Beware of communication vulnerabilities in 2023
Communication is essential for our personal and professional lives, but it also exposes us to cyber threats. In 2023, hackers will exploit the hidden dangers of communication vulnerabilities to steal data, disrupt services, and spy on users. This article will explain the main types of communication vulnerabilities, their impact, and how to protect yourself from them.
Communication Vulnerabilities in 2023: Unveiling the Hidden Dangers and Strategies to Evade Cyber Threats
2023 Security Vulnerabilities in Means of Communication
Communication is essential for individuals and professionals, but it is also exposed to many cyber threats. In 2023, several security breaches affected emails and messages, compromising the security of data, services, and users. These breaches showed the vulnerability of communication systems, which are exposed to increasingly sophisticated and targeted attacks. To protect themselves, users need to encrypt their data and communications with their own keys that they created and stored offline. One of the solutions that can help them achieve this is EviCypher NFC HSM technology by Freemindtronic.
The Reality of Security Breaches in Communication Systems
However, we wanted to highlight a disconcerting reality: users often found themselves defenseless against the hidden dangers of communication vulnerabilities in 2023 that festered beneath the surface for long periods of time. Unaware of these current, imminent or future risks, they unwittingly provided gateways to espionage activities, whether motivated by legitimate or malicious intentions. These vulnerabilities enabled a relentless cycle of cyber victimization, perpetuating the very threats they aimed to mitigate.
Another example, several reports by the Citizen Lab have revealed the existence and the use of Pegasus spyware developed by the Israeli company NSO Group, which sells its services to governments and private actors to spy on targets around the world. Moreover, several investigations by the consortium Forbidden Stories have revealed that more than 50,000 phone numbers have been selected as potential targets by NSO Group’s clients, including heads of state, journalists, human rights activists, etc.
Among the most recent examples of these vulnerabilities, we can mention the cyberattack against the US State Department, which was attributed to hackers linked to China.
Chinese hackers hacked 60,000 emails from the US State Department
In March 2023, Chinese hackers hacked 60,000 emails from the US State Department. Some of them were very sensitive to national security and foreign affairs. They used a Microsoft Exchange flaw named Log4Shell. This vulnerability allows hackers to remotely execute malicious code on servers that use this software. It affects millions of servers worldwide. Senator Mark Warner revealed the attack and criticized the lack of transparency and security of the State Department. He called for strengthening cooperation between government agencies and the private sector to cope with cyberthreats. This attack is part of a context of rising tensions between the US and China, who accuse each other of espionage and sabotage on cyberspace.
The other sensitive organs targeted by the attack
Besides the State Department emails, the attack also targeted other sensitive organs, such as:
- The Bureau of the Coordinator for Cyber Issues, which is responsible for coordinating the State Department’s efforts to prevent and respond to cyberattacks.
- The Bureau of Consular Affairs, which is in charge of issuing passports and visas, as well as protecting US citizens abroad.
- The Bureau of Intelligence and Research, which provides analysis and assessments on foreign policy and national security issues.
These sensitive organs hold confidential or personal information that could be used by the Chinese hackers for espionage, blackmail or sabotage. For example, the hackers could access the biometric data of visa applicants, the reports of intelligence agents or the action plans in case of crisis.
The security flaw exploited by the Chinese hackers
The most serious thing is that some servers that were hacked by the Chinese had not been updated with the patch released by Microsoft on December 10, 2022. This shows that the updates are not automatic and that they have to be installed manually. This also shows the lack of responsiveness and vigilance of the IT security managers. They let the Chinese hackers exploit this flaw before it was fixed by Microsoft, who released security updates. Indeed, this cyberattack shows the vulnerability of communication systems and the need to protect them effectively.
A Case of Satellite Messaging Security Vulnerability
Satellite messaging is a means of communication that allows the transmission of electronic messages or calls via a network of artificial satellites. It is used by professionals and individuals in areas with no cellular coverage or those seeking discreet communication. However, satellite messaging is not immune to security vulnerabilities that can compromise data confidentiality and integrity.
