Chrome V8 confusió RCE: aquesta edició exposa l’impacte global i les mesures immediates per reduir risc — amb guia pràctica, bones pràctiques Zero-DOM i referències oficials.
Search Results for: PassCypher
Chrome v8 confusion RCE: This edition addresses impacts and guidance relevant to major English-speaking markets — United States, United Kingdom, Canada, Australia and India — with region-specific guidance, compliance pointers and references.
Chrome V8 zero-day CVE-2025-10585 — Votre navigateur n’était pas vulnérable. Vous étiez déjà espionné !
Technology Readiness Levels (TRL) provide a structured framework to measure the maturity of innovations, from basic research to mission-proven systems. This Chronicle offers a sovereign perspective on how the TRL 1–9 scale shapes strategic adoption in defense, critical infrastructure, and digital security. ⧉ What We Didn’t Cover This Chronicle focused on TRL as a strategic […]
Vulnerabilitat Passkeys: Una vulnerabilitat crítica, revelada a la DEF CON 33, demostra que les passkeys sincronitzades poden ser objecte de phishing en temps real. De fet, Allthenticate va provar que una sol·licitud d’autenticació falsificable pot segrestar una sessió WebAuthn en viu.
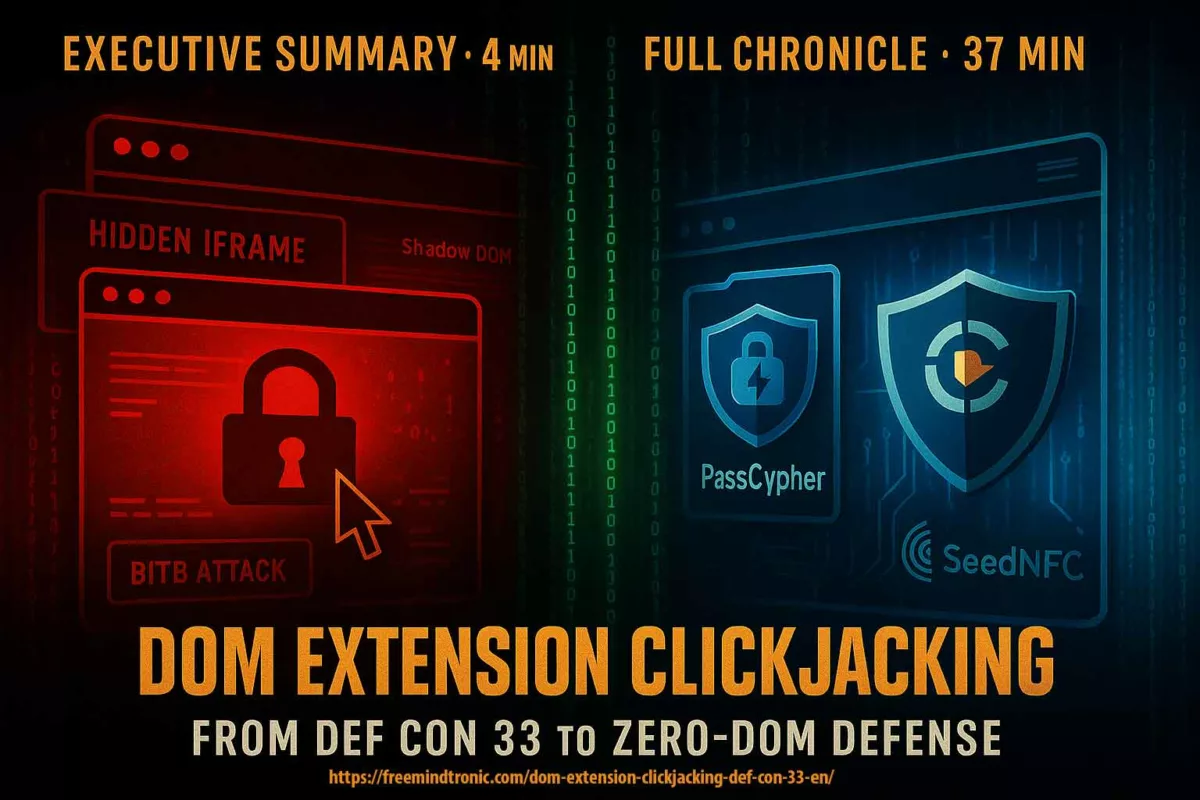
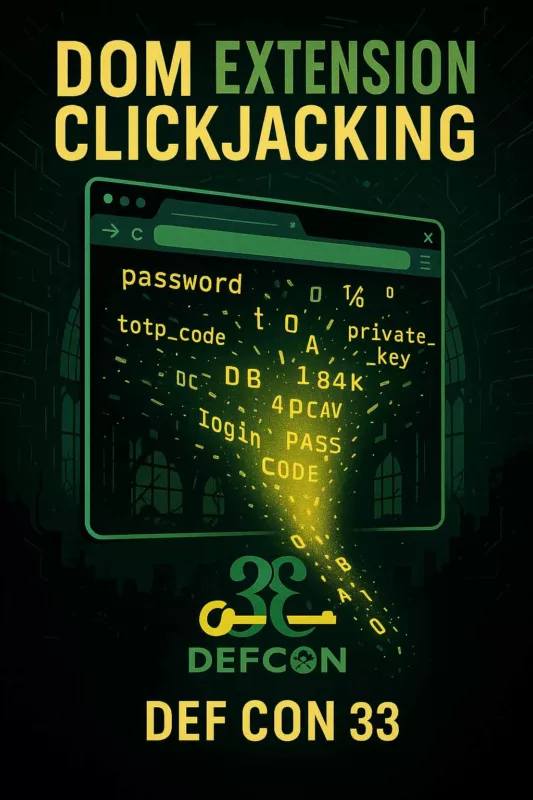
DOM extension clickjacking — a technical chronicle of DEF CON 33 demonstrations, their impact, and Zero-DOM countermeasures. See the Executive Summary below for a 4-minute overview. ☰ Quick navigation Executive Summary History of Clickjacking (2002–2025) What is DOM-Based Extension Clickjacking? Vulnerable Password Managers Technologies of Correction Used Correction Technologies — Technical & Doctrinal Analysis Systemic […]
DOM extension clickjacking — el clickjacking d’extensions basat en DOM, mitjançant iframes invisibles, manipulacions del Shadow DOM i overlays BITB — posa en risc els gestors de contrasenyes; vegeu §Passkeys phishables. Aquesta crònica resumeix les demostracions de DEF CON 33 (DOM-based extension clickjacking i passkeys phishables), el seu impacte i les contramesures Zero-DOM (PassCypher, SeedNFC, […]
Clickjacking d’extensions DOM : DEF CON 33 révèle une faille critique et les contre-mesures Zero-DOM