How to protect yourself from the attack against Microsoft Exchange?
The attack against Microsoft Exchange was a serious security breach in 2023. Thousands of organizations worldwide were hacked by cybercriminals who exploited vulnerabilities in Microsoft’s email servers. How did this happen? What were the consequences? How did Microsoft react? And most importantly, how can you protect your data and communications? Read our comprehensive analysis and discover Freemindtronic’s technology solutions.
Cyberattack against Microsoft: discover the potential dangers of stalkerware spyware, one of the attack vectors used by hackers. Stay informed by browsing our constantly updated topics.
How the attack against Microsoft Exchange on December 13, 2023 exposed thousands of email accounts
On December 13, 2023, Microsoft was the target of a sophisticated attack by a hacker group called Lapsus$. This attack exploited another vulnerability in Microsoft Exchange, known as CVE-2023-23415, which allowed the attackers to execute remote code on the email servers using the ICMP protocol. The attackers were able to access the email accounts of more than 10,000 Microsoft employees, some of whom were working on sensitive projects such as the development of GTA VI or the launch of Windows 12. The attackers also published part of the stolen data on a website called DarkBeam, where they sold more than 750 million fraudulent Microsoft accounts. Microsoft reacted quickly by releasing a security patch on December 15, 2023, and collaborating with the authorities to arrest the perpetrators of the attack. One of the members of the Lapsus$ group, an Albanian hacker named Kurtaj, was arrested on December 20, 2023, thanks to the cooperation between the American and European intelligence services1234.
What were the objectives and consequences of the attack?
The attack against Microsoft Exchange affected more than 20,000 email servers worldwide, belonging to businesses, institutions and organizations from different sectors. These servers were vulnerable because they used outdated versions of the software, which no longer received security updates. The attack exploited a critical vulnerability known as ProxyLogon (CVE-2023-23415), allowing the attackers to execute remote code on the servers and access the email accounts. Despite the efforts to solve the problem, many vulnerable servers remained active, exposing the email accounts of about 30,000 high-level employees, including executives and engineers. The attackers were able to steal confidential information, such as internal projects, development plans, trade secrets or source codes.
