Quantum Security in AES-256 CBC & PGP: Evaluating Resistance with Key Segmentation
As quantum computing rapidly evolves, AES-256 CBC encryption stands at the forefront of security discussions. In this post, we explore how AES-256 and its PGP variant remain resilient against quantum threats. Our analysis focuses on key segmentation, a cutting-edge approach in quantum data protection, and offers both theoretical and practical insights to safeguard sensitive information in a post-quantum world.
Stay informed with our posts dedicated to Technical News to track its evolution through our regularly updated topics.
Background: The Foundations of Quantum Security in AES-256
Understanding AES-256 in Classical Cryptography
AES (Advanced Encryption Standard), especially its 256-bit variant, provides robust protection for sensitive data. The robustness of AES-256 arises from the complexity of its encryption operations, which require a 256-bit key. This key length makes brute-force attacks nearly impossible on classical computers. Furthermore, the National Institute of Standards and Technology (NIST) has standardized AES-256, leading to its widespread global adoption across various applications, from securing communications to protecting databases.
Quantum Algorithms: A New Threat to Encryption Security
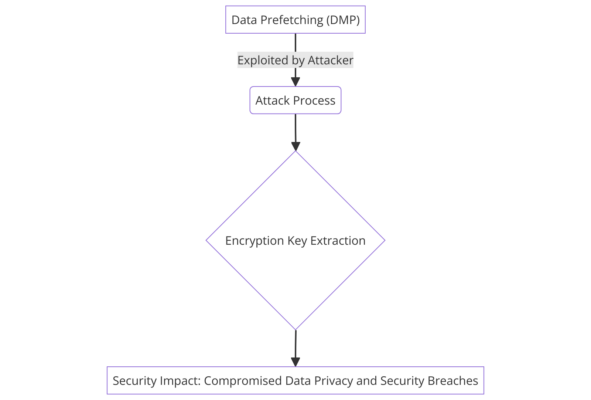
Quantum computing brings significant challenges to symmetric encryption systems such as AES-256 CBC. With the potential of quantum computers to exploit algorithms like Grover’s, the encryption community is actively preparing for these future risks. AES-256 CBC, while robust, faces a quantum computing landscape that demands further adaptation. Two quantum algorithms, in particular, pose significant risks:
-
- Shor’s Algorithm: This algorithm threatens asymmetric encryption systems like RSA by factoring integers in polynomial time, compromising systems reliant on the difficulty of this operation.
-
- Grover’s Algorithm: Grover’s Algorithm significantly impacts symmetric encryption systems by providing a quadratic speedup. For AES-256 CBC, it reduces the required operations from
 to
to  . While still theoretical, ongoing research into quantum cryptanalysis suggests that quantum collision attacks could pose additional risks to cryptographic hashing functions used alongside AES-256-based encryption. As such, integrating key segmentation not only mitigates these threats but adds an extra layer of defense against quantum-enabled adversaries.
. While still theoretical, ongoing research into quantum cryptanalysis suggests that quantum collision attacks could pose additional risks to cryptographic hashing functions used alongside AES-256-based encryption. As such, integrating key segmentation not only mitigates these threats but adds an extra layer of defense against quantum-enabled adversaries.
- Grover’s Algorithm: Grover’s Algorithm significantly impacts symmetric encryption systems by providing a quadratic speedup. For AES-256 CBC, it reduces the required operations from
The Impact of Quantum Attacks on AES-256 Encryption
Grover’s algorithm, a significant development in quantum computing, could reduce the security level of AES-256. Although the attack would still require substantial computational power, we must consider quantum-resilient methods to ensure AES-256 remains secure in the long term. As a result, key segmentation becomes critical in reinforcing AES-256 CBC encryption against these potential vulnerabilities.
Recent NIST Guidelines and Quantum-Resilient Encryption
As part of its ongoing efforts to strengthen encryption standards, the National Institute of Standards and Technology (NIST) has begun integrating quantum-resilient cryptographic algorithms into its guidelines. AES-256 CBC, while still secure against classical attacks, requires advanced mitigation strategies, like key segmentation, to address quantum threats. These updates highlight the importance of future-proofing encryption mechanisms against Grover’s algorithm and other quantum-enabled techniques.