In September 2023, a team of cybersecurity researchers uncovered a significant security vulnerability in the Bullitt satellite messaging service. This vulnerability allowed hackers to read and modify messages sent and received by users, as well as access their personal information, including GPS coordinates and phone numbers. Hackers could also impersonate users by sending messages on their behalf. The vulnerability was found in the PubNub-Kotlin API used by the Bullitt Messenger app to manage communication between devices and the service’s servers. Despite alerting Bullitt, the service provider, about this vulnerability, the researchers received no satisfactory response.
This security flaw poses a high risk to satellite messaging users, as their data can be exposed or manipulated by hackers.
Security Vulnerabilities in Communication Systems: A Closer Look
2023 Security Flaws in Communication Channels is a paramount concern for individuals and organizations across the globe. Hackers frequently exploit vulnerabilities within communication protocols and services to launch attacks that can compromise data confidentiality, integrity, and availability. To illustrate the magnitude and gravity of this issue, we have compiled statistics based on our web research:
Security Vulnerabilities in Emails
Emails serve as a central vector for cyberattacks, representing a significant portion of security incidents, with up to 91% of reported incidents, as per cybermalveillance.gouv.fr. Among these email-targeted threats, ransomware attacks are the most prevalent, comprising 25% of reported security incidents. Additionally, it’s striking to note that 48% of malicious files attached to emails are Microsoft Office documents. These statistics underscore the critical importance of implementing robust security measures for emails to guard against evolving threats.
Furthermore, an analysis conducted by the Verizon Data Breach Investigations Report for 20232 highlights that emails remain the primary variety of malicious actions in data breaches, underscoring their continued relevance as a vector for cyberattacks.
However, it is essential to note that email-specific vulnerabilities can vary based on factors such as email protocol vulnerabilities, server configuration errors, human mistakes, among others.
Security Vulnerabilities in Encrypted Messaging Services
Encrypted messaging services like Signal, Telegram, or WhatsApp are not immune to security vulnerabilities, which can compromise message and file confidentiality, integrity, and availability. In March 2023, Cellebrite, an Israeli data extraction company, claimed to have successfully decrypted messages and files sent via Signal. In June 2023, Google disclosed a vulnerability in its RCS service that allowed hackers to send fraudulent messages to Android users, containing malicious links redirecting victims to compromised websites.
Security Vulnerabilities in Communication Protocols
Communication protocols such as SMTP, RCS, or SMS are also susceptible to security vulnerabilities that can enable hackers to intercept, modify, or spoof messages and calls. SS7 vulnerabilities involve attacks exploiting the vulnerabilities of the SS7 protocol, used to establish and terminate telephone calls on digital signaling networks. These attacks can allow hackers to intercept, modify, or spoof voice and SMS communications on a cellular network. In January 2023, a hacking group named Ransomware.vc launched a data extortion campaign targeting organizations using the Progress MOVEit file transfer tool. The hackers exploited an SS7 vulnerability to intercept verification codes sent via SMS to MOVEit users, gaining access to sensitive data. In February 2023, the Ukrainian power grid was hit by a new malware called Industroyer2, attributed to Russian hackers. The malware used an SS7 vulnerability to take control of network operator phone calls, disrupting electricity distribution in the country. In March 2023, Samsung suffered a data breach that exposed the personal and financial information of millions of customers. The breach was caused by an SS7 vulnerability that allowed hackers to access SMS messages containing online transaction confirmation codes.
An Overview of Security Vulnerabilities in Communication Systems
Communication systems exhibit various vulnerabilities, with each element susceptible to exploitation by hackers. These weaknesses can have severe consequences, including financial losses, damage to reputation, or national security breaches.