What were the objectives of the attack?
The attack was attributed to Lapsus$, a hacker group linked to Russia. According to Microsoft, the group’s main objective was to gain access to sensitive information from various targets, such as government agencies, think tanks, NGOs, law firms, medical institutions, etc. The group also aimed to compromise the security and reputation of Microsoft, one of the leading technology companies in the world. The attack was part of a larger campaign that also involved the SolarWinds hack, which affected thousands of organizations in 2020.
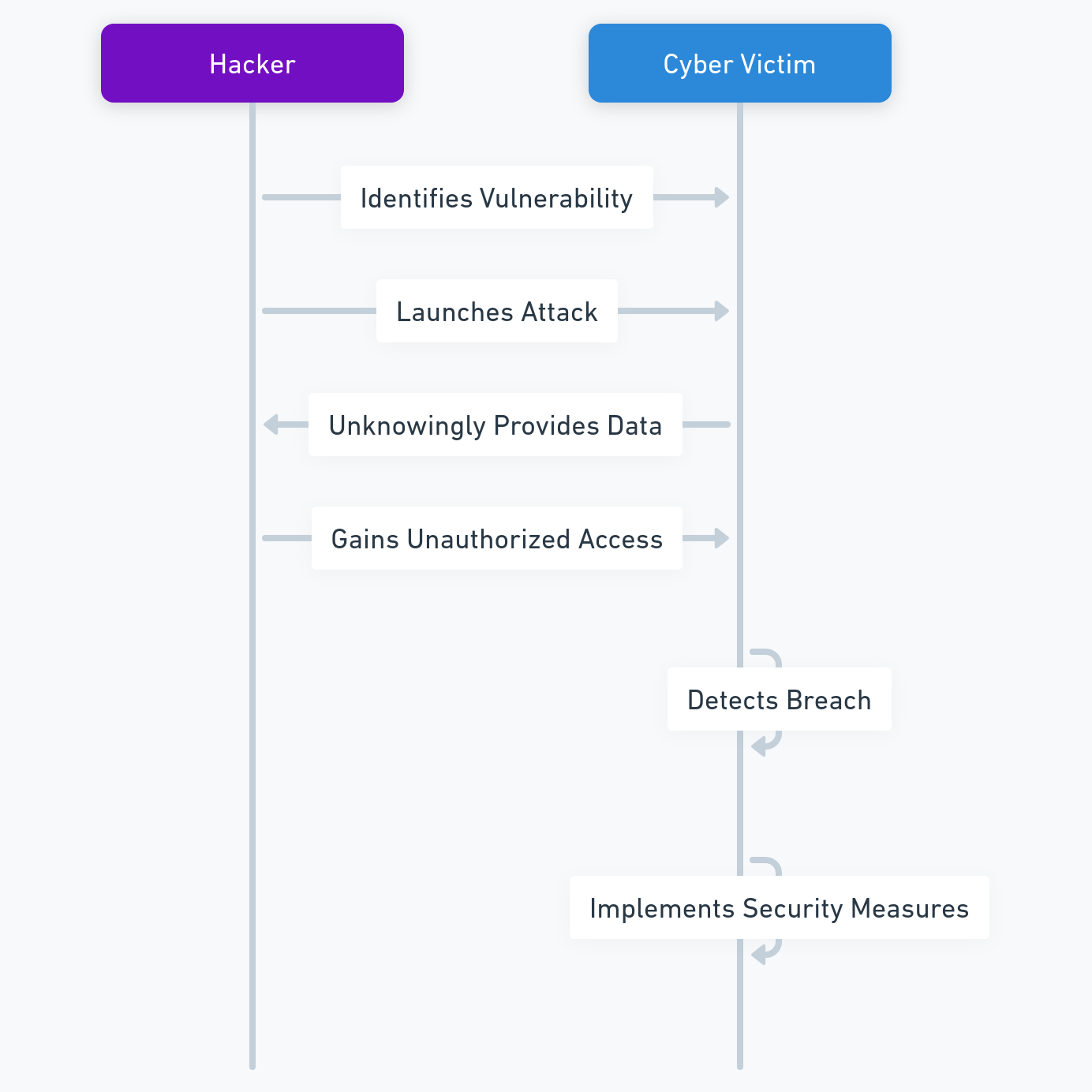
What were the impacts of the attack?
The attack had serious impacts on the victims, both in terms of data loss and reputation damage. The data stolen by the attackers included personal and professional information, such as names, addresses, phone numbers, email addresses, passwords, bank details, credit card numbers, health records, etc. The attackers also leaked some of the data on the DarkBeam website, where they offered to sell the data to the highest bidder. This exposed the victims to potential identity theft, fraud, blackmail, extortion, or other cybercrimes. The attack also damaged the reputation of Microsoft and its customers, who were seen as vulnerable and unreliable by their partners, clients, and users. The attack also raised questions about the security and privacy of email communication, which is widely used in the digital world.
What were the consequences of the attack?
The attack had several consequences for Microsoft and its customers, who had to take urgent measures to mitigate the damage and prevent further attacks. Microsoft had to release a security patch for the vulnerability, and urge its customers to update their software as soon as possible. Microsoft also had to investigate the origin and extent of the attack, and cooperate with the authorities to identify and arrest the attackers. Microsoft also had to provide support and assistance to its customers, who had to deal with the aftermath of the attack. The customers had to check their email accounts for any signs of compromise, and change their passwords and security settings. They also had to notify their contacts, partners, and clients about the breach, and reassure them about the security of their data. They also had to monitor their online activities and accounts for any suspicious or fraudulent transactions. The attack also forced Microsoft and its customers to review and improve their security policies and practices, and adopt new solutions and technologies to protect their data and communication.
