Executive Summary
In the evolving landscape of hybrid warfare, reputation cyberattacks have emerged as a powerful asymmetric tool, targeting perception rather than systems. These operations exploit cognitive vectors—such as false narratives, controlled leaks, and media amplification—to destabilize trust in technologies, companies, or institutions. Unlike conventional cyberattacks, their purpose is not to penetrate networks, but to erode public confidence and strategic credibility. This Chronicle exposes the anatomy, intent, and implications of such attacks, offering sovereign countermeasures grounded in cryptographic attestation and narrative control.
Estimated reading time: 16 minutes
Complexity level: Strategic / Expert
Language specificity: Sovereign lexicon – High concept density
Accessibility: Screen reader optimized – all semantic anchors in place Navigation
In Cyberculture ↑ Correlate this Chronicle with other sovereign threat analyses in the same editorial rubric.
- Executive Summary
- Strategic Definition
- Typology of Reputation Attacks
- Event-Driven Triggers
- Threat Actor Mapping
- Geopolitical Embedding
- Sovereign Countermeasures
- Strategic Case Illustrations
- Intermediate & Legacy Cases
- Common Features & Strategic Objectives
- Strategic Outlook
- Narrative Warfare Lexicon
- Beyond This Chronicle
Strategic Navigation Index
Key insights include:
- Reputation attacks prioritize psychological and narrative impact over system access
- Controlled leaks and unverifiable claims simulate vulnerability without intrusion
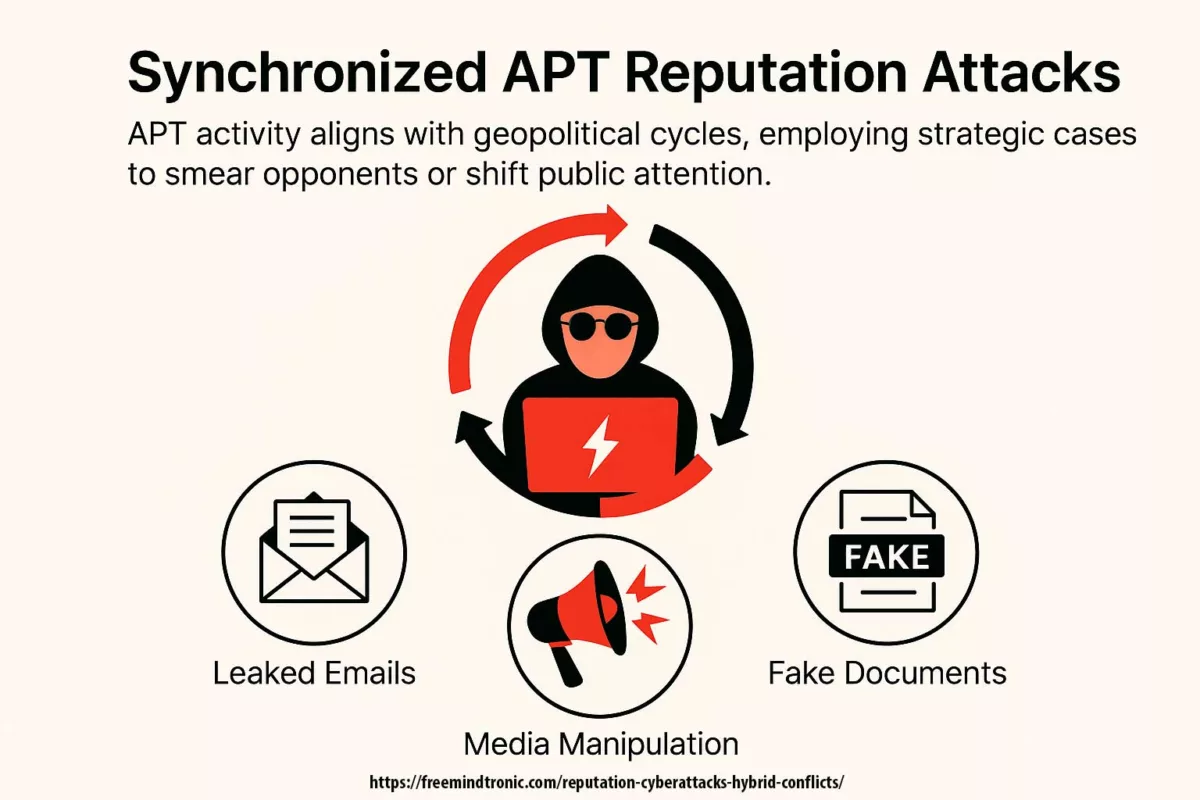
- APT actors increasingly combine narrative warfare with geopolitical timing
- Sovereign countermeasures must address both runtime trust and narrative control
- Legal attribution, hybrid doctrines, and military exercises recognize the strategic threat
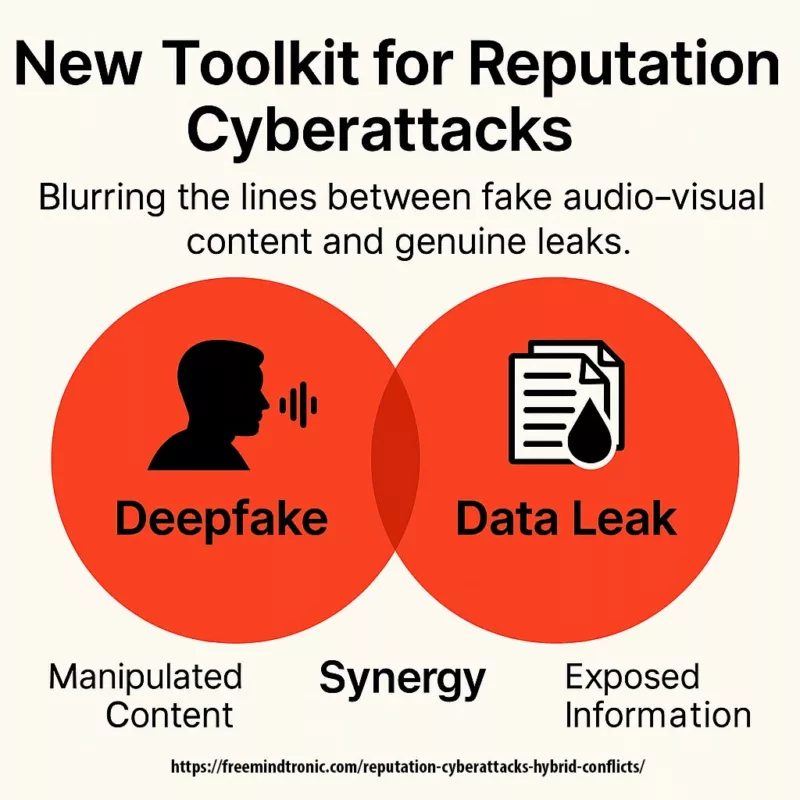
- IA-generated content and deepfake amplification heighten the reputational asymmetry
About the Author – Jacques Gascuel, inventor of internationally patented encryption technologies and founder of Freemindtronic Andorra, is a pioneer in sovereign cybersecurity. In this Cyberculture Chronicle, he deciphers the role of reputation cyberattacks in hybrid warfare and outlines a sovereign resilience framework based on NFC HSMs, narrative control, and runtime trust architecture.
Strategic Definition
Reputation cyberattacks are deliberate operations that undermine public trust in a targeted entity—governmental, industrial, or infrastructural—without necessitating technical penetration. Unlike classical cyberattacks, these actions do not seek to encrypt, extract, or manipulate data systems directly. Instead, they deploy orchestrated influence tactics to suggest compromise, provoke doubt, and corrode strategic credibility.
Key vectors include unverifiable claims of intrusion, dissemination of out-of-context or outdated data, and AI-generated content posing as evidence. These attacks are particularly insidious because they remain plausible without being technically demonstrable. Their targets are not systems but perceptions—clients, partners, regulators, and the broader strategic narrative.
Reputation cyberattacks weaponize doubt and narrative ambiguity. Their objective is not to compromise infrastructure but to simulate weakness, discredit governance, and manipulate perception within strategic timeframes.
