Digital Authentication Security by Jacques gascuel This article will be updated with any new information on the topic, and readers are encouraged to leave comments or contact the author with any suggestions or additions.
How Digital Authentication Security Shields Our Data
Digital authentication security is essential in today’s connected world. Whether accessing bank accounts, social media, or work emails, authentication ensures that only authorized individuals can access sensitive information. With the growing sophistication of cyberattacks, securing our identity online has become critical. This article will explore the evolution of authentication methods, from simple passwords to multi-factor authentication, and how these technologies are essential for protecting both personal and professional data.
2026 Cyber Doctrine Cyberculture
January 4, 2026
2025 Cyber Doctrine Cyberculture
December 10, 2025
2025 Cyber Doctrine Cyberculture
December 10, 2025
2025 Cyberculture EviLink
November 25, 2025
2025 Cyberculture Cybersecurity Digital Security EviLink
November 14, 2025
2025 Cyber Doctrine Cyberculture
November 10, 2025
2025 Cyberculture
November 9, 2025
2025 Cyberculture
November 9, 2025
Digital Authentication Security: The Guardian of Our Digital World
In today’s digital life, authentication has become a vital process. Whether you are accessing your bank accounts, social media, or work emails, you are constantly required to prove your identity. But what is authentication exactly, and why has it become so essential in our digital world?
Authentication is the process of verifying a person’s or device’s identity before granting access to specific resources. While often seen as a simple formality, it plays a crucial role in protecting both personal and professional data.
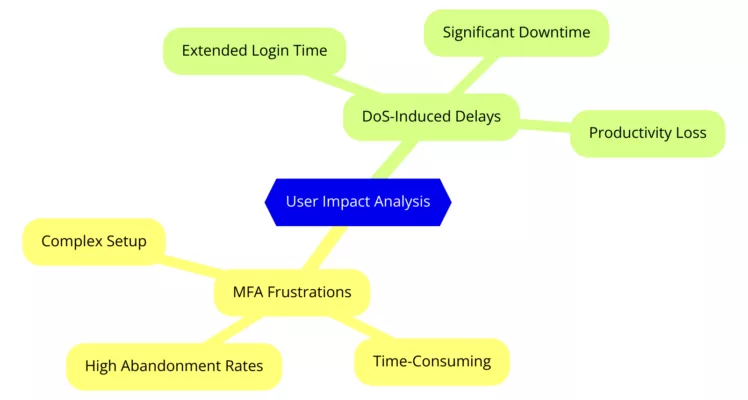
The Stakes of Security
In a world where cyberattacks are becoming increasingly sophisticated and frequent, securing information systems has become a top priority. The consequences of a compromised account can be disastrous—identity theft, fraud, financial loss. The most common threats include phishing, brute force attacks, dictionary attacks, and injection attacks.
To combat these threats, authentication methods have evolved significantly. From the simple password, often considered an easy barrier to breach, we have transitioned to multi-factor authentication systems that are much more robust.
The Evolution of Digital Authentication Security Methods
Over the years, authentication methods have continuously evolved to meet the growing security demands. We have moved from simple password-based authentication, which relies on something you know, to methods that combine several factors:
- Something you know (password)
- Something you possess (security key)
- Something you are (biometrics)
Let’s dive into the various authentication methods, their pros, cons, and applications. We’ll also see how these methods enhance the security of our online accounts and protect our personal data.
Fundamentals of Authentication
Password Authentication: The Historical Pillar
Password authentication is undoubtedly the oldest and most widespread method of verifying a user’s identity. This simple system, which associates a username with a secret password, was long considered enough to secure access to our online accounts.
Advantages:
- Simplicity: Easy to implement and understand for users.
- Universality: Used by almost all online services.
Disadvantages:
- Vulnerability: Passwords can be easily compromised by brute force, dictionary attacks, or phishing.
- Frequent Forgetfulness: Users tend to forget their passwords or create weak ones for easier memorization.
