EviSCP HSM: a secure communication protocol based on patents and ZKP
EviSCP HSM is a secure communication protocol developed by Freemindtronic, which relies on patents, especially segmented key authentication. EviSCP HSM offers an exceptional level of security for sensitive data, using NFC HSM or HSM multi-support devices as hardware security modules. EviSCP transforms any existing communication protocol into a secure communication channel without a server or a database, using random and segmented keys, anti-counterfeiting and anti-replay mechanisms, and advanced cryptographic algorithms. EviSCP also meets the three criteria of the Zero Knowledge Proof (ZKP) protocol: completeness, soundness and zero knowledge. EviSCP has many advantages over existing secure communication solutions, such as application flexibility, bidirectional communication, adaptability to various domains, and personalized security control. EviSCP is an innovative and efficient solution to secure communication between portable electronic devices.
What is EviSCP HSM?
EviSCP HSM is an acronym for “Evi Secure Communication Protocol Hardware Security Module”. It is a secure communication protocol that uses the EviCore HSM technology to manage all types of asymmetric keys, including OpenPGP. This technology allows the user to freely choose the type of algorithm he wants to use (RSA 1024, 2048, 3072, 4096 or ECC). The user can also import a pair of asymmetric keys that he already has, whether it is OpenPGP or not. This technology also allows the user to randomly generate a pair of asymmetric keys with a high degree of randomness.
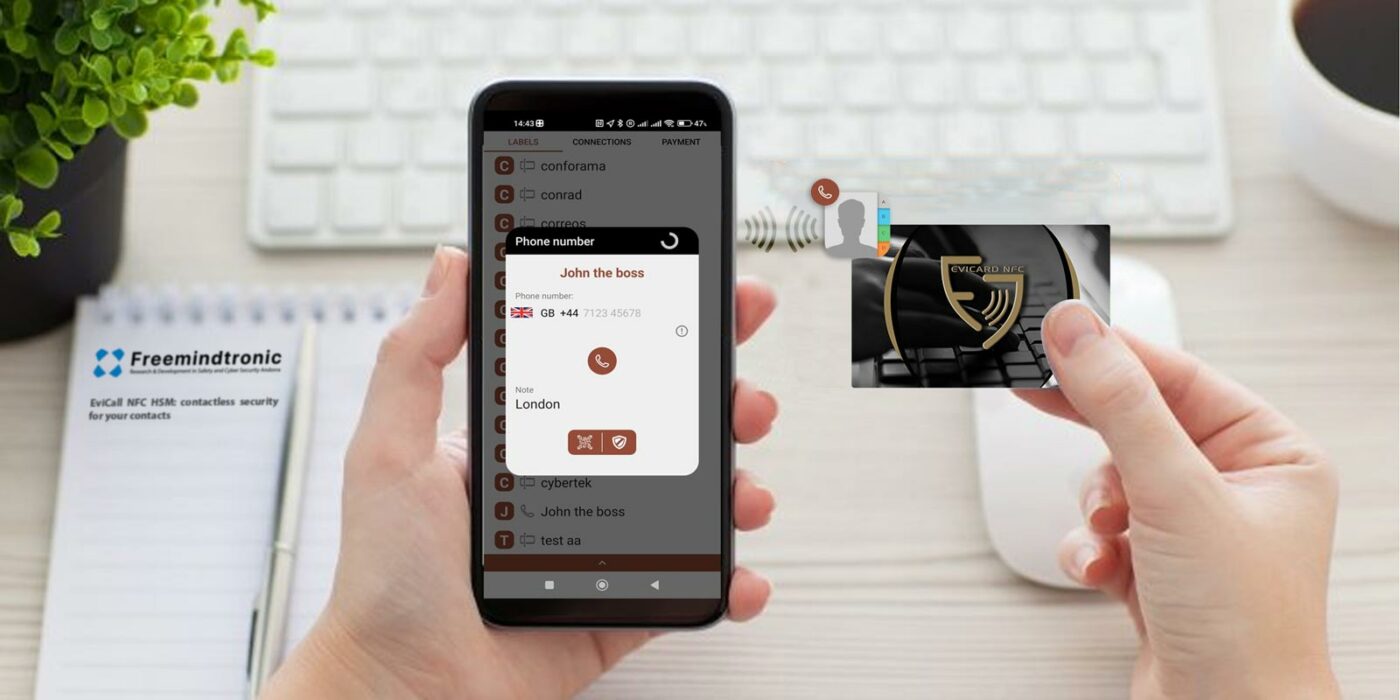
EviSCP HSM transforms any existing communication protocol such as NFC, LAN, WAN, satellite, GSM, Wi-Fi, Bluetooth, into a secure communication channel between portable electronic devices (such as HSM smartphones, NFC HSM or other HSM or NFC HSM storage devices EviKey or EviDisk). This secure communication channel works without a server or a database of secrets, thus greatly improving security.