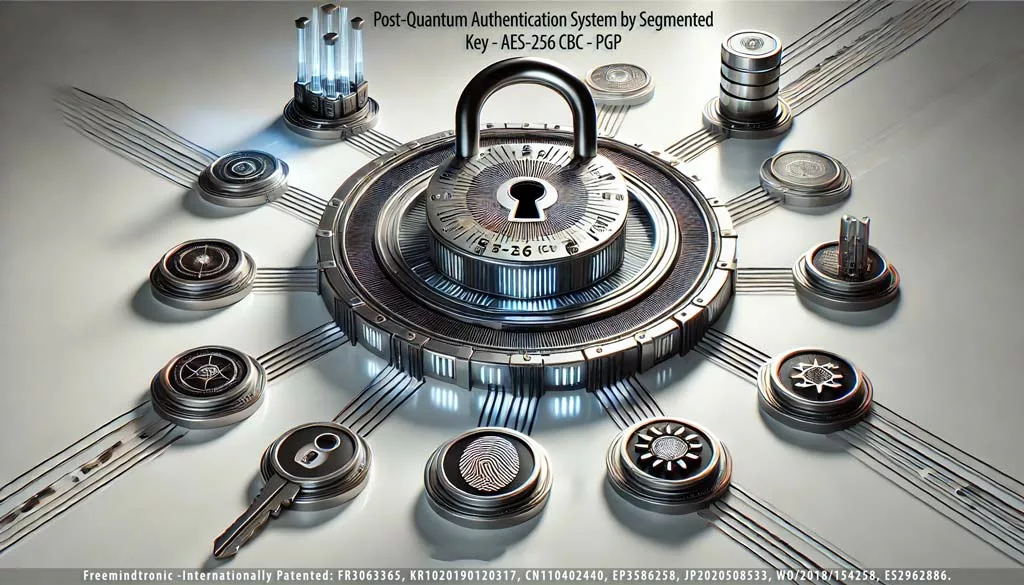
Why Key Segmentation is Crucial for Enhancing Encryption Security
Key segmentation has emerged as a groundbreaking solution to meet the growing demand for quantum-resistant encryption. By dividing the AES-256 CBC encryption key into multiple segments stored across distinct physical devices, unauthorized access becomes exponentially more difficult. This method ensures quantum resilience, making access to the entire key nearly impossible with today’s technology.
Recent NIST Updates on AES-256 and Post-Quantum Security
In light of quantum threats, the National Institute of Standards and Technology (NIST) has recently revisited its AES-256 encryption standards. While the core technical elements remain unchanged, NIST’s ongoing refinements emphasize the importance of post-quantum cryptography and quantum-resilient defenses like key segmentation(NIST). By aligning encryption practices with evolving standards, organizations can better prepare for the future of quantum data protection.
Advanced Quantum Security with Key Segmentation
Key Segmentation as Quantum Defense
“Key segmentation offers a highly effective defense against quantum threats. By leveraging multiple layers of security, this technique disperses the encryption key across various secure devices. Each segment, individually encrypted, becomes a critical barrier to unauthorized access. Even if a quantum-enabled adversary applies Grover’s algorithm, the complexity involved in retrieving all key segments ensures that quantum attacks remain theoretical for the foreseeable future. In the world of Quantum Data Protection, key segmentation stands out as a powerful tool for safeguarding data.”
Moreover, by integrating segmented keys with quantum-resilient algorithms, organizations can future-proof their data security strategies.
Quantum-Ready AES-256 CBC
“While many encryption systems brace for the impact of quantum computing, AES-256 CBC, fortified with key segmentation, remains one of the most quantum-resistant methods available. The encryption landscape is shifting rapidly, with technologies like quantum computers pushing the limits of traditional systems. By ensuring that encryption keys are not stored in a single location but are segmented across multiple devices, Quantum Security reaches new heights. This synergy between quantum-resilient algorithms, such as lattice-based cryptography, and key segmentation forms a multi-faceted defense against emerging quantum threats. As NIST finalizes post-quantum cryptographic standards, integrating these algorithms with segmented key systems will be critical in maintaining robust data protection.y ensuring that encryption keys are not stored in a single location, but are divided across multiple devices, Quantum Security reaches new heights. This advancement guarantees that AES-256 CBC will continue to protect critical data in the face of emerging quantum threats.