- Reuse: Users often reuse the same password across multiple accounts, increasing the risk of data breaches.
Best Practices for Creating Strong Passwords
To enhance the security of your accounts, it is essential to create strong and unique passwords. Here are some tips:
- Length: A password should ideally be at least 12 characters long.
- Complexity: Use a combination of uppercase and lowercase letters, numbers, and special characters.
- Originality: Avoid using easily found personal information (birth dates, family names, etc.).
- Variety: Use different passwords for each account.
Types of Attacks and How to Protect Yourself
Passwords are regularly targeted by cybercriminals. The main threats include:
- Brute Force Attacks: The hacker tries all possible character combinations until the correct password is found.
- Dictionary Attacks: The hacker uses a list of common words or phrases to guess the password.
- Phishing: The hacker sends fake emails or SMS messages to trick the user into revealing their login credentials.
To protect yourself from these attacks:
- Use a Password Manager: This tool allows you to generate and store strong, unique passwords securely for all your accounts.
- Activate Two-Factor Authentication (2FA): This method adds an extra layer of security by requiring an additional verification during login.
- Be Vigilant About Phishing Attempts: Do not click on suspicious links and always verify the sender’s email address.
Limitations of Password Authentication Alone
Despite following best practices, password authentication has inherent limitations. Passwords can be lost, stolen, or forgotten. Moreover, remembering many complex passwords is challenging for users.
To dive deeper into secure authentication best practices and how to defend against common attacks, refer to the OWASP Authentication Cheat Sheet.
In summary, password authentication has been a pillar of computer security for many years. However, its limitations have become more apparent as threats evolve. It is now necessary to combine passwords with other authentication factors to enhance the security of online accounts.
Now, let’s dive into multi-factor authentication methods that offer more robust protection than passwords alone.
Multi-Factor Authentication (MFA) and Digital Authentication Security
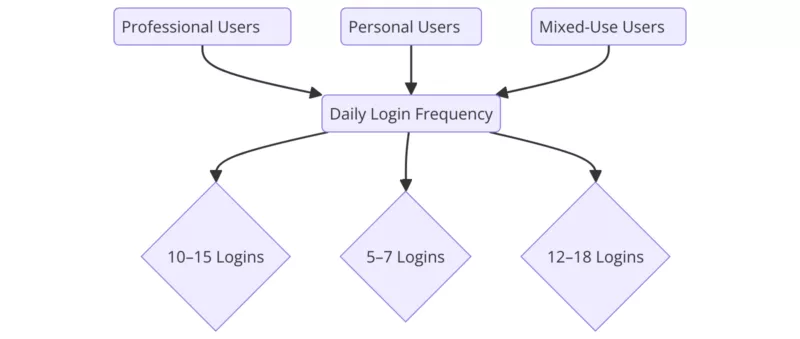
In the previous section, we discussed the limitations of password authentication. To strengthen security, both companies and individuals are increasingly turning to multi-factor authentication methods.
Two-Factor Authentication (2FA)
Two-factor authentication (2FA) is a method that requires the user to provide two distinct proofs of identity to access an account. This approach significantly enhances security by adding an extra layer of protection.
The Principle of 2FA:
2FA relies on combining two different authentication factors. These factors can be:
- Something you know: The password
- Something you possess: A mobile phone, security key, or smart card
- Something you are: A biometric characteristic (fingerprint, facial recognition)
Different Types of 2FA:
- SMS: A one-time code is sent via SMS to the phone number associated with the account.
- Authentication Apps: Apps like Google Authenticator or Microsoft Authenticator generate one-time passcodes.
- Security Keys: Physical devices (USB keys, U2F security keys) that must be inserted into a USB port for login.
Advantages of 2FA for Enhancing Security
Even if an attacker obtains your password, they cannot access your account without the second authentication factor. As a result, 2FA makes brute force and phishing attacks much more difficult.
Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) is an extension of 2FA. It uses more than two authentication factors to further enhance security.
