction changes everything.
Why exposure matters more than raw computational resistance
Future quantum systems may eventually accelerate:
- factorization,
- discrete logarithms,
- certain search operations.
However, quantum systems cannot decrypt:
- data they cannot observe,
- segments they cannot reconstruct,
- metadata they cannot aggregate.
This principle sits at the center of sovereign segmented encryption doctrine.
Because future attacks will likely depend not only on mathematics—
but also on:
- visibility,
- continuity,
- centralization.
Why centralized cloud dependency becomes strategically dangerous
Modern infrastructures increasingly concentrate:
- credentials,
- authentication flows,
- behavioral telemetry,
- metadata.
This concentration creates:
- high-value intelligence targets.
AI-assisted analysis amplifies this danger further.
Because centralized visibility allows:
- pattern recognition,
- identity correlation,
- credential mapping,
- behavioral prediction.
Long before practical quantum attacks emerge, exposure accumulation already begins.
Why offline architectures radically change attacker economics
Freemindtronic’s sovereign model intentionally minimizes:
- continuous online visibility,
- persistent metadata exposure,
- centralized credential concentration.
Offline architectures alter the attack surface fundamentally.
Attackers can no longer rely on:
- mass telemetry aggregation,
- continuous remote observation,
- centralized cloud interception.
Instead, operational complexity increases dramatically.
That complexity becomes strategically valuable.
DataShielder — segmented encryption as sovereign architecture
DataShielder embodies this doctrine operationally.
Its architecture combines:
- AES-256 CBC encryption,
- segmented key structures,
- offline NFC HSM isolation,
- zero-server dependency.
This creates several strategic consequences.
First:
- cryptographic material remains decentralized.
Second:
- metadata leakage decreases dramatically.
Third:
- cloud interception becomes far less useful.
Finally:
- AI-assisted large-scale visibility weakens significantly.
Why segmented key encryption changes future quantum assumptions
Classical cryptographic models often assume:
- a monolithic key structure.
Segmented architectures disrupt this assumption.
Attackers must now:
- identify multiple segments,
- capture independent components,
- correlate fragmented information,
- reconstruct separated authentication logic.
This transforms the problem from:
- pure mathematics
into:
- multi-dimensional operational compromise.
Even future quantum acceleration may not simplify:
- missing metadata,
- offline-isolated fragments,
- distributed sovereign custody.
The migration race already reshapes geopolitical strategy
Quantum migration is no longer confined to research laboratories.
It now influences:
- defense procurement,
- telecommunication policy,
- digital sovereignty planning,
- critical infrastructure modernization.
This shift became unmistakable once major institutions publicly acknowledged that:
post-quantum migration must begin before practical quantum attacks exist.
That statement alone changed the global cybersecurity doctrine.
NIST transformed post-quantum cryptography from theory into operational policy
For years, post-quantum cryptography remained largely academic.
Then the National Institute of Standards and Technology (NIST) fundamentally altered the landscape through its post-quantum standardization process.
The publication of:
- ML-KEM (FIPS 203),
- ML-DSA (FIPS 204),
- SLH-DSA (FIPS 205),
marked a historic transition.
Quantum resilience stopped being speculative research.
It became:
- an engineering roadmap,
- a procurement issue,
- a sovereignty issue.
Meanwhile, the continued evaluation of HQC reinforced another strategic principle:
cryptographic diversity matters.
Why no serious institution expects “one perfect algorithm”
One of the major lessons of cryptographic history is simple:
- every dominant standard eventually faces pressure.
DES collapsed.
SHA-1 weakened.
RSA itself now faces long-term quantum exposure.
Consequently, modern post-quantum strategy increasingly avoids:
- single-algorithm dependence.
That explains why:
- lattice-based cryptography,
- code-based cryptography,
- hash-based signatures,
are all being explored simultaneously.
The future will likely belong not to:
- one universally dominant primitive,
but to:
- crypto agility,
- algorithmic diversity,
- adaptive layered architectures.
The NSA CNSA 2.0 doctrine accelerated strategic urgency
The publication of the NSA CNSA 2.0 guidance represented another decisive moment.
Because the message became impossible to ignore.
The doctrine effectively acknowledged that:
- RSA and ECC face unavoidable long-term exposure,
- migration delays increase strategic risk,
- inventory visibility becomes essential.
This changed the behavior of:
- governments,
- critical infrastructure providers,
- telecommunications operators,
- financial institutions.
The discussion was no longer:
- “Will migration happen?”
The discussion became:
- “How can migration occur without operational collapse?”
Europe adopts a slower but sovereignty-oriented approach
European institutions evolved differently.
Organizations such as:
increasingly emphasize:
- migration governance,
- critical dependency visibility,
- resilience continuity,
- strategic autonomy.
The European posture generally appears more cautious than the American approach.
However, it increasingly prioritizes:
digital sovereignty and operational continuity.
China follows an entirely different philosophy
China’s strategy diverges fundamentally from Western models.
Rather than focusing primarily on decentralized interoperability, China increasingly combines:
- Quantum Key Distribution (QKD),
- PQC deployment,
- state-controlled telecom infrastructure,
- centralized governance.
Projects associated with:
- Quantum Secret,
- Quantum Cloud Seal,
- national quantum communication backbones,
illustrate this sovereign centralized posture.
This model may provide:
- high institutional resilience,
- rapid national deployment capability.
Yet it also increases:
- centralized observability,
- state visibility,
- institutional control.
The geopolitical fracture is becoming philosophical
Quantum migration increasingly reveals a deeper geopolitical divergence.
The United States emphasizes:
- standardization leadership,
- industrial coordination,
- hybrid migration.
Europe increasingly emphasizes:
- regulatory resilience,
- digital sovereignty,
- trust continuity.
China increasingly emphasizes:
- state-coordinated infrastructure control,
- centralized deployment capability.
Meanwhile, decentralized sovereign-security doctrines such as Freemindtronic’s approach prioritize:
- offline resilience,
- segmented key architectures,
- minimal metadata exposure.
These models do not simply reflect technical preferences.
They reflect fundamentally different visions of:
- trust,
- visibility,
- control,
- digital autonomy.