Thus, transitioning to a segmented key approach ensures that sensitive information is protected from even the most advanced quantum-based attacks.
Innovation: Detailed Analysis of Key Segmentation in AES-256
Theoretical Concept of Key Segmentation
Key segmentation involves distributing the encryption key across several segments, each stored on a distinct physical device, such as an NFC token or a secured mobile device. This approach leverages security through dispersion, ensuring that an attacker must gather and correctly assemble all segments to access the complete key.
This concept draws inspiration from principles like multiparty computation (MPC) and secret sharing schemes, such as Shamir’s secret sharing, which divides a secret into multiple parts that must be combined to reconstruct the original secret.
Advanced Implementation: Key Segment Types and Quantum Attack Resistance
Variety in Key Segmentation
Key segments can vary significantly depending on the implementation, adding further layers of security. The segments can be cumulative, ordered, or involve suppression by addition. For example:
- SSID Keys: Segments could be based on SSID keys identifying specific wireless networks, adding location-based authentication.
- Geo-Zone Segments: Key segments could be tied to specific geographic zones, becoming active only when the user is within a designated area.
- Barcode Segments: Segments could be encoded within a barcode, requiring physical access to scan and retrieve the segment.
- Password Segments: Traditional passwords can serve as key segments, enhancing security by requiring correct input alongside other segments.
- Telephone UID: A segment could derive from the unique identifier (UID) of a mobile phone, ensuring that the device itself becomes part of the authentication process.
These segments are integrated into products like PassCypher NFC HSM, SeedNFC HSM, and DataShielder NFC HSM. By adding trust criteria such as SSID, geo-zone, or UID, the system ensures that authentication is only possible when all trust conditions are met, even under potential quantum attack scenarios.
Encapsulation and Secure Storage of Key Segments
Variants of key segmentation further enhance security by encapsulating one or more criteria within encryption, while others are stored in different secure memories, protected by unique keys initially generated randomly. For instance:
- Encapsulation in Encryption: Some segments are securely encapsulated within the encryption process, accessible only during decryption.
- Distributed Secure Storage: Other segments might be stored in separate secure memories, each protected by a different cryptographic key, ensuring that even if one memory is compromised, the attacker would still need to access the others.
