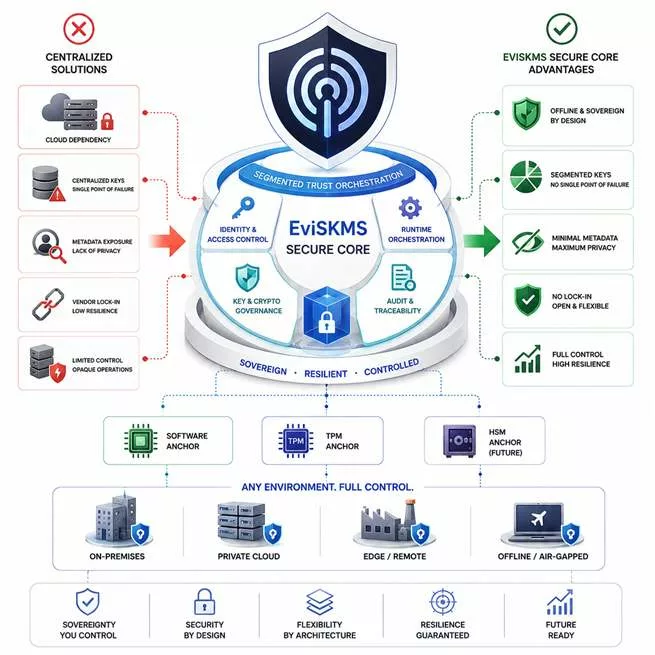
EviSKMS Core Runtime is a sovereign trust doctrine and runtime infrastructure foundation designed to establish evidence-bound trust orchestration, segmented governance and resilient operational continuity across sovereign environments. Unlike conventional cloud KMS platforms, centralized secret vaults or monolithic PKI infrastructures, EviSKMS Core Runtime focuses on runtime integrity, deterministic trust semantics, forensic continuity and fail-closed operational governance.
Designed for offline-first sovereign infrastructures, EviSKMS Core Runtime provides a modular doctrinal foundation supporting hardware-assisted trust, detached verification, runtime evidence continuity and compartmentalized trust execution across software, TPM and hybrid sovereign deployment environments.
Executive summary — What is EviSKMS Core Runtime?
This executive summary takes approximately 4 minutes to read. It explains the architectural role, sovereign principles and operational philosophy behind EviSKMS Core Runtime.
EviSKMS Core Runtime is the doctrinal and contractual foundation of the EviSKMS sovereign trust architecture. It defines runtime trust semantics, segmented governance principles, operational invariants and evidence-bound trust models designed for resilient, offline-capable and fail-closed infrastructures.
Rather than operating as a centralized PKI, cloud KMS or standalone HSM, EviSKMS Core Runtime establishes a sovereign trust framework capable of supporting runtime integrity, detached verification and compartmentalized trust execution across heterogeneous sovereign environments.
Principle — EviSKMS sovereign trust orchestration
EviSKMS Core Runtime separates trust operations into controlled layers. Consequently, sensitive operations can remain compartmentalized while preserving deployment flexibility. Furthermore, the architecture minimizes unnecessary metadata exposure and reduces dependency on third-party providers.
Runtime integrity — Evidence-bound sovereign runtime continuity
Traditional security models often rely on opaque trust assumptions and centralized operational dependencies. In contrast, EviSKMS Core Runtime focuses on runtime evidence continuity, deterministic trust evaluation and fail-closed runtime governance.
Consequently, sovereign infrastructures may preserve operational trust continuity even across constrained, offline or independently governed execution environments.
Strategic issue — Sovereign runtime trust infrastructure
Modern infrastructures increasingly face supply-chain opacity, metadata overexposure and unverifiable operational dependencies. As a result, organizations require sovereign runtime infrastructures capable of preserving trust continuity, detached verification and controlled operational lineage without structural dependency on centralized execution ecosystems.
Sovereign approach — Local cryptographic control strategy
Rather than centralizing secrets and trust decisions, EviSKMS Core Runtime prioritizes:
- segmented sovereign governance;
- runtime integrity continuity;
- offline-first trust execution;
- detached verification;
- forensic operational continuity;
- hardware-assisted sovereign trust;
- fail-closed runtime governance;
- metadata minimization.
Reading parameters
Quick summary: ≈ 4 min
Extended summary: ≈ 7 min
Full technical overview: ≈ 18 min
Technology category: Trust Infrastructure
Complexity level: Sovereign & Technical
Technical density: ≈ 72%
Architecture model: Sovereign runtime trust infrastructure
Deployment modes: Offline / Hybrid / Local / Sovereign
Core domains: runtime integrity, sovereign trust governance, forensic continuity, detached verification
Editorial type: Technology reference — Freemindtronic EviTech™
⮞ Strategic synthesis
EviSKMS Core Runtime does not attempt to replace PKI, TPM or HSM technologies. Instead, it establishes a sovereign runtime trust layer designed to preserve evidence-bound operational continuity, deterministic trust governance and resilient offline-first execution across heterogeneous trust environments.