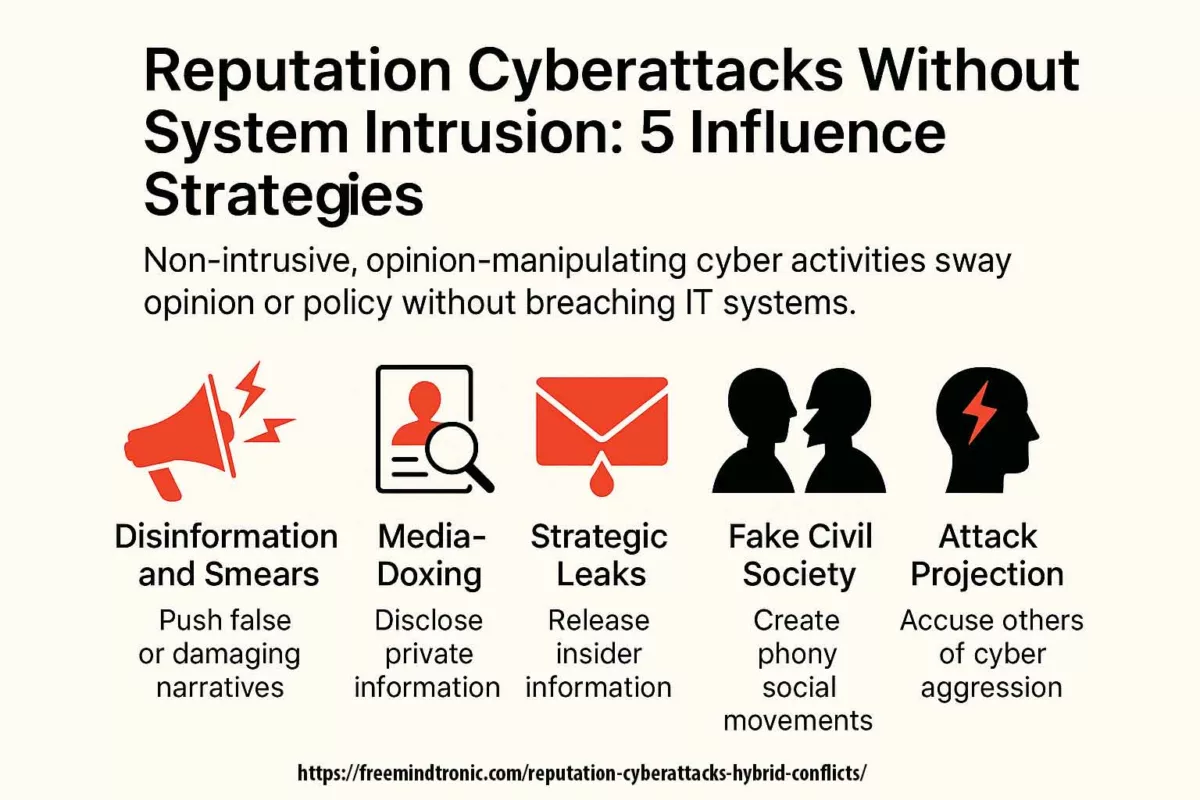
Typology of Reputation Attacks
Reputation cyberattacks operate through carefully structured vectors designed to affect perception without direct intrusion. Their effectiveness stems from plausible ambiguity, combined with cognitive overload. Below is a strategic typology of the most commonly observed mechanisms used in such campaigns.
| Type of Attack | Method | Reputation Objective |
|---|---|---|
| Controlled Leak | Authentic or manipulated data exfiltration | Undermine trust in data integrity or governance |
| Narrative of Compromise | Unverifiable intrusion claim | Simulate vulnerability or technical failure |
| Amplified Messaging | Telegram, forums, rogue media | Pressure decision-makers via public reaction |
| False or Outdated Leaks | Repurposed legacy data as recent | Manipulate interpretation and chronology |
| Brand Cloning / Solution Usurpation | Fake products, clones, apps | Confuse trust signals and damage legitimacy |
Reputation attacks deploy asymmetric cognitive tactics that distort technical signals to generate public discredit. Their sophistication lies in the lack of verifiability and the strategic timing of narrative releases.
Event-Driven Triggers
Reputation cyberattacks rarely occur randomly. They are most often synchronized with sensitive diplomatic, commercial, or regulatory events, maximizing their narrative and psychological effect. These timings allow threat actors to amplify tension, delegitimize negotiations, or destabilize political outcomes with minimum technical effort.
The following correlations have been repeatedly observed across high-impact campaigns:
| Trigger Type | Typical Context | Observed Examples |
|---|---|---|
| Diplomatic Events | G7, NATO, BRICS, UNSC debates | Jean-Noël Barrot’s G7 breach via spyware |
| Contract Finalization | Strategic defense or tech exports | Naval Group leak during Indonesian negotiations |
| Critical CVE Disclosure | Zero-day or CVSS 9+ vulnerabilities | Chrome CVE-2025-6554 exploited alongside eSIM JavaCard leaks |
| Political Transitions | Election cycles, leadership change | GhostNet during 2009 leadership reshuffles in Asia |
| Telecom Infrastructure Breach | U.S. regulatory hearings on 5G security | Salt Typhoon breach of U.S. telecom infrastructure |
| Military Retaliation | India–Pakistan border escalation | APT36 campaign post-Pahalgam attack |
– Surge in Telegram disinformation threads one week before BRICS 2025 summit
– Anonymous claims targeting SM-DP+ infrastructures prior to Kigen certification review
– Attribution disclosures by 🇨🇿 Czechia and 🇬🇧 UK against APT31 and GRU respectively, correlating with vote censure periods
– Military-grade leaks repurposed via deepfake narratives hours before defense debates at the EU Parliament
Threat Actor Mapping
Several Advanced Persistent Threat (APT) groups have developed and deployed techniques specifically tailored to reputation disruption. These actors often operate under, or in coordination with, state objectives—using narrative projection as a form of geopolitical leverage. Freemindtronic has documented multiple such groups across past campaigns involving mobile identity, supply chain intrusion, and staged perception attacks.
| APT Group | Origin | Strategic Focus | Regalian Link |
|---|---|---|---|
| APT28 / Fancy Bear | Russia | Media influence, strategic sabotage | GRU |
| APT29 / Cozy Bear | Russia | Diplomatic espionage, discrediting campaigns | SVR |
| APT41 / Double Dragon | China | eSIM abuse, supply chain injection | MSS |
| Lazarus / APT38 | North Korea | Crypto theft, industrial denigration | RGB |
| APT36 / Transparent T. | Pakistan | Military perception ops, Android surveillance | ISI |
| OceanLotus / APT32 | Vietnam | Telecom narrative control, political espionage | Ministry of Public Security |
Weak Signals:
- Surge in Telegram threads 72h prior to geopolitical summits
- Anonymous code disclosures targeting certified infrastructure
- OSINT forums hinting at state-level leaks without attribution
Timeline of Geopolitical Triggers and Corresponding Leaks
This sovereign timeline reveals how state-sponsored leak campaigns align tactically with geopolitical milestones, transforming passive narrative exposure into calibrated instruments of reputational destabilization.
| Date | Geopolitical Trigger | Leak Activity / APT Attribution |
|---|---|---|
| 11–12 June 2025 | NATO Summit | Massive credential dump via Ghostwriter |
| 18 July 2025 | U.S.–China Trade Talks | Strategic policy leak via Mustang Panda |
| 5 September 2025 | EU–Ukraine Association Agreement | Media smear leaks via Fancy Bear |
| 2 October 2025 | U.S. Sanctions on Russia | Source code exposure via Sandworm |
| 16 November 2025 | China–India Border Standoff | Fake news spike via RedEcho |
| 8 December 2025 | G7 Foreign Ministers’ Meeting | Diplomatic email leak via APT31 |
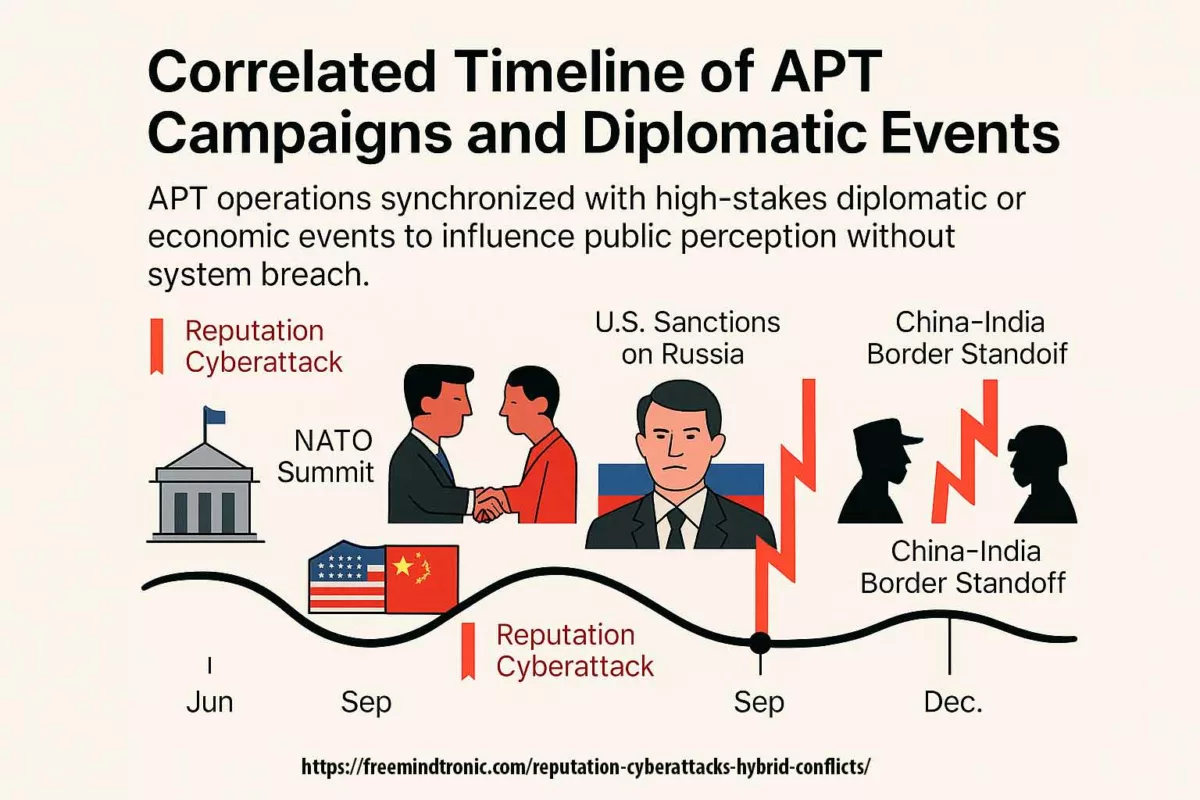
These APTs combine stealth, timing, and plausible deniability to weaponize trust decay. Their toolkit includes mobile clone propagation, certificate revocation simulation, and adversarial AI-driven content generation.
