2022, CyberStealth, Eurosatory, Press release
EviStealth Technology at Eurosatory 2022
EviStealth, its exhibition at Eurosatory 2022
EviStealth stealth data exchange
EviStealth
1
Anonymization
Stealth system to transmit sensitive data with a click from a phone
2
Without compromises
Encrypted data exchange without risk of compromise
3
Untraceable
Leaves no trace in computer and telephone systems
About the event
Eurosatory, Paris, Hall 5B booth C178 from June 13th to June 17th 2022: Freemindtronic will present for the very first time its EviStealth technology. It offers users many usage possibilities from smartphone devices, such as the camera, the microphone, the gyroscope, the GPS, the digital fingerprint, as well as NFC’s means of communication, Bluetooth, Wi-Fi and GSM. The sender transmits, instantly and without leaving any traces, different types of encrypted data (photo, video, text, sound) with the keys of the recipients stealthily, anonymously and secured.
Press ReleaseThe Andorran start-up Freemindtronic Ltd., conceiver and creator of security, cyber-security and counterespionage systems is also specialised in contactless technology (NFC).
The chosen logo for the new technological milestone shows the idea of the solution. Indeed, the Megascops, also named scops owl, is a master in the art of camouflage.
The solution is mainly designed to significantly limit the risk for senders to be compromised and/or the recipients, as well as of the sensitive data transfer.
Press ReleaseThe solution is mainly designed to significantly limit the risk for senders to be compromised and/or the recipients, as well as of the sensitive data transfer.
EviStealth possesses different anonymization implementations such as taking pictures through the digital fingerprint of the smartphone. Therefore, it is the user’s experience that is at the heart of this innovation.
DISCRETION, SIMPLICITY AND QUICK USAGE OF THE SOLUTION IN ONE CLICK
1 ) The discretion is shown, for instance, thanks to the possibility to take pictures while faking that you are making a phone call. The sender has, to do this, a function that is shown on the screen darkened by a discreet framing viewer with the telephone placed close to the ear.
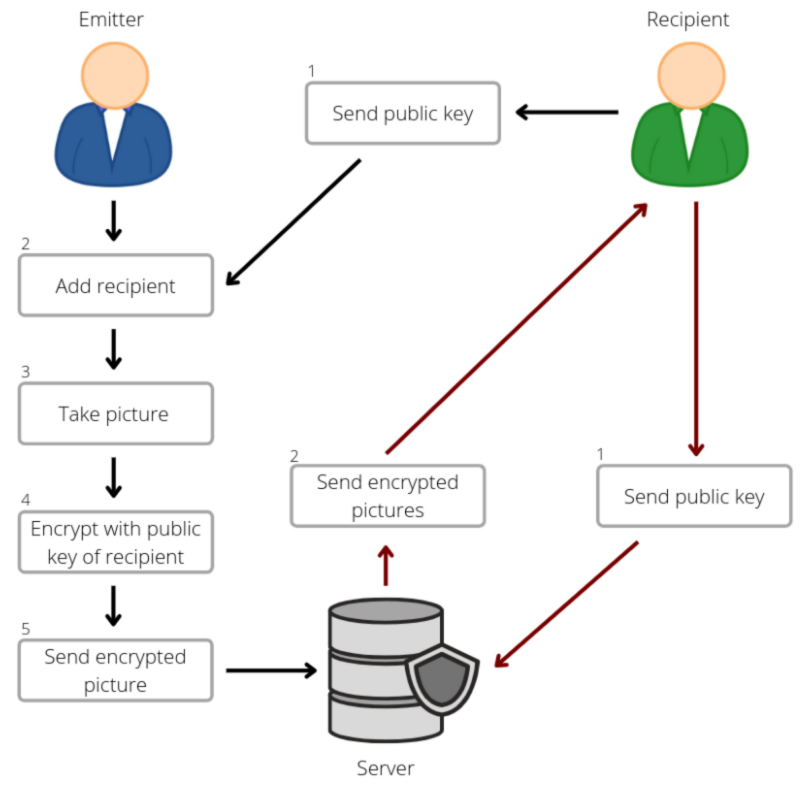
2) The simplicity is found in the different stages of the solution. The sender sends, by a simple click, his encryption key to the recipient, who adds it to his phone in one click. Then, the recipient is authenticated. The recipient’s encription key can also be added via a Freemindtronic’s contactless NFC device.
Press ReleaseThe recipients, as well as the senders, have different possibilities to store their encryption and decryption keys. They can be stored and encrypted in the EviStealth application or in an NFC device. For this latter, the physical externalization of the keys grealtly increases the anonymity, the stealth and the reduction of some compromising risks.
Any transferred data is stored neither on the sender’s phone, nor on the recipient’s one. The data are stored encrypted in a server, temporary or permanently.
3 / Untraceable: Quick usage is crucial. The sender stealthily takes a photo and transfers it instantly to an authenticated recipient, without leaving digital traces, neither in the sender’s system, nor in the recipient’s computer system.
You will understand it with the EviStealth solution, transfer videos, audio messages or photos without leaving any trace, from your phone to your recipient’s phone.
Contact for a meeting on the Freemindtronic stand at Eurosatory
Press release
Multi-language download links for press releases.