These implementations are particularly effective in quantum-resistant security products like PassCypher NFC HSM Lite and DataShielder PGP HSM.
Practical Implementation of Key Segmentation
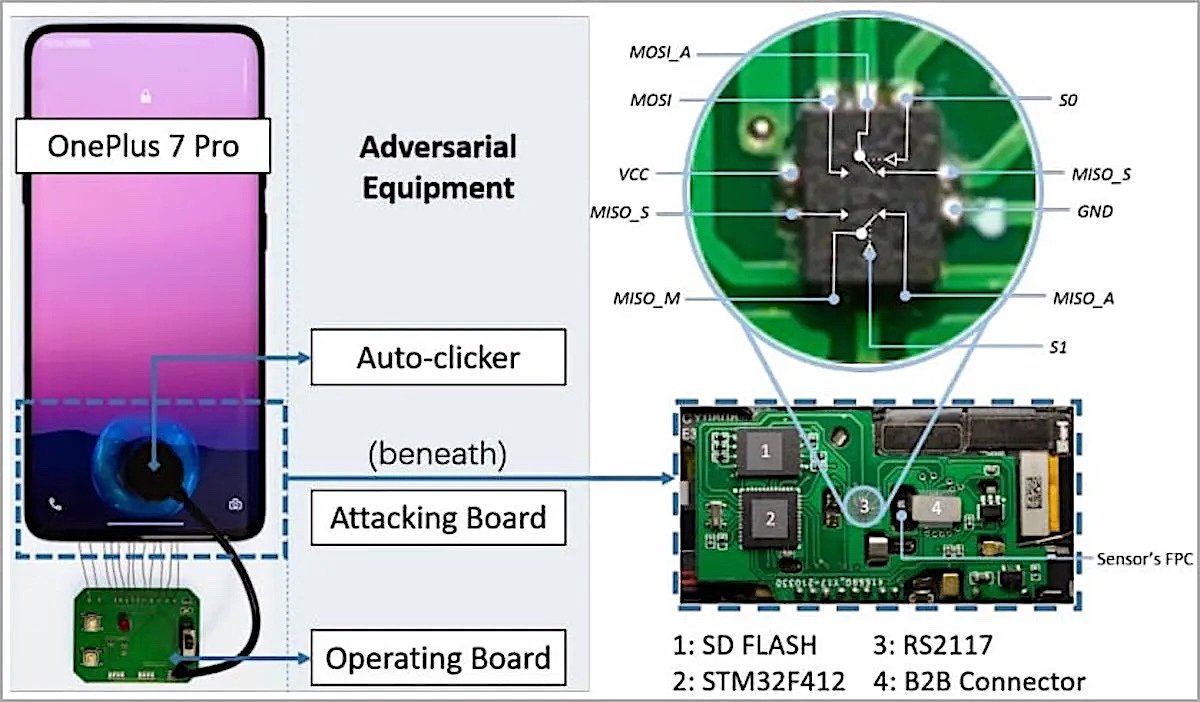
Consider a system that uses AES-256 encryption to secure sensitive data. The 256-bit key is divided into three segments:
- Segment 1: Stored on a primary mobile device, such as a smartphone.
- Segment 2: Stored on an NFC token, hidden in a secure location.
- Segment 3: Stored on another mobile device or secondary token, held by an authorized supervisor.
These segments are never transmitted in plaintext. Instead, they are combined only when needed for decrypting data. The primary mobile device retrieves the segments through near-field communication (NFC), assembles them in a predefined order, and then uses the complete key for decryption.
Best Practices for Implementing Key Segmentation
For organizations transitioning to quantum-resilient encryption, it is vital to establish best practices in the deployment of key segmentation. Regularly refreshing key segments, implementing geo-zoning and device-based segmentation, and using multiple layers of encryption per segment ensures greater protection against quantum threats. Additionally, ensuring strict access control and monitoring the integrity of devices storing these segments can prevent potential breaches. These practices form a robust security framework in the face of advancing quantum capabilities.
Enhancing AES-256 CBC Security with Key Segmentation: A Quantum-Resistant Approach
Key segmentation provides a powerful layer of security against quantum attacks. Even if a quantum adversary applies Grover’s algorithm to crack one segment, they only gain a fraction of the key. Recent research highlights that combining key segmentation with quantum-resilient algorithms ensures even greater protection. Segmentation forces attackers to reconstruct the entire key through multiple independent channels, making such attacks exponentially harder to execute.
Combining this system with rigorous access and device management makes it extremely difficult for an attacker to compromise. Regularly renewing key segments can prevent long-term reconstruction attempts, ensuring ongoing security.
Quantum Security Best Practices
As quantum technologies evolve, adopting best practices in Quantum Data Protection becomes essential. Regularly renewing key segments and maintaining strict access control protocols ensure that encryption remains robust against even the most sophisticated quantum attacks. Additionally, employing geo-zoning and device-based key segmentation adds further layers of complexity. These practices not only strengthen encryption but also create a more dynamic and responsive security infrastructure.”
By adopting these advanced security measures, organizations can protect their data well into the quantum era.
