Physical barrier to regaining control of the data of the Observatoire du Monde Cybernétique CEIS DGRIS France – June 2nd 2021
Freemindtronic: A physical barrier to allow users to regain control of their data

Interview with Jacques Gascuel (co-founder)
Presentation
Jacques Gascuel created the company Freemindtronic in 2010. Previously at the head of a computer company in rural areas, this graduate in electrical engineering and law, specialist in industrial maintenance, measured the impact of computer hacking following the compromise of the systems of one of his breeder customers, which greatly affected the production of the latter. Jacques Gascuel, after the resolution of this incident, turned to cyber safety and security by founding Freemindtronic (“the freedom to create in electronics”). The company, initially based in Comminges, established itself in Andorra from 2016.
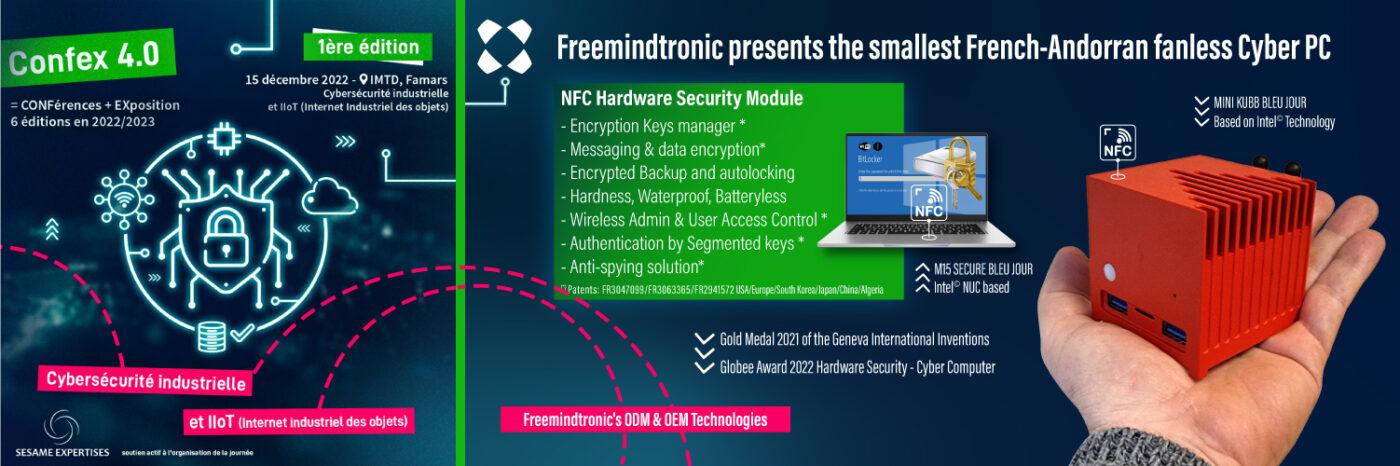
Freemindtronic ensures the complete control of its technological innovations – therefore from the design phase to the industrialization of solutions – and thus does not subcontract any stage of the development cycle. Considering the “all digital” as a threat, the company is guided in its activities by two objectives: to put the human at the heart of security and to preserve as much as possible the anonymity of users.
Solution
All Freemindtronic solutions have as a common denominator a name starting with “Evi” (from the English word “evidence”) with among others EviKey, EviDisk, EviLock, EviToken and EviCard. Such a choice refers to the legal and material evidence produced by a tamper-proof black box, Jacques Gascuel’s patented invention on the safety of electrical appliances with traceability. The latest “EviCypher” solution, the result of four years of R&D, has been ready since March 2021 and aims to restore users control of their data in general, as well as to fight against cybercrime and corporate espionage in particular.