Medium Signals:
- Reactivation of domains previously linked to APT41 and APT36
- Spam waves targeting sectors previously affected (e.g., eSIM, military)
- Cross-platform narrative amplification combining Telegram, deepfakes, and dark web leaks
Geopolitical Embedding
Reputation cyberattacks are rarely isolated actions. They are often embedded within broader geopolitical manoeuvers, aligned with strategic objectives of national influence, dissuasion, or economic disruption. Below are detailed illustrations of how states integrate reputation-based cyber operations within their doctrine of influence.
🇷🇺 Russia – Narrative Sabotage and Attribution Management
APT28 and APT29 operate as complementary arms of Russian strategic disinformation. APT28 performs media amplification and tactical leaks, while APT29 infiltrates strategic diplomatic channels. Both benefit from GRU and SVR coordination, with plausible denial and a focus on exploiting trust asymmetries within European security frameworks.
🇨🇳 China – Espionage Hybridization and Runtime Subversion
APT41 is a paradigm of China’s fusion between state-sponsored espionage and monetized cybercrime. Their use of eSIM runtime abuse and compromised SM-DP+ provisioning chains illustrates a shift from direct intrusion to sovereignty degradation via runtime narrative manipulation. The Ministry of State Security provides structural protection and strategic targeting objectives.
🇰🇵 North Korea – Financial Subversion and Mobile Identity Hijacking
Lazarus Group (APT38) leverages breaches to undermine trust in certified systems. By targeting crypto wallets, blockchain nodes, and mobile identity providers, they transform technical compromise into economic destabilization narratives. These attacks often coincide with international sanctions debates or military exercises, and are directed by the Reconnaissance General Bureau (RGB).
🇵🇰 Pakistan – Military Psychological Pressure on India
APT36 deploys persistent mobile malware and SIM/eSIM spoofing against Indian military actors. These attacks are not solely technical; they aim to discredit Indian defense systems and pressure procurement diplomacy. The Inter-Services Intelligence (ISI) integrates these cyber tactics within regional destabilization agendas.
🇻🇳 Vietnam – Political Control via Telecom Targeting
OceanLotus (APT32) focuses on dissidents, journalists, and telecom infrastructure across ASEAN. Their aim is to dilute external perceptions of Vietnamese governance through discreet leaks and selective disclosure of surveillance capabilities. The Ministry of Public Security provides operational coverage and mission framing.
All of these actors embed their reputation attacks within state-approved strategic cycles. Cyberwarfare thus becomes an extension of diplomacy by other means—targeting trust, not terrain.
Sovereign Countermeasures
Defending against reputation cyberattacks requires more than perimeter security. Sovereign actors must combine cryptographic integrity enforcement, dynamic runtime assurance, and narrative discipline. Reputation attacks flourish in ambiguity—effective defense mechanisms must therefore be verifiable, attestable, and visible to the strategic environment.
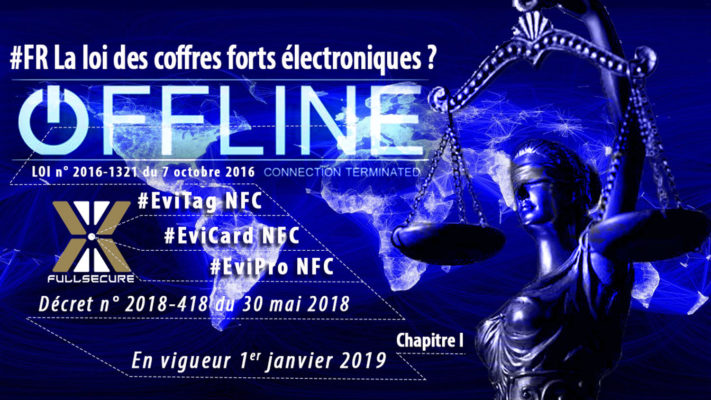
Freemindtronic’s PassCypher NFC HSM / HSM PGP and DataShielder NFC HSM / HSM PGP exemplify sovereign countermeasures in action. Their air‑gapped hardware ensures that integrity attestations and encryption proofs are generated and verified at runtime—securely, transparently, and independently from compromised infrastructure.
Out-of-Band Attestation with NFC HSM
Architectures based on NFC HSMs (Hardware Security Modules) enable offline cryptographic proof of integrity and identity. These devices remain isolated from network vectors and can confirm the non-compromise of key credentials or components, even post-incident. Freemindtronic’s PassCypher NFC HSM, PassCypher HSM PGP, DataShielder NFC HSM and Datashielder HSM PGP technologies patented exemplify this paradigm.
Real-Time Message Provenance Control
DataShielder NFC HSM Auth et DataShielder NFC HSM M-Auth chiffrent toutes les communications par défaut, sur n’importe quel canal, à l’aide de clés matérielles souveraines qui ne peuvent pas être clonées, copiées ou extraites. Ce paradigme offre :
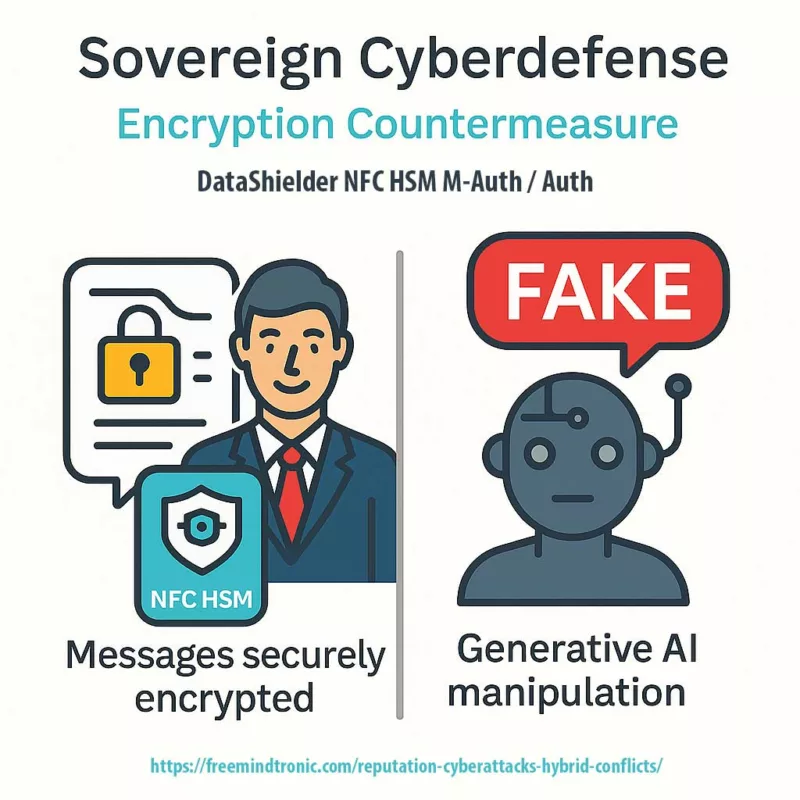
NFC HSM encryption draws a definitive boundary between authentic messages and fabricated narratives—making AI-forged disinformation both detectable and diplomatically indefensible.
