Recent Industry and Government Updates
-
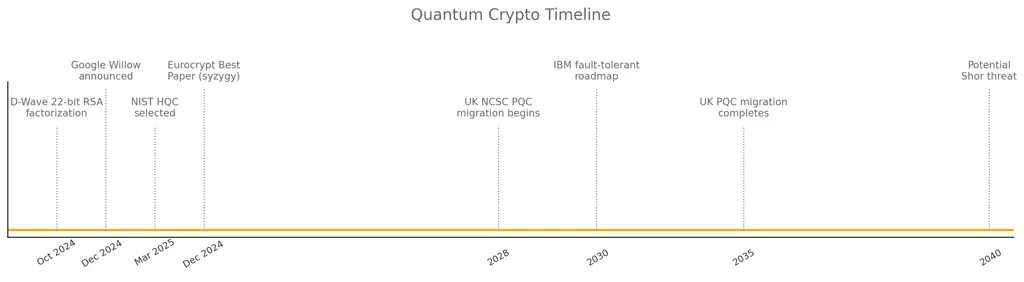
Google’s Willow Processor Clarifies Cryptographic Limits
In December 2024, Google Quantum AI unveiled its 105‑qubit Willow chip—“Meet Willow, our state‑of‑the‑art quantum chip” (Google Quantum AI Blog)—and confirmed it cannot break modern cryptography, as millions more qubits would be required to threaten RSA‑2048 or AES‑256.
-
UK NCSC’s 2035 Roadmap for PQC Migration
In March 2025, the UK’s National Cyber Security Centre published official PQC migration timelines—phased upgrades from 2028 through 2035 to avoid “store now, decrypt later” attacks (NCSC guidance)—and the Financial Times highlighted the need to start by 2028 (FT).
Preparing for the Future: Combining Post-Quantum and Current Cryptography
While PQC algorithms are in development and will likely become the gold standard of encryption in the coming decades, AES-256 CBC combined with segmented key encryption provides an immediate, powerful solution that bridges the gap between current threats and future quantum capabilities. By implementing such strategies now, organizations can stay ahead of the curve, ensuring their data remains secure both today and in the quantum computing era.
The Future of Post‑Quantum Cryptography: A Major French Breakthrough
Post‑quantum cryptography is evolving at breakneck speed, thanks in large part to pioneering work from French experts. Notably, Hugues Randriambololona of ANSSI recently unveiled a bold new method—syzygy analysis—to detect hidden weaknesses in the McEliece cryptosystem, one of the leading candidates for securing tomorrow’s quantum‑era communications. Although McEliece has long been trusted for its resistance to even powerful post‑quantum computers, Randriambololona’s approach uses sophisticated mathematical relations (syzygies) to expose key‑presence patterns without decrypting messages.
Awarded Best Paper at Eurocrypt 2025, this discovery demonstrates France’s agility in post‑quantum innovation, where standards can shift overnight. Looking ahead, technology diversification combined with agile research will be essential over the next 5–10 years. With researchers like Randriambololona leading the way, France cements its role as a global leader—delivering advanced security solutions for the coming quantum age.
Microsoft Majorana 1: Topological Qubit Breakthrough
On February 19, 2025, Microsoft officially unveiled Majorana 1, the world’s first quantum processor powered by topological qubits. This breakthrough chip is built on a new class of materials called topoconductors, designed to host Majorana zero modes (MZMs)—a key component in achieving error-resistant quantum computation. The company claims that Majorana 1 could ultimately scale to support up to one million qubits on a single chip.
Although the system is still experimental, the announcement highlights significant progress toward building a fault-tolerant quantum computer. Microsoft’s roadmap suggests that topological qubits could overcome the instability and noise challenges facing today’s quantum systems.
🔗 Read the full announcement on Microsoft Azure Blog
Actions to Take Now: Strengthen Your Defenses
To stay ahead of quantum threats, organizations should take the following steps:
- Migrate RSA systems to RSA-3072 or adopt post-quantum cryptography (PQC) solutions.
- Monitor developments in AES-256 encryption. As quantum computing progresses, AES-256 remains secure, especially with solutions like Freemindtronic’s segmented key encryption.