⮞ Strategic interpretation
The post-quantum transition is not merely a cryptographic migration.
It is becoming a geopolitical restructuring of global digital trust architectures.
Freemindtronic doctrine — decentralized quantum resilience and exposure minimization
Most cybersecurity strategies continue to focus primarily on:
- stronger algorithms,
- larger infrastructures,
- centralized monitoring.
Freemindtronic’s doctrine follows a radically different direction.
The objective is not only to resist future decryption.
The objective is to reduce observable exposure itself.
That distinction changes everything.
Why exposure matters more than raw computational resistance
Future quantum systems may eventually accelerate:
- factorization,
- discrete logarithms,
- certain search operations.
However, quantum systems cannot decrypt:
- data they cannot observe,
- segments they cannot reconstruct,
- metadata they cannot aggregate.
This principle sits at the center of sovereign segmented encryption doctrine.
Because future attacks will likely depend not only on mathematics—
but also on:
- visibility,
- continuity,
- centralization.
Why centralized cloud dependency becomes strategically dangerous
Modern infrastructures increasingly concentrate:
- credentials,
- authentication flows,
- behavioral telemetry,
- metadata.
This concentration creates:
- high-value intelligence targets.
AI-assisted analysis amplifies this danger further.
Because centralized visibility allows:
- pattern recognition,
- identity correlation,
- credential mapping,
- behavioral prediction.
Long before practical quantum attacks emerge, exposure accumulation already begins.
Why offline architectures radically change attacker economics
Freemindtronic’s sovereign model intentionally minimizes:
- continuous online visibility,
- persistent metadata exposure,
- centralized credential concentration.
Offline architectures alter the attack surface fundamentally.
Attackers can no longer rely on:
- mass telemetry aggregation,
- continuous remote observation,
- centralized cloud interception.
Instead, operational complexity increases dramatically.
That complexity becomes strategically valuable.
DataShielder — segmented encryption as sovereign architecture
DataShielder embodies this doctrine operationally.
Its architecture combines:
- AES-256 CBC encryption,
- segmented key structures,
- offline NFC HSM isolation,
- zero-server dependency.
This creates several strategic consequences.
First:
- cryptographic material remains decentralized.
Second:
- metadata leakage decreases dramatically.
Third:
- cloud interception becomes far less useful.
Finally:
- AI-assisted large-scale visibility weakens significantly.
Why segmented key encryption changes future quantum assumptions
Classical cryptographic models often assume:
- a monolithic key structure.
Segmented architectures disrupt this assumption.
Attackers must now:
- identify multiple segments,
- capture independent components,
- correlate fragmented information,
- reconstruct separated authentication logic.
This transforms the problem from:
- pure mathematics
into:
- multi-dimensional operational compromise.
Even future quantum acceleration may not simplify:
- missing metadata,
- offline-isolated fragments,
- distributed sovereign custody.
SeedNFC — quantum-aware sovereignty for Bitcoin custody
SeedNFC extends the same doctrine into cryptocurrency security.
This matters because Bitcoin ecosystems face a unique quantum paradox.
Bitcoin was designed to eliminate centralized trust.
Yet many wallets unintentionally create:
- persistent public-key visibility,
- long-term signature exposure,
- durable transaction traceability.
Under future Shor-capable environments, those characteristics may eventually become exploitable at scale.
SeedNFC therefore prioritizes:
- offline sovereign custody,
- reduced public-key reuse,
- segmented authentication,
- minimal observable exposure.
The objective is not “perfect theoretical immunity.”
The objective is:
long-term exposure minimization.
Why quantum resilience begins before migration
Many organizations still misunderstand a decisive strategic reality.
Post-quantum resilience does not begin:
- after cryptographic collapse.
It begins:
- during exposure management.
That means:
- inventory visibility,
- metadata reduction,
- segmentation,
- offline isolation,
- crypto agility,
already matter today.
Because once adversaries harvest:
- encrypted archives,
- identity graphs,
- public-key relationships,
- credential ecosystems,
future retrospective decryption may eventually become irreversible.
The future attack surface is becoming behavioral
Traditional cryptography focused primarily on:
- mathematical hardness.
Future attack models increasingly target:
- metadata continuity,
- identity persistence,
- behavioral predictability,
- observability concentration.
This evolution explains why:
- AI-assisted cryptanalysis,
- quantum acceleration,
- mass telemetry aggregation,
are converging strategically.
The future battle may concern:
who controls visibility itself.
✓ Sovereign doctrine
The safest cryptographic infrastructure is not necessarily the most visible, centralized, or computationally powerful.
The safest infrastructure may ultimately be the one that minimizes persistent exposure before future computation transforms exposure into permanent intelligence.
AI-assisted cryptanalysis — the parallel acceleration nobody can ignore
Quantum computing dominates headlines.
Yet another transformation already progresses operationally:
AI-assisted cryptanalysis.
Unlike fault-tolerant quantum systems, AI infrastructure already exists at industrial scale.
And unlike theoretical quantum projections, AI-assisted inference already impacts cybersecurity daily.
This distinction matters enormously.
Because future cryptographic fragility may emerge through:
- the convergence of AI and quantum capabilities,
rather than through quantum computing alone.
Why AI changes cybersecurity before quantum maturity
Modern AI systems excel at:
- pattern recognition,
- behavioral modeling,
- anomaly detection,
- correlation analysis.
This transforms offensive capability dramatically.
Because many attacks no longer depend exclusively on:
- breaking encryption mathematically.
Instead, attackers increasingly exploit:
- metadata continuity,
- credential reuse,
- human behavioral repetition,
- identity correlations.
The rise of exposure intelligence
Future intelligence operations may increasingly combine:
- AI inference,
- telemetry aggregation,
- massive historical archives,
- eventual quantum acceleration.
This creates a dangerous compounding effect.
Because even before practical Shor-capable systems exist:
- AI can already map relationships,
- predict behavior,
- identify weak trust chains.
Quantum systems may later accelerate exploitation.
Why metadata becomes strategically critical
Metadata increasingly matters as much as encryption itself.
Who communicates with whom.
How frequently.