The principle of the secure communication channel is to create an encrypted tunnel between two parties wishing to communicate securely. This tunnel allows to establish a private and confidential connection, which cannot be intercepted or altered by third parties. The EviSCP protocol uses encryption and authentication keys generated randomly and stored in the NFC HSM or HSM multi-support devices, which are tamper-proof hardware security modules. These keys are used to encrypt and decrypt the data exchanged between the parties, as well as to verify their identity and integrity.
EviSCP HSM also uses the Zero Knowledge Proof (ZKP) protocol to prove the truthfulness of statements without revealing any information beyond the simple fact of the truth. The ZKP is a form of cryptography that allows one party (the prover) to prove to another party (the verifier) that a statement is true, without revealing any information beyond the simple fact of the truth of the statement. The ZKP must meet three criteria to be valid:
- Completeness: A ZKP protocol is said to be complete if, when the statement is true, the prover can always convince the verifier with a high probability.
- Soundness: A ZKP protocol is said to be sound if, when the statement is false, the prover cannot convince the verifier with a non-negligible probability.
- Zero knowledge: A ZKP protocol is said to be zero knowledge if the verifier learns no information other than the truthfulness of the statement.
EviSCP HSM uses ZKP to prove that the parties have the secret key segments necessary to access the encrypted data or the NFC HSM or HSM multi-support devices, without revealing these segments or the associated authentication factors. EviSCP HSM also uses ZKP to prove that the parties have the asymmetric keys necessary to establish the encrypted tunnel, without revealing these keys or the data exchanged. EviSCP HSM finally uses ZKP to prove that the NFC HSM or HSM multi-support devices are authentic and intact, without revealing their signature or their content.
How does EviSCP HSM work?
EviSCP HSM works as follows:
- Use of portable electronic devices containing secret key segments: EviSCP uses portable electronic devices, such as smartphones HSM, NFC HSM or other storage devices HSM or NFC HSM EviKey or EviDisk, as storage and authentication supports for secret key segments. These secret key segments are associated with different authentication factors, such as biometric data, PIN codes, passwords or device identifiers. The secret key segments are generated randomly and stored encrypted in AES 256 in the NFC HSM or HSM multi-support devices, which are protected against physical and logical attacks.
- User authentication and access authorization: To access the encrypted data or the NFC HSM or HSM multi-support devices, the user must authenticate using the authentication factors corresponding to the secret key segments. For example, if a secret key segment is associated with a biometric data, the user must scan his fingerprint to authenticate. If a secret key segment is associated with a PIN code, the user must enter his PIN code to authenticate. If a secret key segment is associated with a device identifier, the user must use the corresponding device to authenticate. Only the parties who have the right set of authentication factors can access the encrypted data or the NFC HSM or HSM multi-support devices.