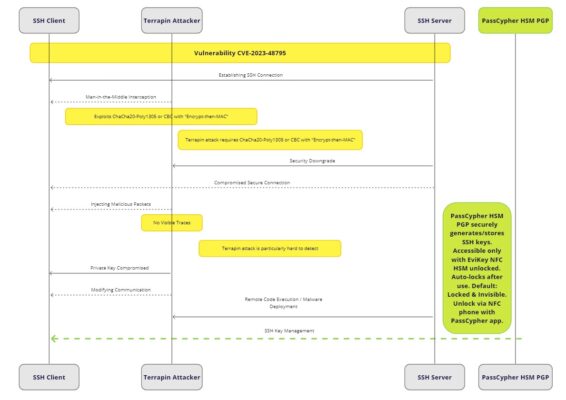
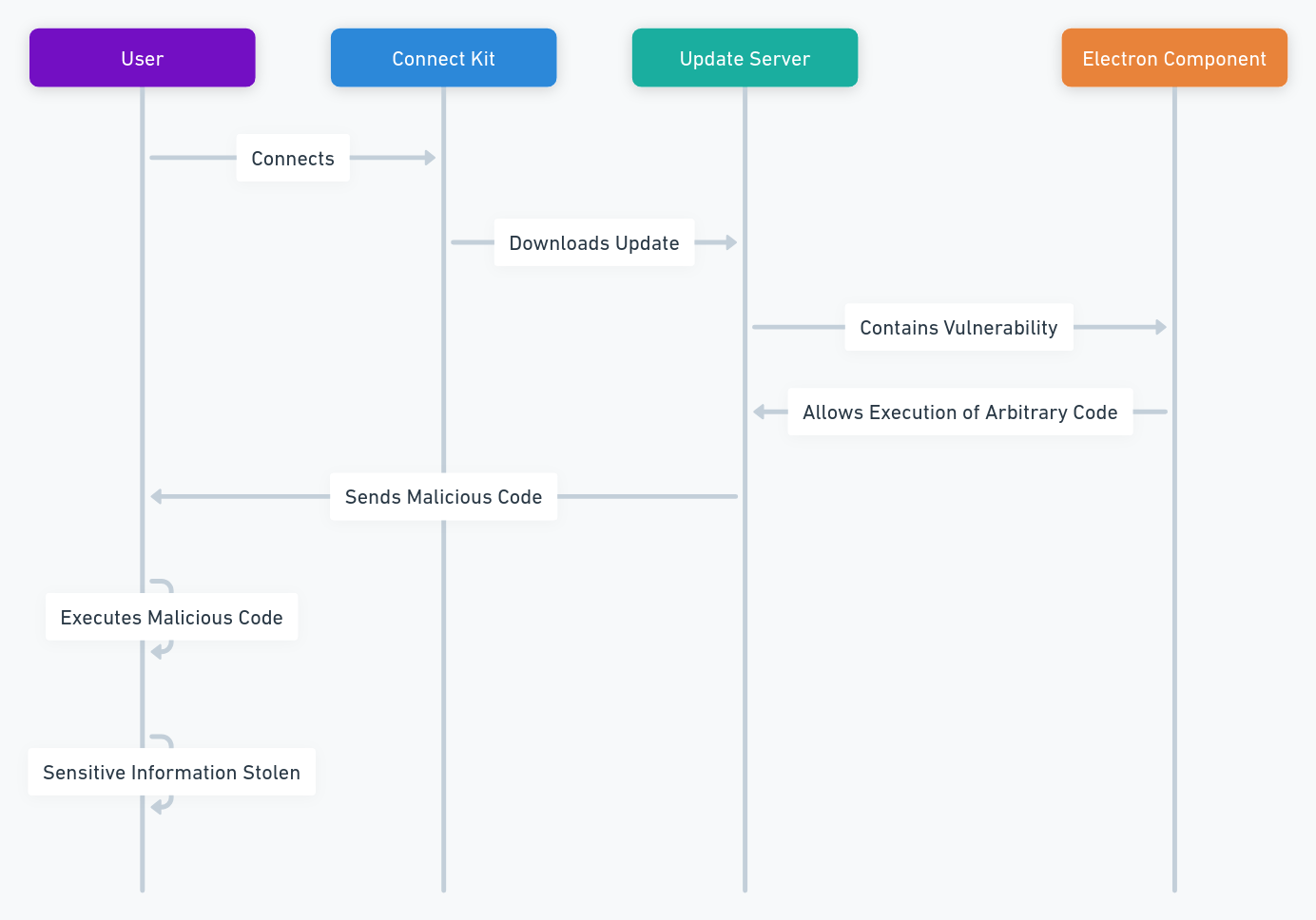
How did the attack succeed despite Microsoft’s defenses?