Under which authentication structures.
Across which trust relationships.
For how long.
AI systems thrive on continuity.
That means infrastructures generating:
- persistent telemetry,
- centralized logs,
- continuous behavioral visibility,
gradually become easier to model.
Over years, those models may become extraordinarily powerful.
Quantum + AI convergence changes the threat model completely
For decades, cryptography assumed:
- mathematical resistance was the central problem.
Future systems may instead confront:
- AI-enhanced exposure analysis,
- behavioral intelligence automation,
- quantum-assisted cryptanalytic acceleration.
This changes the philosophy of defense itself.
The objective can no longer remain:
- “strong encryption only.”
The objective increasingly becomes:
- reduced observability,
- reduced metadata continuity,
- reduced centralized visibility.
Why segmented architectures resist AI better
Segmented architectures create strategic friction for AI systems.
Because AI models depend heavily on:
- large continuous datasets,
- correlated behavioral patterns,
- persistent telemetry continuity.
Offline segmented infrastructures intentionally disrupt:
- global visibility,
- single-point observability,
- centralized aggregation.
This weakens:
- predictive capability itself.
That is why segmentation is not only:
- a cryptographic strategy.
It is also:
- an anti-correlation strategy.
The future battlefield may concern intelligence dominance more than brute-force decryption
This may become the defining strategic shift of the coming decade.
Quantum systems may eventually weaken certain mathematical assumptions.
But AI systems may already determine:
- which infrastructures are most exposed,
- which identities matter most,
- which trust chains remain vulnerable.
Consequently, the future cybersecurity race may no longer concern:
- raw computational power alone.
It may increasingly concern:
- who controls visibility,
- who controls telemetry,
- who controls behavioral intelligence.
⮞ Summary
The future threat landscape is no longer:
“Quantum versus classical.”
It increasingly becomes:
“Quantum acceleration combined with AI-scale exposure intelligence.”
The environmental cost of quantum computing — the overlooked constraint
Public imagination often portrays quantum computing as an almost magical leap in computation.
Reality is far more physical.
And far more expensive.
Because large-scale fault-tolerant quantum systems require enormous industrial infrastructure.
Why cryogenic infrastructure changes everything
Most advanced quantum systems operate near absolute zero.
That means:
- extreme cryogenic cooling,
- continuous thermal stabilization,
- persistent energy-intensive synchronization.
These environments are extraordinarily difficult to maintain.
Even small thermal instability may:
- destroy coherence,
- increase noise,
- invalidate computation.
Consequently, practical quantum infrastructure demands:
- massive energy reliability.
Fault tolerance multiplies infrastructure requirements
Another overlooked issue concerns error correction.
Because useful logical qubits require:
- huge quantities of physical qubits.
This multiplies:
- hardware complexity,
- energy consumption,
- synchronization requirements,
- cooling demands.
In practice, a cryptographically relevant quantum computer may require infrastructure comparable to:
- large scientific facilities,
- specialized industrial environments.
This dramatically limits:
- who can realistically operate such systems.
Why HQC matters in the NIST diversification strategy
This context explains the growing strategic importance of HQC (Hamming Quasi-Cyclic).
Unlike lattice-based systems such as:
- ML-KEM,
- ML-DSA,
HQC belongs to the family of:
- code-based cryptography.
That distinction matters enormously.
Because future cryptographic resilience may depend less on:
- finding one perfect primitive,
and more on:
- avoiding systemic monoculture.
NIST’s continued interest in HQC therefore reflects a strategic principle:
diversity itself becomes resilience.
The post-quantum era may punish monocultures brutally
Modern digital ecosystems increasingly depend on:
- globalized standards,
- shared libraries,
- common trust chains.
This creates efficiency.
But it also creates:
- systemic fragility.
If one dominant cryptographic family eventually weakens:
- entire infrastructures may become simultaneously vulnerable.
That risk explains why future sovereign architectures increasingly prioritize:
- crypto agility,
- segmented trust models,
- algorithmic diversity.
The future belongs to adaptability
Perhaps the greatest misconception surrounding post-quantum cryptography is believing:
- migration is a final destination.
It is not.
Post-quantum security is not:
- a permanent state.
It is:
- a continuous adaptation process.
Future resilience will likely depend on:
- how rapidly infrastructures can evolve,
- how efficiently exposure can be reduced,
- how flexibly cryptographic layers can change.
That means the strongest future systems may not necessarily be:
- the most mathematically elegant.
They may instead be:
- the most operationally agile.
⮞ Summary
The future of post-quantum resilience depends less on one “perfect” algorithm—
and more on diversification, crypto agility, segmented architectures, and long-term operational adaptability.
When not to act — the strategic non-action principle
One of the most underestimated dangers in cybersecurity is panic-driven transformation.
Quantum fear can become operationally destructive when organizations:
- rush migration blindly,
- deploy immature cryptographic stacks,
- break interoperability prematurely.
This creates a paradox rarely acknowledged publicly.
Poor migration may weaken infrastructures faster than quantum computers themselves.
Why premature migration can become dangerous
Post-quantum deployment affects:
- PKI ecosystems,
- certificate authorities,
- embedded devices,
- industrial infrastructure,
- identity systems,
- critical software dependencies.
A rushed migration may trigger:
- authentication failures,
- trust-chain fragmentation,
- certificate incompatibilities,
- service disruption.
In critical infrastructure, those failures may become catastrophic.
Why cryptographic inventory matters before migration
Many institutions still lack:
- complete visibility over their cryptographic dependencies.
That creates a strategic blind spot.
Because organizations cannot safely migrate systems they do not fully understand.
Before any large-scale transition, institutions increasingly need:
- cryptographic inventory mapping,
- lifecycle analysis,
- dependency visibility,
- hybrid interoperability testing.
Without that preparation, migration itself becomes:
- an attack surface.
The real urgency concerns long-lifecycle data
Not all systems face identical risk horizons.
Some data loses value rapidly.
Other information remains sensitive for:
- 10 years,
- 20 years,
- 50 years,
- or permanently.
That distinction changes migration priorities dramatically.
