Pegasus: The Cost of Spying
Pegasus is a powerful spyware that has been used by several countries to spy on political figures, journalists, human rights activists or opponents. How does it work, who has been spied on, what are the consequences, and how much does it cost? Find out in this article.
Pegasus: The Cost of Spying with the Most Powerful Spyware in the World
Pegasus is a spyware developed by the Israeli company NSO Group. It allows to remotely monitor the activities of a mobile phone. According to an investigation conducted by a consortium of international media, several countries have used this software to spy on political figures, journalists, human rights activists or opponents.
The scandal of Pegasus has provoked a global outcry. It has raised many questions about the legality, the ethics and the consequences of this cyber-surveillance. How does Pegasus work? Who has been spied on by Pegasus? Who is responsible for the spying? What are the consequences of the spying? And most importantly, how much does Pegasus cost?
In this article, we will try to answer these questions in detail. We will use reliable and verified sources of information. We will also present some statistics and comparisons to give you an idea of the scale and the impact of Pegasus.
What is Pegasus?
Pegasus is a spyware, also called spy software. It allows to remotely monitor the activities of a mobile phone. It can access the messages, the calls, the contacts, the photos, the videos, the location, the microphone or the camera of the target phone. It can also activate or deactivate certain functions of the phone, such as Wi-Fi or Bluetooth.
Pegasus: a spyware that raises many questions
Pegasus is a powerful spyware that the NSO group designed. It can monitor and steal data and activities from mobile phones secretly. The NSO group is an Israeli company founded in 2010 by former members of Unit 8200; the Israeli military intelligence service. The company claims that its software aims to fight terrorism and organized crime; such as pedophiles or cartel leaders. It also claims that it only sells it to governments or authorized security agencies; with the approval of the Israeli Ministry of Defense. The countries that acquire these systems must respect their commitments stipulated in the license.
However, a consortium of international media outlets revealed that many countries have used Pegasus for other purposes. They have monitored various people, including politicians, journalists, human rights activists and political opponents. This raises many questions about the protection of privacy and human rights in the digital age. It also exposes the vulnerabilities and challenges of cybersecurity in a world where surveillance technologies are becoming more powerful and discreet.
Pegasus works by exploiting security flaws in the operating systems of phones, such as iOS or Android. It can infect a phone in two ways: either by sending a malicious link to the target phone, which must click on it to be infected; or by using a technique called “zero-click”, which allows to infect a phone without any interaction from the user.
Pegasus is a very sophisticated and discreet software. It can self-destruct or camouflage itself to avoid being detected. It can also adapt to security updates of operating systems to continue working. According to NSO Group, Pegasus is able to target more than 50,000 phone numbers in the world.
Unveiling Pegasus Attack Vectors: Stealth and Subterfuge in Cyber Espionage
In the Shadows of Cyber Espionage: Pegasus Strikes Unseen
In the realm of cyber espionage, Pegasus has mastered the art of covert infiltration, employing a spectrum of attack vectors designed to leave its targets unaware and defenseless. As a specialized journalist in the field of espionage, we delve into the clandestine world of Pegasus, shedding light on the methods it employs to breach digital fortresses.
Email: The Trojan Horse
Pegasus’s espionage campaign often commences with a seemingly innocuous email. The target receives a carefully crafted message, concealing a malicious payload. This deception operates with remarkable subtlety, bypassing traditional safeguards. Victims unknowingly execute the payload, granting Pegasus a foothold into their digital lives.
SMS Intrigue: Texts That Betray
SMS messages can become instruments of betrayal when wielded by Pegasus. Crafted to exploit vulnerabilities in messaging apps, these seemingly harmless texts harbor malicious intent. Clicking on a compromised message can be all it takes for Pegasus to silently infiltrate a device.
Web of Deceit: Navigating Vulnerabilities
Pegasus’s reach extends into the very fabric of the internet. Web browsers, portals to information and connectivity, can become gateways for intrusion. By exploiting unpatched browser vulnerabilities, Pegasus sidesteps user interaction, infiltrating systems silently.
