EviEngine
Distributed Secure Authorization Cryptographic System (DSACS-HB) — Hardware-Rooted, Runtime-Validated, Infrastructure-Independent
EviEngine is a hardware-anchored distributed trust execution architecture.
EviEngine is a patented distributed cryptographic authorization architecture implementing hardware-anchored cryptographic validation without centralized infrastructure. It is protected by granted international patents covering segmented cryptographic authentication, distributed authorization mechanisms and secure reconstruction logic.
EviEngine is not a software product but a security architecture model.
Unlike traditional authentication engines, EviEngine operates through a hardware-bound execution logic that allows data storage on any medium chosen by the operator: local drives, removable devices, network storage, or remote repositories.
Originally engineered to enforce software license usage rights for browser extensions without centralized validation servers, EviEngine establishes cryptographically controlled trust relationships between hardware-rooted execution proof + cryptographic segmentation.
EviEngine operates natively across Linux, Windows and macOS environments, enabling deployment from user endpoints to sovereign infrastructure systems.
This architecture eliminates reliance on third-party trust infrastructures while preserving verifiable execution integrity, traceability, and cryptographic authenticity.
Unlike PKI, HSM or IAM architectures, EviEngine removes runtime dependency on external validation authorities and replaces it with locally verifiable authorization logic, creating a class of authorization systems where compromise requires combining multiple independent protection mechanisms across cryptographic and hardware domains rather than exploiting a single centralized point of failure.
EviEngine is a patented advanced distributed authorization architecture whose security guarantees derive from segmented cryptographic design principles and hardware-generated cryptographic proofs, hardware-bound execution context, and infrastructure independence rather than from centralized validation, secret storage, or software-reproducible conditions.
DSACS-HB-RV (Distributed Secure Authentication Cryptographic System — Hardware-Bound — Runtime Verified)
Security does not rely on secrecy, infrastructure, or authority — only on independent validation factors.
EviEngine is a deterministic distributed hardware-bound authorization architecture ensuring cryptographic execution integrity without reliance on centralized infrastructure.
Hardware trust anchors such as TPM proof can be enforced as a cryptographic execution condition and verified through deterministic runtime validation.
EviEngine operates under a deterministic local trust model where authorization validity derives exclusively from verifiable cryptographic conditions and hardware-bound execution context, eliminating reliance on third-party trust authorities.
| Model | Trust Anchor |
|---|---|
| PKI | remote authority |
| OAuth | identity provider |
| IAM | central directory |
| HSM | hardware container |
| EviEngine | execution environment |
EviEngine establishes a trusted execution bridge between the operating system and web browsers through a background cryptographic process. It runs autonomously without user interaction, interface, or manual configuration.
The executable components are code-signed binaries optionally validated through operating-system trust stores (Windows and macOS), ensuring verifiable integrity and authenticity.
EviEngine acts as a hardware-bound cryptographic validator capable of:
This mechanism replaces traditional server-side validation infrastructures with a local cryptographic trust anchor, reducing attack surface and eliminating remote interception vectors.
EviEngine communicates through a native messaging bridge between browser runtime and operating system using structured command messages validated locally before execution.
EviEngine provides a deterministic execution framework combining automation, cryptographic validation, and distributed trust logic.
Because validation occurs locally and cryptographically, execution integrity does not depend on network availability or remote infrastructures.
The security architecture of EviEngine is based on distributed cryptographic segmentation principles.
Each cryptographic segment is isolated and cannot be exploited independently. Reconstruction occurs only under validated execution conditions, preventing unauthorized recomposition attempts.
Because no centralized storage exists, mass extraction attacks are structurally mitigated.
Systems without centralized validation dependencies structurally reduce systemic compromise vectors, because no single compromise event can invalidate global trust.
EviEngine is formally classified within the category of advanced distributed security architectures combining properties observed in:
This positioning places EviEngine outside traditional software categories and within the class of infrastructure-independent trust enforcement mechanisms.