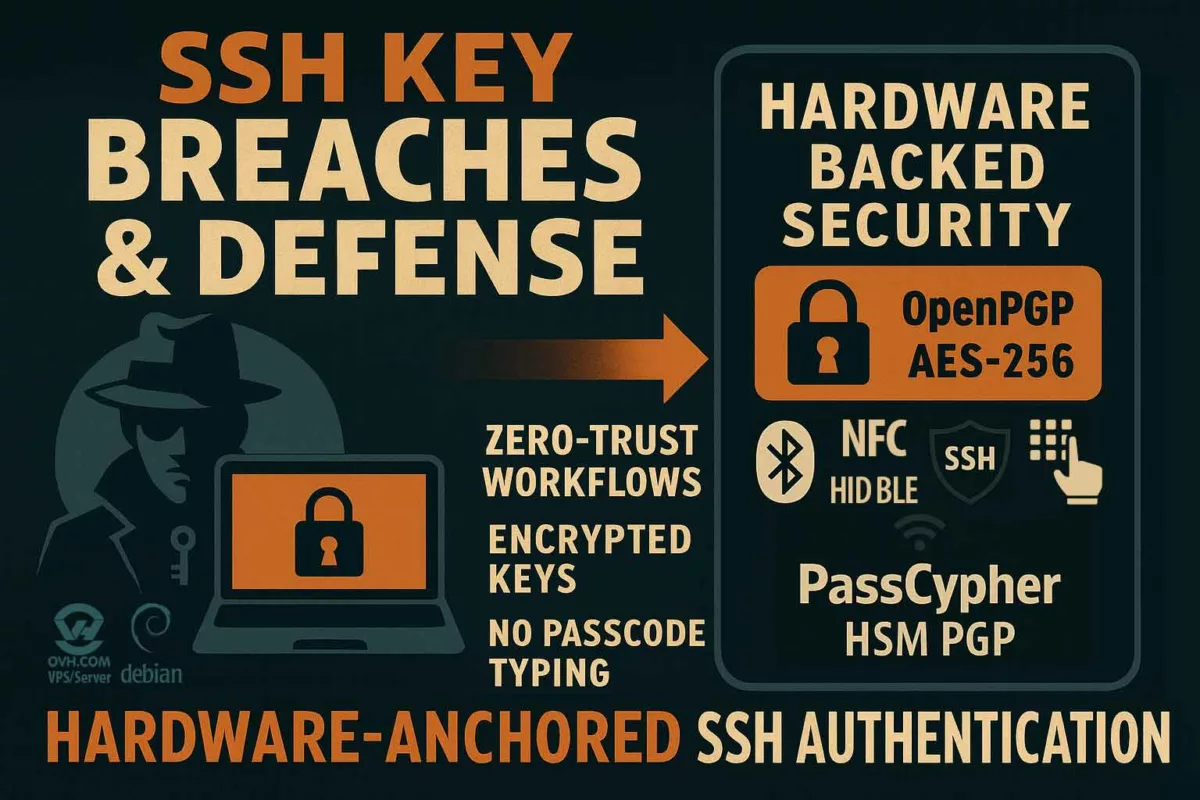
Technical Deep Dive with DataShielder NFC HSM and DataShielder HSM PGP
Implementing Key Segmentation in DataShielder Products
For those with a technical interest, key segmentation can be implemented in encryption hardware and software like DataShielder NFC HSM and DataShielder HSM PGP. These products offer robust security by securely storing and managing cryptographic keys. By integrating key segmentation, these systems can further enhance security, distributing encryption key segments across multiple DataShielder devices to ensure that no single device holds the entire key.
Integration Points with Existing Systems
Integrating key segmentation with existing encryption systems requires careful planning. In DataShielder products, segmentation occurs where keys are generated and stored. The software supports the retrieval and reassembly of key segments only when all segments are present. This approach ensures that even if a single device is compromised, the encryption key remains secure.
Protecting the Innovation: Patent for Key Segmentation
The innovation of key segmentation as a robust solution to quantum threats has been formally recognized and protected under a patent. Invented by Jacques Gascuel, this patent is exploited by Freemindtronic in various implementations, such as PassCypher NFC HSM, PassCypher HSM PGP, SeedNFC HSM, SeedNFC PGP, and EviKey NFC HSM. The patent has been granted in multiple jurisdictions, including the USA, Japan, South Korea, China, the European Unitary Patent, Spain, the United Kingdom, and Algeria. You can refer to the patent documentation for more details on this patented technology.
Comparing AES-256 CBC with Other Encryption Methods in the Face of Quantum Computing
Risk Modeling in Encryption
Without key segmentation, encryption methods like AES-256 rely on a “monolithic” security approach. In this scenario, the single encryption key serves as the main barrier to protection. If compromised, the entire system becomes vulnerable.