Difference Between 2FA and MFA:
The primary difference between 2FA and MFA lies in the number of factors used. MFA can combine several factors, such as a password, an authentication app, and a fingerprint.
Common Factor Combinations:
- Password + SMS Code
- Password + Security Key
- Password + Fingerprint
- Password + Facial Recognition
Advantages of MFA for Strengthening Security
For comprehensive guidelines on implementing multi-factor authentication securely, consult the NIST Multi-Factor Authentication Guide.
MFA offers an even higher level of security than 2FA by making attacks more difficult.
Comparison Between 2FA and MFA
| Characteristic |
2FA |
MFA |
| Number of Factors |
2 |
2 or more |
| Security |
More secure than password alone |
Even more secure than 2FA |
| Complexity |
More complex than password alone |
More complex than 2FA |
| User Experience |
Can be less convenient than password alone |
Can be less convenient than 2FA |
Let’s now explore other advanced authentication methods, such as biometric authentication and token-based systems.
Advanced Methods for Digital Authentication Security
Biometric Authentication: The Unique Signature of Each Individual
Biometric authentication is based on the idea that each individual has unique physical or behavioral traits that can serve as identification methods. These characteristics are known as biometric traits.
Different Biometric Technologies:
- Fingerprints: One of the most common methods, based on analyzing the ridges and valleys on the fingers.
- Facial Recognition: Uses unique facial features to identify a person.
- Iris Scans: The iris is a complex and unique structure that can be analyzed for authentication.
- Voice Recognition: Analyzes vocal characteristics like tone, rhythm, and timbre to identify a person.
- Hand Geometry: Analyzes hand shape, finger length, and joint position.
- Dynamic Signature: Analyzes how a person signs their name, including speed, pressure, and angle.
Advantages of Biometrics:
- Enhanced Security: Biometric traits are hard to falsify or steal.
- Ease of Use: Biometric authentication is often more convenient than typing a password or PIN.
- No Forgetfulness: It’s impossible to forget your face or fingerprint.
Disadvantages of Biometrics:
- Privacy Concerns: Storing and using biometric data raises significant privacy issues.
- Cost: Implementing biometric authentication systems can be expensive.
- Vulnerabilities: Although rare, security breaches can allow bypassing of biometric systems.
Security and Privacy Challenges
- Forgery: Techniques exist to forge biometric data, such as creating molds of fingerprints or using facial masks.
- Data Protection: Biometric data is considered sensitive information and must be protected from unauthorized access.