This architectural positioning places EviEngine within the category of decentralized trust infrastructures designed for high-integrity execution environments.
EviEngine introduces a new architectural class: infrastructure-independent authorization systems.
This class differs from traditional trust models by eliminating dependency on remote validation authority.
This score estimates the degree of architectural rupture compared with dominant licensing and authorization models. It is computed using a transparent multi-axis method.
| Axis | Definition | Weight | Score (0–10) | Rationale |
|---|---|---|---|---|
| Infrastructure elimination | No server/DB/CA/IdP required for authorization | 25% | 10 | Authorization remains operational with zero external infrastructure |
| Systemic risk suppression | No single compromise event can invalidate global trust | 20% | 9 | No centralized datastore or validation endpoint to breach |
| Hardware anchoring | Authorization bound to execution context / hardware factors | 15% | 8 | Hardware-backed validation factors can strengthen authorization guarantees. |
| Segmentation novelty | Distributed segmented cryptographic conditions for authorization | 20% | 9 | Segmentation reduces exploitability of single artifacts and reduces replay feasibility |
| Deployment realism | Works in real environments without specialized infrastructure | 10% | 8 | Browser-native messaging + OS signing model supports production deployment |
| Comparative substitutability | Replaces classes of online licensing patterns | 10% | 8 | Substitutes server validation while preserving authenticity checks |
Weighted Disruption Score: 9.0 / 10
A score above 8 indicates an architectural rupture: the system changes the dominant dependency chain (server → database → centralized authority) into a deterministic local authorization model.
This score does not claim formal certification level. It quantifies architectural differentiation based on infrastructure dependency, systemic compromise vectors, and verification locality.
EviEngine belongs to the class of infrastructure-independent authorization architectures. The matrix below positions it against widely deployed global trust and authorization models.
| Architecture class | Primary trust anchor | Infrastructure dependency | Systemic compromise mode | Typical attack surface | EviEngine relative positioning |
|---|---|---|---|---|---|
| PKI / CA-based trust | Certificate Authority | High (CA, cert lifecycle) | CA compromise cascades globally | issuance, revocation, endpoints | Different model: no CA required |
| Identity federation (OAuth/OIDC) | Identity Provider | High (IdP availability) | IdP breach enables broad impersonation | tokens, redirect flows | Different model: no IdP dependency |
| Centralized IAM | Directory / policy engine | High (directory + policy) | Directory breach affects entire org | admin plane, policy plane | Different model: no central directory |
| Centralized HSM / key vault | Hardware container | Medium/High | Vault compromise impacts key estate | API, admin plane | Different: no central key container |
| Confidential computing (SGX/TEE) | CPU enclave attestation | Medium (attestation stack) | Micro-architectural flaws can break model | side-channels, enclave escapes | Complementary, not equivalent |
| TPM-bound security | TPM + platform state | Low/Medium | Local compromise bounded to host | boot chain, OS compromise | Optional hardware trust anchor enforceable by policy |
| EviEngine (DSACS) | Execution environment + segmented cryptographic conditions | None (serverless/databaseless) | No centralized systemic compromise vector | local host integrity, physical access | Baseline reference for ZITA class |
Interpretation: EviEngine is positioned as a distributed authorization architecture where trust does not propagate through central authorities. The main risk boundary is local execution context integrity rather than infrastructure integrity.
This mapping compares EviEngine to established security paradigms. The goal is categorical clarity, not equivalence claims.