- Adopt segmented key encryption to enhance security. This method prevents attackers from gaining full access to encrypted data, even with quantum tools.
Predictive Models & Scientific References
Using models like Moore’s Law for Qubits, which predicts exponential growth in quantum computational power, gives credibility to these predictions. For instance, models suggest that breaking RSA-2048 requires 20 million stable qubits—a capability that is still decades away. Nature and Science journals provide further academic validation. A 2023 article in Nature on qubit scalability supports claims that advancements necessary to compromise encryption standards like AES-256 and RSA-2048 remain distant.
Microsoft Majorana 1: Topological Qubit Breakthrough
On February 19, 2025, Microsoft officially unveiled Majorana 1, the world’s first quantum processor powered by topological qubits. This breakthrough chip is built on a new class of materials called topoconductors, designed to host Majorana zero modes (MZMs)—a key component in achieving error-resistant quantum computation. The company claims that Majorana 1 could ultimately scale to support up to one million qubits on a single chip.
Although the system is still experimental, the announcement highlights significant progress toward building a fault-tolerant quantum computer. Microsoft’s roadmap suggests that topological qubits could overcome the instability and noise challenges facing today’s quantum systems.
🔗 Read the full announcement on Microsoft Azure Blog
The Quantum Threat to RSA Encryption: An Updated Perspective
While quantum computing has made significant strides, it’s essential to distinguish between current progress and future threats. The RSA algorithm, which relies on the difficulty of factoring large prime numbers, is particularly vulnerable to Shor’s algorithm, a quantum algorithm designed to solve the integer factorization problem.
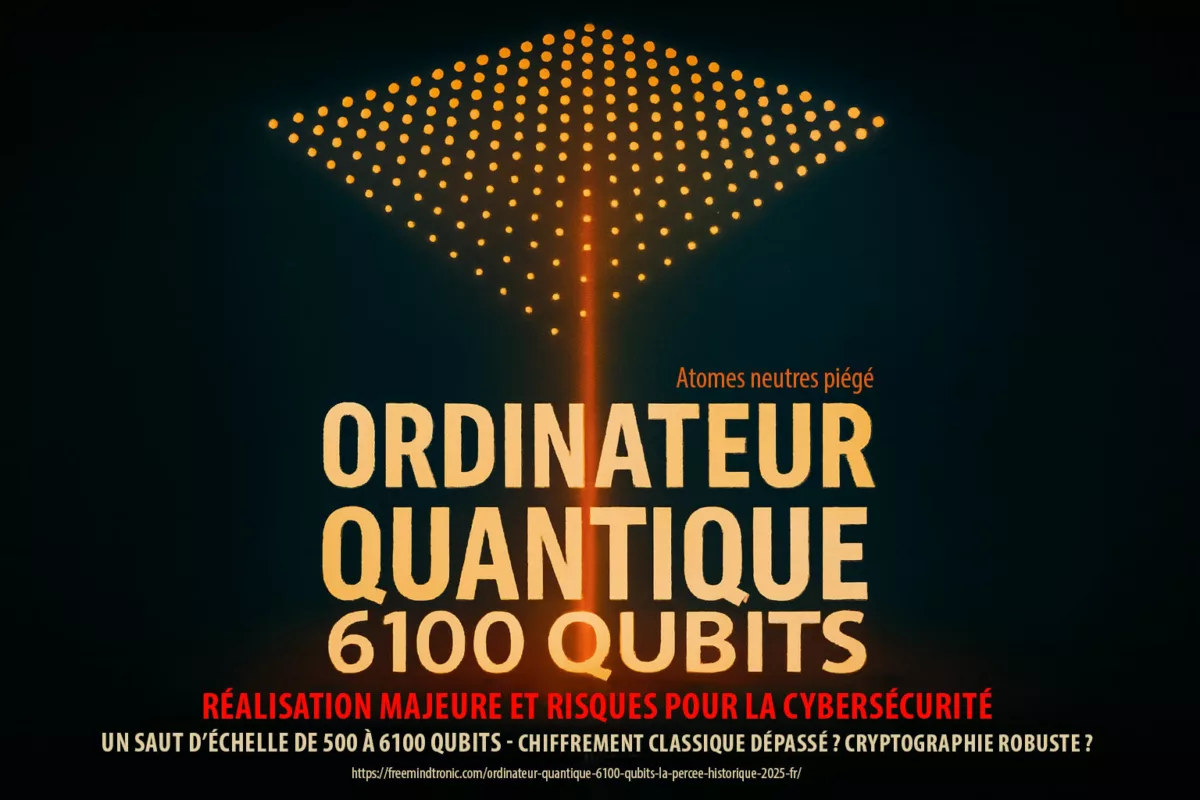
In October 2024, Chinese researchers using D-Wave’s quantum computer successfully factored a 22-bit RSA key. This result drew attention, but it remains far from threatening RSA-2048. Breaking RSA-2048 would require a quantum computer with approximately 20 million stable qubits operating for around eight hours. Current systems, such as D-Wave’s 5,000-qubit machine, are still far from this level of capability.