- Verified encrypted messages sharply contrast with plaintext impersonations or unverifiable sources.
- Default encryption affirms authorship and message integrity without delay or user intervention.
- Falsehood becomes inherently visible, dismantling the ambiguity required for narrative manipulation.
This architecture enforces trust visibility by default—even across untrusted or compromised platforms—transforming every encrypted message into a sovereign proof of authenticity and every anomaly into a potential reputational alert.
Dynamic Certification & Runtime Audit
Static certification loses relevance once a component enters operational use. Reputation attacks exploit this gap by suggesting failure where none exists. Runtime certification performs real-time behavioural analysis, issuing updated trust vectors under sovereign control. Combined with policy-based revocation, this hardens narrative resilience.
Strategic Narrative Control
State entities and critical industries must adopt coherent, pre-structured public response strategies. The absence of technical breach must be communicated with authority and technical grounding. Naval Group’s qualified denial following its 2025 reputation leak demonstrates such sovereign narrative calibration under pressure.
This approach embodies dynamic certification, up to a temporal blockchain of trust. Unlike static attestations bound to deployment snapshots, sovereign systems like PassCypher NFC HSM and DataShielder NFC HSM perform ongoing behavioral evaluation—logging and cryptographically sealing runtime states.Each trust update can be timestamped, signed, and anchored in a sovereign ledger—transforming integrity into a traceable, irreversible narrative artifact. This not only preempts disinformation attempts but establishes a visible cryptographic chronicle that renders forgery diplomatically indefensible.
Sovereign cyberdefense means mastering time, integrity, and narrative. Out-of-band attestation and dynamic certification are not just security features—they are diplomatic weapons in an asymmetric reputational battlefield.
Strategic Case Illustrations
Reputation cyberattacks are no longer incidental. They are increasingly doctrinal, mirroring psyops in hybrid conflicts and weaponizing cognitive ambiguity. Below, we analyze three emblematic case studies where strategic visibility became a vulnerability—compromised not by code, but by coordinated narratives.
Morocco — CNSS Data Breach & Reputational Impact (April 2025)
- Major incident: In April 2025, Morocco’s National Social Security Fund (CNSS) experienced what is widely described as the largest cyber incident in the country’s digital history. The breach exposed personal data of approximately 2 million individuals and 500,000 enterprises, including names, national IDs, salaries, emails, and banking details. [Content verified via: moroccoworldnews.com, therecord.media, resecurity.com]
- Claimed attribution: The Algerian group JabaRoot DZ claimed responsibility, citing retaliation for an alleged breach of the APS (Algerian Press Service) account by Moroccan-linked actors.
- Technical vulnerability: The attack reportedly exploited “SureTriggers,” a WordPress module used by public services that auto-connects to Gmail, Slack, and Google APIs—identified as a likely vector in the incident.
- Collateral effects: The breach prompted temporary shutdowns of key Moroccan ministerial websites (Education, Tax), and government portals were disabled as a preventive cybersecurity measure. [Confirmed via moroccoworldnews.com]
- Institutional response: The NGO Transparency Maroc publicly criticized the lack of disclosure, urging authorities to release investigation findings and audit results to restore public confidence under data protection law 09‑08.
- Continental context: Kaspersky ranked Morocco among Africa’s top cyberattack targets, registering more than 12.6 million cyber threats in 2024, with significant increases in spyware and data exfiltration attempts.
The Moroccan breach illustrates the duality of hybrid threats: a massive technical compromise coupled with reputational erosion targeting public trust. By compromising legitimate governmental interfaces without penetrating core infrastructures, this attack typifies silent reputation warfare in a sovereign digital context.
United Kingdom — Reputation Warfare & Cyber Sabotage (2025)
- Contextual trigger: In May 2025, the UK government formally accused Russian GRU units 26165, 29155, and 74455 of coordinating cyber sabotage and influence operations targeting Western democracies, including the 2024 Paris Olympics and Ukrainian allies. The attribution was backed by the UK’s National Cyber Security Centre (NCSC). [gov.uk — Official Statement]
- Narrative dimension: Public attribution functions as a geopolitical signaling strategy—reasserting institutional legitimacy while projecting adversarial intent within a hybrid warfare doctrine.
- Institutional framing: The UK’s NCSC framed the attacks as hybrid campaigns combining technical compromise, reputational disruption, and online disinformation vectors. [NCSC Report]
The UK case underscores how naming threat actors publicly becomes a sovereign narrative tool—transforming attribution from defensive posture into reputational counterstrike within hybrid strategic doctrine.
Australia & New Zealand — AI‑Driven Reputation Campaigns & SME Disruption (2025)
- Threat escalation: In its July 2025 cyber threat bulletin, CyberCX raised the national threat level from “low” to “moderate” due to increased attacks by pro‑Russia and pro‑Iran hacktivists targeting SMEs and trust anchors. [CyberCX Report]
- AI impersonation cases: The Australian Information Commissioner reported a rise in deepfake voice-based impersonation (“vishing”) affecting brands like Qantas, prompting enhanced institutional controls. [OAIC Notifiable Data Breaches Report]
- Asymmetric reputational vectors: These campaigns leverage low-cost, high-impact impersonation to seed public distrust—especially effective when targeting service-based institutions with high emotional value.
In Australia and New Zealand, deepfake-enabled vishing attacks exemplify the evolution of hybrid threats—where brand trust, rather than infrastructure resilience, becomes the primary vector of reputational compromise.
Côte d’Ivoire — Symbolic Rise in Targeted Attacks (2024–2025)
- Threat profile: In 2024, Côte d’Ivoire recorded 7.5 million cyberattack attempts, including 60 000 identity theft attempts targeting civilian services, military infrastructures, electoral registries, and digital payment platforms.
- Targets: Military, electoral systems, and digital payment systems—underscoring both technical and narrative-driven attack vectors.
- Electoral context (2025): Ahead of the October presidential election, major opposition figures—including Tidjane Thiam, Laurent Gbagbo, Charles Blé Goudé, and Guillaume Soro—were excluded from the final candidate list published on 4 June 2025.
- List finality: The Independent Electoral Commission (CEI), led by Coulibaly‑Kuibiert Ibrahime, announced no further revision of the electoral register would occur before the vote..
- Narrative risk vector: The legal exclusion combined with a fixed submission window (July 25–August 26) constructs a narrow, information‑scarce environment—ideal for reputation attacks via bogus leaks, document falsification, or spoofed portals.
- Strategic interpretation: The limited electoral inclusivity and rigid timelines magnify potential narrative manipulation by actors seeking to simulate fraud or institutional incapacity.
- Sources: Reuters reports (June 4, 2025 – candidate exclusions) ; CEI confirmation of no further register revision :content.
In Côte d’Ivoire, structural cyber intrusions in 2024 and systemic electoral restrictions in 2025 converge into a hybrid threat environment: narrative ambiguity becomes a strategic tool, allowing reputation-based operations to undermine institutional credibility without requiring technical compromise.
AFJOC — Coordinated Regional Cyber Defense (Africa, 2025)
- Continental response: INTERPOL’s 2025 African Cyberthreat Report calls for regional coordination via AFJOC (Africa Joint Operation against Cybercrime).
- Threat evolution: AI-driven fraud, ransomware, and cybercrime-as-a-service dominating the threat landscape.
- Strategic implication: Highlights the necessity of sovereign runtime attestation and regional policy synchronization.
- Source: INTERPOL Africa Cyber Report 2025
AFJOC exemplifies a pan-African response to hybrid cyber threats—moving beyond technical patchwork to coordinated defense governance. Its operational scope highlights runtime integrity as a sovereign imperative.
Naval Group — Strategic Exposure via Reputation Leak
- Modus operandi: “Neferpitou” publishes 13 GB of allegedly internal data, claims 1 TB tied to Naval CMS systems, coinciding with high-level Indo-Pacific negotiations.
- Sovereign framing: Naval Group dismisses technical breach, insists on reputational targeting.
- Narrative vulnerability: Ambiguous provenance (possible reuse of Thales 2022 breach), lack of forensic certitude fuels speculation and diplomatic pressure.
- Systemic insight: CMS systems’ visibility within defense industry increases attack surface despite zero intrusion.
Naval Group’s incident shows how reputation can be decoupled from system security—exposure of industrial branding alone suffices to pressure negotiations, irrespective of intrusion evidence.
Dassault Rafale — Disinformation Post-Skirmish and Trust Erosion
- Tactic: Synthetic loss narratives post-Operation Sindoor. Gameplay footage (ARMA 3), AI-enhanced visuals, and bot networks flood social media.
- Strategic intent: Shift procurement trust toward Chinese J-10C alternatives. Undermine India-France defense collaboration.
