Crypto Wallet Security by Jacques Gascuel: This article will be updated with any new information on the topic.
How EviSeed and EviVault Could Thwart a $41 Million Crypto Heist
Imagine waking up one day to discover that your crypto wallet has been hacked. As a result, all your funds are gone. Unfortunately, this is exactly what happened to more than 50,000 StakeCube users who were staking cryptocurrencies. They lost a massive $41 million in a cyberattack by North Korean hackers. In this article, we will demonstrate how EviSeed and EviVault technologies, developed by Freemindtronic, could have thwarted this theft.
EviSeed and EviVault NFC HSM Technologies could have prevented the $41 million crypto theft by North Korean hackers.
Cryptocurrencies have gained immense popularity, but they have also become increasingly vulnerable to theft. Hackers actively search for vulnerabilities in cryptocurrency storage and exchange platforms, leading to them stealing millions of dollars from users. North Korean hackers recently stole $41 million from the Stake platform, resulting in a high-profile case. In this article, we explore how EviSeed and EviVault NFC HSM technologies could have prevented this theft.
The Significance of Mnemonic Phrases and Private Keys
Before delving into the advantages offered by EviSeed and EviVault, let’s first understand the significance of mnemonic phrases and private keys in cryptocurrency wallet security.
Understanding Mnemonic Phrases and Private Keys’ Role in Cryptocurrency Wallet Security
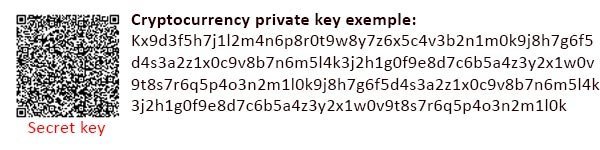
A mnemonic phrase consists of words used to generate and restore your private key, granting access to your cryptocurrency wallet and enabling transactions.Typically composed of 12, 18, or 24 words selected from a standardized list known as BIP39, a mnemonic phrase might look like:
apple, banana, lemon, orange, strawberry, kiwi, pineapple, mango, melon, watermelon, cherry, plum.
This mnemonic phrase is of utmost importance as it represents the sole means of recovering your cryptocurrency wallet in case of loss or theft of the storage device (e.g., smartphone, computer, USB key). Users must meticulously back it up and should never share it with anyone.
A private key, on the other hand, consists of a sequence of numbers and letters corresponding to the mnemonic phrase. It is employed for signing transactions and confirming ownership of the cryptocurrency wallet. A private key example is:
Securing Cryptocurrency Wallets
Now that we’ve examined the importance of mnemonic phrases and private keys, let’s discuss the risks associated with traditional backup methods and how EviSeed and EviVault technologies provide enhanced security solutions.
The Risks of Traditional Backup Methods for Mnemonic Phrases and Private Keys
Nevertheless, these methods have several drawbacks when it comes to cryptocurrency wallet security. Most cryptocurrency users choose to back up their mnemonic phrases and private keys using paper or metal media:
- Impracticality: Manually writing or engraving mnemonic phrases and private keys can be tedious and prone to errors.
- Inefficiency: Retrieving a cryptocurrency wallet or making transactions requires typing or memorizing the mnemonic phrase and private key, which can be time-consuming and cumbersome.
- Lack of Durability: Paper and metal supports degrade over time, can be lost, damaged, or susceptible to environmental factors like fire, water, and physical harm.
- Vulnerability: Physical and logical attacks are potential risks. For instance, if someone finds the support containing the mnemonic phrase and private key, they can access the cryptocurrency wallet and transfer funds to another address. If the support is connected to the internet, it can be infected with malware capable of stealing the mnemonic phrase and private key.
Why is Crypto Wallet Security Important?