Experts estimate that factoring an RSA-2048 key would require a quantum computer equipped with approximately 20 million stable qubits:
( N = 2^{20} ).
These qubits would need to operate continuously for around eight hours. Current systems, like D-Wave’s 5,000-qubit machine, are far from this level of capability. As a result, cracking RSA-2048 remains a theoretical possibility, but it’s still decades away from practical realization.
For more details on this breakthrough, you can review the official research report published by Wang Chao and colleagues here: Chinese Research Announcement.
Even as quantum advancements accelerate, experts estimate that RSA-4096 could resist quantum attacks for over 40 years. Transitioning to RSA-3072 now provides a more resilient alternative in preparation for future quantum capabilities.
However, it is crucial to note that ongoing research continues to assess the vulnerability of RSA to quantum advancements. Indeed, while precise timelines remain uncertain, the theoretical threat posed by Shor’s algorithm remains a long-term concern for the security of RSA-based systems. That’s why migrating to more quantum-resistant alternatives, such as RSA-3072 or post-quantum cryptography algorithms, is an increasingly recommended approach to anticipate future quantum computing threats.
Research on Quantum Vulnerabilities (Shor’s Algorithm and RSA)
Scientific Consensus on RSA’s Vulnerabilities
Peter Shor’s algorithm, which efficiently solves the integer factorization problem underlying RSA, represents the core threat to RSA encryption. Current studies, such as those by the Chinese Academy of Sciences and Google Quantum AI, confirm that implementing Shor’s algorithm on RSA-2048 requires 20 million stable qubits, along with sustained coherence for about eight hours. A 2022 study in Physical Review Letters also estimates that current quantum systems like IBM’s Eagle (127 qubits) and Osprey (433 qubits) are far from this capability.You can explore the original study here.
The Gidney and Ekerå Findings: Factoring RSA-2048
In 2021, Craig Gidney and Martin Ekerå conducted a groundbreaking study titled “How to Factor 2048-bit RSA Integers in 8 Hours Using 20 Million Noisy Qubits”. Their research outlines the quantum resources needed to break RSA-2048 encryption. They found that around 20 million noisy qubits, along with several hours of sustained quantum coherence, would be required to perform the task.
While Microsoft Research estimated that only 4,000 universal qubits are needed to theoretically break RSA-2048, Gidney and Ekerå’s model emphasizes a practical approach. They suggest that 20 million qubits are necessary for this computation within an 8-hour timeframe. This shows the gap between theory and real-world applications.
These results provide an important timeline for when quantum computing threats could materialize. They also highlight the urgent need to develop quantum-safe cryptography, as encryption systems like RSA-2048 may become vulnerable to future advancements in quantum technology.
Logical Qubits vs. Physical Qubits: A Key Distinction
It’s important to differentiate between logical and physical qubits when evaluating quantum computers’ potential to break encryption systems. Logical qubits are the idealized qubits used in models of algorithms like Shor’s. In practice, physical qubits must simulate each logical qubit, compensating for noise and errors, which significantly increases the number of qubits required.
For example, studies estimate that around 20 million physical qubits would be necessary to break RSA-2048 in eight hours. Machines like IBM’s Eagle (127 qubits) are far from this scale, underscoring why RSA-2048 remains secure for the foreseeable future.