- Consent: Users must give informed consent before collecting and processing their biometric data.
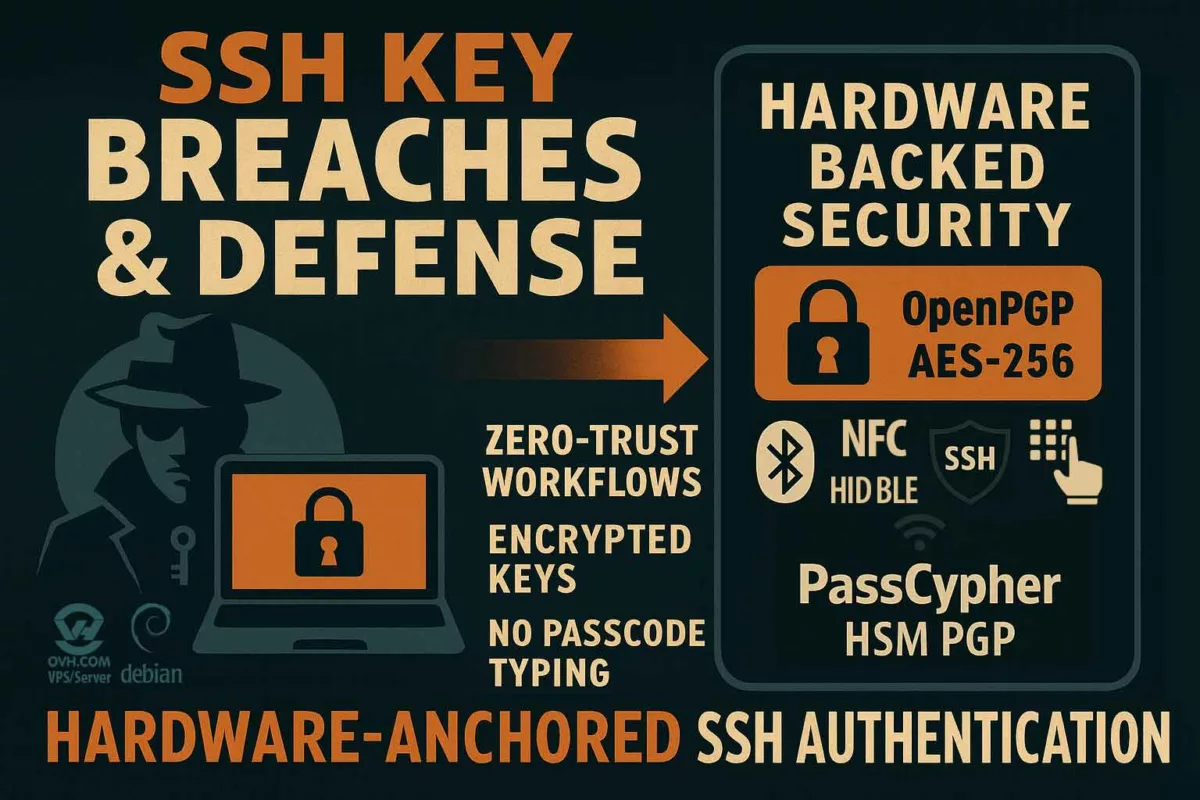
EviOTP NFC HSM: Secure Device-Based Authentication
Another approach to strengthening authentication security involves using secure physical devices. EviOTP NFC HSM is an excellent example of this category. EviOTP NFC HSM technology is embedded in two key products: PassCypher NFC HSM Lite and PassCypher NFC HSM Master, both from Fullsecure Andorra. These products are equipped with quantum security features and are protected by two international invention patents, ensuring cutting-edge protection and international security compliance. These patents ensure a high level of security and protection across borders.This system combines several technologies to offer optimal protection and unmatched flexibility:
- NFC (Near Field Communication): Users can generate unique OTP codes simply by bringing their smartphone close to an NFC reader.
- HSM (Hardware Security Module): Cryptographic keys are securely stored in a dedicated hardware module, making software attacks much more difficult.
- TOTP and HOTP: These algorithms ensure the generation of one-time-use codes, making replay attacks nearly impossible.
- Advanced Customization: EviOTP NFC HSM allows customization of access to each secret key by adding passwords, fingerprints, geolocation, or other additional authentication factors.
- Autonomy: This system operates without servers, databases, or the need to create an account, ensuring absolute anonymity and maximum security.
Advantages of EviOTP NFC HSM:
- Maximum Security: Combining these technologies provides unparalleled security, especially through hardware key protection and customizable access.
- Ease of Use: NFC technology makes authentication simple and intuitive.
- Flexibility: This system can be adapted to different environments and easily integrates with many applications.
- Compliance: EviOTP NFC HSM often meets the strictest security standards, ensuring regulatory compliance.
- Anonymity and Privacy: Operating without servers or databases ensures user privacy.
- Versatility: EviOTP NFC HSM allows for the generation of all types of PIN codes, regardless of length.
Protection Against Common Attacks
Phishing is one of the biggest threats to online account security. By generating one-time-use OTP codes directly on the secure device, EviOTP NFC HSM makes these attacks far less effective. Even if a user is tricked into entering credentials on a fake website, the OTP code generated will be invalid a few seconds later. Additionally, storing cryptographic keys in an HSM makes software-based attacks much more difficult. Even if a device is compromised, the keys cannot be extracted.