- Corporate response: Dassault CEO publicly debunks losses; Indian MoD affirms Rafale superiority.
- Attack vector: Exploits latency in real-world combat validation versus immediate online simulation. Tempo differential becomes narrative leverage.
Dassault’s case highlights digital asymmetry: speed of synthetic disinformation outpaces real-time refutation. Trust erosion occurs before fact-checking stabilizes perceptions.
Kigen eSIM — Certified Component, Runtime Failure, Sovereign Breach
- Flawed certification chain: Java Card vulnerability in GSMA-certified Kigen eUICC enables runtime extraction of cryptographic keys and profiles.
- Collateral impact: >2 billion devices vulnerable across consumer, industrial, and automotive sectors.
- Strategic blind spots: TS.48 test profile lacks runtime attestation, no revocation mechanism, no post-deployment control layer.
- Geopolitical exploitation: APT41 and Lazarus repurpose cloned eSIM profiles for state-level impersonation and tracking.
- Sovereign countermeasure: NFC HSM runtime attestation proposed to separate dynamic trust from static certification.
Kigen illustrates how certification without runtime guarantees collapses in sovereign threat contexts. Attestation must be dynamic, portable, and verifiable—independent of issuing authority.
Israel–Iran — Predatory Sparrow vs Deepfake Sabotage
- Israeli offensive: In June 2025, Predatory Sparrow disrupted the digital services of Iran’s Sepah Bank, rendering customer operations temporarily inoperative.
- Iranian retaliation: Fake alerts, phishing campaigns, and deepfake operations aimed at creating panic.
- Narrative warfare: Over 60 pro-Iranian hacktivist groups coordinated attacks to simulate financial collapse and fuel unrest.
- Source: DISA escalation report
This conflict pair showcases dual-track warfare: targeted digital disruption of critical banking infrastructure, countered by synthetic information chaos designed to manipulate public perception and incite instability.
Intermediate & Legacy Cases
Recent campaigns reveal a growing sophistication in reputation cyberattacks. However, foundational cases from previous years still shape today’s threat landscape. These legacy incidents actively illustrate persistent vectors—ransomware amplification, unverifiable supply chain compromises, and narrative manipulation—that inform current defense strategies.
Change Healthcare Ransomware Attack (USA, 2024)
- Attack type: Ransomware combined with political reputational sabotage
- Immediate impact: Threat actors exposed over 100 million sensitive medical records, causing $2.9 billion in direct losses and paralyzing healthcare payments for weeks
- Narrative shift: The breach transformed into a media symbol of systemic vulnerability in U.S. healthcare infrastructure, influencing regulatory debates
- Source: U.S. HHS official statement
SolarWinds Software Supply Chain Breach (USA, 2020)
- Attack type: Covert infiltration through compromised update mechanism
- Systemic breach: APT29 infiltrated U.S. federal networks, including the Pentagon and Treasury, sparking concerns over supply chain certification trust
- Strategic consequence: Cybersecurity experts advocated for zero-trust architectures and verified software provenance policies
- Source: CISA breach alert
Colonial Pipeline Critical Infrastructure Sabotage (USA, 2021)
- Attack type: Ransomware disrupting fuel distribution logistics
- Operational impact: The attack triggered massive fuel shortages across the U.S. East Coast, igniting panic buying and public anxiety
- Narrative angle: Policymakers used the incident to challenge America’s energy independence and highlight outdated infrastructure protections
- Source: FBI attribution report
Estée Lauder Cloud Security Exposure (2020)
- Incident type: Public cloud misconfiguration without encryption
- Data disclosed: 440 million log entries surfaced online; none classified as sensitive but amplified for reputational damage
- Narrative exploitation: Media outlets reframed the incident as emblematic of weak corporate data governance, despite its low-risk technical scope
- Source: ZDNet technical analysis
GhostNet Global Cyber Espionage Campaign (2009)
- Origin point: China
- Infiltration method: Long-range surveillance across embassies, ministries, and NGOs in over 100 countries
- Reputational effect: The attack revealed the reputational power of invisible espionage and framed global cyber defense urgency
- Source: Archived GhostNet investigation
Signal Clone Breach – TeleMessage Spoofing Campaign (2025)
- Vector exploited: Brand mimicry and codebase confusion via Signal clone
- Security breach: Attackers intercepted communications of diplomats and journalists, casting widespread doubt on secure messaging apps
- Source: Freemindtronic breach analysis
Change Healthcare — Systemic Paralysis via Ransomware
- Incident: In February 2024, the ransomware group Alphv/BlackCat infiltrated Change Healthcare, disrupting critical healthcare operations across the United States.
- Impact: Over 100 million medical records exposed, halting prescription services and claims processing nationwide.
- Reputational fallout: The American Hospital Association labeled it the most impactful cyber incident in U.S. health system history.
- Aftermath: A $22 million ransom was paid; projected losses reached $2.9 billion.
Snowflake Cloud Breach — Cascading Reputation Collapse
- Event: In April 2024, leaked credentials enabled the Scattered Spider group to access customer environments hosted by Snowflake.
- Affected parties: AT&T (70M users), Ticketmaster (560M records), Santander Bank.
- Strategic gap: Several Snowflake tenants had no multi-factor authentication enabled, revealing governance blind spots.
- Reputational impact: The breach questioned shared responsibility models and trust in cloud-native zero-trust architectures.
Salt Typhoon APT — Metadata Espionage and Political Signal Leakage
- Threat actor: Salt Typhoon (Chinese APT), targeting U.S. telecoms (AT&T, Verizon).
- Tactics: Passive collection of call metadata and text records involving politicians such as Donald Trump and JD Vance.
- Objective: Narrative manipulation through reputational subversion and diplomatic misattribution.
- Official coverage: Documented by U.S. security agencies, cited in Congressional Research Service report IF12798.
Legacy is not just history; it’s doctrine.
Common Features & Strategic Objectives
Despite their varied execution, reputation cyberattacks exhibit a set of common features that define their logic, timing, and psychological impact. Recognizing these patterns allows sovereign actors and industrial targets to anticipate narrative shaping attempts and embed active countermeasures within their digital resilience strategy.
Common Features
- Non-technical vectors: Some attacks do not involve system compromise—only plausible disinformation or brand usurpation.
- Perception-centric: They aim at clients, partners, regulators—not infrastructure.
- Strategic timing: Aligned with high-value geopolitical, economic, or regulatory events.
- Narrative instruments: Use of Telegram, forums, deepfakes, AI-generated content, and synthetic media.
- Attribution opacity: Exploits legal and technical gaps in global cyber governance.
Strategic Objectives
- Erode trust in sovereign technologies or industrial actors
- Influence acquisition, regulation, or alliance decisions
- Create asymmetric narratives favoring the attacker
- Delay, deflect, or preempt defense procurement or certification
- Prepare cognitive terrain for future technical or diplomatic intrusion
Reputation cyberattacks blur the lines between cybersecurity, psychological operations, and diplomatic sabotage. Their prevention requires integration of threat intelligence, strategic communications, and runtime trust mechanisms.
Common Features & Strategic Objectives
Despite their varied execution, reputation cyberattacks exhibit a set of common features that define their logic, timing, and psychological impact. Recognizing these patterns allows sovereign actors and industrial targets to anticipate narrative shaping attempts and embed active countermeasures within their digital resilience strategy.
Common Features
- Non-technical vectors: Some attacks do not involve system compromise—only plausible disinformation or brand usurpation.
- Perception-centric: They aim at clients, partners, regulators—not infrastructure.
- Strategic timing: Aligned with high-value geopolitical, economic, or regulatory events.
- Narrative instruments: Use of Telegram, forums, deepfakes, AI-generated content, and synthetic media.
- Attribution opacity: Exploits legal and technical gaps in global cyber governance.
Strategic Outlook
Reputation cyberattacks are no longer peripheral threats. They operate as strategic levers in hybrid conflicts, capable of delaying negotiations, undermining certification, and shifting procurement diplomacy. These attacks are asymmetric, deniable, and narrative-driven. Their true target is sovereignty—technological, diplomatic, and communicational.
The challenge ahead is not merely one of defense, but of narrative command. States and sovereign technology providers must integrate verifiable runtime trust, narrative agility, and resilience to perception distortion. Silence is no longer neutrality; it is vulnerability.
Strong Signals:
- Coordinated leaks following high-level diplomatic statements
- Multiple unverifiable claims against certification authorities
- Escalation in deepfake dissemination tied to defense technologies
Imagine a defense consortium deploying a real-time, attested HSM-based runtime environment that logs and cryptographically proves system integrity in air-gapped mode. A leaked document emerges, claiming operational failure. Within 48 hours, the consortium publishes a verifiable attestation proving non-compromise—transforming a potential discredit into a sovereign show of digital force.