In the Freemindtronic doctrine, sovereign trust does not emerge from centralized control accumulation or dependency-heavy operational ecosystems. Instead, sovereignty emerges from runtime integrity, deterministic governance, evidence continuity and compartmentalized trust execution.
Therefore, EviSKMS Core Runtime focuses on fail-closed operational governance, detached verification and sovereign runtime continuity rather than opaque centralized trust concentration.
Key insights — Sovereign trust infrastructure architecture
- EviSKMS Core Runtime establishes evidence-bound sovereign runtime governance.
- The architecture supports offline-first trust continuity.
- The infrastructure prioritizes fail-closed runtime integrity.
- The runtime supports detached verification and forensic continuity.
- EviSKMS Core Runtime separates doctrine, runtime and sovereign products.
- The architecture supports hardware-assisted and hybrid sovereign trust models.
- The infrastructure minimizes exposure to opaque centralized operational dependencies.
- Executive summary
- ⚙ Sovereign trust orchestration
- Runtime integrity
- Segmented trust infrastructure
- Local control strategy
- Key insights
- Advanced summary
- ⚙ Operational doctrine
- Modular runtime architecture
- Offline trust infrastructure
- Future secure anchors
- Software trust anchors
- TPM-backed operational trust
- Future HSM-compatible trust evolution
- Main architecture
- Core principles
- Runtime evidence governance
- Forensic continuity
- Sovereign runtime
- Architectural layers
- Deployment models
- Technology positioning
- Comparative positioning
- Patent foundations
- Segmented key authentication system — FR3063365
- Access control system — FR3047099
- Sovereign deployment use cases
- Strategic outlook
- Deployment contact
- Technical glossary
Extended summary — Secure Core runtime and segmented trust infrastructure
EviSKMS Core Runtime introduces a sovereign trust orchestration approach designed for infrastructures that require controlled cryptographic execution without excessive reliance on centralized providers. While many cloud-native security architectures aggregate identities, telemetry and operational metadata into external infrastructures, EviSKMS Core Runtime follows a radically different operational doctrine.
Operational doctrine — Secure Core controlled trust execution
First, the architecture minimizes unnecessary exposure. Second, it compartmentalizes runtime operations. Third, it enables trust execution through segmented orchestration layers rather than monolithic centralized trust systems.
Modular cryptographic runtime architecture
Consequently, organizations can deploy:
- local trust runtimes;
- offline-capable identity infrastructures;
- segmented PKI services;
- controlled cryptographic orchestration layers;
- hardware-assisted sovereign trust infrastructures.
Offline trust infrastructure and sovereign deployment
Furthermore, EviSKMS Core Runtime remains intentionally modular. Therefore, organizations can integrate:
- software trust anchors;
- TPM-compatible sovereign runtime environments;
- hardware-assisted sovereign infrastructures;
- offline root infrastructures;
- hybrid sovereign deployment models.
⮞ End of extended summary — Beginning of the technical article
The previous section provided an advanced overview of EviSKMS Core Runtime. The following article now details the architecture, operational doctrine, trust layers and sovereign deployment logic behind this segmented cryptographic runtime technology.
Segmented trust architecture — From runtime orchestration to sovereign control
| Principle | Description |
|---|---|
| Segmented trust governance | Trust operations remain compartmentalized instead of globally centralized. |
| Runtime integrity | The architecture prioritizes controlled execution and operational consistency. |
| Metadata minimization | The infrastructure reduces unnecessary exposure to external analytics ecosystems. |
| Sovereign deployment | Deployments can operate locally, offline or within controlled infrastructures. |
| Anchor abstraction | The runtime remains compatible with software, TPM and future HSM anchoring strategies. |
| Operational resilience | The architecture isolates failures and limits systemic trust exposure. |
Architectural layers — EviSKMS trust orchestration model
| Layer | Role |
|---|---|
| EviSKMS Core Runtime | Runtime orchestration, segmented governance and trust lifecycle coordination. |
| EviSKMS PKI | Identity services, signing operations and trust distribution. |
| EviSKMS Secure Anchors | TPM, software or future HSM anchoring strategies. |
| SDK / API | Controlled integration with external services and sovereign applications. |
| Deployment Runtime | Execution environment for local, hybrid or offline infrastructures. |
Deployment models — Offline trust infrastructure and sovereign runtime
EviSKMS Core Runtime supports multiple deployment approaches because operational sovereignty depends on context. Therefore, organizations can adapt the infrastructure according to operational, industrial or strategic requirements.