The Role of Segmented Key Encryption in Quantum-Safe Security
As quantum systems develop, innovations like segmented key encryption will play a critical role in protecting sensitive data. Freemindtronic’s internationally patented segmented key encryption system divides encryption keys into multiple parts, each independently encrypted. This technique provides additional layers of security, making it more resilient against both classical and quantum attacks.
By splitting a 4096-bit key into smaller segments, a quantum computer would need to coordinate across significantly more qubits to decrypt each section. This adds complexity and makes future decryption attempts—quantum or classical—nearly impossible.
Universal Qubits vs. Adiabatic Qubits: Cryptographic Capabilities
It’s essential to differentiate between universal qubits, used in general-purpose quantum computers like those developed by IBM and Google, and adiabatic qubits, which are found in D-Wave’s systems designed for optimization problems.
While universal qubits can run advanced cryptographic algorithms like Shor’s algorithm, adiabatic qubits cannot. D-Wave’s machines, even with 5,000 qubits, are not capable of breaking encryption methods such as RSA-2048 or AES-256.
The recent D-Wave breakthrough in factoring a 22-bit RSA key was achieved using quantum annealing, which has limited cryptographic applications. When discussing the potential for breaking encryption, the focus should remain on universal quantum computers, which are necessary to run cryptographic algorithms like Shor’s.
You can explore more about Microsoft’s research here.
Adiabatic Qubits: Solving Optimization Problems
It’s important to note that D-Wave’s systems are not general-purpose quantum computers. Instead, they are quantum annealers, designed specifically to solve optimization problems. Quantum annealers cannot run cryptographic algorithms like Shor’s algorithm. Even with 5,000 qubits, D-Wave’s machines are incapable of breaking encryption keys like RSA-2048 or AES-256. This limitation is due to their design, which focuses on optimization tasks rather than cryptographic challenges.
The recent breakthroughs involving D-Wave, such as the factorization of a 22-bit RSA key, were achieved using quantum annealing. However, quantum annealing has a narrow application scope. These advancements are unrelated to the type of quantum computers needed for cryptographic attacks, such as factoring RSA-2048 with Shor’s algorithm. When discussing the potential for breaking encryption, the focus should remain on universal quantum computers—such as those developed by IBM and Google—that are capable of running Shor’s algorithm. You can learn more about D-Wave’s quantum optimization focus here.
What Are Quantum Annealers?
Quantum annealers, like those developed by D-Wave, are specialized quantum computing systems designed for solving optimization problems. These machines work by finding the lowest energy state, or the optimal solution, in a complex problem. While quantum annealers leverage aspects of quantum mechanics, they are not universal quantum computers. They cannot execute general-purpose algorithms like Shor’s algorithm, which is essential for cryptographic tasks such as factoring large numbers to break encryption keys like RSA-2048.
Quantum annealers excel in specific applications like optimization and sampling, but they are not designed to tackle cryptographic challenges. This is why, even though D-Wave’s machines have achieved notable results in their field, they do not pose the same level of threat to encryption that universal quantum computers do.
Implications for Quantum Computing Threats
The distinction between universal and adiabatic qubits is critical for assessing real-world quantum computing threats. While both qubit types push the field of quantum computing forward, only universal qubits can realistically pose a threat to cryptographic systems. For instance, Google Quantum AI achieved a milestone in quantum supremacy, demonstrating the increasing potential of universal qubits. However, they remain far from breaking today’s encryption standards. You can read more about Google’s achievement in quantum supremacy here.
IBM’s Quantum Roadmap: The Future of Universal Qubits
Similarly, IBM’s Quantum Roadmap predicts breakthroughs in fault-tolerant quantum computing by 2030. This progress will further enhance the potential of universal qubits to disrupt cryptographic systems. As universal qubits advance, the need for quantum-safe cryptography becomes increasingly urgent. IBM’s roadmap can be reviewed here.
Looking Ahead: The Evolution of Quantum Cryptographic Capabilities
As quantum computing evolves, it’s essential to understand the differences between universal qubits and adiabatic qubits in cryptography. Universal qubits, developed by Microsoft, Google, and IBM, have the potential to run advanced quantum algorithms like Shor’s algorithm, which could theoretically break encryption methods such as RSA-2048. In contrast, adiabatic qubits, used in D-Wave’s systems, are better suited for solving specific optimization problems rather than breaking encryption algorithms like RSA-2048.