Long-lifecycle exposure includes:
- government archives,
- military intelligence,
- medical records,
- industrial secrets,
- identity infrastructures.
Those environments require earlier preparation because:
- retrospective decryption risk already exists today.
The strategic objective is continuity, not speed alone
Successful post-quantum transition depends on balance.
Too little preparation creates:
- future exposure.
Too much rushed transformation creates:
- present instability.
That is why mature cybersecurity doctrine increasingly emphasizes:
- measured migration,
- crypto agility,
- hybrid coexistence,
- operational continuity.
Why strategic patience is sometimes the strongest defense
Cybersecurity history repeatedly demonstrates that:
- technological transitions rarely succeed through panic.
Strong resilience usually emerges through:
- progressive adaptation,
- careful validation,
- continuous governance.
The same principle now applies to post-quantum migration.
Organizations must prepare early.
But they must migrate intelligently.
⚠ Strategic doctrine
Do not migrate because headlines generate fear.
Migrate because your cryptographic lifecycle analysis demonstrates measurable long-term exposure requiring controlled adaptation.
Freemindtronic sovereign use cases — operational quantum resilience in practice
Many publications discuss quantum resilience abstractly.
Far fewer explore how sovereign architectures operate concretely under future exposure models.
Freemindtronic technologies provide operational examples of how:
- segmentation,
- offline processing,
- minimal metadata exposure,
can already reduce future cryptographic risk today.
Use case — DataShielder and sovereign confidentiality
DataShielder applies a doctrine fundamentally different from cloud-centric cybersecurity.
The objective is not simply encrypting information.
The objective is reducing:
- observable exposure itself.
DataShielder combines:
- AES-256 CBC encryption,
- segmented key management,
- offline NFC HSM isolation,
- zero-server dependency.
This architecture changes several attack assumptions simultaneously.
Because:
- keys remain decentralized,
- metadata visibility decreases,
- telemetry continuity weakens,
- cloud interception loses strategic value.
In a future environment where:
- AI inference,
- mass telemetry analysis,
- quantum acceleration
may converge operationally, this reduction of exposure becomes strategically decisive.
Use case — PassCypher and segmented secret management
PassCypher extends sovereign segmentation into:
- credential protection,
- offline secret storage,
- distributed authentication logic.
Instead of centralizing trust:
- the system fragments observable exposure.
This matters because future attackers will likely target:
- credential correlation,
- identity continuity,
- behavioral repetition.
Segmented secret architectures reduce:
- single-point compromise potential.
Use case — SeedNFC and Bitcoin quantum resilience
SeedNFC applies sovereign cryptographic doctrine directly to Bitcoin custody.
This matters because cryptocurrency ecosystems occupy a unique position in the quantum debate.
Unlike traditional infrastructures:
- blockchains preserve historical signatures permanently,
- public-key relationships remain globally observable,
- transaction histories persist indefinitely.
This permanence transforms cryptocurrency into one of the most visible long-term quantum exposure surfaces ever created.
Why Bitcoin creates a strategic asymmetry
Bitcoin’s transparency provides extraordinary advantages:
- auditability,
- distributed trust,
- consensus verification.
Yet that same transparency also produces:
- persistent cryptographic visibility.
If future Shor-capable systems eventually emerge, archived blockchain ecosystems may provide:
- years of exposed public keys,
- historic transaction relationships,
- observable signature continuity.
That possibility explains why many researchers increasingly recommend:
- minimizing public-key reuse,
- rotating addresses aggressively,
- reducing long-term cryptographic observability.
Why SeedNFC focuses on exposure minimization
SeedNFC therefore follows a deliberately sovereign posture.
The objective is not claiming:
- “quantum immunity.”
The objective is reducing:
- persistent visibility,
- continuous exposure,
- centralized compromise potential.
This includes:
- offline sovereign storage,
- NFC-isolated authentication,
- segmented validation logic,
- minimal public-key persistence.
Such architecture changes the operational assumptions of future attackers significantly.
The future cryptocurrency battle may concern observability more than cryptography alone
Public debate often simplifies the question:
- “Will quantum computers break Bitcoin?”
Reality is far more nuanced.
The decisive issue may not be:
- whether ECDSA becomes theoretically vulnerable.
The decisive issue may instead concern:
- how much cryptographic material remains permanently observable before migration occurs.
This distinction changes the philosophy of long-term digital asset protection fundamentally.
✓ Sovereign security principle
The strongest future protection may not come solely from stronger algorithms.
It may come from reducing what future adversaries can continuously observe, archive, correlate, and centralize today.
Limitations and counter-arguments — separating strategic realism from quantum mythology
Quantum cybersecurity discussions often oscillate between:
- panic,
- skepticism,
- marketing exaggeration.
Both extremes distort strategic understanding.
A serious analysis requires acknowledging uncertainty explicitly.
Timeline uncertainty remains unavoidable
No institution can currently predict precisely:
- when fault-tolerant quantum systems will mature,
- whether topological qubits will scale,
- how rapidly error correction will improve,
- which architectural breakthroughs may emerge unexpectedly.
That uncertainty is structural.
Quantum engineering remains one of the most complex technological challenges in modern history.
Consequently, all timelines remain:
- probabilistic rather than deterministic.
Why quantum hype repeatedly distorts public perception
Commercial announcements frequently amplify confusion.
Media narratives often blur the distinction between:
- experimental qubits,
- logical fault-tolerant qubits,
- practical cryptanalytic capability.
As a result, public discourse sometimes incorrectly assumes:
- larger qubit counts automatically imply imminent RSA collapse.
This is deeply misleading.
A noisy quantum processor with thousands of unstable qubits does not necessarily possess meaningful cryptanalytic capability.
Fault tolerance remains the decisive barrier.
Post-quantum cryptography itself may evolve significantly
Another important limitation concerns PQC algorithms themselves.
History repeatedly demonstrates that:
- cryptographic confidence evolves over time.
Algorithms once considered robust sometimes weaken unexpectedly.
New mathematical approaches occasionally emerge suddenly.
Future research may therefore:
- strengthen certain PQC systems,
- challenge others,
- transform migration priorities again.