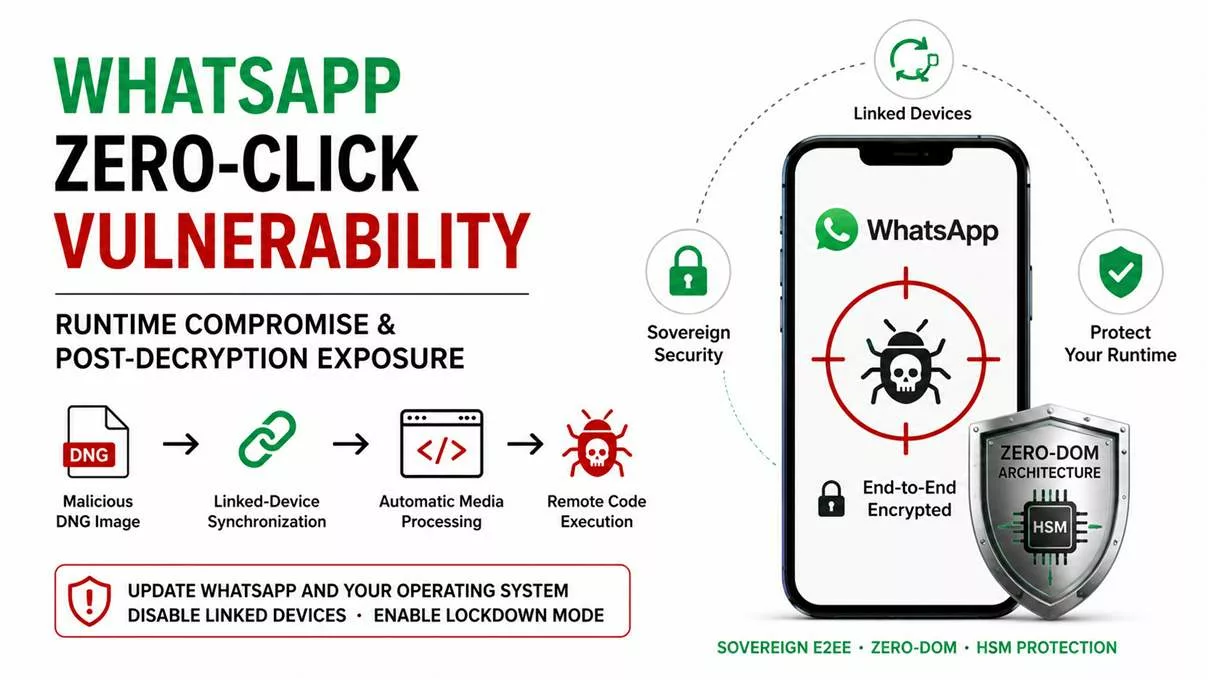
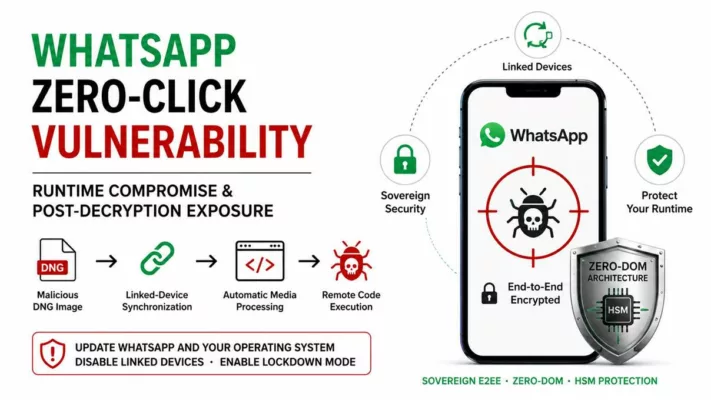
WhatsApp’s Vulnerable Connection
Even encrypted platforms like WhatsApp are not impervious to Pegasus’s advances. The spyware capitalizes on vulnerabilities in this widely used messaging app. A simple call on WhatsApp can translate into a gateway for Pegasus’s covert surveillance.
Zero-Click: A Stealthy Intrusion
The pinnacle of Pegasus’s subterfuge is the “Zero-Click” attack vector. Unlike other methods, “Zero-Click” requires no user interaction whatsoever. It preys upon deep-seated operating system vulnerabilities. Pegasus slips in unnoticed, operating in the shadows, and evading all user alerts.
The Stealth Within Pegasus: An Unseen Hand
Pegasus’s ability to infiltrate devices without leaving a trace raises profound concerns regarding detection and defense. Victims may remain oblivious to their compromised status, and traditional security measures struggle to counteract this stealthy foe.
Pegasus Continues to Threaten iPhone User Privacy and Security
In the ever-evolving landscape of digital security, the Pegasus spyware remains a significant threat to iPhone users’ privacy and security. Despite Apple’s rigorous efforts to enhance iOS safeguards, the sophisticated surveillance tool developed by the Israeli firm NSO Group has continually adapted, finding new ways to infiltrate the defenses of one of the world’s most popular smartphones.
Apple’s Proactive Measures Against Pegasus
Apple has been at the forefront of the battle against cyber threats, releasing timely security updates and patches aimed at thwarting Pegasus’s advanced techniques. The company’s commitment to user privacy has led to the development of new security features designed to protect sensitive information from unauthorized access. However, the dynamic nature of cyber threats, exemplified by Pegasus, poses an ongoing challenge to even the most secure platforms.
The Impact on iPhone Users
For iPhone users, the threat of Pegasus spyware is more than just a privacy concern; it’s a direct attack on their freedom of expression and the security of their personal data. The ability of Pegasus to covertly monitor conversations, access encrypted messages, and even activate cameras and microphones without consent has raised alarms worldwide. This level of surveillance capability not only endangers individual users but also threatens the integrity of global communications networks.