To sustain trust in the era of information warfare, sovereignty must be demonstrable—technically, legally, and narratively.
Narrative Warfare Lexicon
To fortify sovereign understanding and strategy, this lexicon outlines key concepts deployed throughout this chronicle. Each term reflects a recurring mechanism of hybrid influence in reputation-centric cyber conflicts.
Sovereign Attestation:
Verifiable proof of message origin and integrity, enforced by hardware-based cryptography and runtime sealing mechanisms.
Perception Latency:
Delay between technical compromise and public interpretation, allowing adversaries to frame or distort narratives in real-time.
Runtime Ambiguity:
Exploitation of unverified system states or certification gaps during live operation, blurring accountability boundaries.
Trusted Silence:
Intentional lack of institutional response to unverifiable leaks, contrasted by provable data integrity mechanisms.
Strategic Leakage:
Deliberate release of curated data fragments to simulate broader compromise and provoke institutional panic.
Attested Narrative Artifact:
Communication whose authenticity is cryptographically enforced and auditably traceable, independent of central validation.
Adversarial Framing:
Use of metadata, linguistic bias, or visual overlays to recontextualize legitimate content into hostile perception.
Out-of-Band Attestation (NFC HSM):
Isolated cryptographic proof of key integrity, resistant to network manipulation. These air-gapped modules independently enforce the origin and authenticity of communications.
Real-Time Integrity Proof:
Continuous sealing and audit of system states during live operation. Prevents the exploitation of momentary ambiguity or delay in narrative framing.
Dynamic Certification:
Adaptive verification mechanism that evolves with runtime behavior. Unlike static seals, it updates the trust status of components based on real-time performance and sovereign policy triggers.
Temporal Blockchain of Trust:
Time-stamped ledger of cryptographically sealed events, where each proof of integrity becomes a narrative checkpoint. This chained structure forms a verifiable, sovereign memory of truth—resilient against falsification or post-hoc reinterpretation.
Temporal Ledger of Attestation:
A chronologically ordered record of integrity proofs, allowing for verifiable reconstruction of system trust state over time. Especially useful in forensic or diplomatic contexts.
Runtime Proof Anchoring:
Technique by which runtime attestation outputs are immediately sealed and anchored in sovereign repositories, ensuring continuity and traceability of system integrity.
Distributed Sovereign Chronicle:
Federated attestation system in which multiple sovereign or institutional nodes validate and preserve cryptographic proofs of trust, forming a geopolitical ledger of resilience against coordinated narrative subversion.
Beyond This Chronicle
The anatomy of invisible cyberwars is far from complete. As sovereign digital architectures evolve, new layers of hybrid reputational threats will emerge—possibly automated, decentralized, and synthetic by design. These future vectors may combine adversarial AI, autonomous leak propagation, and real-time perception manipulation across untrusted ecosystems.
Tracking these tactics will require more than technical vigilance. It will demand:
- Runtime sovereignty: Systems must cryptographically attest their integrity in real time, independent of external validators.
- Adversarial lexicon auditing: Monitoring how language, metadata, and synthetic narratives are weaponized across platforms.
- Neutral trust anchors: Deploying hardware-based cryptographic roots that remain verifiable even in contested environments.
Freemindtronic’s work on DataShielder NFC HSM and PassCypher HSM PGP exemplifies this shift. These technologies enforce message provenance, runtime attestation, and sovereign encryption—transforming each communication into a verifiable narrative artifact.
Future chronicles will deepen these vectors through:
- Case convergence: Mapping how reputation attacks evolve across sectors, regions, and diplomatic cycles.
- Technological foresight: Anticipating how quantum-safe cryptography, AI-generated disinformation, and decentralized identity will reshape the reputational battlefield.
- Strategic simulation: Modeling sovereign response scenarios to reputational threats using attested environments and synthetic adversaries.
In the next phase, reputation defense will not be reactive—it will be declarative. Sovereignty will be demonstrated not only through infrastructure, but through narrative control, cryptographic visibility, and strategic timing.
APT41 Cyberespionage and Cybercrime represents one of the most strategically advanced and enduring cyber threat actors globally. In this comprehensive report, Jacques Gascuel examines their hybrid operations—combining state-sponsored espionage and cybercriminal campaigns—and outlines proactive defense strategies to mitigate their impact on national security and corporate infrastructures.
APT41 – Navigation Guide:
- History and Evolution
- APT41 – Key Statistics and Impact
- MITRE ATT&CK Matrix Mapping
- Tactics, Techniques and Procedures (TTPs)
- Structure and Operations
- Chrome V8 Exploits
- TOUGHPROGRESS Calendar C2 (May 2025)
- Mitigation and detection strategies
- Malware and tools
- Infrastructure
- Motivations and Targets
- Indicators of Compromise (IOCs)
- Freemindtronic HSM Ecosystem – APT41 Defense Matrix
- Outlook and Next Steps
APT41 (Double Dragon / BARIUM / Wicked Panda) Cyberespionage & Cybercrime Group
Last Updated: April 2025
Version: 1.0
Source: Freemindtronic Andorra
Origins and Rise of the APT41 Cyberespionage and Cybercrime Group
Active since at least 2012, APT41 Cyberespionage and Cybercrime operations are globally recognized for their dual nature: combining state-sponsored espionage with personal enrichment schemes (Google Cloud / Mandiant). The group exploits critical vulnerabilities (Citrix CVE‑2019‑19781, Log4j / Log4Shell – CVE-2021-44228), UEFI bootkits (MoonBounce), and supply chain attacks (Wikipedia – Double Dragon).
APT41 – Key Statistics and Impact
- First Identified: 2012 (active since at least 2010 according to some telemetry).
- Number of Public CVEs Exploited: Over 25, including high-profile vulnerabilities like Citrix ADC (CVE-2019-19781), Log4Shell (CVE-2021-44228), and Chrome V8 (CVE-2025-6554).
- Confirmed APT41 Toolkits: Over 30 identified malware families and variants (e.g., DUSTPAN, ShadowPad, DEAD EYE).
- Known Victim Countries: Over 40 countries spanning 6 continents, including U.S., France, Germany, UK, Taiwan, India, and Japan.
- Targeted Sectors: Government, Telecom, Healthcare, Defense, Tech, Cryptocurrency, and Gaming Industries.
- U.S. DOJ Indictment: 5 named Chinese nationals in 2020 for intrusions spanning over 100 organizations globally.
- Hybrid Attack Model: Unique mix of espionage (state-backed) and cybercrime (personal enrichment) confirmed by Mandiant, FireEye, and the U.S. DOJ.
MITRE ATT&CK Matrix Mapping – APT41 (Enterprise & Defense Combined)
| Tactic | Technique | Description |
|---|---|---|
| Initial Access | T1566.001 | Spearphishing with malicious attachments (ZIP+LNK) |
| Execution | T1059.007 | JavaScript execution via Chrome V8 |
| Persistence | T1542.001 | UEFI bootkit (MoonBounce) |
| Defense Evasion | T1027 | Obfuscated PowerShell scripts, memory-only loaders |
| Credential Access | T1555 | Access to stored credentials, clipboard monitoring |
| Discovery | T1087 | Active Directory enumeration |
| Lateral Movement | T1210 | Exploiting remote services via RDP, WinRM |
| Collection | T1119 | Automated collection via SQLULDR2 |
| Exfiltration | T1048.003 | Exfiltration via cloud services (Google Drive, OneDrive) |
| Command & Control | T1071.003 | Abuse of Google Calendar (TOUGHPROGRESS) |
Tactics, Techniques and Procedures (TTPs)
The APT41 Cyberespionage and Cybercrime campaign has evolved into one of the most widespread and adaptable threats, impacting over 40 countries across critical industries.
- Initial Access: spear‑phishing, pièces jointes LNK/ZIP, exploitation de CVE, failles JavaScript (Chrome V8) via watering-hole, invitations malveillantes via Google Calendar (TOUGHPROGRESS).
- Browser Exploitation: zero-day targeting Chrome V8 engine (e.g., CVE-2025-6554), enabling remote code execution via crafted JavaScript in spear-phishing and watering-hole campaigns.
- Persistence: bootkits UEFI (MoonBounce), loaders en mémoire (DUSTPAN, DEAD EYE).
- Lateral Movement: Cobalt Strike, credential theft, rootkits Winnti.
- C2: abus de Cloudflare Workers, Google Calendar/Drive/Sheets, TLS personnalisé
- TLS fingerprinting: Detect anomalies in self-signed TLS certs and suspicious CA chains (used in APT41’s custom TLS implementation).
- Exfiltration: SQLULDR2, PineGrove via OneDrive.