Crypto wallet security involves protecting your crypto assets from unauthorized access, theft, or loss. Crypto wallet security involves two main components: your mnemonic phrase and your private key. Your mnemonic phrase is a sequence of words that is used to generate and restore your private key, which is the key that allows you to access your crypto wallet and make transactions. The mnemonic phrase and the private key are very important, because they are the only way to recover your crypto wallet in case of loss or theft of the support on which it is stored (smartphone, computer, USB key, etc.). You must therefore backup them carefully and never disclose them to anyone.
Crypto wallet security is important because cryptocurrencies are valuable and vulnerable to attacks. Hackers can exploit vulnerabilities in platforms storing and exchanging cryptocurrencies, employ phishing, malware, or social engineering to deceive users into disclosing their mnemonic phrases or private keys. If hackers get access to these keys, they can transfer the funds to their own addresses and make them untraceable. Therefore, you need to choose reliable and secure backup solutions for your mnemonic phrases and private keys, such as EviSeed and EviVault.
Enhancing Crypto Wallet Security with EviSeed
Now let’s find out how EviSeed technology enhances the security of the crypto wallet. It offers a secure alternative to traditional backup methods.
Simplicity and Automation for Enhanced Crypto Wallet Security
EviSeed simplifies crypto wallet creation, completing all tasks within seconds. It efficiently manages and encrypts mnemonic phrases and their corresponding private keys within the NFC HSM. This automation extends to generating public keys and addresses, ensuring robust Crypto Wallet Security. Importantly, this process occurs offline, shielding sensitive data from exposure. Users can effortlessly monitor their balances using their paired Android NFC smartphones.
Rigorous Security Measures: Protecting Your Crypto Wallet Security
EviSeed employs cutting-edge AES-256 post-quantum encryption in conjunction with key segmentation. Even if malicious actors gain physical access to the NFC HSM, decrypting the mnemonic phrase remains an insurmountable challenge without access to encryption keys and corresponding segments. The device features five segmented encryption keys, bolstered by up to four additional authentication criteria for each wallet, significantly enhancing Crypto Wallet Security. These criteria encompass geographic zones, fingerprints, BSSIDs (Wi-Fi network identifiers), and UIDs of paired Android NFC smartphones.
Multi-Layered Protection: Safeguarding Your Crypto Wallet Security
Access to the NFC HSM is exclusively possible via the Freemindtronic application, seamlessly integrating EviSeed technology for added security, reinforcing your Crypto Wallet Security. In the unlikely event of theft, attackers would require knowledge of all unique authentication criteria to decrypt the private key. Moreover, EviSeed generates an encrypted QR code containing your mnemonic phrase. This QR code can be printed, shared, sent, or used for backup between NFC HSMs, employing RSA 4096 encryption, further enhancing your Crypto Wallet Security. EviSeed also enables hassle-free crypto wallet creation, including an automatic backup of BIP39 seed phrases within NFC HSMs, alongside your private key. The technology effortlessly generates public keys and addresses, allowing you to conduct operations securely, all while maintaining the confidentiality of your seed phrase and private key.
Unmatched Durability for Uncompromising Crypto Wallet Security
NFC HSM devices used by EviSeed are engineered for resilience, with military-grade coatings that protect against water, extreme temperatures ranging from -40°C to +120°C, shocks, and scratches. These devices boast an impressive lifespan, powered by energy recovery from the paired Android smartphone’s NFC signal, ensuring long-term Crypto Wallet Security.
By integrating EviSeed NFC HSM technology into their crypto security strategy, users can significantly bolster the safety of their assets, mitigating the vulnerabilities associated with conventional backup methods, and fortifying their Crypto Wallet Security.
How EviVault NFC HSM Enhances Crypto Wallet Security
Now, let’s explore the remarkable capabilities of EviVault NFC HSM and how it elevates crypto wallet security to unprecedented levels.
A Distinctive Approach to Safeguarding Crypto Wallets
EviVault NFC HSM stands apart as a distinct technology from EviSeed NFC HSM. Its primary objective is to secure cryptocurrency-derived private keys physically and offline, all within a lightning-fast process of fewer than four seconds. This is achieved by scanning the QR code of the derived private key, ensuring swift and robust Crypto Wallet Security.