- Use of asymmetric and symmetric keys generated randomly and stored encrypted in AES 256 in NFC HSM or HSM: EviSCP can work according to two methods, symmetric or asymmetric, left to the discretion of the user depending on the level of security he wishes to use. According to the standard method of using randomly generated asymmetric key pairs auto-stored encrypted in the HSM used to establish encrypted tunnels between the parties by sharing their public keys. Indeed, advantageously with EviSCP HSM OpenPGP, there is no limit to the number of tunnels that can be created with different asymmetric keys. The encrypted private asymmetric keys are also secured by segmentation. The user can choose to create tunnels by symmetric encryption in AES 256 with segmented key with addition of trust criteria. He just needs to use the asymmetric EviSCP channel to share between HSM and/or NFC HSM the symmetric key subject to non-modifiable, non-repudiable trust criteria. Then, in the same way as for the asymmetric encrypted channel, the user will freely choose to use a symmetric encrypted channel standard or OpenPGP with auto integrity control of the symmetric key by auto signature.
- Enhanced security thanks to segmented key authentication and key confidentiality: EviSCP HSM uses a patented mechanism of segmented key authentication, which ensures that only authorized parties can access the encrypted data. The secret key segments are associated with different authentication factors, such as biometric data, PIN codes, passwords or device identifiers. The keys are stored in the NFC HSM or HSM multi-support devices, which are protected against physical and logical attacks.
- Secure storage of keys in NFC HSM or HSM multi-support devices: EviSCP HSM uses NFC HSM or HSM multi-support devices as hardware security modules to store encryption and authentication keys. The NFC HSM or HSM multi-support devices are portable electronic devices, such as NFC HSM EviKey or EviDisk, which are designed to resist invasive or non-invasive attacks. The keys are randomly generated and stored encrypted in AES 256 in the NFC HSM or HSM multi-support devices, ensuring their security and integrity.
- Protection against counterfeiting and replay attacks: EviSCP HSM integrates anti-counterfeiting and anti-replay measures, which prevent falsification or modification of data or NFC HSM or HSM multi-support devices. These measures include signature mechanisms based on asymmetric keys RSA-4096, OpenPGP or other types chosen by the user , which guarantee the authenticity and integrity of data and devices. They also include the use of random and unique keys for each communication session, as well as a data integrity verification mechanism, which prevent reuse or alteration of exchanged data.
- Application flexibility on different communication protocols: EviSCP HSM transforms any existing communication protocol such as NFC, LAN, WAN, satellite, GSM, Wi-Fi, Bluetooth, into a virtual VPN between portable electronic devices. This virtual VPN works without server or database of secrets, making it compatible with any type of network or device. EviSCP HSM thus allows to secure communication between distant or isolated parties, without depending on the type or level of security of the underlying communication protocol.
- Bidirectional communication without bandwidth limitation: EviSCP HSM allows bidirectional communication between parties, without bandwidth or latency limitation. The parties can exchange encrypted and authenticated data in real time, without fear of being intercepted or altered by third parties. EviSCP HSM thus offers a smooth and secure communication experience.
- Adaptability to various domains, including payment and health: EviSCP HSM can be applied in various contexts, where data security is crucial. For example, EviSCP HSM can be used to secure financial transactions, using NFC HSM or HSM multi-support devices as secure payment means. EviSCP HSM can also be used to protect personal health information, using NFC HSM or HSM multi-support devices as secure storage supports. EviSCP HSM thus meets the strict security requirements imposed by standards such as PCI DSS, HIPAA or GDPR.
- Personalized security control thanks to trust criteria defined by the user: EviSCP HSM allows the user to define trust criteria adapted to his specific needs. These criteria determine the authentication factors required to access the encrypted data or NFC HSM or HSM multi-support devices. The user can thus choose the level of security he wants to apply, depending on the context and risk. EviSCP HSM thus offers a customizable and flexible security solution.