| Model | What it primarily solves | Core assumption | Where it breaks | EviEngine relation |
|---|---|---|---|---|
| Zero Trust (network & identity) | Reduce implicit trust across networks | continuous verification via policies/telemetry | depends on centralized policy/identity planes | EviEngine provides a local trust anchor for execution authorization, compatible with Zero Trust programs but infrastructure-independent |
| PKI | Identity & integrity via certificates | CA ecosystem remains trusted | CA compromise / mis-issuance cascades | EviEngine is not PKI: it does not require a CA chain for authorization |
| HSM | Key protection and signing operations | keys remain inside secure boundary | centralization creates high-value target | EviEngine is not a key vault: it enforces authorization conditions rather than acting as a universal key container |
| IAM | Access governance (users, roles, policies) | identity is primary control plane | directory/policy compromise is systemic | EviEngine binds authorization to execution context rather than identity |
| SGX / TEEs | Confidential execution with attestation | TEE isolation is reliable | side-channel & micro-arch vulnerabilities | EviEngine is orthogonal: it can benefit from TEEs but does not rely on them for its trust model |
| TPM | Hardware root-of-trust & measured boot | boot chain integrity can be verified | OS compromise after boot remains possible | EviEngine can use TPM as a hardware binding factor for segmented trust conditions |
EviEngine is best classified as a hardware-anchored, infrastructure-independent authorization engine implementing distributed cryptographic conditions, including segmented reconstruction constraints.
The underlying technology is protected by a family of granted national patents originating from an international patent application, including FR3063365 B1 and EP3586258 B1, as well as corresponding national titles. These patents cover mechanisms for segmented key management, distributed authentication, and secure reconstruction processes.
Patent protection covers core architectural and cryptographic implementation concepts, ensuring enforceability against functional replication, not only source implementation.
The invention originates from the French priority patent FR3063365 B1.
The scope of protection includes:
This intellectual property framework establishes verifiable technical novelty and ensures legal traceability of the architectural concepts implemented.
| Traditional License Systems | EviEngine |
|---|---|
| Server compromise impact | None |
| Server required | No |
| Interception risk | No |
| Cloud dependency | No |
| Remote MITM against validation endpoints | Eliminated in the absence of centralized validation endpoints |
| License cloning | Hardware-prevented |
The absence of centralized validation endpoints removes entire classes of attack vectors including replay attacks, credential harvesting, and infrastructure compromise.
EviEngine integrates both cyber safety and cybersecurity principles through its distributed architecture.
Because execution logic is local, autonomous, and cryptographically validated, the attack surface is reduced to the physical environment itself.
EviEngine assumes adversaries capable of network interception, token extraction, replay attempts and server compromise. Security guarantees hold provided the host operating system integrity is preserved and execution context authenticity is maintained.
EviEngine enables advanced manipulation and control of web-service features while preserving execution integrity.
EviEngine is integrated into advanced cybersecurity software including PassCypher HSM PGP, DataShielder HSM and CryptPeer.
Implements secure secret management using a dedicated instance of the engine.
Implements encryption key lifecycle control with distributed authentication logic.
Peer-to-peer encrypted communication platform implementing distributed authentication and segmented trust validation through EviEngine.
EviEngine is a distributed secure authentication cryptographic system designed to replace centralized validation infrastructures with deterministic local trust mechanisms.
EviEngine introduces a new class of offline-native trust infrastructures.
Institutional Alignment Annex — Sovereign Jurisdiction Compliance Model
Normative classification and architectural alignment statements provided for technical and analytical purposes.
Supported platforms: Linux, Windows and macOS
EviEngine follows core sovereign cybersecurity architecture principles aligned with sovereign cybersecurity architectural principles emphasizing minimized attack surface, elimination of centralized trust dependencies, and strict cryptographic isolation. Its distributed authorization model enforces local trust validation and removes systemic compromise vectors associated with centralized infrastructures.
| Function | EviEngine Implementation |
|---|---|
| Identify | hardware-bound environment validation |
| Protect | local cryptographic authorization logic |
| Detect | execution-context anomaly detection |
| Respond | automatic execution denial |
| Recover | deterministic reconstruction conditions |
Primary class: Distributed Deterministic Authorization Architecture
Subclass: Hardware-Bound Cryptographic Execution Systems
Formal properties
Security guarantees rely on cryptographic hardness assumptions and distributed validation constraints rather than implementation secrecy. Therefore, security properties remain preserved even under full disclosure conditions, consistent with Kerckhoffs’s principle.