In summary, EviOTP NFC HSM represents a cutting-edge authentication solution, ideal for organizations seeking maximum security and flexibility. This solution is particularly suited for sectors where data protection is critical, such as banking, healthcare, and industry. EviOTP NFC HSM offers a multi-layered defense that makes attacks extremely difficult, if not impossible, to carry out.
Comparison Table of Authentication Methods
| Method |
Authentication Factors |
Security |
Ease of Use |
Cost |
Flexibility |
| Password |
Something you know |
Low |
Very easy |
Low |
Very high |
| PIN |
Something you know |
Medium |
Easy |
Low |
Medium |
| Security Key |
Something you possess |
Medium-High |
Medium |
Medium |
Medium |
| Authenticator Apps |
Something you possess |
Medium |
Medium |
Low |
Medium |
| SMS |
Something you possess |
Low |
Easy |
Low |
Medium |
| Biometrics (fingerprint, facial) |
Something you are |
High |
Very easy |
Medium-High |
Medium |
| EviOTP NFC HSM |
Something you possess (NFC) |
Very High |
Very easy |
Medium |
High |
Specific Explanations for EviOTP NFC HSM:
- Very High Security: Thanks to secure key storage in an HSM, dynamic OTP generation, and the ability to customize access with passwords, fingerprints, or geolocation.
- Very High Ease of Use: NFC technology makes authentication simple and intuitive.
- Medium Cost: The cost depends on the number of licenses and additional features chosen.
- High Flexibility: EviOTP NFC HSM can be used in many contexts and adapted to various needs.
Other Advanced Authentication Methods
Token, Certificate, and Smart Card Authentication: Enhanced Security
These authentication methods rely on using physical or digital devices that contain secure identification information.
- Token Authentication: A token is a small physical device (often USB-sized) that generates one-time-use codes. These codes are used in addition to a password to access an account. Tokens are generally more secure than SMS codes, as they are not vulnerable to interception.
- Certificate Authentication: A digital certificate is an electronic file that links an identity to a public key. This public key can be used to verify the authenticity of a digital signature or encrypt data. Certificates are often stored on smart cards.
- Smart Card Authentication: A smart card is a small plastic card with an integrated circuit that can store secure digital information, such as private keys and certificates. Smart cards are widely used in banking and security.
Advantages of These Methods:
- Enhanced Security: Identification information is stored on a secure physical device, making it harder to compromise.
- Flexibility: These methods can be used for various applications, from corporate network access to digitally signing documents.
- Interoperability: Digital certificates are based on open standards, facilitating their interoperability with different systems.
Disadvantages and Challenges:
- Cost: Implementing an authentication infrastructure based on tokens, certificates, or smart cards can be expensive.
- Complexity: These methods can be more complex to implement and manage than traditional authentication methods.
- Loss or Theft: Losing a token or smart card can compromise account security.
Behavioral Authentication
Behavioral authentication analyzes an individual’s habits and behavior to verify their identity. This approach can complement traditional authentication methods.
Principle:
The system analyzes different aspects of the user’s behavior, such as typing speed, dynamic signature, browsing habits, etc. Any significant deviation from usual behavior can trigger an alert.
Advantages:
- Intrusion Detection: This method can detect suspicious activity, even if the attacker knows the user’s credentials.
- Adaptation: Behavioral authentication systems can adapt to changes in user behavior.
Disadvantages:
- False Positives: The system may trigger false alerts if the user’s behavior legitimately changes.
- Complexity: Implementing behavioral authentication systems can be complex and expensive.
In summary, token, certificate, smart card, and behavioral authentication methods offer high levels of security and can complement traditional methods. The choice of the most suitable authentication method will depend on the specific needs of each organization or individual.
Authentication Protocols
Authentication protocols define a set of standardized rules and procedures for verifying a user’s or system’s identity. They enable secure communication between different systems and applications.
Single Sign-On (SSO): One Access for All
Single Sign-On (SSO) is a protocol that allows a user to log in to multiple applications using a single authentication. Once authenticated, the user does not need to re-enter their credentials to access other applications.