The attack was sophisticated and stealthy, using several techniques to bypass Microsoft’s defenses. First, the attackers exploited a zero-day vulnerability, which means that it was unknown to Microsoft and the public until it was discovered and reported. Second, the attackers used a proxy tool to disguise their origin and avoid detection. Third, the attackers used web shells to maintain persistent access to the servers and execute commands remotely. Fourth, the attackers used encryption and obfuscation to hide their malicious code and data. Fifth, the attackers targeted specific servers and accounts, rather than launching a massive attack that would have raised more suspicion.
What are the communication vulnerabilities exploited by the attack?
The attack exploited several communication vulnerabilities, such as:
- Targeted phishing: The attackers sent fake emails to the victims, pretending to be from legitimate sources, such as Microsoft, their bank, or their employer. The emails contained malicious links or attachments, that led the victims to compromised websites or downloaded malware on their devices. The attackers then used the malware to access the email servers and accounts.
- SolarWinds exploitation: The attackers also used the SolarWinds hack, which was a massive cyberattack that compromised the software company SolarWinds and its customers, including Microsoft. The attackers inserted a backdoor in the SolarWinds software, which allowed them to access the networks and systems of the customers who installed the software. The attackers then used the backdoor to access the email servers and accounts.
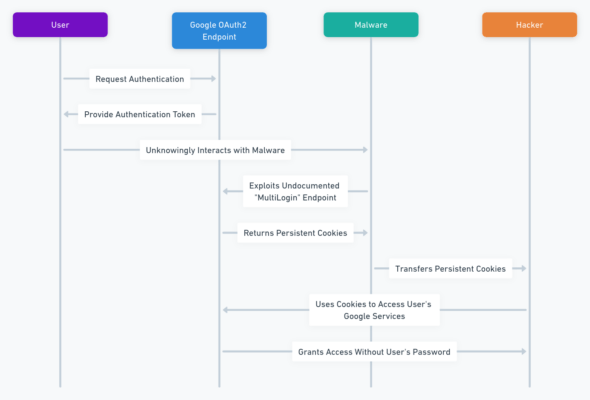
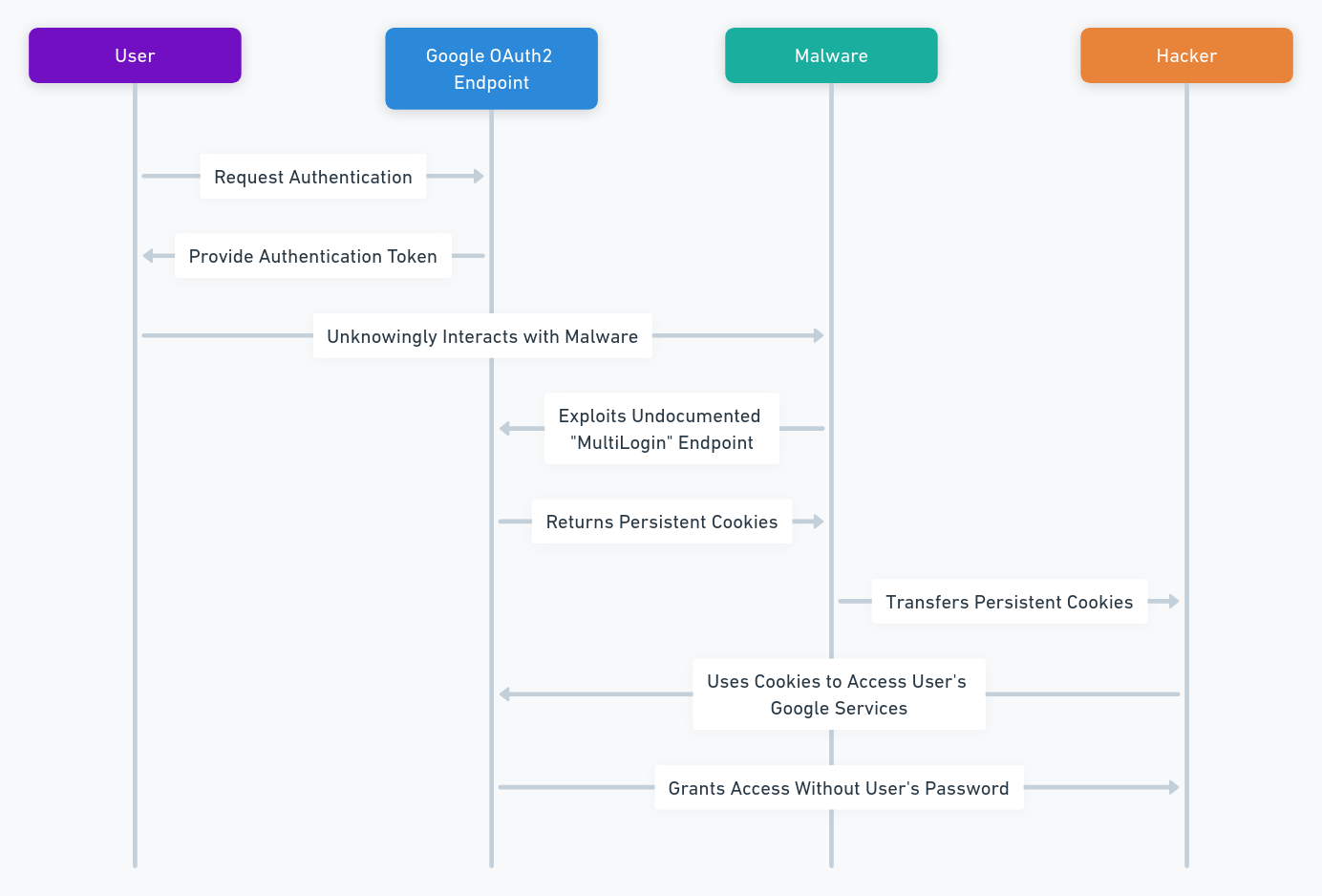