- Protocols: Communication protocols, like Internet Protocol (IP), Simple Mail Transfer Protocol (SMTP), Signaling System 7 (SS7), and Rich Communication Services (RCS), can contain security vulnerabilities. These vulnerabilities enable hackers to intercept, modify, or spoof communications on the network. For instance, an SS7 vulnerability allows hackers to eavesdrop on phone calls or read SMS messages on a cellular network.
- Services: Network services, such as messaging, cloud, streaming, or payment services, possess their own vulnerabilities. These vulnerabilities may permit hackers to access, modify, or delete data within the service. For instance, a vulnerability in an encrypted messaging service enables hackers to decrypt messages or files sent via the service.
- Applications: Software applications, including web, mobile, desktop, or IoT applications, are prone to security vulnerabilities. These vulnerabilities empower hackers to execute malicious code on a user’s device or gain control of the device itself. For example, a vulnerability in a web application allows hackers to inject malicious code into the displayed web page.
- Devices: Physical devices, such as computers, smartphones, tablets, or IoT devices, feature their own set of security vulnerabilities. These vulnerabilities can enable hackers to access the device’s data or functionalities. For instance, a vulnerability in a smartphone grants hackers access to the device’s camera, microphone, or GPS.
In conclusion, the multitude of security vulnerabilities in communication systems presents a significant challenge to all stakeholders. Protecting against these vulnerabilities and enhancing cybersecurity is essential to safeguard sensitive data and infrastructure.
How communication vulnerabilities exposed millions of users to cyberattacks in the past years
Communication is essential for our personal and professional lives, but it also exposes us to cyber threats. In the past years, hackers exploited the hidden dangers of communication vulnerabilities to steal data, disrupt services, and spy on users. These vulnerabilities affected software and services widely used, such as Log4j, Microsoft Exchange, Exim, Signal, Telegram, or WhatsApp. Some of these vulnerabilities have been fixed, while others remain active or in progress. The following table summarizes the main communication vulnerabilities in the past years, their impact, and their status.
| Name of the breach | Type of breach | Impact | Status | Date of discovery | Date of patch |
|---|---|---|---|---|---|
| Log4j | Command injection | Control of servers and Java applications | Fixed | November 24, 2021 | December 18, 2021 |
| Microsoft Exchange | Remote code execution | Data theft and backdoor installation | Fixed | March 2, 2021 | |
| Exim | Multiple vulnerabilities | Control of email servers | June 5, 2020 | ||
| Signal | Denial of service | Blocking of messages and calls | Fixed | May 11, 2020 | May 15, 2020 |
| Telegram | Deserialization | Access to messages and files | Fixed | January 23, 2021 | |
| QR code spoofing | Account hacking | Fixed | October 10, 2019 | ||
| File-based XSS | Code injection | Execution of malicious code in the browser | Not fixed | December 17, 2020 | N/A |
| RCS | QR code spoofing | Interception, modification or spoofing of messages and calls | Not fixed | June 17, 2020 | N/A |
| SMS | SIM swap fraud | Account takeover and identity theft | Active or in progress | ||
| MMS | Stagefright vulnerability | Remote code execution and data theft | Fixed | July 27, 2015 | August-September 2015 |
| SolarWinds Orion | Supply chain compromise | Data theft and backdoor installation | Fixed | December 8, 2020 | February 25, 2023 |
| API PubNub-Kotlin | Privilege escalation by deserialization of untrusted data | Arbitrary command execution on SolarWinds Platform website | Fixed | February 8, 2022 | April 19, 2023 |
| SS7 | Multiple vulnerabilities | Data theft, interception, modification or blocking of communications, location tracking or spoofing, fraud | Active or in progress | 2014 | N/A |
This table provides a concise overview of the hidden dangers of communication vulnerabilities in 2023, their types, impacts, and current statuses.
EviCypher NFC HSM: The technology that makes your communications invulnerable to security breaches
Security vulnerabilities in the means of communication pose a high risk to users, including satellite messaging, as their data can be exposed or manipulated by hackers. Therefore, effective protection against this threat is essential. This is precisely where the EviCypher NFC HSM technologies mentioned in this article come in as an innovative and secure solution.