- Offline deployment — isolated infrastructures and sovereign execution contexts.
- Hybrid deployment — controlled interaction between local runtime and external services.
- Local trust infrastructure — compartmentalized runtime execution on-premises.
- Hardware-assisted sovereign trust — TPM-compatible and hybrid sovereign runtime infrastructures.
Moreover, the architecture intentionally avoids mandatory dependency on centralized trust providers. Consequently, organizations preserve greater operational control over cryptographic governance and trust lifecycle management.
Forensic continuity and sovereign lineage
EviSKMS Core Runtime supports sovereign operational continuity models designed to preserve runtime lineage visibility, release trust continuity and controlled verification semantics across evolving deployment states.
Rather than relying exclusively on centralized telemetry collection, the architecture promotes evidence-bound runtime continuity principles compatible with offline-first sovereign infrastructures.
- runtime evidence continuity;
- detached operational verification;
- release trust lineage;
- supply-chain trust governance;
- fail-closed operational continuity.
Hardware-assisted sovereign trust infrastructure
EviSKMS Core Runtime was intentionally designed to remain independent from a single anchoring model.
Therefore, the architecture supports progressive trust evolution without requiring structural redesign of the runtime orchestration layer.
Unlike rigid infrastructures tightly coupled to proprietary HSM vendors or centralized cloud KMS ecosystems, EviSKMS Core Runtime separates:
- trust orchestration;
- runtime governance;
- trust governance separation;
- cryptographic anchoring mechanisms.
Software trust anchors for sovereign runtime deployment
The runtime can operate using software-based trust anchors when sovereign deployment constraints require flexible local execution.
Consequently, organizations can deploy controlled trust infrastructures without mandatory hardware dependency.
TPM-backed operational trust for secure runtime anchoring
When TPM technologies are available, EviSKMS Core Runtime can integrate platform-assisted trust anchoring strategies aligned with concepts promoted by the Trusted Computing Group (TCG).
Hardware-assisted sovereign trust infrastructure
The architecture supports hardware-assisted sovereign trust environments compatible with controlled runtime governance and detached verification principles, including operational ecosystems aligned with industry validation approaches such as the NIST Cryptographic Module Validation Program (CMVP).
However, EviSKMS Core Runtime does not depend on a specific hardware vendor or closed ecosystem. Instead, the runtime abstracts trust orchestration from the physical anchoring layer itself.
Therefore, organizations may progressively evolve toward:
- offline root trust infrastructures;
- hardware-backed cryptographic governance;
- hardware-assisted sovereign trust models;
- critical infrastructure trust anchoring;
- resilient sovereign execution environments.
EviSKMS Core Runtime does not define sovereignty through hardware alone.
Instead, sovereignty emerges from controlled orchestration, segmented governance and resilient trust execution independently from the underlying anchoring technology.
Runtime evidence governance
EviSKMS Core Runtime introduces a sovereign governance approach where runtime trust continuity relies on evidence-bound operational validation rather than opaque execution assumptions.
The architecture prioritizes:
- runtime integrity continuity;
- deterministic trust semantics;
- detached verification;
- offline operational resilience;
- forensic continuity;
- fail-closed trust evaluation.
Technology positioning — Sovereign PKI, KMS, HSM and trust runtime
Traditional PKI ecosystems commonly rely on standards such as RFC 5280 — Internet X.509 Public Key Infrastructure.
However, EviSKMS Core Runtime focuses primarily on sovereign trust orchestration and segmented runtime governance rather than acting as a monolithic public certificate authority.
| Technology | Primary role | EviSKMS Core Runtime relationship |
|---|---|---|
| Traditional PKI | Certificate hierarchy and trust issuance | Can operate as a trust service layer above Secure Core. |
| Cloud KMS | Centralized key storage and management | EviSKMS minimizes opaque external trust dependencies. |
| HSM | Hardware trust anchoring | Acts as a future-compatible anchoring backend. |
| TPM | Platform trust anchoring | Supports hardware-assisted runtime strategies. |
| EviSKMS Core Runtime | Sovereign trust orchestration runtime | Coordinates segmented cryptographic governance. |
Comparative positioning — Sovereign runtime orchestration versus traditional trust models
| Capability | Traditional Cloud KMS | Traditional PKI | EviSKMS Core Runtime |
|---|---|---|---|
| Offline-capable deployment | Limited | Partial | Native architectural objective |
| Segmented trust orchestration | Limited | No | Core architecture principle |
| Metadata minimization | Low | Moderate | Strategic operational objective |
| Hardware independence | Vendor dependent | Partial | Anchor abstraction compatible |
| Sovereign runtime governance | Externalized | Hierarchical | Compartmentalized runtime model |
| Trust orchestration flexibility | Moderate | Low | High |
Patent foundations — Segmented key authentication and sovereign trust roots
EviSKMS Core Runtime is not solely a conceptual trust orchestration framework. The technology also derives from concrete industrial research and patented security mechanisms developed by Freemindtronic.