- Brute force attack: The attackers also used a brute force attack, which is a trial-and-error method to guess the passwords or encryption keys of the email accounts. The attackers used automated tools to generate and test a large number of possible combinations, until they found the right one. The attackers then used the passwords or keys to access the email accounts.
- SQL injection: The attackers also used a SQL injection, which is a technique to insert malicious SQL commands into a web application that interacts with a database. The attackers used the SQL commands to manipulate the database, and access or modify the data stored in it. The attackers then used the data to access the email accounts.
Why did the detection and defense systems of Microsoft Exchange not work?
The detection and defense systems of Microsoft Exchange did not work because the attackers used advanced techniques to evade them. For example, the attackers used a proxy tool to hide their IP address and location, and avoid being traced or blocked by firewalls or antivirus software. The attackers also used web shells to create a backdoor on the servers, and execute commands remotely, without being noticed by the system administrators or the security software. The attackers also used encryption and obfuscation to conceal their malicious code and data, and prevent them from being analyzed or detected by the security software. The attackers also used zero-day vulnerability, which was not known or patched by Microsoft, and therefore not protected by the security software.
How did Microsoft react to the attack?
Microsoft reacted to the attack by taking several actions, such as:
The main actions of Microsoft
- Releasing a security patch: Microsoft released a security patch for the vulnerability exploited by the attack, and urged its customers to update their software as soon as possible. The patch fixed the vulnerability and prevented further attacks.