That uncertainty reinforces the importance of:
- crypto agility,
- algorithmic diversification,
- segmented architectures.
Offline architectures are not magical immunity
Sovereign offline infrastructures dramatically reduce exposure.
However, no architecture eliminates risk completely.
Offline systems still require:
- secure operational discipline,
- physical protection,
- trusted lifecycle governance,
- human reliability.
Poor operational behavior can compromise even highly resilient systems.
That is why sovereign cybersecurity remains:
- both technological and procedural.
The greatest danger may still be institutional inertia
Ironically, the largest long-term risk may not be quantum computers themselves.
It may be:
- delayed preparation,
- incomplete visibility,
- migration paralysis.
Because once encrypted archives are:
- harvested,
- copied,
- distributed,
future retrospective exposure may become irreversible.
Why strategic realism matters more than prediction certainty
Cybersecurity history consistently rewards:
- adaptive resilience,
- continuous preparation,
- operational flexibility.
It rarely rewards:
- absolute certainty.
That principle applies fully to quantum resilience.
Organizations do not need perfect prediction.
They need:
- visibility,
- crypto agility,
- migration readiness,
- exposure minimization.
⮞ Strategic clarification
Quantum resilience is not a final technological destination.
It is a continuously evolving operational discipline combining cryptography, governance, sovereignty, exposure management, and long-term adaptation.
Glossary — quantum threats to encryption and post-quantum resilience
Shor’s algorithm
The asymmetric cryptography disruptor
Why Shor’s algorithm changes RSA and ECC security assumptions
Introduced by mathematician Peter Shor in 1994, Shor’s algorithm demonstrated theoretically that sufficiently powerful quantum computers could solve:
- integer factorization,
- discrete logarithm problems
exponentially faster than classical systems.
This directly threatens:
- RSA,
- ECC,
- Diffie-Hellman,
- large parts of current PKI infrastructure.
The RSA security assumption relies fundamentally on the practical difficulty of factoring:
where:
- p and q are very large prime numbers.
Classically, recovering:
- p and q from n
becomes computationally infeasible at large scale.
Shor’s algorithm theoretically changes that assumption completely under fault-tolerant quantum conditions.
However, practical execution still requires:
- millions of physical qubits,
- stable logical qubits,
- massive error correction.
Therefore, the threat remains strategic rather than immediate.
Grover’s algorithm
Quadratic acceleration against symmetric encryption
How Grover’s algorithm affects AES-256
Unlike Shor’s algorithm, Grover’s algorithm does not mathematically break AES.
Instead, it accelerates brute-force search quadratically.
Classically, exhaustive AES-256 search requires approximately:
possible operations.
Under idealized Grover conditions, effective complexity becomes approximately:
This remains computationally enormous.
Consequently, AES-256 continues to be considered highly resilient for long-term protection, especially when reinforced through:
- segmented key architectures,
- offline processing,
- reduced metadata exposure.
Logical qubits
The real measure of quantum capability
Why logical qubits matter more than physical qubits
Public discourse frequently confuses:
- physical qubits,
- logical qubits.
This confusion radically distorts perceived quantum capability.
Physical qubits are highly unstable quantum components vulnerable to:
- noise,
- decoherence,
- measurement instability,
- thermal fluctuation.
Logical qubits emerge only after:
- massive error correction,
- continuous synchronization,
- fault-tolerant stabilization.
This distinction is decisive because:
- one logical qubit may require thousands of physical qubits.
Therefore:
- raw qubit counts alone rarely indicate operational cryptanalytic capability.
This explains why:
- “1,000 qubits” in a press announcement does not imply “1,000 cryptographically useful qubits.”
The real industrial challenge remains:
- sustained fault tolerance at scale.
Store Now, Decrypt Later
The retrospective exposure doctrine
Why archived encrypted data already faces long-term strategic risk
Store Now, Decrypt Later (SNDL) describes a long-term intelligence strategy:
- intercept encrypted traffic today,
- archive it for years,
- decrypt it once sufficient quantum capability emerges.
This doctrine particularly concerns:
- government archives,
- military communications,
- health records,
- industrial secrets,
- diplomatic exchanges.
However, retrospective decryption is not automatic.
Successful future exploitation still requires:
- preserved ciphertext,
- public-key exposure,
- protocol visibility,
- sufficient fault-tolerant quantum systems.
For RSA infrastructures, the public modulus:
remains intentionally exposed through certificates.
That exposure explains why:
- harvested encrypted archives already possess long-term intelligence value.
Yet architectures based on:
- forward secrecy,
- ephemeral keys,
- segmented encryption,
- offline processing
can reduce retrospective feasibility considerably.
Segmented key encryption
Reducing exposure through cryptographic fragmentation
How segmented encryption changes attacker economics
Traditional encryption often relies on:
- centralized cryptographic structures.
Segmented key encryption follows a radically different philosophy.
Instead of exposing:
- one monolithic key structure,
cryptographic material becomes divided into:
- independently protected segments.
This changes the attack surface fundamentally.
Future adversaries must:
- capture multiple elements,
- preserve them over time,
- correlate metadata,
- reconstruct fragmented logic.
Consequently:
- cryptanalysis becomes an operational intelligence problem rather than pure mathematics alone.
Freemindtronic applies this doctrine through:
- offline NFC HSM architectures,
- zero server dependency,
- distributed sovereignty-oriented security.
FAQ — quantum threats to encryption, RSA, AES, ECC, and post-quantum migration
Can quantum computers break RSA-2048 today?
No operational capability exists today
Why RSA-2048 remains operationally secure in 2026
No currently available quantum computer can practically break RSA-2048.
Although Shor’s algorithm theoretically threatens RSA, real-world cryptanalytic execution would require:
- millions of physical qubits,
- thousands of stable logical qubits,
- extreme fault tolerance,
- hours of coherent computation.
Current systems remain dramatically below this threshold.
According to research by:
fault tolerance—not theoretical mathematics—remains the decisive bottleneck.
Does Store Now, Decrypt Later guarantee future decryption?
No — exposure conditions still matter
Why future quantum decryption still depends on operational exposure
Store Now, Decrypt Later assumes adversaries preserve:
- ciphertext,
- public-key material,
- protocol visibility,
- sufficient future quantum capability.