Assuming an adversary possessing network interception capability, binary access, storage inspection and execution monitoring, unauthorized execution remains practically infeasible under realistic adversarial conditions unless all of the following conditions are simultaneously compromised including the hardware root of trust:
Because these elements are structurally independent, compromise requires multi-domain simultaneous intrusion, which significantly increases attack complexity and reduces feasibility.
Optional Hardware Reinforcement Model
In certain deployment profiles, execution integrity may be strengthened through hardware-assisted cryptographic validation mechanisms.
Security Objective
When hardware reinforcement is enabled, authorization validity cannot be reproduced through software manipulation alone, as additional cryptographic factors may be derived from non-exportable device capabilities bound to the execution context.
Core Characteristics
EviEngine is designed to maintain a high level of resilience even in scenarios involving binary inspection or reverse-engineering attempts. Its security posture does not rely on source code secrecy but on layered protection mechanisms and segmentation and reconstruction safeguards.
As a result, static analysis, disassembly, or memory inspection alone are insufficient to reproduce or bypass authorization safeguards. Security robustness is achieved through architectural design principles rather than implementation obscurity.
EviEngine follows a structural security paradigm where protection is achieved through architectural properties rather than through obscurity or secrecy of implementation. This model aligns with modern high-assurance system design methodologies.
This table compares different architectures across key dimensions such as attack surface, infrastructure dependency, hardware binding, offline capability, segmentation, and reliance on central authority.
| Architecture | Attack Surface | Infrastructure Dependency | Hardware-Bound | Offline Capability | Segmentation | Central Authority |
|---|---|---|---|---|---|---|
| EviEngine | Very Low | None | Yes | Yes | Native | None |
| PKI | Medium | High | No | No | None | Certificate Authority |
| IAM | High | Total | No | No | None | Directory |
| Central HSM | Low | Medium | Yes | No | Limited | Appliance |
| TPM | Low | Low | Yes | Partial | Limited | Manufacturer |
| SGX | Medium | Medium | Yes | No | Limited | Vendor |
This radar visualization provides a structural comparison of major security architectures across six fundamental dimensions:
attack surface, infrastructure dependency, hardware binding, offline capability, segmentation and central authority reliance.
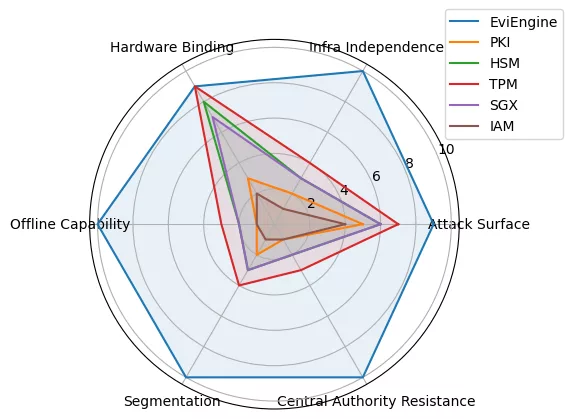
This table highlights the unique differentiators of each technology class, showing how EviEngine departs from traditional models by removing dependencies on centralized infrastructures.
| Technology Class | Key Distinction |
|---|---|
| PKI | No certificate authority dependency |
| HSM | No central key container |
| IAM | Authorization bound to environment, not identity |
| License Systems | No validation server |
| Zero Trust | Local trust anchor rather than remote |
System designation
Distributed Secure Authentication Cryptographic System (DSACS)
Architecture type
Hardware-Anchored Distributed Authorization Engine
Infrastructure model
Deterministic Offline Trust Infrastructure
EviEngine architecture aligns with the cybersecurity governance principles established under Andorran national regulatory frameworks promoting sovereign digital security, infrastructure independence and protection against systemic cyber risk.