- Investigating the attack: Microsoft investigated the origin and extent of the attack, and collected evidence and information about the attackers and their methods. Microsoft also cooperated with the authorities and other organizations to identify and arrest the attackers.
- Providing support and assistance: Microsoft provided support and assistance to its customers, who were affected by the attack. Microsoft offered guidance and tools to help the customers check their email accounts for any signs of compromise, and change their passwords and security settings. Microsoft also offered free credit monitoring and identity theft protection services to the customers, who had their personal and financial data stolen by the attackers.
Microsoft also released patches for the vulnerabilities exploited by the attack
Microsoft also released patches for the other vulnerabilities exploited by the attack, such as the SolarWinds vulnerability, the brute force vulnerability, and the SQL injection vulnerability. Microsoft also improved its detection and defense systems, and added new features and functions to its software, to enhance the security and privacy of email communication.
What are the lessons to be learned from the attack?
The attack was a wake-up call for Microsoft and its customers, who had to learn from their mistakes and improve their security practices. Some of the lessons to be learned from the attack are:
Email security
Email is one of the most widely used communication tools in the digital world, but also one of the most vulnerable to cyberattacks. Therefore, it is essential to ensure the security and privacy of email communication, by applying some best practices, such as:
- Using strong and unique passwords for each email account, and changing them regularly.
- Using multi-factor authentication (MFA) to verify the identity of the email users, and prevent unauthorized access.
- Using encryption to protect the content and attachments of the email messages, and prevent them from being read or modified by third parties.
- Using digital signatures to verify the authenticity and integrity of the email messages, and prevent them from being spoofed or tampered with.
- Using spam filters and antivirus software to block and remove malicious emails, and avoid clicking on suspicious links or attachments.
- Using secure email providers and platforms, that comply with the latest security standards and regulations, and offer features such as end-to-end encryption, zero-knowledge encryption, or self-destructing messages.
Multi-factor authentication
Multi-factor authentication (MFA) is a security method that requires the user to provide two or more pieces of evidence to prove their identity, before accessing a system or a service. The pieces of evidence can be something the user knows (such as a password or a PIN), something the user has (such as a smartphone or a token), or something the user is (such as a fingerprint or a face scan). MFA can prevent unauthorized access to email accounts, even if the password is compromised, by adding an extra layer of security. Therefore, it is recommended to enable MFA for all email accounts, and use reliable and secure methods, such as biometric authentication, one-time passwords, or push notifications.
Principle of least privilege
The principle of least privilege (POLP) is a security concept that states that each user or system should have the minimum level of access or permissions required to perform their tasks, and nothing more. POLP can reduce the risk of data breaches, by limiting the exposure and impact of a potential attack. Therefore, it is advisable to apply POLP to email accounts, and assign different roles and privileges to different users, depending on their needs and responsibilities. For example, only authorized users should have access to sensitive or confidential information, and only administrators should have access to system settings or configuration.
Software update
Software update is a process that involves installing the latest versions or patches of the software, to fix bugs, improve performance, or add new features. Software update is crucial for email security, as it can prevent the exploitation of vulnerabilities that could allow attackers to access or compromise the email servers or accounts. Therefore, it is important to update the software regularly, and install the security patches as soon as they are available. It is also important to update the software of the devices that are used to access the email accounts, such as computers or smartphones, and use the latest versions of the browsers or the applications.
System monitoring
System monitoring is a process that involves observing and analyzing the activity and performance of the system, to detect and resolve any issues or anomalies. System monitoring is vital for email security, as it can help to identify and stop any potential attacks, before they cause any damage or disruption. Therefore, it is essential to monitor the email servers and accounts, and use tools and techniques, such as logs, alerts, reports, or audits, to collect and analyze the data. It is also essential to monitor the email traffic and behavior, and use tools and techniques, such as firewalls, intrusion detection systems, or anomaly detection systems, to filter and block any malicious or suspicious activity.
