Fortyss
Fortyss – Verifiable Backup Platform with Cryptographic Proof and DSACS Integrity Engine
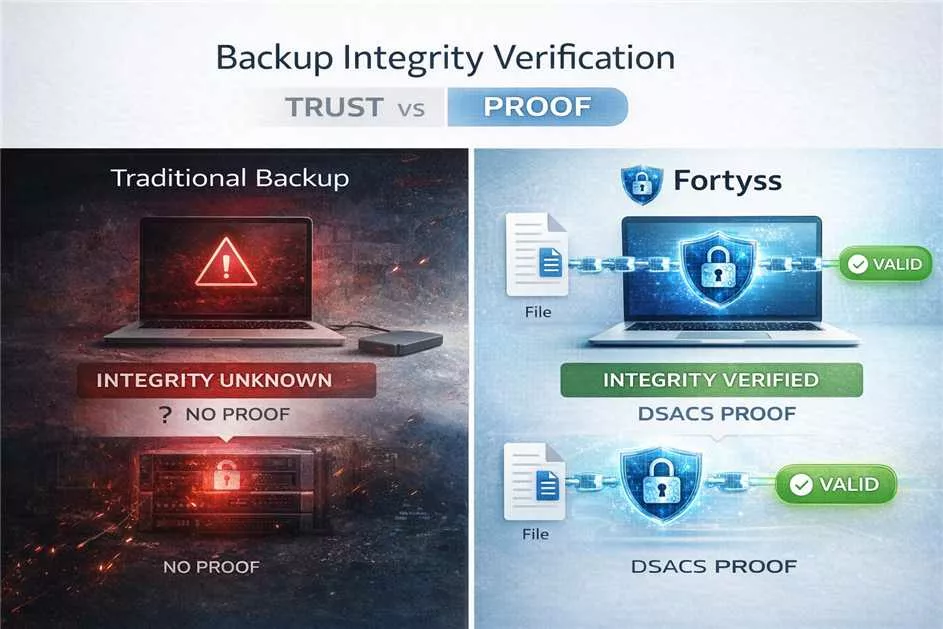
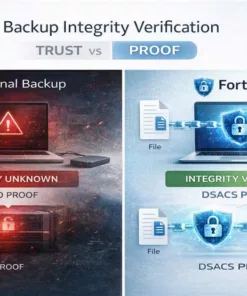
Fortyss is a next-generation verifiable backup platform developed by Freemindtronic Andorra, designed to go beyond traditional data protection by delivering mathematical proof of data integrity.
Unlike conventional backup software that relies on implicit trust, Fortyss enables organizations to verify that data has not been altered, deleted, or tampered with by generating cryptographically verifiable proof for every backup operation through its advanced DSACS (Distributed Secure Audit Chain System) technology.
Fortyss transforms backup into a cryptographic proof infrastructure, combining tamper-evident backup storage, forensic-ready evidence reports, and a strict fail-closed verification model in which integrity is never assumed — only proven.
Patented Security Architecture and Segmented Key Authentication
Fortyss integrates patented security technologies developed by Freemindtronic Andorra, including a unique segmented key authentication system designed to strengthen protection against unauthorized access and cryptographic compromise.
This architecture relies on the distribution and controlled activation of cryptographic key segments so that sensitive operations — such as proof generation, verification, and access control — are never dependent on a single exposed secret.
Key benefits include:
- Segmented key authentication reducing single-point-of-failure risks
- Enhanced resistance to key extraction and replay attacks
- Secure cryptographic operations bound to controlled contexts
- Integration with the DSACS audit chain for verifiable operations
Some of these mechanisms are based on patented innovations, reinforcing the uniqueness, resilience, and defensibility of the Fortyss platform.