EviCypher NFC HSM Technology for Messaging Protection
EviCypher NFC HSM technology is a solution that enables contactless encryption and decryption of data using an NFC card. It employs a hardware security module (HSM) that securely stores encryption keys. It is compatible with various communication services, including emails, SMS, MMS, satellite messaging, and chats.
To use EviCypher NFC HSM technology, simply pair the NFC Card, to an NFC-enabled Android phone and activate it with your fingerprint. Messages sent and received through messaging services are encrypted and decrypted using the NFC card. Only the card owner can access their messages and files. No one can intercept or alter them, even if the service is compromised by a security vulnerability.
EviCypher NFC HSM technology offers optimal protection for commincation, ensuring data confidentiality and integrity. It also safeguards against other types of security vulnerabilities that may affect communication methods, such as Log4Shell or SolarWinds. It is a simple, effective solution that requires no change in user habits.
What is EviCypher NFC HSM technology?
EviCypher NFC HSM technology is a contactless encryption technology that uses hardware security modules (HSM) devices that communicate via NFC (Near Field Communication) protocols. These devices are EviTag and Evicard, which are small and portable devices that can be attached to a keychain or a card holder. They allow users to store and manage their keys and secrets securely, without relying on third-party services or cloud storage.
How does EviCypher NFC HSM technology work?
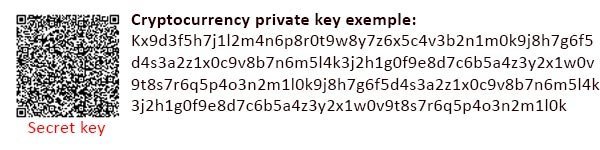
EviCypher NFC HSM technology works by encrypting and decrypting data and communications with the user’s own keys that they created and stored offline. The user can use the devices for various applications, such as encrypting emails, messages or files.
To use NFC HSMs, the user must first pair it with their phone. He chooses the option of encryption or decryption on his phone, writes or reads his messages on his phone. Encryption and decryption operations are performed from the NFC HSM itself, without exposing keys or secrets to the phone. The same operation is available on computer via a phone-paired web extension and using the NFC HSM.
Why is EviCypher NFC HSM technology secure and reliable?
EviCypher NFC HSM technology is integrated into a hardware security module that stores encrypted secrets, such as encryption keys, in the highly secure NFC eprom memory. It enables to encrypt contactless communications upstream, in post-quantum AES 256, before sending them. It is thus secure and reliable, because it encrypts the data before transmitting them without ever keeping the message in plain text.
How can EviCypher NFC HSM technology protect you from security breaches?
EviCypher NFC HSM technology can protect you from security breaches by encrypting your data and communications in advance in volatile memory before sending them encrypted without ever keeping the message in clear automatically destroyed and replaced by its encrypted version in AES 256 symmetry considered post quantum. Thus, even if there are security flaws the messages and emails and their attachments remain always encrypted. This can be done from an Android NFC phone and/or from the Freemindtronic extension.
This way, you can avoid being exposed to past, present or future security vulnerabilities, since the encryption is done on the device itself, without exposing the keys or secrets to the phone or computer. Even if your phone or computer is compromised by a hacker or a spyware, they cannot access your data or messages in clear text. Only you can decrypt them with your device and your PIN code.
EviCypher NFC HSM technology is an innovative solution that offers a high level of security and privacy for your communication systems. It is developed by Freemindtronic, an Andorran company specialized in NFC security. It is based on EviCore NFC HSM technology, which is a hardware security module that combines hardware encryption and NFC communication protocols.
In conclusion, the EviCypher NFC HSM technology is integrated into a hardware security module that stores encrypted secrets, such as encryption keys, in the highly secure NFC eprom memory. It allows to encrypt contactless communications upstream, in post-quantum AES 256, before sending them. It is thus secure and reliable, because it encrypts the data before transmitting them without ever keeping the message in plain text.