User awareness
User awareness is a state of knowledge and understanding of the users, regarding the security risks and threats that they may face, and the best practices and policies that they should follow, to protect themselves and the system. User awareness is key for email security, as it can prevent many human errors or mistakes, that could compromise the email accounts or expose the data. Therefore, it is important to educate and train the email users, and provide them with the necessary information and guidance, to help them recognize and avoid any phishing, malware, or social engineering attacks, that could target their email accounts.
What are the best practices to strengthen information security?
Information security is the practice of protecting the confidentiality, integrity, and availability of the information, from unauthorized or malicious access, use, modification, or destruction. Information security is essential for email communication, as it can ensure the protection and privacy of the data and messages that are exchanged. Some of the best practices to strengthen information security are:
- Adopt the Zero Trust model: The Zero Trust model is a security approach that assumes that no user or system can be trusted by default, and that each request or transaction must be verified and authorized, before granting access or permission. The Zero Trust model can enhance information security, by reducing the attack surface and preventing the lateral movement of the attackers, within the system.
- Use advanced protection solutions: Advanced protection solutions are security solutions that use artificial intelligence, machine learning, or other technologies, to detect and respond to the most sophisticated and complex cyberattacks, that could target the email accounts or data. Some of these solutions are endpoint detection and response (EDR), identity and access management (IAM), or data encryption solutions.
- Hire cybersecurity experts: Cybersecurity experts are professionals who have the skills and knowledge to design, implement, and maintain the security of the system and the information, and to prevent, detect, and respond to any cyberattacks, that could affect the email accounts or data. Cybersecurity experts can help to strengthen information security, by providing advice, guidance, and support, to the email users and administrators.
How can Freemindtronic technology help to fight against this type of attack?
Freemindtronic offers innovative and effective technology solutions such as EviCypher NFC HSM and EviPass NFC HSM and EviOTP NFC HSM and other PGP HSMs. They can help businesses to fight against this type of attack based on Zero Day and other threats. Their technology is embedded in products such as DataShielder NFC HSM and DataShielder HSM PGP and DataShielder Defense or PassCypher NFC HSM or PassCypher HSM PGP. These products provide security and communication features for data, email and password management and offline OTP secret keys.
- DataShielder NFC HSM is a portable device that allows to encrypt and decrypt data and communication on a computer or on an Android NFC smartphone. It uses a contactless hardware security module (HSM) that generates and stores encryption keys securely and segmented. It protects the keys that encrypt contactless communication. This has the effect of effectively fighting against all types of communication vulnerabilities, since the messages and attachments will remain encrypted even if they are corrupted. This function regardless of where the attack comes from, internal or external to the company. It is a counter-espionage solution. It also offers other features, such as password management, 2FA – OTP (TOTP and HOTP) secret keys. In addition, DataShielder works offline, without server and without database. It has a configurable multi-authentication system, strong authentication and secure key sharing.
- DataShielder HSM PGP is an application that transforms all types of physical storage media (USB key, S, SSD, KeyChain / KeyStore) connected or not connected into HSM. It has the same features as its NFC HSM version. However, it also uses standard AES-256 and RSA 4096 algorithms, as well as OpenPGP algorithms. It uses its HSMs to manage and store PGP keys securely. In the same way, it protects email against phishing and other email threats. It also offers other features, such as digital signature, identity verification or secure key sharing.
- DataShielder Defense is a dual-use platform for civilian and military use that offers many functions including all those previously mentioned. It also works in real time without server, without database from any type of HSM including NFC. It also has functions to add trust criteria to fight against identity theft. It protects data and communication against cyberattacks and data breaches.
In summary
To safeguard against the Microsoft Exchange attack, prioritize security updates and patches. Embrace Freemindtronic’s innovative solutions for enhanced protection. Stay vigilant against phishing and employ robust authentication methods. Opt for encryption to shield communications. Engage cybersecurity experts for advanced defense strategies. By adopting these measures, you can fortify your defenses against cyber threats and ensure your data’s safety.