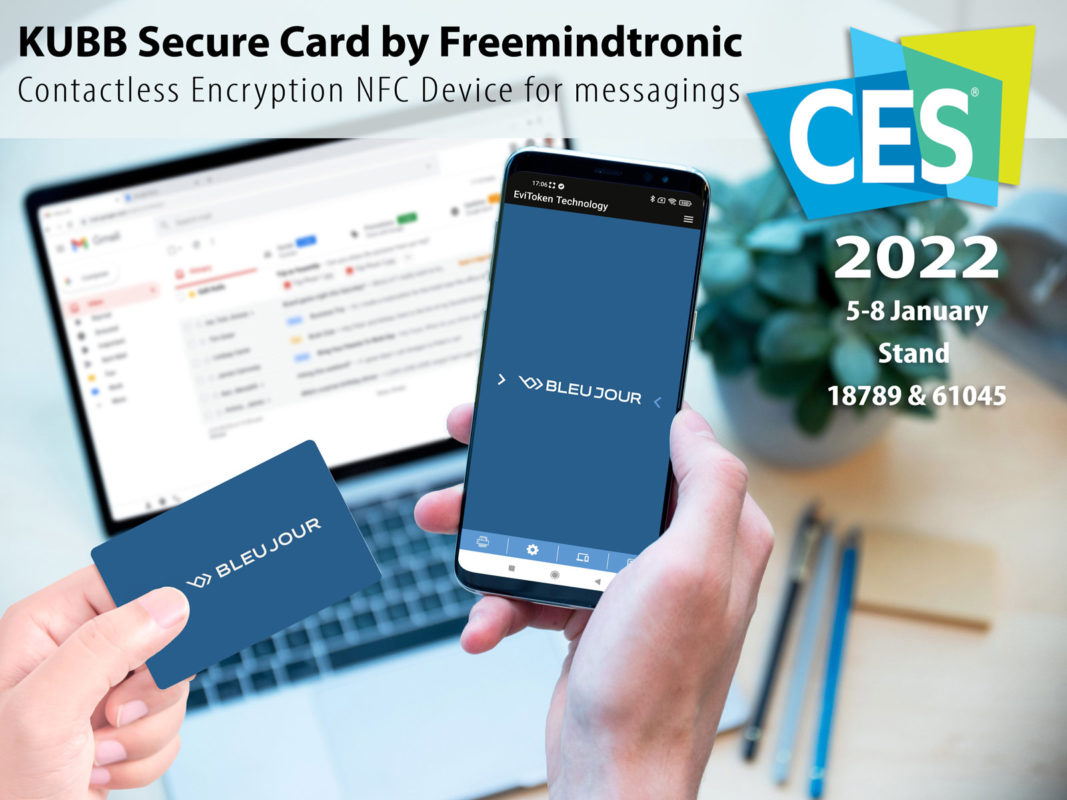
EviCypher is a contactless end-to-end encryption solution from an NFC device [1] (Near-field communication). It is based on an NFC application and physical device in the form of a card. The latter is capable of managing and storing “complicated” passwords, symmetric encryption algorithms (up to two hundred AES 256 keys) and asymmetric encryption (four RSA 2048 keys or two RSA 4096 keys). This “greentech” card has been designed from sustainable materials (fiberglass without halogen and emitting no toxic gases or hazardous residues), which ensure a service life of more than forty years and operation in extreme environments. Without a battery, it recovers energy via the NFC signal emitted by an NFC terminal (energy harvesting). This device, which is only activated on demand, is by default a passive product called “air gap”, which consists in physically isolating from any network the system to be secured.
The application allows you to configure the encryption methods of the EviCypher card and to associate up to twelve “trust criteria” (including geolocation, password, fingerprint, EAN and QR codes…). The latter, which must be respected by any user wishing to decrypt the message, then make it possible to block any fraudulent access attempts in case of theft of the card among others.
The encryption of a content is thus carried out by passing the EviCypher card at the NFC receiver of a terminal equipped with the application (computer, NFC Android smartphone, etc.). The recipient, upon receipt of the message, must repeat the gesture so that his card proceeds to the decryption. It must be physically located in the predefined geographical area (radius of choice from 1 to 2,500 km²) and validate the confidence criteria established by the issuer. In other words, this system, which is not connected to a server or a database, encrypts content even before it is broadcast online or stored on the servers of a mail. In the latter case, the AES256 and RSA 2048 or 4096 ciphers are robust enough against third-party decryption attempts.
Applications
EviCypher wants to be an untraceable solution that preserves the anonymity of its users. Intended at the base for critical state services (government, armies, embassies, etc.) and sensitive companies, the solution was finally declined in a “general public” version, following the recent cyber attacks on hospitals at the beginning of the year. These various intrusions have indeed convinced Freemindtronic to take advantage of the release of its EviCypher tool to raise awareness about the crucial need to protect data.
EviCypher reduces the surface area of exposure to attacks every place and applies to many situations:
- The solution counters espionage and identity theft attempts based on ransomware or phishing attacks aimed at obtaining confidential data (president attack). This is made possible by the authentication system based on multiple trust criteria;
- In the military field, EviCypher can establish, via its geolocation trust criterion, a secure communication between the command in France and the theatre of operations abroad;
- This technology, embedding an intelligent automated fleet manager, is also a way for CISOs to manage both multi-station and NFC antenna terminals serving as an interface.
To go further, Freemindtronic plans, in addition to creating an extension for applications in order to be more “volatile” vis-à-vis its ad hocapplication, to integrate the management of otherencryption systems. Among them, Open PGP, ECC keys, SSH and AWS. Users will also be able to select the type of encryption based on their usages. To date, the new extension for the Thunderbird solution has been developed to encrypt in AES256 mailboxes using the IMAP protocol.
Topicality
After recruiting an R&D director, Freemindtronic, which since its creation has relied on a staff of five technical profiles (cybersecurity engineers, electronics, artificial intelligence, embedded systems, forensic expert), is now starting a recruitment phase that confirms its rise in power.
The company has also received several awards thanks to EviCypher. In March 2021, she won the gold medal in category C at the Geneva International Exhibition of Inventions more info click here. Freemindtronic more recently won three awards last May at the last edition of the Global InfoSec Awards, in the categories “cryptographic security”, “secret management” and “Hardware Password Manager”.
[1] NFC technology is known to be used in contactless payments and transport cards.
[2] Category grouping computer, software, electronics, electricity or communication methods innovations.
- Learn more about the technology Physical barrier to regaining control of the data by EviCypher click here.