However, future decryption remains conditional.
Architectures using:
- forward secrecy,
- ephemeral keys,
- offline processing,
- segmented encryption,
- minimal metadata retention
can significantly reduce retrospective attack feasibility.
Therefore, long-term quantum resilience depends not only on:
- algorithm strength,
but also on:
- exposure persistence.
Is AES-256 still secure against quantum attacks?
Yes — under current scientific consensus
Why AES-256 remains strategically resilient
Grover’s algorithm theoretically reduces AES-256 effective complexity from:
Yet:
- 2¹²⁸ operations remain astronomically large.
Executing Grover’s algorithm operationally would still require:
- advanced fault-tolerant quantum systems far beyond foreseeable infrastructure.
That is why:
continue recommending AES-256 for long-term protection when implemented correctly.
Why is ECC considered more exposed than RSA?
Shorter keys alter Shor scaling dynamics
Why elliptic-curve ecosystems face elevated quantum pressure
ECC relies on the elliptic-curve discrete logarithm problem.
Under Shor’s algorithm:
- ECC may require fewer logical qubits than RSA for equivalent compromise.
This matters because ECC dominates:
- mobile cryptography,
- TLS optimization,
- cryptocurrency ecosystems,
- decentralized identity systems.
Blockchain infrastructures create additional long-term exposure because:
- public keys often remain permanently observable.
Consequently:
- ECC migration urgency may exceed RSA urgency in several strategic sectors.
Should organizations migrate immediately to PQC?
Preparation matters more than panic
Why rushed migration may create dangerous instability
Organizations should begin immediately:
- cryptographic inventory mapping,
- hybrid interoperability testing,
- lifecycle analysis,
- migration planning.
However:
- rushed deployment of immature PQC infrastructures may weaken operational resilience.
Migration failures may affect:
- PKI continuity,
- certificate ecosystems,
- identity infrastructures,
- critical interoperability.
This explains why:
- hybrid cryptography dominates current strategic doctrine.
What is the safest long-term quantum resilience strategy?
Reduce exposure before future computation matures
Why sovereignty matters more than mathematics alone
Long-term resilience no longer depends exclusively on:
- algorithm complexity.
The next generation of cyber resilience increasingly depends on:
- exposure minimization,
- distributed trust,
- offline processing,
- segmented encryption,
- metadata reduction,
- hybrid post-quantum migration.
This is why sovereign architectures become strategically important.
The future challenge is no longer only:
The deeper challenge becomes:
Architectures minimizing:
- centralized exposure,
- continuous telemetry,
- cloud dependency,
- persistent public-key observability
may ultimately prove more resilient than infrastructures relying only on stronger algorithms.
What We Didn’t Cover
Scope boundaries and strategic exclusions
This Chronicle focused deliberately on:
- realistic quantum threats to encryption,
- fault-tolerant quantum timelines,
- post-quantum migration strategy,
- Store Now, Decrypt Later exposure,
- segmented key encryption doctrine,
- sovereign cyber resilience.
Several highly technical or classified domains were intentionally excluded because they require:
- dedicated mathematical treatment,
- continuous validation,
- experimental reproducibility.
This Chronicle therefore did not deep-dive into:
- formal lattice cryptanalysis proofs,
- surface-code engineering mathematics,
- detailed quantum error-correction thresholds,
- specific side-channel attack implementations,
- classified national quantum programs,
- vendor-by-vendor hardware benchmarking.
Likewise, this publication intentionally avoided:
- speculative AGI scenarios,
- unverifiable “quantum supremacy” narratives,
- fear-driven collapse predictions.
The objective was not sensationalism.
The objective was operational clarity.
Strategic outlook — preparing before the quantum threshold
Quantum computing does not merely threaten encryption.
It challenges the entire architecture of digital trust developed during the Internet era.
For decades, cybersecurity strategy assumed:
- mathematical hardness guaranteed long-term confidentiality,
- centralized infrastructures improved scalability,
- cloud concentration increased operational efficiency.
That historical equilibrium is beginning to fracture.
The post-quantum transition reveals a deeper structural reality:
- visibility itself becomes strategic exposure.
This is why the future of cybersecurity may no longer revolve exclusively around:
The more decisive geopolitical question increasingly becomes:
That shift changes everything.
The end of the classical trust model
The classical Internet security model depended heavily on:
- RSA-based PKI,
- ECC trust chains,
- certificate authorities,
- cloud-centralized identity systems.
Quantum pressure reveals the fragility of this architecture over long time horizons.
Even before practical quantum attacks exist, adversaries can already:
- harvest encrypted archives,
- aggregate metadata,
- map trust relationships,
- preserve cryptographic visibility for future exploitation.
Consequently:
- future resilience depends increasingly on reducing persistent observability itself.
The geopolitical divergence accelerates
The world is no longer converging toward one cybersecurity doctrine.
Instead, three major strategic models are emerging simultaneously.
1. Standardization-driven migration
The United States and allied ecosystems increasingly prioritize:
- NIST-led PQC standardization,
- hybrid migration governance,
- crypto agility,
- large-scale interoperability.
This model prioritizes:
- industrial continuity.
Official references:
2. Centralized sovereign quantum infrastructure
China increasingly combines:
- QKD deployment,
- state-operated telecom infrastructure,
- centralized quantum governance,
- national cyber sovereignty.
This model prioritizes:
- state-controlled resilience.
Official references:
3. Decentralized sovereign resilience
A third doctrine increasingly emerges around:
- offline architectures,
- segmented encryption,
- minimal metadata exposure,
- distributed sovereignty.
This posture assumes:
- future attack capability becomes unavoidable eventually.
Therefore:
- reducing visibility matters more than maximizing centralization.
Why AI changes the equation further
Quantum computing alone does not define the future threat landscape.
AI-assisted intelligence amplification increasingly transforms:
- metadata exploitation,
- behavioral correlation,
- credential prediction,
- trust-chain analysis.
This convergence changes the meaning of cybersecurity itself.
The next strategic frontier may not involve:
- breaking encryption directly.