Error-free backup and storage
EviVault simplifies the process further by allowing users to securely record the BIP39-generated recovery phrase, and automatically store it encrypted in an NFC HSM. The user can easily select without using the keyboard assisted by automatic error control system. This has the effect of further strengthening the security of the cryptographic wallet by preventing the backup process in case of error. Thus, all these protection mechanisms are airtight to physical, logical or online threats.
Streamlined Security for Crypto Wallets
EviVault introduces a series of advantages over conventional methods that enhance Crypto Wallet Security comprehensively:
- Simplicity: Users no longer need to manually enter the derived private key. The cumbersome practice of writing, engraving, or copying private keys in plain text, which can be susceptible to malicious third parties, becomes obsolete. Instead, users can swiftly scan the encrypted QR code of the derived private key, created by EviSeed technology, and store it securely within an EviVault NFC HSM in under four seconds.
- Efficiency: Gone are the days of memorizing or typing private keys, or risking exposure by storing them in unencrypted forms. By merely passing their Android NFC smartphone paired with the NFC HSM under the NFC antenna, users can view the private key or its compressed/uncompressed public address. The technology even allows for secure sharing of private keys and encrypted public addresses via a pair of RSA 4096 keys, all without exposing sensitive data to the user’s phone or computer.
- Durability: EviVault stands out with its robust design, devoid of connectors, screens, batteries, buttons, or any other wear-prone components. It offers a lifetime of service, powered by energy recovery from the paired Android smartphone’s NFC signal. Furthermore, EviVault NFC HSM devices, like their EviSeed counterparts, exhibit resistance to water, extreme temperatures ranging from -40°C to +120°C, shocks, and scratches, thanks to a military-grade component coating, ensuring top-tier Crypto Wallet Security in harsh environments.
- Unyielding Security Measures: EviVault incorporates EviCore NFC HSM technology, featuring post-quantum AES-256 encryption and advanced key segmentation. Even if potential attackers gain physical access to the NFC card, decrypting the private key remains an insurmountable task without access to the encryption keys and corresponding segments, each exceeding 256 bits in complexity. Additionally, users can bolster Crypto Wallet Security by adding up to four segmented authentication criteria for each wallet, including geographical zones, fingerprints, BSSIDs (Wi-Fi network identifiers), or UIDs of paired Android NFC smartphones. Access to the NFC card remains exclusive through the Freemindtronic application, which incorporates EviVault technology, fortifying Crypto Wallet Security with an additional layer of protection.
Incorporating EviSeed or EviVault NFC HSM technology into their crypto security strategy empowers cryptocurrency users to elevate the security of their holdings significantly. These technologies not only eliminate vulnerabilities associated with conventional backup methods but also provide formidable protection against both physical and digital threats, ensuring unparalleled Crypto Wallet Security in today’s dynamic digital landscape.
Summary of Enhanced Cryptocurrency Security
The Crucial Role of Crypto Wallet Security
In summary, EviSeed and EviVault NFC HSM technologies offer innovative solutions to enhance cryptocurrency wallet security, safeguarding digital assets from physical and digital threats.
Protecting Your Investments
Given the increasing adoption of cryptocurrencies, it’s essential to invest in secure storage solutions such as EviSeed and EviVault for effective investment protection.
How a Flaw in the Unencrypted Private Key Backup System Allowed the North Korean Hackers to Steal $41 Million in Crypto from StakeCube and How EviSeed and EviVault Could Have Prevented It
March 2023 witnessed a group of North Korean hackers, Lazarus, or APT38. They stole $41 million in cryptocurrencies from StakeCube, an online casino and betting platform. These hackers took advantage of a flaw in the backup system; it stored unencrypted private keys on a centralized and insecure server. These attackers copied the private keys of more than 50,000 users from the server. Subsequently, they transferred the funds to their own addresses using these keys. These attackers evaded detection for several months with great organization and methodology. These attackers also concealed and laundered the stolen funds to make them hard to trace.