Depending on sovereign operational models, runtime governance requirements and trust orchestration layers, EviSKMS Core Runtime may integrate concepts originating from multiple patented technologies focused on sovereign cryptographic governance, segmented trust activation and resilient access control infrastructures.
→ View Freemindtronic international patents
Segmented key authentication system — FR3063365 issued
One of the primary technological foundations behind EviSKMS Core Runtime originates from the patent:
Segmented key authentication system — FR3063365 Issued
This patented approach introduces segmented trust governance principles where cryptographic operations rely on compartmentalized orchestration rather than monolithic centralized key exposure.
Consequently, the architecture supports:
- segmented cryptographic governance;
- deterministic trust governance;
- runtime compartmentalization;
- resilient trust execution models;
- sovereign operational control.
Access control system — FR3047099 issued
Certain EviSKMS deployment models may also implement operational concepts derived from:
Access control system — FR3047099 Issued
This patent contributes to secure identity handling, operational compartmentalization and resilient access orchestration strategies designed for controlled sovereign environments.
Industrial continuity and sovereign implementation
Rather than treating patents as isolated intellectual-property artifacts, Freemindtronic integrates these technologies into operational trust infrastructure strategies designed for real deployment constraints, resilient runtime execution and sovereign digital governance.
Therefore, EviSKMS Core Runtime represents both:
- a sovereign trust orchestration technology;
- and an industrial implementation layer derived from patented security research.
The EviSKMS technology family combines sovereign runtime orchestration, segmented trust governance and patented security mechanisms into a modular trust infrastructure approach designed for long-term operational resilience.
Sovereign deployment use cases — Critical infrastructure and controlled trust runtime
EviSKMS Core Runtime was designed for environments where operational resilience, cryptographic compartmentalization and sovereign execution control remain strategic requirements rather than optional security features.
Consequently, the segmented runtime governance model can support sovereign operational infrastructures requiring resilient trust continuity and reduced dependency exposure.
| Sector | Potential deployment objective |
|---|---|
| Critical infrastructure | Offline-capable trust governance for resilient operational continuity. |
| Defense and sovereign operations | Segmented runtime governance for resilient sovereign operational continuity. |
| Industrial environments | Compartmentalized trust execution for sensitive operational systems. |
| Air-gapped infrastructures | Offline-first sovereign runtime continuity. |
| Sovereign cloud initiatives | Runtime integrity and metadata minimization strategies. |
| Secure mobility ecosystems | Controlled identity orchestration and resilient trust anchoring. |
EviSKMS Core Runtime focuses on operational sovereignty through segmented runtime control, resilient trust orchestration and infrastructure compartmentalization rather than centralized trust accumulation.
Strategic outlook — Secure Core trust infrastructure evolution
As digital infrastructures become increasingly dependent on external telemetry, centralized identity providers and opaque operational chains, sovereign trust infrastructure becomes strategically essential. Therefore, EviSKMS Core Runtime positions itself as a resilient orchestration technology capable of supporting long-term sovereign deployment strategies.
Rather than concentrating trust into a single external provider, the architecture distributes operational responsibility across segmented runtime layers. Consequently, organizations can reinforce resilience while reducing metadata exposure and systemic dependency risks.
Operational evolution pathways may include:
- advanced trust lifecycle orchestration;
- extended PKI services;
- hardware-assisted runtime trust continuity;
- sovereign edge runtime deployments;
- critical infrastructure integration;
- offline trust governance frameworks.
Discuss sovereign trust infrastructure deployment
Organizations exploring sovereign trust runtime orchestration, segmented cryptographic governance or resilient offline-capable deployment strategies may request additional technical information regarding EviSKMS Core Runtime integration models and operational deployment approaches.
- sovereign infrastructure integration;
- offline deployment architecture;
- TPM-compatible and hardware-assisted sovereign trust infrastructures;
- segmented runtime orchestration;
- critical infrastructure deployment scenarios;
- OEM and institutional integration discussions.
→ Contact Freemindtronic for deployment and integration information