Instead, it may involve:
- mapping entire exposure ecosystems around encrypted infrastructures.
In such an environment:
- segmentation becomes a defensive intelligence strategy,
- offline processing becomes a sovereignty mechanism,
- metadata minimization becomes operational resilience.
The energy paradox of quantum power
Another strategic contradiction now emerges:
- large-scale fault-tolerant quantum systems may become extraordinarily expensive energetically.
Quantum capability requires:
- cryogenic cooling,
- continuous synchronization,
- massive error correction,
- persistent infrastructure stability.
Therefore:
- future quantum capability may remain concentrated among major states and industrial actors.
This creates a paradox.
Quantum supremacy does not automatically imply:
- universal quantum attack democratization.
Capability concentration itself may become:
- a geopolitical asymmetry.
The real strategic mistake
The greatest danger is neither:
- panic,
- nor denial.
The greatest danger is strategic inertia.
Organizations delaying:
- inventory mapping,
- crypto agility,
- hybrid migration preparation,
- exposure reduction strategies
may eventually discover that:
- retrospective exposure cannot be reversed once archives have already been harvested at scale.
The future of cyber sovereignty
Quantum resilience is no longer purely a cryptographic discussion.
It becomes simultaneously:
- a governance issue,
- an infrastructure issue,
- an intelligence issue,
- an energy issue,
- a sovereignty issue.
The organizations most likely to adapt successfully will not necessarily be those deploying the fastest migration.
They will be those capable of:
- reducing unnecessary exposure before future computation makes persistent exposure permanent.
Strategic Outlook
The post-quantum era may ultimately redefine cybersecurity around one decisive principle:
Everything You Need to Know About EAN Codes: Andorra’s Shared 84 Code with Spain
Key Highlights: EAN Code Andorra & Spain’s Shared 84 Code
- EAN Code Andorra: All About EAN Codes and Their Importance: Andorra shares the 84 code with Spain, mainly due to strong trade relationships.
- What Is an EAN Code and Why Is It Important?: EAN codes play a critical role in global product identification, especially in retail and supply chains.
- How EAN Codes Are Structured: The structure of EAN codes consists of a country prefix, product number, and check digit.
- Complete List of EAN Codes by Country (Updated in 2024): A comprehensive list of EAN codes for countries with assigned EAN-13 codes, updated for 2024.
- Why Does Andorra Share Its EAN Code with Spain?: Andorra shares its EAN code with Spain due to economic ties and logistical efficiency.
- Examples of Valid EAN Codes for Andorra: Valid EAN codes for Andorran products, starting with the prefix 84.
- How the Shared EAN Code Works: How GS1 manages Andorra’s shared EAN code with Spain.
- Benefits of Sharing the Code: Advantages for Andorra in sharing its EAN code with Spain, such as cost reduction and logistical efficiency.
- How to Verify the Validity of EAN and UPC Codes: Methods for checking the validity of EAN and UPC codes using the check digit.
- UPC and EAN: Differences and Correspondence: The difference between UPC and EAN codes and how they correspond.
- Alternatives to GS1 for Obtaining EAN Codes: Exploring alternatives like resellers, online platforms, and local agencies for obtaining EAN codes.
- Finding the Best EAN Code Solution for Your Business: Determining the right EAN code acquisition strategy depending on your business needs.
All About EAN Codes and Their Importance
EAN Code Andorra illustrates how the EAN (European Article Number) system operates on a global scale. GS1 actively manages this system, which ensures that every product crossing international borders has a unique identifier. Over 100 countries rely on EAN codes to track and identify goods efficiently.
Businesses that engage in international trade must assign EAN codes to their products. These codes play a critical role in streamlining logistics and improving product traceability. By adopting this system, companies guarantee that their products are correctly identified, no matter where they are shipped or sold. As a result, they meet global standards, enhancing both their credibility and operational efficiency in the global market.
What Is an EAN Code and Why Is It Important?
An EAN code allows businesses to identify and track products globally with ease. These codes play a critical role in retail, supply chain management, and product traceability systems. By using EAN codes, businesses automate inventory management and streamline commercial transactions. As a result, companies can manage their stock more efficiently, reduce errors, and ensure their products are easily traceable from production to sale. This makes EAN codes indispensable for businesses operating in today’s fast-paced global market.
How EAN Codes Are Structured
An EAN-13 code is made up of the following elements:
- The first 3 digits are the country prefix, representing where the company is registered.
- The next 9 digits identify the company and its specific product.
- The final digit is a check digit, calculated to verify the accuracy of the code.
Why Does Andorra Share Its EAN Code with Spain?
Andorra, though a co-principality with both France and Spain, actively chooses to share Spain’s EAN 84 code rather than having its own unique code. This decision is primarily driven by practical and economic factors.
First and foremost, Andorra maintains strong economic ties with Spain. Over the years, Andorra has relied on Spain for the majority of its imports, including essential goods such as food, fuel, and other products. This long-standing relationship naturally led Andorran businesses to align themselves more closely with Spain in terms of trade and logistics.
In addition, the small size of Andorra’s market makes it less feasible to maintain a unique EAN code. With a relatively small population and limited market activity, it isn’t cost-effective for Andorra to have its own system. Sharing Spain’s code helps reduce costs and streamline processes, enabling Andorran companies to integrate smoothly into Spain’s commercial network.
Moreover, logistical efficiency plays a critical role in this choice. By using Spain’s well-established commercial infrastructure, Andorra simplifies its logistics and stock management processes. This allows Andorran businesses to focus on their core operations without worrying about managing separate systems for product identification. As a result, they ensure compliance with global trade standards and enhance their ability to participate in international markets.
In the end, Andorra’s decision to share the EAN code with Spain reflects practical realities and strategic choices. Leveraging Spain’s infrastructure for logistics and distribution, Andorran companies enjoy smoother operations, lower costs, and easier access to global markets, all while ensuring that their products meet international standards for identification and trade.
Examples of Valid EAN Codes for Andorra
For Andorra, the EAN-13 code starts with 84. Here are some examples of valid EAN codes for products registered in Andorra:
- 8400000000012
- 8400000000029
- 8400000000036
These codes follow the standard EAN-13 structure, with the prefix “84” indicating Andorra/Spain, followed by a product reference number and a calculated check digit.