This incident emphasizes the significance of cryptocurrency wallet security and the necessity to select dependable and secure backup solutions for private keys and mnemonic phrases. In this article, we will show you how EviSeed and EviVault, two technologies developed by Freemindtronic, can help you protect your crypto assets from hackers.
Lazarus-affiliated North Korean hackers are renowned for their sophisticated attacks. In the case of the StakeCube theft, they demonstrated a high level of organization and methodology. However, EviSeed and EviVault’s advanced security features could have acted as formidable barriers, enhancing crypto wallet security.
- Advanced encryption: EviSeed uses post-quantum AES-256 encryption, which makes it virtually impossible for hackers to decrypt the mnemonic phrases and private keys stored, even if they physically access the device.
- Key segmentation: EviSeed’s key segmentation would have added another layer of protection. Without knowledge of the encryption keys and corresponding segments, which are greater than 256 bits, attackers couldn’t access the private keys.
- Authentication criteria: Users can set up to four additional segmented authentication criteria for each wallet, including geographic zones, fingerprints, BSSID (Wi-Fi network identifiers) or UID of paired Android NFC smartphones. This would have made it extremely challenging for hackers to gain access.
- Offline storage: EviSeed works offline, ensuring that mnemonic phrases and private keys are never exposed to the internet, a common entry point for hackers.
Cyber-Attack-Proof Crypto Wallet Security via EviVault
Cryptocurrencies are valuable digital assets that need protection from hackers or accidents. But how can you secure your crypto wallet effectively and easily? The answer is EviVault NFC HSM, an innovative solution that uses NFC technology to encrypt and backup your private keys.
You know how difficult it can be to back up and encrypt your private keys with traditional methods. This is also where the EviVault NFC HSM technology comes in. Let’s take a look at how EviVault improves crypto wallet security against potential threats, such as North Korean hackers. In the context of protecting your digital assets, we will discover how EviVault combines several protection measures:
- Fortifying Physical Security: EviVault’s resolute physical security measures would have posed an insurmountable challenge to hackers. The private keys, nestled within the NFC card, would remain impenetrable.
- Rampart of Encryption and Key Segmentation: EviVault would have placed attackers in a cryptographic deadlock. It employs post-quantum AES-256 encryption and meticulous key segmentation. Decrypting the private keys would become an exercise in futility.
- Enhancing Authentication Criteria: EviVault introduces a layer of complexity by incorporating additional authentication criteria, such as geographic zones and fingerprints. These sophisticated layers would have further confounded hackers, rendering their attempts futile.
- EviCore Integration: An Extra Layer of Security Access to the NFC card is exclusively governed by the Freemindtronic application, intricately woven with EviVault technology. This integration bestows an added layer of security. It ensures that even if the NFC HSM were stolen, attackers would be stymied by the intricate web of authentication criteria required to decrypt the private key.
We can’t rewrite history or reverse the result of the Stake hack, but it’s clear that EviSeed and EviVault NFC HSM technologies are strong advocates. These are indispensable tools to strengthen the security of the crypto wallet in today’s digital landscape. They act as your shield against potential threats. Note that the Keepser product an NFC Cold Wallet embedding EviVault NFC HSM technology from Freemindtronic click here to learn more.
Official Sources
To support the information presented in this article, we have used the following official sources:
- [FBI press release] that attributes the theft to Lazarus, a North Korean state-sponsored cybercrime unit.
- [IMF report] that analyzes the risks and challenges related to crypto-assets and proposes recommendations to strengthen supervision and international cooperation.
- [Stake.com official website], the online casino and betting platform victim of the theft, that explains how the theft occurred and how they plan to reimburse their users.
- [Freemindtronic official website], the company that developed EviSeed and EviVault technologies, that presents the benefits and features of these secure backup solutions for private keys and mnemonic phrases.