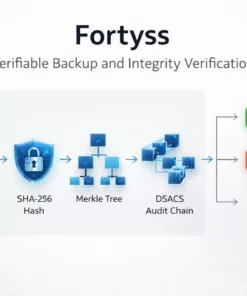
Proof-Based Backup: From Storage to Verifiable Evidence
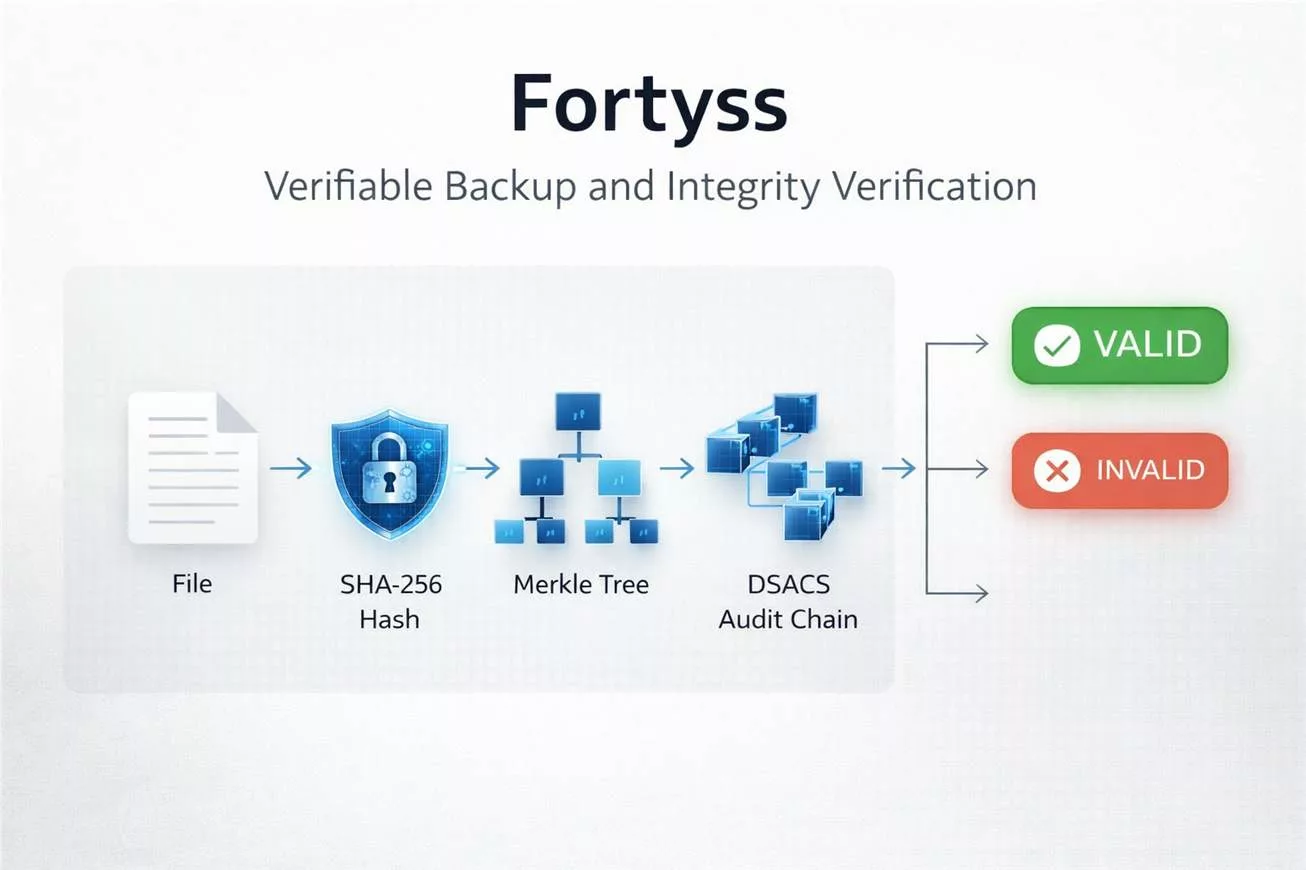
Each backup operation in Fortyss generates a cryptographic proof bundle that can be independently verified at any time. This proof structure includes:
- SHA-256 data hashing for integrity baseline
- Merkle root computation for dataset consistency validation
- Registration in a DSACS-based non-forkable audit chain
- Cryptographic receipt and attestation data
- Proof export in JSON (machine-readable) and PDF (human-readable forensic report)
This makes Fortyss a true backup integrity verification platform, capable of producing deterministic VALID / INVALID results under a strict fail-closed model.