How SSO Works:
During the first login, the user authenticates with an identity provider (IdP). The provider verifies the credentials and issues an authentication token. This token is then sent to the destination application (relying service), which validates it and grants the user access.
SSO Protocols (SAML, OAuth, OpenID Connect):
- SAML (Security Assertion Markup Language): A standard XML protocol for exchanging authentication information between an identity provider and a relying service.
- OAuth: An authorization protocol that allows third-party applications to access a user’s resources on another service without needing the user’s credentials.
- OpenID Connect: An authentication protocol based on OAuth 2.0 that provides an additional identity layer, enabling applications to know the user’s identity.
Advantages of SSO:
- Improved User Experience: Users only need to enter their credentials once.
- Increased Productivity: Users can access the applications they need faster.
- Enhanced Security: SSO centralizes identity and access management, making it easier to implement security policies.
Disadvantages of SSO:
- Single Point of Failure: If the identity provider is compromised, all connected services may be affected.
- Complexity: Implementing an SSO system can be complex, especially in heterogeneous environments.
OAuth/OpenID Connect: Third-Party Authentication
OAuth and OpenID Connect are two closely related protocols that allow third-party applications to access a user’s resources on another service.
Principle of Third-Party Authentication:
A user logs into a third-party application (such as Facebook or Google) using existing credentials. The third-party application then requests the user’s permission to access certain information. If the user agrees, the third-party application receives an access token that allows it to access the requested resources.
Differences Between OAuth and OpenID Connect:
- OAuth focuses on authorization, while OpenID Connect adds an identity layer, allowing applications to know the user’s identity.
Typical Use Cases:
- Social Login: Logging into an application using Facebook, Google, etc.
- Mobile App Development: Using authentication services from third-party providers to simplify the login process.
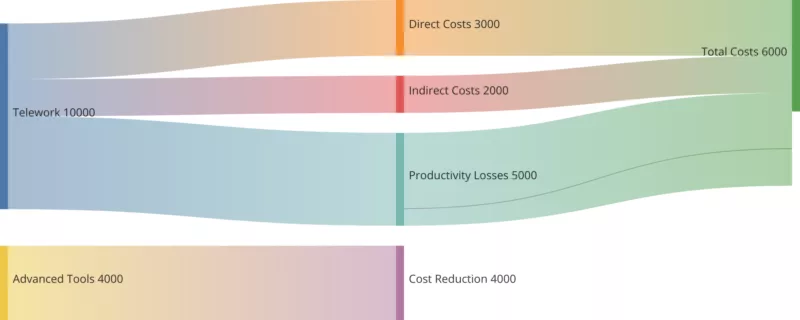
The Stakes of Authentication in the Modern Digital World
Authentication has become a central issue in our digital society. Threats are constantly evolving, regulations are multiplying, and user expectations regarding security are increasing.
Recent Threats
- Sophisticated Phishing: Phishing attacks are becoming increasingly sophisticated, using social engineering techniques and highly realistic fake websites to deceive users.
- Password Attacks: Brute force, dictionary, and password-spray attacks remain significant threats.
- Injection Attacks: Injection attacks (SQL injection, XSS) allow attackers to execute malicious code on servers.
- Session Hijacking: Attackers can steal session cookies to log into accounts without the legitimate user’s credentials.
Data Security Regulations
Many regulations have been put in place to protect personal data and strengthen information system security. Some of the most well-known include:
- GDPR (General Data Protection Regulation): This European regulation requires companies to implement appropriate technical and organizational measures to ensure a level of security adapted to the risks.
- CCPA (California Consumer Privacy Act): This Californian law grants consumers additional rights regarding the protection of their personal data.