Therefore, announcements from companies like Microsoft and D-Wave should not be directly compared in terms of cryptographic capabilities. Each company’s quantum advancements address different computational challenges.
The Need for Segmented Key Encryption
To mitigate the risks posed by quantum computing threats, innovations like segmented key encryption will be crucial. Jacques Gascuel’s internationally patented segmented key encryption system provides extra layers of security by splitting encryption keys into multiple parts. This method makes it significantly more difficult for quantum computers, even those with enhanced capabilities, to decrypt sensitive information. This system is designed to address both classical and quantum attacks, offering robust protection against evolving threats.
Preparing for the Future: Responding to Quantum Threats to Encryption
As quantum systems continue to develop, adopting quantum-safe cryptography and integrating advanced solutions like segmented key encryption will be essential. Even though universal qubits are still far from breaking modern encryption algorithms, the rapid evolution of quantum technologies means that organizations must prepare now. By doing so, they ensure their encryption strategies are resilient against both current and future threats posed by quantum computing threats.
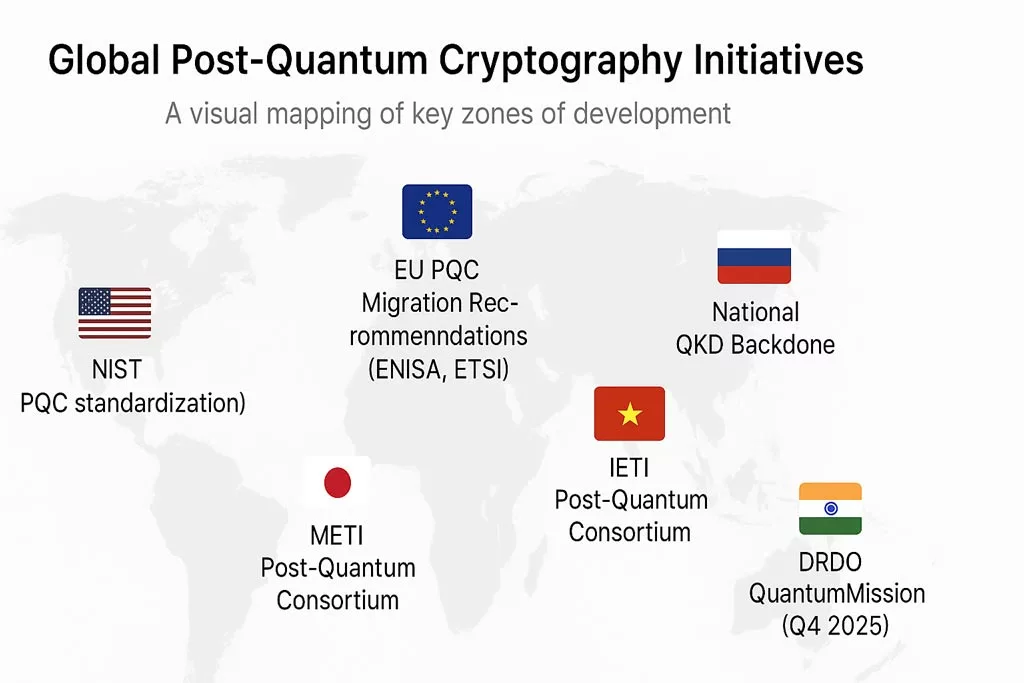
ANSSI’s Guidance on Post-Quantum Migration for Critical Sectors
While no joint statement by the CNIL and ANSSI was issued on May 6, 2025, the ANSSI’s follow-up position paper emphasizes the urgent need for early preparation for quantum-safe cryptography, especially in critical sectors like healthcare and digital identity. This aligns with its official migration roadmap, recommending phased adoption well before 2028 to mitigate the “store now, decrypt later” threat.