How the Shared EAN Code Works
GS1 manages the EAN 84 code that Andorra shares with Spain. Andorran companies register their products for international trade and use Spain’s infrastructure to handle logistics and distribution. This setup ensures that Andorran businesses can efficiently enter global markets without needing their own EAN code.
Other small countries, such as Monaco and San Marino, also share EAN codes with larger neighbors like France and Italy. They benefit from the same logistics and distribution advantages, which simplifies their participation in international trade. By sharing these codes, smaller nations ensure full compliance with global standards, while avoiding the complexities of managing their own code.
Benefits of Sharing the Code
There are several advantages to Andorra sharing its EAN code with Spain:
- Simplified Trade: Andorran products can move freely between Andorra and Spain without needing recoding.
- Cost Reduction: Companies in Andorra avoid the expense of obtaining and managing a separate EAN code.
- Efficient Stock Management: Sharing a code allows businesses to use the same product tracking systems as Spanish companies.
How to Verify the Validity of EAN and UPC Codes
Ensuring that your EAN or UPC codes are valid is essential for avoiding errors in product tracking and inventory management. This section explains how to verify codes by calculating the check digit and ensuring compliance with international standards.
Differences Between EAN and UPC Codes
- UPC (Universal Product Code): This is a 12-digit barcode primarily used in North America.
- EAN (European Article Number): A 13-digit barcode used internationally, particularly in Europe.
Both codes refer to the same products, but the EAN adds a digit to comply with global standards.
Steps to Verify EAN Codes Using the Check Digit
You can verify the validity of an EAN code by calculating its check digit. Let’s take the example of the EAN code 0659436219502 and follow these steps:
- Multiply the digits:
- Multiply the odd-positioned digits (1st, 3rd, 5th, etc.) by 1.
- Multiply the even-positioned digits (2nd, 4th, 6th, etc.) by 3.
- Add the results: Add the results of your multiplications:
- (0 * 1) + (6 * 3) + (5 * 1) + (9 * 3) + (4 * 1) + (3 * 3) + (6 * 1) + (2 * 3) + (1 * 1) + (9 * 3) + (5 * 1) + (0 * 3) = 110.
- Determine the check digit:
- Find the number that, when added to your total, will make it a multiple of 10.
- In this case, the total is 110, which is already a multiple of 10, so the check digit is 0.
- Confirm the code:
- With the check digit 0, the full EAN code 0659436219502 is valid.
How to Verify the Validity of EAN and UPC Codes
Verifying the validity of your EAN or UPC codes is essential for preventing errors in product tracking and inventory management. To confirm that your codes are correct, you can calculate the check digit. This simple process confirms whether the code follows the proper structure. However, to ensure full compliance with global standards, you should consider using tools like Verified by GS1.
By using GS1’s verification service, you can easily check if your product’s code is registered and recognized worldwide. This step not only guarantees that your EAN or UPC code meets international standards, but it also enhances your credibility in the market. As a result, you can ensure smooth operations across the supply chain, minimizing the risk of errors and maintaining trust with your partners and customers.
UPC and EAN: Differences and Correspondence for Andorran Products
While UPC and EAN codes differ in length, they both identify the same product globally. The UPC code typically consists of 12 digits, mainly used in North America, while the EAN code has 13 digits and is used internationally, including in Andorra, which shares the EAN 84 code with Spain.
Here’s how UPC and EAN codes correspond for the same Andorran product:
| Product | UPC | EAN (Andorra) |
|---|---|---|
| Andorran Product 1 | 012345678905 | 84012345678905 |
| Andorran Product 2 | 123456789012 | 84123456789012 |
| Andorran Product 3 | 234567890123 | 84234567890123 |
In these examples, you can see that the EAN codes begin with 84, representing Andorra/Spain, and are structured similarly to UPC codes, with the addition of an extra digit to comply with international standards.
Alternatives to GS1 for Obtaining EAN Codes
While GS1 is the global authority responsible for assigning EAN codes, there are several alternative methods to obtain these codes. These options are often better suited for small businesses or start-ups that may be looking for more cost-effective solutions. Let’s explore these alternatives and their advantages.
EAN Code Resellers
First, you can consider purchasing EAN codes from resellers. These resellers buy unused EAN codes from GS1 and then sell them at a reduced price. As a result, this option can be much more affordable. However, you need to keep in mind that these codes might not be registered under your company in the GS1 database, which could lead to potential issues when it comes to product traceability.
Online Platforms
Another convenient option involves using online platforms like Nationwide Barcode and Buyabarcode.com, which provide EAN codes quickly and at a lower cost. In this case, you benefit from faster access to the codes. However, because these codes might not be directly linked to your company in the official GS1 system, this could cause traceability challenges with larger retailers or international partners.
Local or Regional Solutions
In some regions, local agencies offer EAN codes specifically for use within that country or area. These local solutions are usually cheaper, making them a good choice for businesses that operate regionally. On the downside, these codes may not be recognized internationally, limiting your opportunities for global trade.
Finding the Best EAN Code Solution for Your Business
When you sell products internationally or work with large retailers, obtaining your EAN codes directly from GS1 ensures full recognition and traceability across global markets. This choice provides the highest level of confidence that your products will meet international standards. It helps your business thrive in a competitive environment.
On the other hand, if your business operates primarily in local or regional markets, you should consider exploring more affordable alternatives. You could turn to EAN resellers or local agencies, which offer flexibility at a lower cost. These options still allow you to meet the needs of smaller markets. At the same time, they give you room to scale when necessary. In many cases, this approach proves more cost-effective for businesses that don’t require global compliance right away.
Throughout this guide, you’ve discovered how EAN codes work and learned why Andorra shares the 84 code with Spain. You’ve also found out how to verify code validity. Whether you run a small business with local reach or a large enterprise with global aspirations, understanding the best approach to EAN code acquisition empowers you to make the right decision for your business. In the end, choosing the right path sets your products up for success. It ensures they can be tracked and managed smoothly, no matter where they are sold.