Key segmentation distributes the risk across multiple points. Risk modeling demonstrates that the chance of an attacker accessing all key segments and reconstructing them is exponentially lower. Attack vectors multiply and become interdependent, requiring significant computational power for quantum attacks and physical access to multiple secured devices.
Computational Complexity with Key Segmentation
A brute-force attack on AES-256 encryption without segmentation, using Grover’s algorithm, has a complexity of 21282^{128}. However, in a system with key segmentation, even if one segment is cracked, the attacker faces additional complexity. Each segment adds to the challenge, especially when combined with its correct integration into the complete key. The overall complexity of such an attack could meet or even exceed the original complexity, depending on the number of segments and the encryption scheme used for each segment.
Risk Mitigation Strategies for AES-256 CBC: Leveraging Key Segmentation
Redundancy in Storage Locations
To mitigate risks associated with key segmentation, implementing redundancy in storage locations is crucial. Storing multiple copies of each key segment in different secure locations ensures that the loss or compromise of one location does not endanger the entire key.
Backup Protocols
Effective backup protocols are essential for maintaining the integrity of key segments. Regularly backing up key segments and ensuring these backups are encrypted and stored securely can prevent data loss due to hardware failure or other unforeseen events.
Managing Segment Loss
In cases where a key segment device is lost or compromised, organizations must have protocols in place for quickly invalidating the compromised segment and generating a new one. This process should be seamless to avoid interruptions in operations while maintaining the security of the encryption key.
Application of Key Segmentation to AES-256 PGP Encryption
Overview of AES-256 PGP Security
AES-256 is also a crucial component in PGP (Pretty Good Privacy). PGP is a well-known encryption program that provides cryptographic privacy and authentication. It combines AES-256 encryption with public-key cryptography to secure files, emails, and other digital communications. In PGP, symmetric key encryption (AES-256) is typically used for data encryption, while asymmetric encryption secures the symmetric key itself.
Addressing Quantum Threats in PGP
PGP, like standard AES-256, faces significant challenges from quantum computing. Asymmetric algorithms traditionally used in PGP, such as RSA and DSA, are particularly vulnerable to Shor’s algorithm. Shor’s algorithm can break these in polynomial time. Although more resistant, the symmetric AES-256 encryption within PGP still faces threats from Grover’s algorithm, potentially reducing the effective security level to that of a 128-bit key.
Enhancing AES-256 CBC PGP Security with Key Segmentation
Key segmentation can significantly enhance PGP’s resistance to quantum attacks. In this context, key segmentation involves dividing the symmetric key used for AES-256 encryption into multiple segments, as described earlier. These segments are then distributed across various secure devices. Additionally, transitioning to quantum-resistant algorithms or applying similar segmentation to the asymmetric keys used in PGP could further bolster security.
Practical Implementation of Key Segmentation in PGP Systems
PGP users can implement key segmentation by following these steps:
- Segmenting the Symmetric Key: The AES-256 key used in PGP encryption is divided into multiple segments, which are then stored on different secure devices.
- Securing the Asymmetric Key: Transitioning to quantum-resistant algorithms for the asymmetric keys used in PGP or segmenting these keys similarly.
- Ensuring Compatibility: Ensuring that the key segmentation process is compatible with existing PGP workflows and software. This might require updates or patches to PGP software to maintain security.
Quantum-Resilient Algorithms and Key Segmentation Synergy
As quantum computing progresses, experts are developing quantum-resilient algorithms designed to withstand quantum cryptographic attacks. When these algorithms are combined with key segmentation, they offer a synergistic defense. This approach splits the encryption key across multiple independent devices, ensuring that even if one algorithmic defense falters, the segmented structure adds a nearly insurmountable barrier for attackers. Such integration will be essential for quantum data protection in the coming years.
Strengthening AES-256 CBC PGP Security with Key Segmentation
Integrating key segmentation allows AES-256 PGP to maintain a higher level of security against quantum threats. Even if a quantum computer attempts to exploit Grover’s algorithm, the attacker would still need to reconstruct the key segments. This requirement adds a significant barrier to unauthorized decryption. Therefore, key segmentation provides an effective defense mechanism.