🔗 ANSSI’s official views on post-quantum cryptography transition
ISO/IEC 23894: Toward Global Certification of PQC Systems
In February 2025, the ISO/IEC JTC 1/SC 27 committee initiated work on ISO/IEC 23894, a future standard for certifying post-quantum cryptographic systems. This framework will define interoperability, auditability, and resilience benchmarks for PQC implementations.
Freemindtronic actively monitors this development to ensure its segmented key encryption modules meet future certification requirements. This proactive alignment reinforces trust and regulatory readiness across sectors.
Quantum Threats to Encryption in PKI Migration Strategy
Public Key Infrastructure (PKI) underpins digital trust—TLS, S/MIME, code signing, and identity verification. Yet, most PKI systems rely on RSA or ECC, both vulnerable to quantum attacks.
Migrating Certificate Authorities to PQC
To mitigate quantum threats, certificate authorities must adopt post-quantum cryptography (PQC) standards like HQC and ML-KEM. Freemindtronic’s offline HSM modules support PQC-ready key generation and segmented key storage, enabling sovereign PKI migration without cloud dependencies.
AES-256 Resilience Against Quantum Threats to Encryption
AES-256 remains resilient even when factoring Grover’s algorithm, as breaking it would still require:
[
N = 2^{256} rightarrow N = 2^{128}
]
operations—an unachievable number for current or near-future quantum systems. Moreover, Freemindtronic’s DataShielder solutions ((DataShielder NFC HSM Lite, Master, ‘Auh’, M-Auth and HSM PGP) integrate segmented key encryption, adding layers of complexity and further enhancing AES-256’s quantum resilience.
However, it is important to emphasize that the scientific community continues to study the resistance of AES-256 to quantum algorithms. Although the estimated time required to break AES-256 with a powerful quantum computer remains prohibitive, research actively explores potential vulnerabilities. Therefore, combining AES-256 with innovative techniques like segmented key encryption, as offered by Freemindtronic with its DataShielder solutions, provides a crucial additional layer of security to strengthen protection against future quantum computing threats.
Current Research and Theses
Recent Theses & Academic Research
Theses and academic papers from institutions such as MIT, Stanford, and ETH Zurich often provide deep insights into post-quantum cryptography and quantum resilience. Specifically, the work of Peter Shor on Shor’s algorithm underpins much of the concern around RSA’s vulnerability to quantum computing. Mentioning Waterloo University’s Quantum-Safe Cryptography Group can also substantiate your argument on AES-256’s continued resilience when combined with techniques like segmented key encryption.
Research Supporting AES-256’s Resilience
AES-256’s Resilience in Current Research: The strength of AES-256 against Grover’s algorithm can be further supported by recent research published in Physical Review Letters and IEEE. These studies emphasize that even if quantum computers reduce the complexity of breaking AES-256 to 2^128 operations, this still remains infeasible for current quantum machines. Citing such studies will validate your claims regarding the security of AES-256 for the next 30 to 40 years, especially when using additional safeguards like segmented key encryption.
Estimating the Time to Crack AES-256 with Quantum Computers
Though AES-256 is secure for the foreseeable future, estimating the time it would take quantum computers to crack it offers valuable insights. Experts predict that a quantum system would need 20 million stable qubits to effectively execute Grover’s algorithm. Even with a reduction in security to AES-128 levels, quantum computers would still need to perform:
[
N = 2^{128}
]
operations. This remains computationally infeasible and poses significant challenges for quantum systems.
Currently, machines like D-Wave’s 5,000-qubit computer fall short of the qubit count required to compromise AES-256 encryption. Moreover, these qubits would need to maintain stability over extended periods to complete the necessary operations, further complicating such an attack. Consequently, AES-256 is expected to remain secure for at least the next 30 to 40 years, even with advancements in quantum computing.
Organizations should begin preparing for these future quantum threats by adopting solutions like Freemindtronic’s DataShielder, which utilizes segmented key encryption to add additional layers of protection. These segmented keys provide enhanced security, ensuring that sensitive data remains secure and future-proof against the looming quantum computing threats.
Advanced Techniques to Combat Quantum Computing Threats
To combat the emerging quantum threats, Freemindtronic has developed a patented segmented key encryption system, protected under patents in the USA, China, Europe, Spain, the UK, Japan, South Korea, and Algeria. This technique divides encryption keys into multiple segments, each of which is independently encrypted. To decrypt the data, an attacker would need to obtain and decrypt all segments of the key. Even with current quantum computers, achieving this is impossible.