Global Footprint of APT41 Victimology
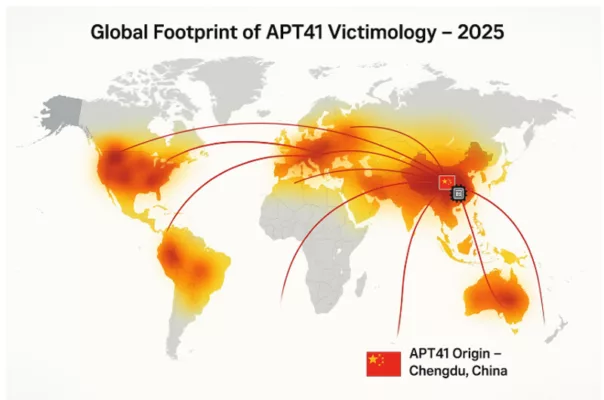
The global heatmap illustrates the spread of APT41 cyberattacks in 2025, with Chengdu, China marked as the origin. Curved arcs highlight targeted regions in North America, Europe, Asia, and beyond. heir targeting spans critical infrastructure, multinational enterprises, and governmental agencies.
APT41 Cyberespionage and Cybercrime – Structure and Operations
The APT41 Cyberespionage and Cybercrime group is believed to operate as a contractor or affiliate of the Chinese Ministry of State Security (MSS), with ties to regional cyber units. Unlike other nation-state groups, APT41 uniquely combines state-sponsored espionage with financially motivated cybercrime — including ransomware deployment, cryptocurrency theft, and illicit access to video game environments for profit. This hybrid approach enables the group to remain operationally flexible while continuing to deliver on geopolitical priorities set by state actors.
Attribution reports from the U.S. Department of Justice (DOJ) [DOJ 2020 Indictment] identify several named operatives associated with APT41, highlighting the structured and persistent nature of their operations. The group has demonstrated high coordination, advanced resource access, and the ability to pivot quickly between long-term intelligence operations and short-term financially motivated campaigns.
APT41 appears to operate with a dual-hat model: actors perform espionage tasks during official working hours and engage in financially driven attacks after hours. Reports suggest the use of a shared malware codebase among regional Chinese APTs, but with distinct infrastructure and tasking for APT41.
Attribution & Legal Action
In September 2020, the U.S. Department of Justice publicly indicted five Chinese nationals affiliated with APT41 for a global hacking campaign. Although not apprehended, these indictments marked a rare instance of legal attribution against Chinese state-linked actors. The group’s infrastructure, tactics, and timing patterns (active during GMT+8 working hours) strongly point to a connection with China’s Ministry of State Security (MSS).
APT41 Cyberespionage and Cybercrime – Chrome V8 Exploits
In early 2025, APT41 was observed exploiting a zero-day vulnerability in the Chrome V8 JavaScript engine, identified as CVE-2025-6554. This flaw allowed remote code execution through malicious JavaScript payloads delivered via watering-hole and spear-phishing campaigns.
This activity demonstrates APT41’s increasing focus on client-side browser exploitation to gain initial access and execute post-exploitation payloads in memory, often chained with credential theft and privilege escalation tools. Their ability to adapt to evolving browser engines like V8 further expands their operational scope in high-value targets.
Freemindtronic’s threat research confirmed active use of this zero-day in targeted attacks on European government agencies and tech enterprises, reinforcing the urgent need for browser-level monitoring and hardened sandboxing strategies.
TOUGHPROGRESS Calendar C2 (May 2025)
In May 2025, Google’s Threat Intelligence Group (GTIG), The Hacker News, and Google Cloud confirmed APT41’s abuse of Google Calendar for command and control (C2). The technique, dubbed TOUGHPROGRESS, involved scheduling encrypted events that served as channels for data exfiltration and command delivery. Google responded by neutralizing the associated Workspace accounts and Calendar instances.
Additionally, Resecurity published a June 2025 report confirming continued deployment of TOUGHPROGRESS on a compromised government platform. Their analysis revealed sophisticated spear-phishing methods using ZIP archives with embedded LNK files and decoy images.
To support detection, SOC Prime released Sigma rules targeting calendar abuse patterns, now incorporated by leading SIEM vendors.
Mitigation and Detection Strategies
- Update Management: proactive patching of CVEs (Citrix, Log4j, Chrome V8), rapid deployment of security fixes.
- UEFI/TPM Protection: enable Secure Boot, verify firmware integrity, use HSMs to isolate cryptographic keys from OS-level access.
- Cloud Surveillance: behavioral monitoring for abuse of Google Calendar, Drive, Sheets, and Cloudflare Workers via SIEM and EDR systems.
- Memory-based Detection: YARA and Sigma rules targeting DUSTPAN, DEAD EYE, and TOUGHPROGRESS malware families.
- Advanced Detection: apply Sigma rules from SOC Prime for identifying C2 anomalies via calendar-based techniques.
- Network Isolation: enforce segmentation and air gaps for sensitive environments; monitor DNS and TLS outbound patterns.
- Browser-level Defense: enable Chrome’s Site Isolation mode, enhance sandboxing, monitor abnormal JavaScript calls to the V8 engine.
- Key Isolation: use hardware HSMs like DataShielder to prevent unauthorized in-memory key access.
- Network TLS profiling: Alert on unknown certificate chains or forged CAs in outbound traffic.
Malware and Tools
- MoonBounce: UEFI bootkit linked to APT41, detailed by Kaspersky/Securelist.
- DUSTPAN / DUSTTRAP: Memory-resident droppers observed in a 2023 campaign.
- DEAD EYE, LOWKEY.PASSIVE: Lightweight in-memory backdoors.
- TOUGHPROGRESS: Abuses Google Calendar for C2, used in a late-2024 government targeting campaign.
- ShadowPad, PineGrove, SQLULDR2: Advanced data exfiltration tools.
- LOWKEY/LOWKEY.PASSIVE: Lightweight passive backdoor used for long-term surveillance.
- Crosswalk: Malware for targeting both Linux and Windows in hybrid cloud environments.
- Winnti Loader: Shared component used to deploy payloads across various Chinese APT groups.
- DodgeBox – Memory-only loader active since 2025 targeting EU energy sector, using PE32 x86 DLL signature evasion.
- Lateral Movement: Cobalt Strike, credential theft, Winnti rootkits, and legacy exploits like PrintNightmare (CVE-2021-34527).
Possible future threats include MoonWalk (UEFI-EV), a suspected evolution of MoonBounce, targeting firmware in critical systems (e.g., Gigabyte and MSI BIOS), as observed in early 2025. Analysts should anticipate deeper firmware-level persistence across high-value targets.
Use of Cloudflare Workers, Google APIs, and short-link redirectors (e.g., reurl.cc) for C2. TLS via stolen or self-signed certificates.
APT41 Cyberespionage and Cybercrime Motivations and Global Targets
APT41 Cyberespionage and Cybercrime campaigns are driven by a unique dual-purpose strategy, combining state-sponsored intelligence gathering with financially motivated cyberattacks. Unlike many APT groups that focus solely on espionage, APT41 leverages its advanced capabilities to infiltrate both government networks and private enterprises for political and economic gain. This hybrid model allows the group to target a wide range of industries and geographies with tailored attack vectors.
- Espionage: Governments (United States, Taiwan, Europe), healthcare, telecom, high-tech sectors.
- Cybercrime: Video game industry, cryptocurrency wallets, ransomware operations.
APT41 Operational Model – Key Phases
This mindmap offers a clear and concise visual synthesis of APT41 Cyberespionage and Cybercrime activities. It highlights the key operational stages used by APT41, from initial access via spearphishing (ZIP/LNK) to data exfiltration through cloud-based Command and Control (C2) infrastructure.
Visual elements illustrate how APT41 combines memory-resident malware, lateral movement, and cloud abuse to achieve both espionage and monetization goals.
Mindmap: APT41 Operational Model – Tracing the full attack lifecycle from compromise to monetization.
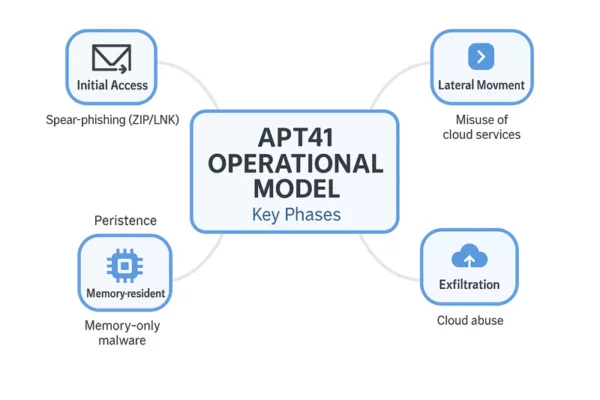
This section summarizes the typical phases of APT41 Cyberespionage and Cybercrime operations, from initial compromise to exfiltration and monetization.