Data sheet
| Feature | Description |
|---|---|
| Product name | EviSCP HSM |
| Developer | Freemindtronic |
| Product type | Secure communication protocol |
| Patents | Segmented key authentication (WO2018154258), Salting system (WO2010086552), Access control (WO2017129887), Black box monitoring (WO2010086552) |
| Technology used | EviCore HSM |
| Types of asymmetric keys | RSA 1024, 2048, 3072, 4096 or ECC ; OpenPGP or other types imported by the user |
| Symmetric algorithm | AES 256 standard and AES 256 OpenPGP |
| Portable electronic devices | Smartphones HSM, NFC HSM or other storage devices HSM or NFC HSM EviKey or EviDisk |
| Compatible communication protocols | NFC, LAN, WAN, Satellite, GSM, Wi-Fi, Bluetooth, VPN |
| Main advantages | Enhanced security, secure storage of keys, protection against attacks, application flexibility, bidirectional communication, adaptability to various domains, personalized security control |
| Zero Knowledge Proof (ZKP) protocol | Completeness, soundness and zero knowledge |
What are the applications of EviSCP HSM?
EviSCP HSM is a versatile and adaptable solution that can be applied in various domains and contexts, where data security is crucial. Some of the possible applications of EviSCP HSM are:
- Secure financial transactions: EviSCP HSM can be used to secure financial transactions, such as online payments, transfers, or withdrawals, using NFC HSM or HSM multi-support devices as secure payment means. EviSCP HSM ensures that the transaction data is encrypted and authenticated, and that the parties are verified and authorized. EviSCP HSM also protects against fraud, counterfeiting, and replay attacks, by using random and unique keys for each transaction, and by monitoring the integrity and authenticity of the devices.
- Secure personal health information: EviSCP HSM can be used to protect personal health information, such as medical records, prescriptions, or test results, using NFC HSM or HSM multi-support devices as secure storage supports. EviSCP HSM ensures that the health data is encrypted and accessible only by authorized parties, such as doctors, patients, or insurers. EviSCP HSM also protects against data breaches, theft, or loss, by using segmented key authentication and trust criteria defined by the user.
- Secure remote work: EviSCP HSM can be used to secure remote work, such as telecommuting, freelancing, or collaboration, using portable electronic devices as communication means. EviSCP HSM ensures that the work data is encrypted and exchanged securely between the parties, regardless of the type or level of security of the underlying communication protocol. EviSCP HSM also protects against eavesdropping, interception, or modification, by using ZKP to prove the identity and integrity of the parties and devices.
- Secure IoT devices: EviSCP HSM can be used to secure IoT devices, such as smart home appliances, wearables, or sensors, using NFC HSM or HSM multi-support devices as security modules. EviSCP HSM ensures that the IoT data is encrypted and transmitted securely between the devices and the cloud or other platforms. EviSCP HSM also protects against hacking, tampering, or spoofing, by using anti-counterfeiting and anti-replay measures, and by controlling access to the devices.
These are just some examples of the applications of EviSCP HSM. There are many other potential use cases for this innovative and efficient solution.
What are the statistics on secure communication protocols?
This is a relevant question for EviSCP. According to a study by the University of Cambridge, secure communication protocols are widely used in various domains, such as e-commerce, e-government, e-health, e-learning, and e-voting. The study estimates that more than 80% of the web traffic is encrypted with secure communication protocols, such as HTTPS, SSL/TLS, SSH, or IPsec. However, the study also identifies some challenges and limitations of these protocols, such as performance degradation, compatibility issues, configuration errors, or security breaches.
Compliance with international laws and standards for secure communication protocols
This is also a relevant topic for EviSCP. Depending on the context and the jurisdiction of the parties involved in the communication, different laws and standards may apply to ensure the legality and the quality of the secure communication protocols. For example, some countries may require the use of specific encryption algorithms or key lengths, or may impose restrictions on the export or import of cryptographic products or services. Some examples of international laws and standards for secure communication protocols are: the Wassenaar Arrangement, the EU General Data Protection Regulation (GDPR), the ISO/IEC 27001 standard, or the NIST Special Publication 800-52.