Case Study: Applying Key Segmentation to Encryption in a Sensitive Environment
Consider a large financial institution using AES-256 encryption to protect its customer databases. The institution decides to implement key segmentation to guard against future quantum threats. The encryption key is divided into segments stored on devices held by different departments, such as IT, security, and management. To access a sensitive database, a user must retrieve each segment using a primary mobile device. The key is then reconstructed and used to decrypt the data.
Results and Benefits of Implementing Key Segmentation
Penetration testing simulations show that the data remains secure even if one segment is stolen. The requirement to retrieve all segments in a specific order prevents any successful attack. Additionally, the use of varied segment types, such as SSID keys, geo-zone restrictions, and UID-based segments, adds layers of complexity that make unauthorized access nearly impossible. Cost-benefit analysis reveals that while key segmentation involves initial implementation and training costs, the security and data protection gains are substantial. Therefore, key segmentation proves to be a highly effective security measure.
Resistance to Quantum Attacks: Key Segmentation Without a Trusted Third Party
Key segmentation can resist quantum attacks without the need for a trusted third party. The segmented key components are distributed across multiple secure devices, each functioning independently. This decentralization ensures that even with the advent of quantum technology, an attacker would face a monumental challenge in reconstructing the key without access to all segments. The absence of a single trusted authority also reduces the risk of central points of failure, making the system more robust against both internal and external threats.
Future Perspectives: Developing Post-Quantum Cryptography (PQC)
As quantum computing advances, developing post-quantum cryptography (PQC) becomes increasingly critical. NIST leads the efforts to establish new cryptographic standards resistant to quantum attacks. These emerging algorithms could complement key segmentation strategies, offering an additional layer of protection. For example, integrating quantum-resistant algorithms with segmented keys could further enhance security, providing a comprehensive defense against future threats.
Comparing Key Segmentation with Other Quantum-Resistant Strategies
While key segmentation offers a robust solution, it is essential to compare it with other quantum-resistant strategies to provide a broader understanding of the landscape. Alternatives such as lattice-based cryptography, hash-based signatures, and multivariate quadratic equations present different approaches to quantum resistance.
- Lattice-Based Cryptography: This method relies on the hardness of lattice problems, which are believed to be resistant to quantum attacks. However, unlike key segmentation, which disperses the risk, lattice-based methods focus on computational complexity.
- Hash-Based Signatures: These signatures offer security based on the collision resistance of cryptographic hash functions. They provide a different approach from key segmentation but can be combined to enhance overall security.
- Multivariate Quadratic Equations: These equations are used in cryptographic systems considered resistant to quantum attacks. When combined with key segmentation, they could provide an even more robust defense.
Technical Deep Dive: DataShielder NFC HSM and DataShielder HSM PGP
For users with a technical interest, implementing key segmentation in encryption hardware and software, such as DataShielder NFC HSM and DataShielder HSM PGP, offers a practical and secure approach to quantum-resistant cryptography. These products can store and manage cryptographic keys securely, ensuring that each segment is protected independently.
In practice, key segmentation within these systems distributes segments across multiple devices, ensuring that no single device holds the entire key. Integrating with existing systems requires careful consideration of segment retrieval, reassembly, and compatibility with existing encryption workflows. By securing each segment with independent cryptographic keys and implementing rigorous access controls, DataShielder products significantly reduce the risk of key compromise.
Conclusion: Enhancing AES-256 Quantum Security with Key Segmentation
This scientific evaluation shows that AES-256 encryption, including its use in PGP, is theoretically vulnerable to Grover’s attacks. However, key segmentation provides an innovative and robust solution. By dividing the key into segments stored on secured devices, this additional barrier significantly complicates any attempts to compromise the system, whether from external attackers or internal threats.
Future Perspectives on Quantum Security
Key segmentation is likely to become a standard in high-security environments, especially as quantum computing advances. Researchers must continue to explore segmentation mechanisms, improve their management, and integrate them into broader cybersecurity systems. Future standards, such as those being developed by NIST for post-quantum cryptography, could incorporate these concepts to create even more robust solutions. Therefore, the ongoing development of quantum-resistant security measures remains crucial.