For example, if you segment a 4096-bit key into four 1024-bit sections, a quantum computer would need to coordinate across significantly more qubits, thereby complicating the decryption process. This method effectively future-proofs encryption systems against quantum advancements and significantly strengthens the security of AES-256 CBC encryption.
Quantum Computing Threats: What’s Next for RSA and AES?
Shor’s Algorithm Timeline for RSA-2048
In October 2024, Chinese researchers using D-Wave’s quantum computer successfully factored a 22-bit RSA key showcases the potential of quantum computing. However, cracking RSA-2048 requires exponential advancements in quantum capabilities, far beyond today’s systems. Experts estimate that breaking RSA-2048 could take at least 30 years, while RSA-4096 may resist attacks for over 40 years.
To safeguard encryption during this period, NIST recommends transitioning to RSA-3072, which offers better quantum resistance than RSA-2048. Additionally, adopting post-quantum cryptography (PQC) solutions, especially for critical infrastructures, will ensure systems remain resilient as quantum technologies advance. For AES-256, it’s estimated that 295 million qubits would be required to crack it, reaffirming its continued security. With innovations like segmented key encryption, AES-256 will likely remain highly resistant to quantum computing for decades.
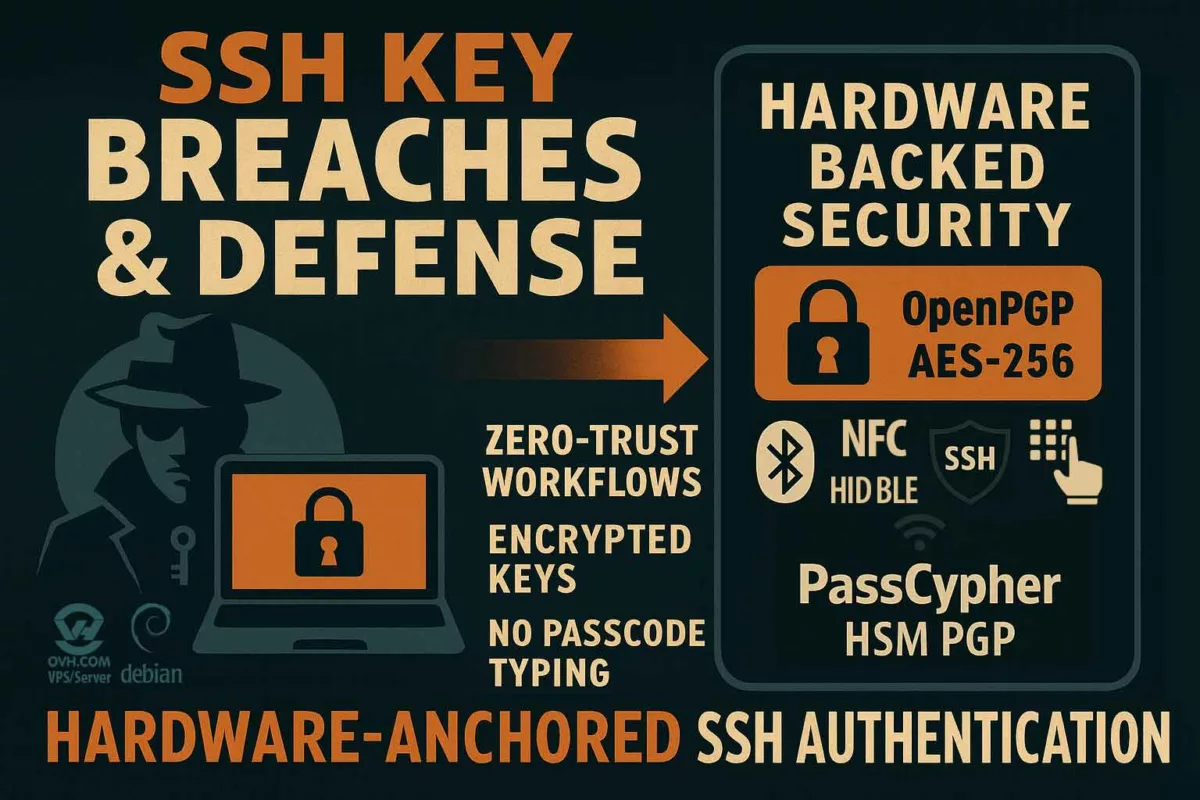
Freemindtronic Solutions for Enhanced Security
Freemindtronic provides cutting-edge tools to strengthen defenses against both classical and quantum threats. These solutions leverage AES-256 CBC with segmented keys, offering an extra layer of protection against quantum brute-force attacks.
