EviToken & EviCypher Technology a new way to keep secrets and pass them on.
EviToken & EviCypher technology to control information privacy is an absolute necessity today, as there are so many cyber malicious acts. We can cite among others acts such as phishing, stalking or ransomware. These so-called “cyber” threats alone represent approximately 75% of the infiltration techniques giving access to your confidential or personal data. All of these techniques have the same approach, which is identity theft. This mechanism allows an individual, or a machine, to impersonate someone or something else. The recipient thus deceived, lifts his natural mistrust to trust this ill-intentioned sender.
Protection techniques for transmitting confidential or personal data have been around for a very long time, as have signature mechanisms. They are most often based on asymmetric key algorithms, with strong encryption (RSA of 2048 or 4096 bits or even ECDSA). Unfortunately, if the model on which these encryption techniques are based is proven and ensures flawless security, its IT implementation is, for its part, often undermined by man-in-the-middle attacks, or by elevations of law on information systems. These attacks, when identification or decryption relies only on one-factor authentication, allow the theft of encryption keys, and directly compromise the security of your data. To mitigate these threats, two-factor authentication (or 2FA) adds a layer of protection by either obtaining a unique code sent by SMS to your phone number, or by validating a request for it authentication (Google / Facebook), or through the use of authenticators which is increasingly recommended by security specialists.
Why use the EviToken & EviCypher Technology?
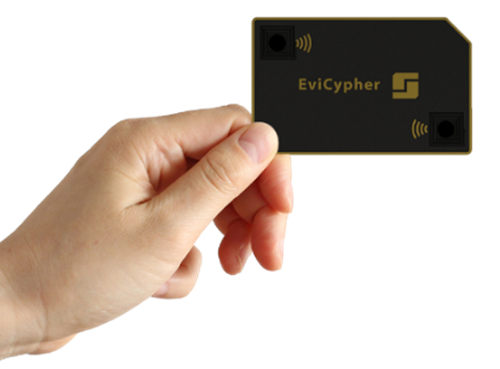
The purpose of EviToken & EviCypher technology is to secure secrets of different kinds, such as asymmetric keys (RSA), symmetric keys (AES) but also login information, PIN codes, account or bank card identifiers, cryptocurrency private keys, cryptocurrency wallet passphrases, cryptocurrency recovery phrases (SEED), etc. The EviToken & EviCypher secure safe is contained in a simple NFC card, not connected to a computer system. It communicates with the latter, on demand, via a near-field transmission protocol (NFC) which transmits data over an encrypted channel, built by EviToken & EviCypher. Secrets stored in the card are segmented and encrypted to make them physically inaccessible to cybercriminals. The EviToken & EviCypher secure safe is a real natural Air Gap component. Thus, apart from the case of data transmission, the architecture used has: no power supply; no security breach due to an increase in temperature (which makes it immune to malware such as “BitWhisper and Fansmitter”); no emission of sound signals, even those inaudible to the human ear and no emission of light or waves. Finally, to avoid a conflation with smart card-based systems, the support of EviToken & EviCypher technology does not require dedicated physical connection hardware with the digital system, nor does it have an operating system, which makes it insensitive to the introduction of malicious code as on a Java architecture. Like any electronic component, the EviToken & EviCypher secure safe can undergo invasive attacks which consist in using acids to expose the electronic circuit that will then have to be analyzed to try to understand the implementation of the secure secrets in multiple scrambled segments.
If EviToken & EviCypher technology provides security in a secure vault, what about the use of encryption keys to transport secrets over a secure channel?
In the context of two-factor authentication, we consider that you are the only one who can hold the second criterion of trust. This security measure traditionally allows, in case of failure, not to trigger the secure transport of your data. However, this function is not intended to secure the transport, it is the role of the encryption protocol to perform this operation. Thus, if the encryption keys are compromised, the data could be compromised during a listen. Faced with this problem, EviToken & EviCypher directly integrates metadata trust criteria into its encryption keys, in order to secure the encrypted messages during their transport. Thus, even in the event of a compromise of the keys, decryption remains blocked by the trust criteria. With this in mind, why stop at two criteria of trust? In its basic version, EviToken & EviCypher offers nine trust criteria based on the possession of a third-party object, technical components (phone ID, barcode, password, geolocation or BSSID) but also environmental and specific components to the sender, or recipient, to make data compromise even more difficult.
A simple example, you want to send a confidential message containing your latest invention to a colleague in a hostile environment, with a high probability of compromise. You will therefore add non-digital trust criteria to your encryption key, to ensure its protection in the event of a compromise. The decryption of the message by the AES 256 symmetric key will only be accessible, by the digital tool, once the conditions related to the trust criteria have been met. If we base one of the trust criteria on a geolocation for example, the recipient must not only be in possession of an EviToken & EviCypher card, but also be physically located at the location of geolocation defined in the trust criteria to decrypt the message. This location may be known to the recipient like a convention, but may also not be known. The trust criterion will then be transmitted to him as one of the authentication multi-factors, by SMS / QR Code / Photo or any other means.
If EviToken & EviCypher technology provides security in a secure safe, encryption of messages with trust criteria based on environmental components, technical or not, what about the transmission of keys for use in a space digital connected?
To secure end-to-end transmissions, several tools, used as gateways, such as smartphones or virtual keyboards, will be crossed. EviToken & EviCypher then builds encrypted channels, from the first communications between the EviToken & EviCypher card and the first NFC communication gateway, using an AES 128 symmetric pairing key. The latter will be replaced by a 256-bit AES symmetric key, with different trust criteria depending on the user’s choice, when recording a secret. Communication with web browsers is achieved using 256-bit ECC ephemeral keys (X25519), to negotiate exchanges between the smartphone and the browser plugin, to insert website authentication, text decryption, etc. As for the transmission, from the smartphone, of texts, images or encrypted files, the encryption is carried out with a symmetric key AES 256 bits with trust criteria.