APT41 combines advanced cyberespionage with financially motivated cybercrime in a streamlined operational cycle. Their tactics evolve constantly, but the core lifecycle follows a recognizable pattern, blending stealth, persistence, and monetization.
- Initial Access: Spearphishing campaigns using ZIP+LNK attachments or fake software installers.
- Execution: Fileless malware or memory-only loaders such as DUSTPAN or DodgeBox.
- Persistence: UEFI implants like MoonBounce or potential MoonWalk variants.
- Lateral Movement: Exploitation of remote services (e.g., RDP, PrintNightmare), AD enumeration.
- Exfiltration: Use of SQLULDR2, OneDrive, Google Drive for data exfiltration.
- Command & Control: Cloud-based channels, including Google Calendar events and TLS tunnels.
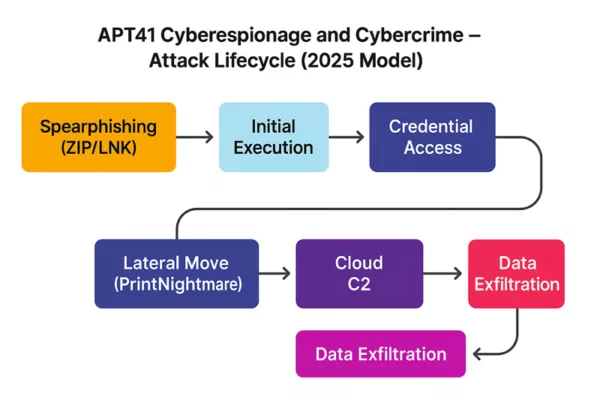
APT41 Cyberespionage and Cybercrime – Attack Lifecycle (2025): From spearphishing to data exfiltration via cloud command-and-control.
Mobile Threat Vectors – Emerging Tactics
APT41 has tested malicious fake installers (.apk/.ipa) targeting mobile platforms, including devices used by diplomatic personnel. These apps are often distributed via private links or QR codes and may allow persistent remote access to mobile infrastructure.
Future Outlook on APT41 Cyberespionage and Cybercrime Operations
APT41 Cyberespionage and Cybercrime exemplifies the hybrid model of modern digital threats, combining stealth operations with financial motives. Its use of stealth technologies—such as UEFI bootkits, memory-only malware, and cloud infrastructure abuse—demands a defense-in-depth approach supported by constantly refreshed threat intelligence. This document will be updated as new discoveries emerge (e.g., MoonWalk, DodgeBox…).
“APT41 represents a quantum leap in hybrid threat models—blurring the lines between state espionage and digital crime syndicates. Understanding their operational asymmetry is key to defending both critical infrastructure and intellectual sovereignty.”
— Jacques Gascuel, Inventor & CEO, Freemindtronic Andorra
APT41 Operational Lifecycle: From Cyberespionage to Cybercrime
APT41 Cyberespionage and Cybercrime operations typically begin with reconnaissance and spear-phishing campaigns, followed by the deployment of malware loaders such as DUSTPAN and memory-only payloads like DEAD EYE. Once initial access is achieved, the group pivots laterally across networks using credential theft and Cobalt Strike, often deploying Winnti rootkits to maintain long-term persistence.
Their hybrid lifecycle blends strategic espionage goals — like exfiltrating data from healthcare or governmental institutions — with opportunistic attacks on cryptocurrency platforms and gaming environments. This dual approach complicates attribution and enhances the group’s financial gain, making APT41 one of the most versatile and dangerous cyber threat actors to date.
Indicators of Compromise (IOCs)
- Malware: MoonBounce, TOUGHPROGRESS, DUSTPAN, ShadowPad, SQLULDR2.
- Infrastructure: Google Calendar URLs, Cloudflare Workers, reurl.cc.
- Signatures: UEFI implants, memory-only malware, abnormal TLS behaviors.
Mitigation and Detection Measures
- Updates: Patch CVEs (Citrix, Log4j), update UEFI firmware.
- UEFI/TPM Protection: Enable Secure Boot, use offline HSMs for key storage.
- Cloud Surveillance: Track anomalies in Google/Cloudflare-based C2 traffic.
- Memory Detection: YARA/Sigma rules for TOUGHPROGRESS and DUSTPAN.
- EDR & Segmentation: Enforce strict network separation.
- Key Isolation: Offline HSM and PGP usage.
APT41 Cyberespionage and Cybercrime – Strategic Summary
APT41 Cyberespionage and Cybercrime operations continue to represent one of the most complex threats in today’s global cyber landscape. Their unique blend of state-aligned intelligence gathering and profit-driven criminal campaigns reflects a dual-purpose doctrine increasingly adopted by advanced persistent threats. From exploiting zero-days in Chrome V8 to abusing Google Workspace and Cloudflare Workers for stealthy C2 operations, APT41 exemplifies the modern hybrid APT. Organizations should adopt proactive defense measures, such as offline HSMs, UEFI security, and TLS fingerprint anomaly detection, to mitigate these risks effectively.
Freemindtronic HSM Ecosystem – APT41 Defense Matrix
The following matrix illustrates how Freemindtronic’s HSM solutions neutralize APT41’s most advanced techniques across both espionage and cybercriminal vectors.
Encrypted QR Code – Human-to-Human Response
To illustrate a real-world countermeasure against APT41 cyberespionage operations, this demo showcases the use of a secure encrypted QR Code that can be scanned with a DataShielder NFC HSM device. It allows analysts or security officers to exchange a confidential message offline, without relying on external servers or networks.
Use case: An APT41 incident response team can securely distribute an encrypted instruction or key via QR Code format — the message remains encrypted until scanned by an authorized device. This ensures end-to-end encryption, offline delivery, and complete data sovereignty.

Illustration of a secure QR code-based message exchange to counter APT41 cyberespionage and cybercrime threats.
🔐 Scan this QR code using your DataShielder NFC HSM device to decrypt a secure analyst message related to the APT41 threat.
| Threat / Malware | DataShielder NFC HSM | DataShielder HSM PGP | PassCypher NFC HSM | PassCypher HSM PGP |
|---|---|---|---|---|
| Spear‑phishing / Macros | ✘ | ✔ Sandbox |
✘ | ✔ PGP Container |
| MoonBounce (UEFI) | ✔ NFC offline |
✔ OS‑bypass |
✘ | ✔ Secure Boot enforced |
| Cloud C2 | ✔ 100 % offline |
✔ Offline |
✔
Offline |
✔ No external connection |
| TOUGHPROGRESS (Google Abuse) | ✔
No Google API use |
✔ PGP validation |
✔ Encrypted QR only |
✔ Isolated |
| ShadowPad | ✔ No key in RAM |
✔ Offline use |
✔ No clipboard use |
✔ Sandboxed login |
Future Outlook on APT41 Cyberespionage and Cybercrime Operations
APT41 Cyberespionage and Cybercrime exemplifies the hybrid model of modern digital threats, combining stealth operations with financial motives.Its use of stealth technologies—such as UEFI bootkits, memory-only malware, and cloud infrastructure abuse—demands a defense-in-depth approach supported by constantly refreshed threat intelligence. This document will be updated as new discoveries emerge (e.g., MoonWalk, DodgeBox…).
As of mid-2025, security researchers are closely monitoring the evolution of APT41’s toolset and objectives. Several indicators point toward the emergence of MoonWalk—a suspected successor to MoonBounce—designed to target UEFI environments in energy-sector firmware (Gigabyte/MSI BIOS suspected). Meanwhile, campaigns using DodgeBox and QR-distributed fake installers on Android and iOS platforms show a growing interest in covert mobile infiltration. These developments suggest a likely increase in firmware-layer intrusions, mobile surveillance tools, and social engineering payloads targeting diplomatic, industrial, and defense networks.
“APT41 represents a quantum leap in hybrid threat models—blurring the lines between state espionage and digital crime syndicates. Understanding their operational asymmetry is key to defending both critical infrastructure and intellectual sovereignty.”
— Jacques Gascuel, Inventor & CEO, Freemindtronic Andorra
Strategic Recommendations
- Deploy firmware validation routines and Secure Boot enforcement in critical systems
- Proactively monitor TLS traffic for custom fingerprinting or rogue CA chainsde constr
- Implement out-of-band communication tools like encrypted QR codes for human-to-human alerting
- Use memory-scanning EDRs and YARA rules tailored to new loaders like DodgeBox and DUSTPAN
- Monitor mobile ecosystems for signs of unauthorized app distribution or QR-based spearphishing
- Review permissions and logging for Google and Cloudflare API usage in corporate networks
APT41 Cyberespionage and Cybercrime exemplifies the hybrid model of modern digital threats…