Its design is consistent with the strategic objectives defined by Andorra’s national cybersecurity governance model, which emphasizes:
Because EviEngine operates without centralized validation servers, external trust authorities or remote execution dependencies, its architecture inherently satisfies structural resilience principles recommended for sovereign digital systems operating under national jurisdictional control.
This architectural independence makes EviEngine particularly suitable for deployment in environments requiring jurisdictional control, regulatory predictability and verifiable autonomy of execution.
Systems without centralized validation authority structurally eliminate systemic compromise vectors because no single breach can invalidate global authorization integrity. EviEngine enforces this principle through distributed cryptographic segmentation and local deterministic verification.
EviEngine architecture is structurally aligned with European cybersecurity resilience principles reflected in regulatory frameworks governing digital infrastructure security, including requirements related to operational continuity, systemic risk reduction and secure execution environments.
Because authorization validation occurs locally and cryptographically, compromise of external infrastructure cannot affect system integrity. This architectural property supports resilience expectations defined for critical digital services operating within European regulatory environments.
EviEngine is designed to operate within sovereign digital environments where infrastructure independence, jurisdictional control and deterministic execution verification are required.
Its architecture eliminates reliance on third-party validation authorities, remote license servers or centralized trust providers. As a result, operational control remains entirely within the deployment jurisdiction.
This model supports sovereign deployment requirements for environments where external infrastructure trust cannot be assumed.
EviEngine implements a resilience-first architecture where execution validity depends exclusively on locally verifiable cryptographic conditions rather than network availability or remote system integrity.
This design provides intrinsic resistance against systemic infrastructure failures including:
Because no remote dependency exists, infrastructure failure does not degrade authorization reliability. Execution guarantees therefore remain stable even under degraded network conditions or hostile connectivity environments.
EviEngine belongs to the class of deterministic distributed authorization architectures whose security guarantees derive from structural design rather than from operational secrecy. Systems in this category are considered intrinsically resilient to systemic compromise because no single failure condition can invalidate global authorization integrity.
Because authorization validity is locally determined, failure of any external infrastructure cannot propagate into execution authorization states. This property ensures failure isolation and prevents cascading trust compromise.
Based on its architectural characteristics, EviEngine can be classified within the category of infrastructure-independent security control systems designed to operate in high-integrity environments.
Qualifying properties
These characteristics align with security architecture principles commonly required for software components deployed within sensitive or high-reliability operational environments.
Based on architectural properties and operational behavior, EviEngine belongs to the category of distributed trust enforcement systems suitable for high-integrity execution environments requiring infrastructure independence and deterministic authorization control.
Security Tier Classification
| Security Dimension | Resistance Level |
|---|---|
| Remote attack surface | Minimal |
| Infrastructure dependency | None |
| Cryptographically and architecturally mitigated | Structurally mitigated |
| Replay attack resistance | Native |
| Server compromise exposure | structurally irrelevant |
| resistant to practical offline attacks under standard computational assumptions | High |
| Systemic compromise probability | significantly reduced in the absence of physical or kernel-level compromise |
Formal architectural robustness classification:High Assurance Distributed Authorization System
Security guarantees are evaluated assuming adversaries with advanced capabilities including:
Pure software emulation cannot reproduce the same authorization guarantees under hardware-assisted validation conditions.
Under these conditions, authorization integrity remains preserved because execution validity depends on distributed cryptographic conditions rather than on secrecy of implementation.
| Threat Class | Resistance Mechanism |
|---|---|
| Credential harvesting | No central credential storage |
| License cloning | Hardware-bound validation |
| MITM attack | No remote validation channel |
| Server breach | No server dependency |
| Replay attack | Context-bound authorization |
| Mass extraction | Distributed segmentation |
| Infrastructure compromise | Local deterministic verification |
Architectures that eliminate centralized validation authority structurally remove systemic compromise vectors. EviEngine implements this principle by ensuring that authorization validity cannot be altered through compromise of any single infrastructure component.
These characteristics position EviEngine within the class of high-assurance authorization control architectures suitable for environments requiring predictable execution integrity.