Key solutions include:
- DataShielder NFC HSM Lite: Implements AES-256 with segmented keys, resistant to quantum and classical brute-force attacks.
- DataShielder NFC HSM Master: Provides secure key exchange and uses AES-256 CBC encryption.
- PassCypher NFC HSM Lite: A robust encryption solution that integrates AES-256 and segmented keys for email and file security.
- PassCypher NFC HSM Master: Offers additional security for file communications and authentication, using AES-256 encryption.
- DataShielder HSM Auth: Strengthens authentication through secure key exchange.
- DataShielder HSM M-Auth: Ensures secure key creation and exchange, combining traditional and quantum-resistant methods.
- PassCypher HSM PGP: Protects email and file communications with strong encryption, ensuring security against phishing and MITM attacks.
- PassCypher HSM PGP Free: A free version offering PGP encryption for secure communication.
- SeedNFC HSM: Ensures secure cryptocurrency wallet management with AES-256 encryption, protecting wallets against quantum threats.
- Keepser NFC HSM: Provides a hardware-based solution for secure password and key management, integrating AES-256 encryption.
The Future of Post-Quantum Cryptography
As quantum computing evolves, organizations must prepare for future encryption challenges. While post-quantum cryptography (PQC) solutions are emerging, systems like AES-256 with segmented key encryption will remain secure for the foreseeable future.
Actions to Strengthen Defenses
Organizations should take the following steps to stay ahead of quantum threats:
- Migrate RSA systems to RSA-3072 or adopt PQC solutions.
- Monitor AES-256 developments, as it remains secure, especially with solutions like segmented key encryption.
- Adopt segmented key encryption to enhance security. This method prevents attackers from gaining full access to encrypted data, even with quantum tools.
The Environmental Cost of Quantum Security
While quantum computing promises breakthroughs in encryption and computational power, its environmental impact remains a growing concern. The energy requirements to sustain millions of stable qubits—often under extreme cryogenic conditions—are immense. Operating a fault-tolerant quantum system capable of executing Shor’s algorithm for practical RSA-2048 decryption would demand enormous physical infrastructure and constant cooling near absolute zero.
This high energy footprint raises a critical question: even if quantum decryption becomes technically feasible, would it be sustainable at scale? In contrast, offline encryption solutions like Freemindtronic’s DataShielder, which require no servers, power-hungry data centers, or network connections, offer a low-energy, environmentally resilient alternative—immune to centralized infrastructure vulnerabilities and ecological limitations alike.
🌱 Energy Efficiency: Offline Encryption vs Quantum Infrastructure
Operating a fault-tolerant quantum computer requires cryogenic cooling near absolute zero, energy-intensive error correction, and massive infrastructure. A single quantum decryption session could consume megawatts of power.
In contrast, Freemindtronic’s SeedNFC and DataShielder modules operate fully offline, with near-zero energy consumption. They require no servers, no cloud, and no persistent connectivity—making them ideal for deployment in low-resource environments or critical infrastructure with strict energy budgets.
This ecological advantage complements their cryptographic resilience, offering a future-proof solution that’s both secure and sustainable.
Act Now to Counter Quantum Computing Threats
Quantum computing presents future risks to encryption standards like RSA-2048 and AES-256 CBC, but current advancements are far from threatening widely used systems. Organizations can counter quantum computing threats today by migrating to post-quantum cryptography and adopting segmented key encryption.
Freemindtronic’s patented solutions, such as DataShielder NFC HSM and PassCypher HSM PGP, ensure encryption systems are future-proof against the evolving quantum threat.