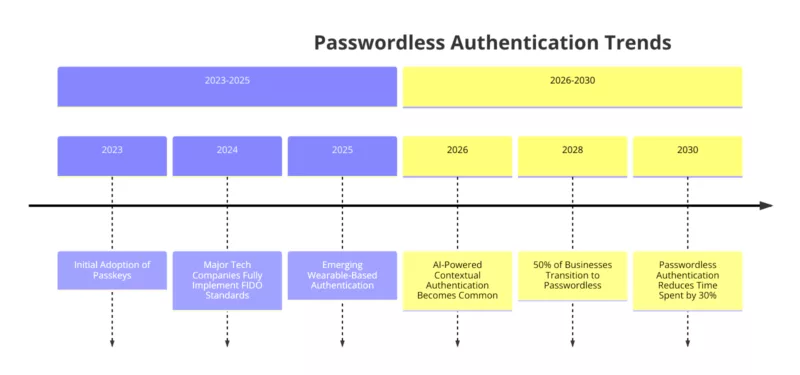
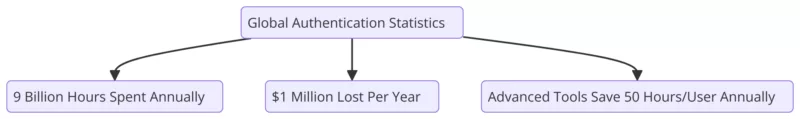
Future Trends in Authentication
- Passwordless Authentication: As passwords are a prime target for attacks, many initiatives aim to replace them with more secure authentication methods like biometrics or security keys.
- Passkeys: Passkeys are a new authentication technology that allows users to log in to websites and apps without needing to create or remember passwords.
- Artificial Intelligence: AI can be used to improve fraud detection and personalize the user experience by adapting authentication methods based on context.
Summary of Authentication Methods
Authentication is a constantly evolving field. To combat growing threats, it is essential to adopt strong authentication methods and stay informed about the latest trends.
Summary of Various Methods:
Throughout this article, we’ve seen that many authentication methods exist, each with advantages and disadvantages. The choice of the most appropriate method will depend on factors such as:
- The required level of security
- Ease of use
- Implementation cost
- Regulatory constraints
Recommendations for Choosing the Most Appropriate Authentication Method
- Combine Multiple Authentication Factors: Combining multiple factors (something you know, something you possess, something you are) is the most effective way to enhance security.
- Use Strong Authentication Methods: Prioritize biometric authentication, security keys, and digital certificates.
- Implement Strict Security Policies: Set clear rules for creating and managing passwords, raising user awareness, and responding to security incidents.
- Stay Updated on the Latest Threats and Best Practices: Stay informed about the latest security trends and regularly update authentication systems.
Future Challenges in Authentication
The future challenges of authentication are numerous:
- Balancing Security and Usability: It is essential to find a balance between security and ease of use so that users adopt new authentication methods.
- Privacy Protection: Biometric authentication methods raise significant privacy concerns.
- Interoperability: Developing open standards to facilitate interoperability between different authentication systems is necessary.
Building a Future of Resilient Digital Authentication Security
The continuous evolution of threats in the digital landscape demands a proactive approach to Digital Authentication Security. Scientific research consistently highlights the importance of layered security systems, combining various authentication factors to mitigate vulnerabilities. By integrating advanced solutions such as multi-factor authentication (MFA), biometric systems, and hardware-based security like EviOTP NFC HSM, organizations and individuals can significantly reduce their exposure to cyber risks.
Understanding the science behind authentication algorithms, such as the cryptographic protocols securing biometric data or the OTP generation process, is essential for developing robust defenses. As future technologies like quantum computing emerge, the security models we rely on today will need adaptation and reinforcement. Hence, a commitment to ongoing research and technological advancements is crucial for maintaining resilient Digital Authentication Security systems.
Looking forward, the focus must shift toward creating secure, user-friendly authentication frameworks that also respect privacy concerns. This will ensure that as we move deeper into the digital age, our data remains secure without sacrificing convenience. Maintaining vigilance, investing in new technologies, and continuously refining our approaches will be key to staying ahead of the next wave of cyber threats.