Why choose the EviToken & EviCypher technology?
Our goal is to better understand the feasibility of digital malicious acts through a human approach to attacks. Thus, if you do not physically have the EviToken & EviCypher card, or if you do not have access to it with a connection duration long enough to carry out an attack, it will be very difficult to compromise the safe, but it is quite obvious that «to the impossible no one is bound “. “However, this attack requires physical contact, it is no longer possible to hide behind anonymizers. Assuming that the encrypted message is sufficiently protected, with algorithms such as 2048- or 4096-bit RSA or even ECDSA, then it is necessary to look into the protection of the key. Indeed, this protection will remain true as long as the encryption and decryption keys remain secret. History of computer attacks shows certain difficulties in maintaining this assertion. It is therefore necessary to strengthen the protection of the keys, by accepting the compromise of the latter, while protecting the message during its transport. at best for this requirement, non-digital trust criteria, that is to say criteria known, held, observable or understandable by the recipient, are required for the decryption of the message and no longer of the key.
EviToken & EviCypher technology, by adding these trust criteria, changes the current paradigm of access to secrets. Thus, even if a secret, and more particularly a decryption key, were stolen, it could only be used if the trust criteria are met.
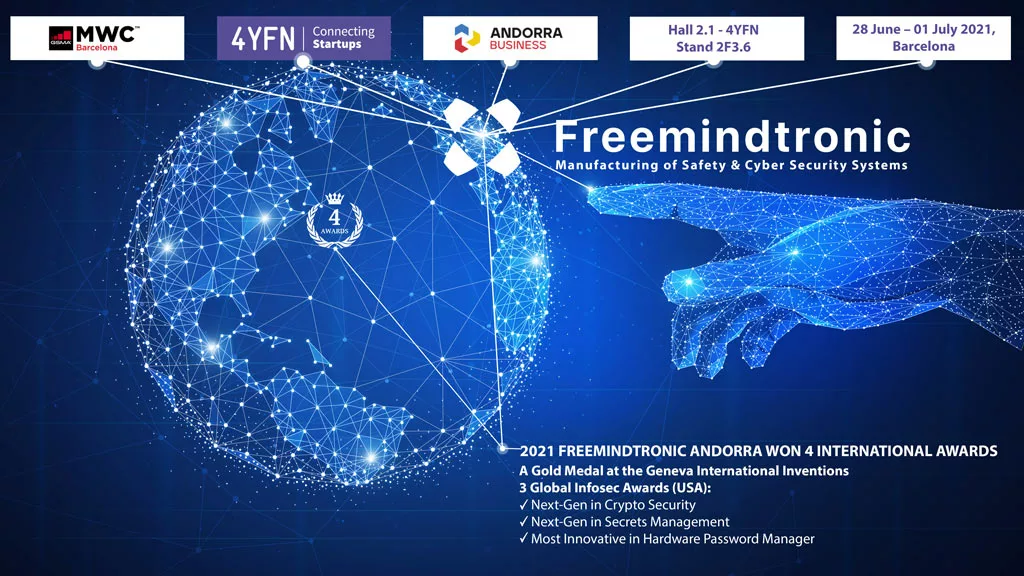
Based on the EviToken & EviCypher principle, the new EviCypher technology, which won the 2021 gold medal for international inventions from Geneva, brings new innovations in the creation, management, integration and augmented intelligence linked to the use of trust criteria. A new chapter on this internationally patented invention on segmented key authentication is opening.
About the author
 Fabrice Crasnier is the director of Research & Development departement of FREEMINDTRONIC. Freemindtronic, Andorran start-up designs and manufactures tailor-made solutions for its customers in the field of safety and cyber security of information systems and computer systems.
Fabrice Crasnier is the director of Research & Development departement of FREEMINDTRONIC. Freemindtronic, Andorran start-up designs and manufactures tailor-made solutions for its customers in the field of safety and cyber security of information systems and computer systems.
Fabrice is Associate Professor at Paul Sabatier University in Toulouse where he teaches cybercrime phenomena. He is at the origin of the creation of 3 forensic laboratories as head of forensic activities within the french police in Toulouse and within the SCASSI company. He has worked for 27 years in the judicial police, including 17 years following national and international cybercrime investigations. As a judicial expert since 2004 at the Court of Appeal of Toulouse, he has witnessed the delinquent transformation of cyberspace between 2000 and 2017. As a computer engineer, he has understood that the origin of cyberthreats is not always due to a defect in computer tools but more often to a misuse of these tools.
Fabrice can be reached online on LinkedIn: https://www.linkedin.com/in/fabricecrasnier/
For more information, visit the company website at www.freemindtronic.com





























































 Fabrice Crasnier is the director of Research & Development departement of FREEMINDTRONIC. Freemindtronic, Andorran start-up designs and manufactures tailor-made solutions for its customers in the field of safety and cyber security of information systems and computer systems.
Fabrice Crasnier is the director of Research & Development departement of FREEMINDTRONIC. Freemindtronic, Andorran start-up designs and manufactures tailor-made solutions for its customers in the field of safety and cyber security of information systems and computer systems.