Recent Revelations in Jordan Amplify Global Pegasus Concerns
In 2024, shocking reports emerged, spotlighting Jordan’s use of Pegasus against journalists and activists. This development underscores the pervasive reach of NSO Group’s spyware. Allegedly, the Jordanian authorities targeted individuals crucial to civil society. These actions have stoked fears about privacy invasions and press freedom suppression. Amidst Israel-Jordan tensions, this move signals a worrying trend of using cyberweapons to stifle dissent. Consequently, global watchdogs are calling for stringent controls on spyware sales and usage. This incident not only highlights the urgent need for robust digital rights protections but also raises significant ethical questions about surveillance technologies’ global impact.
India’s Pegasus Scandal: A Deep Dive into Surveillance and Democracy
The year 2023 brought to light India’s alleged surveillance of journalists and opposition figures using Pegasus. This revelation has sparked a nationwide debate on privacy, press freedom, and democratic values. High-profile journalists and political dissenters reportedly fell victim to this covert tool, leading to widespread condemnation. Despite government denials and a lack of cooperation with Supreme Court probes, the issue remains unresolved. Such use of Pegasus not only threatens individual freedoms but also undermines the very fabric of democratic societies. As countries grapple with the dual use of surveillance technologies, the call for transparent, regulated, and ethical practices has never been louder. This situation serves as a crucial reminder of the delicate balance between national security and personal liberties.
How Pegasus spied on the Catalan independence movement and the Spanish government
Pegasus, a powerful spyware designed by the NSO Group, has the capability to clandestinely monitor and steal data and activities from mobile phones. A consortium of international media outlets exposed the fact that numerous countries have employed Pegasus to conduct surveillance on various individuals, including political figures, journalists, human rights activists, and political opponents.
In Spain, the Pegasus scandal unfolded, implicating over 60 individuals associated with the Catalan independence movement. According to a report from Citizen Lab, Pegasus was utilized to target these individuals between 2017 and 2020. In an alarming twist, the Spanish government itself accused Pegasus of spying on its own officials in 2021.
The Catalan independence movement under surveillance
The Catalan independence movement represents a political and social endeavor that aims to secure Catalonia’s independence from Spain. This movement gained significant momentum in 2017 when the Catalan government conducted an unauthorized referendum on self-determination. In response, the Spanish government took action by suspending Catalonia’s autonomy and apprehending several of its leaders.
Citizen Lab’s report revealed that Pegasus had specifically targeted more than 60 individuals associated with the Catalan independence movement from 2017 to 2020. This list includes notable figures such as three presidents of the Generalitat of Catalonia: Artur Mas, Quim Torra, and Pere Aragonès. These individuals have taken legal action, filing a complaint against Paz Esteban and the NSO Group. Paz Esteban serves as the director of CNI, Spain’s intelligence service.
Additional alleged victims encompass Members of the European Parliament, lawyers, journalists, and activists. For example, Carles Puigdemont, the former president of Catalonia who sought refuge in Belgium following the referendum, was also subjected to Pegasus surveillance. The list further includes Roger Torrent, the former speaker of the Catalan parliament, and Jordi Cañas, a pro-union Member of the European Parliament.
The Spanish government under attack
The situation escalated in significance when the Spanish government disclosed that Pegasus had also surveilled its own officials in 2021. The government attributed this to an “external attack” but refrained from identifying the perpetrators. Various media outlets hinted at the possibility of Moroccan involvement, occurring against the backdrop of a diplomatic standoff between the two nations.
Prime Minister Pedro Sánchez and Defense Minister Margarita Robles were among the primary targets. In February 2021, while on an official visit to Morocco, their mobile phones fell victim to Pegasus infections8. This compromise allowed the spyware access to their messages, calls, contacts, photos, videos, location, microphone, and camera.
Additionally, Foreign Minister Arancha González Laya and Interior Minister Fernando Grande-Marlaska faced Pegasus surveillance in May 2021. This intrusion occurred during their management of a migration crisis in Ceuta, a Spanish enclave in North Africa that witnessed a mass influx of Moroccan migrants.
The outcry of the victims
Those who have potentially or definitively fallen victim to Pegasus expressed their outrage and concerns surrounding this spying scandal. They vehemently decried it as a grave infringement upon their fundamental rights and vociferously demanded both explanations and accountability. Furthermore, they sought access to the findings of the judicial investigation and the data collected by the spyware.
For example, Quim Torra expressed feeling “violated” and “humiliated” by the intrusive spying. He squarely pointed fingers at the Spanish state and demanded an apology from Prime Minister Sánchez. Torra also declared his intent to pursue legal action against NSO Group and CNI.
Likewise, Pedro Sánchez conveyed his profound worry and anger regarding the spying. He committed to seeking clarifications from Morocco and Israel while simultaneously reinforcing his government’s cybersecurity measures.