Advanced Cryptographic Architecture
Fortyss combines proprietary and industry-standard security mechanisms developed by Freemindtronic:
- DSACS Engine: audit-chain-based proof registration and verification
- SHA-256 hashing: cryptographic fingerprinting of backup data
- Merkle Tree validation: structural integrity verification for datasets
- AES-256-GCM encryption (optional): authenticated encryption for backup data at rest
- Proof bundles: including receipt, audit chain segment, and verification metadata
- Fail-closed verification: any inconsistency results in failure, never silent success
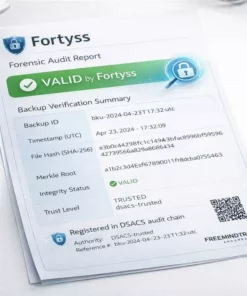
Forensic-Ready Proof and Audit Compliance
Fortyss produces audit-ready, forensic-ready reports suitable for cybersecurity investigations, compliance workflows, and evidence documentation.
Exports include:
- Technical JSON proof bundle (source of truth)
- Human-readable PDF forensic report
Each report can include:
- Backup ID and timestamp (UTC)
- File name and versioning information
- Data hash and Merkle root
- Integrity status (VALID / INVALID)
- Trust level (DEVELOPMENT / TRUSTED)
- Authority type (local-dev / dsacs-trusted)
- Audit chain references and receipt data
- Verification timestamps and evidence summary
This makes Fortyss relevant for forensic analysis, cybersecurity audits, compliance-driven environments, and documentation designed to support legal and audit workflows.
Resilience Against Ransomware and Data Tampering
Fortyss improves resilience against ransomware and malicious data modification by combining:
- Immutable proof verification mechanisms
- Versioned backup tracking per file
- Mandatory integrity validation before restore
- Fail-safe restore policies that restore only verified backups
Any unauthorized modification triggers an immediate HASH_MISMATCH or INVALID status, ensuring that compromised backups are never silently trusted or restored.
Flexible Deployment and Trust Models
Fortyss supports multiple security levels:
- Standard Mode: development authority for testing and local environments
- Trusted Mode: DSACS trusted authority with cryptographic key enforcement
- Sovereign Mode (planned roadmap feature): hardware-rooted trust with TPM and secure boot integration
Designed for High-Security and Critical Environments
Fortyss is designed for:
- Critical infrastructure and sensitive systems
- Cybersecurity and incident response teams
- Compliance-driven organizations and regulated sectors
- Digital forensic investigations
- Sovereign and offline-secured data storage environments
Freemindtronic Technology Ecosystem Integration
Developed by Freemindtronic Andorra, Fortyss can integrate with advanced proprietary technologies:
- DSACS secure audit chain system
- Hardware Security Modules (HSM)
- EviKey secure storage devices (optional hardware-based protection)
- Advanced cryptographic architectures and secure elements
Key Features of Fortyss
| Category | Feature | Fortyss |
|---|---|---|
| Backup | File and dataset backup with proof | ✅ |
| Versioning per file | ✅ | |
| Restore with integrity verification | ✅ | |
| Security | SHA-256 hashing | ✅ |
| Merkle root validation | ✅ | |
| AES-256-GCM encryption (optional) | ✅ | |
| Fail-closed verification | ✅ | |
| Proof | DSACS audit chain | ✅ |
| Proof bundle export | ✅ | |
| Forensic PDF report | ✅ | |
| Deployment | Offline / sovereign capability | ✅ |
| CLI / API / UI access | ✅ |
Fortyss redefines backup by transforming it into a verifiable, auditable, and cryptographically provable backup system, where integrity assurance is no longer based on trust — but on mathematical evidence.
Unlike traditional backup solutions, Fortyss is built on a patented cryptographic architecture combined with segmented key authentication, delivering a level of integrity assurance and access control that is difficult to replicate with conventional backup architectures.
Be the first to review “Fortyss” Cancel reply
This site uses Akismet to reduce spam. Learn how your comment data is processed.

Reviews
There are no reviews yet.